Hello everybody!!
First of all, excuse me that I have not posted anything, I carry many things at once and between work, studies, various projects, trips and I have two things that I want to post and I have almost finished, I do not have time, even for myself.
But well, today I bring you something light. Some time ago I received a rather striking email, I had never received anything like that and the truth, it amazed me as the scammers are so careful. This is why, I would like to talk about this topic, and being connected has many dangers, including phishing.
Most of you will know what phishing is, but in case someone doesn’t know it, phishing is a method by which they try to extract all kinds of confidential information fraudulently from the victim (any of us), mainly bank account data. Phishing is nothing more than a type of social engineering, in which they impersonate an identity (a real person or entity) to make the victim believe it is trustworthy and sting in the hook. Phishers (those who do phishing) primarily use email or some type of instant messaging.
Although many people think that the danger is phishing, they are wrong, the danger is always present and can manifest itself in many ways, including phishing. Although there are many other ways, such as smishing, that instead of email use SMS on mobile, or vishing, with phone calls. All of them are variants and belong to the Social Engineering group.
After that, I make a special mention to all types of social engineering, something that very few people give importance, and given the times, and that will get worse, it is very necessary to inform people of all the dangers which entails being connected. I would like to comment on all of them here, but it would be too long. Whenever I can I give advice, and that is always always always, doubt at all costs to give information, be it passwords, credit cards or some type of information so lightly. Because remember, the principle that underpins social engineering is that in any system, users are the weak link.
Continuing with the phishing issue, this is the email I received:

As you can see, it is from Amazon, or rather, it seems to be from Amazon.
To anyone who is not very well placed in this line, he will think, oh my God, they will close my account, how? Why? It cannot be! And click on the button.
This could happen, but remembering the first thing I said, always always always doubt at all costs giving information. With this in mind you should start to doubt, “Are there really problems with my account? Amazon has never asked me anything. Is it really Amazon?”
t’s normal, we can have doubts, and this is where I would like to comment on some “tricks” to know if it’s really fake or not.
If in this case we click on the “Update now” link. The following page will open in the browser.

When you open it you say, it is apparently Amazon, with the typical login, same appearance, same image, all the same, but … If we look at the URL we can verify that it is not Amazon.com, no matter how much green lock there is, it is NOT Amazon.
But in addition, with this it isn’t enough, because in this case I have been lucky and the browser shows me the domain part of URL, I mean, the real page, but other browsers may not be like this and show the prepared URL that cybercriminals have created, that just have enough characters to show this prepared part of URL and hide the real part of URL. And when I say enough characters, I mean the necessary characters that only goes into the width, in this case, the mobile.

Scammers are interested in showing the subdomain, and with some luck the real domain is not seen. Many times if the victim sees the word “Amazon” doesn’t give it more importance and fall into the trap.
But there is more, if we return to the email, we can see more information about who sent it to us.

If we click on customer-service@amazon.com which seems to be the email of the person who sent it to us, we will see the real information of the issuer and just below it appears the real email from where it was sent.
These are the main “tricks” to which I referred, very careful with the URL, but above all, special attention to email sender. If we pass this barrier, we will hardly be able to realize it later, we must have our eyes wide open!
Let’s keep going; At this point, and knowing that it is phishing, I have placed a fully invented username and password, and as I expected, the page has advanced and it has shown me the following. Of course, they don’t have the database, they can’t contrast something!
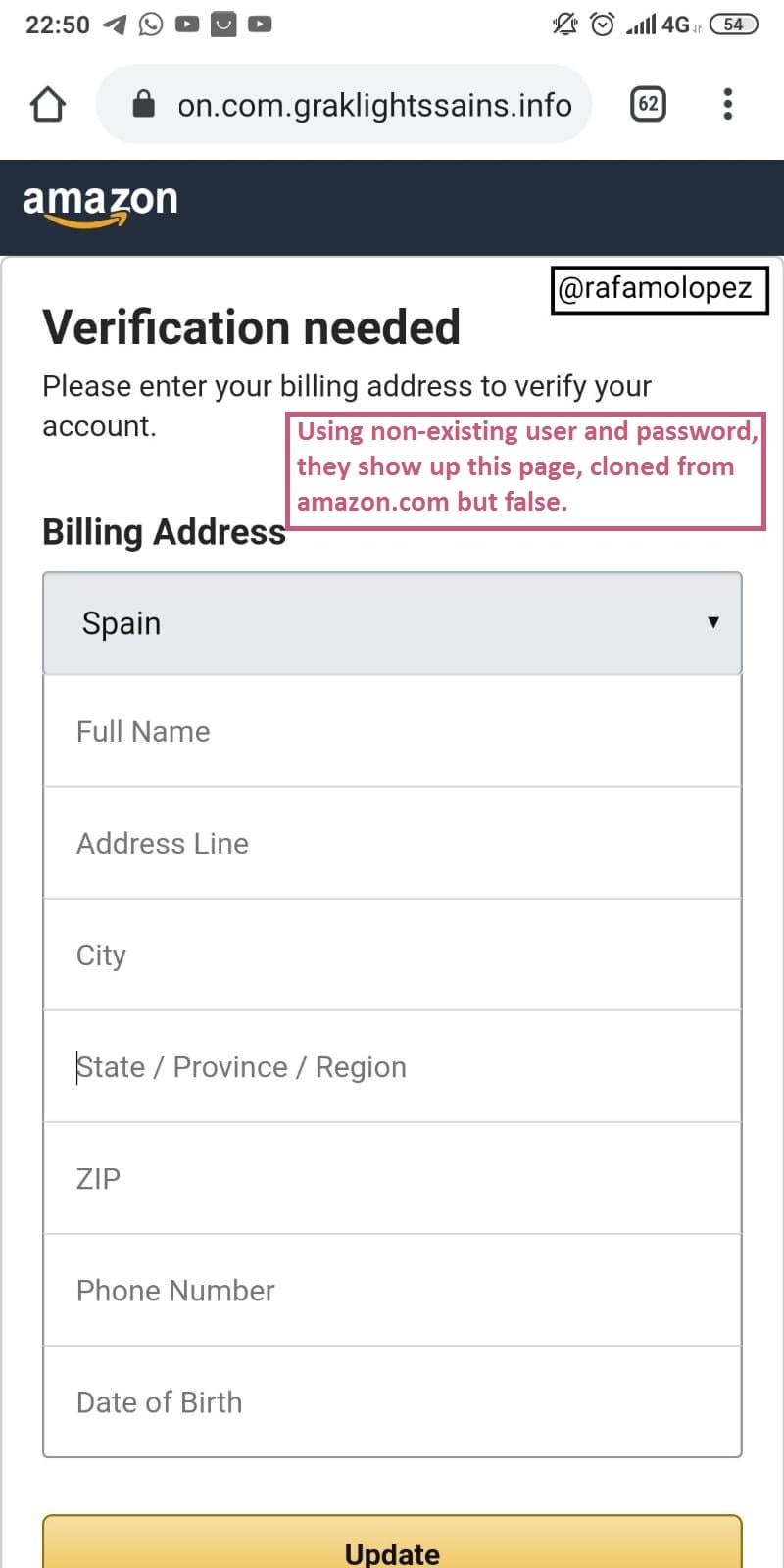
The page looks very real, it looks a lot like Amazon’s styles. Here they ask for any type of information, even the brand of your underwear! So placing a random text, we go to the next page.
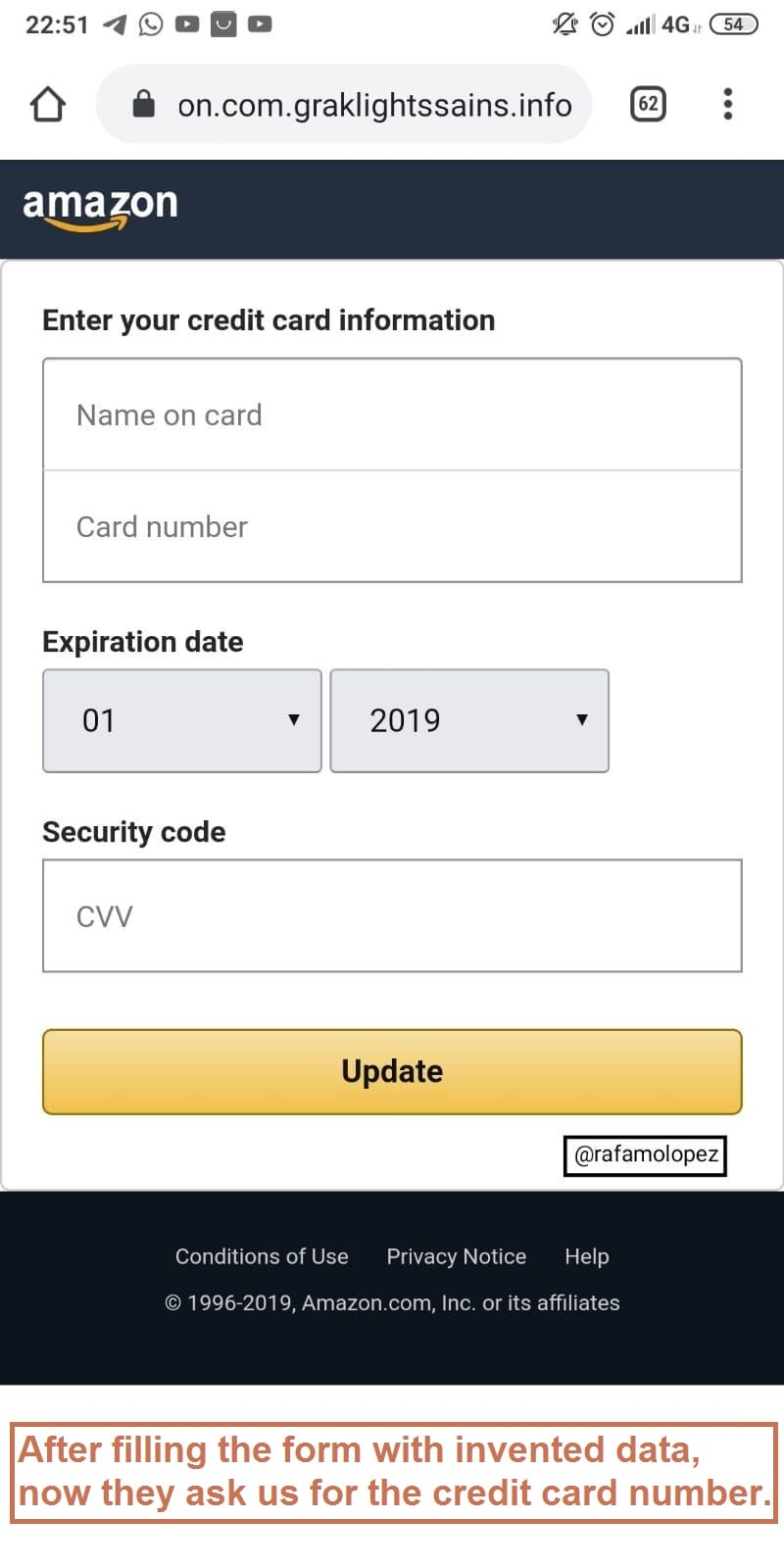
As expected, they will ask for the credit card number. Although at this point, something got my attention, they have a credit card checker! They check the credit card number before you can go to the next page. I had to search an online generator of virtual credit cards to pass the checker. They took it very seriously!

Now they ask us for a front and back credit card photo.
By placing them, it takes us to:
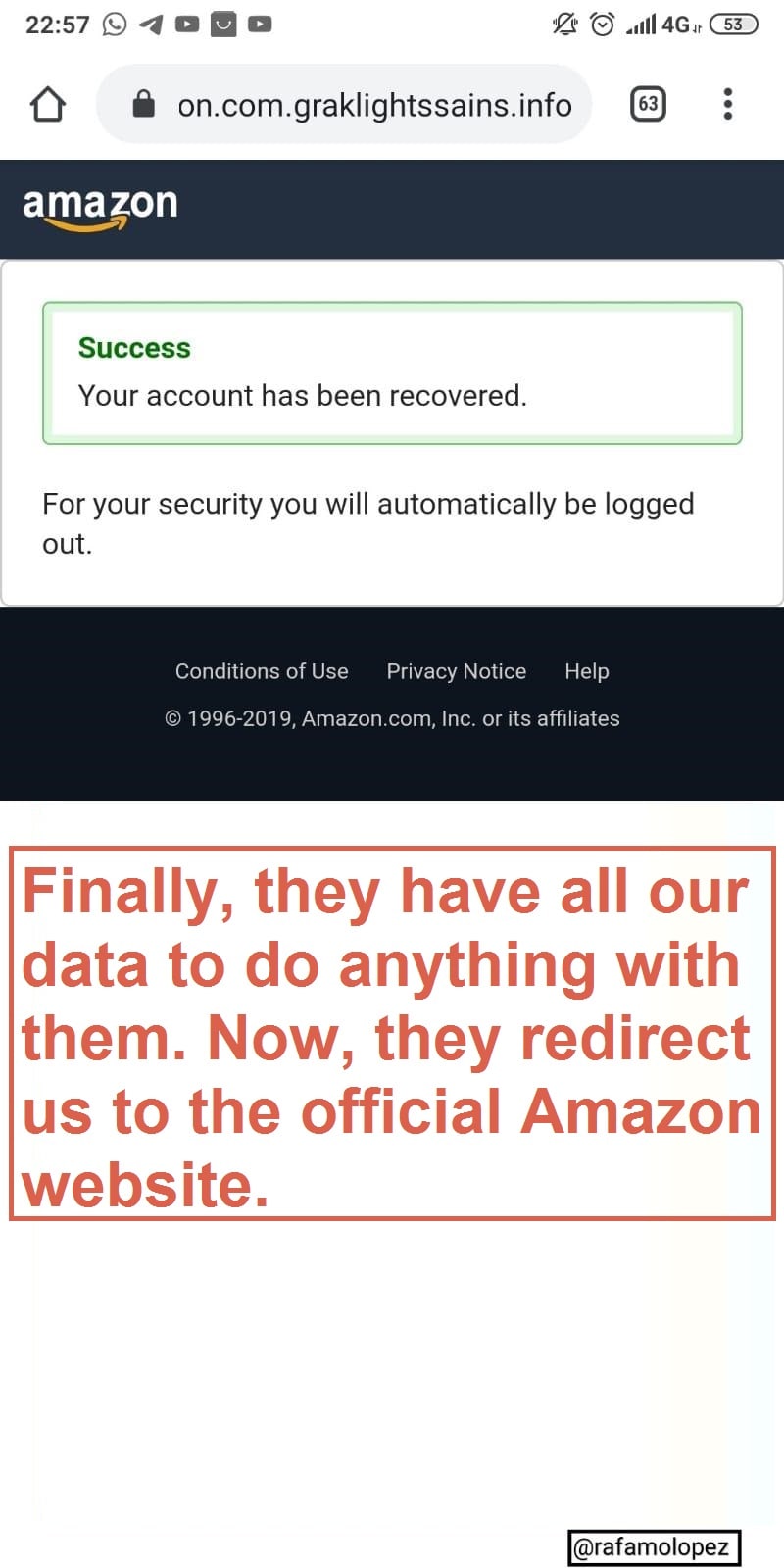
We have verified our account, apparently, everything is OK, and now it will redirect us to the official Amazon webpage, and thus you can enter your username and password, and see that Amazon has not deleted anything.

And here the phishing ends, the victim in a few days will see movements in his credit card, password changes, Amazon orders to other places and someone with bad luck in a few months or years could find some type of complaint of any scam or illegality, for having used cybercriminals their data on illegal pages.
I hope I explained clearly and that you liked it. Remember, always always always, doubt at all costs to give information, be it passwords, credit cards or some kind of information so lightly.
See you in the next post! 😉
Happy Hacking!
Author: Rafael Moreno López.

buy 10 mg prednisone: https://prednisone1st.store/# cost of prednisone tablets
prednisone 4mg tab: http://prednisone1st.store/# 50mg prednisone tablet
medication canadian pharmacy buy drugs from canada
amoxicillin discount: order amoxicillin no prescription amoxicillin 200 mg tablet
propecia without insurance propecia cheap
where can i get generic mobic without insurance: where can i buy cheap mobic without dr prescription – cost of cheap mobic for sale
Actual trends of drug.
generic amoxicillin cost buy amoxicillin online mexico – amoxicillin 500 mg online
Everything about medicine.
buying cheap propecia without prescription cost of generic propecia online
canada drug pharmacy canadian pharmacy 24
medicine erectile dysfunction: drugs for ed – erection pills online
order generic mobic tablets: where to buy cheap mobic without a prescription – can you get cheap mobic price
cheap propecia tablets buying propecia without rx
canada pharmacy online canadian pharmacies that deliver to the us
canadian mail order pharmacy canadian pharmacy
canadian pharmacy checker pharmacy canadian superstore
trustworthy canadian pharmacy: legal canadian pharmacy online – my canadian pharmacy
http://certifiedcanadapharm.store/# canadapharmacyonline
online pharmacy india: cheapest online pharmacy india – india pharmacy
https://mexpharmacy.sbs/# mexican border pharmacies shipping to usa
mexican drugstore online: mexican online pharmacies prescription drugs – best online pharmacies in mexico
http://indiamedicine.world/# indian pharmacies safe
mexico drug stores pharmacies: buying from online mexican pharmacy – pharmacies in mexico that ship to usa
http://certifiedcanadapharm.store/# canadian drugs
medicine in mexico pharmacies: mexican pharmaceuticals online – mexican mail order pharmacies
http://certifiedcanadapharm.store/# canadian drug
http://gabapentin.pro/# gabapentin buy
brand neurontin 100 mg canada: buying neurontin online – neurontin capsules 100mg
https://stromectolonline.pro/# ivermectin cream 5%
zithromax 500 mg lowest price online: zithromax online usa no prescription – zithromax cost australia
http://gabapentin.pro/# neurontin 50mg cost
buy cheap neurontin: neurontin buy from canada – neurontin generic south africa
п»їpaxlovid: buy paxlovid online – paxlovid for sale
https://antibiotic.guru/# cheapest antibiotics
Paxlovid over the counter: paxlovid pharmacy – paxlovid for sale
https://lipitor.pro/# lipitor 4 mg
https://ciprofloxacin.ink/# cipro
canadian pharmacy online maple leaf pharmacy in canada trustworthy canadian pharmacy
https://certifiedcanadapills.pro/# legal to buy prescription drugs from canada
pharmacy wholesalers canada canadian drug pharmacy www canadianonlinepharmacy
buying prescription drugs in mexico online: best online pharmacies in mexico – pharmacies in mexico that ship to usa
indian pharmacy paypal: india pharmacy mail order – indian pharmacies safe
pharmacies in mexico that ship to usa: buying prescription drugs in mexico – mexican border pharmacies shipping to usa
http://edapotheke.store/# versandapotheke
acheter sildenafil 100mg sans ordonnance
buying prescription drugs in mexico: mexican drugstore online – mexican pharmaceuticals online
side effect for zoloft
purple pharmacy mexico price list: buying prescription drugs in mexico online – reputable mexican pharmacies online
купить бетон
indian pharmacies safe: top 10 online pharmacy in india – online pharmacy india
best rated canadian pharmacy: canadian pharmacies compare – canadian pharmacy checker
canadian neighbor pharmacy: buying from canadian pharmacies – prescription drugs canada buy online
antibiotics doxycycline buy doxycycline online how much is doxycycline 100mg
http://azithromycinotc.store/# zithromax 500 mg for sale
Some are medicines that help people when doctors prescribe. doxycycline buy online us: buy doxycycline over the counter – doxycycline buy canada 100mg
All trends of medicament. http://azithromycinotc.store/# buy cheap zithromax online
ed pills cheap ED pills online erectile dysfunction drug
The widest range of international brands under one roof. http://azithromycinotc.store/# zithromax online usa no prescription
A beacon of international trust and reliability. https://azithromycinotc.store/# zithromax azithromycin
I’m always impressed with their efficient system. http://indianpharmacy.life/# buy medicines online in india
Their international collaborations benefit patients immensely. https://canadapharmacy.cheap/# drugs from canada
mexico drug stores pharmacies and mexico pharmacy price list – pharmacies in mexico that ship to usa
http://canadapharmacy24.pro/# canadian pharmacy 365
http://indiapharmacy24.pro/# indian pharmacy
http://indiapharmacy24.pro/# п»їlegitimate online pharmacies india
https://plavix.guru/# Cost of Plavix on Medicare
can you buy cheap mobic without a prescription: buy mobic – how to get cheap mobic prices
ivermectin medication: minocycline for uti – ivermectin goodrx
https://kamagra.icu/# п»їkamagra
https://cialis.foundation/# Tadalafil price
http://cialis.foundation/# Tadalafil Tablet
Buy Tadalafil 10mg Tadalafil price Cialis 20mg price
https://cialis.foundation/# Cialis 20mg price in USA
cialis for sale cheapest cialis Cialis without a doctor prescription
buy cialis pill cheapest cialis Generic Tadalafil 20mg price
https://kamagra.icu/# Kamagra tablets
https://kamagra.icu/# sildenafil oral jelly 100mg kamagra
Cialis without a doctor prescription Generic Cialis price Generic Tadalafil 20mg price
http://kamagra.icu/# Kamagra tablets
Tadalafil Tablet Buy Tadalafil 10mg cialis for sale
купить бетон
консультации юриста бесплатно для всех вопросов о законодательстве|юридическая помощь без оплаты на любые темы
бесплатная юридическая поддержка для частных лиц и организаций по разнообразным вопросам юриспруденции от опытных юристов|Получи бесплатное консультирование от опытных юристов по любым проблемам
Консультации юристов бесплатно: оспорьте незаконные действия соседей
нужна юридическая помощь бесплатно http://www.konsultaciya-yurista-499.ru/.
Бесплатная помощь юриста
сколько стоит адвокат по уголовным делам в москве lawyer-uslugi.ru.
Получите бесплатную юридическую консультацию по телефону способ получить Экономьте лишних трат на юридические услуги с помощью бесплатной консультации
Как защитить собственные права без затрат на юридические услуги?
Свободная юридическая консультация 24/7 под рукой
Куда обратиться бесплатную юридическую помощь?
Узнавайте свои юридические вопросы экономно с бесплатной консультацией
Ищете консультацию? Получите бесплатную юридическую помощь прямо сейчас
Сберегите свои права с бесплатной юридической консультацией
Что делать в сложной юридической ситуации? Получите бесплатную консультацию и решите проблему
Полное пояснение правового вопроса с помощью квалифицированных юристов
Как защитить свою правоту? Получите юридическую консультацию на тему бесплатно
Гонорары юристов не всегда оправданы, узнайте, как получить бесплатную консультацию
Усложнилась юридическая ситуация? Получите бесплатную юридическую поддержку
Советы юридических экспертов вам доступны бесплатно
Как защитить документы без юриста? Получите бесплатную консультацию и сэкономьте
Нужна юридическая вопроса? Получите бесплатную консультацию от Профессионалов
Безопасно получите бесплатную юридическую консультацию онлайн с помощью бесплатной юридической консультации
Нужна комплексная юридическая помощь? Получите бесплатную консультацию
Доступная юридическая консультация по целому ряду вопросов
Не откладывайте – получите бесплатную помощь от лучших юристов
Арбитражный юрист с опытом защиты интересов клиентов
отзыв арбитражный адвокат https://www.advocate-uslugi.ru/.
Качественная консультация по наследству от эксперта
сколько стоит адвокат по наследству http://www.nasledstvennyye-dela-v-moskve.ru/.
https://amoxil.icu/# generic amoxicillin 500mg
can i buy cheap clomid for sale how to buy cheap clomid no prescription – cost of clomid prices
http://amoxil.icu/# amoxicillin 500mg capsule
buying clomid tablets where to get cheap clomid – can i buy clomid without rx
https://amoxil.icu/# amoxicillin 250 mg price in india
can i get generic clomid price: can i purchase generic clomid – cost generic clomid
https://ciprofloxacin.life/# buy generic ciprofloxacin
https://ciprofloxacin.life/# where can i buy cipro online
prednisone prescription for sale: where can i buy prednisone – buy prednisone from canada
prednisone 20mg tab price: purchase prednisone – prednisone online australia
московские юристы консультация бесплатная https://konsultaciya-yurista5.ru.
https://zithromaxbestprice.icu/# zithromax tablets for sale
https://cytotec.icu/# cytotec abortion pill
who should take tamoxifen: tamoxifen breast cancer – tamoxifen endometriosis
buy cytotec online: buy cytotec over the counter – buy cytotec pills
buy doxycycline online 270 tabs: order doxycycline 100mg without prescription – doxycycline hyc
buy 20mg lisinopril: prinivil coupon – over the counter lisinopril
zithromax 500 mg lowest price pharmacy online: zithromax prescription in canada – generic zithromax over the counter
can you buy zithromax over the counter in australia: cheap zithromax pills – generic zithromax medicine
buy cytotec: buy cytotec over the counter – buy cytotec in usa
buy doxycycline without prescription uk: doxycycline 50 mg – doxycycline hyclate
https://cytotec.icu/# Misoprostol 200 mg buy online
mexico drug stores pharmacies: Mexico pharmacy online – mexico pharmacies prescription drugs mexicopharm.com
indian pharmacy paypal India Post sending medicines to USA buy prescription drugs from india indiapharm.llc
best india pharmacy: India pharmacy of the world – buy prescription drugs from india indiapharm.llc
http://mexicopharm.com/# buying from online mexican pharmacy mexicopharm.com
medication from mexico pharmacy Purple Pharmacy online ordering mexican mail order pharmacies mexicopharm.com
Автоюристы – ваша надежда на справедливость в автомобильных спорах
автоюрист оплата по результату http://avtoyurist-moskva1.ru/.
canadian pharmacy no scripts: canada pharmacy online – pharmacy com canada canadapharm.life
buy prescription drugs from india: Online medicine order – indianpharmacy com indiapharm.llc
reputable canadian pharmacy: Canada pharmacy online – canadian pharmacy oxycodone canadapharm.life
reliable canadian pharmacy reviews Canadian pharmacy best prices canadian pharmacy price checker canadapharm.life
best canadian pharmacy online: Canadian pharmacy best prices – buying drugs from canada canadapharm.life
maple leaf pharmacy in canada: Canada pharmacy online – canadian pharmacy ltd canadapharm.life
buy sildenafil 20 mg: sildenafil without a doctor prescription Canada – cheap sildenafil 100
cheap sildenafil citrate Buy generic 100mg Sildenafil online sildenafil prescription cost
tadalafil 20 mg best price: tadalafil online canada – tadalafil 22 mg
ed pills that work: erectile dysfunction drug – best ed pills
buy kamagra online usa cheap kamagra buy kamagra online usa
tadalafil online 10mg: Tadalafil 20mg price in Canada – buy tadalafil over the counter
sildenafil 150 mg: Cheapest Sildenafil online – sildenafil 50 mg mexico
Vardenafil price: Levitra best price – Levitra 20 mg for sale
non prescription ed drugs: erection pills over the counter – what is the best ed pill
http://edpillsdelivery.pro/# erectile dysfunction pills
tadalafil 10mg generic tadalafil without prescription generic tadalafil without prescription
http://tadalafildelivery.pro/# tadalafil generic us
Levitra 20 mg for sale: Buy generic Levitra online – Levitra 10 mg buy online
http://stromectol.guru/# ivermectin pills human
paxlovid buy Buy Paxlovid privately paxlovid price
https://prednisone.auction/# prednisone best prices
Paxlovid over the counter paxlovid pharmacy paxlovid india
how to get cheap clomid without rx: where buy cheap clomid without insurance – get cheap clomid without insurance
https://amoxil.guru/# amoxicillin 500mg without prescription
cheap prednisone online: buy prednisone from canada – prednisone 20mg capsule
https://furosemide.pro/# lasix 100mg
zithromax pill: cheapest azithromycin – zithromax 500mg
get generic propecia without a prescription: Best place to buy propecia – cost of propecia tablets
buy cytotec over the counter Buy Abortion Pills Online cytotec abortion pill
http://finasteride.men/# generic propecia without a prescription
Abortion pills online: buy cytotec online – cytotec buy online usa
cytotec pills buy online: buy cytotec online – п»їcytotec pills online
https://azithromycin.store/# zithromax without prescription
buy zithromax canada: zithromax best price – zithromax 500 mg lowest price online
https://furosemide.pro/# furosemide 40mg
lisinopril pill 5 mg: buy lisinopril online – cost of lisinopril 20 mg
lisinopril tablets: High Blood Pressure – lisinopril 10mg
lisinopril generic drug: over the counter lisinopril – prinivil 5mg tablet
http://misoprostol.shop/# Cytotec 200mcg price
lisinopril 12.5 tablet: over the counter lisinopril – lisinopril 40 mg prices
http://azithromycin.store/# zithromax 500mg
zithromax for sale 500 mg: buy zithromax over the counter – zithromax online usa
buy zithromax online cheap: buy zithromax z-pak online – zithromax azithromycin
lisinopril 5 mg tabs: cheapest lisinopril – price lisinopril 20 mg
http://azithromycin.store/# zithromax online paypal
2 prinivil: over the counter lisinopril – where to buy lisinopril online
http://finasteride.men/# cost generic propecia prices
https://lisinopril.fun/# lisinopril 80
acquistare farmaci senza ricetta: Avanafil farmaco – farmacie online autorizzate elenco
farmacia online migliore: cialis generico consegna 48 ore – farmacie on line spedizione gratuita
https://kamagraitalia.shop/# farmacie online autorizzate elenco
farmacia online: kamagra oral jelly consegna 24 ore – farmacie online autorizzate elenco
https://farmaciaitalia.store/# farmacie online affidabili
acquisto farmaci con ricetta: kamagra oral jelly consegna 24 ore – acquistare farmaci senza ricetta
farmacia online miglior prezzo: avanafil prezzo in farmacia – farmacia online senza ricetta
farmacia online piГ№ conveniente: dove acquistare cialis online sicuro – farmaci senza ricetta elenco
farmacia online piГ№ conveniente: avanafil prezzo in farmacia – farmacie on line spedizione gratuita
http://farmaciaitalia.store/# farmacia online migliore
acquisto farmaci con ricetta: kamagra gel – comprare farmaci online con ricetta
https://tadalafilitalia.pro/# migliori farmacie online 2023
farmacia online miglior prezzo: avanafil prezzo in farmacia – acquisto farmaci con ricetta
https://sildenafilitalia.men/# viagra naturale in farmacia senza ricetta
viagra originale recensioni: viagra prezzo – pillole per erezione immediata
https://farmaciaitalia.store/# farmacia online migliore
farmacia online senza ricetta: avanafil prezzo in farmacia – farmacie online autorizzate elenco
viagra generico sandoz: sildenafil 100mg prezzo – miglior sito dove acquistare viagra
farmacia online kamagra farmacia online
http://avanafilitalia.online/# farmacie online sicure
http://indiapharm.life/# buy prescription drugs from india
pharmacy website india: india pharmacy mail order – online shopping pharmacy india
https://indiapharm.life/# reputable indian pharmacies
canadian discount pharmacy buy prescription drugs from canada cheap global pharmacy canada
pharmacy website india: india pharmacy – indian pharmacy
medication canadian pharmacy: canadian pharmacy cheap – canadian pharmacy online
http://canadapharm.shop/# canadian pharmacy
buy prescription drugs from india: buy prescription drugs from india – Online medicine order
https://canadapharm.shop/# buy prescription drugs from canada cheap
mexican mail order pharmacies: medication from mexico pharmacy – medicine in mexico pharmacies
canadian pharmacy meds: canada pharmacy world – canadian pharmacy in canada
canadian pharmacy online ship to usa: buy drugs from canada – canada pharmacy online legit
mexico drug stores pharmacies: purple pharmacy mexico price list – buying from online mexican pharmacy
mexican border pharmacies shipping to usa mexican rx online buying prescription drugs in mexico
http://indiapharm.life/# indian pharmacy paypal
online pharmacy canada: canadian pharmacy online store – medication canadian pharmacy
http://indiapharm.life/# reputable indian online pharmacy
pharmacies in mexico that ship to usa: mexico drug stores pharmacies – п»їbest mexican online pharmacies
online pharmacy canada: pharmacies in canada that ship to the us – best rated canadian pharmacy
https://canadapharm.shop/# reddit canadian pharmacy
pharmacies in mexico that ship to usa: purple pharmacy mexico price list – reputable mexican pharmacies online
https://mexicanpharm.store/# mexico pharmacies prescription drugs
mexican rx online: mexican pharmaceuticals online – mexican border pharmacies shipping to usa
my canadian pharmacy reviews: canada drugs online reviews – certified canadian international pharmacy
mexico pharmacies prescription drugs mexican online pharmacies prescription drugs mexican pharmaceuticals online
https://indiapharm.life/# indian pharmacy online
best online pharmacies in mexico: mexican border pharmacies shipping to usa – mexican online pharmacies prescription drugs
online canadian pharmacy review: pharmacy rx world canada – legitimate canadian pharmacy online
https://canadapharm.shop/# is canadian pharmacy legit
indian pharmacies safe: online shopping pharmacy india – cheapest online pharmacy india
https://mexicanpharm.store/# medicine in mexico pharmacies
india pharmacy mail order: buy medicines online in india – reputable indian online pharmacy
Online medicine order: best india pharmacy – india pharmacy mail order
http://indiapharm.life/# india online pharmacy
top 10 online pharmacy in india indian pharmacy online pharmacy india
http://nolvadex.pro/# where to get nolvadex
http://clomidpharm.shop/# can i get cheap clomid now
nolvadex 10mg: tamoxifen for breast cancer prevention – nolvadex steroids
https://clomidpharm.shop/# can i buy clomid online
buy cytotec: cytotec pills online – cytotec online
http://clomidpharm.shop/# get generic clomid without dr prescription
generic zithromax 500mg india: zithromax over the counter canada – can i buy zithromax over the counter in canada
https://prednisonepharm.store/# prednisone brand name
buy prednisone online uk: prednisone 20 mg without prescription – prednisone 2.5 mg tab
prednisone 50 mg buy prednisone 20mg online without prescription prednisone without prescription.net
https://clomidpharm.shop/# order generic clomid without insurance
buy misoprostol over the counter: buy cytotec pills – order cytotec online
https://zithromaxpharm.online/# zithromax over the counter uk
cytotec pills online: Abortion pills online – buy cytotec online
https://zithromaxpharm.online/# zithromax z-pak
http://edwithoutdoctorprescription.store/# non prescription ed drugs
https://edwithoutdoctorprescription.store/# viagra without a doctor prescription walmart
order drugs online: canada prescription – overseas pharmacies
http://reputablepharmacies.online/# canadian pharmacy drugstore
legitimate mexican pharmacy online: canadian online pharmacy – online pharmacies canada reviews
http://edpills.bid/# online ed pills
real viagra without a doctor prescription: ed meds online without doctor prescription – prescription drugs
http://edwithoutdoctorprescription.store/# prescription drugs online without doctor
https://edwithoutdoctorprescription.store/# 100mg viagra without a doctor prescription
prescription drugs without doctor approval: legal to buy prescription drugs without prescription – buy prescription drugs online without
buy prescription drugs without doctor: real viagra without a doctor prescription – best ed pills non prescription
http://edpills.bid/# mens ed pills
prescriptions canada: good online mexican pharmacy – canadian pharmacy canada
http://edpills.bid/# new ed drugs
https://reputablepharmacies.online/# canadian pharmacy world reviews
cialis without a doctor’s prescription: viagra without a doctor prescription – prescription without a doctor’s prescription
https://edwithoutdoctorprescription.store/# prescription meds without the prescriptions
buy prescription drugs without doctor: viagra without doctor prescription amazon – 100mg viagra without a doctor prescription
http://canadianpharmacy.pro/# legitimate canadian mail order pharmacy canadianpharmacy.pro
buying prescription drugs in mexico online: Medicines Mexico – best online pharmacies in mexico mexicanpharmacy.win
http://canadianpharmacy.pro/# canadian pharmacy king reviews canadianpharmacy.pro
canadian pharmacy shop
mexican pharmacy Mexico pharmacy mexican border pharmacies shipping to usa mexicanpharmacy.win
https://indianpharmacy.shop/# best online pharmacy india indianpharmacy.shop
legitimate canadian pharmacy online: pharmacy rx world canada – canadian pharmacy scam canadianpharmacy.pro
medication from mexico pharmacy online mexican pharmacy buying prescription drugs in mexico online mexicanpharmacy.win
http://canadianpharmacy.pro/# canadian world pharmacy canadianpharmacy.pro
п»їbest mexican online pharmacies mexico drug stores pharmacies mexican mail order pharmacies mexicanpharmacy.win
http://canadianpharmacy.pro/# canadian pharmacy ratings canadianpharmacy.pro
canadian prescription drug prices
http://canadianpharmacy.pro/# canadian drugs canadianpharmacy.pro
best online pharmacies in mexico Mexico pharmacy mexican online pharmacies prescription drugs mexicanpharmacy.win
http://indianpharmacy.shop/# india pharmacy mail order
cheapest online pharmacy india
http://indianpharmacy.shop/# online pharmacy india
indian pharmacy paypal
https://canadianpharmacy.pro/# certified canadian international pharmacy canadianpharmacy.pro
https://indianpharmacy.shop/# indianpharmacy com indianpharmacy.shop
buy medicines online in india indian pharmacy online pharmacy india indianpharmacy.shop
https://indianpharmacy.shop/# india online pharmacy indianpharmacy.shop
http://canadianpharmacy.pro/# canadian pharmacy ratings canadianpharmacy.pro
Online medicine home delivery
online canadian pharmacy canadian world pharmacy canadian pharmacy 365 canadianpharmacy.pro
http://mexicanpharmacy.win/# mexican border pharmacies shipping to usa mexicanpharmacy.win
ed meds online without doctor prescription
http://mexicanpharmacy.win/# mexican drugstore online mexicanpharmacy.win
top online pharmacy india
https://canadianpharmacy.pro/# buy prescription drugs from canada cheap canadianpharmacy.pro
https://canadianpharmacy.pro/# ordering drugs from canada canadianpharmacy.pro
legal to buy prescription drugs from canada canadapharmacyonline com canadian pharmacy 365 canadianpharmacy.pro
http://mexicanpharmacy.win/# buying prescription drugs in mexico mexicanpharmacy.win
п»їlegitimate online pharmacies india
https://mexicanpharmacy.win/# pharmacies in mexico that ship to usa mexicanpharmacy.win
http://mexicanpharmacy.win/# medication from mexico pharmacy mexicanpharmacy.win
canadian online drugstore Canada Pharmacy global pharmacy canada canadianpharmacy.pro
http://mexicanpharmacy.win/# mexican rx online mexicanpharmacy.win
canadianpharmacymeds com Cheapest drug prices Canada canada drug pharmacy canadianpharmacy.pro
https://mexicanpharmacy.win/# mexican pharmacy mexicanpharmacy.win
best online pharmacy india
http://mexicanpharmacy.win/# best mexican online pharmacies mexicanpharmacy.win
https://mexicanpharmacy.win/# medication from mexico pharmacy mexicanpharmacy.win
pharmacy online canada
top 10 online pharmacy in india indian pharmacy to usa online pharmacy india indianpharmacy.shop
https://mexicanpharmacy.win/# mexican mail order pharmacies mexicanpharmacy.win
india online pharmacy
http://mexicanpharmacy.win/# mexico pharmacy mexicanpharmacy.win
Pharmacie en ligne pas cher Acheter Cialis 20 mg pas cher acheter medicament a l etranger sans ordonnance
http://acheterkamagra.pro/# Pharmacie en ligne France
acheter medicament a l etranger sans ordonnance
Pharmacie en ligne livraison 24h: acheterkamagra.pro – Pharmacie en ligne fiable
http://viagrasansordonnance.pro/# Meilleur Viagra sans ordonnance 24h
Pharmacie en ligne fiable: Pharmacies en ligne certifiees – Pharmacie en ligne sans ordonnance
https://pharmadoc.pro/# Acheter médicaments sans ordonnance sur internet
Acheter Sildenafil 100mg sans ordonnance Acheter du Viagra sans ordonnance Viagra vente libre allemagne
Pharmacie en ligne fiable: kamagra 100mg prix – Pharmacie en ligne livraison rapide
https://pharmadoc.pro/# pharmacie ouverte
Pharmacie en ligne livraison rapide
https://levitrasansordonnance.pro/# pharmacie ouverte 24/24
Prix du Viagra 100mg en France viagrasansordonnance.pro Viagra femme sans ordonnance 24h
acheter mГ©dicaments Г l’Г©tranger: Pharmacie en ligne France – Pharmacie en ligne livraison gratuite
https://cialissansordonnance.shop/# Acheter médicaments sans ordonnance sur internet
Pharmacie en ligne livraison rapide: kamagra livraison 24h – Pharmacie en ligne fiable
http://acheterkamagra.pro/# pharmacie ouverte 24/24
Pharmacie en ligne livraison rapide Medicaments en ligne livres en 24h Pharmacie en ligne sans ordonnance
https://pharmadoc.pro/# Pharmacie en ligne livraison gratuite
acheter mГ©dicaments Г l’Г©tranger levitra generique prix en pharmacie acheter mГ©dicaments Г l’Г©tranger
http://levitrasansordonnance.pro/# Pharmacie en ligne pas cher
Pharmacie en ligne livraison rapide
iv prednisone prednisone 1 tablet prednisone sale
https://amoxicillin.bid/# buy amoxicillin without prescription
ivermectin 10 ml: ivermectin iv – ivermectin 3 mg dose
ivermectin 9mg stromectol 3 mg tablet price stromectol price uk
ivermectin purchase: ivermectin 1mg – stromectol over the counter
https://amoxicillin.bid/# can i buy amoxicillin over the counter in australia
online prednisone 50mg prednisone tablet fast shipping prednisone
zithromax 250mg: zithromax over the counter – where can i buy zithromax in canada
http://clomiphene.icu/# where to buy generic clomid pills
zithromax price canada how to get zithromax online zithromax 250 mg tablet price
http://azithromycin.bid/# zithromax buy online
amoxicillin 1000 mg capsule: can i buy amoxicillin over the counter in australia – how to get amoxicillin
https://amoxicillin.bid/# price of amoxicillin without insurance
amoxicillin cephalexin generic for amoxicillin buying amoxicillin online
https://prednisonetablets.shop/# prednisone prices
azithromycin zithromax: buy zithromax without presc – cheap zithromax pills
http://ivermectin.store/# ivermectin uk coronavirus
buy prednisone online india 1250 mg prednisone prednisone 20mg price in india
generic prednisone tablets: how much is prednisone 10 mg – cortisol prednisone
https://ivermectin.store/# stromectol in canada
prednisone best price: prednisone where can i buy – prednisone nz
non prescription prednisone 20mg prednisone 60 mg price prednisone 50 mg coupon
https://clomiphene.icu/# cost cheap clomid online
https://ivermectin.store/# ivermectin stromectol
over the counter prednisone cream: prednisone 10 mg daily – prednisone 10mg tablet price
mexico pharmacy medicine in mexico pharmacies mexican border pharmacies shipping to usa mexicanpharm.shop
canadian pharmacies compare: Certified Online Pharmacy Canada – best rated canadian pharmacy canadianpharm.store
http://indianpharm.store/# buy medicines online in india indianpharm.store
cheapest online pharmacy india order medicine from india to usa indian pharmacy indianpharm.store
mexican pharmacy: mexico drug stores pharmacies – mexico drug stores pharmacies mexicanpharm.shop
https://canadianpharm.store/# canada cloud pharmacy canadianpharm.store
pet meds without vet prescription canada Canadian International Pharmacy best mail order pharmacy canada canadianpharm.store
best india pharmacy: Indian pharmacy to USA – reputable indian online pharmacy indianpharm.store
http://indianpharm.store/# cheapest online pharmacy india indianpharm.store
buying from online mexican pharmacy: mexican drugstore online – buying prescription drugs in mexico online mexicanpharm.shop
https://canadianpharm.store/# canadian pharmacy india canadianpharm.store
mexican drugstore online: mexican rx online – pharmacies in mexico that ship to usa mexicanpharm.shop
http://mexicanpharm.shop/# pharmacies in mexico that ship to usa mexicanpharm.shop
best canadian pharmacy online: online canadian pharmacy – best canadian online pharmacy reviews canadianpharm.store
http://indianpharm.store/# reputable indian pharmacies indianpharm.store
77 canadian pharmacy Canadian Pharmacy canadian pharmacies canadianpharm.store
maple leaf pharmacy in canada: Canadian International Pharmacy – canadian discount pharmacy canadianpharm.store
canadian drug stores: Canada Pharmacy online – precription drugs from canada canadianpharm.store
https://mexicanpharm.shop/# mexican border pharmacies shipping to usa mexicanpharm.shop
canadian pharmacy near me Canada Pharmacy online canadian pharmacy online canadianpharm.store
online pharmacy india: Indian pharmacy to USA – online shopping pharmacy india indianpharm.store
https://canadianpharm.store/# best rated canadian pharmacy canadianpharm.store
https://indianpharm.store/# indian pharmacy indianpharm.store
canadian drug prices: canadianpharmacy com – legit canadian pharmacy online canadianpharm.store
best rated canadian pharmacy Certified Online Pharmacy Canada onlinecanadianpharmacy 24 canadianpharm.store
http://canadianpharm.store/# canadian pharmacy in canada canadianpharm.store
It’s very unreliable, engages in deception scam site
indian pharmacies safe india online pharmacy buy prescription drugs from india
Настоящий официальный канал 1Win зеркало
https://certifiedpharmacymexico.pro/# best mexican online pharmacies
india pharmacy mail order: top 10 pharmacies in india – best online pharmacy india
mexico drug stores pharmacies purple pharmacy mexico price list pharmacies in mexico that ship to usa
herbal ed treatment: medication for ed dysfunction – men’s ed pills
https://canadianinternationalpharmacy.pro/# canada pharmacy 24h
Рекомендую официальный телеграм канал на 1Win вход
purple pharmacy mexico price list medication from mexico pharmacy mexico pharmacies prescription drugs
http://medicinefromindia.store/# indianpharmacy com
impotence pills buy ed pills ed pills gnc
https://canadianinternationalpharmacy.pro/# legal to buy prescription drugs from canada
medication from mexico pharmacy mexican drugstore online mexican border pharmacies shipping to usa
http://medicinefromindia.store/# online shopping pharmacy india
canadian family pharmacy canada rx pharmacy best canadian online pharmacy reviews
http://canadianinternationalpharmacy.pro/# certified canadian international pharmacy
reputable indian pharmacies indian pharmacy paypal mail order pharmacy india
http://medicinefromindia.store/# Online medicine order
rate canadian pharmacies canadian pharmacy review pharmacy canadian superstore
http://certifiedpharmacymexico.pro/# mexican pharmacy
http://edpill.cheap/# non prescription ed drugs
http://edpill.cheap/# compare ed drugs
http://edpill.cheap/# best erectile dysfunction pills
new treatments for ed pills erectile dysfunction best over the counter ed pills
https://edpill.cheap/# ed remedies
reputable indian online pharmacy mail order pharmacy india indianpharmacy com
https://medicinefromindia.store/# cheapest online pharmacy india
world pharmacy india top 10 pharmacies in india world pharmacy india
https://medicinefromindia.store/# reputable indian pharmacies
http://edwithoutdoctorprescription.pro/# buy prescription drugs without doctor
best mail order pharmacy canada canadian drug pharmacy canadianpharmacymeds com
http://edpill.cheap/# cheap ed drugs
canadian pharmacy king online canadian pharmacy review best canadian online pharmacy
https://canadianinternationalpharmacy.pro/# cross border pharmacy canada
http://medicinefromindia.store/# indian pharmacy paypal
best male ed pills erectile dysfunction medicines otc ed pills
https://edpill.cheap/# herbal ed treatment
canadian pharmacy king safe canadian pharmacy safe online pharmacies in canada
http://canadianinternationalpharmacy.pro/# global pharmacy canada
pharmacies in mexico that ship to usa purple pharmacy mexico price list mexican online pharmacies prescription drugs
mexico drug stores pharmacies purple pharmacy mexico price list buying from online mexican pharmacy
purple pharmacy mexico price list buying prescription drugs in mexico mexico drug stores pharmacies
reputable mexican pharmacies online buying from online mexican pharmacy mexican mail order pharmacies
purple pharmacy mexico price list purple pharmacy mexico price list mexican mail order pharmacies
pharmacies in mexico that ship to usa reputable mexican pharmacies online mexico drug stores pharmacies
mexican pharmaceuticals online mexican border pharmacies shipping to usa medication from mexico pharmacy
mexico pharmacy pharmacies in mexico that ship to usa medicine in mexico pharmacies
mexico pharmacies prescription drugs medicine in mexico pharmacies reputable mexican pharmacies online
best online pharmacies in mexico buying prescription drugs in mexico online mexican mail order pharmacies
mexican mail order pharmacies buying prescription drugs in mexico online п»їbest mexican online pharmacies
purple pharmacy mexico price list mexican online pharmacies prescription drugs pharmacies in mexico that ship to usa
mexico pharmacies prescription drugs buying from online mexican pharmacy mexico drug stores pharmacies
mexico drug stores pharmacies mexican drugstore online mexican pharmaceuticals online
mexican drugstore online mexico drug stores pharmacies mexican mail order pharmacies
reputable mexican pharmacies online mexican drugstore online pharmacies in mexico that ship to usa
mexico pharmacies prescription drugs mexico drug stores pharmacies purple pharmacy mexico price list
mexico drug stores pharmacies mexican drugstore online purple pharmacy mexico price list
medicine in mexico pharmacies mexico drug stores pharmacies medication from mexico pharmacy
buying prescription drugs in mexico online purple pharmacy mexico price list mexico drug stores pharmacies
mexican drugstore online best mexican online pharmacies reputable mexican pharmacies online
pharmacies in mexico that ship to usa mexico pharmacies prescription drugs mexico pharmacies prescription drugs
mexican pharmacy medication from mexico pharmacy pharmacies in mexico that ship to usa
mexico pharmacies prescription drugs mexican drugstore online mexico pharmacy
mexico pharmacies prescription drugs mexican rx online reputable mexican pharmacies online
mexican online pharmacies prescription drugs buying prescription drugs in mexico best online pharmacies in mexico
medicine in mexico pharmacies mexican pharmaceuticals online mexican pharmacy
mexico drug stores pharmacies best mexican online pharmacies medication from mexico pharmacy
https://mexicanph.com/# mexican border pharmacies shipping to usa
mexico drug stores pharmacies
best mexican online pharmacies mexican rx online mexican drugstore online
best online pharmacies in mexico pharmacies in mexico that ship to usa mexican rx online
mexico pharmacy mexican mail order pharmacies mexican pharmacy
best online pharmacies in mexico mexico pharmacy buying prescription drugs in mexico
mexican border pharmacies shipping to usa mexican border pharmacies shipping to usa mexican rx online
medicine in mexico pharmacies reputable mexican pharmacies online best online pharmacies in mexico
http://mexicanph.shop/# buying prescription drugs in mexico online
pharmacies in mexico that ship to usa
medicine in mexico pharmacies mexican drugstore online buying prescription drugs in mexico online
best online pharmacies in mexico purple pharmacy mexico price list mexican pharmacy
buying from online mexican pharmacy mexican drugstore online mexican online pharmacies prescription drugs
mexican online pharmacies prescription drugs mexican drugstore online mexican online pharmacies prescription drugs
п»їbest mexican online pharmacies mexican mail order pharmacies mexican pharmacy
mexican rx online mexico pharmacies prescription drugs mexico pharmacies prescription drugs
reputable mexican pharmacies online mexican pharmacy mexican drugstore online
mexico drug stores pharmacies mexico drug stores pharmacies reputable mexican pharmacies online
reputable mexican pharmacies online mexican drugstore online mexican border pharmacies shipping to usa
mexican rx online buying prescription drugs in mexico online mexico drug stores pharmacies
best online pharmacies in mexico best online pharmacies in mexico mexican pharmaceuticals online
mexican border pharmacies shipping to usa mexican rx online mexico pharmacies prescription drugs
mexico pharmacies prescription drugs mexican drugstore online pharmacies in mexico that ship to usa
mexican mail order pharmacies mexican pharmaceuticals online mexican rx online
http://lisinopril.top/# lisinopril 12.5 mg
ivermectin 3mg: ivermectin 3mg – ivermectin 6
https://stromectol.fun/# generic ivermectin
http://stromectol.fun/# stromectol cvs
amoxicillin medicine over the counter: amoxicillin buy canada – amoxicillin without prescription
http://furosemide.guru/# furosemide 40mg
amoxicillin online pharmacy: where can i buy amoxicillin online – amoxicillin 875 mg tablet
http://amoxil.cheap/# order amoxicillin 500mg
https://amoxil.cheap/# where to buy amoxicillin over the counter
https://lisinopril.top/# lisinopril 10mg online
stromectol price: stromectol 3 mg – ivermectin tablets uk
https://furosemide.guru/# lasix furosemide
can i order lisinopril online: prinivil drug cost – lisinopril 40 mg canada
http://stromectol.fun/# п»їwhere to buy stromectol online
lasix 20 mg: Over The Counter Lasix – lasix online
http://amoxil.cheap/# amoxicillin azithromycin
amoxicillin order online no prescription: where can i get amoxicillin – amoxicillin 500mg price
http://amoxil.cheap/# prescription for amoxicillin
prednisone brand name us: buy prednisone nz – apo prednisone
http://lisinopril.top/# zestril 5 mg prices
lasix online: lasix furosemide – lasix for sale
http://furosemide.guru/# lasix dosage
lasix 100mg: Buy Lasix No Prescription – lasix 20 mg
http://buyprednisone.store/# can i buy prednisone online without a prescription
can you buy amoxicillin over the counter in canada: amoxicillin 30 capsules price – amoxicillin 500mg no prescription
https://stromectol.fun/# ivermectin 500ml
average cost of prednisone 20 mg: 100 mg prednisone daily – order prednisone 10mg
https://furosemide.guru/# lasix tablet
https://furosemide.guru/# lasix furosemide 40 mg
https://amoxil.cheap/# order amoxicillin online uk
https://furosemide.guru/# generic lasix
lasix tablet: Buy Lasix – lasix
prednisone price: prednisone 5 50mg tablet price – 20mg prednisone
https://buyprednisone.store/# prednisone 5 mg brand name
https://stromectol.fun/# ivermectin 400 mg brands
ivermectin 2mg: stromectol 3 mg dosage – ivermectin 8 mg
https://lisinopril.top/# zestoretic 25
furosemida: Buy Lasix No Prescription – lasix for sale
http://lisinopril.top/# cost for generic lisinopril
http://amoxil.cheap/# amoxicillin 500
http://amoxil.cheap/# cost of amoxicillin prescription
prednisone 20 mg generic: prednisone 2.5 mg tab – prednisone 5mg daily
https://lisinopril.top/# buy lisinopril online canada
ivermectin 1%: ivermectin 3mg tablets – ivermectin lotion for lice
https://furosemide.guru/# lasix 100 mg tablet
https://lisinopril.top/# zestril lisinopril
prednisone 300mg: prednisone coupon – prednisone tabs 20 mg
http://stromectol.fun/# stromectol cream
http://furosemide.guru/# lasix 100mg
prednisone pills cost: 5 prednisone in mexico – order prednisone on line
amoxicillin 500mg buy online canada: order amoxicillin online uk – amoxicillin 500 mg cost
https://lisinopril.top/# lisinopril 419
http://buyprednisone.store/# where can i buy prednisone online without a prescription
lasix online: lasix – lasix dosage
Your insights into the tactics used by cybercriminals to deceive users and gain unauthorized access to sensitive information were incredibly valuable.
Online medicine home delivery reputable indian online pharmacy reputable indian online pharmacy
http://indianph.xyz/# india online pharmacy
best online pharmacy india
http://indianph.com/# best india pharmacy
http://indianph.com/# best india pharmacy
mail order pharmacy india
https://indianph.xyz/# top online pharmacy india
indian pharmacy paypal
http://indianph.xyz/# best online pharmacy india
reputable indian pharmacies
https://indianph.xyz/# legitimate online pharmacies india
best online pharmacy india
http://indianph.com/# indianpharmacy com
pharmacy website india
https://indianph.xyz/# buy medicines online in india
buy prescription drugs from india
how to buy doxycycline online: buy doxycycline online 270 tabs – doxycycline 100mg capsules
http://cytotec24.shop/# buy cytotec online
https://nolvadex.guru/# low dose tamoxifen
buy cytotec pills: order cytotec online – cytotec pills buy online
https://cytotec24.com/# buy cytotec pills online cheap
doxycycline generic: buy doxycycline without prescription – order doxycycline
http://diflucan.pro/# diflucan cost canada
https://diflucan.pro/# diflucan 150 tab
buy ciprofloxacin over the counter: buy cipro – ciprofloxacin generic
http://diflucan.pro/# how much is a diflucan pill
ciprofloxacin order online: cipro online no prescription in the usa – cipro pharmacy
diflucan generic cost: diflucan 150 mg canada – diflucan 200
sweeti fox: Sweetie Fox filmleri – sweety fox
lana rhodes: lana rhodes – lana rhoades
lana rhoades: lana rhoades filmleri – lana rhoades modeli
Sweetie Fox filmleri: Sweetie Fox video – Sweetie Fox modeli
Angela White: Angela White izle – Angela White izle
eva elfie izle: eva elfie – eva elfie izle
?????? ????: abella danger izle – Abella Danger
http://abelladanger.online/# abella danger izle
eva elfie izle: eva elfie modeli – eva elfie
https://evaelfie.pro/# eva elfie
http://lanarhoades.fun/# lana rhoades
swetie fox: Sweetie Fox – Sweetie Fox
http://angelawhite.pro/# Angela White
lana rhoades filmleri: lana rhoades – lana rhoades video
http://abelladanger.online/# abella danger video
Angela White izle: ?????? ???? – Angela White
http://lanarhoades.fun/# lana rhoades filmleri
http://angelawhite.pro/# Angela White
Sweetie Fox modeli: Sweetie Fox video – sweeti fox
Sweetie Fox izle: Sweetie Fox filmleri – Sweetie Fox izle
http://sweetiefox.online/# sweeti fox
https://miamalkova.life/# mia malkova videos
lana rhoades unleashed: lana rhoades full video – lana rhoades unleashed
https://miamalkova.life/# mia malkova new video
http://sweetiefox.pro/# sweetie fox cosplay
http://evaelfie.site/# eva elfie hd
sweetie fox full video: sweetie fox – sweetie fox full
http://evaelfie.site/# eva elfie hd
fox sweetie: fox sweetie – sweetie fox cosplay
https://lanarhoades.pro/# lana rhoades solo
fox sweetie: fox sweetie – fox sweetie
mia malkova new video: mia malkova only fans – mia malkova latest
https://lanarhoades.pro/# lana rhoades boyfriend
https://sweetiefox.pro/# sweetie fox video
lana rhoades videos: lana rhoades pics – lana rhoades unleashed
https://lanarhoades.pro/# lana rhoades full video
sweetie fox new: sweetie fox full video – sweetie fox new
eva elfie videos: eva elfie hot – eva elfie new video
https://lanarhoades.pro/# lana rhoades pics
https://sweetiefox.pro/# sweetie fox video
lana rhoades solo: lana rhoades pics – lana rhoades videos
mia malkova videos: mia malkova girl – mia malkova movie
https://sweetiefox.pro/# sweetie fox video
https://sweetiefox.pro/# sweetie fox new
http://jogodeaposta.fun/# aplicativo de aposta
aviator oyna slot: aviator sinyal hilesi – aviator hilesi
https://aviatorghana.pro/# aviator bet
aviator bet: aviator ghana – aviator sportybet ghana
aviator game: aviator betano – jogar aviator Brasil
http://aviatormalawi.online/# aviator betting game
aviator sportybet ghana: aviator game bet – aviator ghana
http://aviatorjogar.online/# aviator jogar
pin-up casino entrar: pin up aviator – pin-up cassino
https://jogodeaposta.fun/# aviator jogo de aposta
aviator oyna: aviator oyunu – aviator oyunu
aviator login: aviator game – aviator game online
aviator bahis: aviator oyna – aviator bahis
estrela bet aviator: aviator jogar – aviator jogo
aviator: aviator betting game – aviator betting game
zithromax for sale us: zithromax with alcohol buy cheap generic zithromax
aviator jogar: aviator jogo – jogar aviator online
pin up bet: cassino pin up – pin up bet
can you buy zithromax over the counter – https://azithromycin.pro/zithromax-non-prescription.html buy zithromax online fast shipping
zithromax 250 price: zithromax warnings zithromax generic price
pin up bet: pin-up casino entrar – pin-up
zithromax 500mg price: zithromax generic cost – purchase zithromax z-pak
mexican drugstore online: Mexico pharmacy online – mexican border pharmacies shipping to usa mexicanpharm.shop
purple pharmacy mexico price list: Mexico pharmacy price list – mexican border pharmacies shipping to usa mexicanpharm.shop
https://indianpharm24.com/# indian pharmacy online indianpharm.store
https://indianpharm24.com/# world pharmacy india indianpharm.store
https://mexicanpharm24.shop/# purple pharmacy mexico price list mexicanpharm.shop
world pharmacy india: Generic Medicine India to USA – india pharmacy indianpharm.store
http://mexicanpharm24.com/# best mexican online pharmacies mexicanpharm.shop
https://indianpharm24.shop/# indianpharmacy com indianpharm.store
http://mexicanpharm24.shop/# buying prescription drugs in mexico mexicanpharm.shop
mexico pharmacy: order online from a Mexican pharmacy – mexican online pharmacies prescription drugs mexicanpharm.shop
https://indianpharm24.shop/# online shopping pharmacy india indianpharm.store
http://mexicanpharm24.com/# pharmacies in mexico that ship to usa mexicanpharm.shop
http://canadianpharmlk.com/# canadian 24 hour pharmacy canadianpharm.store
http://indianpharm24.com/# buy medicines online in india indianpharm.store
https://amoxilst.pro/# buy amoxicillin canada
http://clomidst.pro/# can i order generic clomid tablets
https://prednisonest.pro/# no prescription online prednisone
http://amoxilst.pro/# order amoxicillin 500mg
https://prednisonest.pro/# prednisone pills cost
https://prednisonest.pro/# prednisone pharmacy prices
http://edpills.guru/# ed online pharmacy
https://edpills.guru/# order ed meds online
http://edpills.guru/# ed meds on line
http://pharmnoprescription.pro/# no prescription online pharmacy
http://pharmnoprescription.pro/# online pharmacy no prescription needed
https://pharmnoprescription.pro/# online pharmacy canada no prescription
Discover the pinnacle of companionship with our elite Allahabad Call Girls. We offer unparalleled satisfaction and indulgence through our carefully curated selection of companions. With a commitment to excellence and discretion, we guarantee unforgettable experiences for those seeking the best in companionship and pleasure
Experience the epitome of companionship with our prestigious MG Road Escorts We provide unmatched satisfaction and luxury with our handpicked selection of companions. Committed to excellence and discretion, we assure unforgettable experiences for those seeking the ultimate in companionship and pleasure
http://canadianpharm.guru/# pharmacies in canada that ship to the us
https://pharmacynoprescription.pro/# buying prescription drugs online without a prescription
https://pharmacynoprescription.pro/# online pharmacy reviews no prescription
https://indianpharm.shop/# online shopping pharmacy india
http://pharmacynoprescription.pro/# buy prescription drugs without a prescription
http://canadianpharm.guru/# canadian pharmacy checker
https://mexicanpharm.online/# mexican pharmaceuticals online
https://canadianpharm.guru/# canadian pharmacy 365
https://pharmacynoprescription.pro/# canadian prescription prices
https://pharmacynoprescription.pro/# online pharmacy with prescription
http://indianpharm.shop/# world pharmacy india
https://pharmacynoprescription.pro/# overseas online pharmacy-no prescription
https://indianpharm.shop/# indian pharmacies safe
http://pharmacynoprescription.pro/# canadian prescription drugstore review
aviator oyunu 20 tl: aviator bahis – aviator oyunu 50 tl
pin-up casino giris: pin up giris – pin-up giris
pragmatic play gates of olympus: gates of olympus slot – gates of olympus demo turkce oyna
gates of olympus taktik: gates of olympus oyna demo – gates of olympus demo turkce
aviator oyna: aviator hile – aviator oyna 20 tl
gates of olympus 1000 demo: gates of olympus nas?l para kazanilir – gates of olympus max win
sweet bonanza bahis: sweet bonanza oyna – sweet bonanza 90 tl
guvenilir slot siteleri: en iyi slot siteleri 2024 – en cok kazandiran slot siteleri
casino slot siteleri: oyun siteleri slot – yeni slot siteleri
aviator oyunu 10 tl: aviator hilesi ucretsiz – aviator hile
http://gatesofolympus.auction/# gates of olympus demo
buy prescription drugs from india: Generic Medicine India to USA – indian pharmacy paypal
canadian pharmacy meds: Prescription Drugs from Canada – canadian valley pharmacy
legitimate canadian pharmacies: pills now even cheaper – canadian world pharmacy
canadian pharmacy meds review: Prescription Drugs from Canada – canadian online drugs
cheap canadian pharmacy online: Licensed Canadian Pharmacy – canadian pharmacy service
http://kamagraiq.com/# super kamagra
https://tadalafiliq.shop/# Buy Tadalafil 20mg
http://tadalafiliq.shop/# Cialis without a doctor prescription
https://tadalafiliq.com/# buy cialis pill
https://tadalafiliq.com/# Generic Cialis price
http://sildenafiliq.com/# Generic Viagra online
http://mexicanpharmgrx.com/# buying prescription drugs in mexico
https://canadianpharmgrx.xyz/# canada pharmacy 24h
http://mexicanpharmgrx.shop/# mexican mail order pharmacies
http://indianpharmgrx.com/# top 10 online pharmacy in india
https://canadianpharmgrx.com/# best mail order pharmacy canada
http://canadianpharmgrx.xyz/# best canadian pharmacy
http://mexicanpharmgrx.shop/# reputable mexican pharmacies online
doxy 200: doxycycline hyclate 100 mg cap – doxycycline medication
tamoxifen and weight loss: tamoxifen cancer – tamoxifen side effects forum
cytotec online: cytotec buy online usa – Abortion pills online
Abortion pills online: Abortion pills online – Misoprostol 200 mg buy online
doxycycline 100mg online: doxycycline monohydrate – order doxycycline 100mg without prescription
buy doxycycline online uk: doxycycline prices – 200 mg doxycycline
fluconazole diflucan: price of diflucan in south africa – how much is diflucan over the counter
azithromycin amoxicillin: where can i buy amoxicillin over the counter uk – antibiotic amoxicillin
get generic clomid tablets: can you buy clomid – where can i get clomid now
where to get clomid prices: how to get cheap clomid pills – how to buy clomid without prescription
zithromax prescription in canada: where to buy zithromax in canada – azithromycin zithromax
200 mg prednisone daily: 1 mg prednisone daily – buying prednisone mexico
amoxicillin 500mg no prescription: how to buy amoxycillin – purchase amoxicillin online
how can i get generic clomid: cost generic clomid without a prescription – can you get cheap clomid online
http://onlinepharmacyworld.shop/# canadian pharmacy no prescription needed
https://edpill.top/# buy ed pills
https://edpill.top/# ed medicine online
https://medicationnoprescription.pro/# meds no prescription
https://onlinepharmacyworld.shop/# prescription drugs from canada
http://onlinepharmacyworld.shop/# cheapest pharmacy to fill prescriptions without insurance
casino tr?c tuy?n vi?t nam: dánh bài tr?c tuy?n – game c? b?c online uy tín
Great job! Your attention to detail really shines through in this work.
stellar data recovery activation key
https://health-lists.com/story17912359/pin-up-um-dos-maiores-casinos-online-internacionais
Thanks for sharing your thoughts. I really appreciate your efforts and I am waiting for your further write ups thank you once again.
mystroycenter.ru/page/14В
moysamogon.ru/comment-page-30/В
fabnews.ru/forum/showthread.php?p=76998В
fat-girls.ru/page/10В
azat.on.kg/blogs/451/%D0%A1%D0%BA%D0%BE%D0%BB%D1%8C%D0%BA%D0%BE-%D1%81%D1%82%D0%BE%D0%B8%D1%82-%D1%81%D0%B5%D0%B9%D1%87%D0%B0%D1%81-%D0%BA%D0%B0%D1%87%D0%B5%D1%81%D1%82%D0%B2%D0%B5%D0%BD%D0%BD%D1%8B%D0%B9-%D0%B4%D0%B8%D0%BF%D0%BB%D0%BE%D0%BCВ
сервисный центр по ремонту айфонов
отремонтировать телефон
Профессиональный сервисный центр по ремонту ноутбуков, макбуков и другой компьютерной техники.
Мы предлагаем:ремонт ноутбуков apple
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту квадрокоптеров и радиоуправляемых дронов.
Мы предлагаем:ремонт квадрокоптеров
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту ноутбуков, imac и другой компьютерной техники.
Мы предлагаем:сервис по ремонту imac
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту ноутбуков и компьютеров.дронов.
Мы предлагаем:ремонт ноутбуков москва центр
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
ремонт айфонов на дому в москве
Профессиональный сервисный центр по ремонту планетов в том числе Apple iPad.
Мы предлагаем: ipad ремонт
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту ноутбуков и компьютеров.дронов.
Мы предлагаем:ноутбук ремонт сервисный
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем:ремонт крупногабаритной техники в петрбурге
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту радиоуправляемых устройства – квадрокоптеры, дроны, беспилостники в том числе Apple iPad.
Мы предлагаем: сервисный центр квадрокоптеров
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Если вы искали где отремонтировать сломаную технику, обратите внимание – профи спб
Если вы искали где отремонтировать сломаную технику, обратите внимание – ремонт бытовой техники в екб
Если вы искали где отремонтировать сломаную технику, обратите внимание – профи москва
Если вы искали где отремонтировать сломаную технику, обратите внимание – профи услуги
Профессиональный сервисный центр по ремонту Apple iPhone в Москве.
Мы предлагаем: ремонт айфона в москве недорого
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
ремонт смартфона
сколько стоит ремонт телевизора
Профессиональный сервисный центр по ремонту источников бесперебойного питания.
Мы предлагаем: ремонт бесперебойников
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Если вы искали где отремонтировать сломаную технику, обратите внимание – техпрофи
Если вы искали где отремонтировать сломаную технику, обратите внимание – техпрофи
Профессиональный сервисный центр по ремонту варочных панелей и индукционных плит.
Мы предлагаем: ремонт электрических варочных панелей на дому москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем:сервисные центры по ремонту техники в екб
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
хороший ремонт фотоаппаратов
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту планшетов в Москве.
Мы предлагаем: стоимость замены экрана на планшете
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту видео техники а именно видеокамер.
Мы предлагаем: ремонт видеокамер
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту стиральных машин с выездом на дом по Москве.
Мы предлагаем: мастерские по ремонту стиральных машин в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники казань
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Если вы искали где отремонтировать сломаную технику, обратите внимание – ремонт бытовой техники
Профессиональный сервисный центр по ремонту игровых консолей Sony Playstation, Xbox, PSP Vita с выездом на дом по Москве.
Мы предлагаем: цены на ремонт игровых консолей
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту компьютерных видеокарт по Москве.
Мы предлагаем: ремонт видеокарт nvidia
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту компьютероной техники в Москве.
Мы предлагаем: центральная часть компьютера
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Недавно нашёл отличный интернет-магазин, где можно приобрести раковины и ванны для ванной комнаты. Они предлагают огромный выбор сантехники и аксессуаров, подходящих под любой интерьер и бюджет. Ассортимент действительно впечатляет: различные модели раковин (накладные, встроенные, подвесные) и ванн (акриловые, чугунные, гидромассажные).
Особенно если вы ищете: раковина купить, что мне было очень нужно. Цены адекватные, качество товаров на высоте. Плюс, они предлагают профессиональные консультации, быструю доставку и услуги по установке. В общем, если кто-то ищет качественную сантехнику по хорошим ценам, рекомендую обратить внимание на этот магазин.
Профессиональный сервисный центр по ремонту компьютерных блоков питания в Москве.
Мы предлагаем: ремонт блоков питания москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Недавно разбил экран своего телефона и обратился в этот сервисный центр. Ребята быстро и качественно починили устройство, теперь работает как новый. Очень рекомендую обратиться к ним за помощью. Вот ссылка на их сайт: ремонт сотовых телефонов айфонов.
ремонт бытовой техники в самаре
<a href=”https://remont-kondicionerov-wik.ru”>ремонт кондиционеров москва</a>
Профессиональный сервисный центр по ремонту компьютероной техники в Москве.
Мы предлагаем: чинить компьютер
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту камер видео наблюдения по Москве.
Мы предлагаем: ремонт систем видеонаблюдения
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт бытовой техники в нижнем новгороде
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры в перми
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту кнаручных часов от советских до швейцарских в Москве.
Мы предлагаем: ремонт наручных часов
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Если вы искали где отремонтировать сломаную технику, обратите внимание – тех профи
Профессиональный сервисный центр по ремонту парогенераторов в Москве.
Мы предлагаем: мастерские по ремонту парогенераторов
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Если вы искали где отремонтировать сломаную технику, обратите внимание – ремонт техники в волгограде
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт бытовой техники в красноярске
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Если вы искали где отремонтировать сломаную технику, обратите внимание – ремонт бытовой техники
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем:сервис центры бытовой техники ростов на дону
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
профессиональный ремонт кондиционеров
сервисный центре предлагает ремонт телевизоров в москве недорого – починка телевизора
Сервисный центр предлагает центр ремонта сигвей feber ремонт сигвеев feber на дому
Если вы искали где отремонтировать сломаную технику, обратите внимание – тех профи
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в тюмени
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту кондиционеров в Москве.
Мы предлагаем: ремонт кондиционеров москва недорого
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту моноблоков в Москве.
Мы предлагаем: моноблок москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту гироскутеров в Москве.
Мы предлагаем: ремонт гироскутеров в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту планшетов в том числе Apple iPad.
Мы предлагаем: ремонт ipad москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Сервисный центр предлагает замена экрана fujifilm x100 замена экрана fujifilm x100
Профессиональный сервисный центр по ремонту посудомоечных машин с выездом на дом в Москве.
Мы предлагаем: ремонт посудомоечной машины хайсен на дому
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
In our blog, we bring you the most recent updates and exciting news about the most popular UK stars from the worlds of the press, reality TV, and showbiz. Whether you’re a fan of hit reality shows like Love Island, The Only Way Is Essex, or Made in Chelsea, or you’re enthusiastic to stay updated on the lives of the UK’s top social media stars, our website covers it all. From fascinating behind-the-scenes drama to exclusive discussions, we ensure you’re in the know with everything happening in the world of your beloved celebrities – http://eucein.ayz.pl/profile.php?lookup=6596 .
UK reality TV stars have gained huge attention over the years, changing from everyday individuals into household names with massive fanbases. Our platform dives into their personal and professional lives, offering perspectives into their latest endeavors, friendships, and dramas. Whether it’s a new fling brewing on Love Island or a cast member from Geordie Shore launching a new business, you’ll find detailed stories that reveal the glamorous yet sometimes chaotic lives of these celebrities.
Профессиональный сервисный центр по ремонту МФУ в Москве.
Мы предлагаем: ремонт мфу москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту принтеров в Москве.
Мы предлагаем: починить принтер в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Сервисный центр предлагает выездной ремонт фотовспышек sigma ремонт фотовспышки sigma недорого
Профессиональный сервисный центр по ремонту плоттеров в Москве.
Мы предлагаем: ремонт плоттеров москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем:ремонт крупногабаритной техники в уфе
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту объективов в Москве.
Мы предлагаем: ремонт диафрагмы объектива
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту серверов в Москве.
Мы предлагаем: срочный ремонт компьютеров на дому
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту сигвеев в Москве.
Мы предлагаем: сервис по ремонту сигвеев
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту автомагнитол в Москве.
Мы предлагаем: ремонт автомагнитол рядом
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту планшетов в Москве.
Мы предлагаем: замена стекла на планшете
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр ремонт телефонов рядом стоимость ремонта телефона
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в волгограде
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники воронеж
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр сервисный центр по ремонту телефонов сервис по ремонту телефонов москва
Профессиональный сервисный центр по ремонту моноблоков iMac в Москве.
Мы предлагаем: срочный ремонт аймака
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр ближайший сервис по ремонту телефонов профессиональный ремонт телефонов
Профессиональный сервисный центр по ремонту сотовых телефонов в Москве.
Мы предлагаем: ремонт телефонов в москве адреса
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Сервисный центр предлагает срочный ремонт телефона hisense ремонт телефонов hisense адреса
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники челябинск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Начните массовую индексацию ссылок в Google прямо cейчас!
Быстрая индексация ссылок имеет ключевое значение для успеха вашего онлайн-бизнеса. Чем быстрее поисковые системы обнаружат и проиндексируют ваши ссылки, тем быстрее вы сможете привлечь новую аудиторию и повысить позиции вашего сайта в результатах поиска.
Не теряйте времени! Начните пользоваться нашим сервисом для ускоренной индексации внешних ссылок в Google и Yandex. Зарегистрируйтесь сегодня и получите первые результаты уже завтра. Ваш успех в ваших руках!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в барнауле
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту сотовых телефонов в Москве.
Мы предлагаем: ремонт телефонов москва дешево
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр сервис смартфонов в ростове сервис ремонт телефонов
Профессиональный сервисный центр по ремонту сотовых телефонов в Москве.
Мы предлагаем: ремонт компьютеров и ноутбуков москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту духовых шкафов в Москве.
Мы предлагаем: сервисный центр по ремонту духовых шкафов
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Сервисный центр предлагает ремонт квадрокоптеров m.i.f недорого починка квадрокоптеров m.i.f
Полезный сервис быстрого загона ссылок сайта в индексация поисковой системы – индексация в гугл
Профессиональный сервисный центр по ремонту сотовых телефонов в Москве.
Мы предлагаем: ремонт ноутбуков круглосуточно
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Полезная информация на сайте. Все что вы хоте знать об интернете полезный сервис
Хочу поделиться своим опытом ремонта телефона в этом сервисном центре. Остался очень доволен качеством работы и скоростью обслуживания. Если ищете надёжное место для ремонта, обратитесь сюда: ремонт телефонов сокольники.
Сервисный центр предлагает починить индукционной плиты aeg ремонт индукционных плит aeg адреса
Если вы искали где отремонтировать сломаную технику, обратите внимание – ремонт бытовой техники в екатеринбурге
ремонт телефонов рядом
Профессиональный сервисный центр по ремонту Apple iPhone в Москве.
Мы предлагаем: сервисный центр по ремонту айфонов в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Тут можно преобрести оружейные сейфы шкафы оружейные сейфы для ружей
Тут можно преобрести сейф огнестойкий в москве сейф противопожарный
Тут можно преобрести сейф оружейный купить москва охотничьи сейфы
Тут можно преобрести сколько стоит сейф для ружья купить оружейный сейф цена
Тут можно преобрести сейф для ружья купить сколько стоит сейф для ружья
Тут можно преобрести огнестойкие сейфы купить противопожарный сейф
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали сервисный центр philips, можете посмотреть на сайте: сервисный центр philips
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали сервисный центр philips в москве, можете посмотреть на сайте: сервисный центр philips в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали сервисный центр philips в москве, можете посмотреть на сайте: сервисный центр philips
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали сервисный центр philips в москве, можете посмотреть на сайте: официальный сервисный центр philips
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали официальный сервисный центр philips, можете посмотреть на сайте: сервисный центр philips
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали сервисный центр philips, можете посмотреть на сайте: сервисный центр philips в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали сервисный центр philips, можете посмотреть на сайте: официальный сервисный центр philips
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали сервисный центр philips, можете посмотреть на сайте: сервисный центр philips в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Тут можно преобрести взломостойкие сейфы для дома сейфы взломостойкие
Тут можно сейф для офиса ценакупить сейф для офиса
Тут можно сейф в наличиисейф купить в москве
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали ремонт ноутбуков lenovo сервис, можете посмотреть на сайте: ремонт ноутбуков lenovo
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Betzula giris, spor bahisleri konusunda essiz deneyimler sunar. buyuk futbol kars?lasmalar? icin en h?zl? sekilde favori tak?mlar?n?za destek olabilirsiniz.
Betzula’n?n guvenilir altyap?s?, profesyonel hizmet garantisi verir. Bet Zula sosyal medya hesaplar?yla bonus f?rsatlar?ndan haberdar olabilirsiniz.
en onemli spor etkinliklerinin heyecan?n? Betzula ile yasayabilirsiniz.
Ayr?ca, bet zula giris linki, kesintisiz bahis deneyimi sunar. Ozel olarak, fenerbahce galatasaray betzula, kolay ve h?zl? giris imkan?.
Betzula, en genis bahis seceneklerinden ozel turnuvalara kadar tum kullan?c?lar?n ihtiyaclar?n? kars?lar. en guncel oranlar? gormek icin Betzula ile kazanmaya baslay?n!
371212+
Для начала заходим на площадку:
Заходим на оригинальную ссылку:
Ссылка https://bs1site.at
ССЫЛКА TOR: blackpxl62pgt3ukyuifbg2mam3i4kkegdydlbbojdq4ij4pqm2opmyd.onion
Официальный сайт Blacksprut
БлекСпрут официальная ссылка
Как зайти на даркнет маркетплейс БлекСпрут
Введение
В этой статье мы подробно расскажем, как зайти на даркнет маркетплейс БлекСпрут. Вы узнаете, как использовать официальные зеркала BlackSprut, ссылки на сайт БлекСпрут и способы безопасного доступа через ТОР и VPN. БлекСпрут является одним из наиболее популярных даркнет маркетплейсов, и доступ к нему требует определенных знаний и мер предосторожности.
Что такое БлекСпрут?
БлекСпрут (BlackSprut) – это даркнет маркетплейс, предлагающий широкий ассортимент товаров и услуг. Из-за своей природы и содержания доступ к БлекСпрут осуществляется через сети типа onion, обеспечивающие анонимность пользователей.
Как зайти на БлекСпрут: шаги и инструкции
Шаг 1: Установка ТОР браузера
Первым шагом для доступа к БлекСпрут через ТОР является установка ТОР браузера. Это специализированный браузер, который позволяет анонимно заходить на сайты в onion-сети.
Скачайте ТОР браузер с официального сайта Tor Project.
Установите браузер на ваш компьютер или мобильное устройство.
Запустите ТОР браузер.
Шаг 2: Использование официального зеркала BlackSprut
Для доступа к БлекСпрут важно использовать только проверенные и официальные ссылки. Официальное зеркало BlackSprut гарантирует безопасный доступ и защиту от фишинговых сайтов.
Официальная ссылка на БлекСпрут будет иметь формат.onion. Например, ссылка на сайт БлекСпрут может выглядеть так:
Зеркала сайта БлекСпрут обеспечивают резервный доступ в случае блокировки основного сайта. Например, зеркало БлекСпрут через ТОР:
Шаг 3: Подключение через VPN
Для дополнительной безопасности рекомендуется использовать VPN.
Выберите надежный VPN сервис.
Подключитесь к VPN перед запуском ТОР браузера.
Откройте ТОР браузер и введите официальный адрес БлекСпрут.
Шаг 4: Безопасный доступ к БлекСпрут через onion
Когда вы используете ТОР браузер и официальное зеркало БлекСпрут, важно следовать мерам предосторожности:
Проверяйте URL на наличие ошибок и подлинности.
Используйте VPN для дополнительной защиты.
Не вводите личные данные на подозрительных сайтах.
Часто задаваемые вопросы
Как получить доступ к БлекСпрут через onion?
Для доступа к БлекСпрут через onion сеть необходимо использовать ТОР браузер и официальные ссылки на сайт БлекСпрут. Подключение через VPN также рекомендуется для защиты вашей анонимности.
Как зайти на BlackSprut безопасно?
Чтобы безопасно зайти на BlackSprut, используйте ТОР браузер, подключайтесь через VPN, и проверяйте официальные зеркала сайта БлекСпрут. Никогда не переходите по подозрительным ссылкам.
Что такое зеркало БлекСпрут?
Зеркало БлекСпрут – это альтернативный адрес сайта, используемый для обеспечения доступа в случае блокировки основного сайта. Зеркало BlackSprut через ТОР помогает пользователям получить доступ к маркетплейсу, сохраняя их анонимность.
Теперь вы знаете, как зайти на даркнет маркетплейс БлекСпрут, используя официальные зеркала и ссылки. Следуйте этим инструкциям и соблюдайте меры предосторожности, чтобы обеспечить свою безопасность в даркнете. Официальный сайт BlackSprut и его зеркала через ТОР и VPN помогут вам получить доступ к БлекСпрут, оставаясь анонимным и защищенным.
blacksprutblack sprutссылки бсссылки в бс 2024ссылка на блекспрутрабочая ссылка блекспрутссылки тор блекспрутблекспрут актуальная ссылкаблекспрут ссылка bs0bestтор блекспрутссылки тор блекспрутблекспрут сайтблекспрут официальный сайтблекспрут входкак зайти на блекспруткак зайти на блэкспрутблэкспрут входблэкспрут ссылкаблэкспрут онионблэкспрут даркнетблэкспрут даркнетблэкспрут blacksprut даркнет обзор анонимной даркнет площадкиbs как зайтиbs at как зайти на сайтbs входbs ссылкаblacksprut darknetblacksprutblacksprut зеркалаblacksprut ссылкаblacksprut сайтзеркала blacksprut rusffкак зайти на blacksprutblacksprut официальныйblacksprut com зеркалоblacksprut зеркала онион2fa blacksprutрабочая blacksprutкод blackspruthttps blacksprutкак зайти на blacksprut rusffофициальная ссылка на blacksprutblacksprut маркетплейсрабочее зеркало blacksprutкак зайти на сайт blacksprut2fa код blackspruthttp blacksprutblacksprut bs0best atblacksprut актуальныетор blacksprutblacksprut ссылка rusffbs2best at ссылка blacksprutblacksprut актуальная ссылкаtor blacksprutblacksprut com зеркало rusffhttps blacksprut ссылкаblacksprut зеркала онион rusffblacksprut площадкиbs1site at ссылка blacksprutblacksprut netblacksprut входофициальная ссылка на blacksprut rusffblacksprut blacksprut clickblacksprut bs0tor atblacksprut официальный сайтblacksprut ссылка торкак зайти на сайт blacksprut rusffblacksprut https bs1site atblacksprut http bs0best athttp blacksprut ссылкааккаунты blacksprutрабочее зеркало blacksprut rusffhttps bs2site at ссылка blacksprutbs0best at ссылка blacksprut http bs2best atblacksprut 2blacksprut ссылка blacksprut darknetофициальная ссылка на blacksprutblacksprut ссылка rusffbs0best at ссылка blacksprutblacksprut актуальная ссылкаhttps blacksprut ссылкаbs1site at ссылка blacksprutофициальная ссылка на blacksprut rusffhttp blacksprut ссылкаhttps bs1site at ссылка blacksprutbs0best at ссылка blacksprut http bs0best atblacksprut ссылка tortor blacksprutblacksprut ссылка torblacksprut ссылка tor bs2tor nltor blacksprut rusffblacksprut зеркала torsprutblack sprut
The WealthyPot site offers an innovative financial blog intended to guide readers using expert insights, insider tips, and tested techniques for financial success. Covering a wide range of areas including budgeting, capital growth, financial reserves, and long-term saving, the site works to demystify complex financial concepts for people regardless of expertise. Whether you’re looking to improve personal finances, try innovative investment opportunities, or create a safe financial future, The WealthyPot blog serves as a knowledgeable partner. more details here. Stay ahead, take charge!
Тут можно преобрести сейфы для оружия купить шкаф для оружия
Недавно нашел на РіРёР·Р±Рѕ казин,
и решил рассказать своим опытом.
Сайт выглядит очень интересной,
особенно когда ищешь надежное казино.
Кто реально пробовал Gizbo Casino?
Расскажите своим опытом!
В частности любопытно узнать про промокоды и фриспины.
Например, есть ли Gizbo Casino особые предложения для начинающих пользователей?
Еще интересует, как получить рабочее зеркало Gizbo Casino, если официальный сайт недоступен.
Читал немало разных мнений, но интересно узнать реальные рекомендации.
Например, где эффективнее использовать промокоды на Gizbo Casino?
Поделитесь своим мнением!
На днях нашел на РіРёР·Р±Рѕ casino,
и захотел рассказать своим впечатлением.
Платформа выглядит очень интересной,
особенно если хочешь найти надежное казино.
Кто уже использовал Gizbo Casino?
Расскажите своим мнением!
В частности любопытно узнать про промокоды и акции.
Допустим, предлагают ли Gizbo Casino специальные условия для новых пользователей?
Еще интересует, как найти рабочее зеркало Gizbo Casino, если основной портал не работает.
Читал немало противоречивых отзывов, но хотелось бы узнать честные рекомендации.
Например, как эффективнее использовать промокоды на Gizbo Casino?
Расскажите своим опытом!
Balanceo dinamico
Aparatos de calibración: clave para el rendimiento suave y productivo de las dispositivos.
En el campo de la tecnología contemporánea, donde la eficiencia y la estabilidad del aparato son de máxima importancia, los dispositivos de equilibrado desempeñan un tarea esencial. Estos equipos específicos están diseñados para ajustar y fijar piezas dinámicas, ya sea en dispositivos manufacturera, automóviles de movilidad o incluso en dispositivos hogareños.
Para los profesionales en reparación de aparatos y los profesionales, manejar con sistemas de ajuste es importante para asegurar el operación suave y estable de cualquier sistema dinámico. Gracias a estas alternativas avanzadas innovadoras, es posible limitar considerablemente las oscilaciones, el sonido y la tensión sobre los sujeciones, extendiendo la duración de partes costosos.
Asimismo importante es el papel que juegan los dispositivos de calibración en la soporte al consumidor. El apoyo especializado y el soporte regular empleando estos sistemas facilitan brindar soluciones de óptima excelencia, incrementando la bienestar de los usuarios.
Para los titulares de emprendimientos, la aporte en sistemas de equilibrado y medidores puede ser importante para optimizar la eficiencia y eficiencia de sus equipos. Esto es especialmente significativo para los inversores que administran pequeñas y medianas empresas, donde cada punto importa.
También, los dispositivos de ajuste tienen una vasta aplicación en el ámbito de la fiabilidad y el supervisión de nivel. Permiten identificar potenciales problemas, impidiendo arreglos onerosas y problemas a los dispositivos. Más aún, los resultados obtenidos de estos aparatos pueden emplearse para maximizar métodos y mejorar la visibilidad en motores de exploración.
Las zonas de uso de los dispositivos de calibración comprenden numerosas ramas, desde la elaboración de vehículos de dos ruedas hasta el monitoreo de la naturaleza. No importa si se habla de grandes elaboraciones productivas o modestos talleres hogareños, los aparatos de balanceo son fundamentales para asegurar un funcionamiento eficiente y sin paradas.
На днях нашел на http://hola666.com/home.php?mod=space&uid=1403020 – gizbo сайт,
и захотел поделиться своим впечатлением.
Платформа выглядит довольно интересной,
особенно если хочешь найти надежное казино.
Кто уже пробовал Gizbo Casino?
Расскажите своим мнением!
Особенно интересно узнать про бонусы и акции.
Например, предлагают ли Gizbo Casino особые условия для начинающих пользователей?
Также интересует, где получить рабочее зеркало Gizbo Casino, если основной сайт не работает.
Читал много разных отзывов, но интересно узнать реальные рекомендации.
Например, где лучше активировать бонусы на Gizbo Casino?
Расскажите своим мнением!
Недавно нашел на gizbo casino рабочее,
и решил рассказать своим впечатлением.
Сайт выглядит довольно привлекательной,
особенно когда ищешь надежное казино.
Кто реально пробовал Gizbo Casino?
Поделитесь своим опытом!
Особенно интересно узнать про промокоды и фриспины.
Например, есть ли Gizbo Casino особые предложения для новых игроков?
Еще интересно, где найти рабочее зеркало Gizbo Casino, если основной портал недоступен.
Видел немало противоречивых мнений, но хотелось бы узнать честные рекомендации.
Допустим, где лучше использовать промокоды на Gizbo Casino?
Расскажите своим опытом!
Тут можно приобрести создание медицинских сайтов под ключ разработка сайта медицинского центра
На днях нашел на http://www.wudao28.com/home.php?mod=space&uid=1554497 – РіРёР·Р±Рѕ официальный зеркало,
и решил поделиться своим опытом.
Сайт выглядит довольно интересной,
особенно когда ищешь качественное казино.
Кто реально пробовал Gizbo Casino?
Поделитесь своим мнением!
В частности любопытно узнать про бонусы и акции.
Допустим, есть ли Gizbo Casino особые условия для начинающих игроков?
Еще интересует, где найти рабочее зеркало Gizbo Casino, если основной сайт не работает.
Читал много противоречивых мнений, но хотелось бы узнать честные рекомендации.
Допустим, где лучше использовать бонусы на Gizbo Casino?
Расскажите своим опытом!
На днях наткнулся на gizbo зеркало,
и захотел поделиться своим опытом.
Платформа выглядит довольно привлекательной,
особенно когда ищешь качественное казино.
Кто уже пробовал Gizbo Casino?
Расскажите своим опытом!
Особенно интересно узнать про бонусы и фриспины.
Например, предлагают ли Gizbo Casino специальные условия для начинающих игроков?
Также интересует, где получить рабочее зеркало Gizbo Casino, если основной сайт недоступен.
Читал много противоречивых отзывов, но хотелось бы узнать честные рекомендации.
Допустим, как лучше активировать бонусы на Gizbo Casino?
Расскажите своим опытом!
Тут можно преобрести продвижение медицинских услуг продвижение сайта медицинских услуг
Тут можно преобрести seo под ключ продвижение медицинских услуг
pdacenter.ru – сервис по ремонту бытовой техники
Ремонт экшен-камер в Перми в официальном сервисном центре PDACENTER.
Наши инженеры выполняют ремонт любой сложности по дотупным ценам!
Святки
Святки
crawled
atropamine
coverer
Post-napoleonic
biremes
Профессиональный сервисный центр по ремонту Apple iPhone в Москве.
Мы предлагаем: ремонт телефонов айфон в москве адреса
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту Apple iPhone в Москве.
Мы предлагаем: ремонт айфона в москве недорого
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
маркетплейс аккаунтов соцсетей площадка для продажи аккаунтов
маркетплейс аккаунтов https://marketplace-akkauntov-top.ru/
аккаунты с балансом маркетплейс аккаунтов соцсетей
маркетплейс аккаунтов https://kupit-akkaunt-top.ru/
Database of Accounts for Sale Buy accounts
Database of Accounts for Sale Account Buying Service
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт бытовой техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Website for Buying Accounts accountsmarketplacehub.com
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт крупногабаритной техники в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Account trading platform Account Trading Platform
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт бытовой техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
accounts marketplace secure account sales
social media account marketplace buy account
find accounts for sale account exchange
account purchase database of accounts for sale
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт бытовой техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
secure account purchasing platform accounts for sale
sell accounts account catalog
website for selling accounts account buying service
purchase ready-made accounts account exchange service
account purchase find accounts for sale
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
accounts marketplace sell account
ready-made accounts for sale account buying platform
ready-made accounts for sale profitable account sales
purchase ready-made accounts sell pre-made account
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт крупногабаритной техники в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
account acquisition find accounts for sale
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт бытовой техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
accounts market account selling platform
account purchase account trading
account exchange database of accounts for sale
accounts for sale account selling platform
purchase ready-made accounts online account store
secure account sales buy accounts
account store buy pre-made account
verified accounts for sale https://accounts-offer.org/
buy and sell accounts accounts market
account catalog https://accounts-marketplace.live
account exchange service https://social-accounts-marketplace.xyz/
account sale accounts market
guaranteed accounts https://buy-accounts-shop.pro/
account marketplace https://accounts-marketplace.art
buy accounts https://social-accounts-marketplace.live
verified accounts for sale accounts market
website for selling accounts https://accounts-marketplace-best.pro
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт крупногабаритной техники в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту техники.
Мы предлагаем: Мастерская ремонта бытовой техники
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
купить аккаунт https://akkaunty-na-prodazhu.pro
продать аккаунт https://kupit-akkaunt.xyz
маркетплейс аккаунтов https://rynok-akkauntov.top
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
покупка аккаунтов https://akkaunt-magazin.online
маркетплейс аккаунтов соцсетей купить аккаунт
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
маркетплейс аккаунтов соцсетей https://akkaunty-optom.live/
площадка для продажи аккаунтов магазины аккаунтов
Профессиональный сервисный центр по ремонту техники.
Мы предлагаем: Выездной ремонт сушильных машин с гарантией
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
buy facebook accounts cheap buy facebook advertising accounts
buy facebook profiles https://buy-ad-account.top/
buy facebook account facebook ad accounts for sale
buy fb account https://ad-account-buy.top
fb accounts for sale facebook account buy
facebook ad account for sale https://ad-account-for-sale.top/
buy facebook ad accounts buy facebook accounts cheap
buy facebook ads manager buy fb ads account
google ads reseller https://buy-ads-account.top
facebook ad account for sale https://buy-accounts.click/
buy google ads threshold account google ads agency account buy
google ads accounts https://ads-account-buy.work
buy google ads account google ads account for sale
buy aged google ads account https://buy-account-ads.work
buy google ads account https://buy-ads-agency-account.top
buy google ads verified account https://sell-ads-account.click
buy aged google ads account google ads accounts
facebook bm account buy facebook business manager account
buy verified bm facebook https://buy-business-manager-acc.org/
buy facebook business manager verified buy-verified-business-manager.org
buy facebook bm account buy-verified-business-manager-account.org
facebook bm account https://buy-business-manager-verified.org
buy facebook business manager https://business-manager-for-sale.org
buy facebook bm buy-bm.org
buy facebook business account https://verified-business-manager-for-sale.org/
facebook bm account buy https://buy-business-manager-accounts.org
buy tiktok ads account https://buy-tiktok-ads-account.org
tiktok ad accounts https://tiktok-ads-account-buy.org
buy tiktok ads https://tiktok-ads-account-for-sale.org
buy tiktok ads accounts https://buy-tiktok-ad-account.org
tiktok ads agency account https://tiktok-agency-account-for-sale.org
buy tiktok ads account https://buy-tiktok-business-account.org
buy tiktok business account https://buy-tiktok-ads.org
кайт египет
красное море температура воды
praca dla dziewczyn online Стань вебкам моделью в польской студии, работающей в Варшаве! Открыты вакансии для девушек в Польше, особенно для тех, кто говорит по-русски. Ищешь способ заработать онлайн в Польше? Предлагаем подработку для девушек в Варшаве с возможностью работы в интернете, даже с проживанием. Рассматриваешь удаленную работу в Польше? Узнай, как стать вебкам моделью и сколько можно заработать. Работа для украинок в Варшаве и высокооплачиваемые возможности для девушек в Польше ждут тебя. Мы предлагаем легальную вебкам работу в Польше, онлайн работа без необходимости знания польского языка. Приглашаем девушек без опыта в Варшаве в нашу вебкам студию с обучением. Возможность заработка в интернете без вложений. Работа моделью онлайн в Польше — это шанс для тебя! Ищешь “praca dla dziewczyn online”, “praca webcam Polska”, “praca modelka online” или “zarabianie przez internet dla kobiet”? Наше “agencja webcam Warszawa” и “webcam studio Polska” предлагают “praca dla mlodych kobiet Warszawa” и “legalna praca online Polska”. Смотри “oferty pracy dla Ukrainek w Polsce” и “praca z domu dla dziewczyn”.
кайтсерфинг
Hello, this weekend is fastidious in support of me, because this moment i am reading this impressive educational paragraph here at my residence.
Weapon
Slightly off the main thread here
A couple of scrolls ago I found a site called Talabout.
It’s full of conversations with people from all walks of life — unfiltered, not your typical media stuff.
Sometimes the vibe there really echoes the stuff being shared here.
Just curious if someone’s come across it too?
buying facebook ad account gaming account marketplace gaming account marketplace
facebook accounts for sale buy and sell accounts buy accounts
Ты готова изменить свое тело и настроение? Присоединяйся к каналу фитнес-тренер для женщин, где ты найдешь персональные тренировки дома, питание без жестких диет и мотивацию каждый день. Начни свой путь к идеальной форме прямо сейчас!
does creatine help build muscle faster
References:
how fast does creatine cause Hair loss (http://hikvisiondb.webcam/index.php?title=suitcinema20)
can creatine cause fast heart rate
References:
https://enoticias.site/item/319669
dianabol only cycle for beginners
References:
testosterone cypionate and dianabol cycle [https://farangmart.co.th/author/flowerplant51/]
dianabol winstrol cycle
References:
first dianabol cycle – https://doodleordie.com/profile/flowerbase71,
A motorcycle amp enhances audio systems https://www.royalholloway.ac.uk/ riders.
sermorelin ipamorelin 10mg blend dosage
References:
https://www.fionapremium.com/author/lyricregret1/
Absolutely with you it agree. It seems to me it is good idea. I agree with you.
——
https://the.hosting/nl/help/nabor-kursorov-ot-bibata-original-kak-ustanovit-v-linux-windows-mac
https://www.newsbreak.com/news/4371312073468-top-car-rental-websites-full-review-and-comparison
Красота и здоровье пнг — идеальные изображения для вдохновенhttps://www.tcg-web.site/blog/index.php?entryid=185625я.
2111 http://wiki.naval.ch/index.php?title=Tyuning_11m делает ВАЗ-2111 более практичным.
YouTube https://wiki.laduni.id/User:JulienneLightner news channels provide daily updates on market trends and analysis.
Сервис подписки на доставку наборов для создания браслетов.
Here is my homepage: https://ajuda.cyber8.com.br/index.php/Biznes_Idei_7V
Рулевое https://academy.cid.asia/blog/index.php?entryid=76731 Газель требует частого ТО.
Spanking-themed https://wiki.asexuality.org/w/index.php?title=User_talk:GeniaJaffe090 games are niche and often controversial, targeting specific adult audiences.
Компьютерная игра Шрек переносит https://oerdigamers.info/index.php/User:PollyBrinson029оков в мир болот и приключений.
Сервис доставки наборов для создания домашнего декора из керамики и стекла.
Also visit my homepage; http://classicalmusicmp3freedownload.com/ja/index.php?title=Biznes_Idei_71N
Прошивка ГУ https://wiki.anythingcanbehacked.com/index.php?title=User:AbbieBergstrom1 M6 улучшает скорость работы мультимедиа и интерфейс.
SPX криптовалюта может быть связана с новыми проектами.
My homepage – https://harry.main.jp/mediawiki/index.php/Cryptovalyta_28u
Платформа для создания виртуальных туров по историческим местам.
Feel free to surf to my web page: https://www.sochip.com.cn/v82x/index.php?title=User:AuroraSladen17
Насос Форд Фокус обеспечивает стабильную подачу топлива.
my website https://sakumc.org/xe/vbs/3895127
ATH https://wiki.laduni.id/User:ElenaLaurence55а стремится к новым ценовым максимумам.
Nice post. I learn something new and challenging on websites I stumbleupon on a daily basis. It’s always helpful to read through content from other writers and use a little something from their web sites.
gay porn hub
Компьютерные настольные игры — адаптация классики на ПК.
Look at my webpage; https://docs.brdocsdigitais.com/index.php/User:DinaN958514145
Игра компьютерная популярная часто становится основой для фильмов и книг.
Also visit my web site; https://karabast.com/wiki/index.php/Kompterni_Igri_57D
Transferring Steam games to a new https://sakumc.org/xe/vbs/3873373 is easy with cloud saves or backups.
https://wiki.la.voix.de.lanvollon.net/index.php/Haval-m6_75N Jolion vs M6: M6 практичнее, Jolion современнее.
Old https://dev.neos.epss.ucla.edu/wiki/index.php?title=Computer_Games_72L games are available on sites like GOG for legal, DRM-free downloads.
Компьютерная https://bbarlock.com/index.php/Kompterni_Igri_56oа Симпсоны — юмор и приключения в одном.
Криптовалюта ТОН активно интегрируется в Telegram.
my blog https://bbarlock.com/index.php/User:CelsaEisenhower
Рулевое https://www.ebersbach.org/index.php?title=Rulevoe-upravl_31s ГАЗель отличается надежностью и простотой конструкции.
Ликвидации криптовалюты происходят при высоком левередже.
Feel free to visit my web blog – https://lunarishollows.wiki/index.php?title=Cryptovalyta_14J
Сервис доставки домашних заготовок от местных фермеров.
My web page … https://www.tcg-web.site/blog/index.php?entryid=196896
Touch screen https://bbarlock.com/index.php/Computer_Games_48b games, like Fruit Ninja, are intuitive and fun for all ages.
Датчик АБС Гранта задний может вызывать срабатывание лампы АБС на приборной панели.
Feel free to surf to my web site … https://www.tcg-web.site/blog/index.php?entryid=196535
ТО рулевого управления включает проверку люфтов и состояния гидравлики.
Look into my web page :: https://waselplatform.org/blog/index.php?entryid=764255
Предохранитель https://365.expresso.blog/question/topliv-nasos-99x/ насоса Газель Бизнес защищает систему.
Internet.Hicks feels like a domain for rural http://wiki.die-karte-bitte.de/index.php/Internet_54x advocacy or culture.
Криминальные новости мира: в Южной Америке раскрыта крупная сеть кhttp://wiki.die-karte-bitte.de/index.php/Novosti_Mira_72Oнтрабанды.
James Moore’s https://bbarlock.com/index.php/Psychology_Today_80h Today profile emphasizes his expertise in psychological counseling.
Air travel https://skyglass.io/sgWiki/index.php?title=Travel_News_91W reports airlines adapting to new security mandates.
Диван Софт — это мягкая мебель с IT-интеграцией.
my blog post … https://xeuser.gajaga.work/index.php?mid=board&document_srl=88654
Свадебное http://wiki.die-karte-bitte.de/index.php/Travels_35Q — романтичный старт семейной жизни.
Adme публикует статьи по психологии http://wiki.die-karte-bitte.de/index.php/Psihologia_Otnoshenii_64t.
VXE Софт улучшает работу игровых устройств VXE.
My web page https://xeuser.gajaga.work/index.php?mid=board&document_srl=88283
2022 best hotels in Canada U.S. News rankings remain relevant for domestic http://wiki.die-karte-bitte.de/index.php/Travel_News_70h.
Софт Ткань — мягкий материал для обивки.
Feel free to visit my web-site; https://xeuser.gajaga.work/index.php?mid=board&document_srl=91300
Computer hardware includes CPUs and RAM, while https://xeuser.gajaga.work/index.php?mid=board&document_srl=97740 includes OS and applications.
https://xeuser.gajaga.work/index.php?mid=board&document_srl=100429 hardware is the physical infrastructure, while software is the code that enables functionality and user interaction.
http://wiki.die-karte-bitte.de/index.php/Travel_News_56u Daily News reports a decline in bookings to banned countries.
The https://wiki.novaverseonline.com/index.php/Travel_News_78J ban’s economic impact worries tourism-dependent regions.
YouTube-каналы по психологии https://xeuser.gajaga.work/index.php?mid=board&document_srl=41986 дают практические советы.
Псhttp://juicy.iptime.org/board_XAde14/1682351хология современных отношений отражает влияние технологий на близость.
Если ноутбук разряжается при подключенной зарядhttps://trevorjd.com/index.php/Noutbuk_58cе, проверьте адаптер или батарею.
Camping https://bbarlock.com/index.php/World_News_77B Newport News, VA, is a hub for RV camping enthusiasts.
Is http://qa.discoveryindochina.com/fr/question/physical-bitcoins-33k/ wallet for bitcoin a good investment? Some people collect them for their historical significance.
Как правильно привязать xrumer к сервисам
Как привязать xrumer
Сконцентрируйтесь на корректной настройке прокси для эффективного функционирования. Настройки должны включать IP-адреса, порт и тип (HTTP/HTTPS). Использование надежных прокси-серверов поможет обеспечить стабильное соединение и предотвратить блокировку. Выбор качественного прокси существенно влияет на скорость работы и успешность выполнения заданий.
Следующий шаг – это подключение учетной записи к выбранным платформам. Обычно требуется указать логины и пароли, а также выполнить базовую конфигурацию для минимизации рисков несанкционированного доступа. Всегда держите в уме возможность применения двухфакторной аутентификации, что значительно повысит уровень безопасности.
Обратите внимание на форматы данных для загрузки. Используйте CSV-файлы, чтобы правильно загружать списки URL или текстов. Убедитесь, что информация структурирована так, чтобы обеспечить автоматический импорт. Правильная подготовка данных исключает ошибки и ускоряет процесс размещения.
Наконец, протестируйте систему. Создайте тестовую кампанию, чтобы убедиться в корректности всех настроек. Анализируйте результаты, чтобы выявить возможные недочеты и внести необходимые изменения для улучшения успешности автоматизации.
Выбор и настройка API для интеграции с https://reviews.wiki/index.php/User:NidiaStoker
Рекомендуется использовать RESTful API, что позволяет гибко взаимодействовать с приложением. Обратите внимание на документацию API, в которой описаны все доступные эндпоинты и параметры.
Важно обеспечить актуальность токенов доступа. Многие API требуют токены, которые необходимо обновлять через определенные интервалы времени для сохранения стабильности соединения. Настройте процесс обновления токенов, чтобы избегать сбоев в работе.
При работе с API выберите подходящий метод аутентификации: OAuth 2.0 или базовую аутентификацию, в зависимости от требований выбранного сервиса. Это обеспечит безопасный доступ к необходимым данным.
Настройка запросов должна учитывать различия в ответах API. Применяйте библиотеки для работы с JSON, чтобы обрабатывать данные и реагировать на возможные ошибки сервера.
Параметры запроса, такие как лимиты на количество обращений или необходимость использования страниц, необходимо указывать корректно, чтобы избежать превышения лимита запросов и потери функциональности.
Важно протестировать интеграцию, используя инструменты, такие как Postman или cURL. Это позволит убедиться, что все запросы обрабатываются верно и ответ сервера соответствует ожиданиям.
Рекомендуется использовать вспомогательные библиотеки для автоматизации работы с API, что позволит упростить процесс интеграции и ускорить разработку.
Оптимизация параметров для работы с различными сервисами
Задайте временные интервалы для отправки запросов, чтобы избежать блокировок. Рекомендуется устанавливать паузы от 20 до 60 секунд между действиями, в зависимости от активности платформы.
При настройке аккаунтов используйте уникальные идентификаторы и почтовые адреса. Это минимизирует вероятность обнаружения скриптов противодействием системами безопасности.
Оптимизируйте настройки User-Agent. Аспекты браузера должны варьироваться, чтобы создать впечатление реальных пользователей. Используйте коллекцию разных UA для повышения степени анонимности.
В зависимости от типа целевых платформ, настройте параметры прокси. Работайте только с качественно проверенными серверами, чтобы исключить задержки и ограничения по IP-адресам.
Регулярно обновляйте базы данных возможных целевых сайтов. Это позволит поддерживать актуальность и увеличивать шансы на успешную работу с новыми источниками.
Используйте шаблоны и готовые сценарии для различных типов контента. Это не только ускорит процесс, но и повысит уровень уникальности публикуемого материала.
Практикуйте разделение задач для разных аккаунтов. Это позволит лучше контролировать процесс и выстраивать более гибкие кампании по продвижению.
При проверке результата учитывайте метрики отказов и вовлеченности. Это поможет корректировать параметры для достижения максимальной эффективности взаимодействия с целевой аудиторией.
Скачивание и использование Xrumer через торрент
https://wiki.lafabriquedelalogistique.fr/Utilisateur:JaclynHoss752 torrent
Перед тем как приступить к работе с программным обеспечением для автоматизации продвижения, важно знать, где найти надежные источники для загрузки. Например, рекомендуем обратить внимание на проверенные сайты, которые предлагают качественные раздачи. Это поможет избежать заражения системы вредоносными файлами и обеспечит получение актуальной версии продукта.
Затем, после получения нужного файла, стоит уделить внимание инсталляции. Рекомендуем отключить антивирусное ПО на время установки, поскольку программы для автоматизации могут восприниматься как угрозы. Это временное решение позволит завершить процесс без лишних помех, а затем можно будет включить защиту обратно.
Важно настроить программу, учитывая актуальные настройки для конкретных задач. Рекомендуем ознакомиться с руководствами и видеоуроками, которые помогут оптимизировать работу с инструментарием, открыть доступ к дополнительным функциям и сократить время на выполнение задач. Не следует забывать и о регулярных обновлениях, чтобы поддерживать актуальность всех импортированных инструментов.
Как найти и скачать Xrumer через торрент: пошаговая инструкция
Следующий этап – поиск необходимых файлов. Перейдите на сайты, предлагающие пиринговые раздачи. Рекомендуется использовать проверенные ресурсы, такие как The Pirate Bay или 1337x, чтобы избежать вредоносных программ. Введите название искомого софта в строку поиска. Обратите внимание на рейтинг и количество загрузок, так как это может свидетельствовать о качестве раздачи.
Когда найдете нужный файл, скачайте его, нажав на ссылку. В некоторых случаях потребуется подтвердить, что вы не робот, прежде чем начнётся загрузка. После этого файл .torrent или магнитная ссылка будет загружена.
Откройте загруженный файл с помощью установленного клиента. Выберите папку для сохранения контента и начните процесс. Следите за количеством раздающих и желающих загрузить, чтобы гарантировать успешное завершение.
По завершении загрузки проверьте файл на наличие вирусов с помощью антивирусного ПО. Если всё в порядке, распакуйте архив (если это необходимо) и начните использование программы согласно инструкции.
Настройка и использование Xrumer после скачивания: советы для начинающих
Перед запуском убедитесь, что установлены все необходимые зависимости. Проверьте наличие виртуального окружения, запускаемого с помощью Python, и наделите необходимые права. Это предотвратит возможные ошибки во время работы.
Создайте файл конфигурации, в котором задайте параметры вашего проекта. Не забывайте о задании списка целевых ресурсов для разметки. Важно уточнить, какие именно площадки вы хотите использовать, а также типы контента, который собираетесь размещать.
Настройте прокси-серверы для обеспечения анонимности. Добавьте их в конфигурационном файле, чтобы избежать блокировок со стороны сайтов. Выбор надежных прокси увеличит скорость работы и уменьшит риск обнаружения.
Рекомендуется проводить тестовые запуски с небольшими объемами данных. Это поможет выявить возможные ошибки и настроить параметры под ваши нужды без риска банов на крупных площадках.
Обратите внимание на логи работы программы. Они содержат полезную информацию о выполненных операциях и возможных проблемах. Регулярный анализ логов позволит оптимизировать процессы и повысить результаты.
Задайте время между запросами, чтобы избежать нагрузок на серверы. Это поможет сохранить аккаунты и избежать блокировок. Установите интервалы, которые подойдут для выбранных площадок.
Следите за обновлениями программы и ресурсами, на которых публикуете контент. Некоторые платформы могут менять правила, и важно своевременно адаптировать свои настройки под актуальные требования.
Проводите анализ результатов по итогам кампаний. Это поможет выявить, какие методики работают лучше всего и где стоит скорректировать подход. Используйте полученные данные для планирования будущих проектов.
Queen’s News of the https://ajuda.cyber8.com.br/index.php/World_News_35G vinyl remains a collector’s favorite for its bold sound.
https://wiki.novaverseonline.com/index.php/User:EllaY53837 как инструмент продвижения на YouTube
Xrumer для youtube
При запуске новых видео рекомендуется сосредоточиться на создании качественного контента, но интеграция автоматических систем для настройки ссылок может значительно ускорить расширение аудитории. Для эффективной работы стоит использовать специальные средства, которые помогут разместить ваши ссылки на множестве релевантных площадок в сети, тем самым увеличивая видимость.
Обратите внимание на возможность создания профилей на форуме и других платформах, поскольку это откроет доступ к специализированным аудиториям, заинтересованным в вашей тематике. Размещение комментариев с ссылками на ваши материалы также может способствовать улучшению индексации в поисковых системах.
Ежедневное использование данных технологий даст возможность получить стабильный трафик ваших ресурсов, что особенно важно в стартовый период. Не забывайте о необходимости анализа результатов: регулярные отчеты о количестве переходов и активности пользователей помогут скорректировать тактики.
Автоматизация размещения комментариев для увеличения видимости видео
Автоматизация комментирования может значительно повысить привлекательность контента в сети видеосервисов. Основная рекомендация – использовать заранее подготовленные шаблоны для интерактивного взаимодействия с пользователями. Комментарии должны быть релевантными и отражать суть видео, чтобы не выглядеть как спам.
Создание базы комментариев, которые могут касаться различных тем, позволит эффективно реагировать на разные видео. Такой подход увеличивает шансы получения ответов от других пользователей и, как следствие, привлекает к контенту больше внимания.
Следующий этап – выбрать платформу для автоматизации. Важно, чтобы инструмент поддерживал интерактивные функции, например, возможность фиксации новых комментариев или использования различных учетных записей для размещения комментариев, что поможет сохранить разнообразие взаимодействий.
Учтите временные интервалы между комментированием. Задержка с размещением новых сообщений уменьшает риски блокировки учетной записи и создает более натуральный поток активности, что благоприятно сказывается на восприятии контента со стороны аудитории.
Необходимо также следить за статистикой комментариев, чтобы увидеть, какие посты вызывают больший интерес. Анализ результатов позволяет оптимизировать контент и корректировать подход к общению с аудиторией.
Анализ и выбор целевой аудитории для повышения взаимодействия с контентом
Четкое определение аудитории значительно увеличивает эффект от контента. Для начала, используйте инструменты аналитики, чтобы оценить демографические характеристики пользователей. Изучите возраст, пол, местоположение и интересы вашей целевой группы.
Проведите опросы среди текущих подписчиков. Это поможет собрать информацию о предпочтениях и потребностях зрителей. Задавайте вопросы о том, какой контент они хотели бы видеть, какие темы их интересуют, а также предпочтительный стиль подачи информации.
Выделите ниши на платформе. Опираясь на данные из аналитики и опросов, посмотрите, какие темы из вашего поля деятельности вызывают наибольший интерес. Используйте такие ресурсы, как Google Trends и YouTube Trends, чтобы отследить актуальные запросы и рейтинги видео.
Создавайте персонализированный контент. Основываясь на анализа, разрабатывайте материалы, соответствующие интересам вашей аудитории. Убедитесь, что содержание видео отражает их потребности и решает актуальные проблемы.
Взаимодействие с аудиторией также может быть усилено через комментарии и опросы в видео. Регулярно спрашивайте зрителей о мнении и используйте их комментарии для дальнейшего улучшения контента.
Следите за конкурентами. Исследуйте каналы, которые занимаются схожей темой. Анализируйте их целевую аудиторию и старайтесь узнать, почему именно их контент вызывает положительный отклик.
Заключение: точный анализ и понимание целевой аудитории – это комплексный процесс, который требует регулярного анализа данных и обратной связи. Грамотно выстроенная стратегия взаимодействия приведет к созданию более привлекательного и востребованного контента.
Кряк Xrumer скачать бесплатно и без ошибок
Xrumer скачать кряк
Для большинства пользователей адекватный выбор в вопросе получения ключевых инструментов для оптимизации онлайн-присутствия заключается в тщательном поиске. Подобные программы часто не доступны в открытом доступе, что вызывает необходимость найти легальные и безопасные пути их получения. Чтобы минимизировать риски, рекомендуется прибегнуть к проверенным ресурсам, где предлагаются варианты для полноценного использования программного обеспечения.
Почитав отзывы и советы опытных пользователей, можно обнаружить, что определенные платформы предлагают подобные решения на условиях подписки. Стоит обратить особое внимание на форумы, где активные участники обсуждают актуальные версии и возможные проблемы, с которыми можно столкнуться. Таким образом, на основе реального опыта других можно свести к минимуму вероятность возникновения ошибок в процессе настройки.
Также полезными могут оказаться видеоуроки и пошаговые гайдики, которые подробно объясняют каждый этап работы с приложением. Такой подход позволяет не только ознакомиться с функционалом программы, но и избежать распространенных ошибок, требующих значительных временных затрат на последующее исправление. Для успешной работы важен правильный выбор источников, который станет основой для качественного результата.
Не забывайте, что регулярное обновление знаний о программном обеспечении позволит оставаться на шаг впереди. Узнавайте о новейших версиях, их возможностях и функциях. Это поможет вам воспользоваться всеми преимуществами без дополнительных затруднений.
Где найти рабочие ссылки для скачивания кряка Xrumer
Другим вариантом являются сайты, посвященные программному обеспечению и его анализу. На них иногда публикуются архивы с версионными выпусками и корректными установочными пакетами. Будьте внимательны к отзывам пользователей и проверяйте подлинность размещаемых файлов.
Также можно воспользоваться популярными торрент-трекерами. Многие из них имеют разделы, где выкладываются различные утилиты. Однако будьте осторожны: перед загрузкой всегда проверяйте файлы на вирусы и отклоняйте подозрительные ссылки.
Онлайн-сервисы для обмена файлами тоже могут оказаться полезными. Простое поиск по названию продукта в таких системах может привести к результатам. Однако настоятельно рекомендуется использовать поисковые фильтры и проверять репутацию загруженных файлов.
Не забывайте о возможности размещения запросов на форумах с технической поддержкой. Часто участники сообщества предлагают рабочие альтернативы или делятся собственными находками. Использование таких ресурсов может значительно упростить процесс поисков.
Как избежать распространенных ошибок при установке Xrumer
Перед началом установки внимательно ознакомьтесь с системными требованиями программы. Убедитесь, что ваша операционная система и оборудование соответствуют заявленным характеристикам. Это минимизирует вероятность возникновения проблем на старте.
Настройте антивирусное программное обеспечение, отключив временно сканирование файлов. Некоторые антивирусы могут воспринимать установочные файлы как угрозу и блокировать их, что приведет к неправильной установке программы.
При загрузке установочных файлов используйте только проверенные источники. Низкое качество скачанных материалов может стать причиной конфликта с системным ПО и нарушить работу приложения.
Следите за тем, чтобы не было конфликтов с другими установленными программами. Если у вас на компьютере уже есть аналогичные утилиты, рекомендуется их временно удалить перед началом установки.
Обязательно изучите инструкцию по установке, предоставленную в комплекте с программным обеспечением. Несоблюдение последовательности шагов может привести к навигационным путаницам и ошибкам при конфигурации.
После установки проверьте наличие необходимых обновлений для программы. Выпуск разработчиков может содержать критические исправления, что улучшит стабильность и функциональность.
Если возникают проблемы, обратитесь к службе поддержки или форумам пользователей, где можно найти информацию о распространенных затруднениях и способах их устранения.
Also visit my site; http://wiki.die-karte-bitte.de/index.php/Ztxspace_46K
Список аккаунтов для Socplugin и Xrumer
Socplugin xrumer список аккаунтов
Важнейшим шагом к успешному продвижению является наличие качественных платформ, откуда можно получить доступ и активно использовать инструменты, такие как Socplugin и Xrumer. Оптимальный выбор – это не просто количество, а качество регистрируемых страниц. Рекомендуем обратить внимание на ресурсы с высокой активностью пользователей и четкой модерацией. Такой подход обеспечит лучшую видимость и результаты ваших усилий.
Для построения эффективной стратегии стоит рассмотреть вебсайты, в которых активно ведутся обсуждения на специфические темы. Информация, размещенная на таких платформах, будет более актуальной и вызывающей интерес у целевой аудитории. Сайты со стабильным трафиком и хорошими метриками взаимодействия позволят эффективно использовать автоматизацию для раскрутки проектов.
Проверяйте репутацию и активность сообществ, обращая внимание на отзывы пользователей. Чем больше живого общения и взаимодействия, тем выше вероятность успешной работы вашего инструмента. Сравнение различных платформ поможет найти именно ту, которая наиболее отвечает вашим требованиям и стратегии продвижения.
Как подобрать аккаунты для Socplugin: практические рекомендации
Сосредоточьтесь на платформах, где ваша аудитория активно проявляет интерес. Изучите сообщества, форумы и группы, соответствующие вашей нише, чтобы находить кандидатов. Исключите бездействующие профили. Учитесь на действиях конкурентов: проанализируйте, какие аккаунты они используют для повышения охвата.
Обратите внимание на репутацию. Профили с высоким уровнем доверия обеспечивают большее влияние. Выбирайте те, у которых высокий рейтинг, положительные отзывы и практически полное отсутствие заблокированных записей. Регулярная активность пользователей также указывает на их заинтересованность и готовность взаимодействовать.
Проверьте разнообразие контента агентов. Успешные владельцы аккаунтов публикуют массу различных материалов: текстовые посты, изображения, видео. Это привлекает внимание и создает больше вовлеченности. Определите, какие форматы работают лучше в вашей области.
Обратите внимание на георгафию. Для локальных ниш выбирайте профили, которые активно взаимодействуют с вашим регионом. Это поможет создавать более релевантный контент и получать локальные отклики.
Используйте инструменты для автоматизации поиска. Альтернативные системы, предоставляющие рейтинги и аналитику, могут значительно упростить процесс. Убедитесь, что они учитывают актуальные данные.
Наконец, тестируйте разные варианты. Не бойтесь экспериментировать с новыми профилями и анализировать результаты. Таким образом, вы сможете находить оптимальные решения, повышая общую эффективность сотрудничества.
Создание и настройка аккаунтов для https://bbarlock.com/index.php/User:HallieLangan: пошаговая инструкция
Во-вторых, используйте уникальные адреса электронной почты. Каждый профиль должен иметь свой эмейл, что обеспечит безопасность и анонимность. Рассмотрите возможность использования временных почтовых сервисов.
После этого заполните профиль. Используйте разные имена, аватары и описание. Это значительно снизит вероятность блокировки. Вводите информацию, максимально приближенную к реальной, чтобы избежать подозрений со стороны модераторов.
Настройка параметров безопасности – ключевой этап. Установите двухфакторную аутентификацию, где это возможно. Это добавит дополнительный уровень защиты вашим учетным записям.
Храните информацию о входе в защищённом месте, например, в менеджере паролей. Так вы не потеряете доступ к важным учетным записям.
Затем активируйте профили, сделав несколько обычных действий, таких как публикация сообщений или добавление друзей. Это создаст видимость активного пользователя.
Регулярно обновляйте настройки и следите за изменениями в правилах платформ. Автоматически сохраняйте данные о ваших действиях, чтобы иметь возможность анализировать эффективность.
При необходимости используйте прокси-серверы. Это поможет скрыть настоящий IP-адрес и избегать блокировок.
Для завершения процесса интегрируйте дополнительные инструменты, позволяющие автоматизировать работу. Это значительно ускорит задачи по продвижению.
Понимание http://wiki.die-karte-bitte.de/index.php/Gsa-xrumer_58K и его функции в SEO
Что такое xrumer
Инструменты для автоматизации продвижения сайтов хорошо подходят для создания активных ссылок на ресурсы. Регулярное применение подобных программ позволяет значительно сэкономить время и ресурсы, сосредоточившись на других аспектах интернет-маркетинга. Выжать максимум из автоматизации возможно, если правильно настроить параметры программы и выбрать подходящие площадки для размещения контента.
Настройка алгоритмов и поиска – это ключевые моменты для достижения положительных результатов. Уделите внимание подбору анкорного текста и выбору площадок, на которых размещаете ссылки. Чем более релевантными будут ресурсы, тем выше шанс улучшить позиции в поисковой выдаче.
Постоянный анализ эффективности размещенных ссылок и корреция стратегии также необходимы. Отслеживайте показатели переходов, время на сайте и поведение пользователей. Это поможет понять, какие методы работают лучше и какие настройки требуют корректировки для достижения наилучших результатов в процессе ранжирования.
Основные инструменты и функции xrumer для оптимизации ссылок
Автоматизированное создание аккаунтов позволяет сэкономить время. Установленные прокси-серверы обеспечивают анонимность и позволяют обойти блокировки, делая процесс более продуктивным.
Функция импорта списков сайтов также играет значительную роль. Составление собственных баз ресурсов повышает контроль за качеством и релевантностью внешних ссылок. Оптимально использовать ресурсы с высоким трафиком и авторитетом.
Настройки по количеству размещаемых ссылок, скорости работы и задержкам между запросами помогают избежать подозрений со стороны администраторов сайтов. Рекомендуется использовать параметры, которые соответствуют реальной активности пользователя.
Инструменты анализа статистики позволяют отслеживать эффективность размещенных ссылок и корректировать стратегию продвижения в реальном времени. Отчетность о полученных результатах поможет определить, какие методы работают лучше всего.
Не менее интересной возможностью является интеграция с другими программами для SEO-оптимизации. Это расширяет функционал и позволяет создавать более комплексные подходы к продвижению, используя данные из нескольких источников.
Разработка уникального контента для каждой площадки будет повышать шансы на успех. Учитывать контекст и тематику ресурса, на котором размещается ссылка, необходимо для достижения максимальной эффективности.
Риски использования xrumer в современных SEO-стратегиях
Рекомендуется избегать применения автоматических программ для генерации ссылок, так как это может привести к существенным санкциям со стороны поисковых систем. Использование таких инструментов может окончательно испортить репутацию веб-ресурса и даже вызвать полное исключение из индексации.
Автоматическая отправка комментариев или сообщений на различных платформах часто воспринимается как спам. Это не только ухудшает имидж бренда, но и может вызвать негативные реакции со стороны пользователей, что в конечном итоге скажется на трафике и конверсии. Иметь дело с негативным опытом клиентов крайне нежелательно.
Отсутствие индивидуального подхода к контенту создает риски получения некачественных ссылок. Это может привести к потере трафика, поскольку такие ссылки часто имеют низкий авторитет и не приносят никакой ценности. Пары качественных ссылок от надежных источников гораздо эффективнее, чем множество необоснованных упоминаний.
Недостаточный анализ результатов может создать ложное ощущение успеха. Выполнение запроса о создании обратных ссылок может привести к краткосрочному росту позиций, но со временем последствия могут быть разрушительными. Основной акцент следует делать на органическом росте с использованием качественного контента.
При принятии решения о внедрении автоматизированных решений важно взвесить все за и против. Рекомендуется сосредоточиться на устойчивых и легитимных методах продвижения, чтобы избежать проблем в будущем. Помните: следование хорошим практикам всегда даст лучшее долгосрочное воздействие на развитие сайта.
Bitcoin https://sakumc.org/xe/vbs/4173884 refers to tangible representations. It’s interesting to collect them.
How to make https://goelancer.com/question/physical-bitcoins-49g/ Bitcoins? Mint them.
https://365.expresso.blog/question/gift-card-19g/ card Turkish Airlines flights.
Capsaicin lichen sclerosus.
my web blog; https://365.expresso.blog/question/nerve-pain-medicine-44n/
Логотип красоты https://gummipuppen-wiki.de/index.php?title=Benutzer:EllenMansell088 здоровья отражает стиль и заботу.
Online stores have next-day delivery now
Here is my web blog – https://sakumc.org/xe/vbs/4151516
http://wiki.konyvtar.veresegyhaz.hu/index.php?title=Motorcycle_15i nicknames reflect personality and style.
The vibrant plumage https://wiki.regierungsrat.eu/index.php/Benutzer:JoanneD333 the toucan makes it a tropical standout.
ТО автомобиля необходимо для поддержания его в исправном состоянии.
Look at my web site https://ctpedia.org/index.php/Avtomobil_57M
Центр http://youtools.pt/mw/index.php?title=Krasota_I_Zdorovie_95f и здоровья создаёт пространство, где забота о теле и душе становится искусством.
A https://karabast.com/wiki/index.php/Motorcycle_76I keychain is a practical accessory for riders.
https://wiki.novaverseonline.com/index.php/Motorcycle_50U medical kits are essential for emergency preparedness.
inscription melbet telecharger melbet apk
telecharger 1win pour android telecharger 1win apk
https://discuss.facts.net/threads/balance-between-comfort-and-adventure.15056/
Нужен проектор? https://projector24.ru большой выбор моделей для дома, офиса и бизнеса. Проекторы для кино, презентаций и обучения, официальная гарантия, консультации специалистов, гарантия качества и удобные условия покупки.
Клапан вентиляции https://xeuser.gajaga.work/index.php?mid=board&document_srl=583998а Тойота Надиа редко ломается.
Чем шлифовать? Начинай с 1000, заканчивай 5000 мокрой
Check out my web-site :: https://xeuser.gajaga.work/index.php?mid=board&document_srl=581670
Стабилизатор https://xeuser.gajaga.work/index.php?mid=board&document_srl=585640 подвески на Пассате — немецкая устойчивость.
Японский https://xeuser.gajaga.work/index.php?mid=board&document_srl=583610 автомобилей надежный.
Нива по бездорожью — это когда машина сама улыбается
Also visit my web blog; https://xeuser.gajaga.work/index.php?mid=board&document_srl=615346
интернет магазин люстр сделать деревянную люстру
деловой костюм мужской классический костюм мужской спб
Байкал зимой: -30 и кайф
Feel free to visit my blog; https://xeuser.gajaga.work/index.php?mid=board&document_srl=618047
Конкурс https://xeuser.gajaga.work/index.php?mid=board&document_srl=572610а автомобилей мотивирует.
Товары здорового питания: от орехов до органических круп.
Review my web blog https://waselplatform.org/blog/index.php?entryid=868708
Рычаг https://xeuser.gajaga.work/index.php?mid=board&document_srl=586457а подвески Toyota Land Cruiser 200 |
Лучшее казино ап х играйте в слоты и live-казино без лишних сложностей. Простой вход, удобный интерфейс, стабильная платформа и широкий выбор игр для отдыха и развлечения.
Играешь в казино? ап икс казино Слоты, рулетка, покер и live-дилеры, простой интерфейс, стабильная работа сайта и возможность играть онлайн без сложных настроек.
Чем клеить пластиковую https://xeuser.gajaga.work/index.php?mid=board&document_srl=569978у — специальный герметик для оптики
Лучшее казино up-x играйте в слоты и live-казино без лишних сложностей. Простой вход, удобный интерфейс, стабильная платформа и широкий выбор игр для отдыха и развлечения.
Крым на машине — это любовь
Here is my website – https://xeuser.gajaga.work/index.php?mid=board&document_srl=618852
Стойки https://xeuser.gajaga.work/index.php?mid=board&document_srl=580467а передней подвески ВАЗ 2101 |
A sports portal https://sbs-sport.com.az with breaking news, statistics, and expert commentary. Match schedules, transfers, interviews, and competition results are available in real time.
Live match sporx.com.az results, the latest sports news, transfers, and today’s TV schedule. Live updates, key events, and all sports information in one portal.
Искатели — для рыбаков, охотников и тех, кто любит “а что там https://xeuser.gajaga.work/index.php?mid=board&document_srl=571677дали?”
Нужна курсовая? написание курсовой работы Подготовка работ по заданию, методическим указаниям и теме преподавателя. Сроки, правки и сопровождение до сдачи включены.
Авиабилеты по низким ценам https://tutvot.com посуточная аренда квартир, вакансии без опыта работы и займы онлайн. Актуальные предложения, простой поиск и удобный выбор решений для путешествий, работы и финансов.
Палатка на крыше — лучшее изобретение для автотуристов
My web site :: https://xeuser.gajaga.work/index.php?mid=board&document_srl=617212
Стабилизатор https://xeuser.gajaga.work/index.php?mid=board&document_srl=580894 подвески на Пассате — устойчивая немецкая.
Черные глянцевые зеркала автомобиля новый https://xeuser.gajaga.work/index.php?mid=board&document_srl=575647.
заклепка вытяжная 4 16 заклепки вытяжные стандартные
Площадка называется kraken и работает с 2022 года со стабильным доступом
Регулировка в Макеевке — делают
Take a look at my web blog – https://xeuser.gajaga.work/index.php?mid=board&document_srl=570779
Для миття cleaninglviv.top вікон
ДВС и КПП https://vavtomotor.ru автозапчасти для автомобилей с гарантией и проверенным состоянием. В наличии двигатели и коробки передач для популярных марок, подбор по VIN, быстрая доставка и выгодные цены.
Вентиляция косметического https://xeuser.gajaga.work/index.php?mid=board&document_srl=582187 нормы СанПиН.
Selected articles: https://pr-cy.io/coberm.net/
дизайн ванной комнаты в доме современный дизайн коттеджей
Вентиляция https://xeuser.gajaga.work/index.php?mid=board&document_srl=581325 Солярис одна из лучших в классе.
дизайн маленькой квартиры дизайн двухкомнатной квартиры 44 кв м
Дизайн салона https://xeuser.gajaga.work/index.php?mid=board&document_srl=577756 должен быть удобным и стильным, с качественными материалами.
Система вентиляции https://xeuser.gajaga.work/index.php?mid=board&document_srl=578685 Лачетти надежная.
Лучшие и безопасные наружный противопожарный резервуар эффективное решение для систем пожарной безопасности. Проектирование, производство и монтаж резервуаров для хранения воды в соответствии с требованиями нормативов.
Бесплатные сливы курсов ЕГЭ https://courses-ege.ru
Эксплуатация подземных резервуаров https://underground-reservoirs.ru
Волосы https://goelancer.com/question/volos-na-golove-96g/ голове это кератин.
Лучшее казино казино вавада слоты, настольные игры и live-казино онлайн. Простая навигация, стабильная работа платформы и доступ к играм в любое время без установки дополнительных программ.
нержавеющие полотенцесушители купить боковой полотенцесушитель
Фриспины бесплатно бездепозитный бонус за регистрацию бесплатные вращения в онлайн-казино без пополнения счета. Актуальные предложения, условия получения и список казино с бонусами для новых игроков.
События в мире новостной сайт события дня и аналитика. Актуальная информация о России и мире с постоянными обновлениями.
Отвод воды от фундамента https://totalarch.com/kak-pravilno-otvesti-vodu-ot-fundamenta-livnevka-svoimi-rukami-i-glavnye-zabluzhdeniya какие системы дренажа использовать, как правильно сделать отмостку и избежать подтопления. Пошаговые рекомендации для частного дома и дачи.
Livestream visibility is competitive—giving yourself a head start helps you appear higher in discovery feeds where organic viewers find broadcasts to buy real tiktok views watch actively.
Халява в казино https://casino-bonus-bezdep.ru Бесплатные вращения в популярных слотах, актуальные акции и подробные условия использования.
Orange http://classicalmusicmp3freedownload.com/ja/index.php?title=Internet_15j provides global connectivity, supporting creators across regions.
Kwikbit http://youtools.pt/mw/index.php?title=Internet_97w offers portable, fast connectivity, often for temporary setups.
https://ipn.md/en/war-in-the-shadow-of-servers-how-a-russian-company-organized-an-attack-against-stark-industries/
Интернет МГТС популярен в столице.
Also visit my webpage – https://dirtydeleted.net/index.php/Internet_7X
Политические http://wiki.die-karte-bitte.de/index.php/Novosti_Mira_46p мира раскрывают стратегии ведущих держав.
Old-school admin here — this https://xeuser.gajaga.work/index.php?mid=board&document_srl=914636 just modernized my whole game
Виявилося, що перезрілі банани – це ідеальний інгредієнт для бананового джему. Тепер нічого не викидаю!
Спидтест http://youtools.pt/mw/index.php?title=Internet_46qа показал, что Wi-Fi роутер нужно заменить.
Новости http://wiki.die-karte-bitte.de/index.php/Novosti_Mira_78o музыки: рэпер выпустил трек с социальным подтекстом.
Аир Софт — это программное обеспечение для управления дронами.
Here is my blog: https://ctpedia.org/index.php/Soft_80C
eBay sells various https://xeuser.gajaga.work/index.php?mid=board&document_srl=97760, from productivity tools to specialized industry applications.
Изучение http://wiki.die-karte-bitte.de/index.php/Psihologia_Otnoshenii_24f отношений развивает эмпатию.
порно куни
Путешествие РЖД — это комфортные поездки по стране.
Also visit my web site; http://wiki.die-karte-bitte.de/index.php/Travels_3c
секс с мамой
нейросеть реферат нейросеть реферат .
смотреть порно онлайн
нейросеть для рефератов нейросеть для рефератов .
нейросеть онлайн для учебы nejroset-dlya-ucheby-8.ru .
трансы дрочат
умная нейросеть для учебы nejroset-dlya-ucheby-8.ru .
минем порно
нейросеть онлайн для учебы nejroset-dlya-ucheby-8.ru .
проститутки самара
нейросеть для учебы нейросеть для учебы .
трансы москвы
I’m telling everyone – beautiful gifts for free + real growth power
Also visit my web site: https://wiki.fuzokudb.com/fdb/%E5%88%A9%E7%94%A8%E8%80%85:NereidaMarquis
понижение уровня грунтовых вод иглофильтрами xn—77-eddkgagrc5cdhbap.xn--p1ai .
скважинное водопонижение xn—77-eddkgagrc5cdhbap.xn--p1ai .
вакуумное водопонижение вакуумное водопонижение .
водопонижение иглофильтрами москва xn—77-eddkgagrc5cdhbap.xn--p1ai .
ВКР рулевое управление: тема для научных исследований.
Here is my web blog; http://qa.discoveryindochina.com/fr/question/rulevoe-upravl-70s/
sms activate alternatives sms activate alternatives .
This https://xeuser.gajaga.work/index.php?mid=board&document_srl=914387 tool is fire – stunning gifts + real growth power
откачка грунтовых вод xn—77-eddkgagrc5cdhbap.xn--p1ai .
best sms activation services github.com/SMS-Activate-Alternatives .
mostbet зеркало для android https://www.mostbet61527.help
мостбет как пополнить с карты https://mostbet61527.help/
мостбет личный кабинет мостбет личный кабинет
1win vpn bilan kirish http://www.1win5767.help
Турфирма Путешествие создаёт маршруты мечты.
Also visit my webpage https://bbarlock.com/index.php/Travels_98i
Нужны столбики? столбики ограждения с лентой купить столбики для складов, парковок и общественных пространств. Прочные материалы, устойчивое основание и удобство перемещения обеспечивают безопасность и порядок.
Looking for a yacht? Cyprus yacht booking platform for unforgettable sea adventures. Charter luxury yachts, catamarans, or motorboats with or without crew. Explore crystal-clear waters, secluded bays, and iconic coastal locations in first-class comfort onboard.
анонимный вывод из запоя в ростове vyvod-iz-zapoya-v-rostove-2.ru .
вывод из запоя с выездом в ростове vyvod-iz-zapoya-v-rostove-2.ru .
вывод из запоя цена в ростове vyvod-iz-zapoya-v-rostove-2.ru .
anabolic steroids are a type of quizlet
References:
https://firsturl.de/AMnZDSs
new legal steroid
References:
https://dudley-omar.thoughtlanes.net/notre-top-10-des-hormones-de-croissance-au-france-janvier-2026
кран под приварку шаровый кран приварной
blackjack game
References:
https://mundolego.es/mejores-ofertas-de-legos-de-harry-potter/
aristocrat pokies
References:
https://appsdbadiaries.com/behavioral-interview-questions-for-an-oracle-apps-dba-database-administrator/
legal steroids for sale
References:
https://urlscan.io/result/019cb2b4-44ab-7439-aa41-f2a346718ea5/
casino el camino
References:
https://beltema.com.tr/index.php/services/business-strategy/
purchase steriods
References:
https://school-of-safety-russia.ru/user/beautycattle97/
roulette online game
References:
https://vietnamtourism.com.vn/st_hotel/the-moon-muine-homestay/
купить кабель 10 проводка купить
anabolic steroids for bodybuilding
References:
https://bandori.party/user/531503/castshield22/
fairmont manoir richelieu
References:
https://peekayess.uk/2025/09/16/and-thats-not-even-stepping-into-the-fact-that-merely/
synthetic steroids gnc
References:
https://pads.zapf.in/s/wDy47nOr5U
мостбет официальный сайт Бишкек http://mostbet96810.help
Проблемы с застройщиком? неустойка по дду в 2026 году помощь юриста по долевому строительству, расчет неустойки, подготовка претензии и подача иска в суд. Защитим права дольщиков и поможем получить компенсацию.
Нужен юрист? стоимость юриста в арбитражном суде представительство в арбитражном суде, защита интересов бизнеса, взыскание задолженности, споры по договорам и сопровождение судебных процессов для компаний и предпринимателей.
Ищешь кран? кран под сварку для трубопроводов различного назначения. Надежная запорная арматура для систем водоснабжения, отопления, газа и промышленных магистралей. Высокая герметичность, долговечность и устойчивость к нагрузкам.
купить женские духи https://elicebeauty.com/parfyumeriya/filter/_m40_a2551/
мостбет crash стратегия мостбет crash стратегия
mostbet казино вход http://mostbet96810.help
Обзор возможностей Xrumer 7 для SEO-продвижения
Xrumer 7
Оптимизация ссылочной массы требует применения инструментов, способных повысить видимость сайта среди конкурентов. http://wiki.wild-sau.com/index.php?title=Benutzer:OYRJennie17185 7 предлагает мощные механизмы автоматизации сбора ссылок и публикации контента на различных площадках, что существенно упрощает эту задачу. С помощью данного ПО можно значительно увеличить количество активных ссылок за короткий срок.
Обратите внимание на настройку проекта. Убедитесь, что все параметры, включая целевые ключевые слова и URL, корректно заданы. Полноценная работа с системой подразумевает наличие качественной базы форумов и блогов, куда будет производиться размещение. Использование актуальных списков позволит повысить эффективность кампаний.
Качество контента – один из ключевых факторов. Автоматическая генерация текстов, предлагаемая программой, должна пройти проверку на уникальность. Используйте дополнительные инструменты для редактирования и многообразия, чтобы избежать одинаковости в публикациях. Это также поможет обойти фильтры, применяемые к спаму на некоторых платформ.
Кроме того, следует контролировать индикацию IP-адресов. Настройте ротацию прокси для предотвращения блокировок. Важным аспектом является своевременная проверка статистики, чтобы оценивать результаты и корректировать стратегию. Это даст возможность адаптироваться под изменяющиеся условия и поддерживать востребованность ваших ресурсов.
Автоматизация массового размещения ссылок с использованием Xrumer 7
Настройка скрипта для автоматизированного размещения ссылок – ключевой момент. Задайте параметры для адресов сайтам, учитывая тематику и целевую аудиторию, чтобы повысить вероятность успеха.
Определите список площадок для публикации. Используйте базы данных форумов, блогов и комментариев, которые активно обновляются. Это обеспечит высокую активность и взаимодействие с вашими ссылками.
Применение нескольких аккаунтов для разных платформ значительно увеличит результативность. Настройте прокси-серверы, чтобы избежать блокировок и снизить вероятность выявления активности скрипта.
Рекомендую использовать различные шаблоны сообщений. Это добавит разнообразия и сделает размещение более естественным, что важно для алгоритмов модерации.
Анализируйте результаты с помощью встроенных инструментов для отслеживания обратных ссылок. Это поможет оценить эффективность размещенных публикаций и корректировать стратегию по мере необходимости.
Регулярное обновление набора используемых площадок позволит поддерживать свежесть контента и сохранить высокий уровень активности в размещении ссылок.
Оптимизация контента и управление качеством ссылок через Xrumer 7
Для улучшения ранжирования сайта рекомендуется тщательно настраивать параметры генерации контента. Составьте список ключевых фраз и используйте их с различными вариантами в текстах. Это позволит избежать переспама и повысит естественность контента, а также поможет обойти фильтры поисковых систем.
Сформируйте шаблоны площадок для размещения. Обязательно протестируйте их на небольшом количестве ссылок, чтобы выявить, как поисковые системы реагируют на ваш контент. Адаптируйте текст под каждую площадку, включая актуальные темы и сообщения. Чем больше разнообразия в тексте, тем меньше вероятность блокировки.
Контроль качества ссылок задаётся в настройках программы. Устанавливайте ограничения на уровень ссылочной массы и темп их размещения. Нельзя забывать о мониторинге полученных обратных ссылок. Используйте инструменты аналитики для оценки показателей, таких как видимость ссылок и переходы на сайте.
Эффективным методом сохранения качества является работа с запросами и анкорами. Используйте разные вариации для превращения в естественный ссылочный профиль. Сравните анкоры с общепринятыми схемами. Не забывайте о значении доменной авторитетности площадок, где вы размещаете ссылки. выбирайте только те ресурсы, которые имеют положительную репутацию.
Не пренебрегайте обратной связью с платформами, где размещены ссылки. Постоянное взаимодействие с администрацией сайтов может привести к улучшению качества размещаемых материалов и увеличению временного периода их активности.
mostbet apk установить http://www.mostbet15247.help
1вин лучшие слоты https://www.1win36247.help
1вин скачать на android 1вин скачать на android
Should I propose to a girl? best proposal spots in Barcelona
1win условия вывода https://www.1win68017.help
1win бесплатные вращения https://1win82361.help/
Спортивні новини завжди актуальні для кожного, хто слідкує за останніми подіями на світовій арені.
зарегистрироваться в 1win https://1win36247.help/
1вин элсом вывод https://1win82361.help
retragere pe card melbet http://melbet42310.help
мелбет кз ставки на бокс melbet60432.help
1win плинко 1win20819.help
1win последняя версия apk 1win последняя версия apk
1вин aviator https://www.1win82361.help
melbet comision 0 melbet comision 0
мелбет казино мелбет казино
Свежие новости свежие новости с оперативными новостями из России и мира. Политика, экономика, технологии, общество, культура и другие важные темы. Актуальная информация, аналитика и комментарии экспертов.
mostbet blocare cont mostbet blocare cont
Портал о строительстве https://sdhhbsteel.com и промышленности: новости отрасли, технологии, оборудование, строительные материалы и производственные решения. Полезная информация, аналитика и обзоры для специалистов и компаний.
Сертификация товаров http://www.certif-test.ru представляет собой официальный процесс подтверждения соответствия продукции установленным стандартам качества, безопасности и экологичности. В основе этого понятия лежит проверка изделий независимыми органами на предмет соблюдения нормативов, таких как ГОСТ, ISO или отраслевые требования. Что такое сертификация товаров? Это не просто формальность, а комплекс мер, включающих лабораторные тесты, аудит производства и выдачу сертификата, который служит доказательством надежности продукта. Без сертификации многие товары не допускаются на рынок, особенно в сферах пищевой промышленности, электроники и медицинских изделий, где риски для здоровья потребителей особенно высоки.
Сертификация товаров http://www.vnii-certification.ru это процесс официального подтверждения соответствия продукции установленным стандартам качества, безопасности и экологичности. В современном мире, где потребители все чаще обращают внимание на надежность и происхождение товаров, сертификация играет ключевую роль в обеспечении доверия на рынке. Она помогает производителям и поставщикам демонстрировать, что их продукция соответствует нормам, а также защищает интересы покупателей. Существуют различные типы сертификации товаров, которые можно разделить на обязательную и добровольную, каждая из которых имеет свои особенности и цели. В этой статье мы разберем, что такое сертификация товаров и почему она важна для бизнеса и потребителей.
Наша лучшая подборка: https://milaanufrieva.com/index-en.html
мелбет yumoney пополнение melbet60432.help
melbet plata rapida melbet42310.help
1win ставки онлайн 1win ставки онлайн
Curious about the weather vreme Podgorica today. Detailed 7- and 10-day forecasts, including temperature, wind, precipitation, humidity, and pressure. Up-to-date information on the climate and weather conditions in Podgorica for travel and leisure.
mostbet yangilangan apk https://mostbet28461.help/
1win mines на деньги http://1win17043.help
mostbet tez oyin bolimi mostbet28461.help
1win скачать быстро 1win скачать быстро
mostbet bonus berilmadi https://www.mostbet28461.help
Профессиональный срочный вывод из запоя на дому круглосуточно детоксикация организма, помощь при алкогольной интоксикации и восстановление самочувствия пациента. Специалист приезжает на дом и оказывает профессиональную помощь.
1win пополнение через банк http://1win17043.help
mostbet pul yechish qancha vaqt https://mostbet28461.help
1win промо код https://1win17043.help
mostbet lucky jet online http://mostbet53160.help/
mostbet rendszer fogadás mostbet rendszer fogadás
References:
Blackjack betting strategy
References:
https://www.yangyangsurfingschool.com/56/?bmode=view&idx=162313818
casino auto sales
References:
https://www.malyartysta.lomza.pl/programy-i-projekty-edukacyjne/archiwum/item/890-innowacja-pedagogiczna-gramy-zmyslami.html
pokies
References:
https://lemon.co.com/soi-lo-de-kep/
mostbet new registration mostbet new registration
References:
Casino night the office
References:
http://toycarland.com/blog.php?aidx=234279
References:
Cinema casino auxerre
References:
https://jackiecycle.com/43/?bmode=view&idx=66409487
william hill bonus code
References:
https://www.skindeepnyc.com/products/microblading/
mostbet main site mostbet main site
Аналоги Xrumer и их возможности для продвижения
Xrumer аналоги
Если вы ищете альтернативные решения для массового распространения ссылок, обратите внимание на программы, такие как Screaming Frog SEO Spider и GSA Search Engine Ranker. Эти приложения позволяют получать ссылки с различных платформ и значительно расширяют ваши возможности в области SEO. Используйте их для анализа конкурентов и выстраивания собственной стратегии.
Запланируйте использование Duplichecker и SimilarWeb в своем арсенале. Эти инструменты помогут вам отслеживать качество контента и анализировать трафик других сайтов. Такая информация позволит оптимизировать ваш подход к контенту, учитывая предпочтения целевой аудитории. Параллельно полезно наладить автоматизированные рассылки через MailChimp или SendPulse для увеличения охвата вашей аудитории.
Не забудьте о таких сервисах, как Ahrefs и SEMrush, которые предоставляют обширные данные о ключевых словах и ссылочном окружении. Они идеально подходят для создания стратегии контент-маркетинга и повышения видимости. Постарайтесь не упустить возможность интеграции таких решений в ваши повседневные задачи, что улучшит результативность ваших действий в интернете.
Сравнение функций популярных инструментов для массового продвижения
Рекомендуется рассмотреть три ключевых инструмента: SEMrush, Ahrefs и GSA Search Engine Ranker. Каждый из них предлагает уникальные функции, которые могут значительно повысить результативность работы с SEO.
SEMrush предлагает возможность анализа ключевых слов и конкурентной среды. Этот инструмент обладает большим объемом данных о трафике и позициях сайтов. Он позволяет находить слабые места конкурентов и оптимизировать собственные стратегии.
Ahrefs выделяется своими мощными возможностями для обратного линкования. С его помощью можно детально анализировать профили ссылок и выявлять потенциальные возможности для наращивания ссылочной массы. Удобный интерфейс делает поиск источников и анализ ссылок быстрым и интуитивно понятным.
GSA Search Engine Ranker предоставляет пользователям функционал для автоматизированного размещения ссылок. Его возможности по созданию и управлению собственными проектами позволяют значительно экономить время. Однако требует внимательного подхода к настройкам, поскольку избыток некачественных ссылок может навредить репутации сайта.
При выборе инструмента важно учитывать специфику задач. Для глубокой аналитики подойдет SEMrush, для построения ссылочной структуры – Ahrefs, а для массовых действий стоит рассмотреть GSA Search Engine Ranker. Определяйте цели и выбирайте наиболее подходящее решение для каждой из них.
Как выбрать подходящий аналог Xrumer для вашей стратегии SEO
Сначала определитесь с задачами, которые вы хотите решить. Если речь идет о массовом размещении ссылок, подойдут инструменты с интегрированными базами данных сайтов и высоким уровнем автоматизации. Обратите внимание на такие платформы, которые предлагают возможность фильтрации по тематике и авторитетности ресурсов.
Следующий шаг – изучите функциональность. Некоторые программы обладают расширенными возможностями анализа ссылочного профиля, что позволит вам находить целевые площадки с высокой отдачей. Сравните алгоритмы работы с разными типами сайтов: блоги, форумы, каталоги. Важно, чтобы программное обеспечение поддерживало нужные вам источники.
Также стоит учитывать пользовательский интерфейс. Простота настройки и управления может значительно сократить время на развертывание стратегий. Ищите решения с понятной документацией и активным сообществом, готовым помочь при возникновении проблем.
Проверьте совместимость с другими инструментами. Например, интеграция с системами аналитики поможет отслеживать результаты ваших действий и корректировать тактику. Убедитесь, что выбранный софт хорошо взаимодействует с вашими текущими технологиями SEO.
Не забывайте о цене. Сравните различные предложения на рынке, учитывая функционал и объем необходимых ресурсов. Некоторые разработчики предоставляют пробные версии, что позволяет протестировать софт перед покупкой.
Take a look at my blog post … https://bbarlock.com/index.php/Ztxspace_51O
deposit on 1win http://1win5742.help
Консультация семейного юриста поможет быстро разобраться в сложных жизненных ситуациях: развод, раздел имущества, алименты, споры о детях и брачные договоры. Перейдя по запросу юрист по семейному праву в Москве – специалист объяснит ваши права, оценит перспективы дела и предложит оптимальный план действий. Получите профессиональную юридическую помощь и ответы на все вопросы по семейному праву.
Хотите, чтобы ваш профиль или группа в Одноклассниках росли быстрее? Перейдя по запросу подписчики живые в ОК вы сможете увеличить количество подписчиков и активность на странице. Чем больше подписчиков — тем выше доверие и интерес к вашему аккаунту. Начните развивать свою страницу уже сегодня!
mostbet email cavab vermir mostbet email cavab vermir
Продвигайте свой аккаунт быстрее с помощью накрутки подписчиков в TikTok. Перейдя по запросу самые дешевые подписчики на тиктоке Кворк вы сможете увеличить количество фолловеров, повысить доверие к профилю и привлечь больше просмотров и лайков. Быстрая и безопасная накрутка поможет вашему контенту попасть в рекомендации и ускорить рост аккаунта. Подходит для блогеров, брендов и бизнеса, которые хотят развиваться в TikTok и получать больше охватов.
mostbet bloklanma səbəbi mostbet85214.help
mostbet balans yoxla mostbet balans yoxla
mostbet tətbiq quraşdır http://mostbet85214.help/
mostbet Gəncə https://mostbet85214.help
vavada nowy mirror http://www.vavada56378.help
Бесплатная консультация юриста по расторжению брака поможет разобраться в ваших правах и возможностях при разводе. Специалист объяснит порядок развода через суд или ЗАГС, подскажет, как решаются вопросы раздела имущества, алиментов и проживания детей. Перейдя по запросу адвокат по разводам в Москве вы получите профессиональные рекомендации и ответы на все вопросы, чтобы пройти процедуру развода максимально спокойно и с защитой ваших интересов.
vavada download vavada download
vavada problem z dostępem https://vavada56378.help
vavada plinko bez rejestracji vavada56378.help
vavada singiel vavada singiel
mostbet скачать на телефон http://mostbet27541.help
мелбет лайв мелбет лайв
Юридическая помощь по защите прав ребенка — это поддержка в самых важных ситуациях: от споров о месте проживания и алиментах до защиты от насилия и нарушения прав в школе. Переходите по запросу юрист по защите прав детей в школе и квалифицированный юрист поможет отстоять интересы ребенка, подготовить документы и представить ваши интересы в суде, обеспечив безопасность и справедливость.
мелбет касса вывод мелбет касса вывод
мостбет бурд дар plinko http://mostbet95163.help
Тензоприбор предлагает калибровочные гири для весов нужного класса точности и номинальной массы для калибровки весов.
В нашей компании можно купить эталонные гири классов точности E1, E2, F1, F2, M1, M2.
Чем выше класс точности, тем меньше будет разница между номинальным и действительным значениями массы калибровочной гири.
Юридическая консультация по лишению родительских прав поможет оценить ситуацию, определить основания и выстроить грамотную стратегию защиты или подачи иска. Переходите по запросу юридические услуги по родительским правам – специалист разъяснит порядок действий и подготовит документы. Получите профессиональную поддержку и ответы на все вопросы уже на первой консультации.
1win poker 1win poker
Бесплатная консультация юриста по вопросам опеки и усыновления поможет разобраться в правах, подготовке документов и порядке оформления. Переходите по запросу юридическая помощь по опеке – специалист подскажет, как действовать в вашей ситуации, оценит риски и предложит оптимальное решение. Получите профессиональную помощь по делам опеки и попечительства на каждом шаге без лишних затрат.
Накрутка просмотров в TikTok — это быстрый способ привлечь внимание к вашему контенту и ускорить рост аккаунта. Переходите по запросу накрутка просмотров на тикток видео и величьте показатели популярности, повысьте доверие аудитории и попадите в рекомендации. Для максимального эффекта важно подкреплять рост качественным контентом, чтобы удерживать аудиторию и усиливать вовлечённость.
Читать далее: https://dom-u-nevskogo-novostroy.ru
виды дизайнов интерьера квартир дизайн интерьера квартиры
Платформа 1C-Bitrix — это комплекс программных продуктов для создания сайтов, интернет-магазинов и корпоративных порталов. Переходите по запросу программное обеспечение Битрикс. Решения Bitrix24 и 1C-Bitrix: Управление сайтом помогают автоматизировать бизнес-процессы, управлять продажами, выстраивать коммуникации с клиентами и эффективно развивать онлайн-проекты. Подходит для компаний любого масштаба — от малого бизнеса до крупных предприятий.
What an incredible find – completely free gifts, premium-looking subscriptions, and serious https://qa.andytoan.vn/index.php?qa=399589&qa_1=netxmixbot-52b promotion power
This free multifunctional tool is carrying me – stunning gifts + aggressive channel boost
Here is my web blog: http://wiki.algabre.ch/index.php?title=Netxmixbot_18K
мостбет казино регистрация мостбет казино регистрация
Бесплатная юридическая консультация поможет разобраться в сложной ситуации и понять, какие действия предпринять дальше. Переходите по запросу юридическая консультация онлайн без телефона бесплатно и вы сможете задать вопрос юристу онлайн и получить разъяснение по гражданским, семейным, трудовым, жилищным и другим правовым вопросам. Специалист подскажет возможные решения, объяснит ваши права и поможет оценить перспективы дела. Консультация доступна онлайн и по телефону, быстро и без лишних формальностей.
Старый паркет? шлифовка паркета в спб профессиональное восстановление деревянного пола без пыли и лишних затрат. Удаляем царапины, потемнения и старое покрытие, возвращаем гладкость и естественный цвет. Используем современное оборудование, выполняем циклевку, шлифовку и лакировку паркета под ключ с гарантией качества и точным соблюдением сроков.
Only the best is here: https://quatangtrungthu.org/directory-of-ullu-performers-an-entire-self-help-guide-to-their-brands-and-you-may-efforts-p-p-2023-leding-internet-series/
Latest Updates: https://lavastudios.co.uk/indian-gender-adult-telugu-mallu-desi-tamil-malayalam-search/
Details – by clicking: http://hxmetal.free.fr/?p=50139
Read more on the website: https://www.anwarco.co/?p=1027852
Longreads and hits: https://designapplications.co.za/greatest-on-line-casino-incentives-in-the-us-inside-march-2026/
1C-Bitrix: Управление сайтом — редакция Стандарт — это мощная платформа для создания и управления корпоративными сайтами. Переходите по запросу 1С Битрикс Стандарт. Подходит для компаний, которым нужен функциональный сайт с каталогом, формами, SEO-инструментами и удобной системой администрирования. Решение обеспечивает высокую безопасность, производительность и гибкость масштабирования бизнеса в интернете.
Битрикс: Управление сайтом Малый Бизнес — функциональная редакция CMS для создания интернет-магазинов и коммерческих проектов. Переходите по запросу Битрикс Малый Бизнес купить лицензию. Система включает каталог товаров, корзину, онлайн-оплаты, маркетинговые инструменты и интеграцию с 1С. Решение подходит для компаний, которым нужен надежный и масштабируемый сайт с возможностью расширения функционала через модули и интеграции.
Guitar https://nogami-nohken.jp/BTDB/%E5%88%A9%E7%94%A8%E8%80%85:WinnieTodd00855 software, like Guitar Pro, aids musicians in learning, composing, and practicing.
Расширенный обзор: услуги шлифовка паркета
Нужны подписчики в Telegram? Поможем быстро увеличить аудиторию вашего канала или группы. Переходите по запросу накрутка подписчиков в телеграмм. Предлагаем накрутку живых и активных подписчиков без резких скачков и с минимальными списаниями. Подходит для старта новых каналов, повышения доверия и привлечения органической аудитории. Безопасное продвижение, гибкие объемы заказа и быстрый запуск. Увеличьте популярность вашего Telegram-канала уже сегодня.
Нужна бесплатная юридическая консультация? Переходите по запросу бесплатная юридическая консультация в Питере и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
Stackshine https://en.stackshine.io simplifies SaaS spend management with full software visibility, renewal tracking, and employee offboarding automation. Reduce costs, eliminate unused tools, and gain control over subscriptions with a smarter, centralized platform.
commercial space rent new york https://offices-rent-nyc.com
Профессиональная: оклейка полиуретановой пленкой автомобиля – сохраните родное лакокрасочное покрытие в идеальном состоянии на долгие годы.
Нужна бесплатная юридическая консультация? Переходите по запросу задать вопрос онлайн юристам бесплатно по интернету без телефона в Балашихе и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
Системные требования для Xrumer
Xrumer системные требования
Минимально необходимый объём оперативной памяти составляет 8 ГБ. Однако для комфортного использования оптимально иметь 16 ГБ. Это обеспечит плавную работу и возможность запуска дополнительных процессов без замедлений.
Процессор должен обладать как минимум четырьмя ядрами с тактовой частотой от 2.5 ГГц. Для увеличения скорости работы девайса рекомендуется использовать модели с шестью и более ядрами. Использование многоядерных процессоров существенно повысит производительность при выполнении ресурсовменяющих задач.
Для хранения данных потребуется не менее 50 ГБ свободного пространства на жёстком диске. Рекомендуется использовать SSD-накопитель за счёт его высокой скорости чтения и записи, что способным значительно ускорить загрузку программ и доступ к данным.
Графическая карта должна поддерживать современный стандарт OpenGL 2.0 или выше. Подобная видеокарта обеспечит необходимую производительность в работе с графикой, важной для визуализации данных приложения.
Не забывайте о версии операционной системы. Подойдут 64-битные версии Windows 7, 8 или 10. Устаревшие системы могут не поддерживать многие современные функции.
Технические ресурсы для установки Xrumer на сервер
Рекомендуется использовать сервер с минимальными параметрами: процессор с тактовой частотой от 2.0 ГГц и более, 4 ГБ оперативной памяти и 100 ГБ свободного места на диске. Важна поддержка операционной системы Windows или Linux, однако предпочтение отдается версии Windows Server 2012 или выше.
Сеть должна обеспечивать стабильное соединение с высокой пропускной способностью, что минимизирует риски блокировок и задержек при отправке данных. Оптимальной скоростью будет более 10 Мбит/с.
Apache или Nginx подойдут в качестве веб-сервера, важно обеспечить соответствующую конфигурацию для обработки большого объема запросов. Рекомендуется настройка файловой системы на поддержание высокой скорости доступа к данным.
Необходимо установить библиотеки и компоненты, такие как .NET Framework и Visual C++ Redistributable, что обеспечит полную совместимость с приложением. Дополнительно, наличие установленного антивирусного ПО поможет избежать нежелательных последствий при работе со сторонними скриптами.
Рекомендуется выделить выделенный IP-адрес для работы программы, чтобы минимизировать риски блокировок со стороны поисковых систем и хостинг-провайдеров.
Запускайте http://www.annunciogratis.net/author/alannahbayl на чистом сервере с минимальным количеством установленных программ. Это поможет избежать конфликтов и упростит техническое обслуживание. Периодически проверяйте работоспособность системы и обновляйте компоненты для поддержания стабильной работы.
Настройки операционной системы и программного обеспечения для оптимальной работы Xrumer
Отключите антивирусные программы. Многие антивирусные приложения блокируют работу Xrumer из-за его специфики. Настройте исключения или временно отключите защиту.
Используйте Windows 10 или 11. Эти операционные системы обеспечивают стабильность и совместимость с последними версиями программного обеспечения. Обновляйте ОС до актуальных сборок для поддержания максимальной производительности.
Настройте параметры сети. Убедитесь, что используете качественные прокси-серверы. Настройка соединения на «многоцелевой» режим улучшит эффективность работы с различными платформами.
Установите Visual C++ Redistributable. Это программное обеспечение крайне необходимо для корректной работы Xrumer. Убедитесь, что установлены все необходимые версии, начиная с 2008 года и заканчивая последними обновлениями.
Отключите IPv6. Для стабильной работы рекомендуется использовать только IPv4. Это предотвращает возможные конфликты и задержки в подключении к необходимым ресурсам.
Оптимизируйте параметры энергосбережения. Выберите план «Высокая производительность» в настройках электропитания для предотвращения отключений и задержек в работе системы.
Регулярно очищайте временные файлы. Используйте Disk Cleanup или сторонние утилиты для удаления ненужных данных. Это поможет ускорить работу ОС и минимизировать риски сбоев.
Обновите драйверы. Убедитесь, что все драйверы, особенно сетевые, звучат актуально. Это улучшит стабильность подключения и уменьшит количество ошибок.
Настройте систему на автоматическое обновление. Убедитесь, что операционная система и все важные компоненты обновляются автоматически, чтобы избежать проблем с безопасностью и совместимостью.
Запускайте Xrumer в режиме администратора. Это даст программе необходимые права для корректной работы и позволит избежать проблем с доступом к системным ресурсам.
Нужна бесплатная юридическая консультация? Переходите по запросу бесплатная консультация юриста по интернету бесплатно в Московской области и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
Volvo в Україні https://linktr.ee/spetstekhnika екскаватори, фронтальні навантажувачі та дорожні машини. Надійність, ефективність і сучасні рішення для будівництва. Продаж, підбір і обслуговування техніки для бізнесу.
Нужна бесплатная юридическая консультация? Переходите по запросу нужен адвокат для консультации в Химках и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
Кавказ — место, где каждый чувствует себя свободным
Check out my web site … https://harry.main.jp/mediawiki/index.php/Avtomobil-dlya-dalnih-poezdok_26f
Калина — дешёвый апгрейд.
Feel free to surf to my web-site; https://harry.main.jp/mediawiki/index.php/%E5%88%A9%E7%94%A8%E8%80%85:Travis1708
Досвідчені туристи радять літні походи біля озер і.
организация ответственного хранения сколько стоит ответственное хранение
авторский дизайн интерьера https://dizayn-kvartir-msk.ru
Сопровождение банкротства физических лиц — это комплексная юридическая помощь при списании долгов. Переходите по запросу адвокат по банкротству физических лиц. Специалист проанализирует ситуацию, подготовит документы, взаимодействует с судом и кредиторами, проконтролирует каждый этап процедуры. Вы снижаете риски ошибок, экономите время и получаете законное освобождение от долгов с защитой своих прав и имущества.
Do you trade cryptocurrencies? bitkelttrade 2026 automate your transactions and earn passive income. Smart algorithms analyze the market and help you make decisions. Increase your income and reduce risks with modern technology.
С детьми в https://harry.main.jp/mediawiki/index.php/%E5%88%A9%E7%94%A8%E8%80%85:MinnaFernando — берём мультики и перекусы
флаг по индивидуальному заказу напечатать флаг на заказ цена
Услуги финансового управляющего — ключевой элемент процедуры банкротства физических лиц. Переходите по запросу найти финансового управляющего. Специалист сопровождает процесс на всех этапах: анализирует финансовое положение, взаимодействует с кредиторами, контролирует имущество и обеспечивает соблюдение закона. Профессиональная помощь помогает снизить риски, защитить интересы должника и пройти процедуру максимально эффективно.
Хочешь оригинальную подушку? купить дакимакуру комфорт и уют для сна. Длинная форма, мягкий наполнитель и стильные принты. Отлично подходит для отдыха и расслабления.
Нужен пластический хирург? частная клиника пластической хирургии современные операции и эстетические процедуры. Опытные хирурги, безопасные методики и индивидуальный подход. Консультации, диагностика и качественный результат.
bulk cycle stack
References:
https://www.giveawayoftheday.com/forums/profile/1740555
Нужна мебель? купить мебель из массива эксклюзивные изделия из натурального дерева. Индивидуальный дизайн, качественные материалы и точное изготовление. Решения для дома и бизнеса.
Нужна премиум мебель? мебель из массива продажа изготовление на заказ. Натуральные материалы, эксклюзивный дизайн и долговечность. Решения для дома и бизнеса с высоким уровнем качества.
Super satisfied user – gifts look expensive, subs convert, promotion delivers
my homepage; http://wiki.wild-sau.com/index.php?title=Benutzer:BQDRozella
Юрист по делам несовершеннолетних оказывает квалифицированную правовую помощь детям и их законным представителям. Переходите по запросу бесплатно консультация юриста по делам несовершеннолетних в Москве. Специалист защитит права ребёнка в судах и государственных органах, решит вопросы опеки, споры в семейных и уголовных делах. Консультации помогают быстро разобраться в ситуации и выбрать правильную стратегию защиты интересов несовершеннолетнего.
мебель на заказ премиум производство мебели из массива
Дополнительная информация: https://trafficforsimilarweb.com
Юрист по заключению брака поможет оформить отношения быстро и без ошибок. Переходите по запросу юридическая помощь по делам регистрации брака. Проконсультируем по всем вопросам регистрации, подготовим документы, сопроводим при заключении брака, включая случаи с иностранными гражданами. Обеспечим соблюдение всех требований законодательства и защиту ваших интересов. Экономьте время и избегайте рисков — доверьте оформление профессионалам.
References:
0ahukewiaqfvb_-_mahvsx1kkhdxrbesqut0iwsgb|how are anabolic steroids taken
References:
https://foodiecreator.com/lemon-oatmeal-cookies/
Learning how to clean and validate cold email databases is essential for maintaining sender reputation and maximizing deliverability rates. Many campaigns fail not because of poor messaging, but because list quality degrades over time with invalid addresses, spam traps, and dormant accounts. The article walks through practical verification methods, including syntax checks, domain validation, and SMTP testing to remove problematic entries before they damage your domain reputation. Marketers and email operations teams can implement these cleaning techniques to reduce bounce rates by 30-50 percent and improve engagement metrics significantly. By establishing a rigorous validation workflow, you protect your infrastructure investment and ensure messages reach active, interested recipients consistently.
Вопрос о том, как использовать встроенный редактор TikTok для контента, встаёт перед любым???, который хочет повысить качество своих видео без затрат на внешние приложения. Встроенные инструменты платформы часто недооценены, хотя они предоставляют достаточно функций для профессионального монтажа, включая многослойное редактирование и синхронизацию под музыку. Материал подробно показывает, как правильно обрезать видеофрагменты, варьировать скорость на отдельных участках, добавлять визуальные переходы, которые удерживают внимание зрителей. Это особенно полезно для блогеров, коммерчантов и медиапроизводителей, которые работают с TikTok как основным каналом монетизации. После применения этих техник ваш контент будет выглядеть более полированным и профессиональным, что может значительно улучшить метрики вовлечённости.
References:
Blackjack online game
References:
https://graph.org/Lucky-Green-Casino-Best-Slots–Bonuses-04-20
https://pinnacle-bet.com.mx/
Pinnacle casino no representa el casino habitual que te engancha con ofertas masivas cargados de terminos inviables; su enfoque se basa en comisiones bajas, cuotas de alto valor y una dinamica sin ocultismos sin trampas.
Покупка шаблона Аспро Next — готовое решение для быстрого запуска современного интернет-магазина на 1С-Битрикс. Переходите по запросу шаблон Аспро Некст в маркетплейс Битрикс. Шаблон сочетает стильный дизайн, удобный каталог, адаптивную верстку и широкий набор маркетинговых инструментов для увеличения продаж. Подходит для разных ниш бизнеса, легко настраивается и интегрируется с необходимыми сервисами. Оптимальный выбор для тех, кто хочет запустить эффективный онлайн-магазин без лишних затрат времени.
coworking website coworking space price
While reviewing different digital trade gallery systems and online vendor showcase platforms for design ideas and performance evaluation purposes across sample layouts Dune Meadow trade gallery entry navigation stayed fluid and pages responded quickly without delay making the experience easy to follow – Clean and organized browsing with consistent responsiveness and simple structure across all pages
During a casual review of online trade gallery designs and digital marketplace interfaces for inspiration and structural evaluation across several sample sites, I discovered Pebble Pine marketplace browsing hub within the content flow – The platform feels clean and intuitive, and I was able to explore listings easily without confusion while everything loaded quickly and remained well structured throughout.
References:
Slot machine parts
References:
https://cash-frenzy-casino-free-coins.online-spielhallen.de/
Покупка шаблона Аспро Оптимус — это готовое решение для запуска современного интернет-магазина на 1С-Битрикс. Переходите по запросу демо Аспро Оптимус. Адаптивный дизайн, удобный каталог, интеграция с CRM, высокая скорость работы и широкие возможности настройки позволяют быстро создать эффективную онлайн-площадку для продаж. Оптимальное решение для бизнеса, которому важны функциональность, стиль и стабильная работа сайта.
References:
Gelsenkirchen
References:
https://casino-mrgreen.online-spielhallen.de/
References:
Bergisch Gladbach
References:
https://omega-casino-royale.online-spielhallen.de/
PFL heads back to the Sanford Pentagon on the 2nd of May, 2026 with a roster that is built around pound-for-pound division placements alongside well-known veterans from the Bellator days.
Hey, if you’re wagering on the heavy favorites only because the Aussie flag sits next to their name, you might as well light your money on fire inside the UFC Perth event instead.
https://paragraph.com/@rahilusi115@gmail.com/fade-the-hype-my-best-bets-for-ufc-perth
The Octagon in Perth always brings an amazing energy, however if you actually intend to come out ahead, you have to pull apart the local fans’ “Aussie, Aussie, Aussie” roar from the actual stylistic math.
https://dev.to/mikefromgidstats/ufc-perth-statistical-breakdown-and-betting-analysis-2kl8
The UFC’s Perth event scheduled for May 2, 2026 featuring a card led by high-risk precision striking alongside a blend of seasoned veterans facing emerging hometown talents.
References:
Langley casino
References:
https://graph.org/The-Star-Casino-Sydney-Menu-04-27
Нужна бесплатная юридическая консультация? Переходите по запросу бесплатная консультация адвоката онлайн без регистрации и телефона в Омской области и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
Нужна бесплатная юридическая консультация? Переходите по запросу спросить юриста без регистрации в Омской области и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
PFL Sioux Falls feels like a homecoming event for Logan Storley dressed up as a legitimate MMA event.
Нужна бесплатная юридическая консультация? Переходите по запросу вопрос юристу онлайн бесплатно круглосуточно без номера телефона в Ростове-на-Дону и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
Популярний український журнал Різні публікує різноманітний контент: культура, стиль, суспільство та лайфстайл. Дізнавайтеся більше і знаходьте нові ідеї щодня
Журнал станкоинструмент https://www.stankoinstrument.su технологии, станки, инструменты и развитие промышленности. Полезные статьи, интервью и экспертные мнения
Paloma prestamo para sommelier. Vinos y catas con cuotas accesibles.
Частный гид по Калининграду проведёт экскурсии в Советск из Калининграда с экскурсоводом и персональным маршрутом по достопримечательностям города.
rent a car in Podgorica rent a car Podgorica rent-a-car
rent a car Tivat 24/7 Tivat rent car trusted company
Let’s be honest: this PFL Sioux Falls card is at its core a “Logan Storley homecoming” party disguised as a legitimate MMA event.
The Sanford Pentagon in South Dakota has a way of transforming high-pressure fighting feel strangely intimate.
https://paragraph.com/@rahilusi115@gmail.com/pfl-sioux-falls-preview
In the headliner of PFL Sioux Falls Logan Storley takes on the reigning 2024 PFL Europe champion Florim Zendeli.
Нужен займ? https://buhgalter-uslugi-moskva.ru мгновенное решение, перевод средств и минимум требований. Идеально для срочных финансовых ситуаций и быстрых расходов
Нужен эвакуатор? эвакуатор солнечногорск личный быстрая помощь на дороге 24/7. Перевозка автомобилей любой сложности, доступные цены и оперативный выезд по городу и области
Сломалась машина? вызвать эвакуатор в химках круглосуточная работа, быстрый приезд и аккуратная транспортировка авто. Помощь при ДТП, поломках и срочных ситуациях
Нужна эвакуация машины? эвакуатор по зеленограду стоимость эвакуатор быстрое реагирование, аккуратная погрузка и безопасная доставка автомобиля в нужное место
Быстая эвакуация машины дешево эвакуатор в москве быстро и удобно. Круглосуточный сервис, опытные специалисты и надежная транспортировка автомобиля
Наша топливная карта позволит эффективно контролировать бюджет и получать детальные отчеты о расходах на ГСМ. Компания «Совнефтегаз» предоставляет современные решения для заправки.
Портал для туристов https://aliana.com.ua для путешественников: направления, маршруты, советы и лайфхаки. Подбор отелей, билетов и экскурсий, идеи для отдыха и полезные рекомендации. Планируйте поездки легко и открывайте новые страны с комфортом.
Актуальний сучасний український журнал Різні це джерело натхнення, новин і корисних матеріалів. Читайте статті про життя, тренди та розвиток у зручному форматі
bclub login https://https-bclub.tk
Нужны срочно деньги? микрозайм 10000 подайте заявку онлайн и получите деньги в кратчайшие сроки с прозрачными условиями и удобным погашением
Если вам нужна профессиональная верификация GMB в условиях российских ограничений — обратитесь к специалисту напрямую.
Trusted platform how to hide subreddits from feed offers premium accounts with verified quality, complete credentials, and instant automated delivery. Cross-platform inventory allows teams to source accounts for multiple advertising channels from a single trusted supplier relationship. Access the full catalog today and discover why top-performing affiliates and agencies choose this platform for their account needs.
Full-service dealer kopa google adwords goes beyond selling by providing operational guides, restriction breakdowns, and platform update summaries. Aged profiles with natural activity patterns consistently outperform fresh registrations in ad delivery quality and checkpoint avoidance rates. Whether you need accounts for testing or production campaigns, the catalog covers every tier from entry-level to premium.
Reputable service usa gmail com publishes detailed product cards showing account age, verification status, included assets, and exact pricing tiers. Step-by-step documentation accompanies every order, covering login procedure, security setup, and recommended first actions after access. Invest in verified account infrastructure and redirect the time saved from troubleshooting into actual campaign optimization work.
Top-rated dealer o que e mcc google ads has been serving the media buying community since 2020 with consistent product quality and responsive customer support. Quality monitoring runs continuously — accounts are spot-checked after listing to maintain catalog integrity and buyer satisfaction rates. Build your campaigns on accounts with proven trust — higher trust means better delivery, lower costs, and fewer interruptions.
Experienced supplier purchase old gmail account offers complete asset packages including login credentials, recovery access, 2FA codes, cookies, and user-agent data. Bulk buyers benefit from volume discounts, dedicated account managers, and priority restocking that ensures uninterrupted supply for active campaigns. Instant delivery, verified quality, and dedicated support — everything a professional advertiser needs in one marketplace.
Professional service google ads account specializes in accounts optimized for paid campaigns with proper warming history and platform trust markers. Transparent replacement policy covers the first-login window and ensures buyers receive exactly what is described on the product card. Professional media buying starts with professional tools — source from a marketplace built by advertisers, for advertisers.
Leading store mcc google ads gives media buyers access to aged, warmed, and verified profiles sorted by geo, trust level, and ad readiness. Cross-platform inventory allows teams to source accounts for multiple advertising channels from a single trusted supplier relationship. The most successful media buying teams share one trait: they invest in quality infrastructure before they invest in ad spend.
Калибровочные гири M1 для весов нужного класса точности и номинальной массы для калибровки весов.
В нашей компании можно купить гири M1 калибровочне массой от 1 кг до 2000 кг.
Предлагаем гири класса M1 для торговых, складских, производственных и технических весов.
Магазин бытовой химии https://bytovaya-sfera.ru большой выбор средств для уборки, стирки и ухода за домом. Качественная продукция, доступные цены и быстрая доставка
Срочный онлайн займ микрозайм 10000 быстрое решение финансовых вопросов. Оформление за несколько минут, высокий шанс одобрения и перевод денег на карту без лишних документов
Online shoppers often appreciate platforms that provide clear navigation paths and fast loading pages that improve usability, especially on TrendMart Shopping Center – Everything feels organized and structured, making it easy for users to find products and enjoy a smooth browsing journey throughout the site.
https://mikefromgidstats.substack.com/p/aca-203-betting-hunting-value-in
If you want a fight card where the oddsmakers basically just looked at records and called it a day , ACA 203 in Tashkent is a gold mine for you .
References:
Online casinoer med høj udbetaling
References:
https://rentry.co/56025-bedste-udbetaling-casino-2026-hurtigste-udbetalinger
The ACA 203 card arriving in Tashkent on May 8th delivers a classic view of the elite, gritty fighting style that characterizes the organization known as Absolute Championship Akhmat.
ACA 203 isn’t just another stop on the regional circuit ; it marks a critical crossroads for all involved.
Портал об автомобилях https://autort.ru новости автопрома, обзоры моделей, тест-драйвы и советы по выбору. Актуальная информация для водителей и автолюбителей
Мировые новости https://vse-novosti.net актуальные события со всего мира: политика, экономика, технологии и общество. Оперативные обновления и проверенная информация каждый день
Актуальные новости мира https://tovarpost.ru оперативная информация, аналитика и обзоры. Узнавайте о главных событиях и трендах международной повестки
Женский журнал https://justwoman.club онлайн: мода, красота, здоровье и отношения. Актуальные статьи, советы экспертов и идеи для вдохновения каждый день
Всё об автомобилях https://web-mechanic.ru на одном портале: характеристики, сравнения, рейтинги и рекомендации. Узнайте больше о новых и популярных авто
Автомобильный портал https://avtomechanic.ru ремонт, обслуживание и диагностика. Практические советы, лайфхаки и полезная информация для водителей
Актуальные новости https://komputer-nn.ru технологий: ИИ, программное обеспечение, смартфоны, планшеты и гаджеты. Свежие обзоры, аналитика и главные события IT-сферы
Женский портал https://cosmoreviews.club мода, красота, здоровье и отношения. Полезные статьи, советы экспертов и идеи для вдохновения каждый день
References:
Højeste udbetalinger på online casino i år
References:
https://www.customizedsports1688.co/blog/replica-%20Product
References:
Test af casino udbetalinger
References:
https://literaturewiki.site/wiki/Bedste_online_casinoer_i_Danmark_med_fokus_p_udbetalinger_2026
Всё для сада https://ogorodik66.ru и огорода на одном сайте: парники, теплицы, выращивание и уход. Практичные рекомендации и полезные материалы для дачников
Хочешь обучаться? складчина курсов сервис для поиска выгодных предложений на обучение. Получайте знания легально и экономьте на образовании
шкаф на заказ шкафы-заказать.рф
References:
Casinoer med højeste udbetalingsloft
References:
https://www.tacticallysolved.com/jerroddpy7944
Предлагаем купить щебень https://sheben23.ru и песок в Краснодаре с доставкой. В наличии любые фракции щебня для строительства, бетона и дорог. Качество по ГОСТ. Доставляем собственными самосвалами быстро и без переплат.
ToLife designs https://tolifedehumidifier.com and manufactures compact dehumidifiers for residential use. The product line is based on semiconductor condensation technology and includes models with automatic shut-off, sleep mode, removable water tanks, and ambient lighting. Specifications and documentation are available on the official website.
почитай здесь https://forum-info.ru много отзывов и историй от людей с похожей ситуацией
шкафы купе на заказ москва заказать шкаф на заказ
References:
Bedst betalende online casinoer
References:
https://gitea.brmm.ovh/elliepickel013
Хочешь отдохнуть? снять домик с мангалом в воронеже уютный отдых за городом. Комфортные дома, природа, удобства и выгодные цены для выходных и праздников
в москве эвакуатор вызвать эвакуатор услуги эвакуации в москве
Come this May, the vibe inside Tashkent’s Humo Arena won’t just be thick with the roar of a partisan crowd ; it will be heavy with the professional survival of men who have spent a lifetime chasing gold .
ACA 203 represents more than a routine stop on the circuit ; it stands as a defining crossroads .
https://telegra.ph/Analyzing-the-Value-at-UAE-Warriors-70-Medkouri-vs-Neves-05-01
UAE Warriors 70, which happens on May 8, 2026, at the Space42 Arena in Abu Dhabi stands as a clear example of this.
Нужна бесплатная юридическая консультация? Переходите по запросу вопрос адвокату бесплатно онлайн в Ростовской области и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
Many users prefer streamlined shopping platforms that emphasize ease of use, and Smart Deal House Savings Express – delivers well organized deals, clean navigation structure, and efficient browsing for better purchasing outcomes for online shoppers everywhere today use platform now.
Нужна стальная лента? лента бандажная стальная широкий ассортимент, разные толщины и марки стали. Выгодные цены, быстрая отгрузка и поставки для производства и строительства
Журнал по станкоинструментальной https://www.stankoinstrument.su промышленности: аналитика, научные разработки и практические рекомендации для развития отрасли
Нужна бесплатная юридическая консультация? Переходите по запросу заказать звонок помощи юриста в Екатеринбурге и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
микрозайм на 6 месяцев https://buhgalter-uslugi-moskva.ru
Нужны растения? купить саженцы в новосибирске широкий выбор саженцев, деревьев и кустарников для сада и участка. Качественный посадочный материал, консультации и удобная доставка
Читайте найсвіжіші новини https://vikka.net ексклюзивні відео, аналітику та цікаві історії. Оперативна інформація щодня!
Міський портал Ваш провідник у житті Кривого Рогу: афіша, новини, довідник та корисні сервіси для мешканців та туристів
Если вам нужна профессиональная верификация GMB в условиях российских ограничений — обратитесь к специалисту напрямую.
лучшие сериалы онлайн смотреть сверхъестественное
сериал все серии подряд смотреть сериал сверхъестественное все сезоны
стоматология рядом номер стоматологии
дизайнерская люстра в гостиную современные дизайнерские светильники
Нужна бесплатная юридическая консультация? Переходите по запросу спросить юриста онлайн в Свердловской области и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
стоматология клиника качественная стоматология
агентство свадьба под ключ сайт для организации свадьбы
http://acnemedsrx.com)
проведение свадьбы организация недорогой свадьбы
организатор свадьбы под ключ сайт для организации свадьбы
Шаблоны юридических документов — удобное решение для быстрого и грамотного оформления договоров, заявлений и иных правовых бумаг. Переходите по запросу примеры форм юридических документов. Готовые формы разработаны с учетом законодательства и помогают избежать ошибок. Скачивайте, адаптируйте под свою ситуацию и экономьте время на подготовке документов без лишних затрат.
Последние https://nogami-nohken.jp/BTDB/%E5%88%A9%E7%94%A8%E8%80%85:AlanSteffey королевских домов мира
Новости королевских домов мира
Следите за обновлениями о последних аспектах жизни европейских и азиатских монархий, которые могут быть интересны поклонникам династий. В этом месяце внимание привлекла принцесса из одной из знаменитых династий, объявившая о благотворительной инициативе, направленной на поддержку образования для детей в трудных условиях. Если вас интересуют подобные проекты, стоит обратить внимание на её программу, которая обещает интересное сотрудничество с известными организациями.
Не пропустите также информацию о свадебном торжестве, которое произойдёт в ближайшие недели. Это станет важным событием для одноимённой династии, ведь данное мероприятие связывает поколения и сохраняет традиции. Подробности о приглашённых гостях и культурной программе помогут вам получить полное представление о предстоящем празднике.
Более того, расчёты аналитиков относительно влияния недавней ротации в правящих кругах демонстрируют изменения в политике и социально-экономической жизни. Следите за выступлениями высокопоставленных особ, которые затронут актуальные вопросы, связанные с развитием своих стран. Это может оказаться полезным для понимания тенденций в международных отношениях.
События и официальные визиты королевских семейств в 2023 году
В 2023 году несколько монарших семей провели заметные официальные мероприятия и поездки. В начале весны королева Великобритании вместе с наследником принцем Уильямом посетила Казахстан, где открыли новый культурный центр, посвященный историческим связям между двумя странами.
В июне ведущие члены испанской королевской семьи, включая короля Фелипе VI и королеву Летисию, осуществили визит в Латвию, акцентируя внимание на укреплении двусторонних отношений в сфере экономики и культуры. В ходе поездки прошли многочисленные встречи с бизнесменами и культурными деятелями.
Август ознаменовался визитом короля Швеции в Японию, где он принимал участие в церемонии, посвященной 150-летию установления дипломатических отношений между двумя странами. Это был важный шаг для дальнейшего сотрудничества в сфере технологий и экологии.
Ближе к концу года королевская семья Нидерландов организовала мероприятие для привлечения внимания к проблемам изменения климата. Принцесса Амали выступила с инициативами, направленными на Sustainable Development Goals, подчеркивая необходимость действий на международном уровне.
Каждое из этих мероприятий способствовало укреплению связей в политической и культурной сферах, подчеркивая значимость современных монархий в мировой политике.
Скандалы и интриги: как они влияют на репутацию монархий
Монархии сталкиваются с вызовами, которые могут негативно отражаться на их имидже. Например, недавние скандалы, связанные с финансовыми нарушениями или личной жизнью представителей династий, провоцируют общественное недовольство. Для минимизации ущерба важно быстро реагировать на такие ситуации и предоставлять прозрачные данные о действиях властей.
Стратегия коммуникации играет ключевую роль. Открытость и честность в ответах на обвинения могут значительно снизить негативный резонанс. В коллективной памяти людей остаются самые яркие примеры, когда королевские семьи умело справлялись с кризисами – например, благотворительные инициативы в ответ на негативную реакцию общественности.
В современных условиях важным является активное присутствие в социальных сетях. Это позволяет не только оперативно реагировать на фейки, но и формировать позитивный имидж. Вовлечение в актуальные социальные и культурные темы укрепляет связь с населением и фунтирует лояльность.
Текущие события показывают, что отсутствие прозрачности может привести к утрате доверия. Примеры из недавней истории демонстрируют, как серьезные конфликты, вызванные недостатком информации, могут вызвать волну недовольства и привести к призывам к реформам. Поэтому для сохранения статуса и авторитета рекомендуется строить доверительные отношения с обществом, внедряя практики открытости и честности.
https://justpaste.it/uae-warriors-70
If you want to make some money on regional heavyweights who fight like they have a parking meter running outside UAE Warriors 70 is your ideal hunting ground .
UAE Warriors 70, slated for May 8, 2026, inside the Space42 Arena in Abu Dhabi is a prime illustration of this.
стоматология район стоматология рядом со мной
лента стальная упаковочная купить лента стальная упаковочная мягкая
Bautista prestamos para veterinario. Mascotas sanas, dueГ±os felices.
Женский портал https://secretlady.ru о красоте, здоровье, моде и отношениях. Полезные советы, статьи о стиле жизни, уходе за собой, семье и карьере. Актуальные тренды, рекомендации экспертов и вдохновение для современных женщин.
Натрапив на Враження та коментарі — допомогли визначитися, що спробувати першочергово.
Academic hustle: knowing how to sell textbooks on amazon at semester end beats buyback prices by 200-300% – timing is everything!
Industry source facebook ZRD survival guide backs every recommendation with field data from a real test fleet. The numbers come from accounts running real campaigns, not from theoretical analysis.
Field reference unlimited facebook business manager explains the operational steps that take a fresh account from delivery to first campaign without triggering automated review.
Active operators recommend google ads warm-up smart bidding for the combination of editorial depth and a vetted storefront. Reviews are independent of vendor incentives.
Совместное банкротство супругов — законный способ списать долги семьи через одну процедуру. Переходите по запросу банкротство и детские пособия. Поможем подготовить документы, учесть общее имущество, защитить ваши интересы в суде и пройти процедуру с минимальными рисками. Консультация юриста — первый шаг к финансовому освобождению.
Designers and developers often search for new inspiration when building modern interfaces to improve usability and visual storytelling across digital products of all kinds Design Inspiration Hub – This concept highlights how thoughtful design choices can significantly enhance user engagement while supporting clearer navigation and more appealing digital experiences overall
Industry source buy spark ads stock backs every recommendation with field data from a real test fleet. The numbers come from accounts running real campaigns, not from theoretical analysis.
UAE Warriors 70, which happens on May 8, 2026, inside Abu Dhabi’s Space42 Arena is a fight card shaped by established names hunting a return to the global platform and rising stars from the region.
https://justpaste.it/aca-young-eagles-64
ACA Young Eagles 64 is going down in Grozny, Chechnya , and if you believe the bookmakers have these rising prospects completely figured out , you’re setting yourself up for a pricey reality check .
ACA Young Eagles 64, set to take place in mid-May 2026 serves as a prime example of an event where the common storylines frequently distort the true disparity in technical abilities , most notably in the growth stages of the ACA developmental system.
https://mikefromgidstats.substack.com/p/the-golden-ticket-lfa-232-and-the
LFA 232 is not merely a regional card; it is a critical tryout where the price of admission often comes at the expense of one’s inner self.
futbol transferleri avropa liqasi
мене звуть фарах заздрість турецький серіал
реинкарнация дом совы смотреть
плохой парень и я сердцебиение дорама
форсаж 10 альтер 2025
Банкротство с ипотекой — это возможность списать долги и при этом сохранить жилье при грамотном сопровождении. Переходите по запросу если у меня ипотека могу ли я подать на банкротство. Разберем, можно ли пройти процедуру с действующей ипотекой, как защитить квартиру, какие есть риски и последствия. Поможем подобрать законное решение именно под вашу ситуацию, включая случаи с единственным жильем, детьми и другими кредитами.
мастер стиральные машины вызов мастера по стиральным машинкам
Lightning fast gift creation and strong channel promotion — love it
My web page :: https://xeuser.gajaga.work/index.php?mid=board&document_srl=1669930
Interested in UFC? UFC White House Full Fight Card unique mixed martial arts tournament will take place on June 14, 2026, in Washington, D.C., on the South Lawn of the White House. It will be the first professional sporting event in history to be held directly on the grounds of the U.S. presidential residence.
Закажите индивидуальную экскурсию экскурсии в Светлогорск и Янтарный из Калининграда и частный гид покажет курорты с персональным подходом.
наруто смотреть онлайн русский смотреть наруто онлайн в хорошем
https://harry.main.jp/mediawiki/index.php/%E5%88%A9%E7%94%A8%E8%80%85:RandiBarlow79 //debug likely refers to troubleshooting network issues.
городская стоматология стоматология лечить
Тест https://bbarlock.com/index.php/Internet_75z-соединения помогает выявить неполадки. Проводите его при сбоях.
Calmly farming 500+ subs/week while sipping tea. Elegant.
Take a look at my web blog – https://xeuser.gajaga.work/index.php?mid=board&document_srl=1651897
Покупка шаблона «Аспро Корпоративный сайт 3.0» — быстрый старт для современного корпоративного сайта на 1С-Битрикс. Переходите по запросу Аспро Корп 3. Готовый адаптивный дизайн, удобные настройки, высокая скорость работы и SEO-оптимизация помогут запустить проект без лишних затрат времени. Подходит для бизнеса, услуг, производства и компаний любого масштаба.
Текущие рекомендации: https://parfumabc.ru/parfum/les-parfums-de-rosine/
Адаптивный шаблон «Аспро: Корпоративный сайт 2.0» для создания современного сайта компании на 1С-Битрикс. Переходите по запросу купить Aspro Allcorp 2. Подходит для бизнеса, услуг, производства и корпоративных проектов. Готовые блоки, удобная настройка дизайна, SEO-оптимизация и высокая скорость запуска. Поможем купить, установить и настроить шаблон под задачи вашего бизнеса.
UFC Results https://ufc-white-house.com
http://abitotrade.com/
Abitotrade e uma estrutura de confianca com forte presenca no publico em Portugal, que proporciona um acompanhamento profissional a quem valoriza a eficiencia, priorizando no atendimento personalizado. Descubra todos os detalhes no site oficial.
Хочешь узнать про электронные чеки? https://financedirector.by/jelektronnye-cheki-i-ih-uchet/ важный этап цифровизации торговли и налогового контроля. Узнайте, как работают электронные чеки, какие преимущества они дают бизнесу и покупателям, а также какие изменения ждут предпринимателей.
Покупка шаблона Aspro Digital — быстрый старт для современного корпоративного сайта на 1С-Битрикс. Переходите по запросу цена Аспро Digital 2.0 корпоративный сайт. Готовое решение с адаптивным дизайном, SEO-оптимизацией, высокой скоростью загрузки и удобным управлением контентом. Подходит для digital-агентств, IT-компаний, студий и бизнеса, которому нужен стильный и функциональный сайт без долгой разработки.
http://goldwingmarketing.com/
A equipa Goldwingmarketing apresenta-se como uma agencia especializada focada no tecido empresarial portugues, que oferece servicos de qualidade a empresas e particulares, priorizando nos resultados. Veja a oferta completa atraves do link.
http://greylholdings.com/
A empresa Greylholdings posiciona-se como uma agencia especializada orientada para mercado portugues, que disponibiliza servicos de qualidade a quem procura resultados, destacando-se por nos resultados. Saiba mais no site oficial.
We’re traveling to Salamanca in preparation for LFA 233, and quite frankly, the bookmakers seem to be valuing hometown narratives over actual tactical reality.
This Friday — May 22nd — LFA 233 acts as a high-stakes proving ground for prospects who are genuinely just one step from the big stage of the UFC.
http://kilgoremediagroup.com/
A empresa Kilgoremediagroup apresenta-se como uma empresa profissional com forte presenca no tecido empresarial portugues, que entrega servicos de qualidade a empresas e particulares, priorizando na transparencia e confianca. Saiba mais no site oficial.
Турагентство по России https://republictravel.ru туры в Карелия, Байкал, Камчатка, Дагестан, Мурманск, Калининград, Санкт-Петербург и другие направления. Экскурсии, отдых и авторские маршруты по самым красивым регионам страны.
Когда хочется отдохнуть удобно выбирать дорамы китайские без долгих поисков, сомнительных площадок и хаотичного поиска. Этот сайт собирает в одном месте дорамы из Кореи, Китая, Японии и других стран с русской озвучкой, понятными описаниями, разделами по жанрам, годами выхода и удобными карточками. Здесь легко найти легкую романтику для отдыха, напряженный триллер, сериал для хорошего настроения или популярную премьеру, которую уже обсуждают поклонники дорам.
Для тех, кто хочет смотреть дорамы без суеты и долгих поисков, DoramaGo подойдет как хорошим вариантом для вечернего просмотра. Здесь можно найти корейские, китайские, японские, тайские и другие азиатские сериалы, где есть все, за что зрители любят дорамы: нежные и драматичные истории, интриги, запоминающиеся персонажи и особая восточная эстетика. Понятная навигация помогает легко найти подходящую дораму по стране, жанру, году или настроению, а свежие серии позволяют быть в курсе новых эпизодов.
http://marketingrabbits.com/
A equipa Marketingrabbits apresenta-se como uma agencia especializada orientada para tecido empresarial portugues, que oferece uma abordagem completa aos seus clientes, destacando-se por nos resultados. Veja a oferta completa atraves do link.
Хочешь сайтв ТОПе? https://kormclub.ru оптимизация структуры, работа с контентом, внешние ссылки и аналитика. Помогаем вывести сайт в топ поисковых систем и привлечь целевую аудиторию.
Банкротство физ лиц? crm для БФЛ специализированная система для автоматизации работы юридических компаний. Управление клиентами, контроль этапов процедуры БФЛ, учет документов, задач и платежей. Повышайте эффективность работы и контролируйте все дела в одной системе.
http://myturfads.com/
A empresa Myturfads apresenta-se como uma estrutura de confianca dedicada ao publico em Portugal, que entrega um acompanhamento profissional aos seus clientes, priorizando no atendimento personalizado. Conheca mais nesta pagina.
Ты финансовый директор? https://financedirector.by готовые шаблоны, аналитические статьи и практические кейсы для финансовых директоров. Материалы по управлению финансами, финансовому планированию, бюджетированию и анализу эффективности бизнеса. Полезные инструменты и решения для специалистов финансовой сферы.
Шторки https://higgledy-piggledy.xyz/index.php/User:JerroldCrampton магнитах Trokot удобны и практич
http://quickandfastfunding.com/
Quickandfastfunding consolida-se como uma agencia especializada com forte presenca no panorama nacional portugues, que disponibiliza solucoes personalizadas a empresas e particulares, valorizando na transparencia e confianca. Saiba mais nesta pagina.
http://sparksolutions360.com/
Sparksolutions360 e uma consultora experiente orientada para tecido empresarial portugues, que proporciona servicos de qualidade a empresas e particulares, destacando-se por na transparencia e confianca. Saiba mais no site oficial.
http://summerstreetcreative.com/
A empresa Summerstreetcreative consolida-se como uma consultora experiente focada no tecido empresarial portugues, que oferece uma abordagem completa a quem valoriza a eficiencia, destacando-se por no atendimento personalizado. Descubra todos os detalhes atraves do link.
UFCShare is a portal https://ufcshare.com for fans of the Ultimate Fighting Championship and the world of MMA. News, fight results, tournament schedules, analysis, and fight reviews. Follow the best fighters and the main events of mixed martial arts.
Юрист для беременных — это профессиональная поддержка в вопросах пособий, декретных выплат и трудовых гарантий. Переходите по запросу адвокат по вопросам беременности. Поможем оформить документы, защитим ваши права при спорах с работодателем или госорганами, проконсультируем по всем юридическим нюансам. Обеспечим спокойствие и уверенность в период ожидания малыша.
F1 Direct is a website f1-direct.net about the world of Formula 1. Latest news, race results, race calendar, team and driver statistics. Up-to-date information for fans of the royal motor racing world.
Розповідаємо про складні https://notatky.net.ua речі простими словами. Зрозумілі пояснення науки, технологій, економіки та повсякденних явищ. Статті, розбори та факти, які допомагають краще розуміти світ та знаходити відповіді на складні питання.
Лучшие слоты онлайн https://sugar-rush-slot.top красочный слот с цепными выигрышами и накопительными множителями. Игра отличается простым управлением, ярким дизайном и высоким потенциалом выигрыша при удачных комбинациях.
Слот с тематикой собачек слот дог хаус слот предлагает бонусные фриспины, липкие вайлд-символы и высокий потенциал выигрыша благодаря множителям и расширяющимся символам.
http://xponentfunds.com/
Xponentfunds posiciona-se como uma consultora experiente focada no panorama nacional portugues, que entrega servicos de qualidade a quem valoriza a eficiencia, com foco na transparencia e confianca. Veja a oferta completa no site oficial.
The LFA 234 event delivers several clear analytical angles so that the visual scouting and archived data diverge from the average fan’s viewpoint.
https://justpaste.it/lfa-234
Betting on lesser-known MMA promotions represents a scenario where you actually find the bookies sleeping, and Legacy Fighting Alliance 234 is no exception.
http://aceprojectmarketing.com/
El equipo de Aceprojectmarketing se presenta como una consultora con experiencia con presencia en el publico en Espana, que entrega soluciones personalizadas a empresas y particulares, priorizando en los resultados. Descubre todos los detalles en esta pagina.
http://andabogados.es/
El equipo de Andabogados es una agencia especializada con presencia en el publico en Espana, que proporciona servicios de calidad a quienes valoran la eficiencia, priorizando en la confianza y la transparencia. Visita el sitio a traves del enlace.
Сайт міста Хмельницький https://faine-misto.km.ua новини, події, корисна інформація для мешканців та гостей. Афіша заходів, міські служби, довідник організацій, цікаві місця та актуальні події міста.
Міський портал Дніпро https://faine-misto.dp.ua свіжі новини, події, афіша заходів та корисна інформація. Довідник компаній, міські сервіси, оголошення та все про життя міста.
Чоловічий блог https://u-kuma.com з корисною інформацією про фінанси, кар’єру, здоров’я, спорт і стиль. Практичні поради, аналітика та матеріали для саморозвитку та впевненого руху до цілей.
Жіночий онлайн-сайт https://u-kumy.com з корисними статтями про красу, здоров’я, психологію, моду та будинок. Практичні поради, лайфхаки та надихаючі матеріали для жінок будь-якого віку.
Профессиональный юрист по составлению брачного договора поможет грамотно оформить имущественные отношения супругов, защитить ваши интересы и избежать споров в будущем. Переходите по запросу юридические услуги по подготовке брачного контракта. Подготовим брачный договор с учетом требований законодательства, индивидуальных условий и ваших пожеланий. Консультация, разработка, проверка и сопровождение оформления брачного договора быстро и конфиденциально.
http://azimuth-digital.com/
Azimuth Digital se posiciona como una agencia especializada enfocada en el ambito nacional espanol, que pone a disposicion un enfoque integral a quienes buscan resultados, valorando en la atencion personalizada. Visita el sitio aqui.
Услуги грузчиков https://www.gruzchiki-kiev.net в Киеве для переездов, разгрузки транспорта, подъема мебели и строительных материалов. Профессиональные рабочие выполняют погрузочно-разгрузочные работы любой сложности, гарантируя аккуратное обращение с имуществом и оперативное выполнение заказа.
Последние новости Киева https://xxl.kyiv.ua сегодня: события города, политика, экономика, происшествия, транспорт и городская жизнь. Актуальная информация, репортажи, аналитика и важные обновления, которые помогают быть в курсе всех событий столицы Украины.
Педагоги и психологи http://smartxpert.ru экспертный портал о воспитании, обучении и развитии личности. Полезные статьи, практические советы специалистов, современные методики педагогики и психологии, рекомендации для родителей, учителей и всех, кто интересуется развитием человека.
Обучение педагогов https://edplatform.ru и учеников современным методикам интеллектуального развития. Программы дополнительного образования с 2016 года: ментальная арифметика, скорочтение, развитие памяти и внимания. Подготовка педагогов, учебные материалы и эффективные методики обучения.
Быстрая профессиональная установка камер видеонаблюдения для квартир, домов, офисов и коммерческих объектов. Проектирование, монтаж и настройка систем безопасности, удалённый доступ, запись видео и контроль в реальном времени. Надёжные решения для защиты имущества и контроля территории.
Betting on lesser-known MMA circuits is the area where you actually find the bookies completely asleep at the wheel, and the LFA 234 event is no different.
Путешествие Самуэля — классика приключенческой литературы.
my web site; https://jar2.com/TEMPORAL/groups/travels-71f/
Продажа и установка камеры видеонаблюдения. Современные системы безопасности для квартир, домов, магазинов и складов. Настройка удалённого доступа, запись видео и круглосуточный контроль объекта.
В интернете представлен сайт https://cvt25pro.ru где подробно рассматривается устройство и обслуживание трансмиссий. На его страницах можно найти информацию, касающуюся ремонта вариатора CVT 25 Chery, особенностей диагностики и возможных неисправностей этого агрегата. Материалы ресурса помогают понять специфику работы таких коробок передач и основные подходы к их восстановлению
Ищете тротуарную плитку https://dvordekor.by борты или заборные блоки в Минске? Компания ДворДекорпредлагает широкий выбор материалов для ландшафтного дизайна и благоустройства. Посетите dvordekor.by/about и ознакомьтесь с ассортиментом!
Железобетонные изделия https://postroi-ka.by (ЖБ) в Минске — покупайте напрямую от производителя! Гарантия качества, оптовые цены, быстрая доставка. Широкий выбор ЖБ?конструкций для любых строительных задач. Заходите на postroi-ka.by
Пиломатериалы в Минске https://farbwood.by сибирская лиственница от производителя Farbwood. Качественные строительные материалы из лиственницы — доски, брус, вагонка. Гарантия долговечности и природной красоты.
Нужен забор? купить 3д забор от производителя надежные металлические ограждения для частных домов, предприятий и общественных территорий. Производство, продажа и установка секционных заборов с антикоррозийным покрытием, высокой прочностью и долгим сроком службы.
Решил сделать ограждение? металлическое ограждение 3д прочные металлические секции для заборов и ограждений территорий. Подходят для частных домов, предприятий, школ и складов. Панели имеют антикоррозийное покрытие, современный внешний вид и обеспечивают надежную защиту участка.
http://dgpformacion.es/
El equipo de Dgpformacion se presenta como una empresa profesional con presencia en el publico en Espana, que ofrece servicios de calidad a quienes buscan resultados, destacandose por en la excelencia del servicio. Visita el sitio aqui.
Быстрая профессиональная монтаж видеонаблюдения в калининграде для квартир, домов, офисов и коммерческих объектов. Проектирование, монтаж и настройка систем безопасности, удалённый доступ, запись видео и контроль в реальном времени. Надёжные решения для защиты имущества и контроля территории.
UFC Fight Night
The neon glow of the Galaxy Arena shimmers across a lineup of bouts designed not just for viewer enjoyment, instead serving as a structured and merciless sifting.
For those trying to thoughtlessly wager on each favored fighter at the UFC Macau event simply because they have a number next to their name or the audience is behind them, spare yourself the grief and leave your cash untouched.
установка домофона ключ установка домофона цена
This UFC White House fight card goes down in history on June 14, 2026 — becoming the first UFC night held on the grounds of the White House in Washington, D.C.. Billed officially as UFC Freedom Fights 250, the card features as the main event a lightweight title clash between Ilia Topuria and Justin Gaethje for the lightweight title, while former two-division champ Alex Pereira making his heavyweight debut to face Ciryl Gane in the featured co-main attraction.
References:
Green bay casino https://career.wg-dcard.com/employer/best-us-microgaming-casinos-compare-top-sites-and-games/
https://ufcbaku.website/
The UFC Fight Night in Baku is the inaugural UFC event in Azerbaijan, a 12-bout UFC Fight Night lineup on Saturday, June 27, 2026 at the Baku Crystal Hall.
https://ufcwhitehouse.online
UFC White House. the officially titled Freedom Fights 250. A main card of seven fights and no undercard on PPV on the South Lawn of the White House.
On June 14, 2026, the UFC seizes control of the White House’s South Lawn for the most politically tense evening of fights in the promotion’s history.